When a
computer device is infected by a malicious code infection the user will often notice degradation of system performance as the infection can create unwanted and
time consuming system activity, excessive memory usage, and bandwidth consuming network traffic.
These factors can also cause
instability problems leading to application or system-wide crashes.
The user of an infected device may incorrectly assume that poor performance is a result of
software flaws or hardware problems, taking inappropriate
remedial action, when the actual cause is a malicious code infection of which they are unaware.
Detecting the presence of malicious code infections is challenging as the authors of malicious code design their
software code to be difficult to detect, often employing
obfuscation techniques that deliberately hides the presence of malicious code infections on a computer system.
But this need to be in control of the
file system comes at a cost.
Trying to install multiple malware detection products on a single computer system typically results in a deadly embrace, where both products fight for absolute control of the
file system.
This deadly embrace results in a malfunctioning computer as each malware detection product sees the other as an
adversary launching a malicious
attack designed to take control of the
file system.
This “one only” installation limitation puts the user at another
disadvantage in that the malware detection product currently installed may have limited knowledge of “new emerging viruses” and as a result is likely to report that a computer system is “clean,” when in fact it is infected with a malicious code infection.
Examining live running computer systems for malicious code infections incurs certain risks, one of which is that the
hacker has shielded his / her malicious code from discovery within the running
operating system environment.
Current malware vendor solutions do not recover deleted files for scanning purposes.
This limitation ignores the possibility that hackers, in compromising a computer system, have attempted to cover their tracks by deleting incriminating files.
In totality, no other malware vendor or
open source solution offers this combination of malware specific scanning and reporting options in a single
user interface.
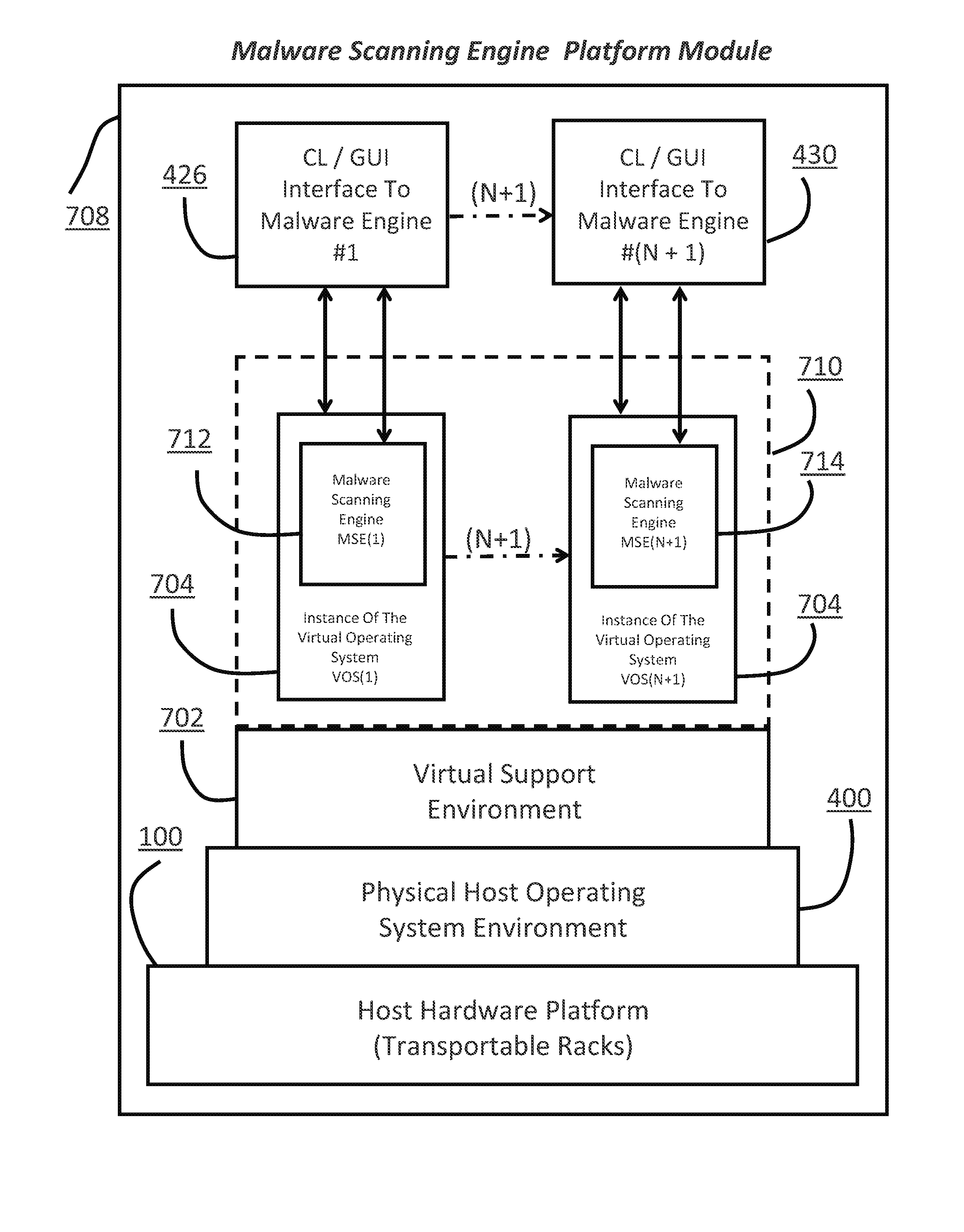
Current vendor solutions typically only permit one malware scanning engine to be installed on a single computer system.
Installing multiple malware engines on the same computer system is actively discouraged by both the prior art commercial and open-source vendors due to technical conflicts.
Having multiple malware scanning engines producing differently formatted updates and reports poses a significant logistics challenge.
These governing factors may prevent the organization from allowing data from computer systems suspected of being compromised from leaving their physical facility or control.
 Login to View More
Login to View More  Login to View More
Login to View More