[0008] The
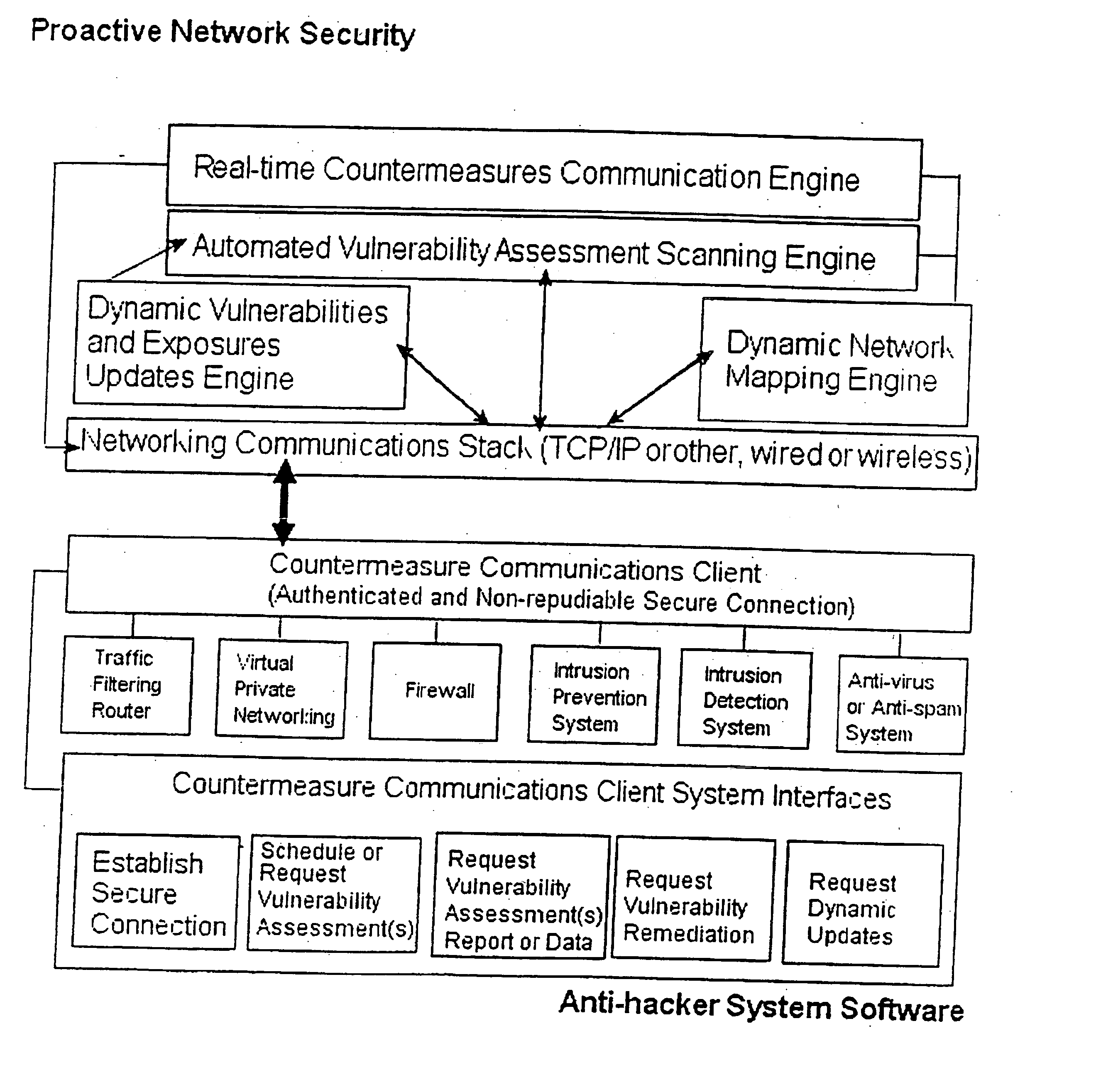
software engine may securely and dynamically update one or all components of the INFOSEC ENGINE and / or all INFOSEC ENGINE PLUGINs as well as other key security components. The
software engine acts as a gateway between users, personal computers, servers, services and the
computer network (internet,
intranet,
extranet,
wide area network,
wireless network or
local area network). An
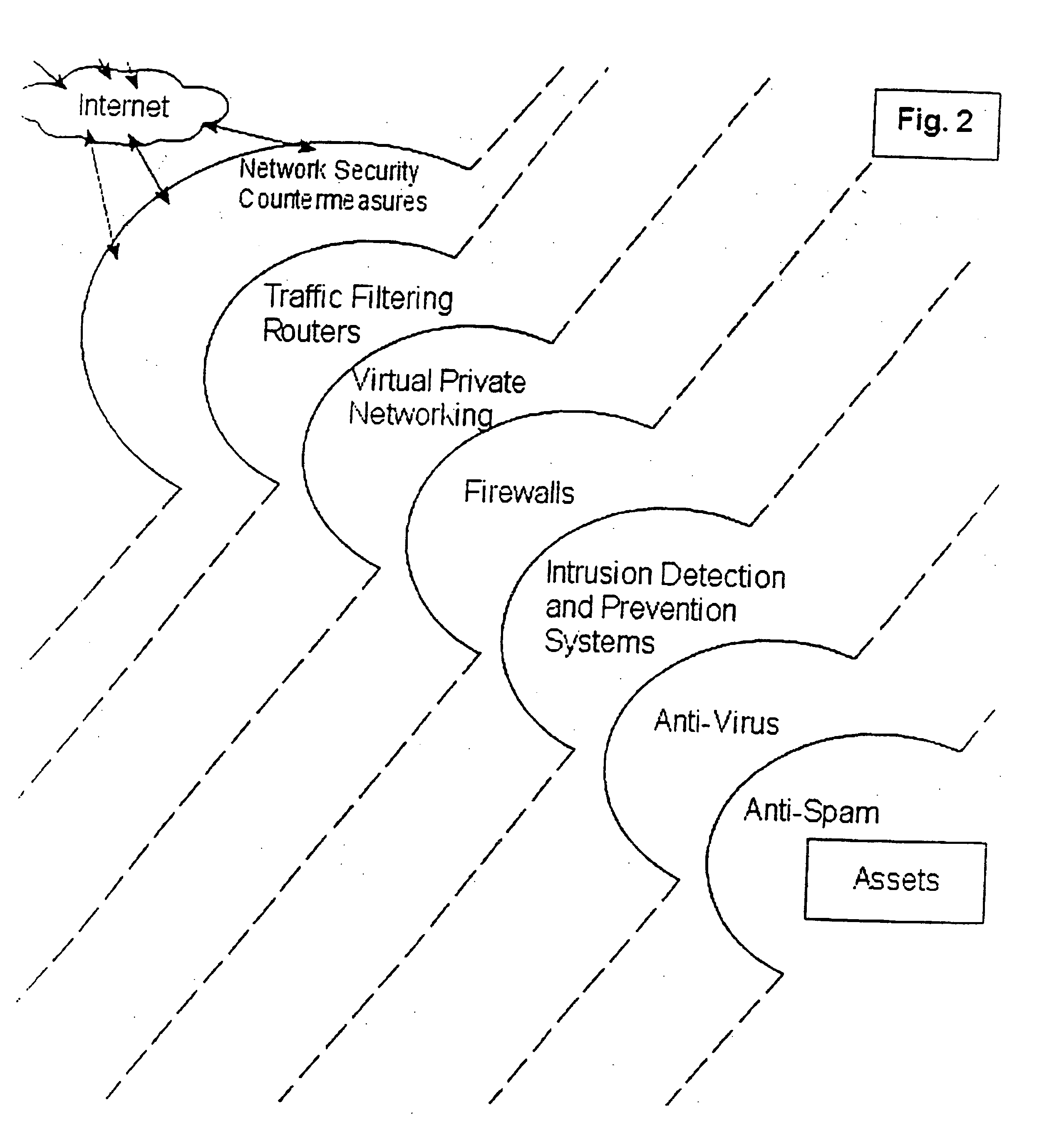
Information Security (INFOSEC)
software component may plug into the INFOSEC engine to, from time to time, expand the INFOSEC capabilities. Sample PLUGINs may include Firewalls (FW), virtual private networks (VPNs) AntiVirus Servers (AVS), Anti Distributed Denial of Service (Anti-DDoS),
Certificate Authorities (CA),
Content Filtering and Application Caching (PROXY),
Encryption Acceleration and Secure Sockets Layer (SSL), Intrusion Detection Systems (IDS), Intrusion Prevention Systems (IPS),
Vulnerability Assessment (VA),
Vulnerability Remediation (VR), and
Wireless Security (802.11b) using
Wireless Encryption Protocol (WEP), Clustering and
High Availability (HA). The
system may also include an
operating system that has been hardened against known weaknesses and
attack methodologies of hackers. In a further optional embodiment, the
system may include a software component that enables the INFOSEC Engine to be deployed on more than one system that can act as a single INFOSEC Engine through a
computer network. An optional software component “heart-beat” monitor may exchange
heartbeat signals between two or more INFOSEC appliances and enables one appliance to takeover for another should the other malfunction. The systems and methods described herein can be operated on conventional hardware platforms including
Personal Computer (PC) or generic
server appliances that run the Windows or Linux operating systems. Optionally, the systems may employ a
client-
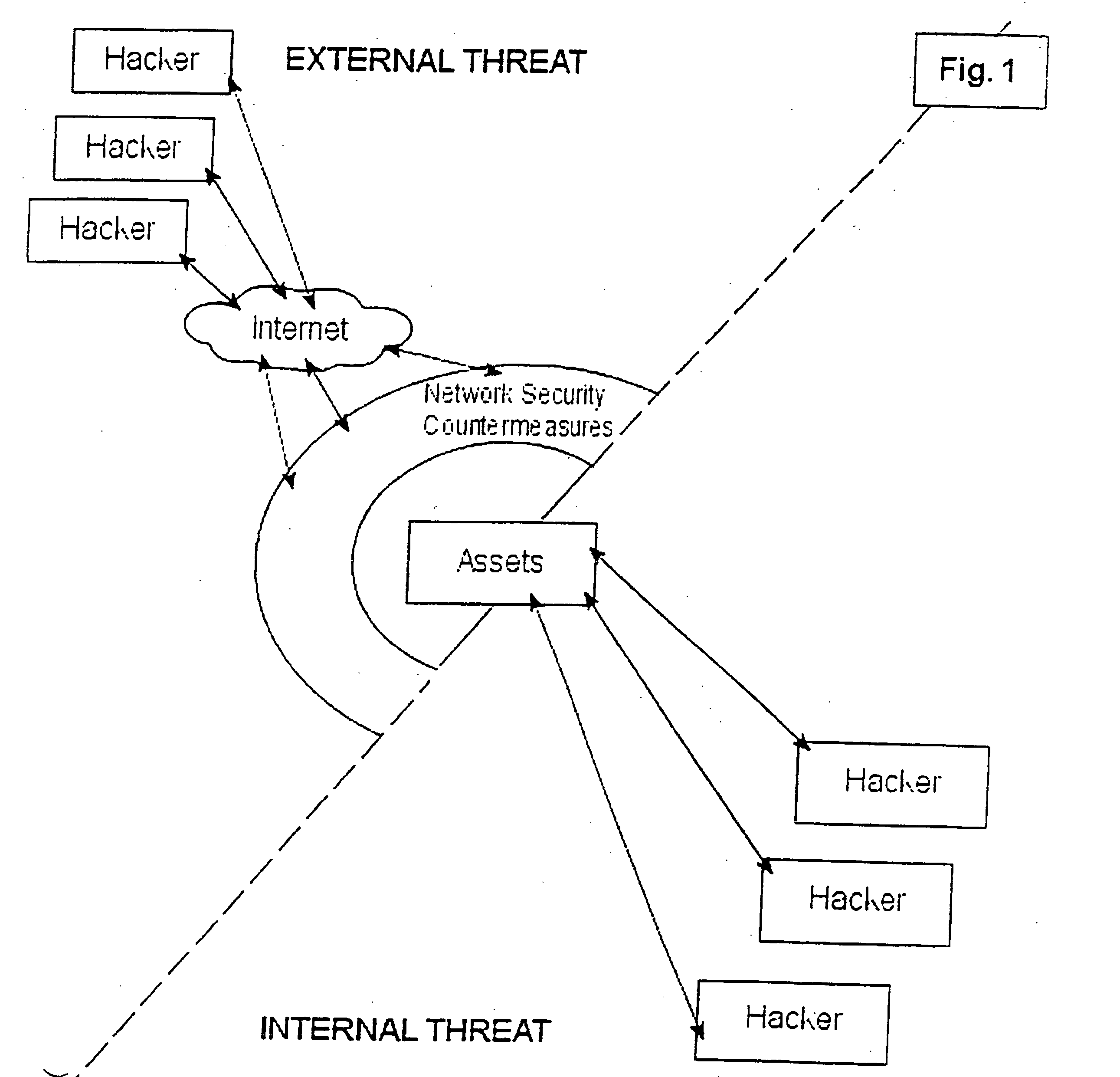
server modular based software structure for secure, authenticated an non-repudiable communications between the Proactive
Network Security system and a traditional Countermeasures
System to increase the probability that a hacker will not be able to break into the existing network infrastructure through automated
vulnerability assessment, reporting, and remediation.
[0019] Another object is to provide a proactive
network security system to protect against hackers that can perform numerous INFOSEC functions in one “open box” appliance that scales in physical size from a small PC to a large generic
server appliance. Should these INFOSEC functions exist in another
network security appliance, the systems described herein shall be able to communicate with said INFOSEC
countermeasure through a well-defined and
secure communication interface to enable more proactive network security through
automation.
 Login to View More
Login to View More  Login to View More
Login to View More