Visual image authentication and transaction authorization using non-determinism
a technology of transaction authorization and visual image, applied in the security field, can solve the problems of user's computer, lack of secure integration of user identity, and insecure transactions
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Benefits of technology
Problems solved by technology
Method used
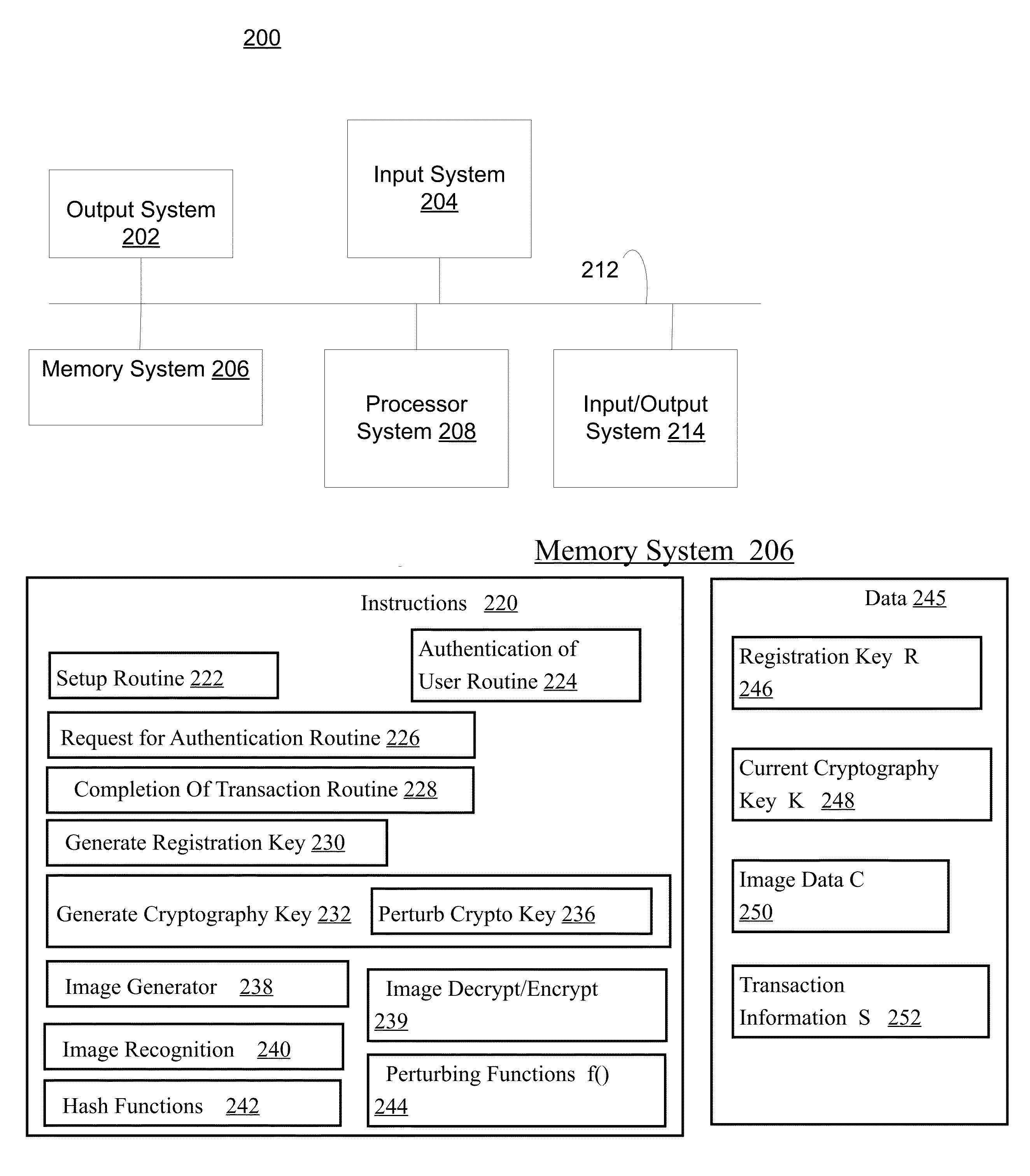
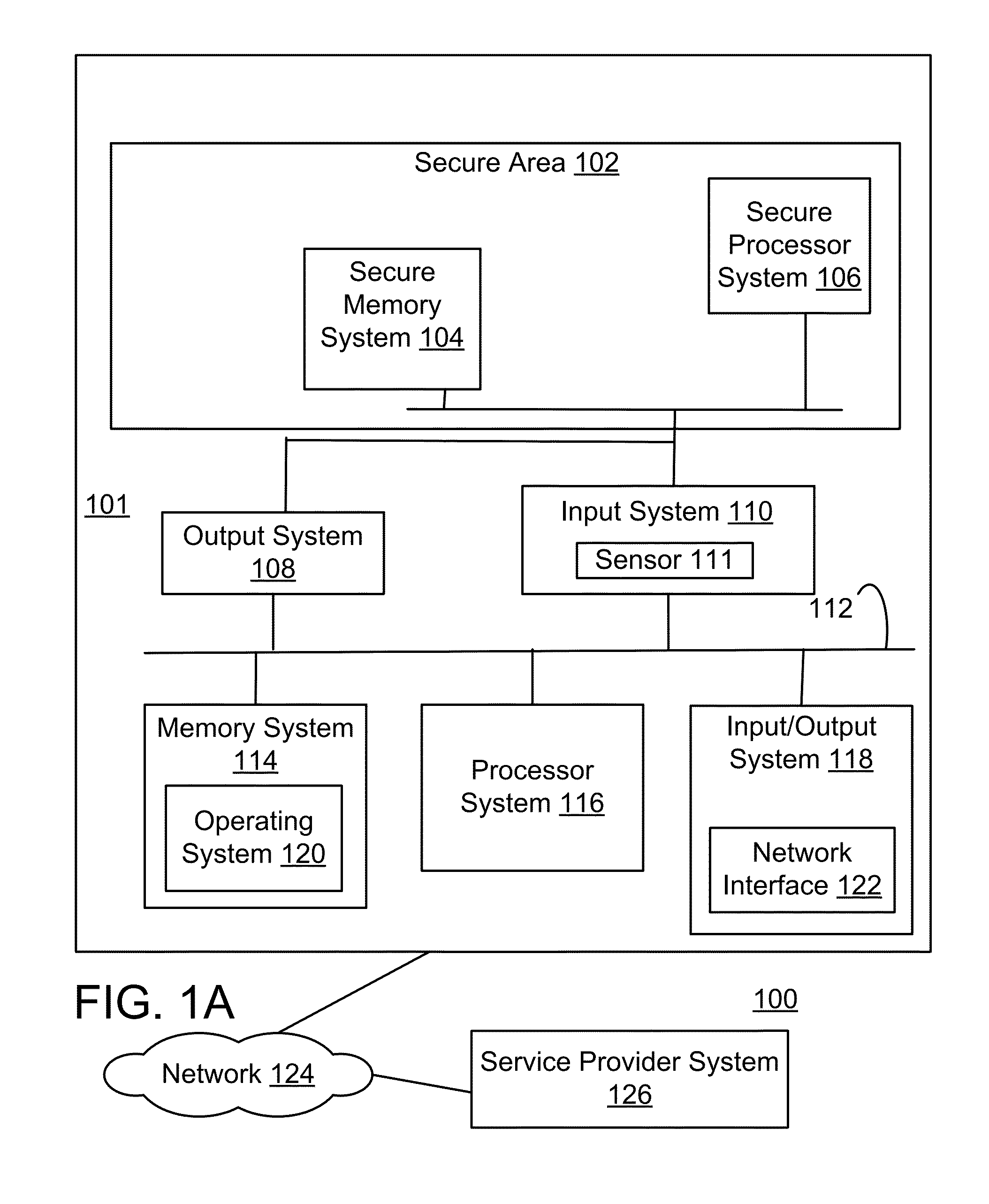
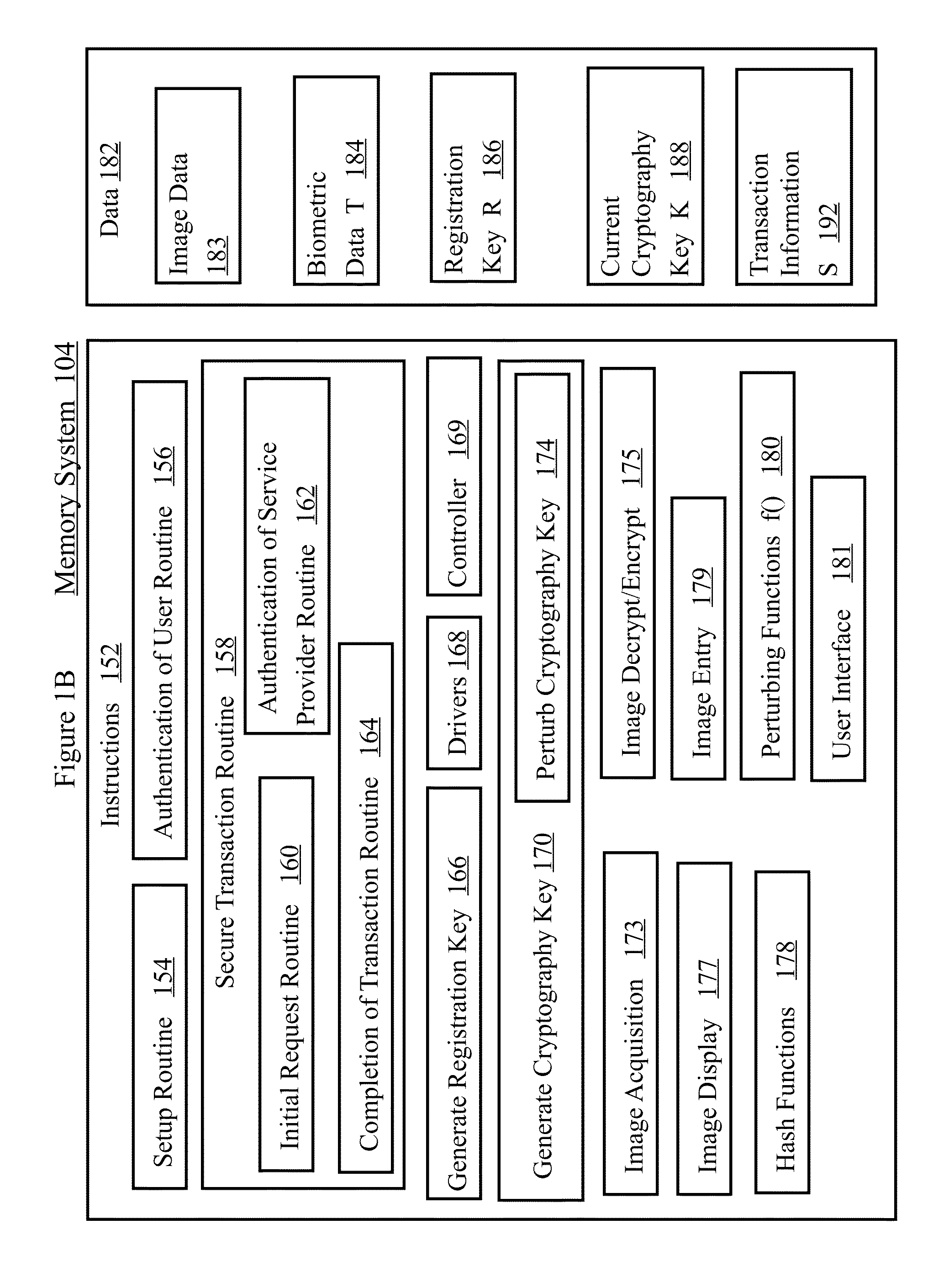
Image
Examples
Embodiment Construction
[0051]Although the issues discussed in the background or elsewhere may have motivated some of the subject matter disclosed below, nonetheless, the embodiments disclosed below do not necessarily solve all of the problems associated with the subject matter discussed in the background or elsewhere. Some embodiments only address one of the problems, and some embodiments do not solve any of the problems associated with the subject matter discussed in the background or elsewhere. In general, the word “embodiment” is used to specify an optional feature and / or configuration.
[0052]A groundbreaking method for cybersecurity is described that is more secure against modern malware, and provides a much better user experience compared with passwords or hardware tokens such as SecurID. No More Passwords uses visual images that are selected by a user to create a set of “favorites” that can easily be recalled and quickly selected by the user at login.
[0053]No more passwords leverages the superior pow...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More