Patents
Literature
70 results about "Malware analysis" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
Malware analysis is the study or process of determining the functionality, origin and potential impact of a given malware sample such as a virus, worm, trojan horse, rootkit, or backdoor. Malware or malicious software is any computer software intended to harm the host operating system or to steal sensitive data from users, organizations or companies. Malware may include software that gathers user information without permission.
Malware Target Recognition
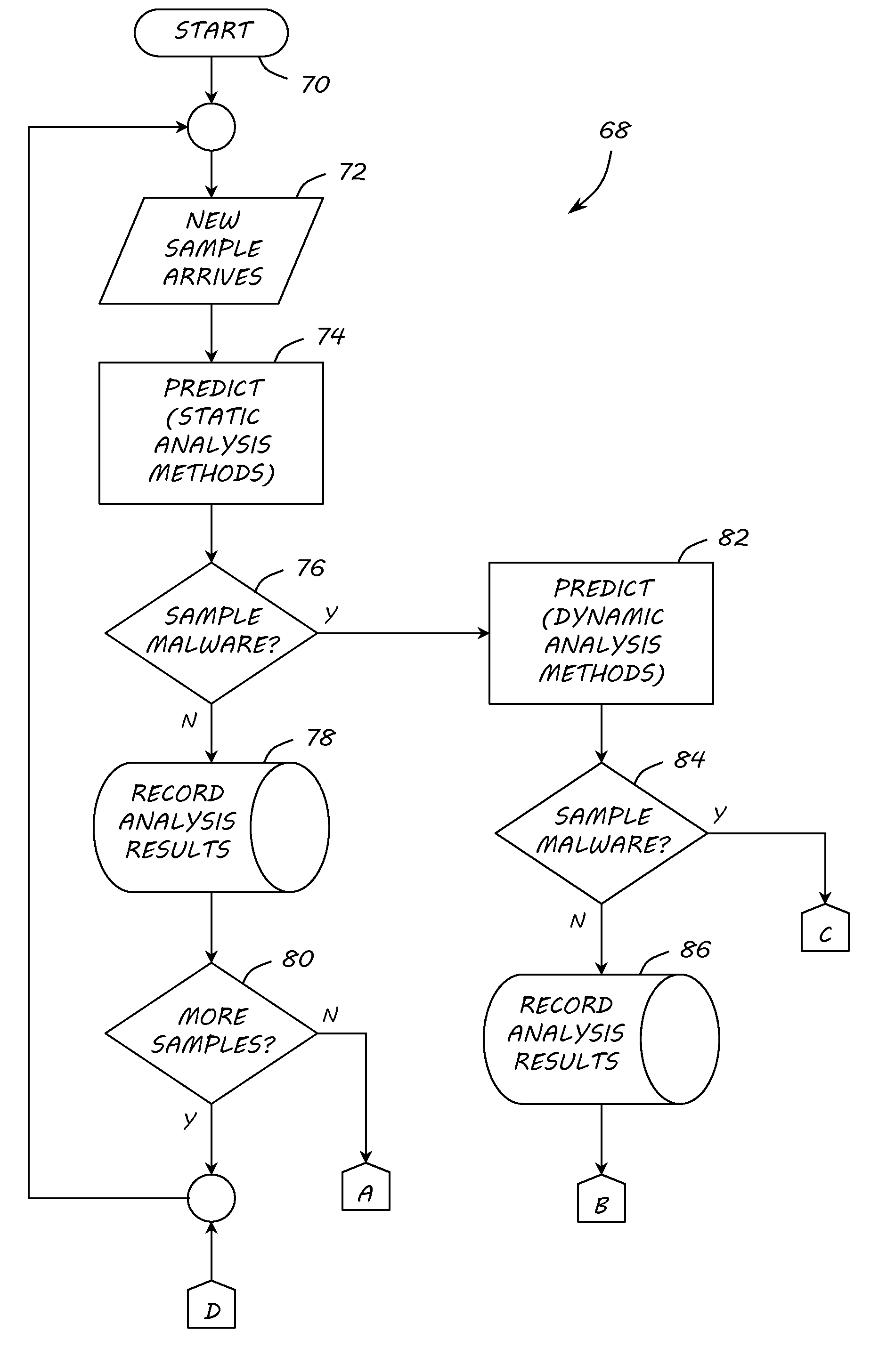
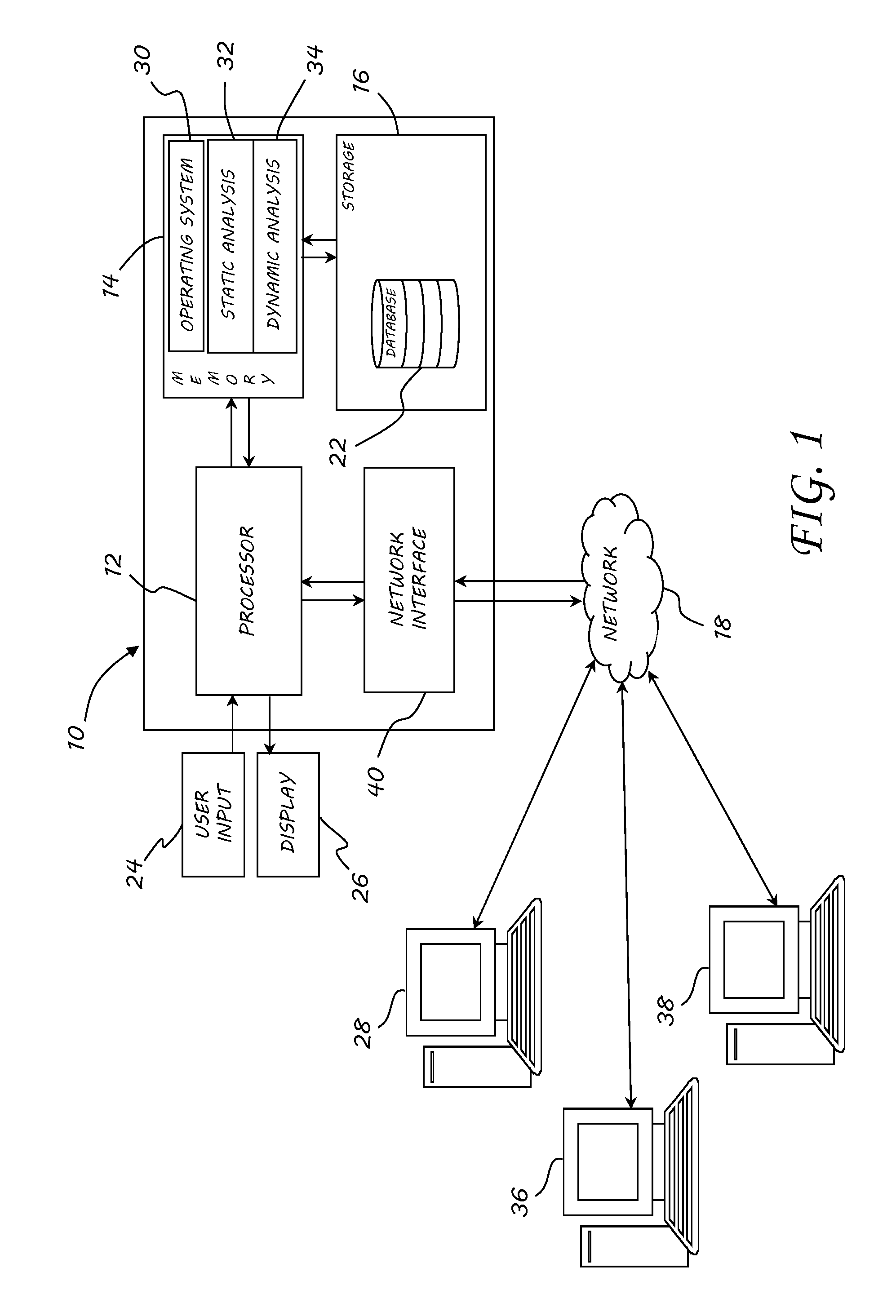
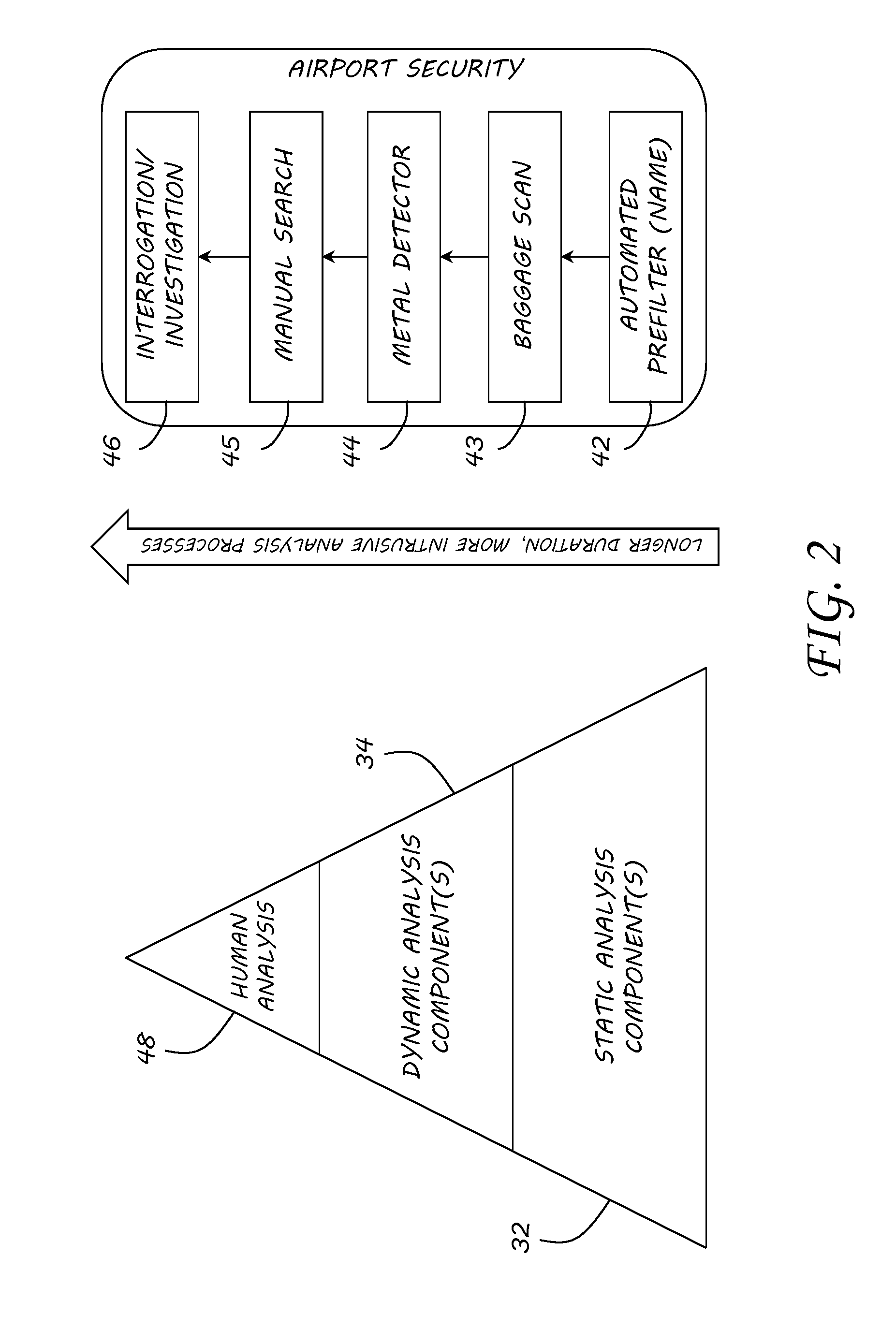
InactiveUS20120260342A1Memory loss protectionError detection/correctionMalware analysisAnalysis method
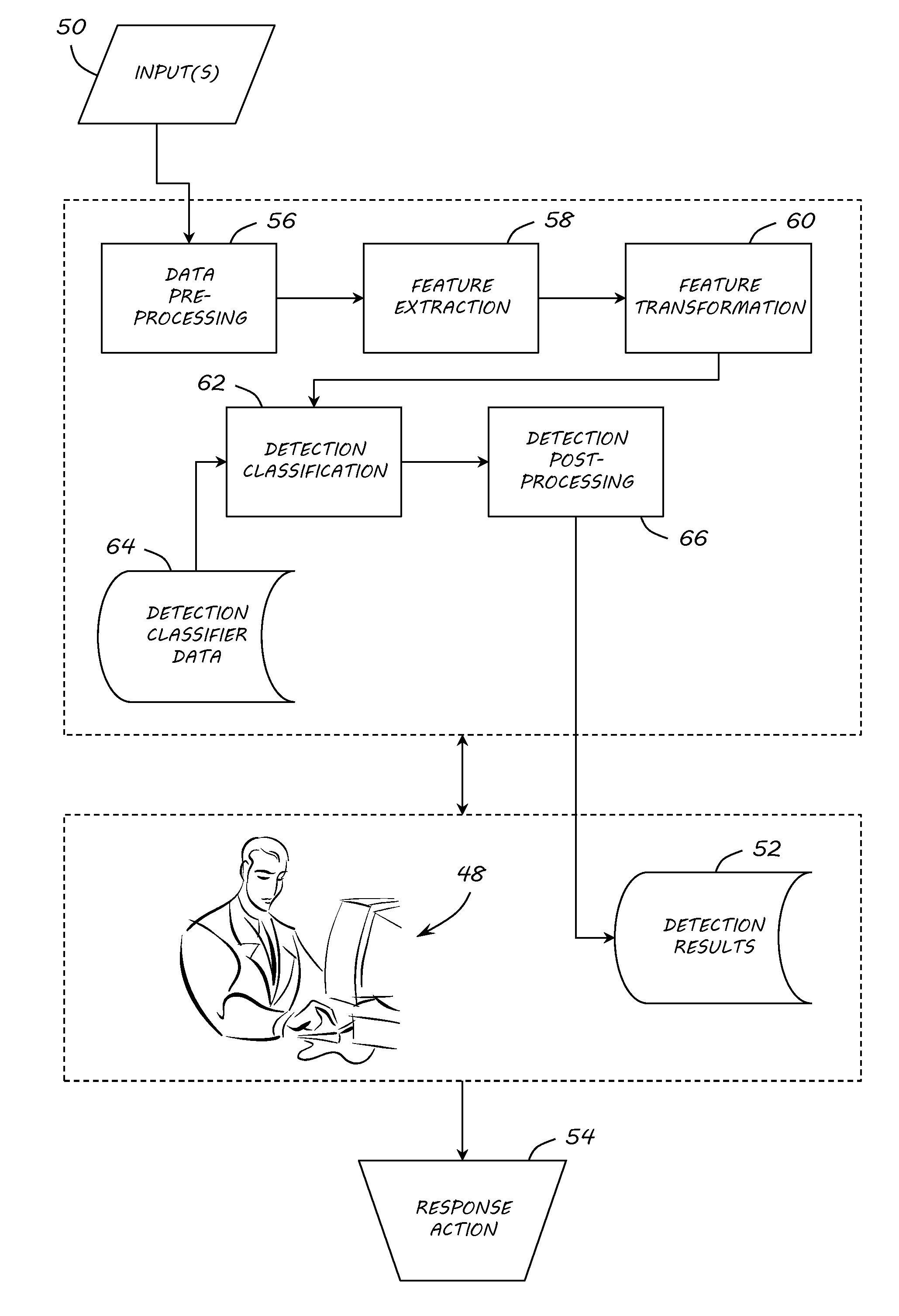
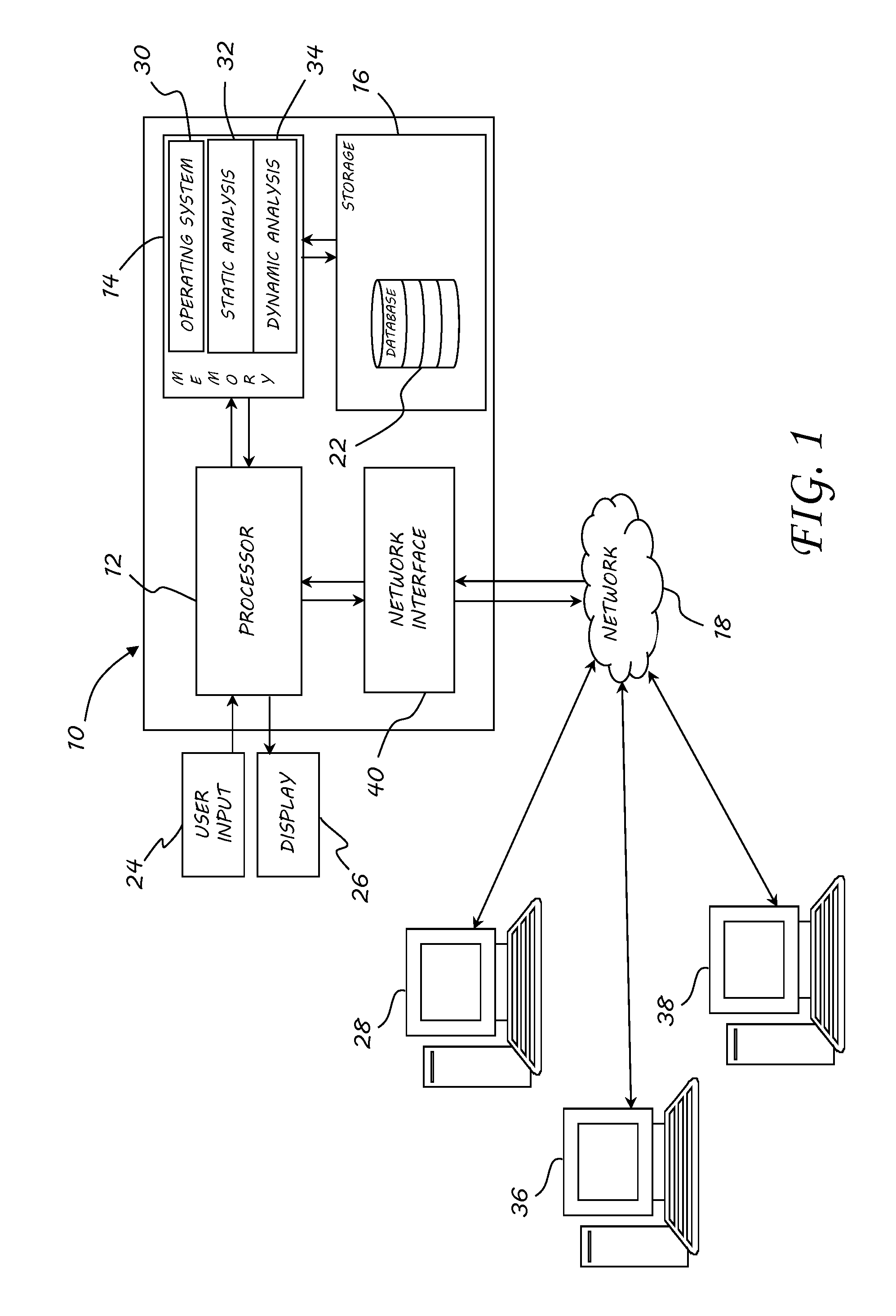
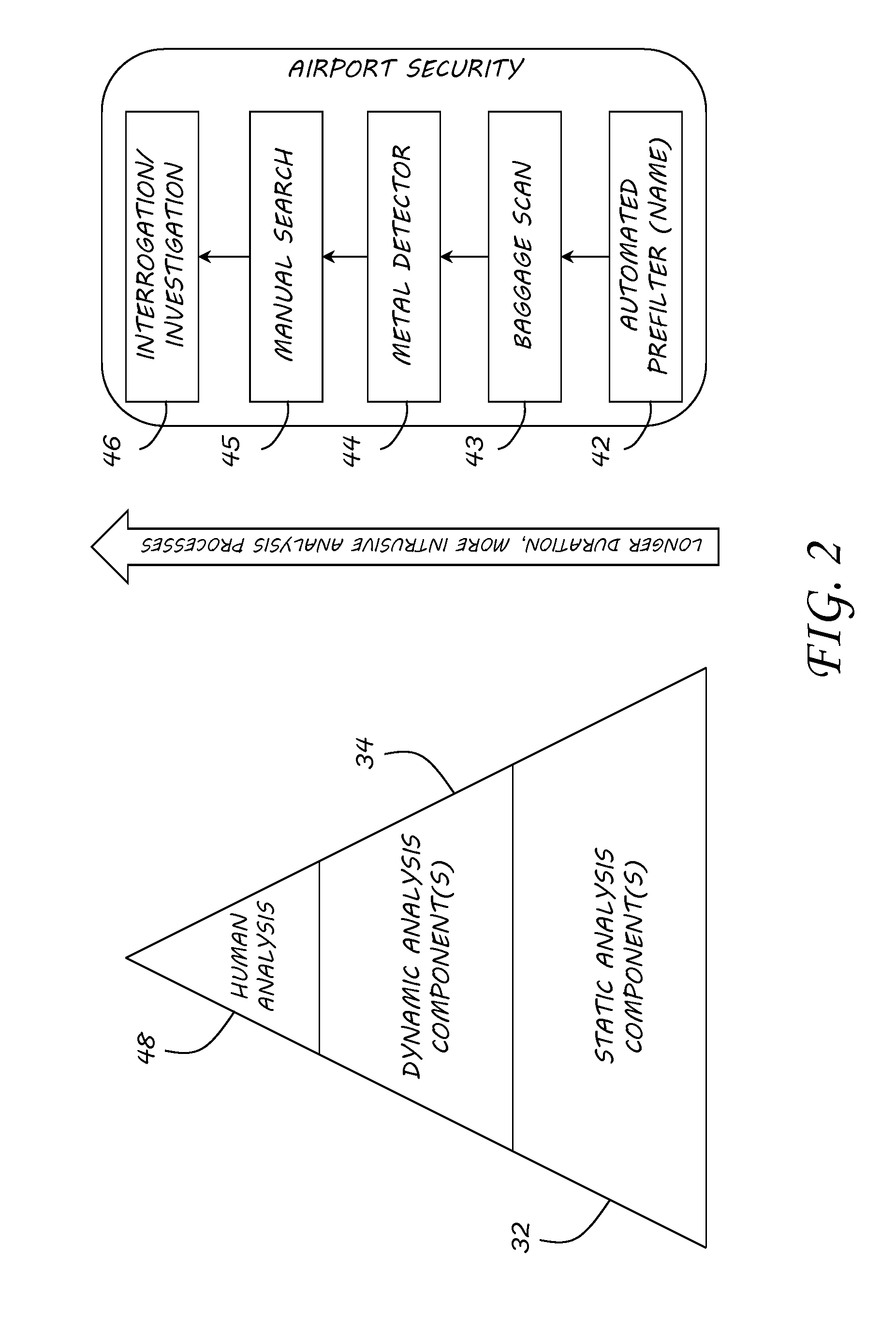
A method, apparatus and program product are provided to recognize malware in a computing environment having at least one computer. A sample is received. An automatic determination is made by the at least one computer to determine if the sample is malware using static analysis methods. If the static analysis methods determine the sample is malware, dynamic analysis methods are used by the at least one computer to automatically determine if the sample is malware. If the dynamic analysis methods determine the sample is malware, the sample is presented to a malware analyst to adjudicate the automatic determinations of the static and dynamic analyses. If the adjudication determines the sample is malware, a response action is initiated to recover from or mitigate a threat of the sample.
Owner:THE UNITED STATES OF AMERICA AS REPRESETNED BY THE SEC OF THE AIR FORCE
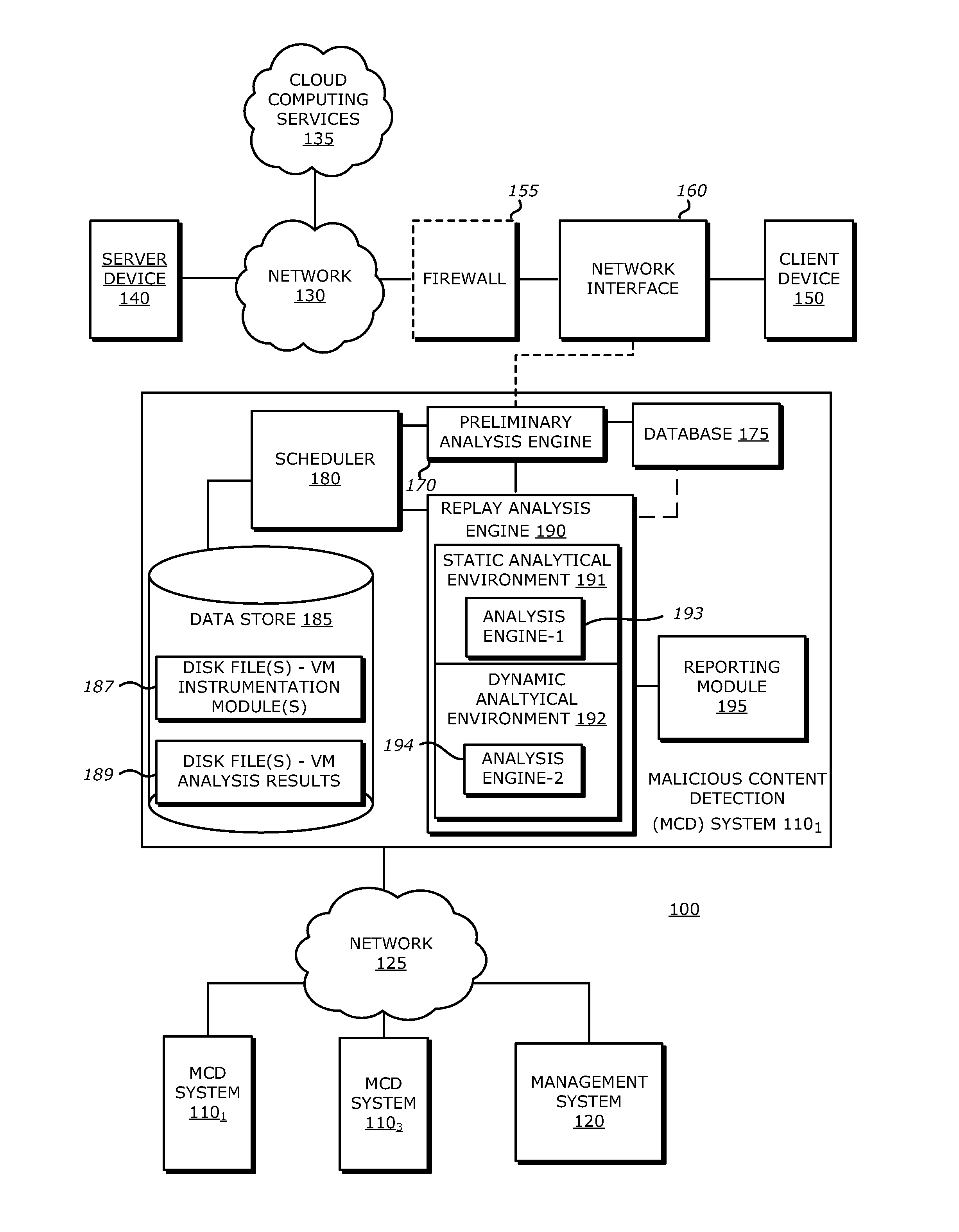
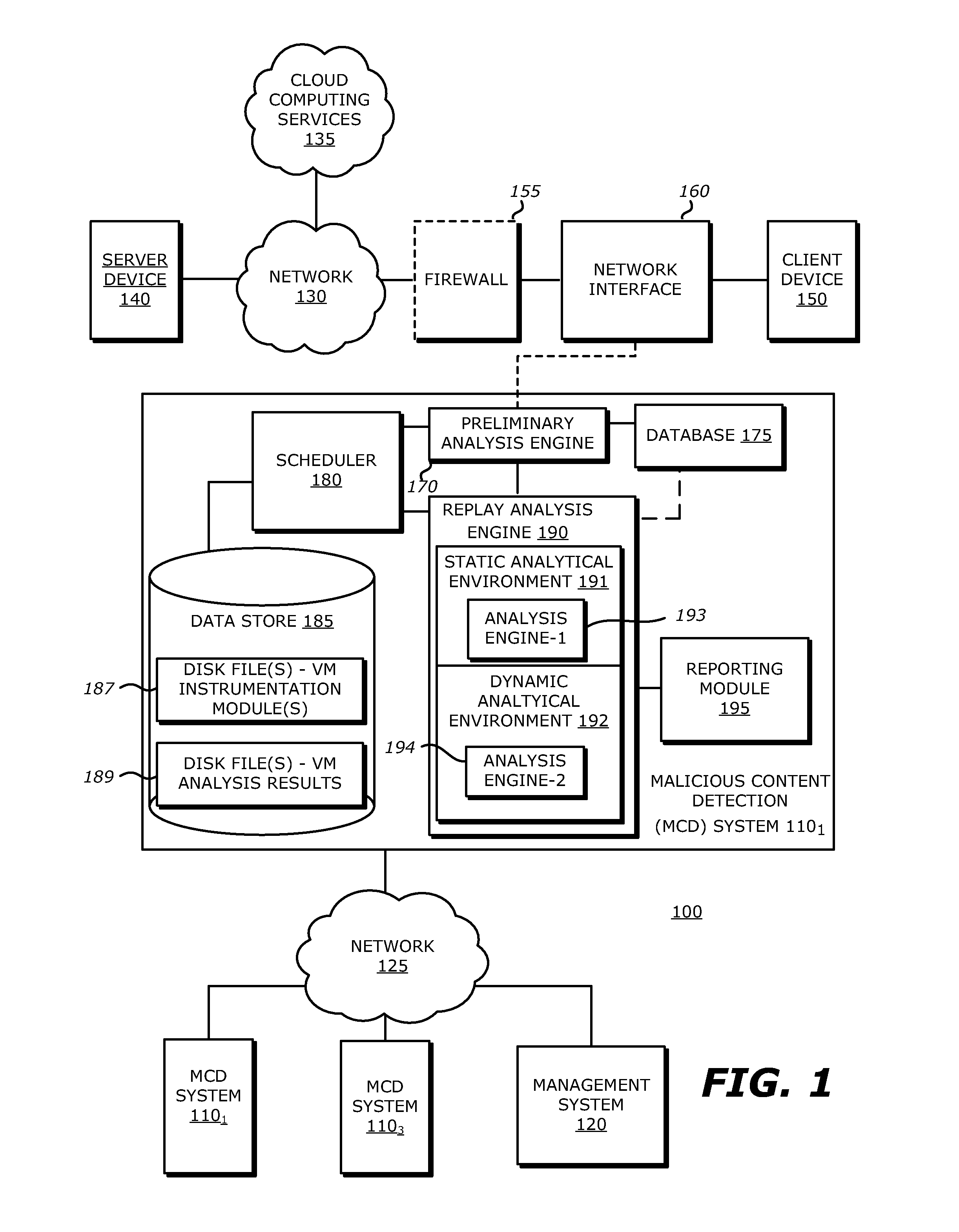
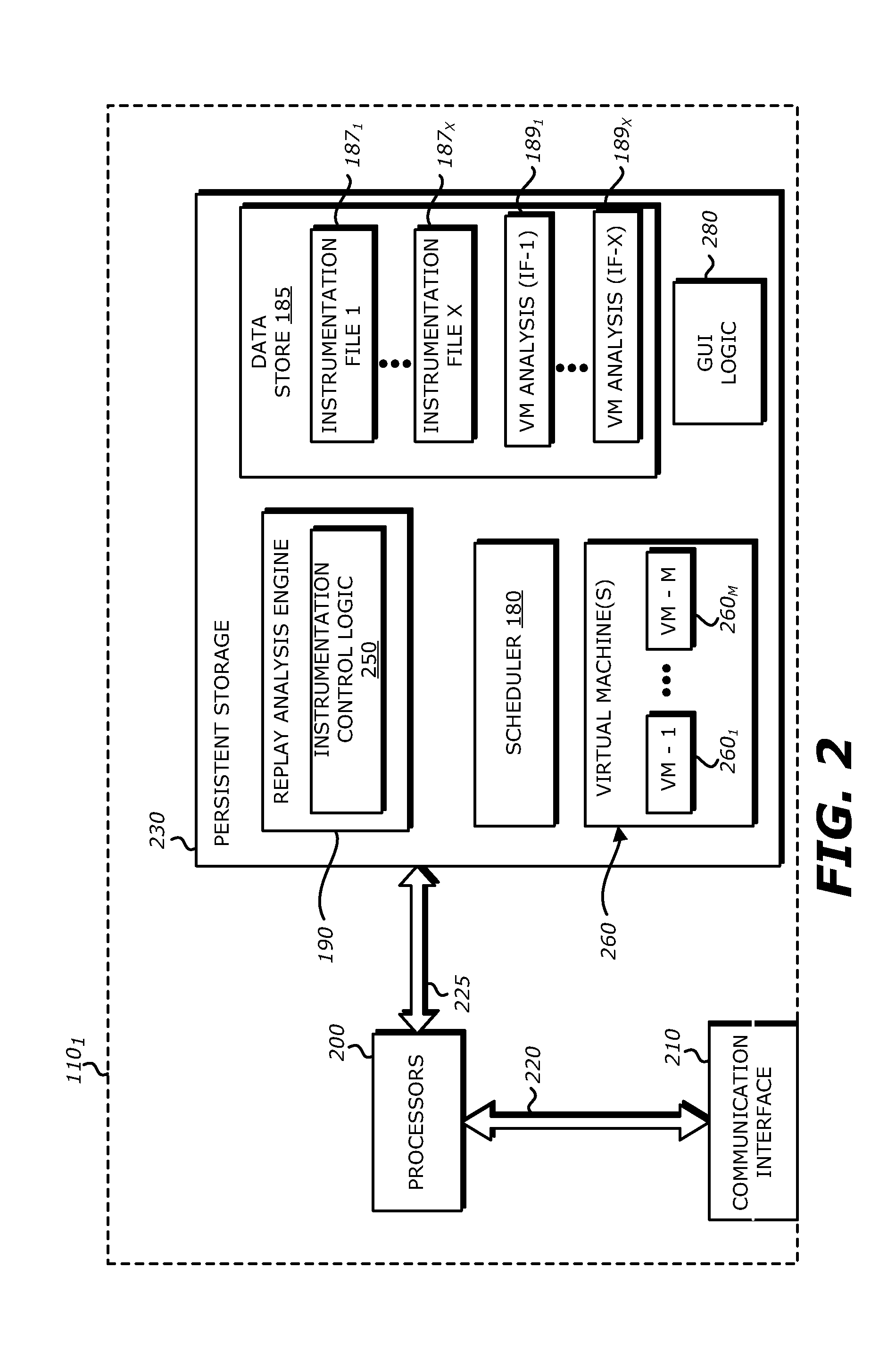
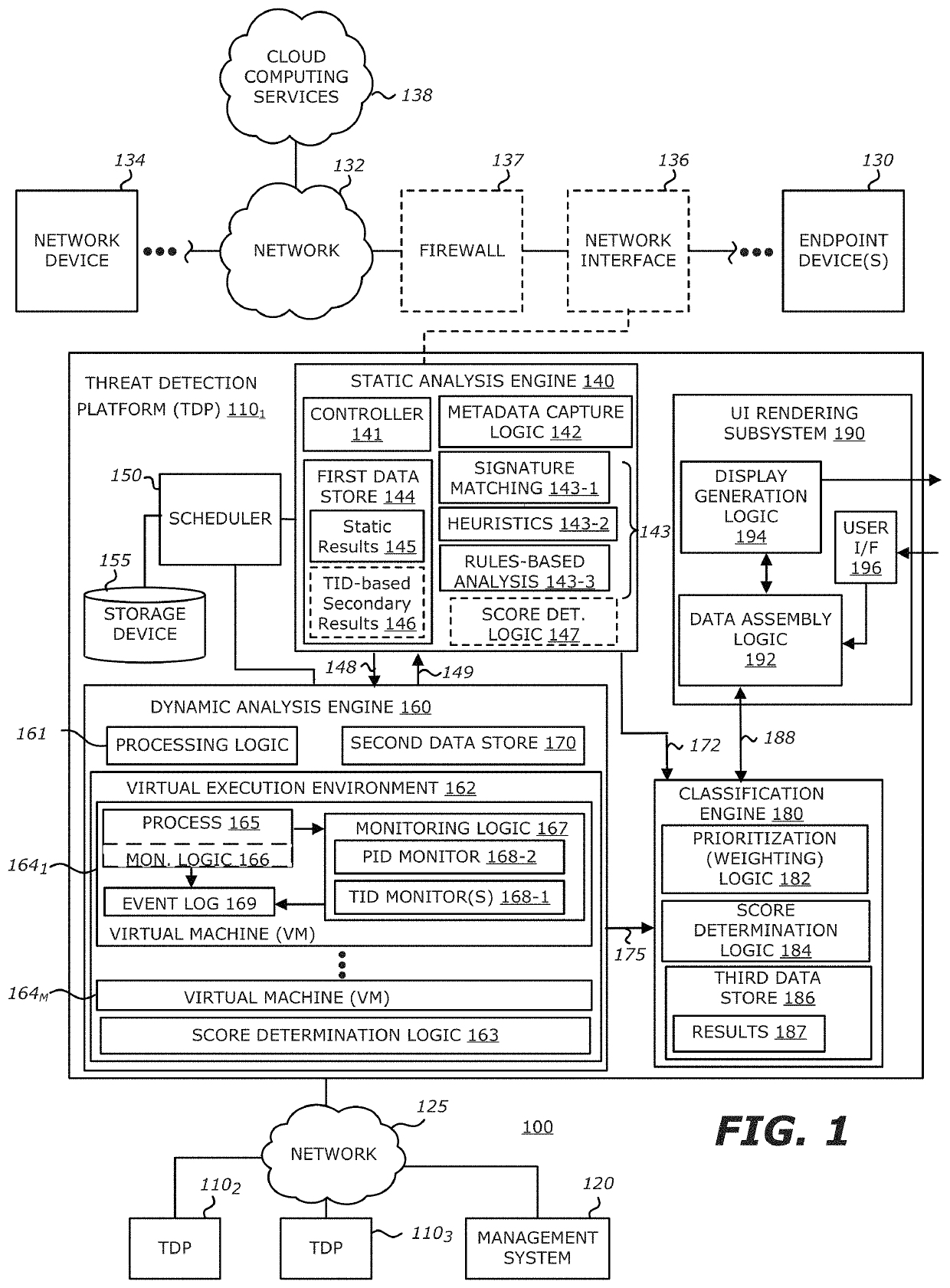
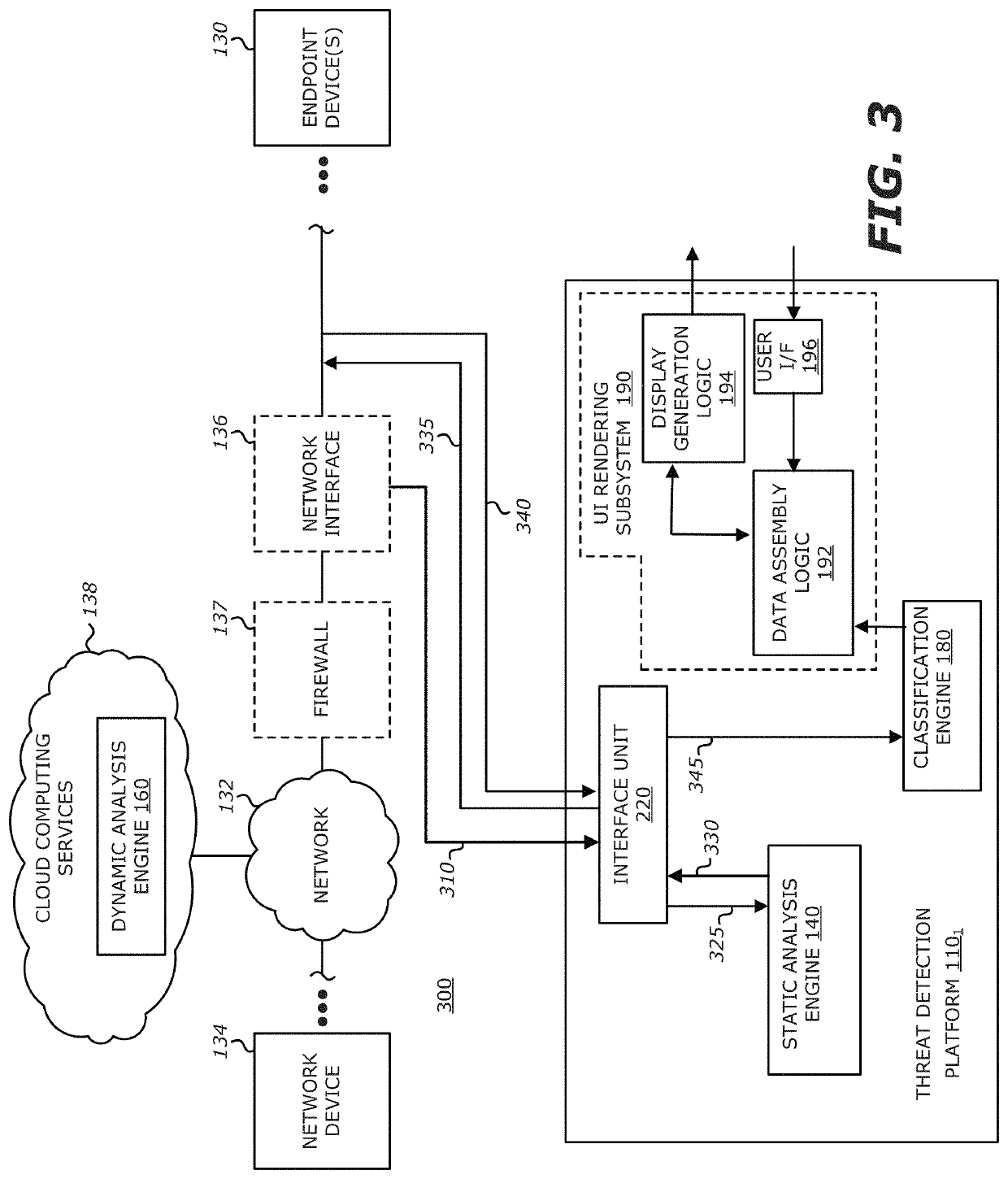
System, Apparatus and Method for Using Malware Analysis Results to Drive Adaptive Instrumentation of Virtual Machines to Improve Exploit Detection
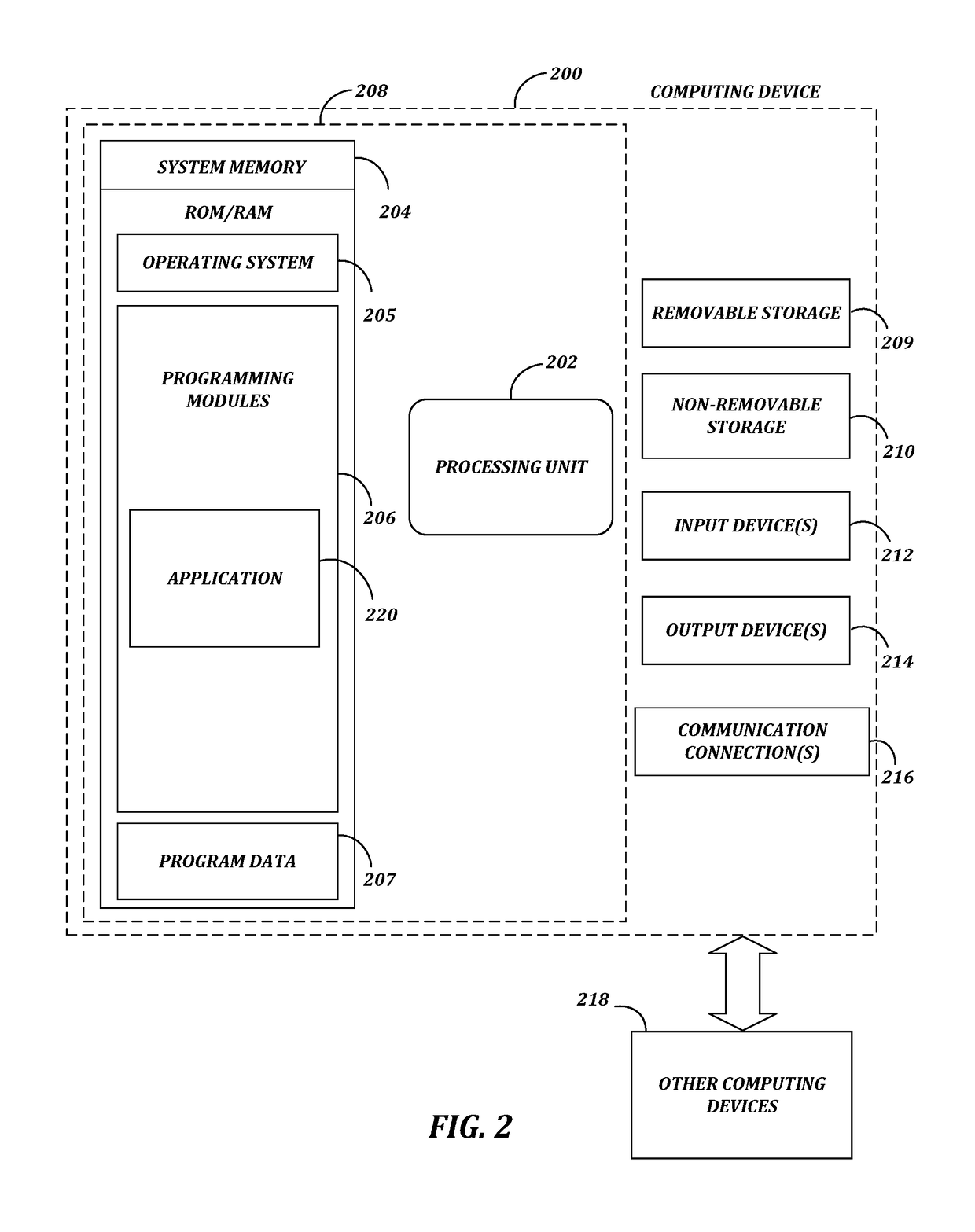
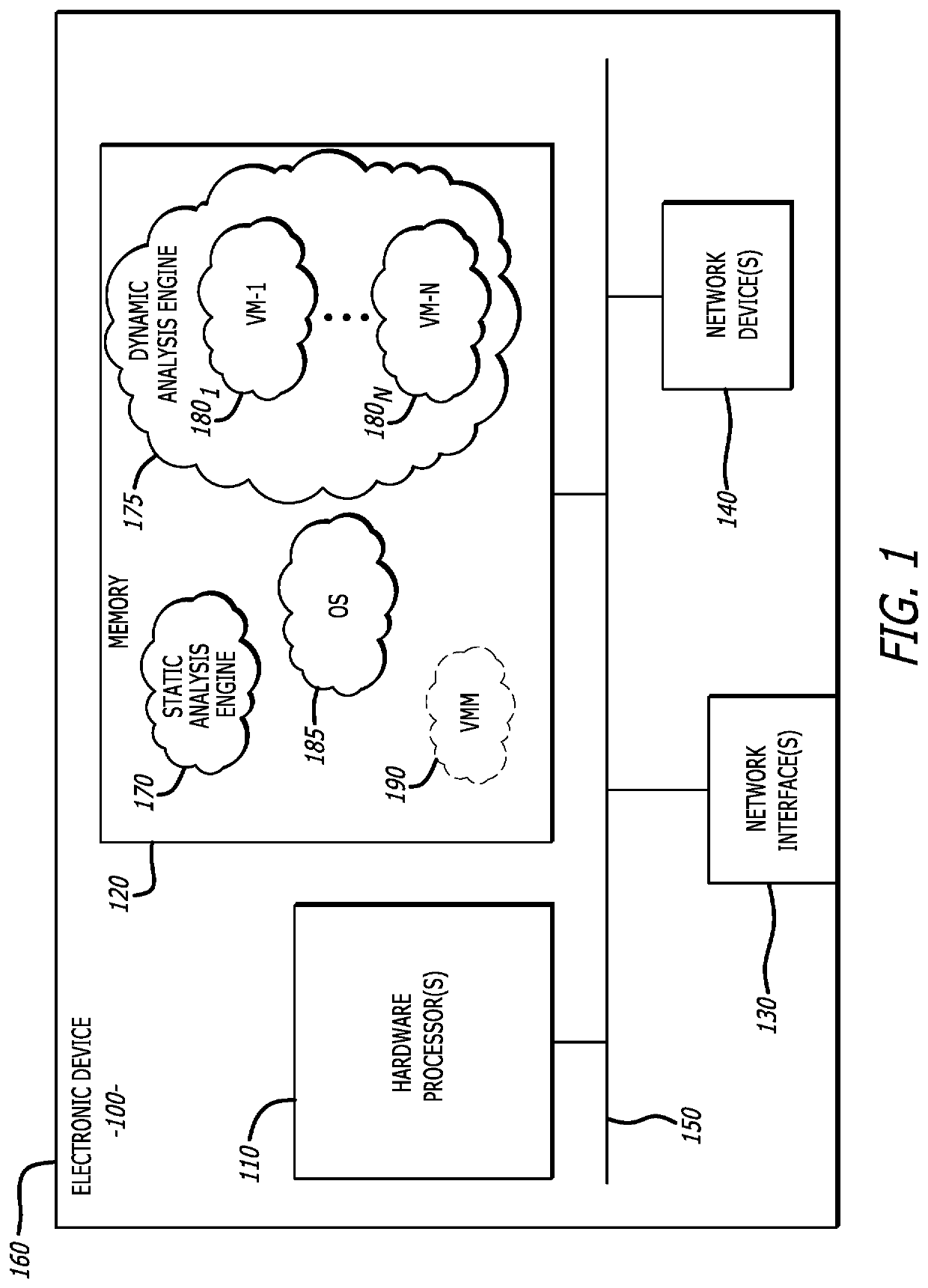
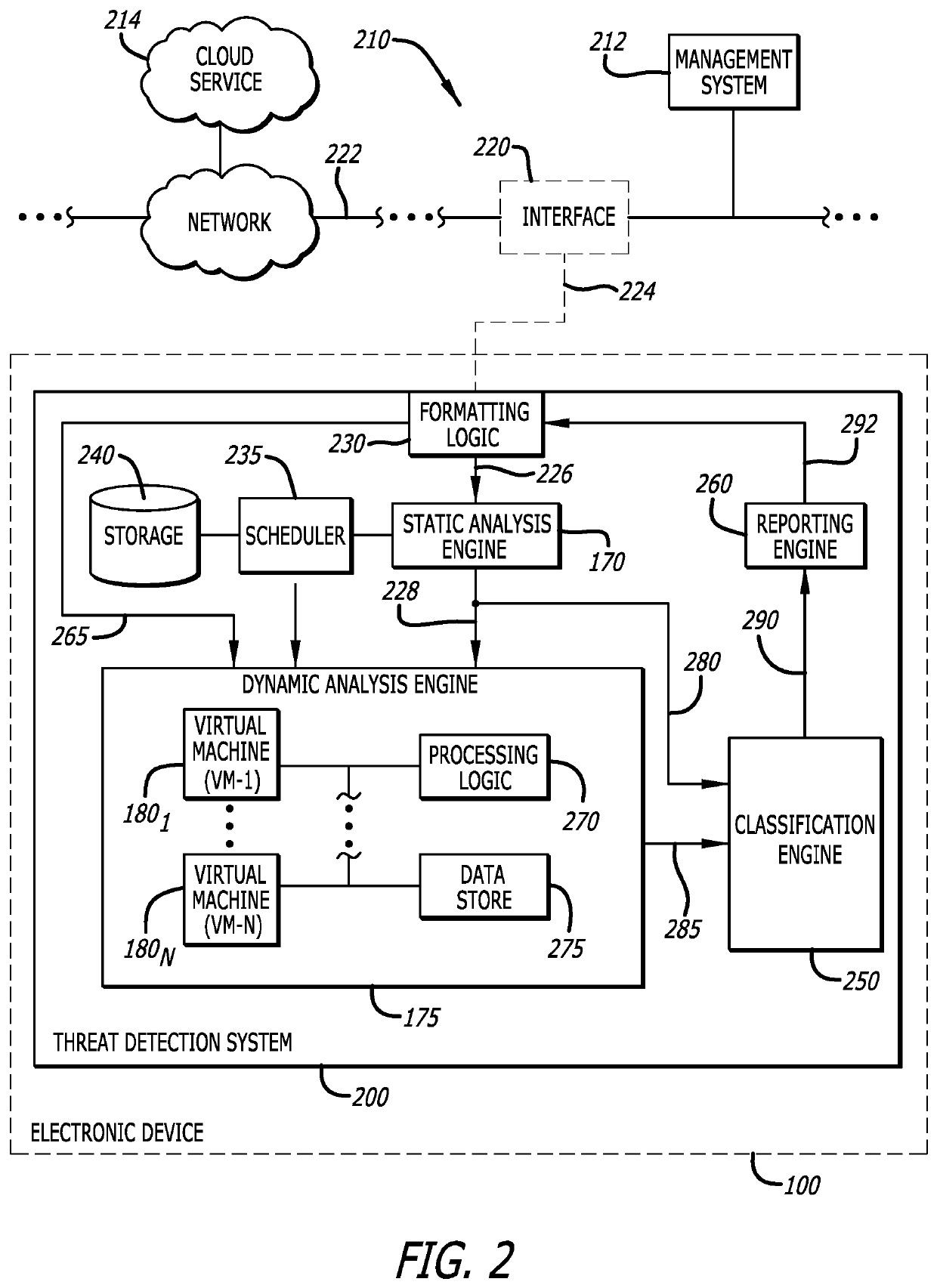
According to one embodiment, an electronic device comprises a memory to store information and a processor. The processor is adapted to receive information associated with content such as network traffic, to process the stored information and to conduct operations on the content. These operations may comprise determining, by a virtual machine processed by the processor, an occurrence of an event during malware analysis of an object associated with the content, and dynamically altering a virtual machine instrumentation of the virtual machine based on information associated with the event.
Owner:FIREEYE SECURITY HLDG US LLC
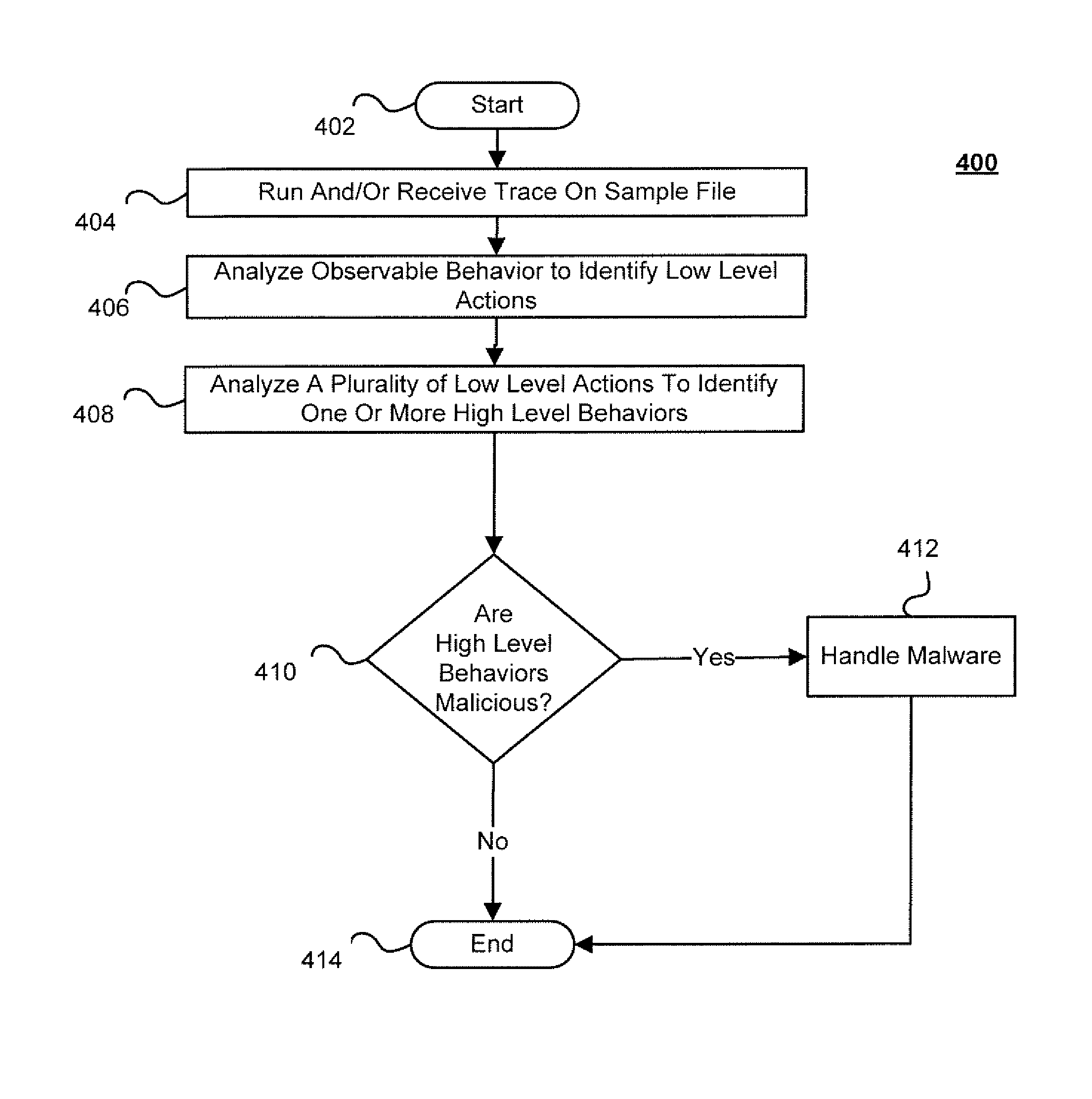
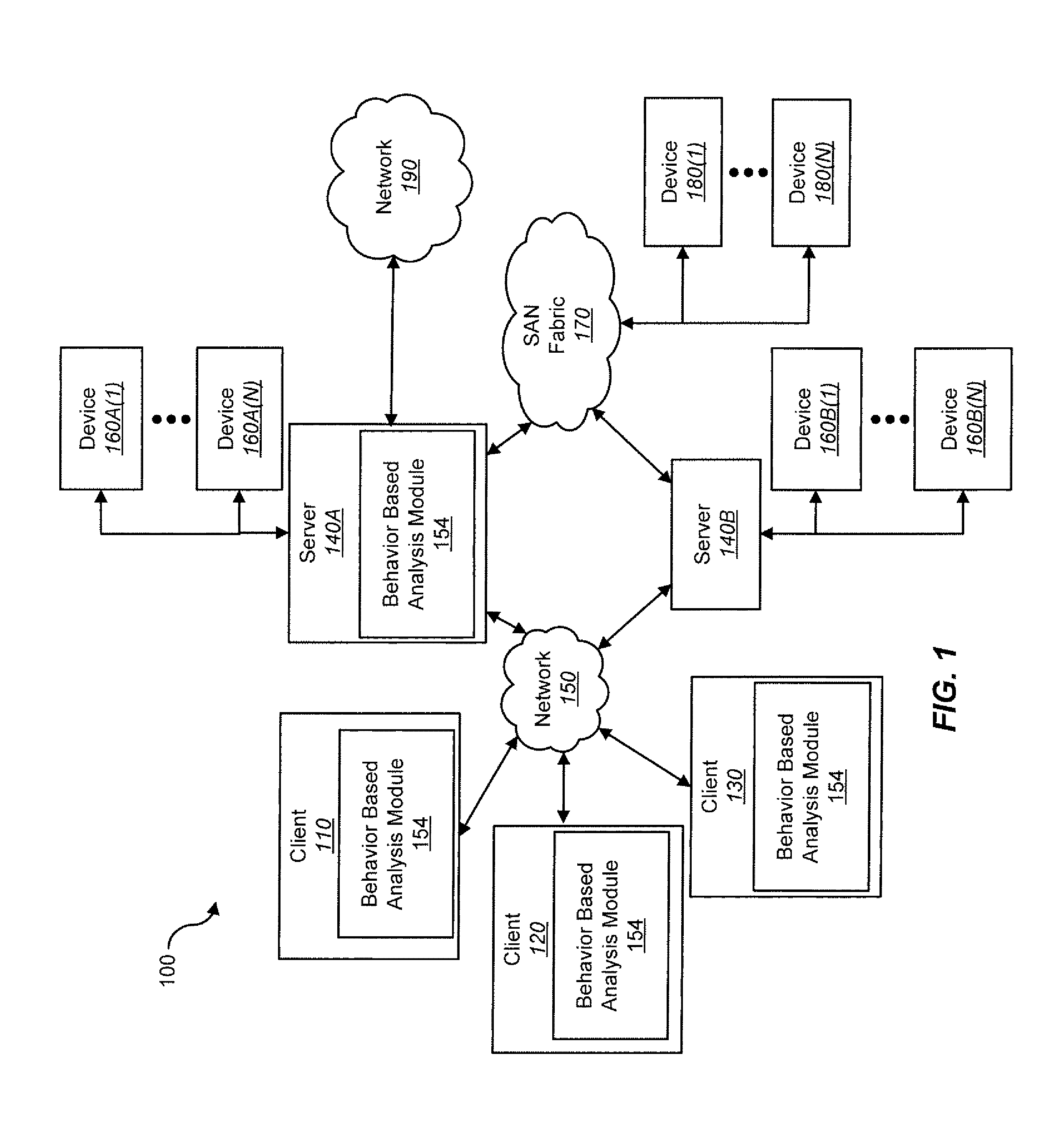
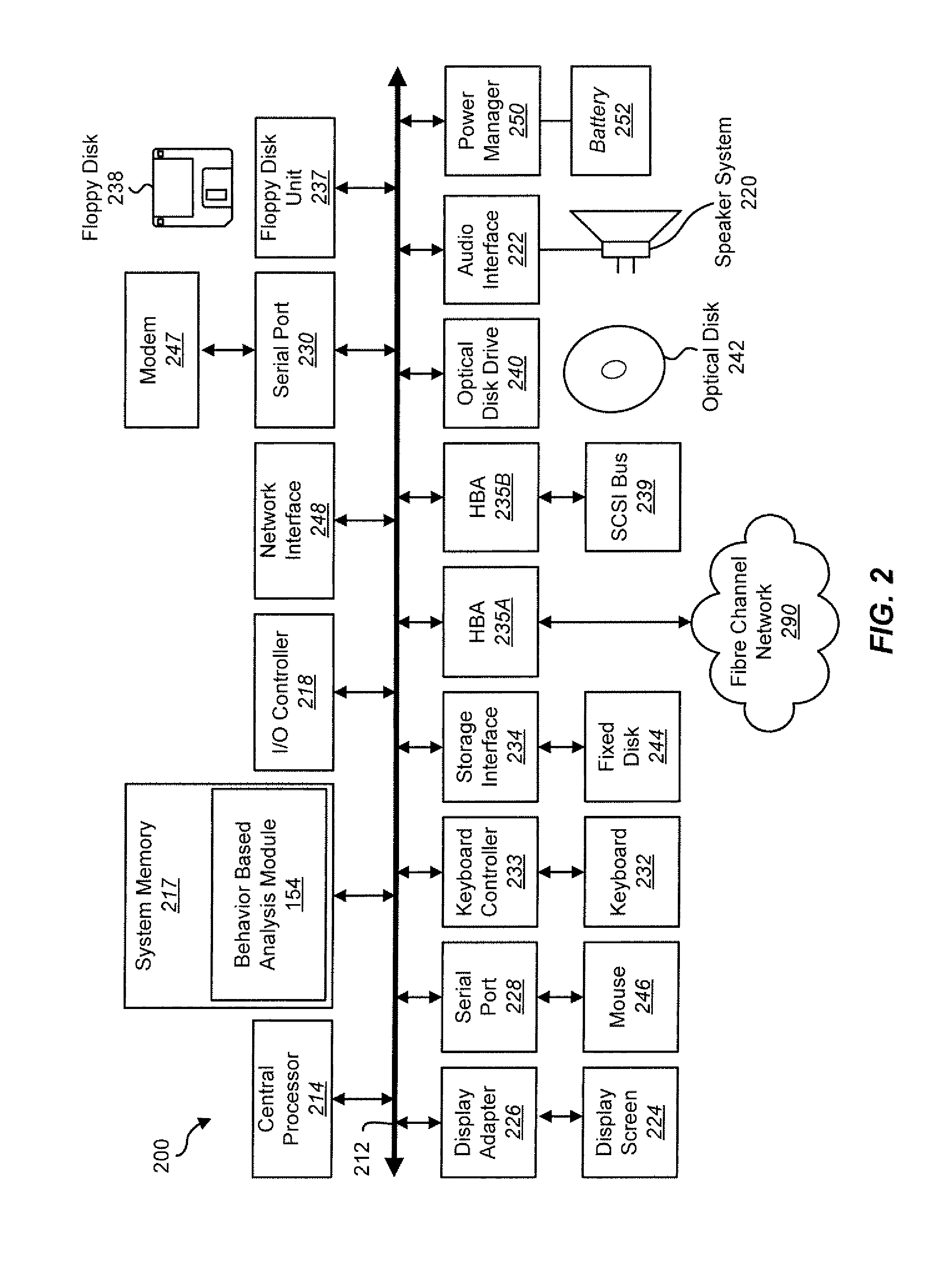
Techniques for behavior based malware analysis
ActiveUS8555385B1Avoid associationMemory loss protectionUnauthorized memory use protectionMalware analysisComputer science
Techniques for behavior based malware analysis are disclosed. In one particular exemplary embodiment, the techniques may be realized as a method for behavior based analysis comprising receiving trace data, analyzing, using at least one computer processor, observable events to identify low level actions, analyzing a plurality of low level actions to identify at least one high level behavior, and providing an output of the at least one high level behavior.
Owner:CA TECH INC
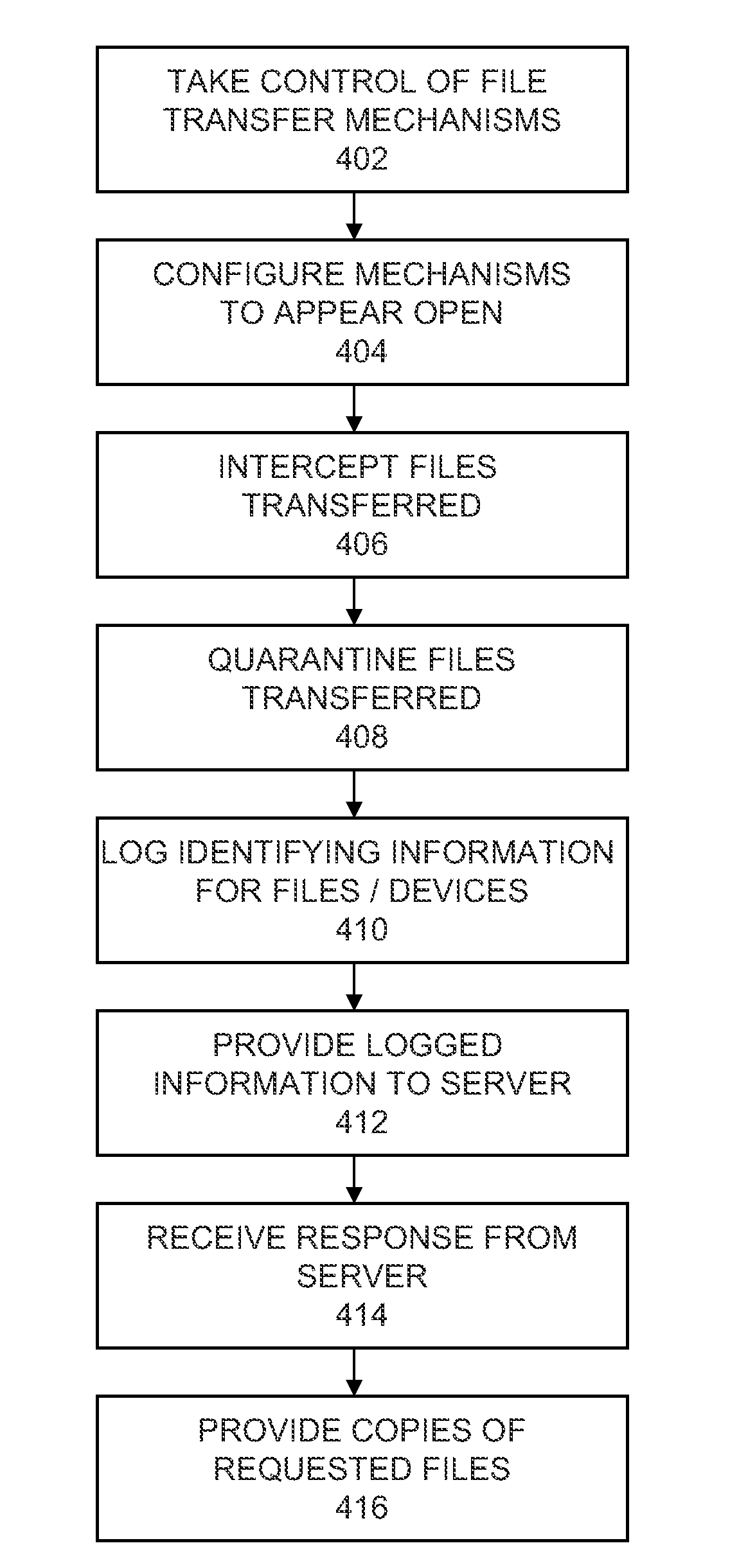
Short-range mobile honeypot for sampling and tracking threats
InactiveUS20130091570A1Memory loss protectionError detection/correctionMalware analysisMobile device
Owner:REEFEDGE
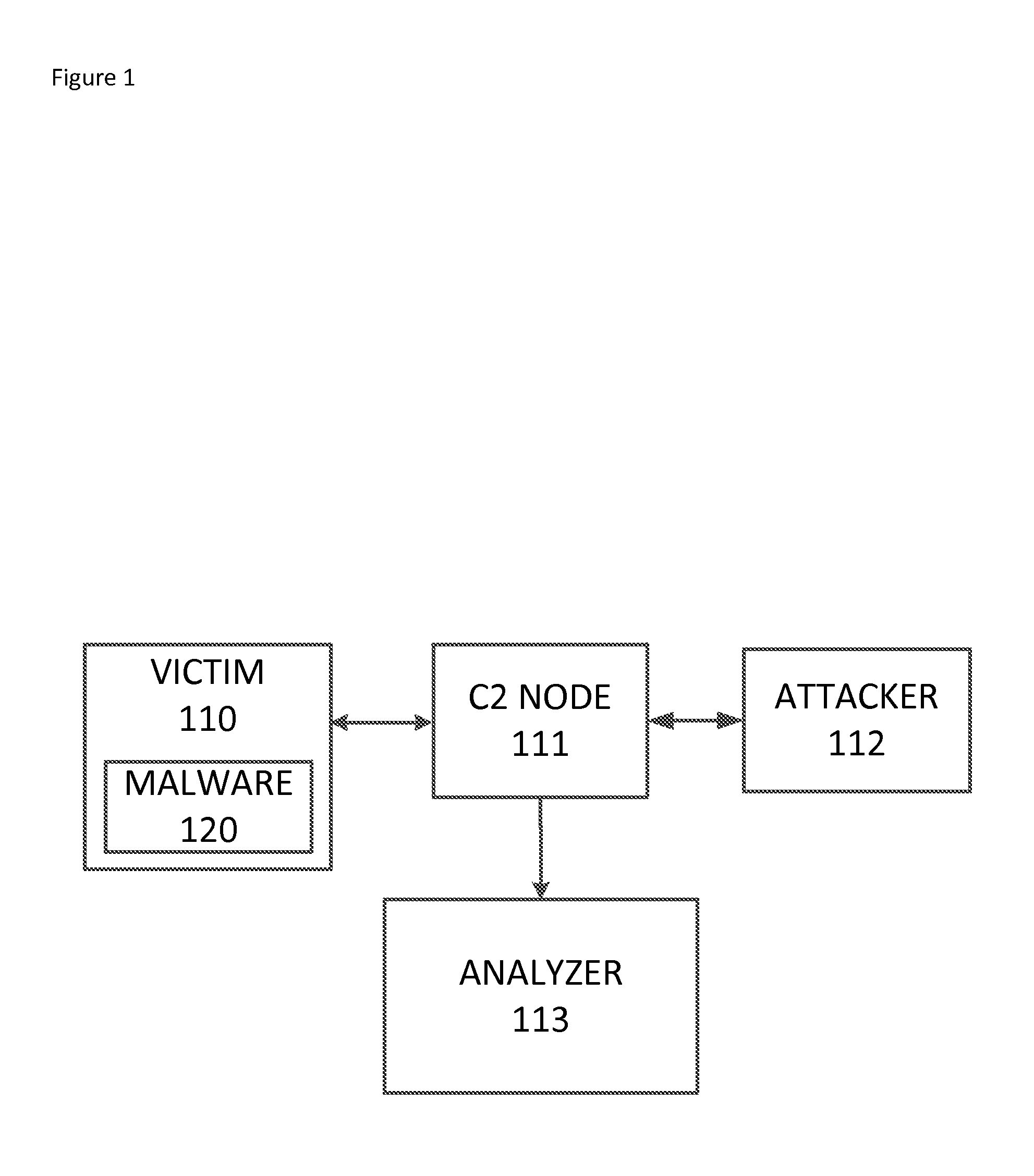
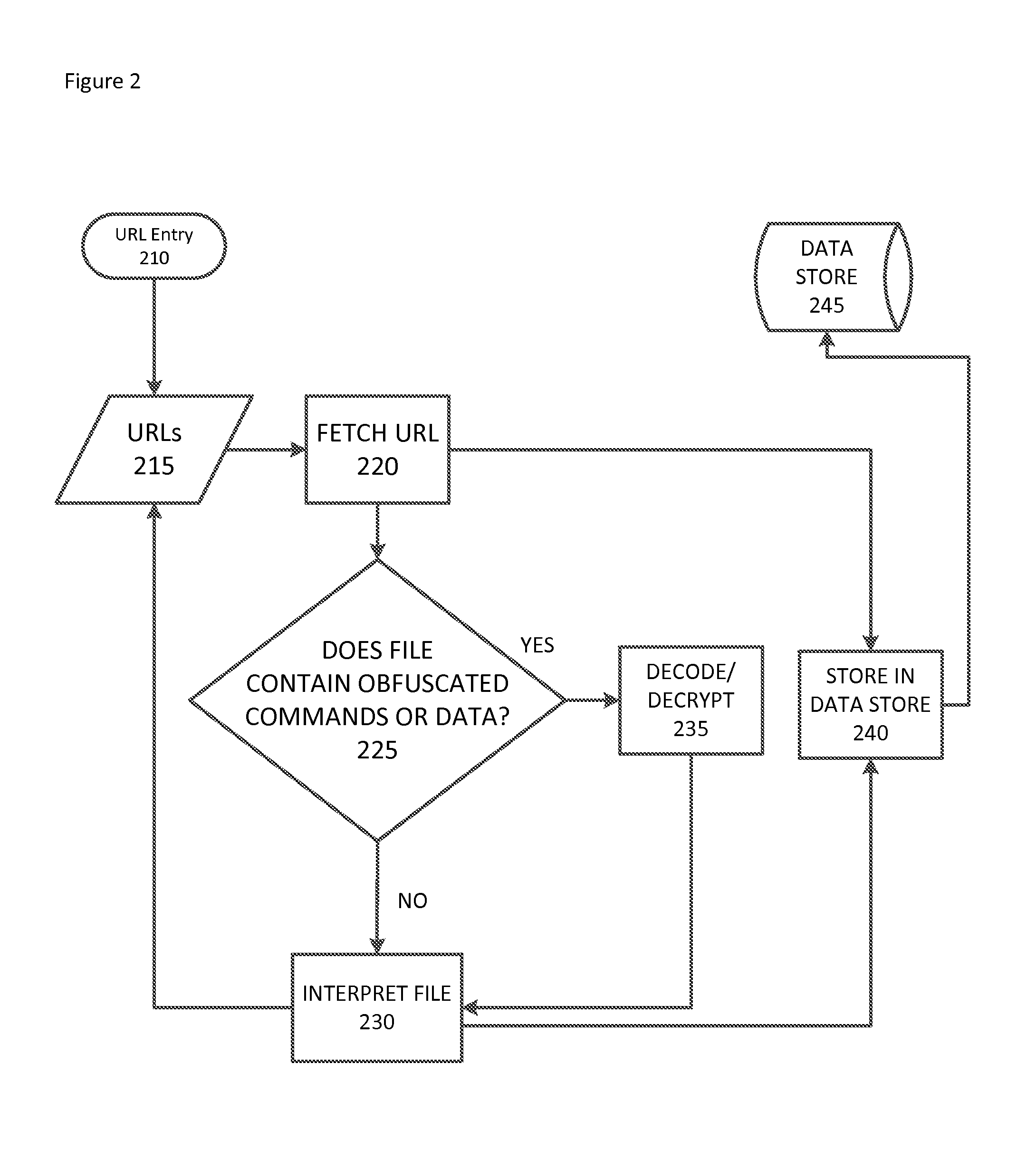
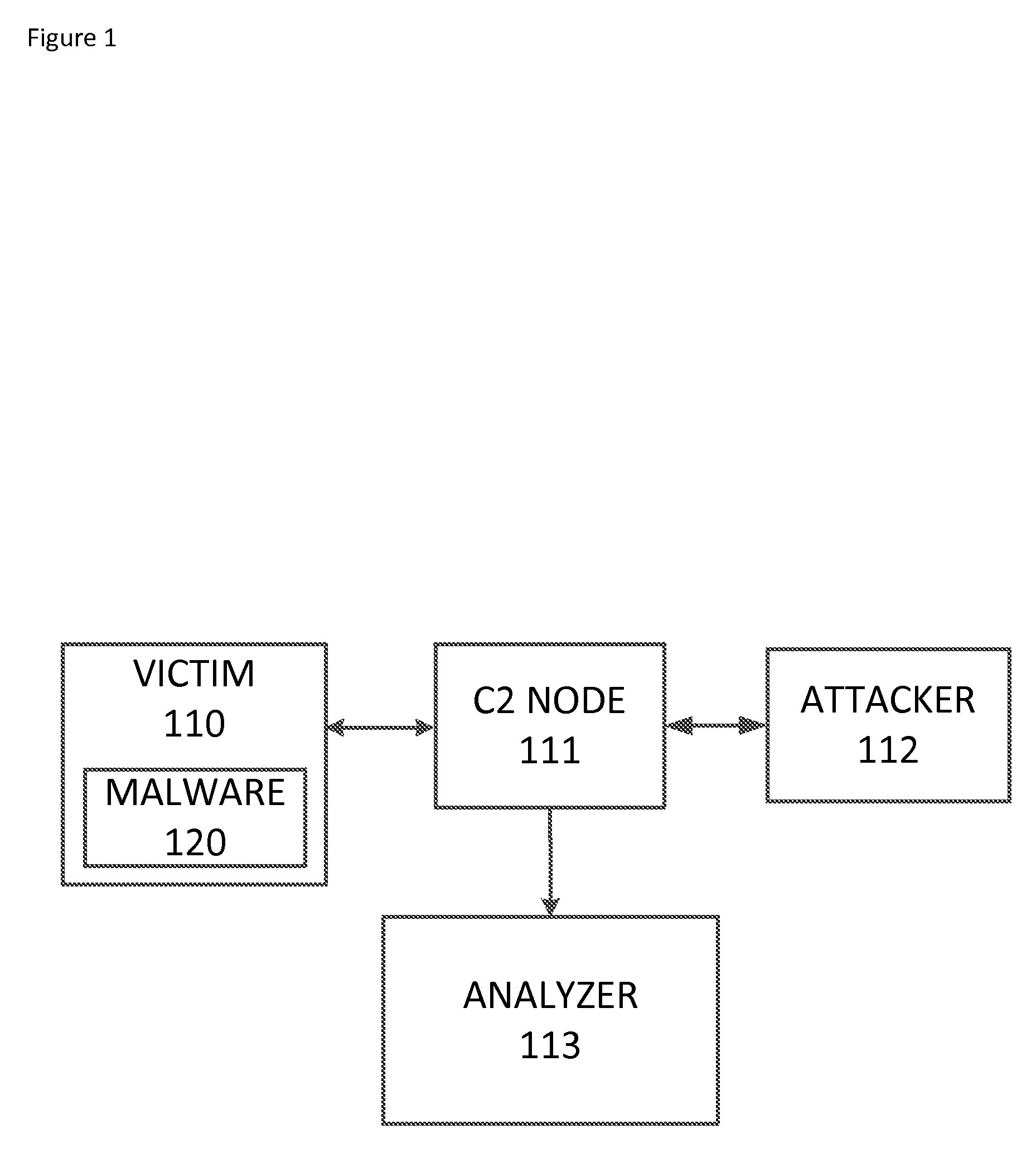
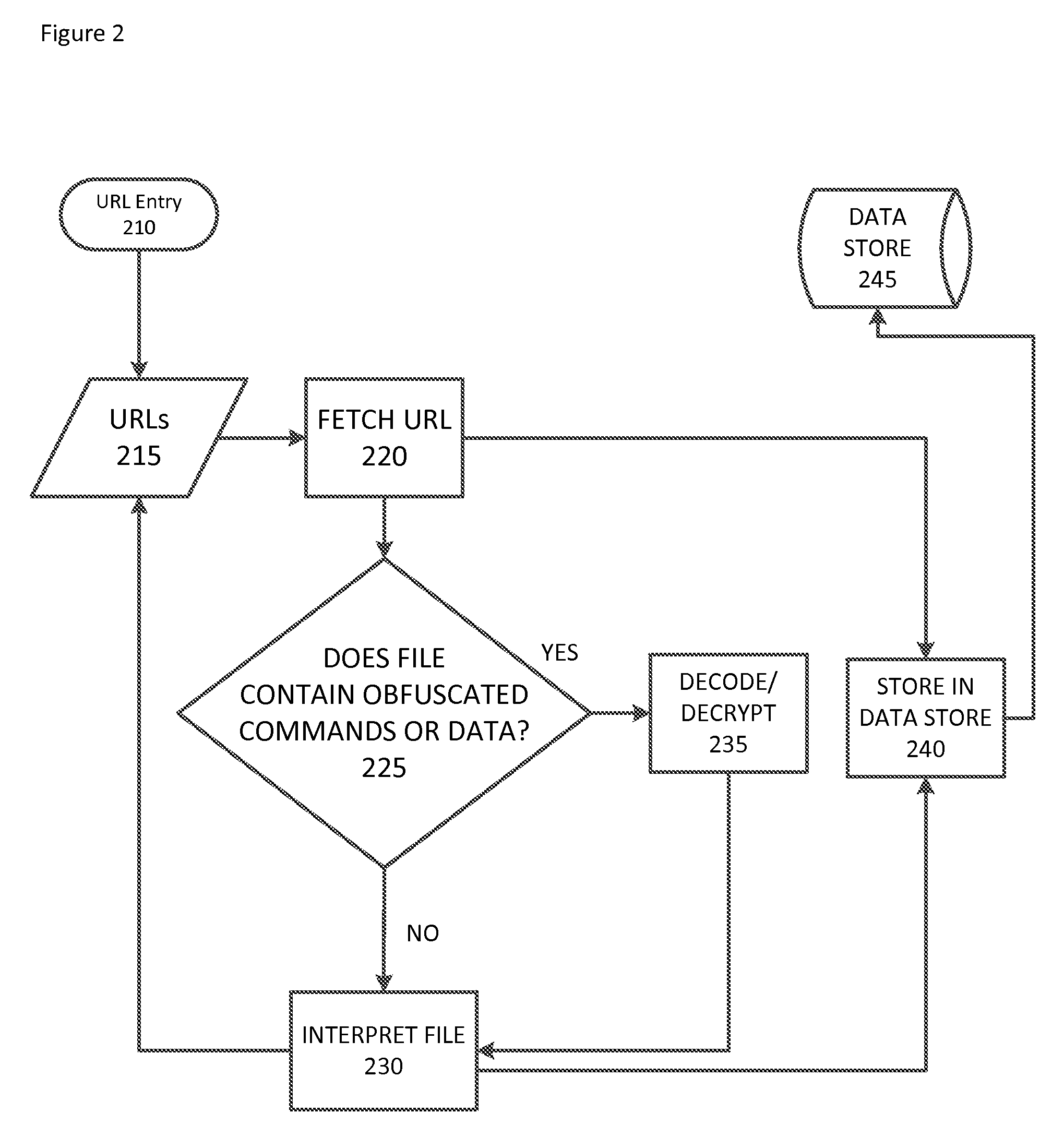
Systems and methods for automated malware artifact retrieval and analysis
An automated malware analysis method is disclosed which can perform receiving a first universal resource locator identifying a first intermediate network node, accessing the first intermediate network node to retrieve a first malware artifact file, storing the malware artifact file in a data storage device, analyzing the malware artifact file to identify a second universal resource locator within the malware artifact file, and accessing a second intermediate network node to retrieve a second malware artifact file.
Owner:CYBER ENG SERVICES
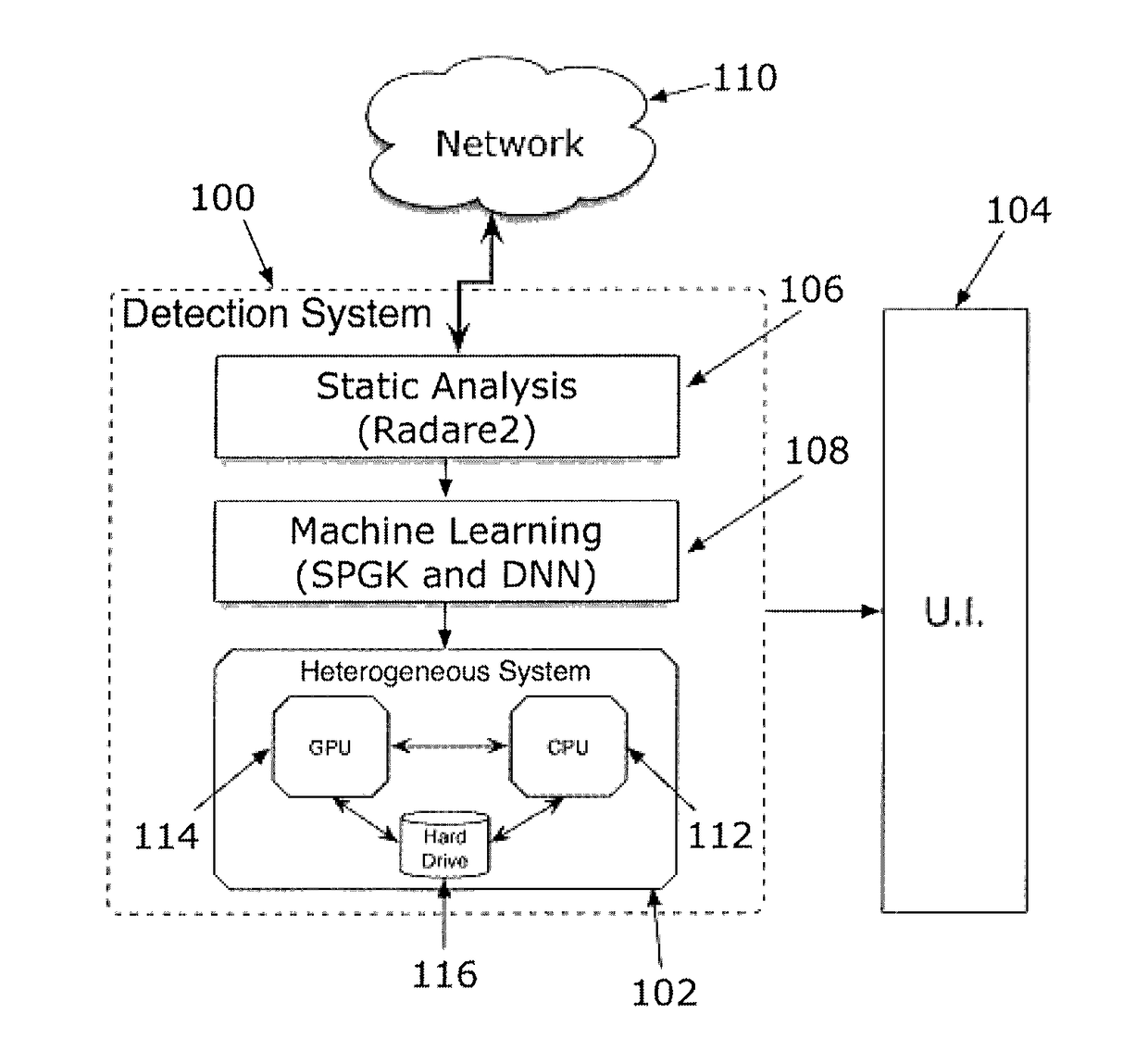
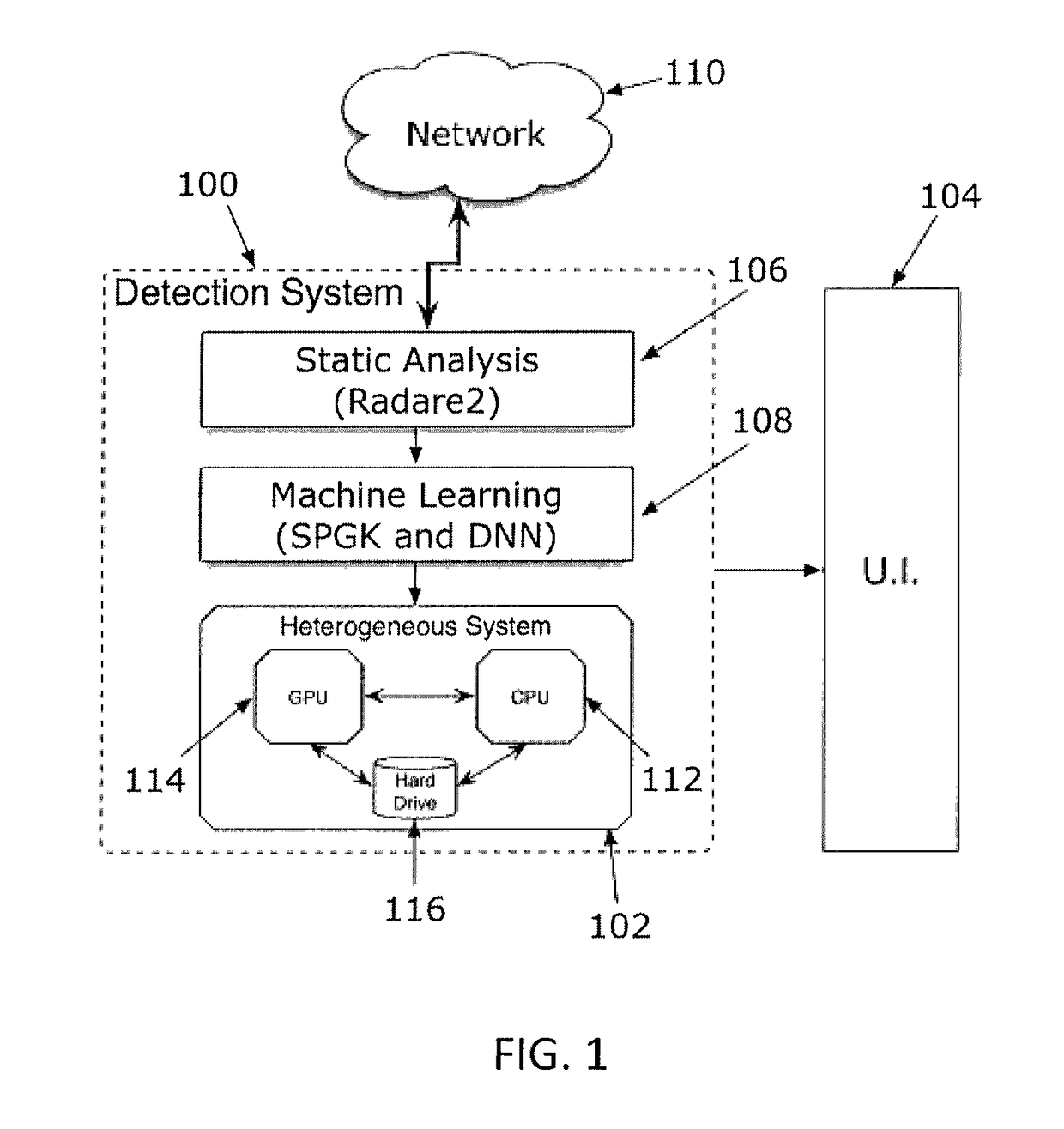
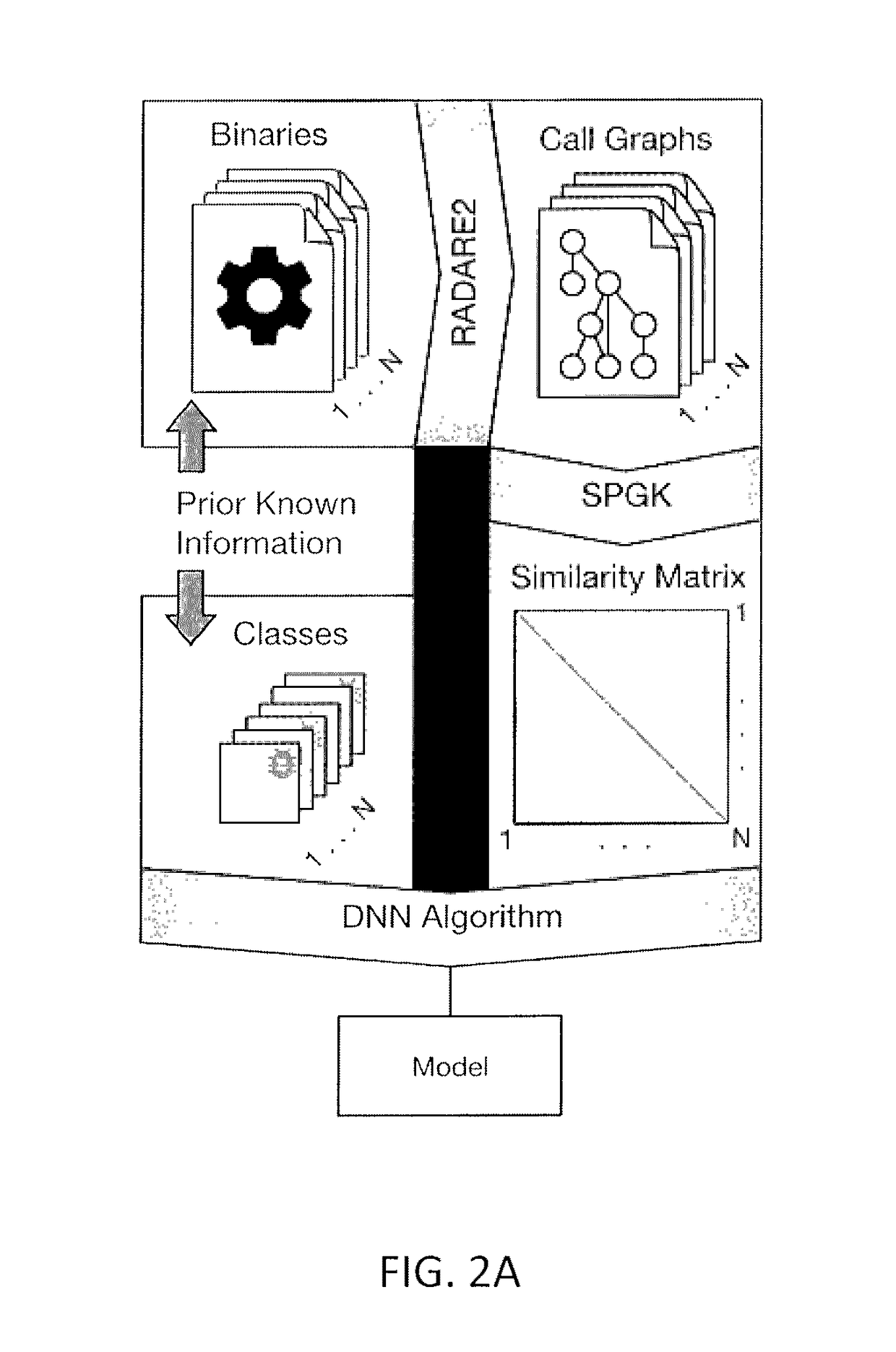
Malware analysis and detection using graph-based characterization and machine learning
Malware detection methods systems, and apparatus are described. Malware may be detected by obtaining a plurality of malware binary executables and a plurality of goodware binary executables, decompiling the plurality of malware binary executables and the plurality of goodware binary executable to extract corresponding assembly code for each of the plurality of malware binary executables and the plurality of goodware binary executable, constructing call graphs for each of the plurality of malware binary executables and the plurality of goodware binary executables from the corresponding assembly code, determining similarities between the call graphs using graph kernels applied to the call graphs for each of the plurality of malware binary executables and the plurality of goodware binary executables, building a malware detection model from the determined similarities between call graphs by applying a machine learning algorithm such as a deep neural network (DNN) algorithm to the determined similarities, and identifying whether a subject executable is malware by applying the built malware detection model to the subject executable.
Owner:UNIVERSITY OF DELAWARE
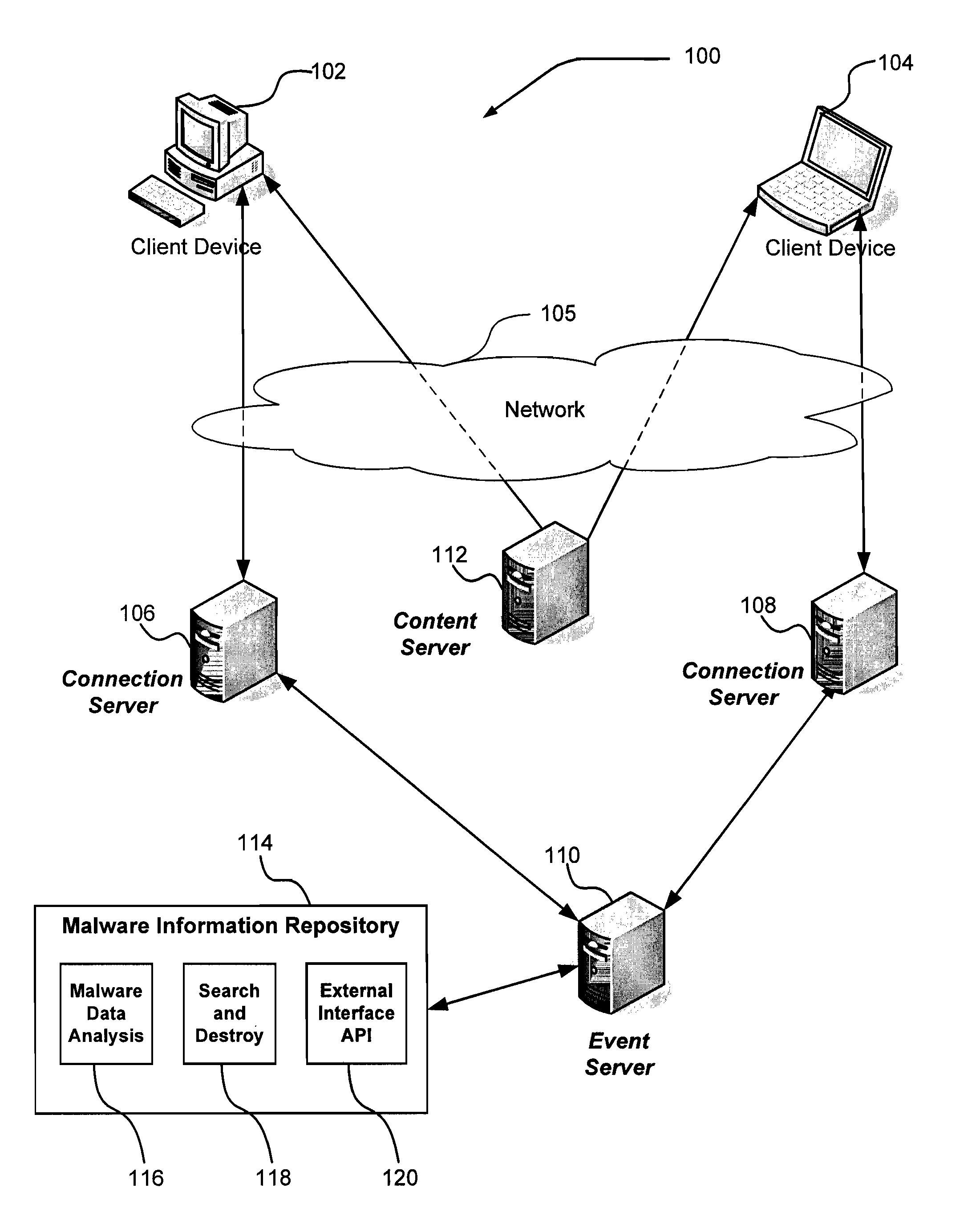
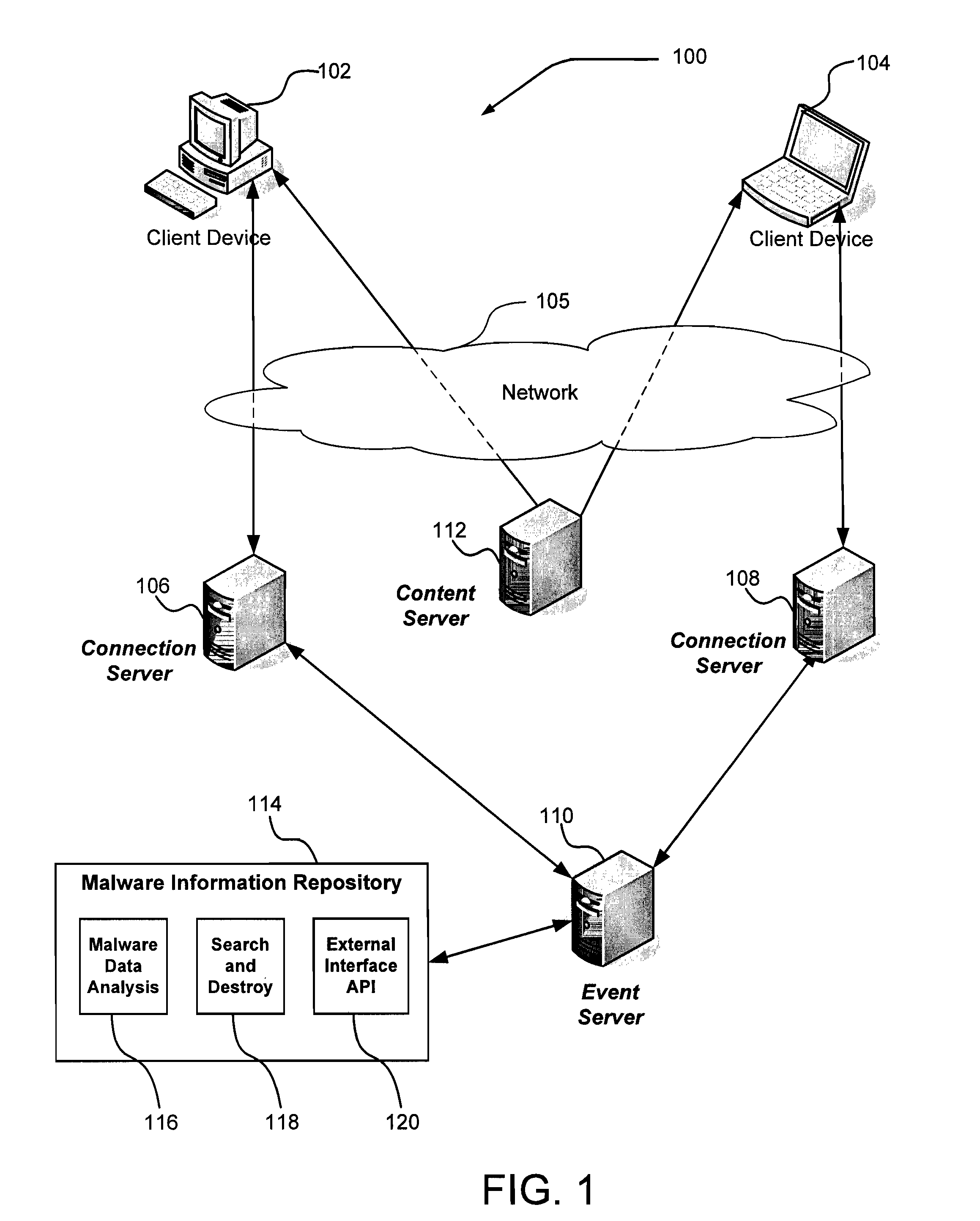
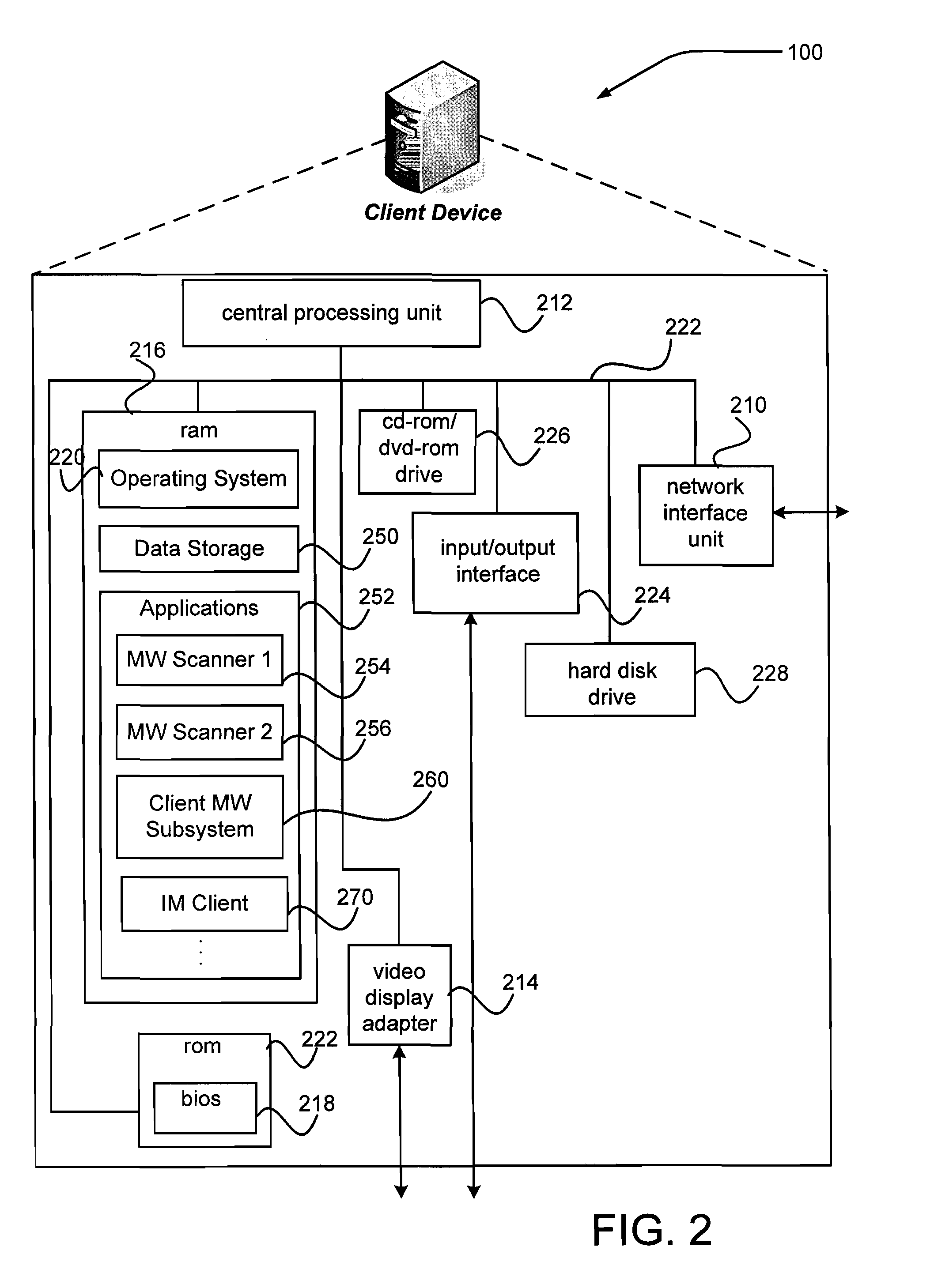
Instant messaging malware protection
InactiveUS20090064335A1Memory loss protectionError detection/correctionInformation repositoryMalware
A system including a content server and a plurality of instant messaging clients is configured to enable each client device to scan for malware on incoming or outgoing instant messages. The content server may receive malware configuration information and distribute the malware configuration information to each client device. Each client device may employ the malware configuration information to perform a number of actions, including determining one or more malware scanners to use, selectively scanning incoming or outgoing instant messages, reporting instances of malware that are detected, or selectively restricting one or more instant messaging functions. The system may include a malware information repository that receives and reports of detected malware, analyzes the reports, and determines sources of malware.
Owner:R2 SOLUTIONS
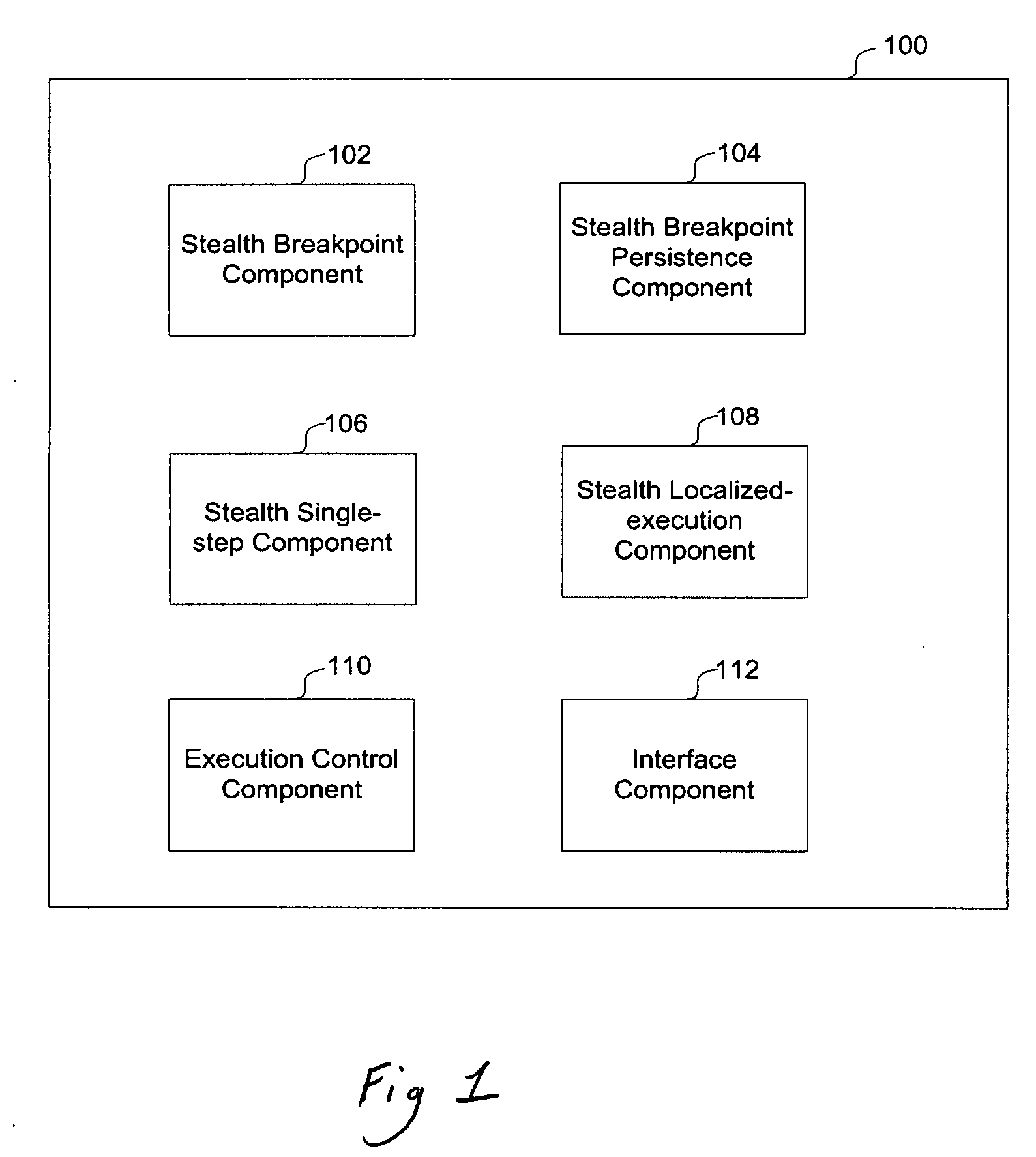
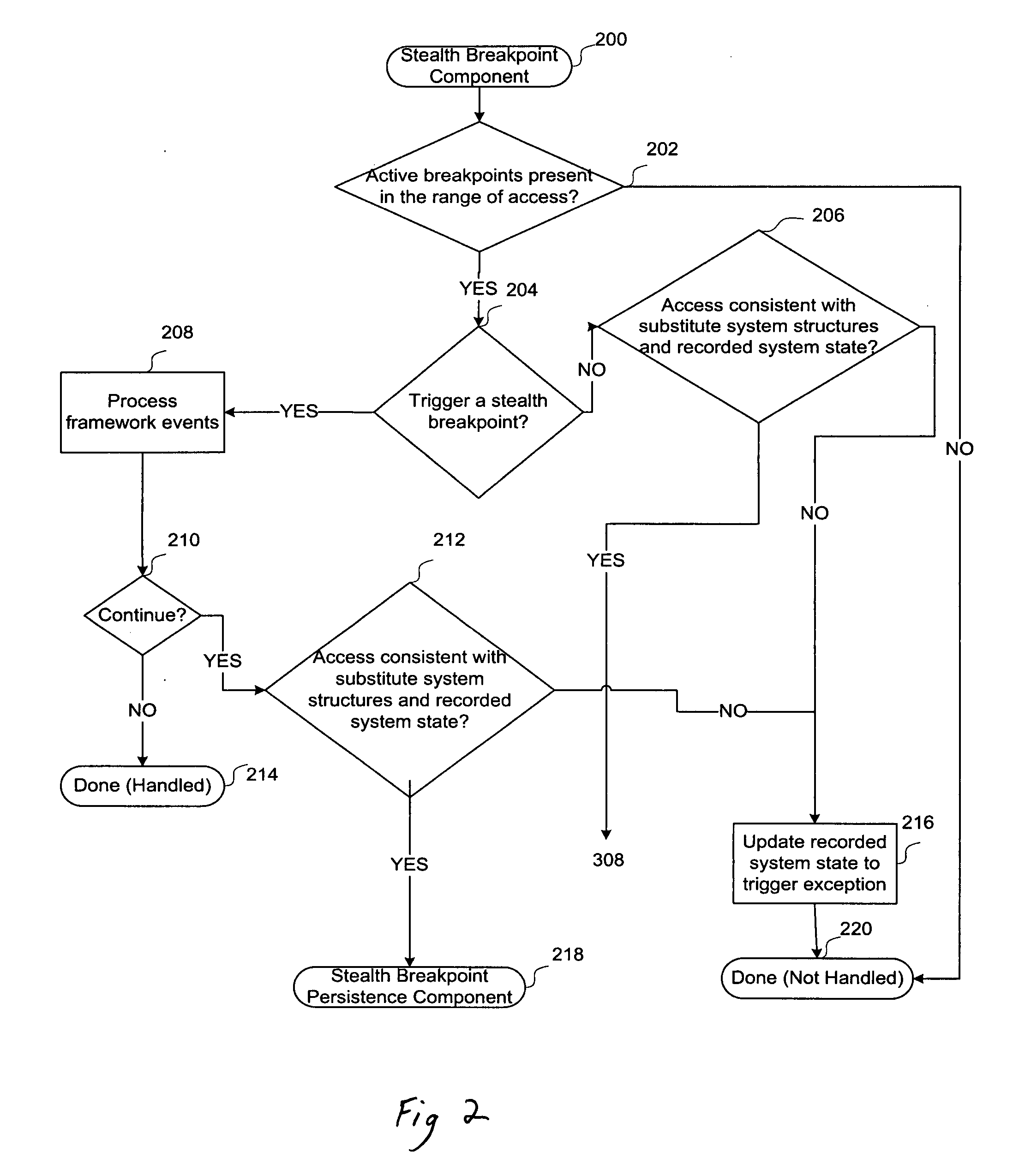
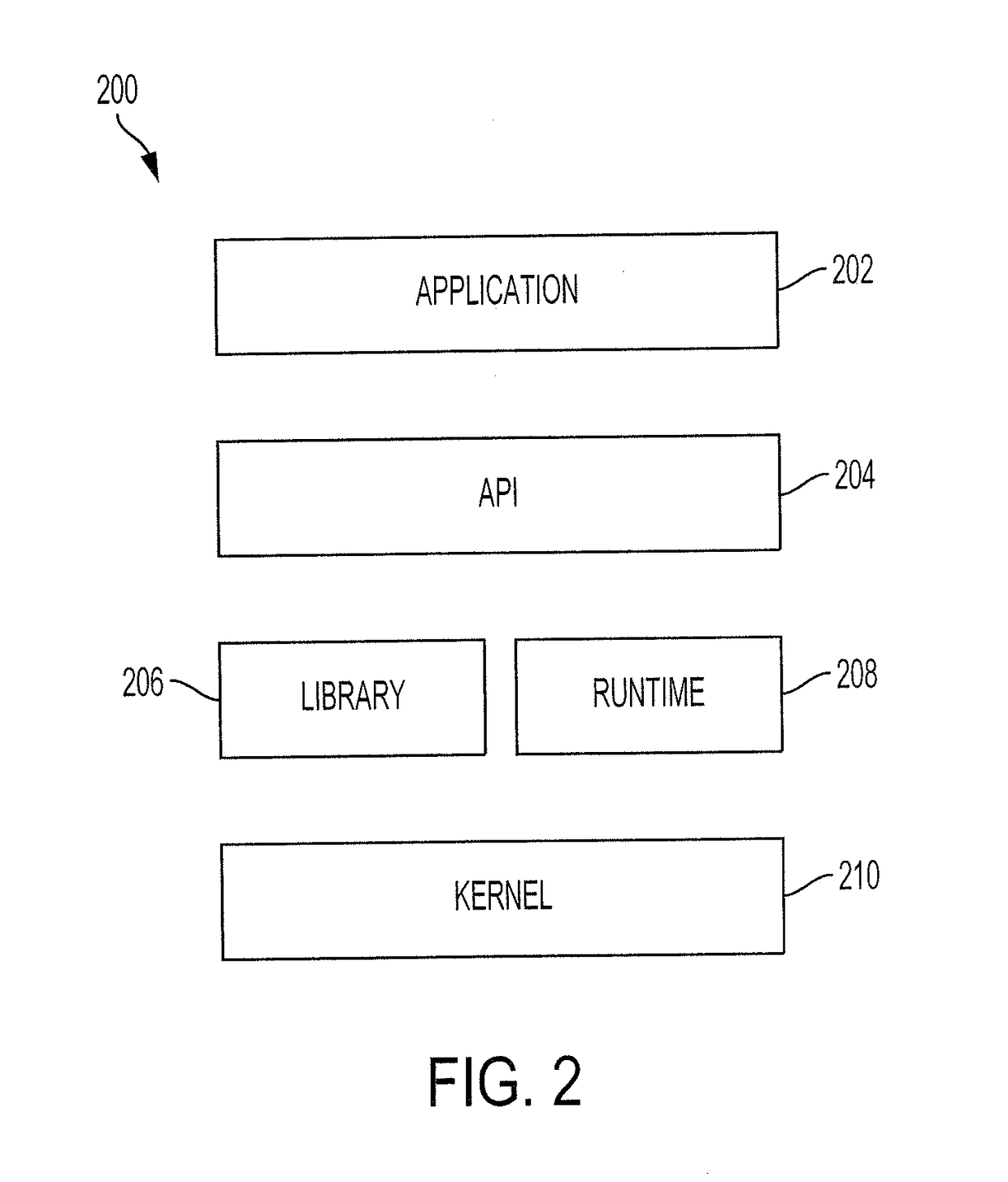
Framework for stealth dynamic coarse and fine-grained malware analysis
InactiveUS20080127114A1Computer security arrangementsSpecific program execution arrangementsMalware analysisGranularity
A framework and method for creating malware analysis tools for dynamic and stealth coarse- and fine-grained malware analysis is provided. In one embodiment a method stalls the execution of a desired code on any form of access to memory or other devices. This can be used to monitor the behavior of the malware with respect to the system at a high level. Upon identification of a high level access, another method can be employed in order to decompose a desired range of code into its individual instructions as they execute thereby revealing the inner structure of the malware as it executes. Since the framework does not employ any processor debugging features, and its methods are self-resilient and completely invisible to the executing code, malware that employ any form of anti-debugging and / or anti-analysis strategy including using framework methods can be easily and effectively analyzed.
Owner:VASUDEVAN AMIT
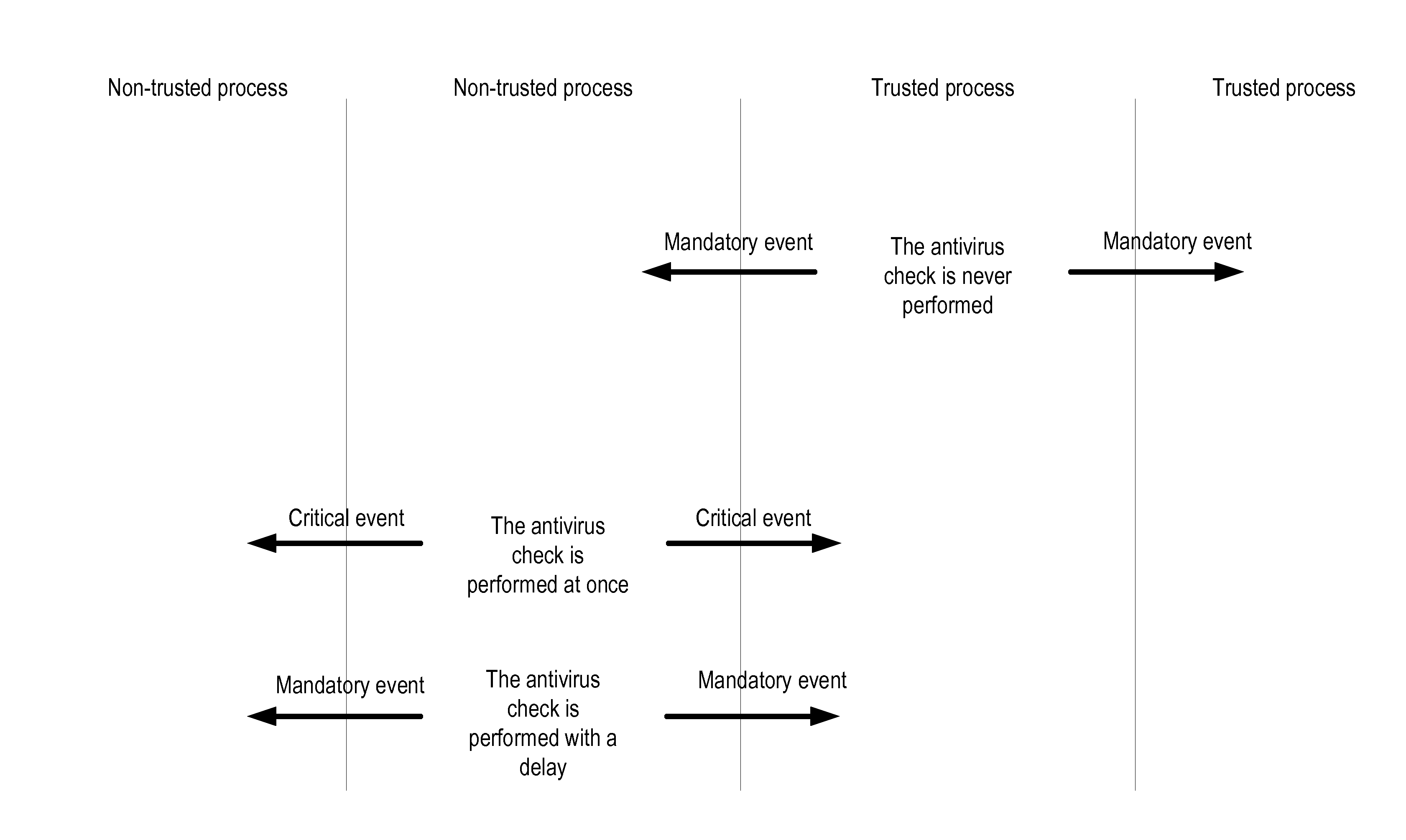
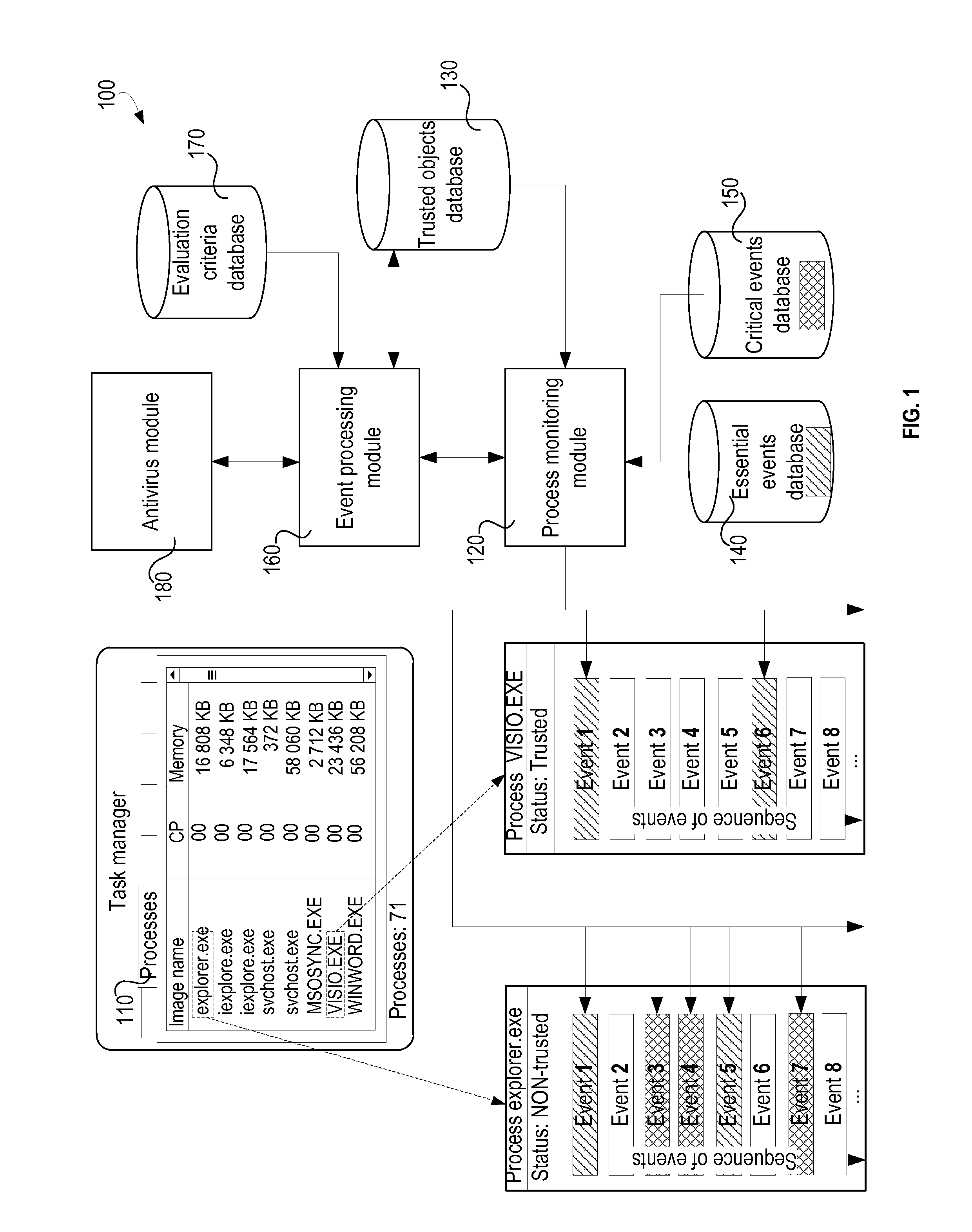
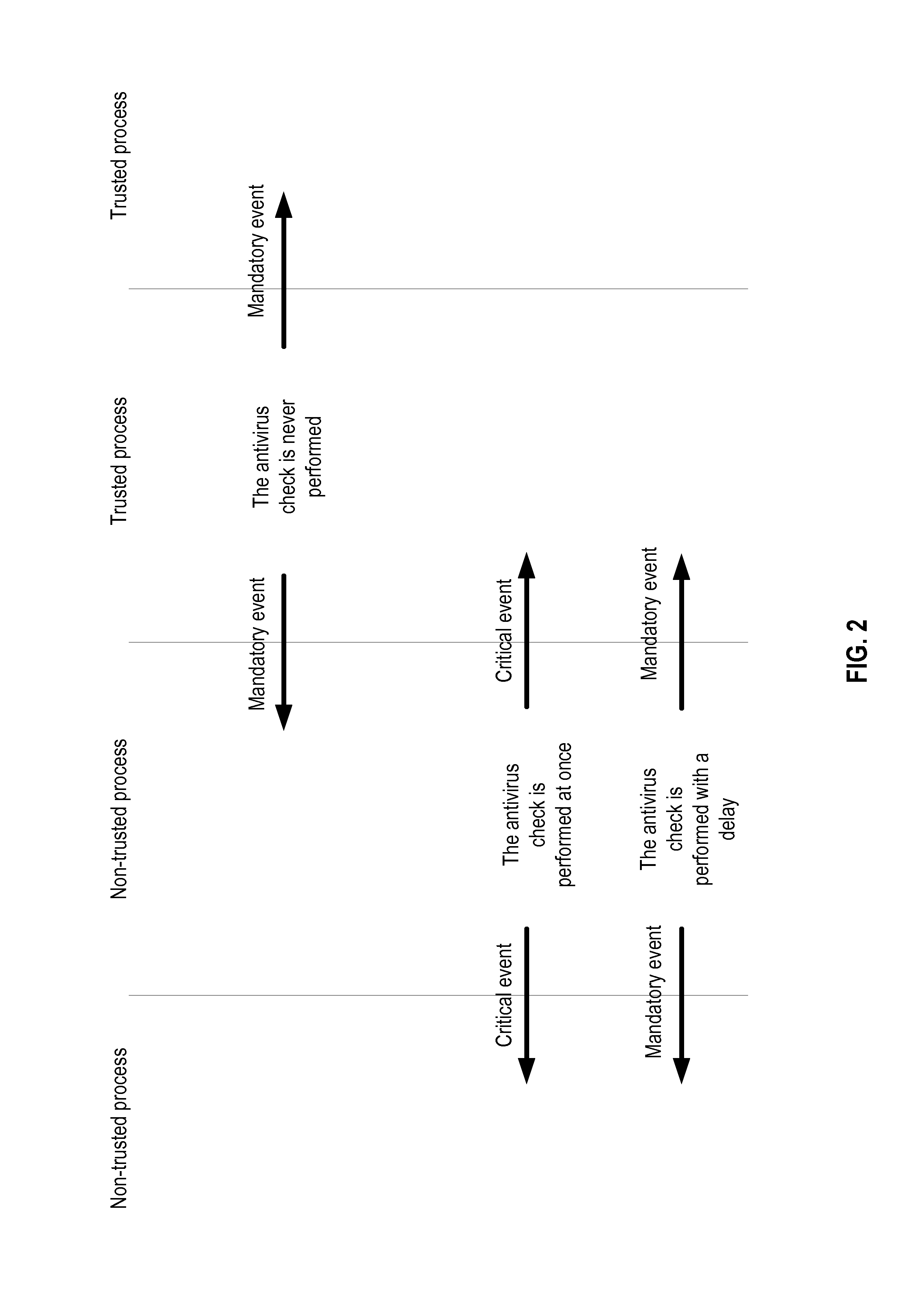
System and method for reducing load on an operating system when executing antivirus operations
ActiveUS20150163231A1Memory loss protectionError detection/correctionMalware analysisOperational system
An initial trust status is assigned to a first object, the trust status representing one of either a relatively higher trust level or a relatively lower trust level. Based on the trust status, the first object is associated with an event type to be monitored, where the event type is selected from among: essential events, occurrence of which is informative as to trust status evaluating for an object, and critical events, including the essential events, and additional events, occurrence of which is informative as to execution of suspicious code. Occurrences of events relating to the first object are monitored. In response to the first object being assigned the relatively higher trust level, only the essential events are monitored. In response to the first object being assigned the relatively lower trust level, the critical events are monitored. A need for performing malware analysis is determined based on the trust status of the first object and the event type. In response to determination of the need for performing the malware analysis, the malware analysis for the first object is either performed, or not.
Owner:AO KASPERSKY LAB
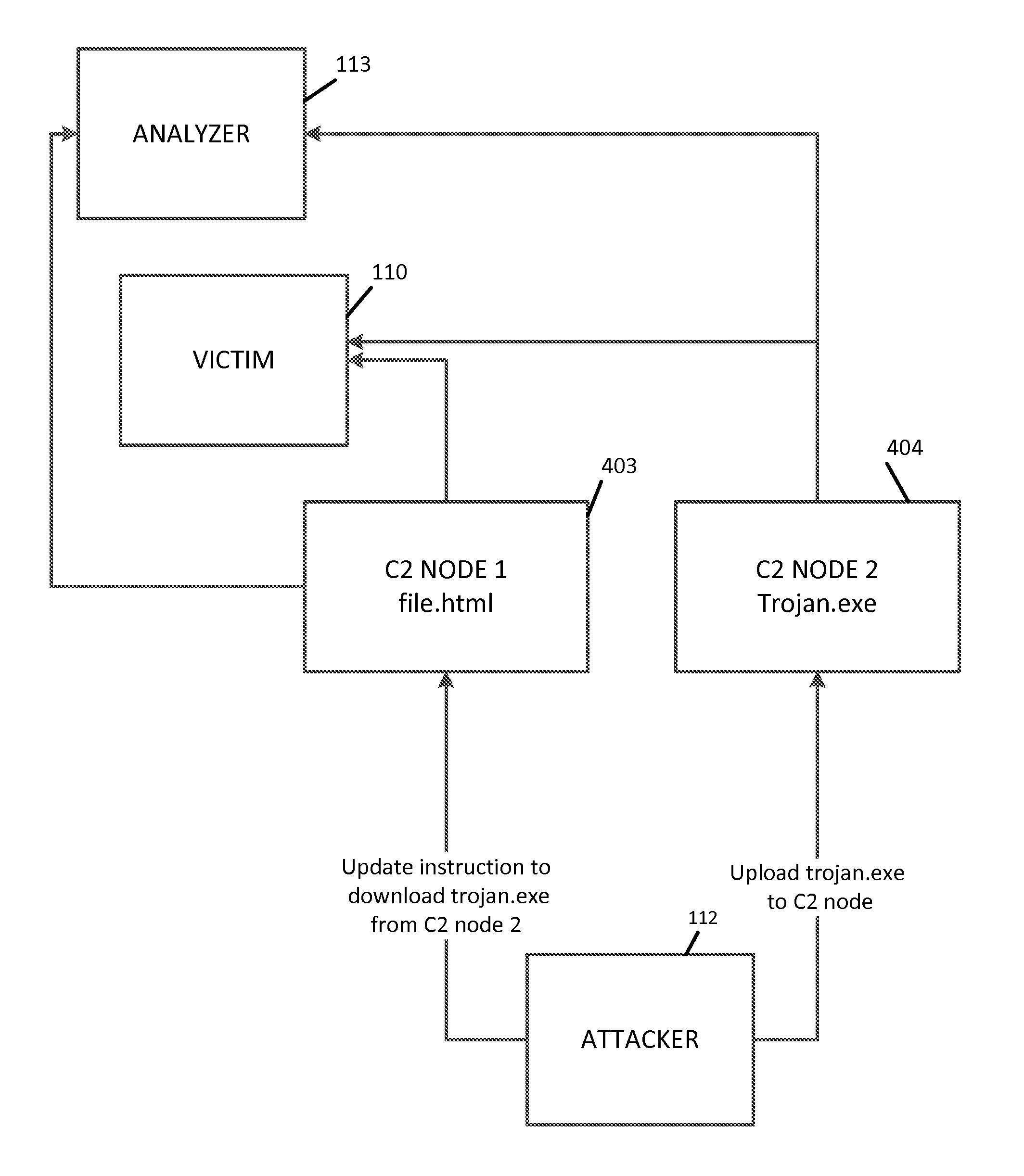
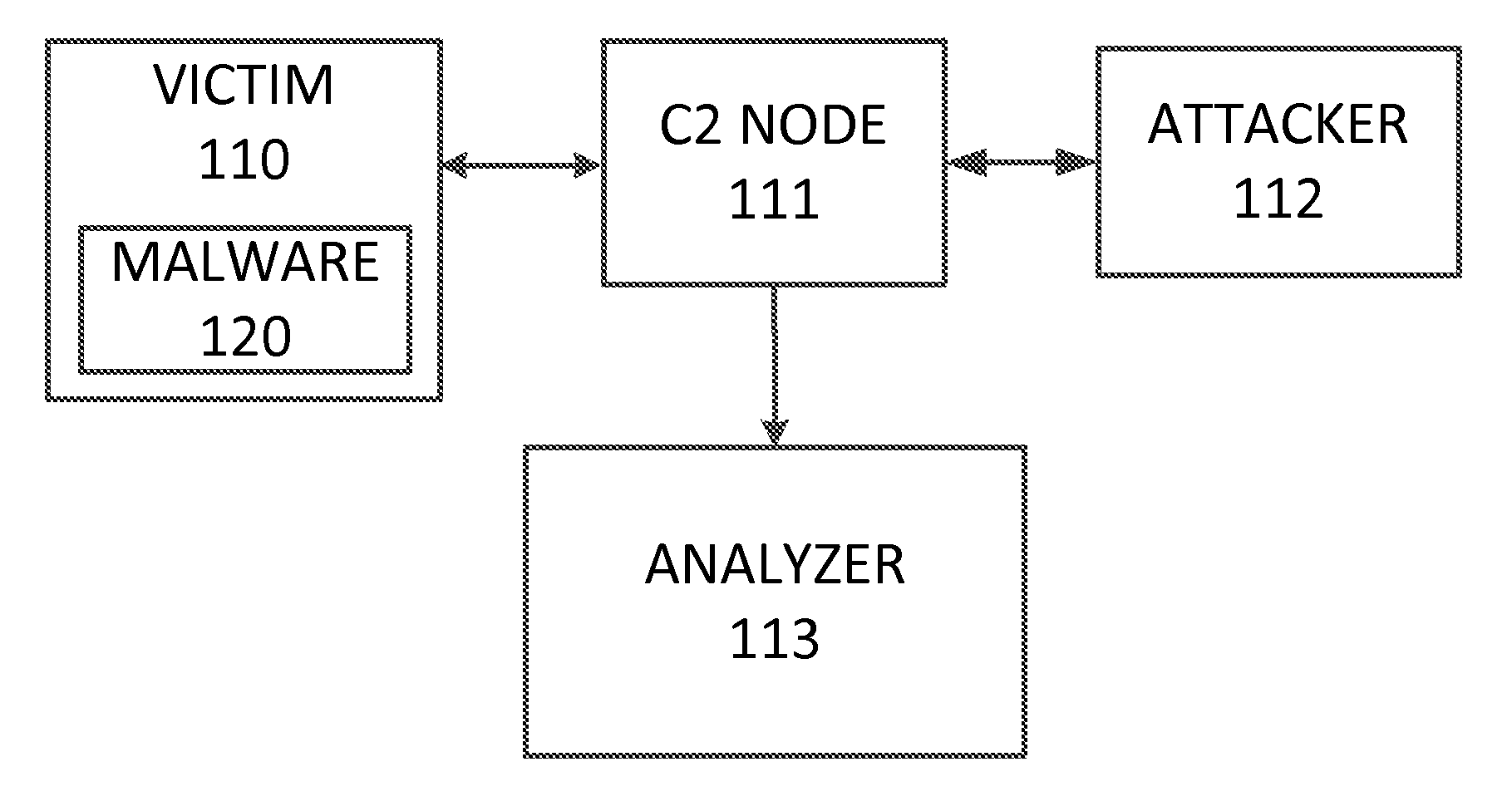
Systems and methods for automated malware artifact retrieval and analysis
InactiveUS8850585B2Memory loss protectionUnauthorized memory use protectionMalware analysisComputer network
An automated malware analysis method is disclosed which can perform receiving a first universal resource locator identifying a first intermediate network node, accessing the first intermediate network node to retrieve a first malware artifact file, storing the malware artifact file in a data storage device, analyzing the malware artifact file to identify a second universal resource locator within the malware artifact file, and accessing a second intermediate network node to retrieve a second malware artifact file.
Owner:CYBER ENG SERVICES
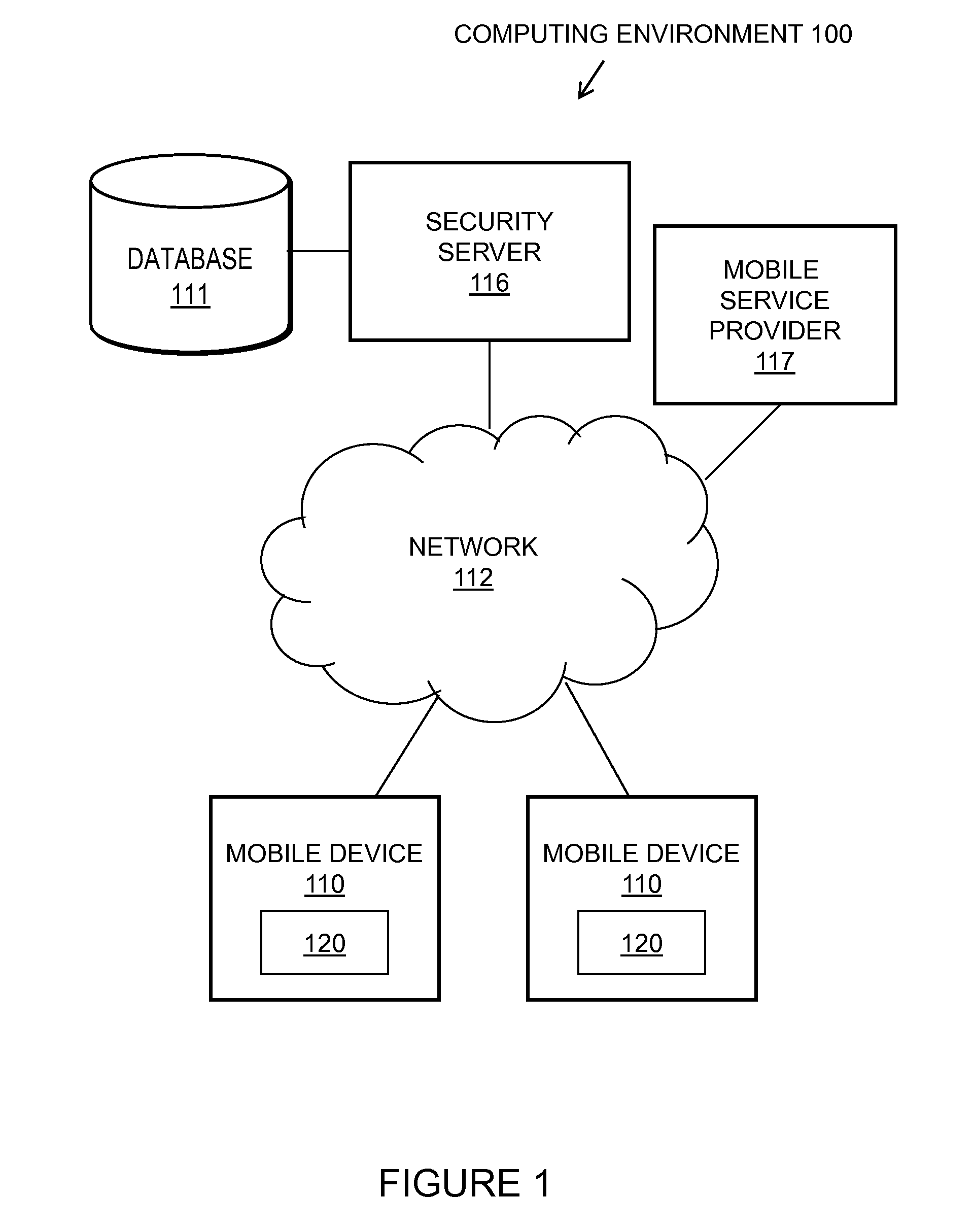
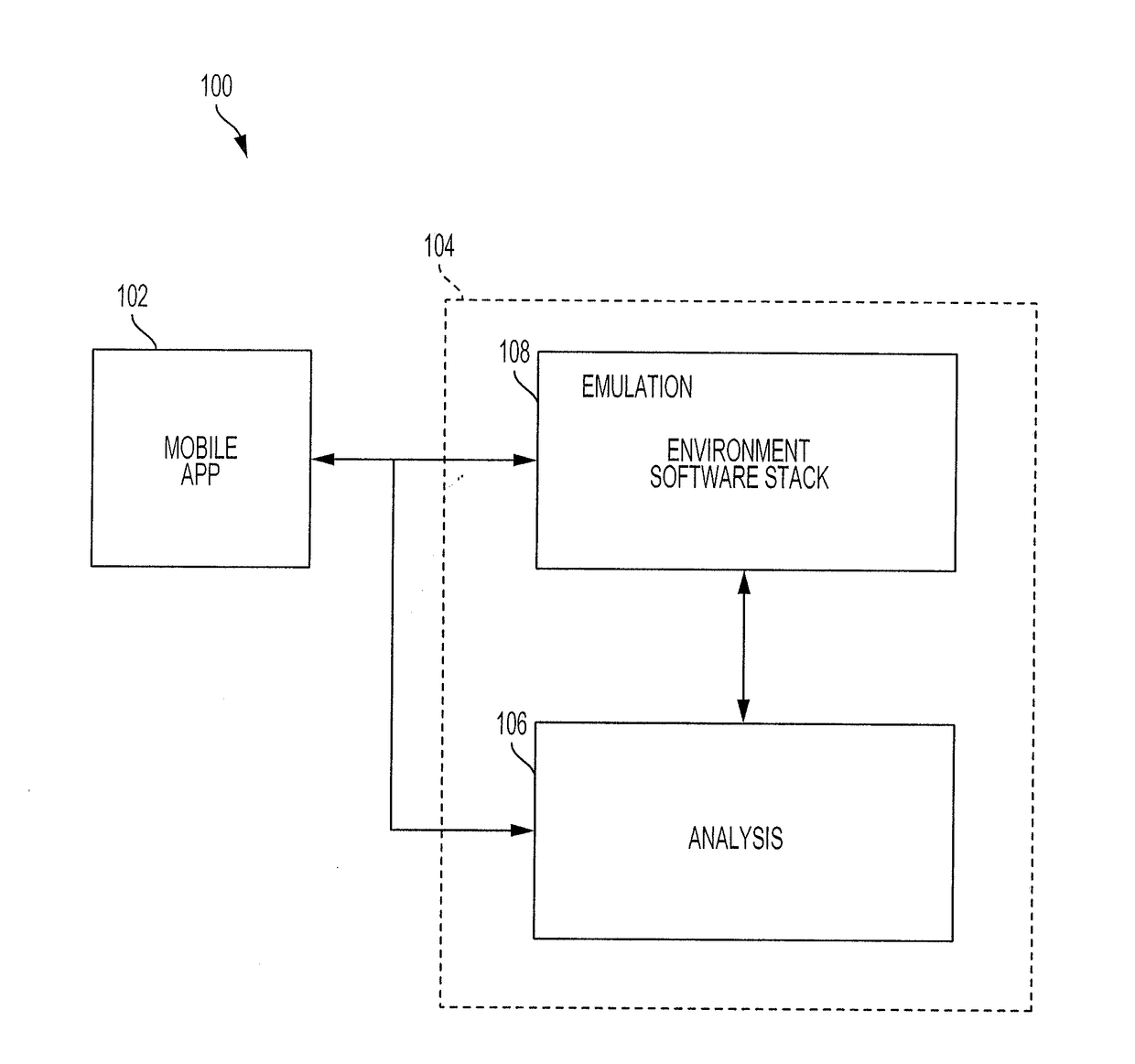
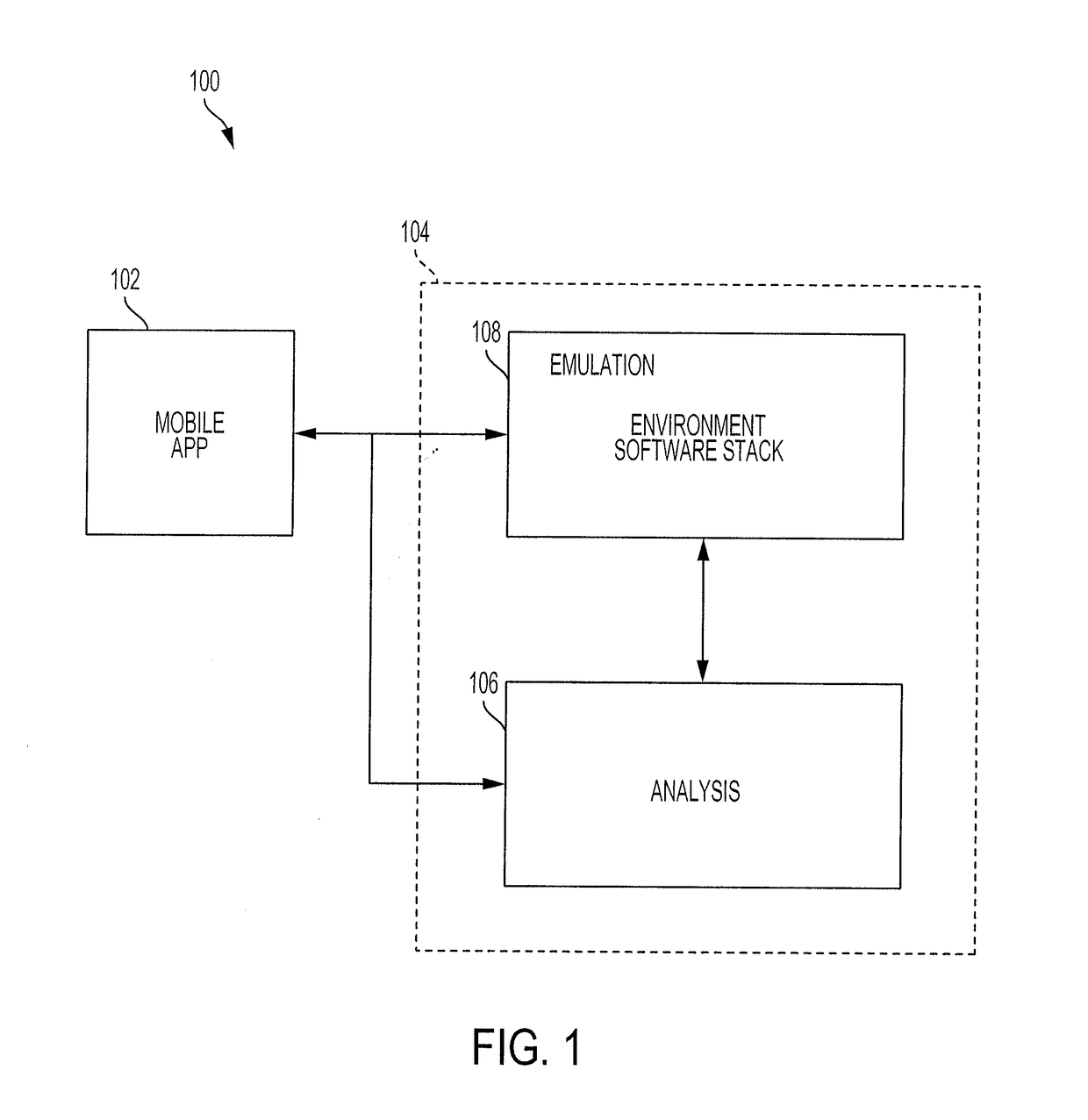
System and method for vetting mobile phone software applications
ActiveUS20170277891A1Simulation is accurateGood lookingPlatform integrity maintainanceTransmissionMalware analysisSoftware emulation
A system and method for implementing a software emulation environment is provided. In one example, a mobile application can interface with an emulation environment that can be used to test whether the mobile application includes malware that can compromise the security and integrity of an enterprise's computing infrastructure. When the mobile application issues a call for data, a device mimic module can intercept the call and determine if the call includes a call for one or more checkable artifacts that can reveal the existence of the emulation environment. If such a call for data occurs, the device mimic module can provide one or more spoofed checkable artifacts that have been recorded from a real-world mobile device. In this way, the existence of the emulation environment can be concealed so as to allow for a more thorough analysis of a mobile application for potential hidden malware.
Owner:MITRE SPORTS INT LTD
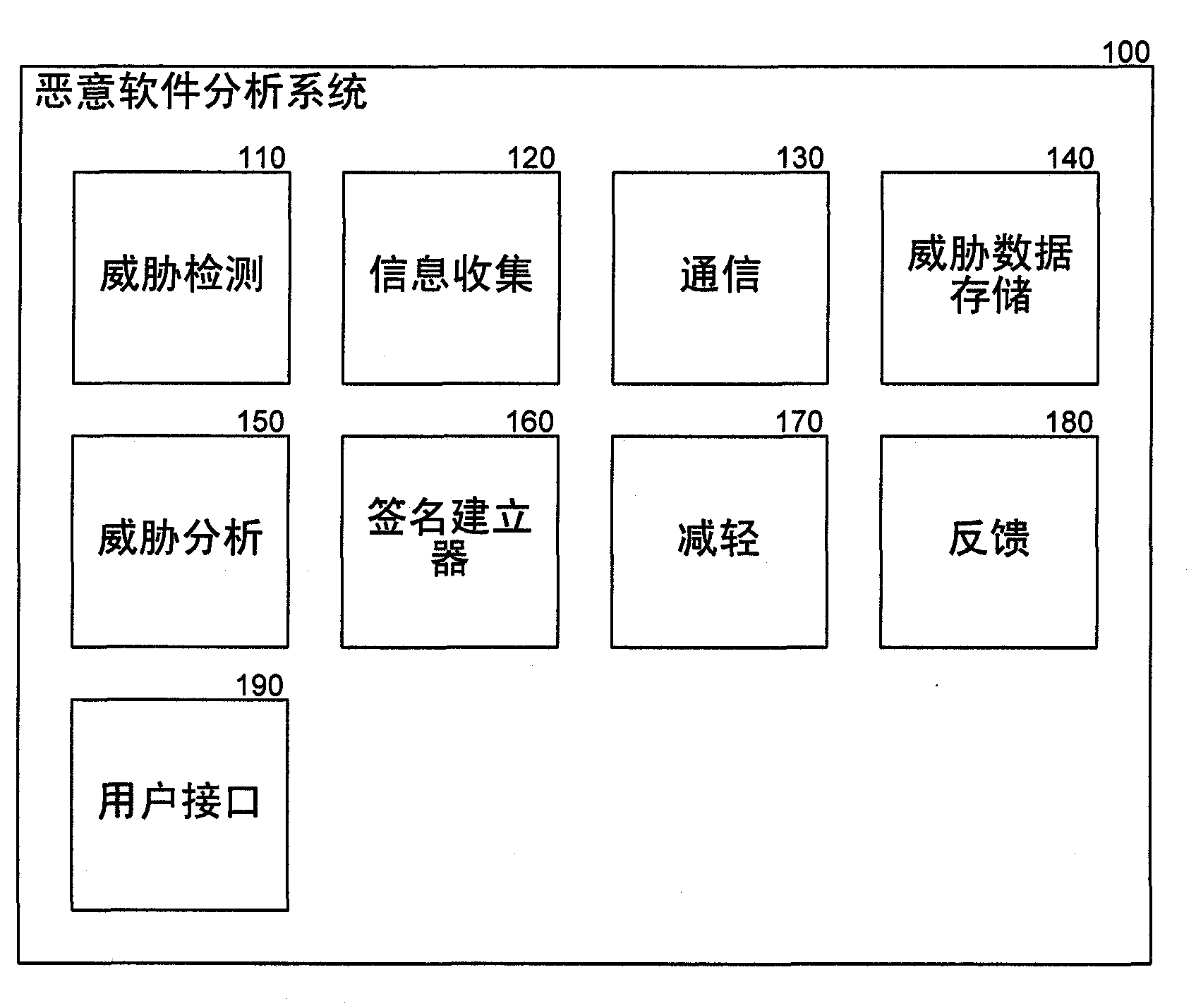
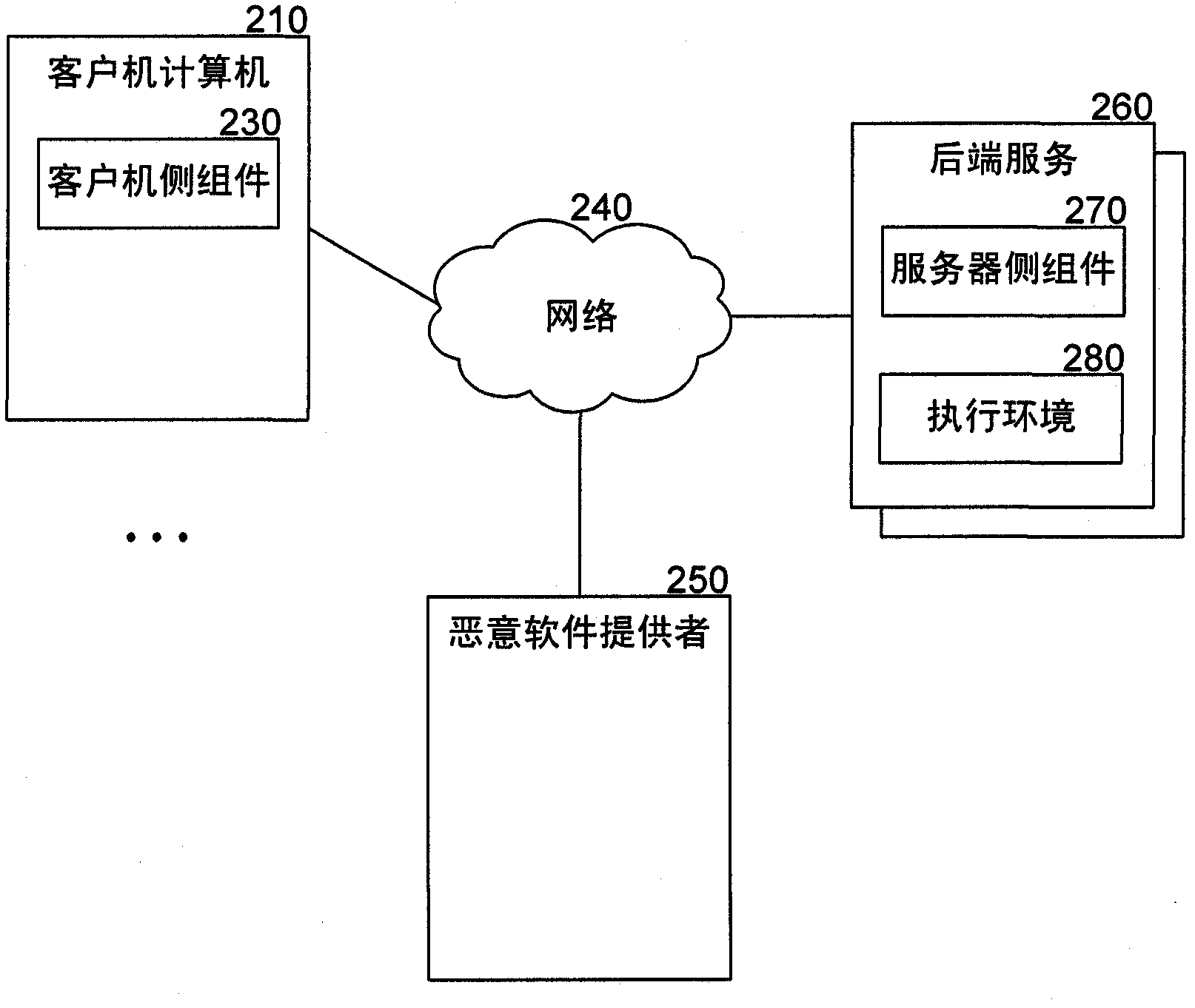
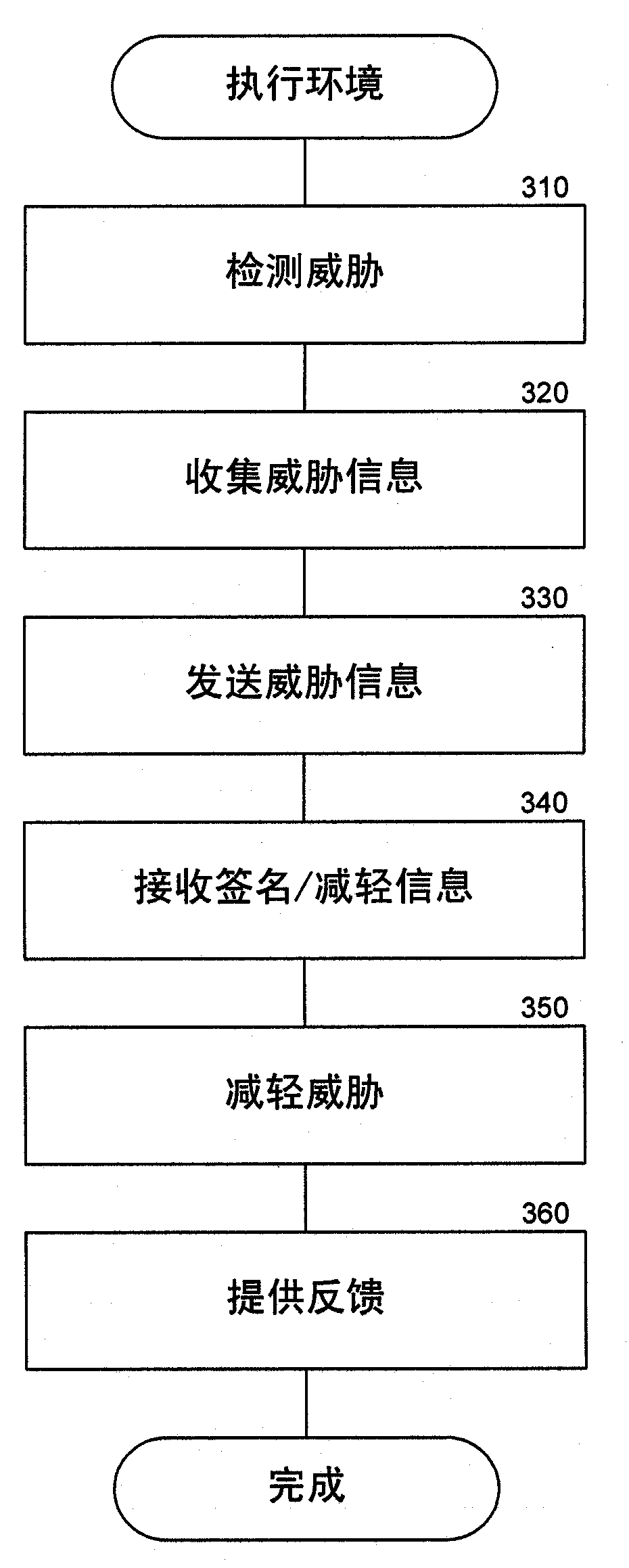
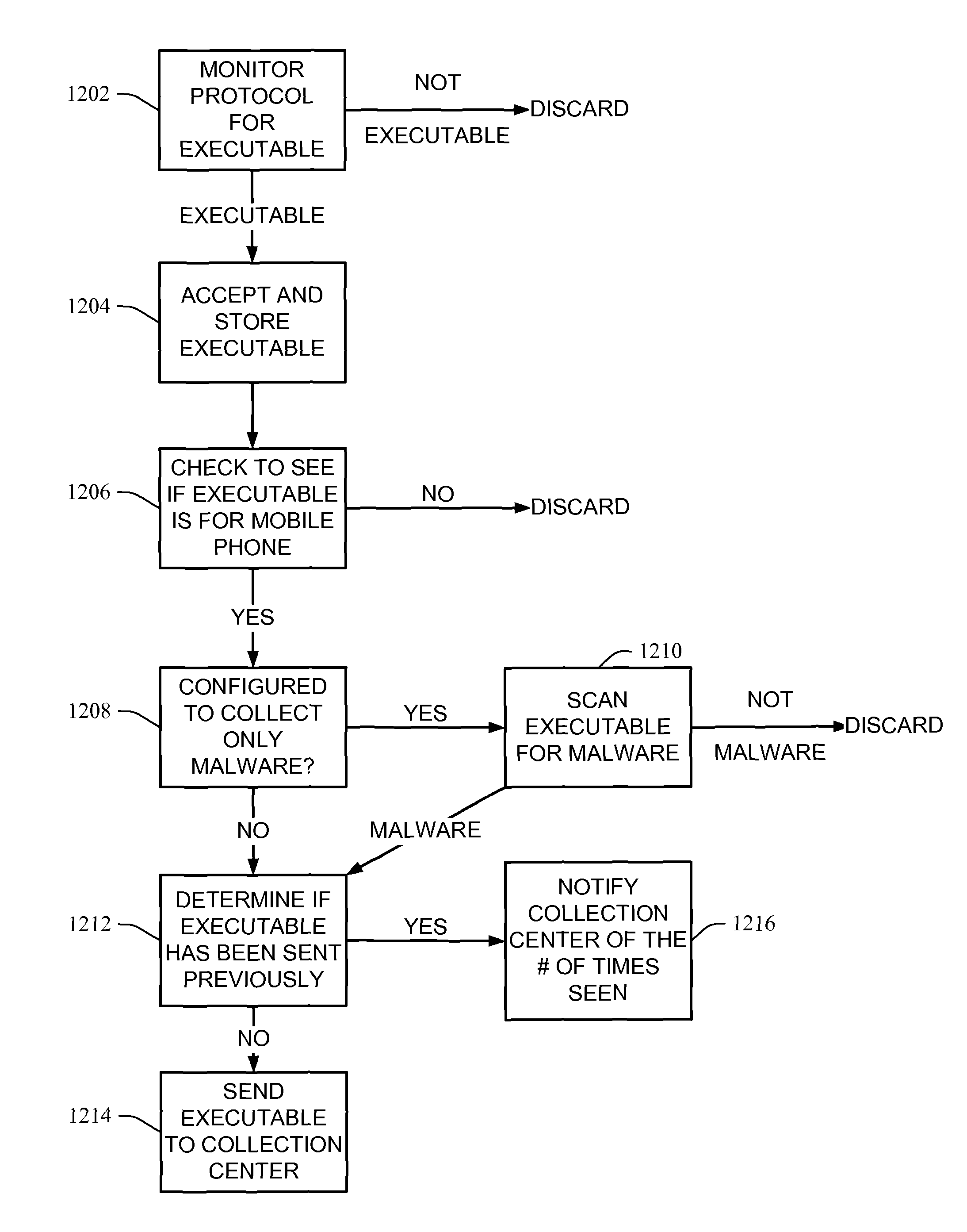
Collecting and analyzing malware data
ActiveCN102160048AComputer security arrangementsMultiple digital computer combinationsMalware analysisTechnician
A malware analysis system is described that provides information about malware execution history on a client computer and allows automated back-end analysis for faster creation of identification signatures and removal instructions. The malware analysis system collects threat information on client computers and sends the threat information to a back-end analysis component for automated analysis. The back-end analysis component analyzes the threat information by comparing the threat information to information about known threats. The system builds a signature for identifying the threat family and a mitigation script for neutralizing the threat. The system sends the signature and mitigation data to client computers, which use the information to mitigate the threat. Thus, the malware analysis system detects and mitigates threats more quickly than previous systems by reducing the burden on technicians to manually create environments for reproducing the threats and manually analyze the threat behavior.
Owner:MICROSOFT TECH LICENSING LLC
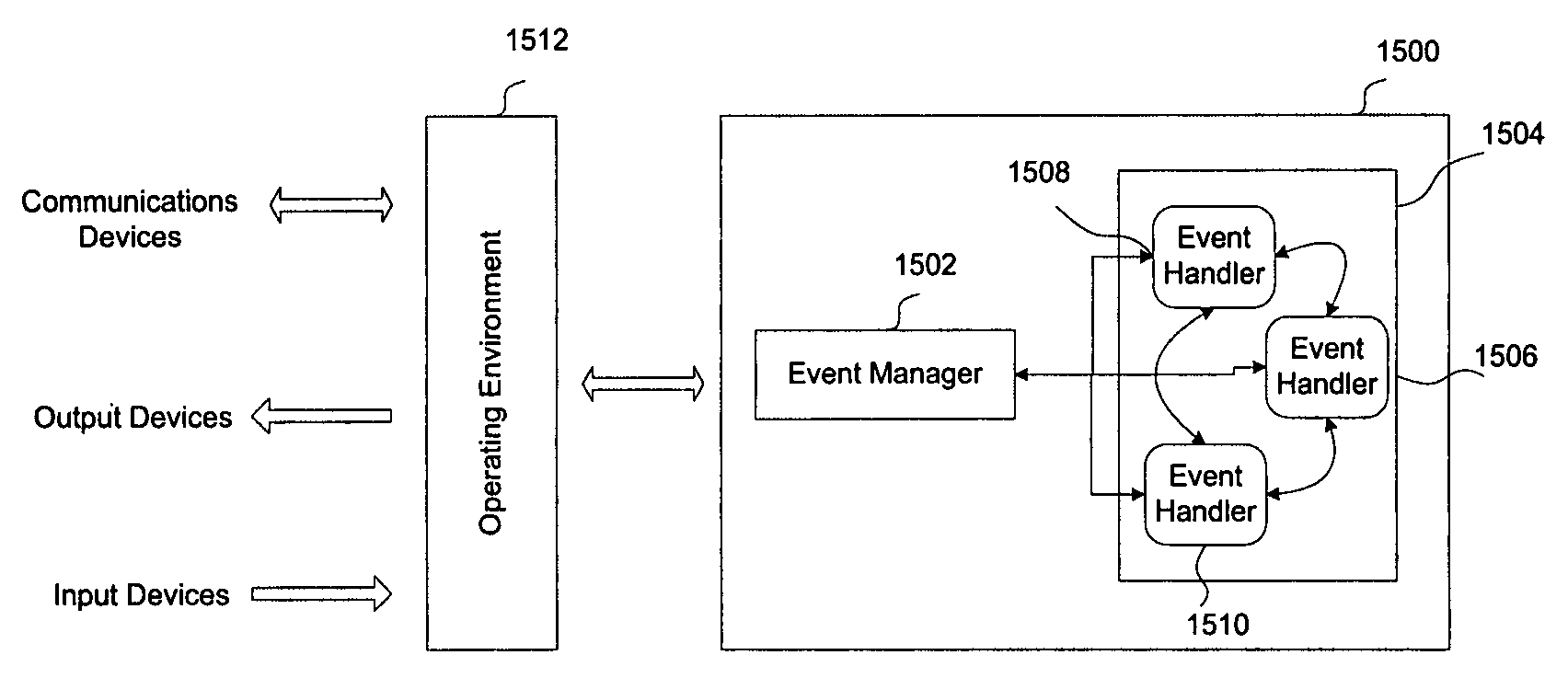
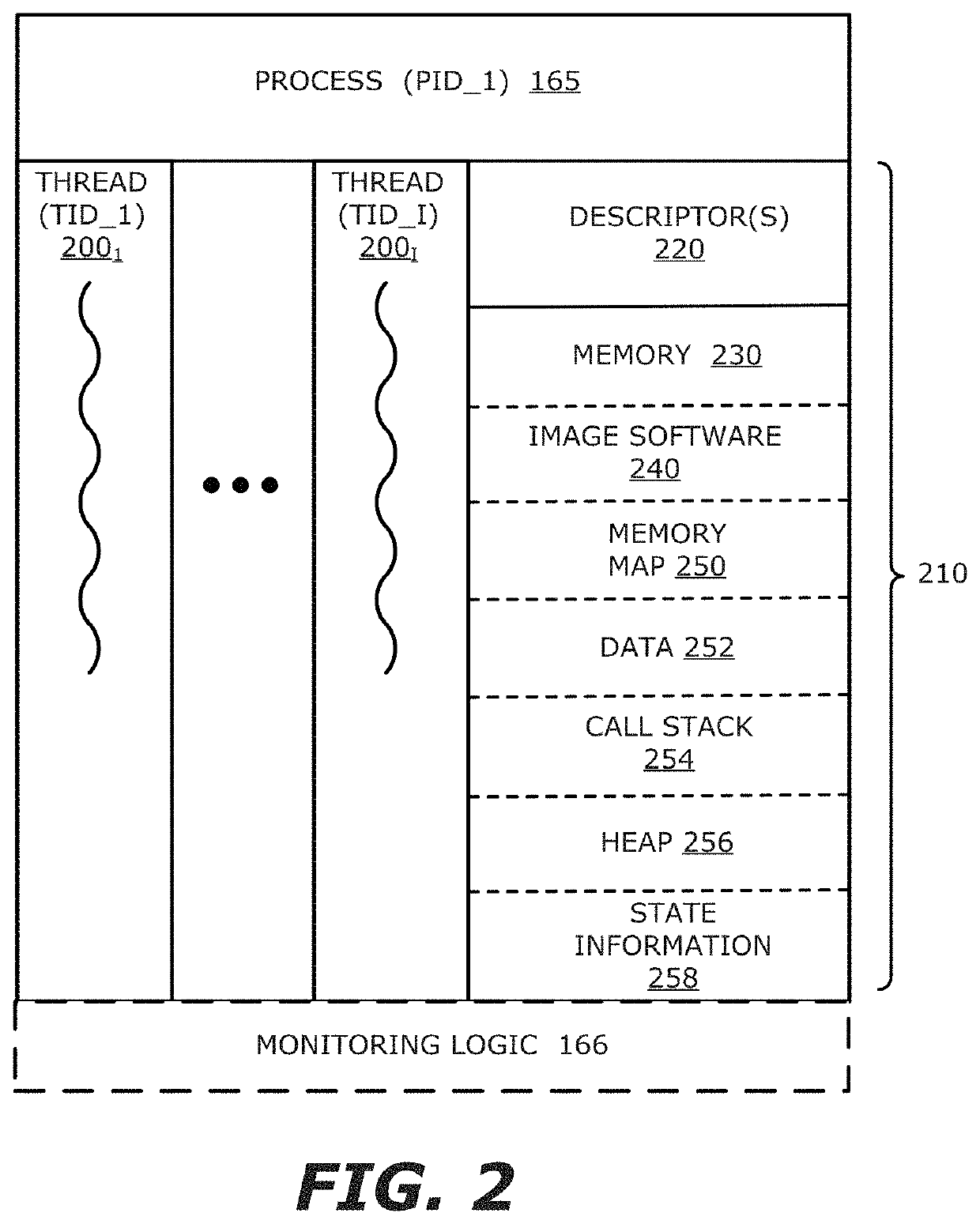
System and method for malware analysis using thread-level event monitoring
According to one embodiment, a computerized method comprises processing one or more objects by a first thread of execution that are part of a multi-thread process, monitoring events that occur during the processing of the one or more objects by the first thread, and storing information associated with the monitored events within an event log. The stored information comprises at least an identifier of the first thread to maintain an association between the monitored events and the first thread. Subsequently, the stored information within the event log is accessed for rendering a graphical display of the monitored events detected during processing of the one or more objects by the first thread on a display screen.
Owner:FIREEYE SECURITY HLDG US LLC
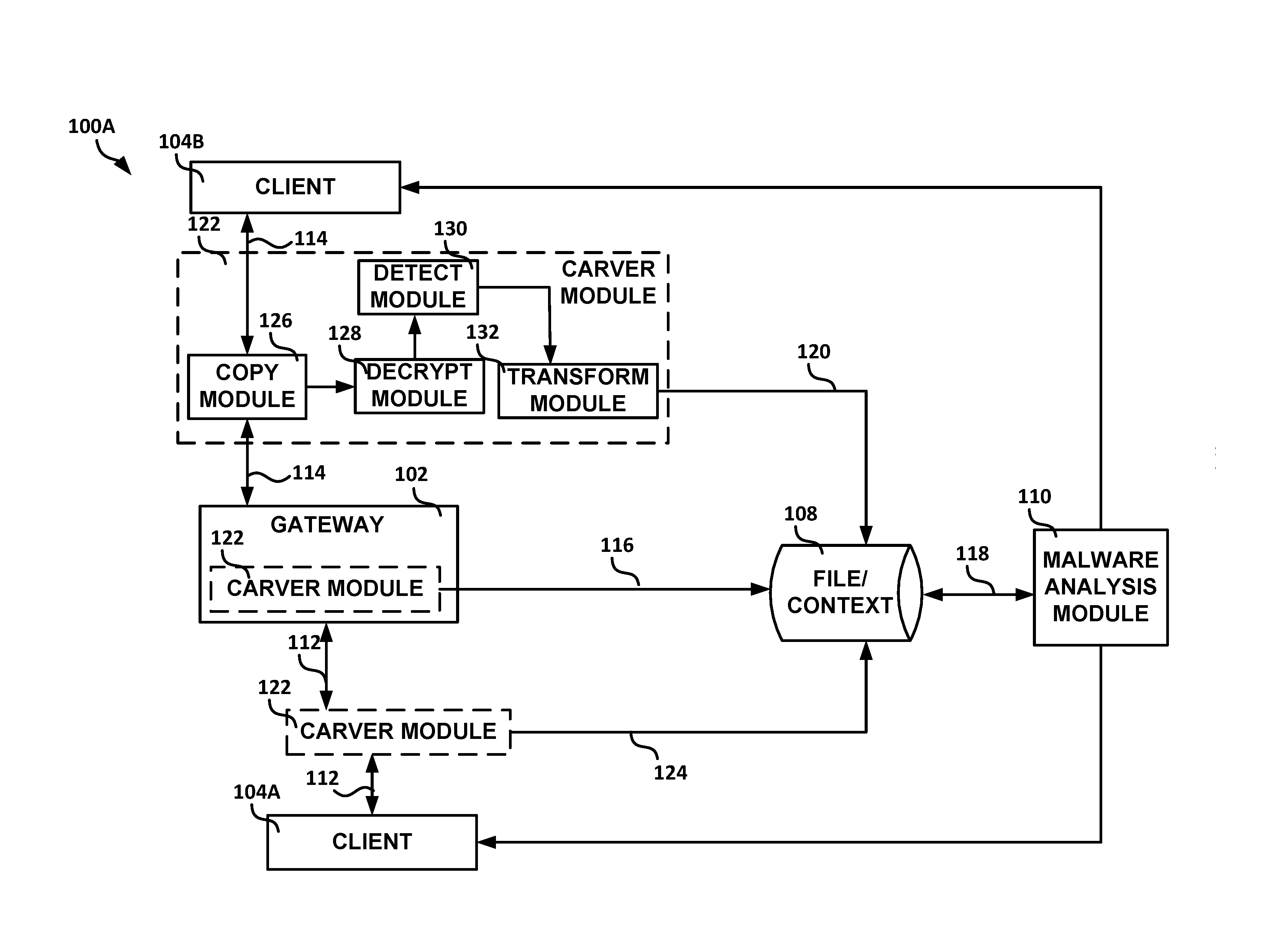
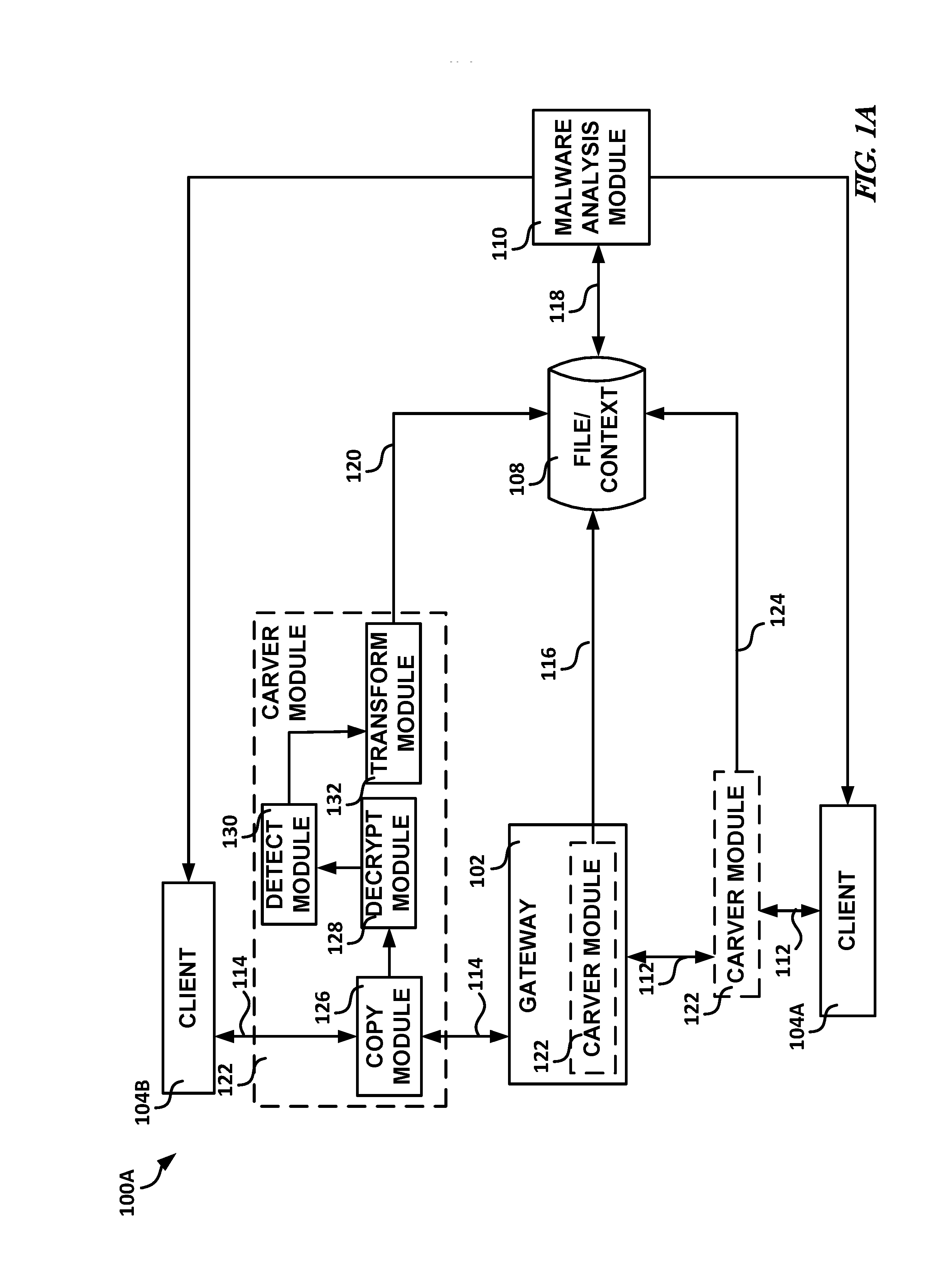
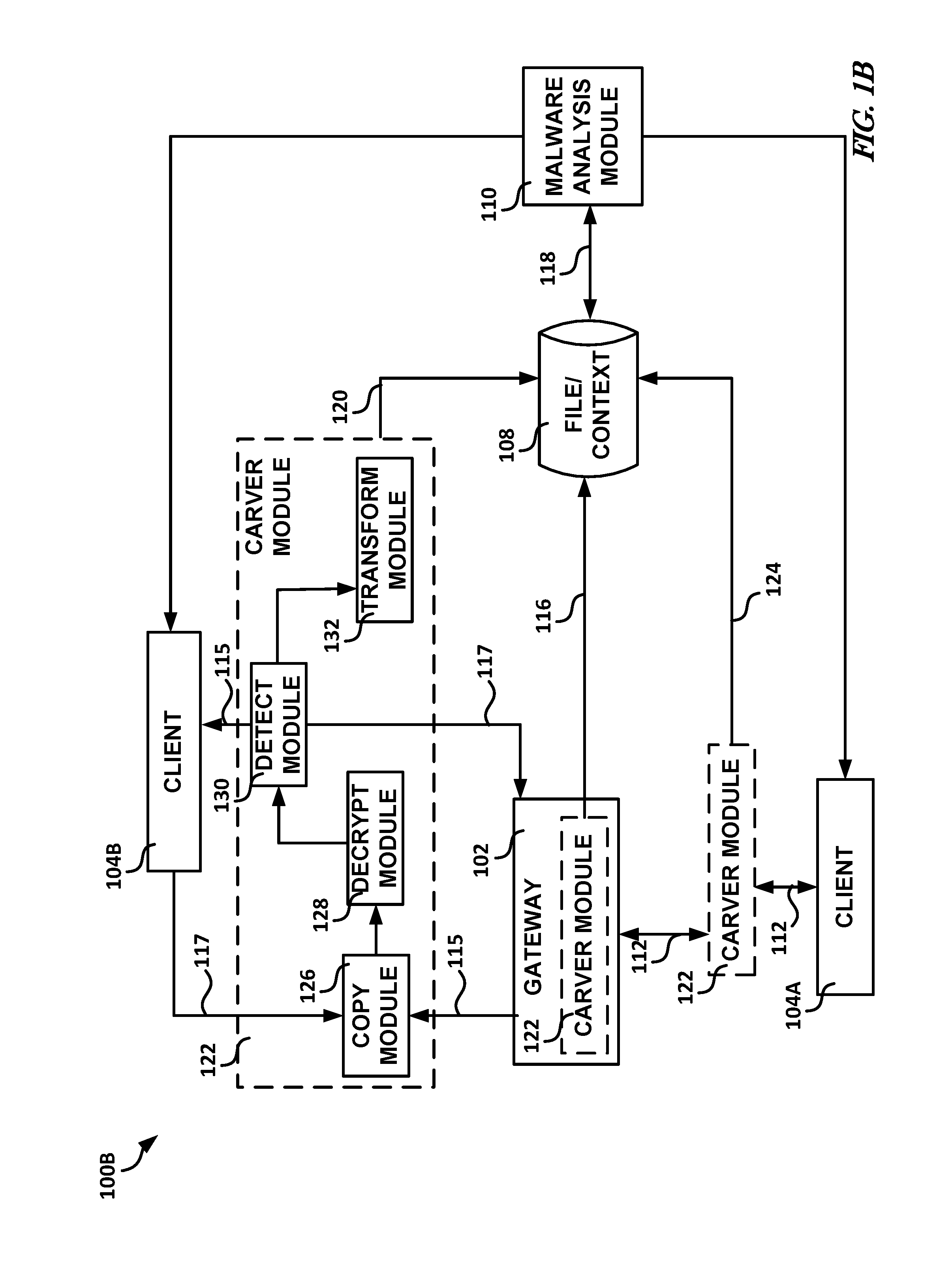
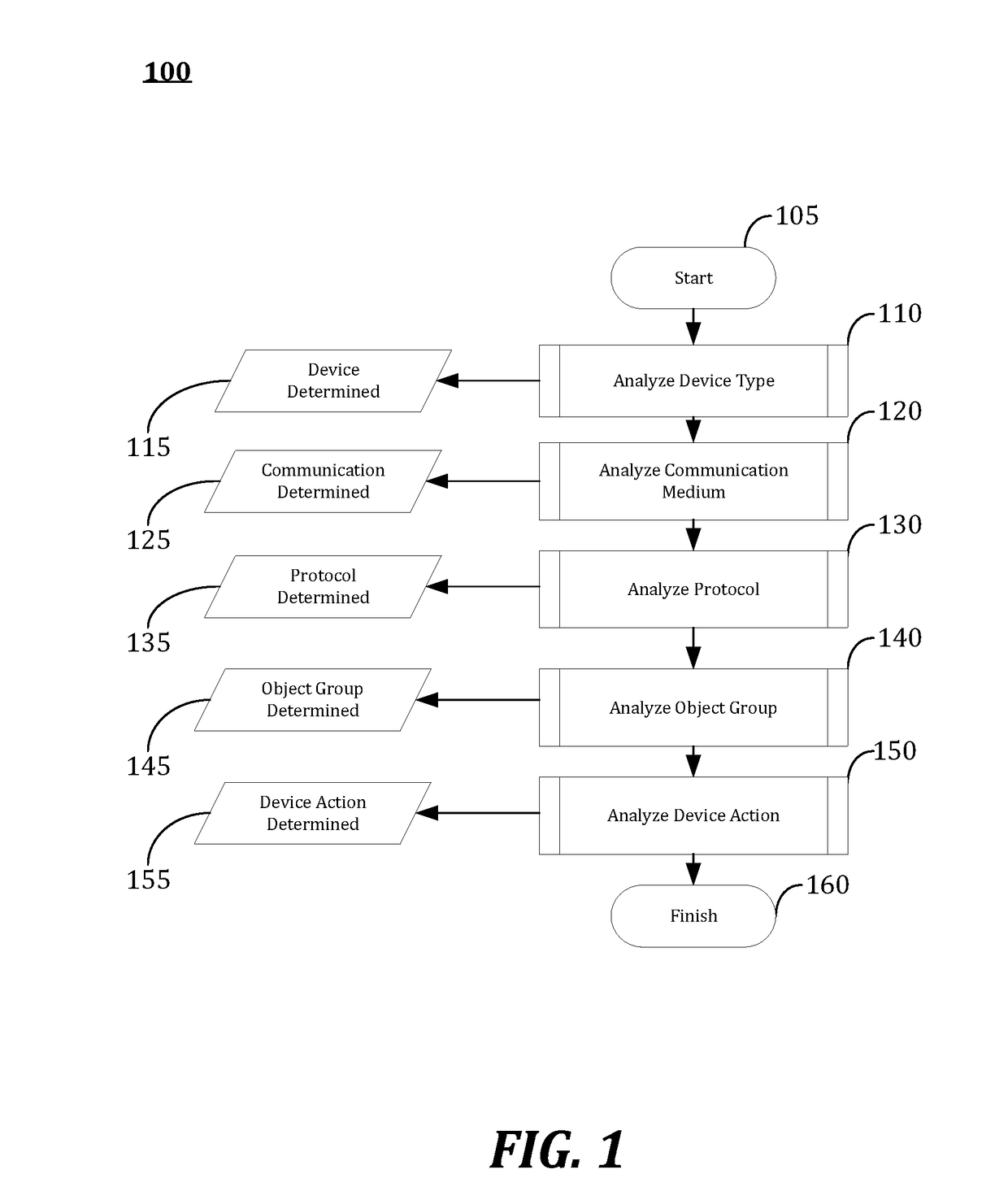
Systems and methods for malware analysis of network traffic
Generally discussed herein are systems, devices, and methods for malware analysis. In one or more embodiments, a method can include copying application layer data traffic to create copied application layer data traffic, forwarding at least a portion of the application layer data traffic to a destination client prior to a malware analysis of corresponding copied application layer data traffic, determining whether the copied application layer data traffic includes a specified property, and in response to a determination that the copied application layer data traffic includes the specified property, storing the copied application layer data traffic determined to include the specified property for subsequent malware analysis, the stored copied application layer data traffic including context data of the copied application layer data traffic.
Owner:FORCEPOINT FEDERAL
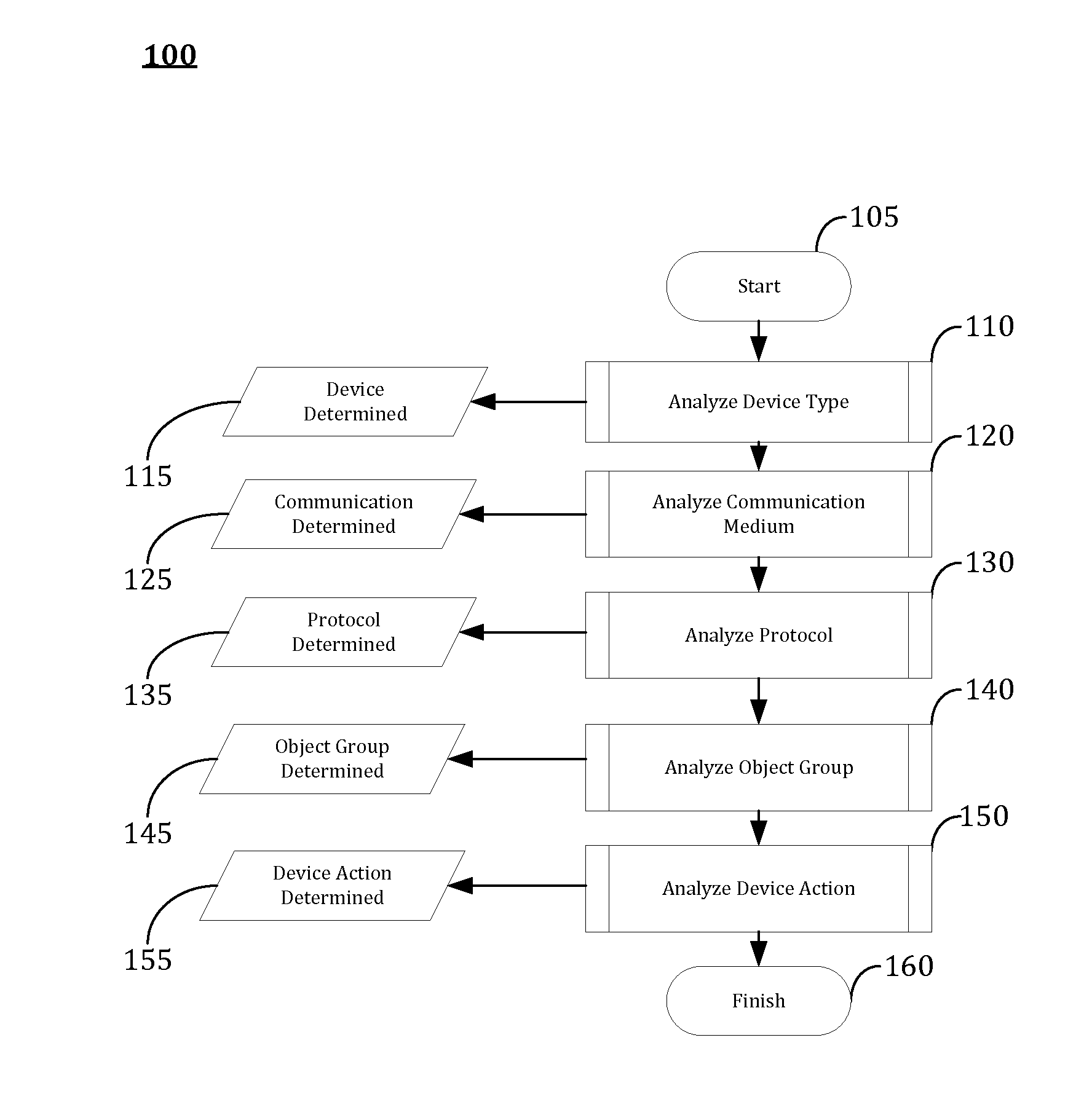
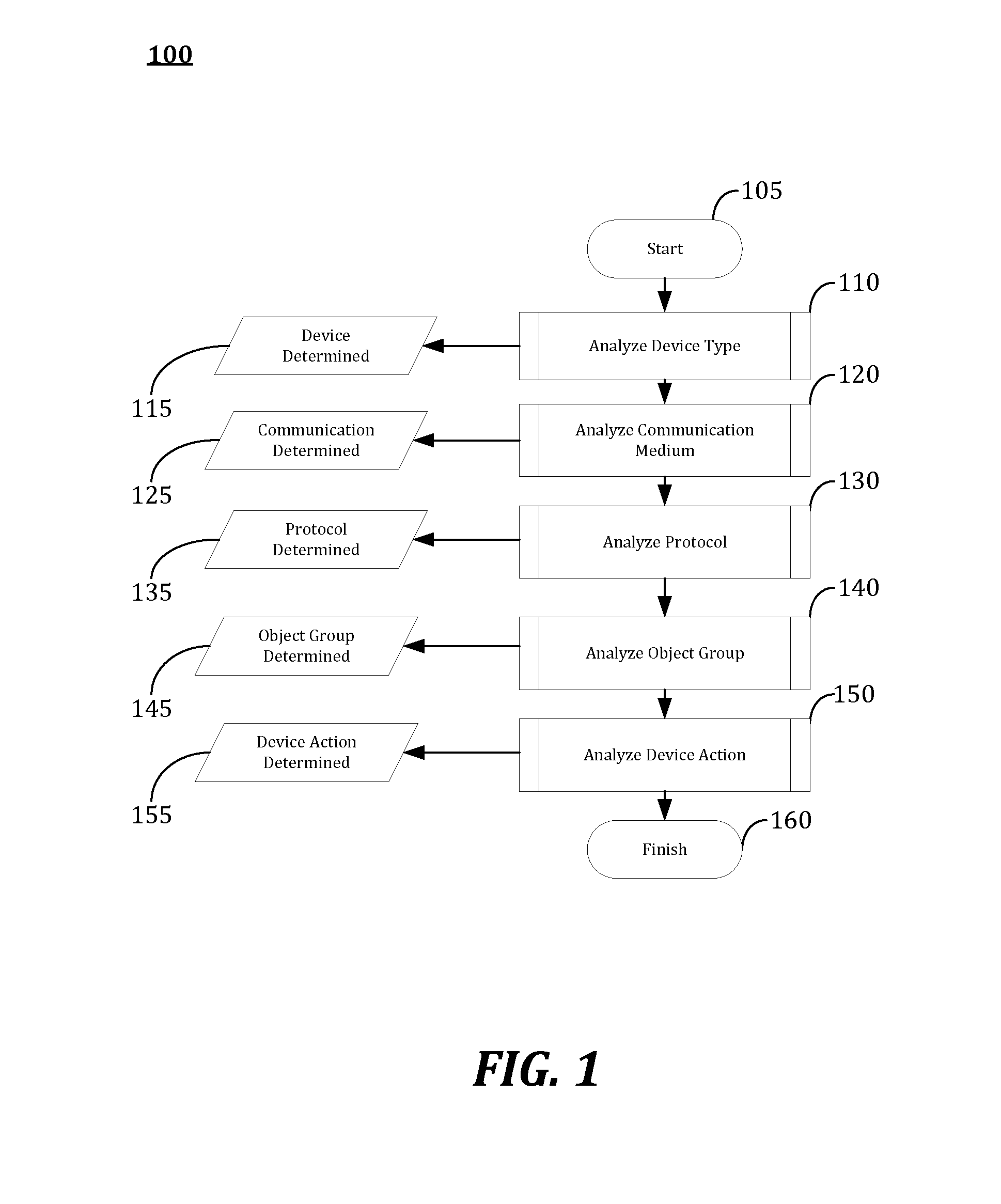
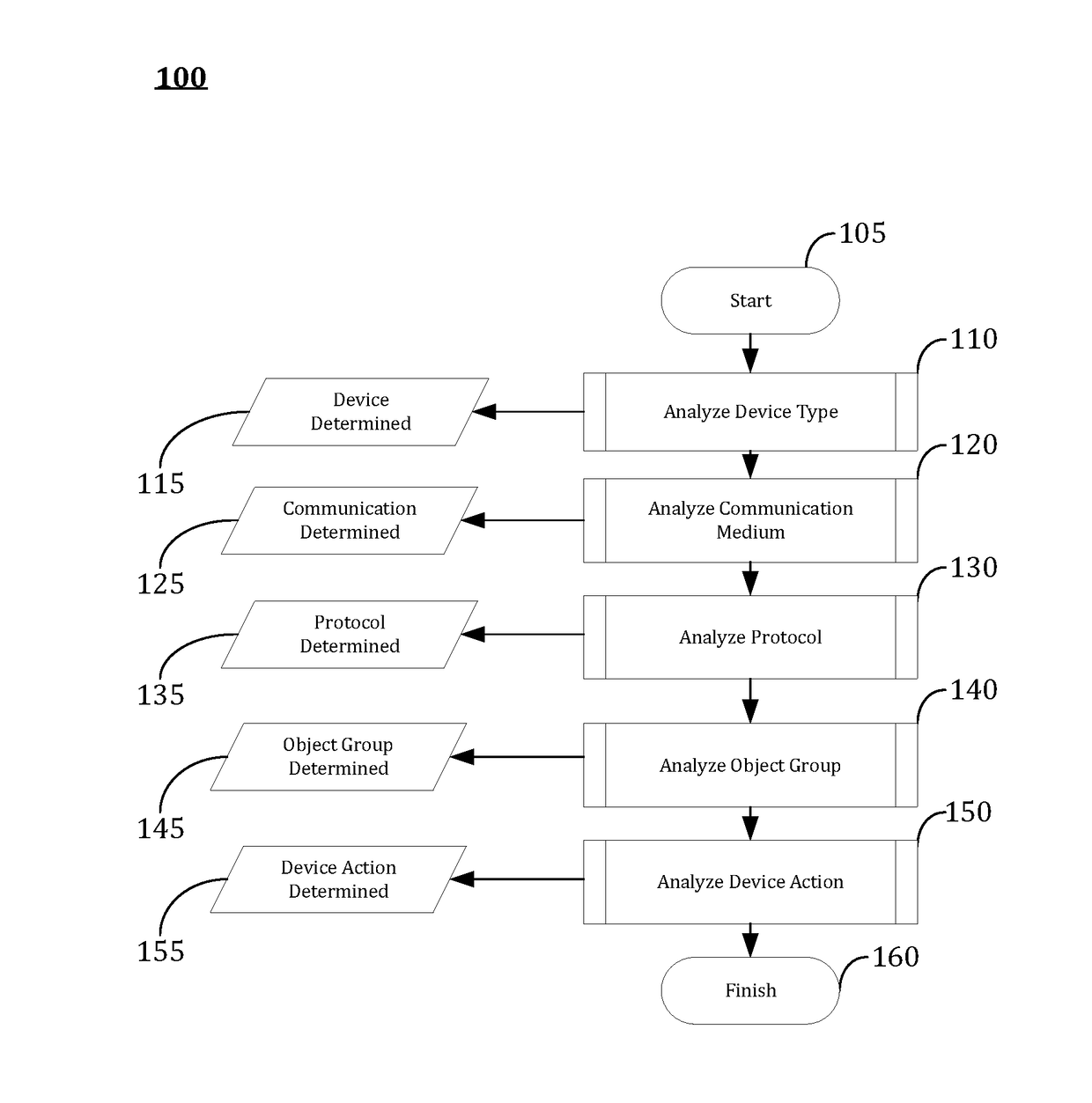
Industrial Control System Emulator for Malware Analysis
InactiveUS20150205966A1Improve defenseDisrupt operationMemory loss protectionError detection/correctionMalware analysisOil and natural gas
Embodiments of the present invention may provide an Industrial Control System (ICS) Emulator for Malware Analysis. The ICS Emulator may be embodied in a software. The software may be developed by testing and operating thousands of ICS devices that are used every day in critical infrastructure from power to oil & gas. Then, based on the tests and operations, the software may be configured to identify if, when, and how malware may be attacking various industrial control systems.
Owner:MALCRAWLER
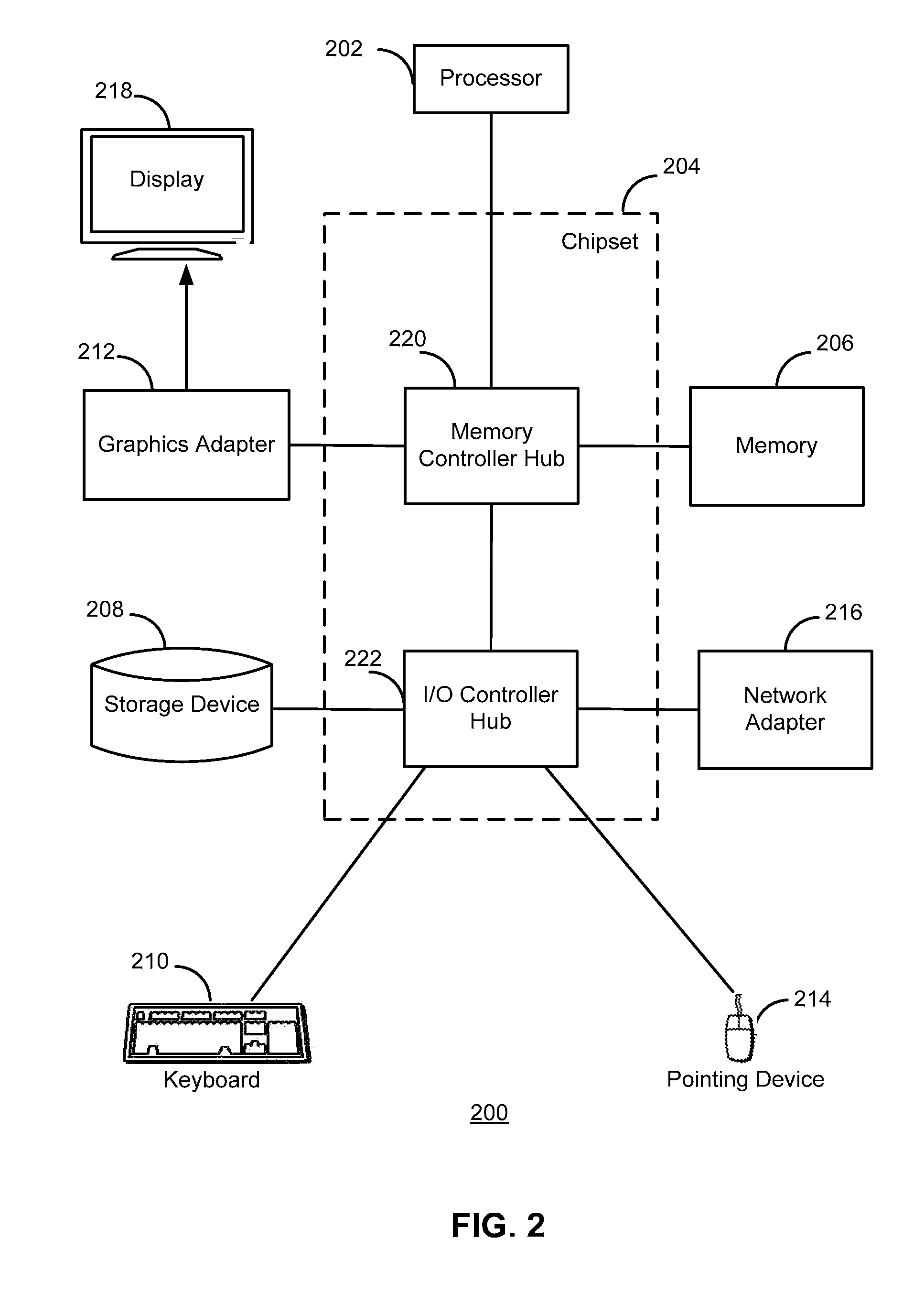
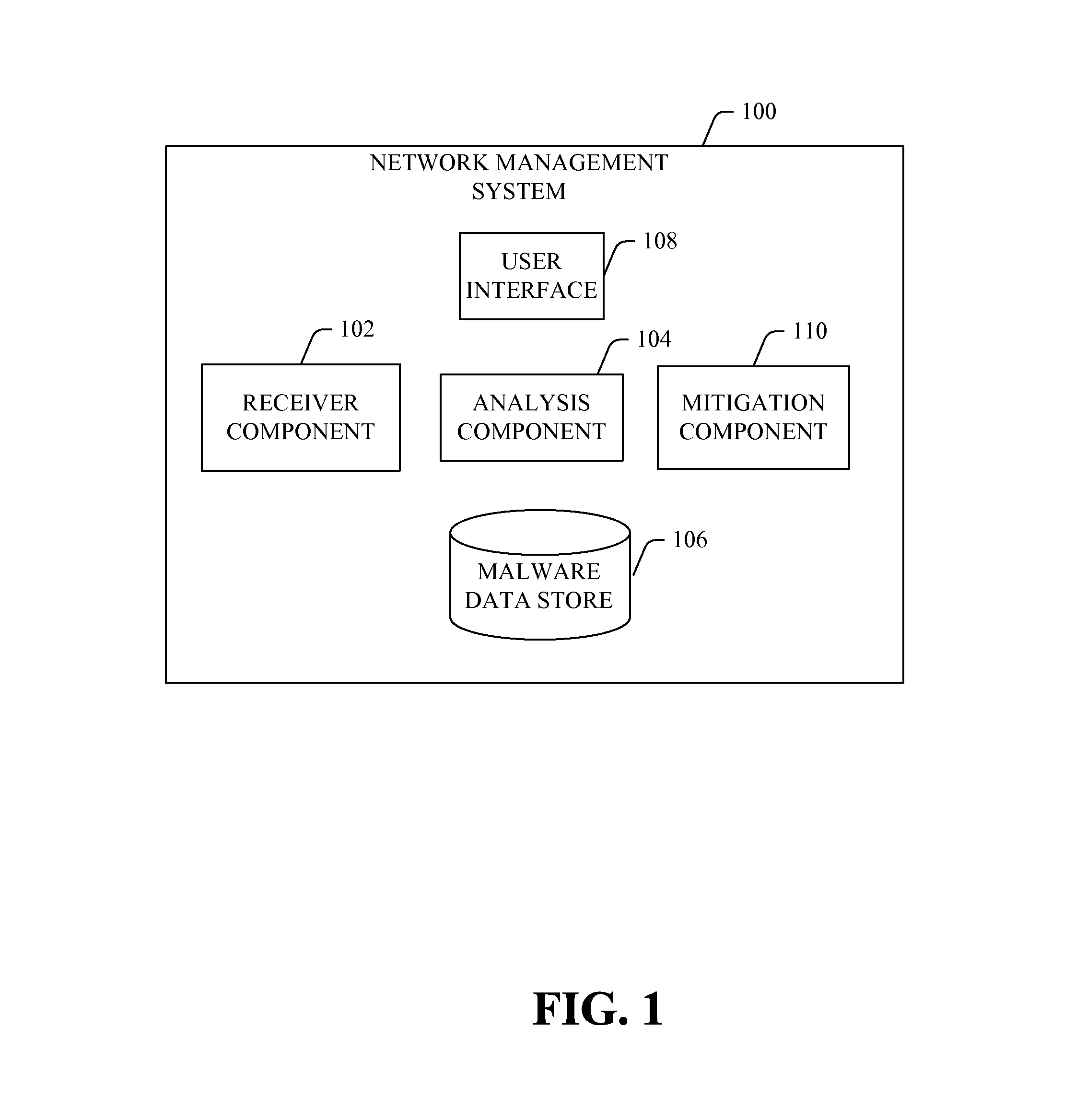
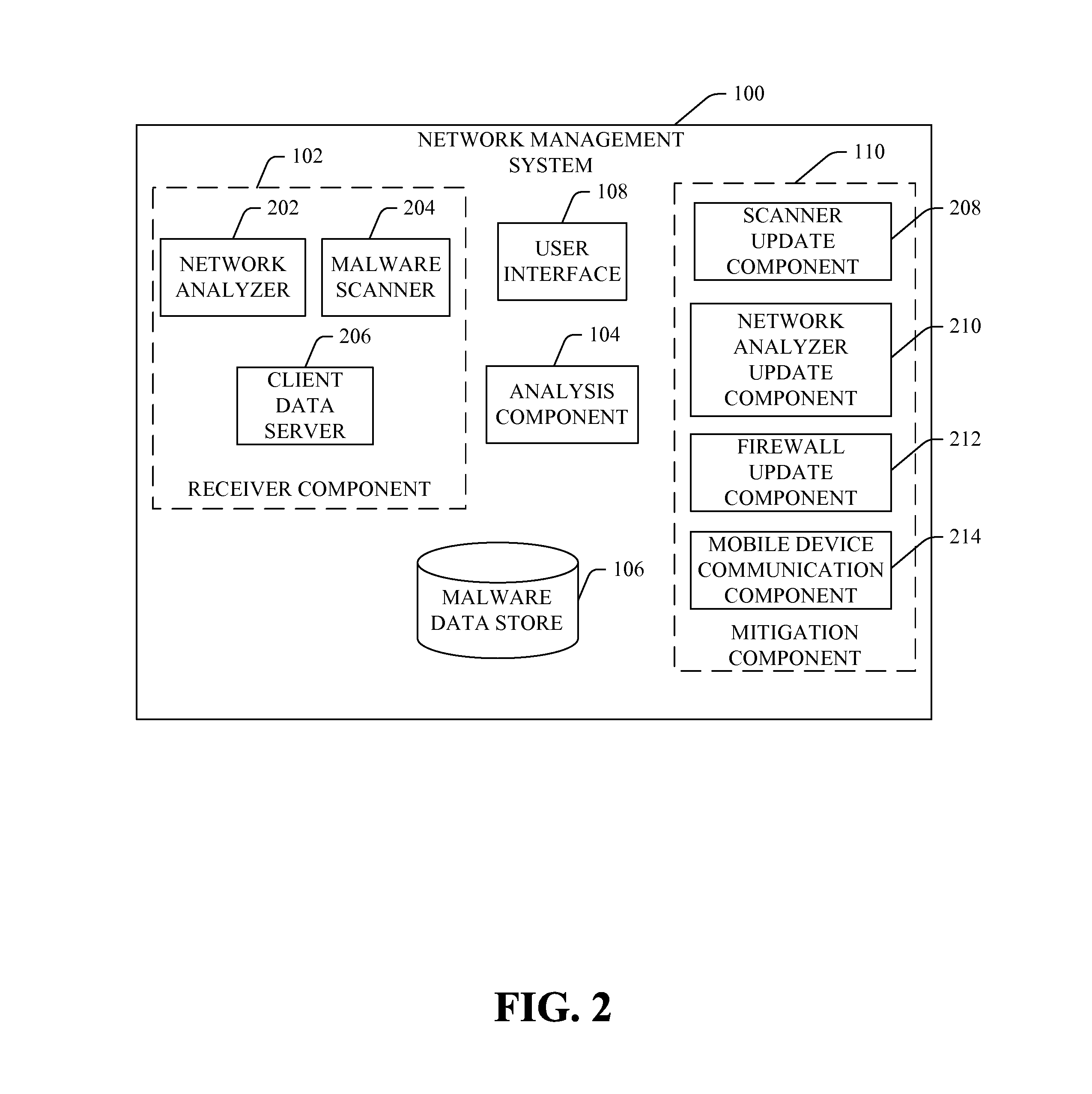
System and method of reporting and visualizing malware on mobile networks
InactiveUS9069957B2Raise the possibilityMemory loss protectionError detection/correctionMalware analysisMonitoring system
A network management system monitors malware within a mobile network. The system comprises a receiver component that obtains data regarding malware in the mobile network. The data is obtained from a first source and a second source, where the first source is of a different type than the second source. The monitoring system also includes an analysis component that generates a malware analysis of the mobile network as a function of the data.
Owner:JUMIPER NETWORKS INC
Malware target recognition
InactiveUS8756693B2Memory loss protectionDigital data processing detailsMalware analysisAnalysis method
Owner:THE UNITED STATES OF AMERICA AS REPRESETNED BY THE SEC OF THE AIR FORCE
Industrial Control System Emulator for Malware Analysis
InactiveUS20170177865A1Improve defenseDisrupt operationPlatform integrity maintainanceTransmissionMalware analysisOil and natural gas
Embodiments of the present invention may provide an Industrial Control System (ICS) Emulator for Malware Analysis. The ICS Emulator may be embodied in a software. The software may be developed by testing and operating thousands of ICS devices that are used every day in critical infrastructure from power to oil & gas. Then, based on the tests and operations, the software may be configured to identify if, when, and how malware may be attacking various industrial control systems.
Owner:MALCRAWLER
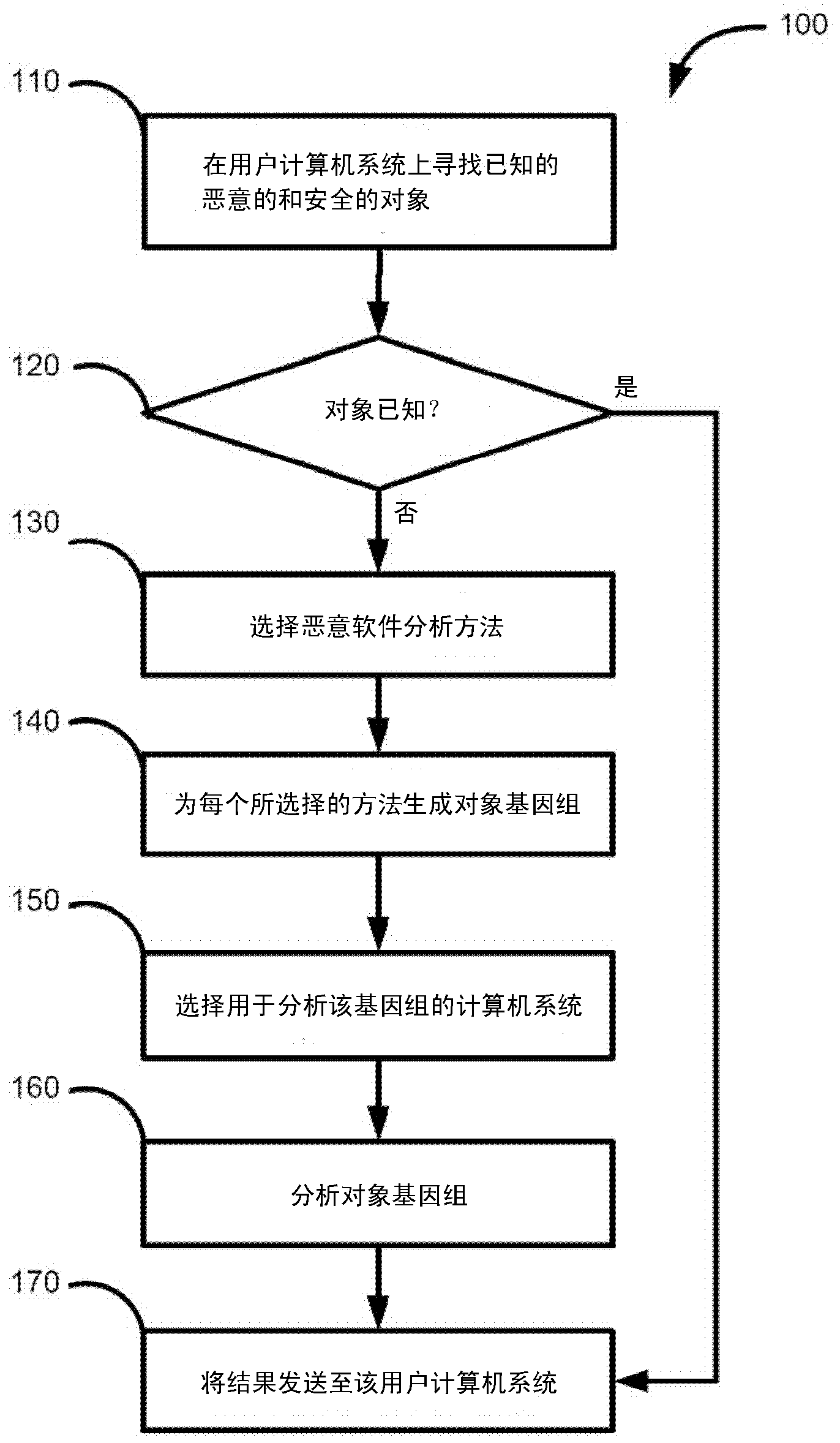
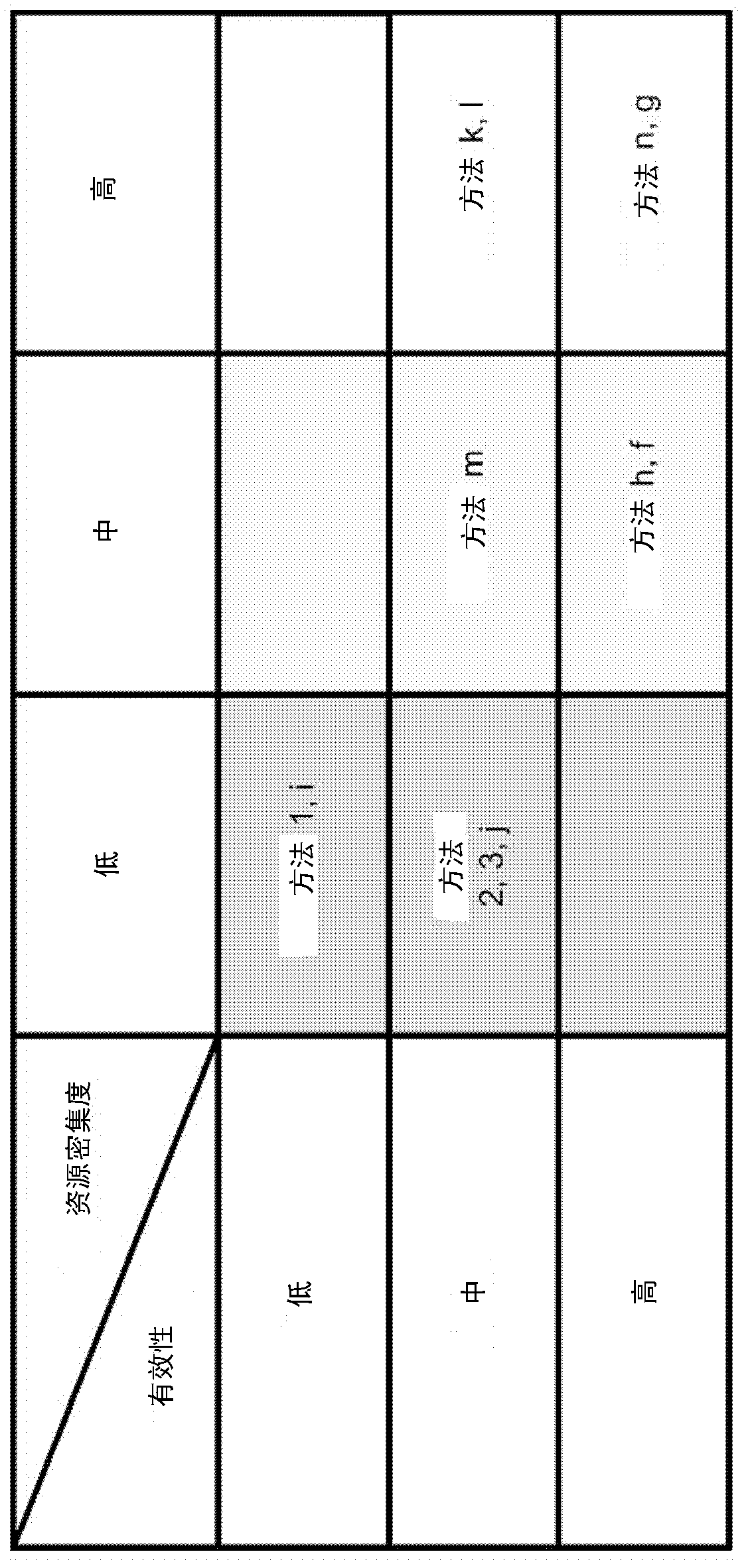
System and method for detecting unknown malware
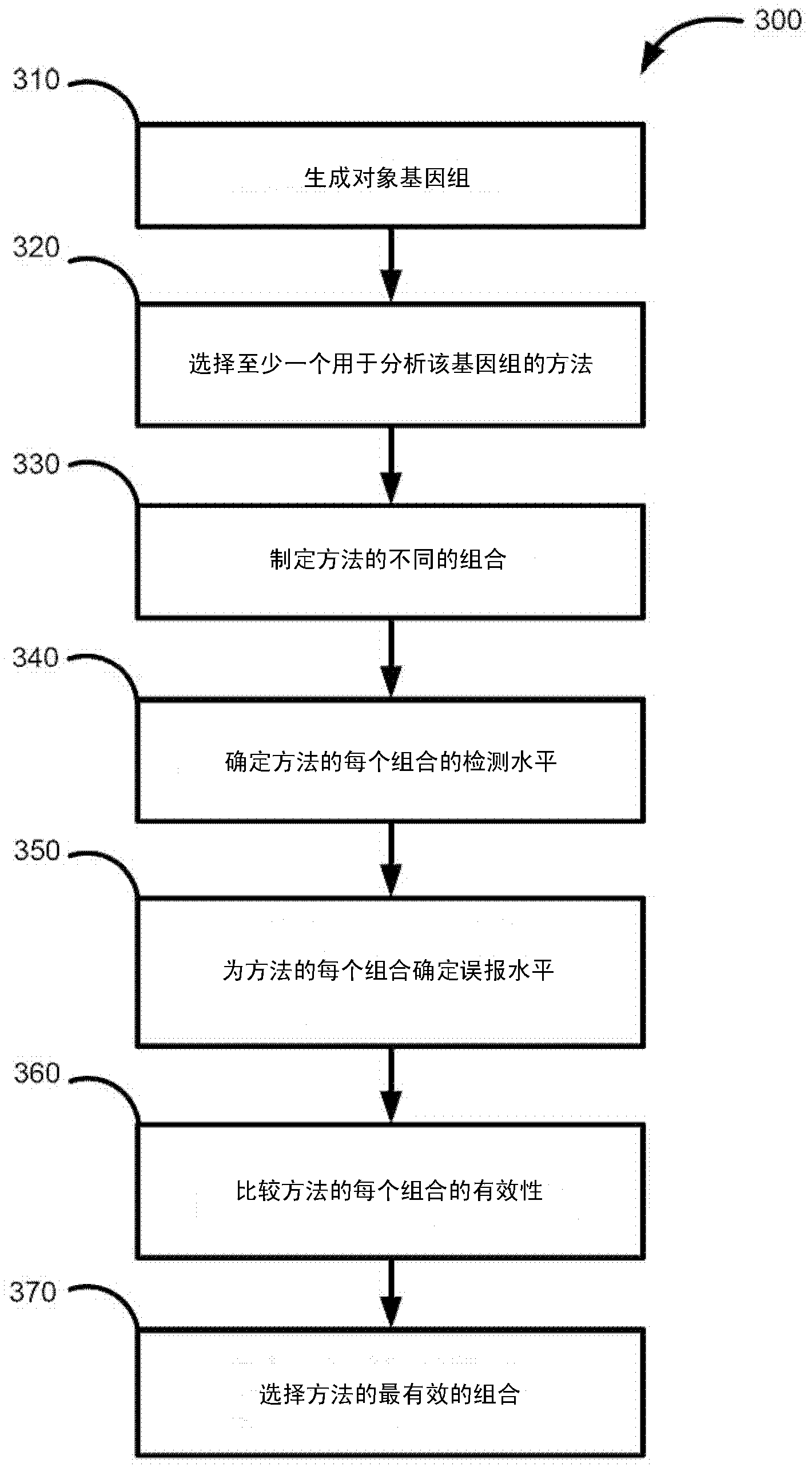
Disclosed are systems, methods and computer program products for detecting unknown malware. A method comprises generating genes for known malicious and clean objects; analyzing object genes using different malware analysis methods; computing a level of successful detection of malicious objects by one or a combination of malware analysis methods based on analysis of genes of the known malicious objects; computing a level of false positive detections of malicious objects by one or a combination of malware analysis methods based on analysis of genes of known clean objects; measuring effectiveness of each one or the combination of malware analysis methods as a function of the level of successful detections and the level of false positive detections; and selecting one or a combination of the most effective malware analysis methods for analyzing unknown object for malware.
Owner:AO KASPERSKY LAB
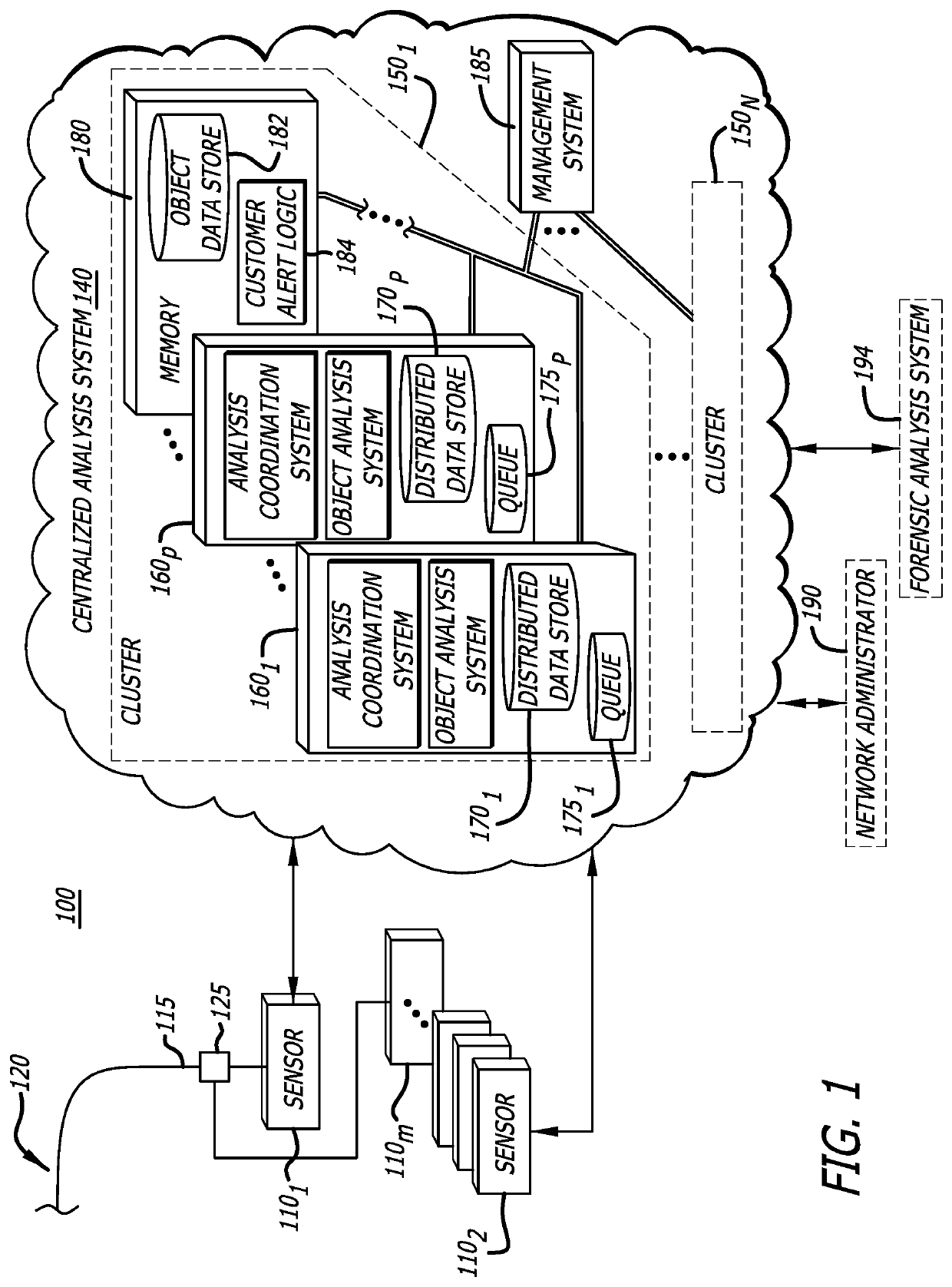
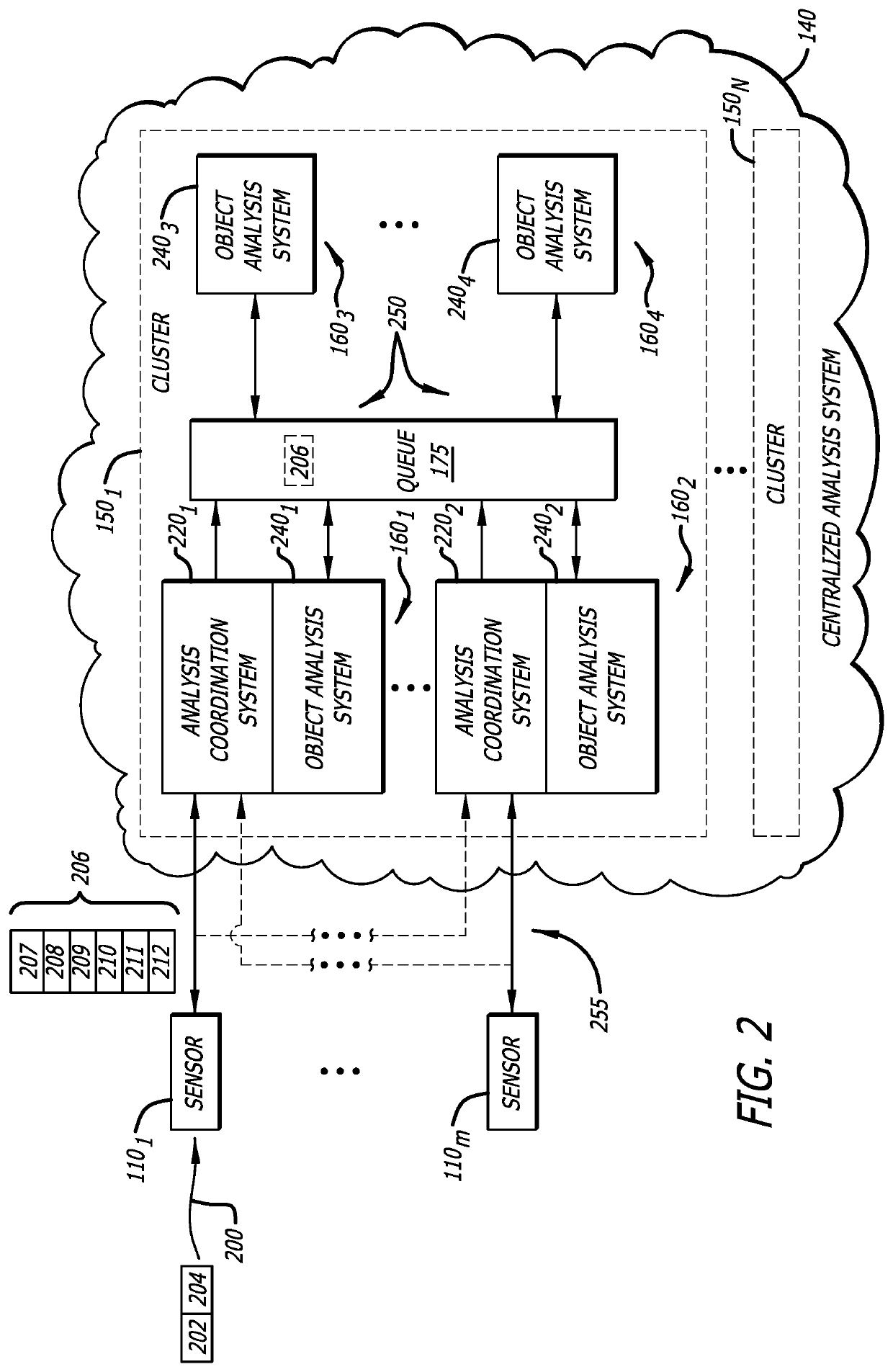
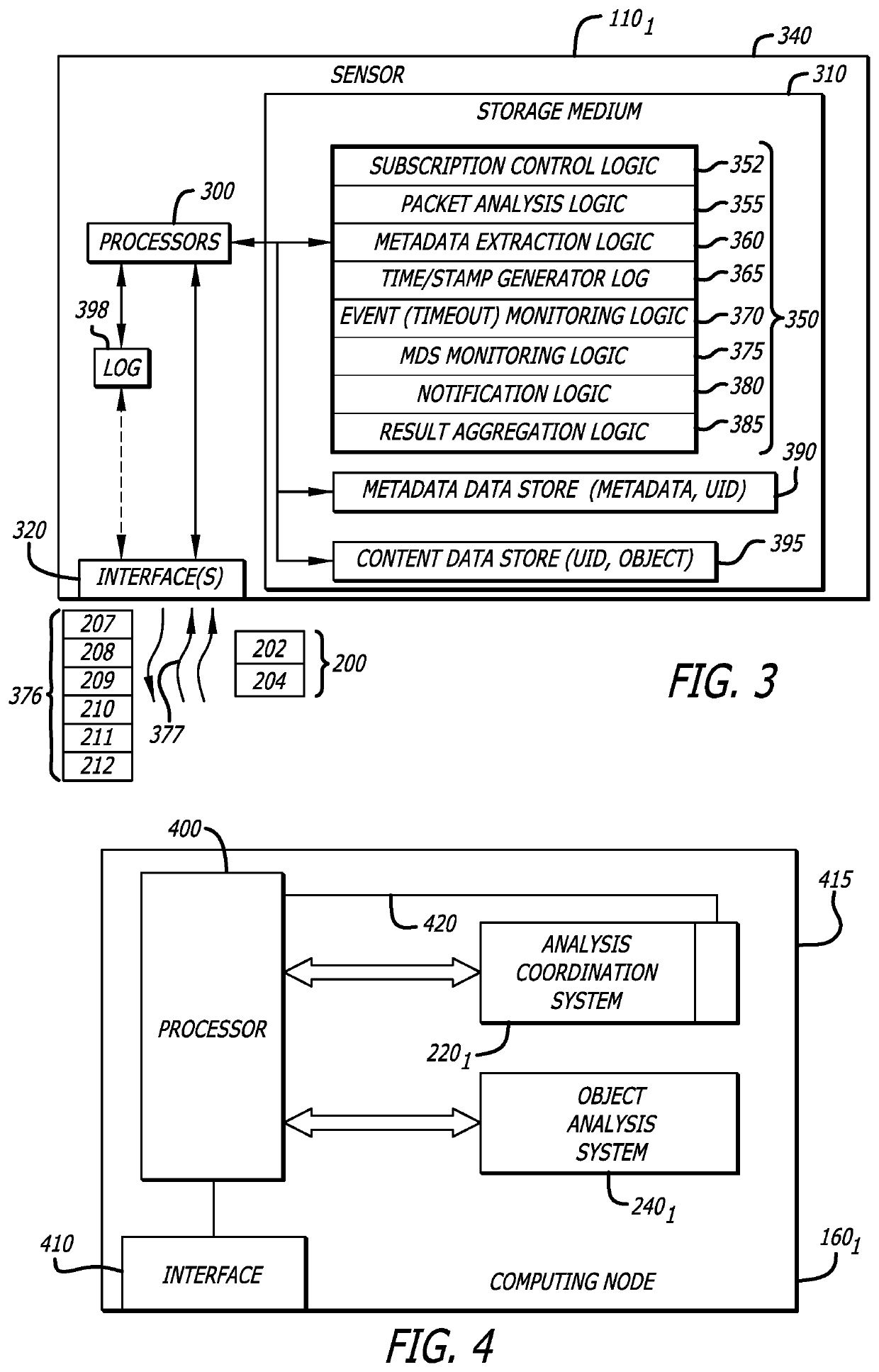
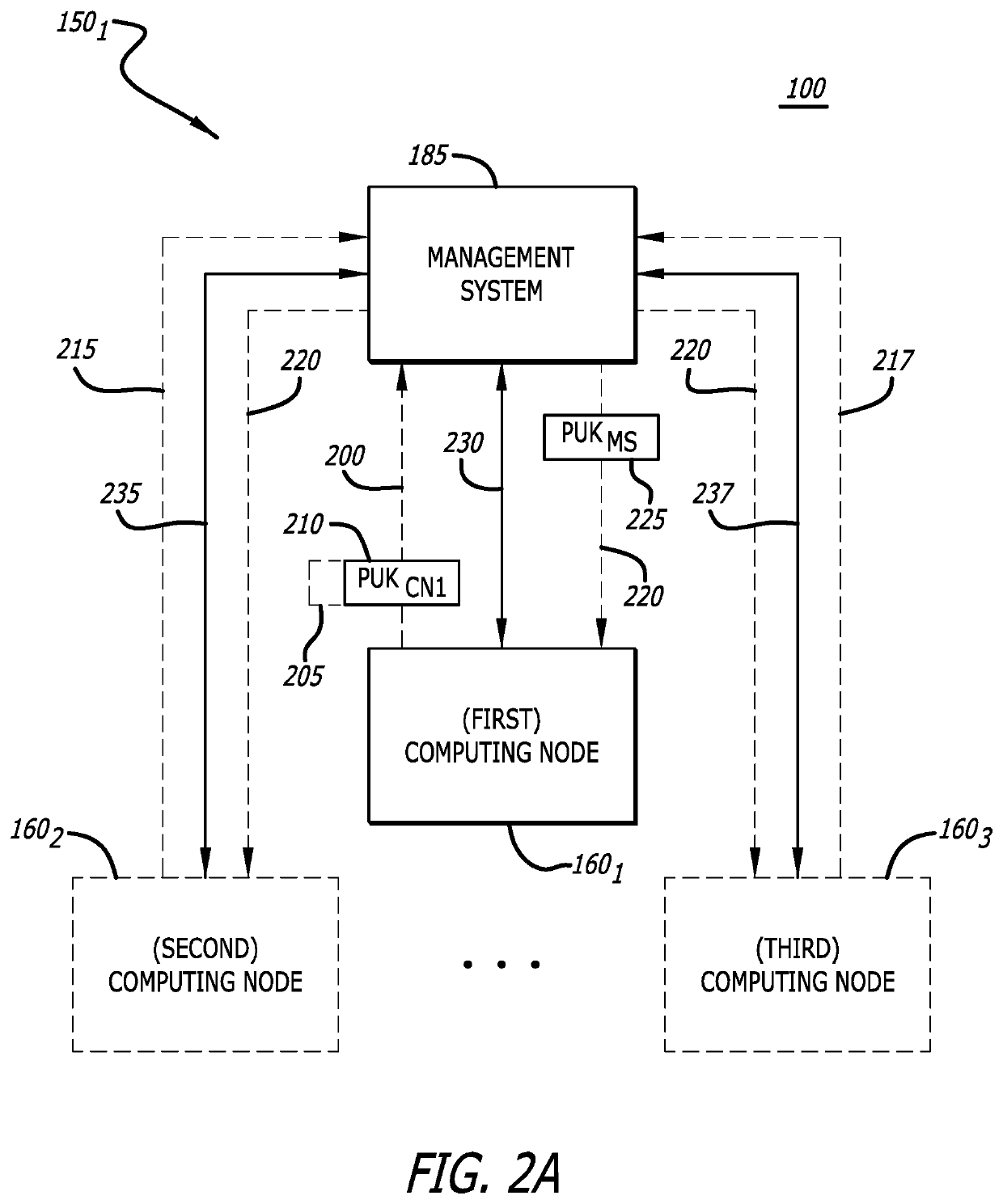
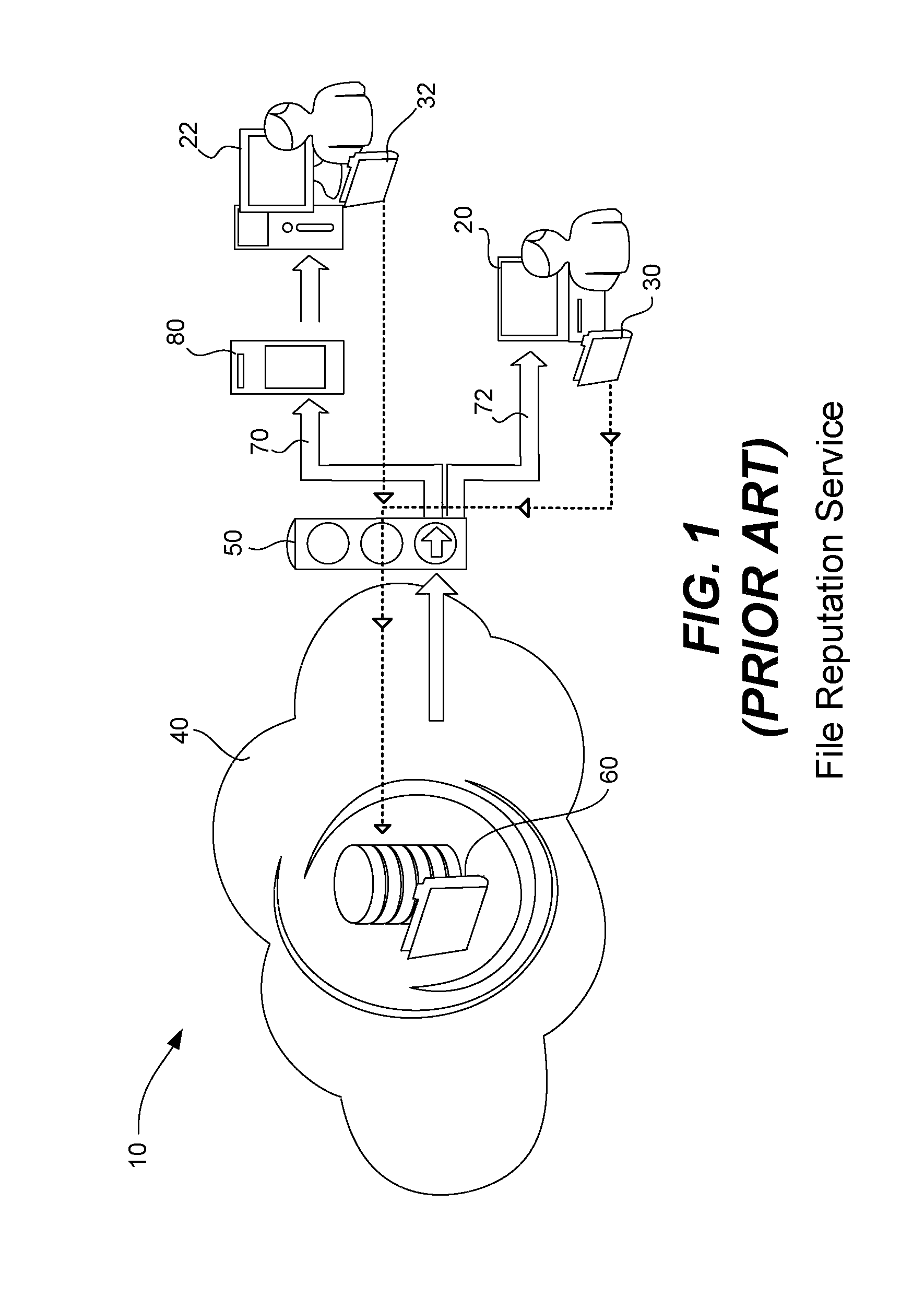
Distributed malware detection system and submission workflow thereof
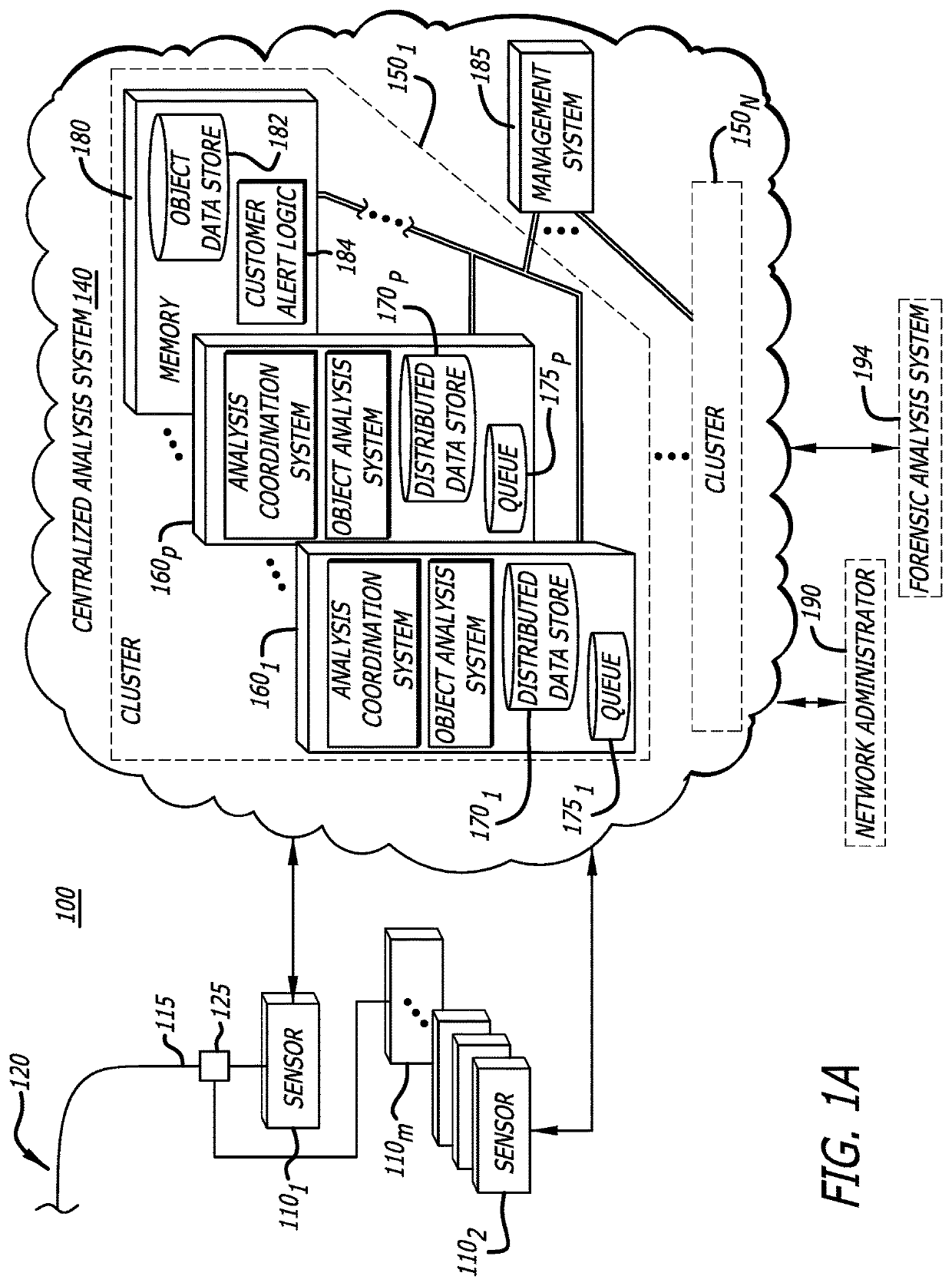
A submission process for a malware detection system including one or more sensors and a cluster including one or more computing nodes is described. The process includes the sensor that determines whether a prior malware analysis has been conducted on any previously submitted object matching the object under analysis. If not, the process determines whether the object is suspicious, namely a first probability of the first object being associated with malware. If suspicious, metadata associated with the suspicious object is sent to an analysis coordinator of a first computing node of the cluster. The metadata is used in determining whether a prior malware analysis has been previously conducted within the cluster on any object that matches the suspicious object. The metadata is also used in fetching, by an object analyzer of the same or a different computing node of the cluster, the suspicious object from the sensor for malware analysis.
Owner:FIREEYE SECURITY HLDG US LLC
System and methods for sandboxed malware analysis and automated patch development, deployment and validation
A system and methods for sandboxed malware analysis and automated patch development, deployment and validation, comprising a business operating system, vulnerability scoring engine, binary translation engine, sandbox simulation engine, at least one network endpoint, at least one database, a network, and a combination of machine learning and vulnerability probing techniques, to analyze software, locate any vulnerabilities or malicious behavior, and attempt to patch and prevent undesired behavior from occurring, autonomously.
Owner:QOMPLX INC
Launcher for setting analysis environment variations for malware detection
ActiveUS10834107B1Error detection/correctionUnauthorized memory use protectionMalware analysisRobust analysis
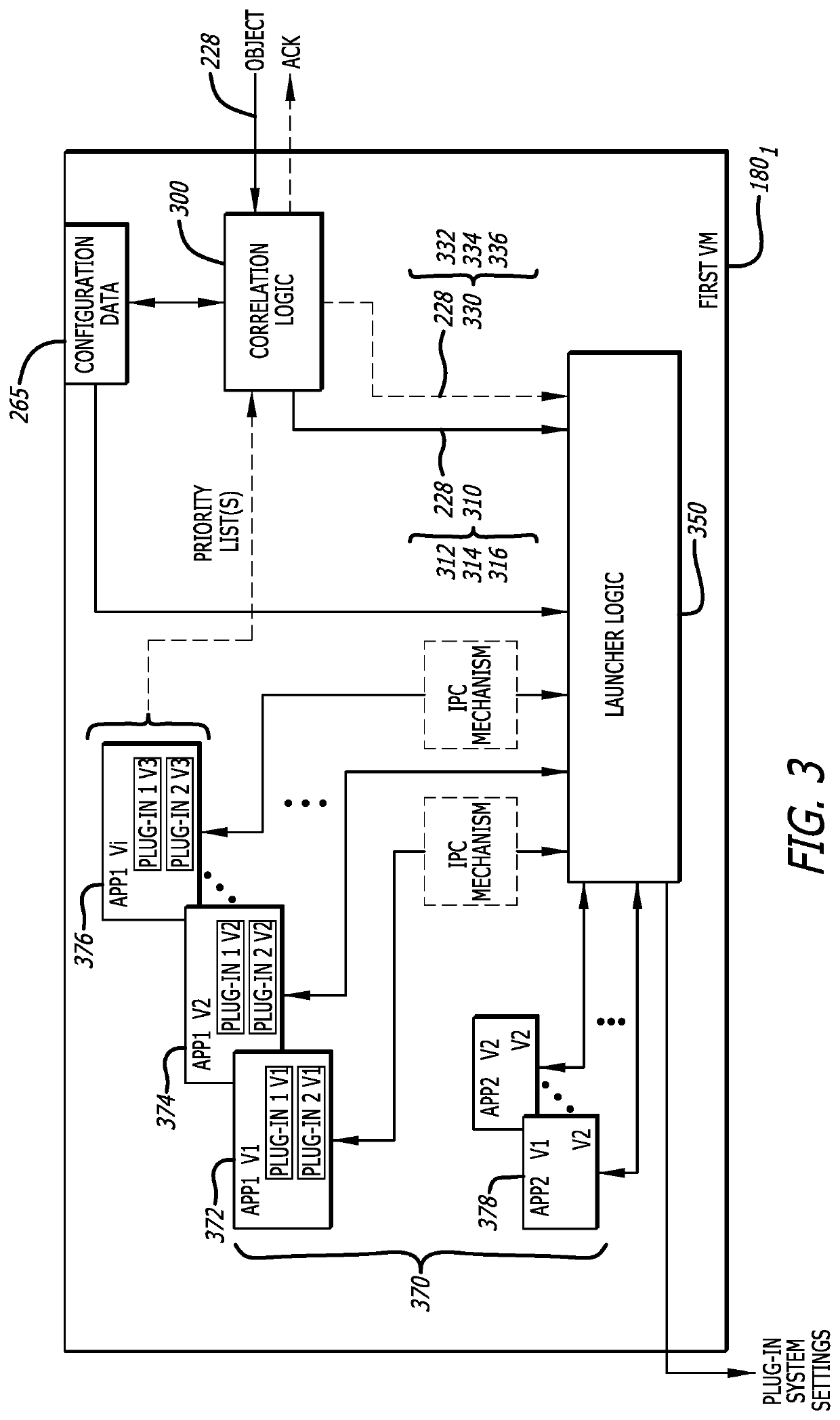
A system and method for automatically analyzing an object for malware is described. Operating one or more virtual machines, the system and method provide an analysis environment variation framework to provide a more robust analysis of an object for malware. The multi-application, multi-plugin processing framework is configured within a virtual machine, where the framework for configuring a plurality of processes for analyzing the object for malware and each of plurality of processes is configured with a different application and plug-in combination selected based in part on a type of object being analyzed and operating concurrently with each other.
Owner:FIREEYE SECURITY HLDG US LLC
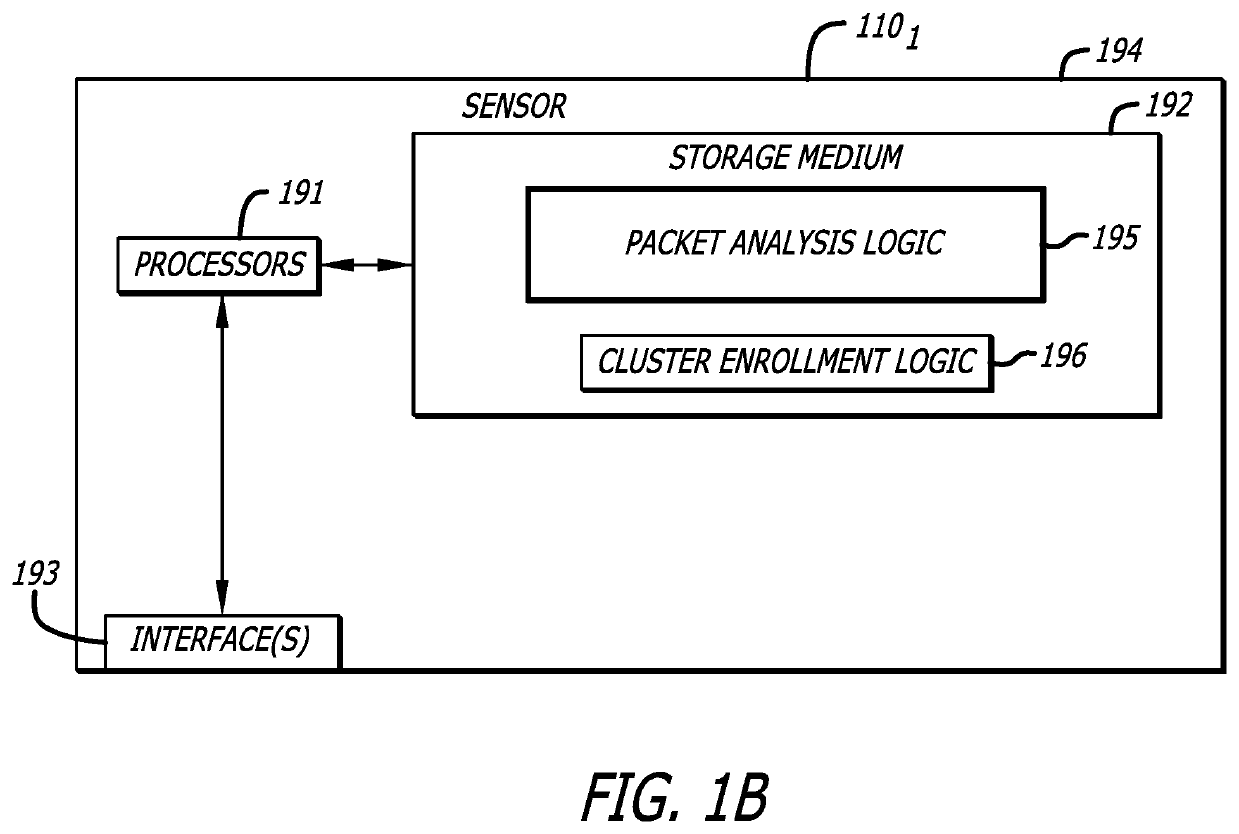
System and method for managing sensor enrollment
Sensor enrollment management is conducted where features and capabilities for one or more broker computing nodes within the cluster are received by an enrollment service operating within a management system. The enrollment service is configured to receive advertised features and capabilities for computing nodes that are part of a cluster and provide address information associated with the enrollment service to the sensor. Based on information supplied by the sensor, the enrollment service authenticates the sensor, and upon authentication, forwards keying material associated with the sensor to a computing node selected that is selected for supporting communications to the cluster from the sensor. Also, the enrollment service provides a portion of the advertised features and capabilities associated with the computing node to the sensor to enable the sensor to establish a secure communication path with the computing node for malware analysis of suspicious objects within network traffic monitored by the sensor.
Owner:FIREEYE SECURITY HLDG US LLC
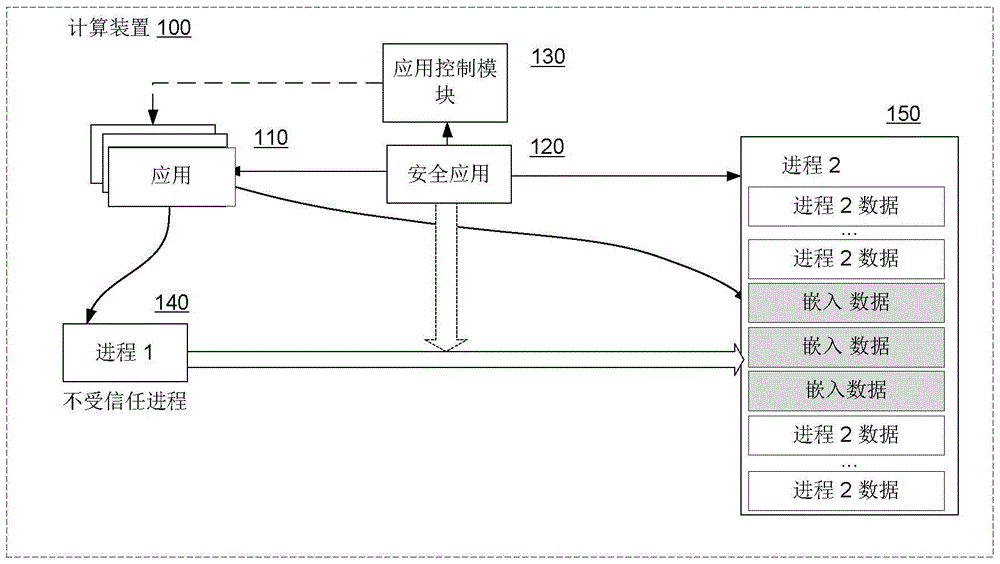
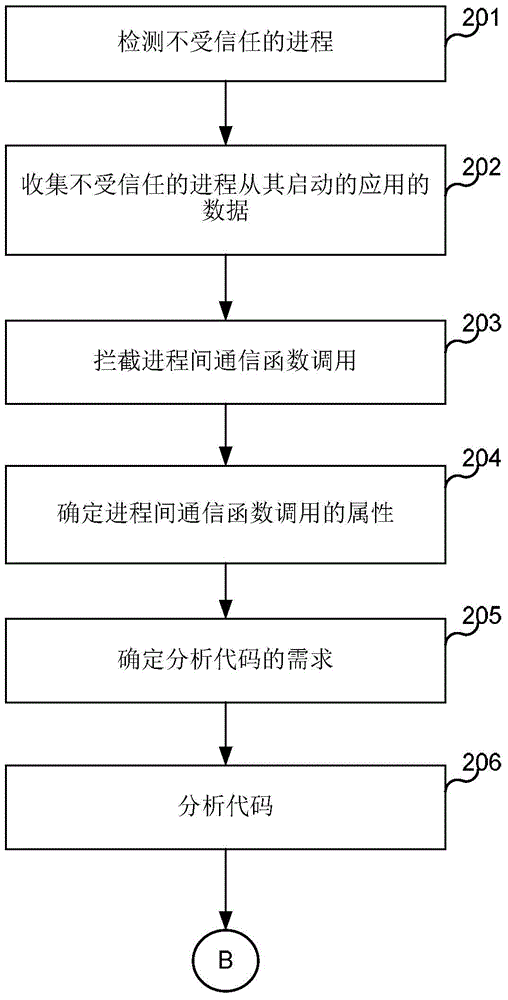
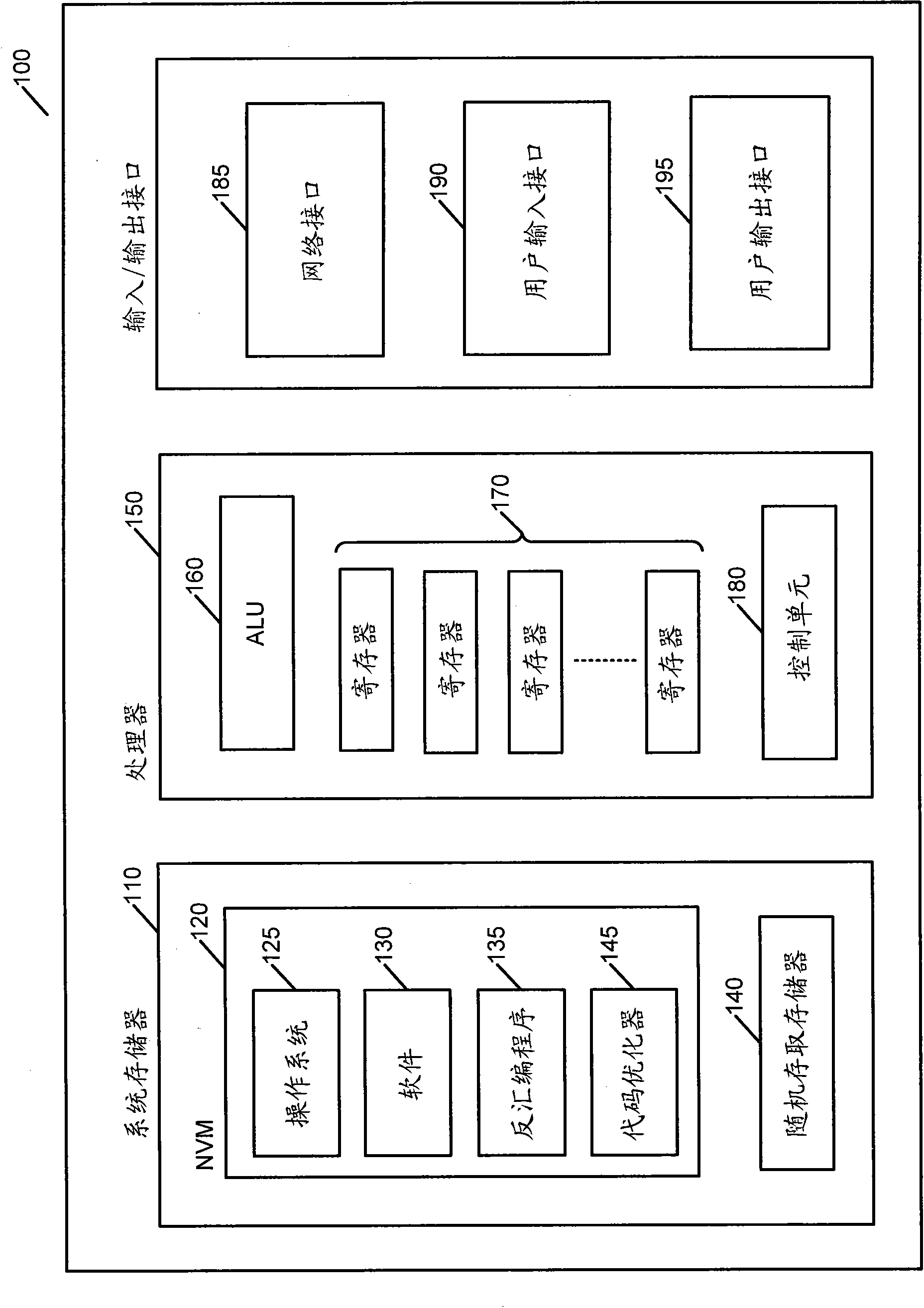
System and method used for detecting malicious code of random access memory
ActiveCN105760787AInternal/peripheral component protectionPlatform integrity maintainanceAnti virusMalware analysis
The invention discloses a system and a method used for detecting malicious code of a random access memory. The embodiment is characterized in that a hardware processor is used to detect the process of the untrusted application; the hardware processor is used to identify the function call including the inter-process function call from the generating of the process to the target process generated by the process of the untrusted application; the hardware processor is used to determine whether the execute the malicious software analysis executing the code in the address space of the target process called by the inter-process function generated by the process of the untrusted application; when the malicious software analysis is decided to be executed, the anti-virus software executed by the hardware processor can be used to analyze the code in the address space of the target process called by the inter-process function generated by the process of the untrusted application.
Owner:KASPERSKY LAB ZAO
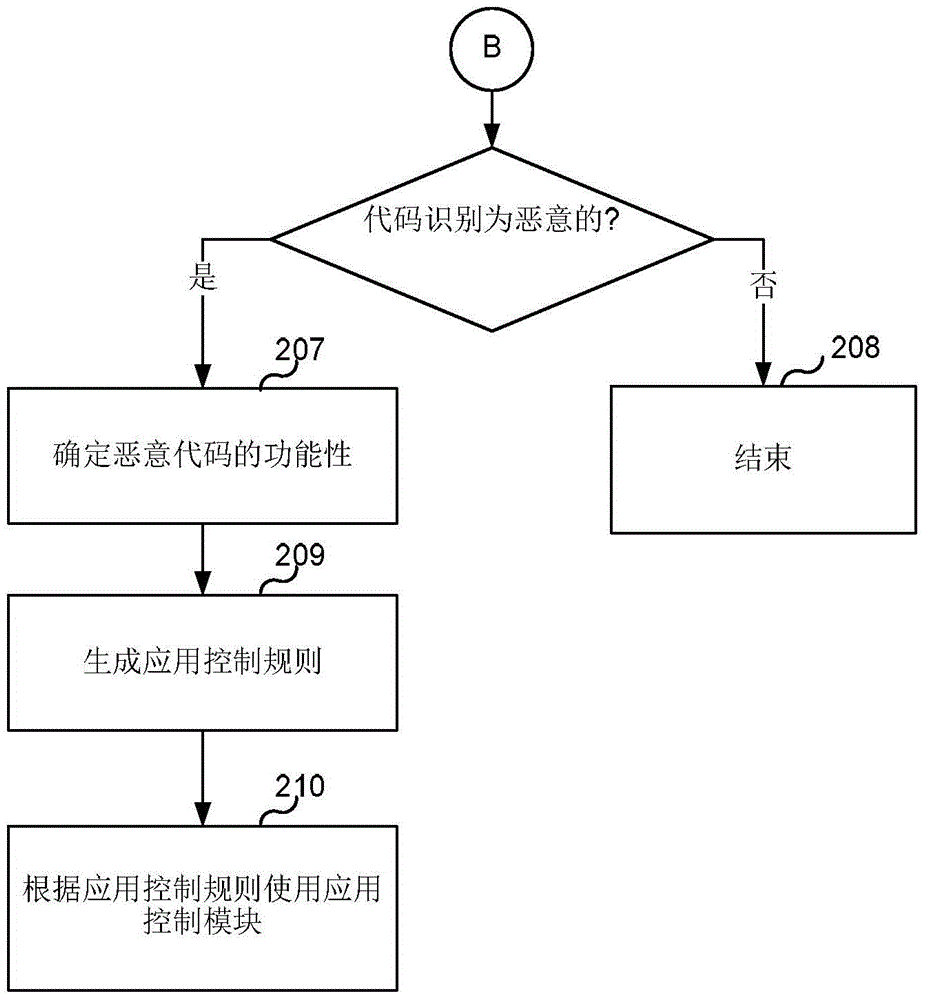
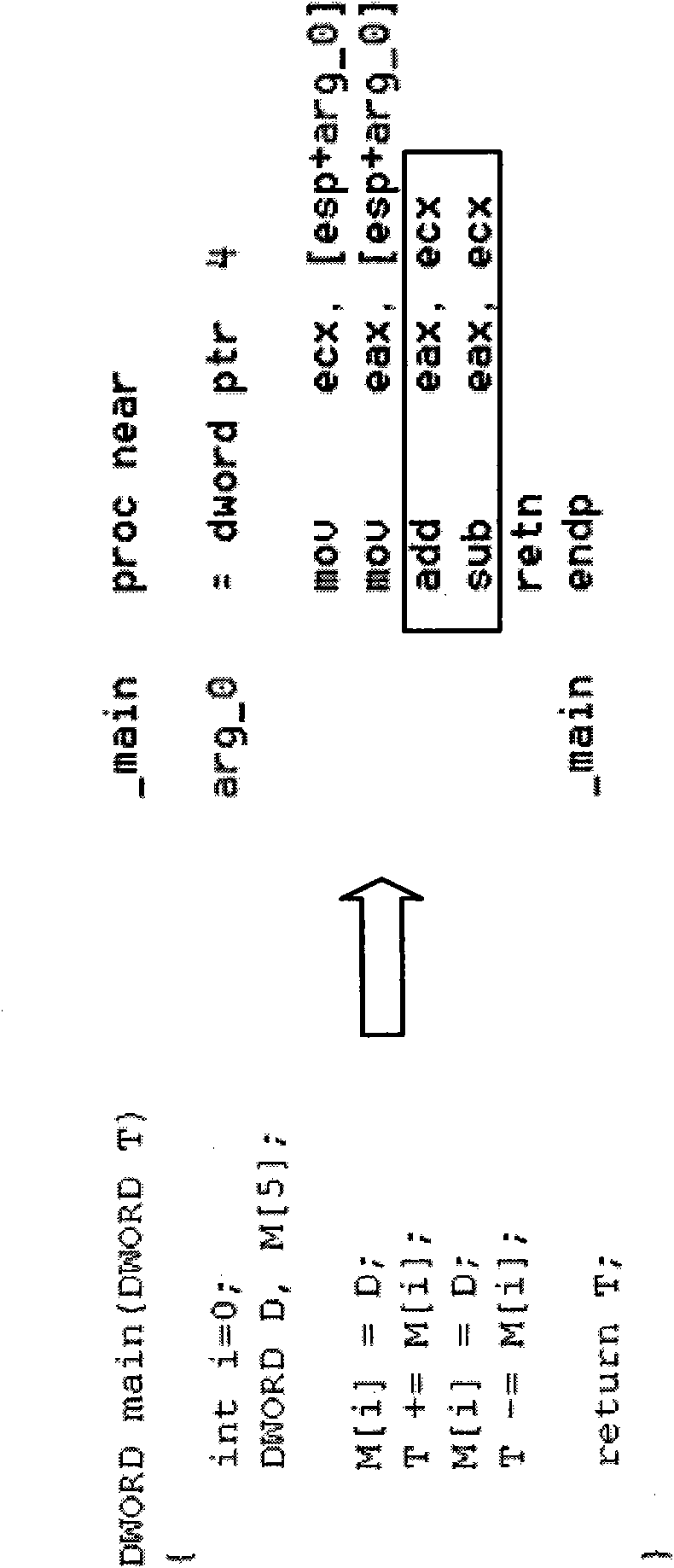
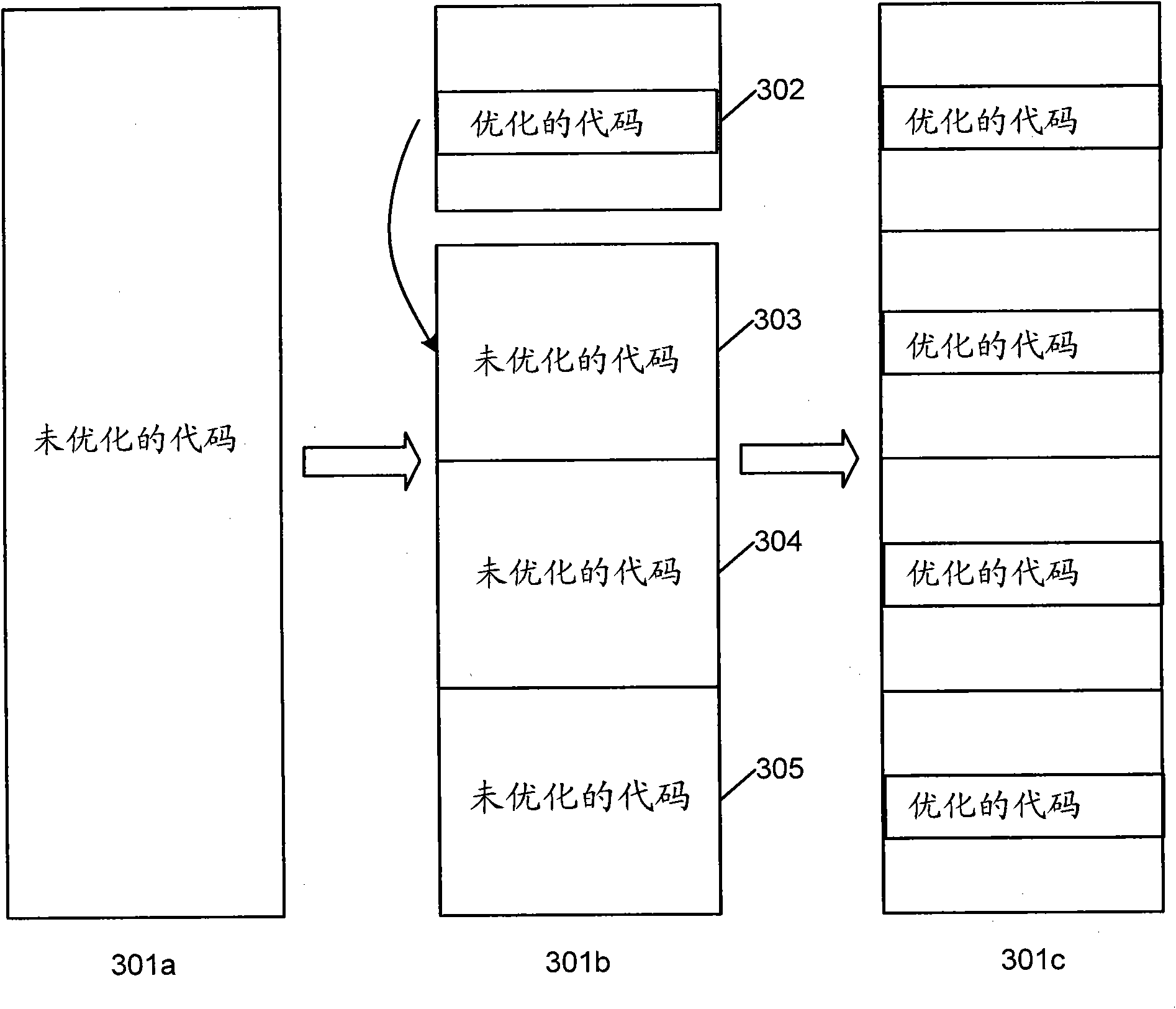
Systems and methods for detecting obfuscated malware
Disclosed are systems, methods and computer program products for efficient and reliable analysis, optimization and detection of obfuscated malware. One disclosed example method for malware detection includes loading an executable software code on a computer system and disassembling the software code into an assembly language or other low-level programming language. The method then proceeds to simplifying complex assembly instructions and constructing a data flow model of the simplified software code. The dependencies and interrelations of code elements of the data flow model are analyzed to identify obfuscated software codes therein. The identified obfuscated codes are then optimized. Based on the results of optimization, determination is made whether the software code is malicious and / or whether further antimalware analysis of the optimized software code is necessary.
Owner:AO KASPERSKY LAB
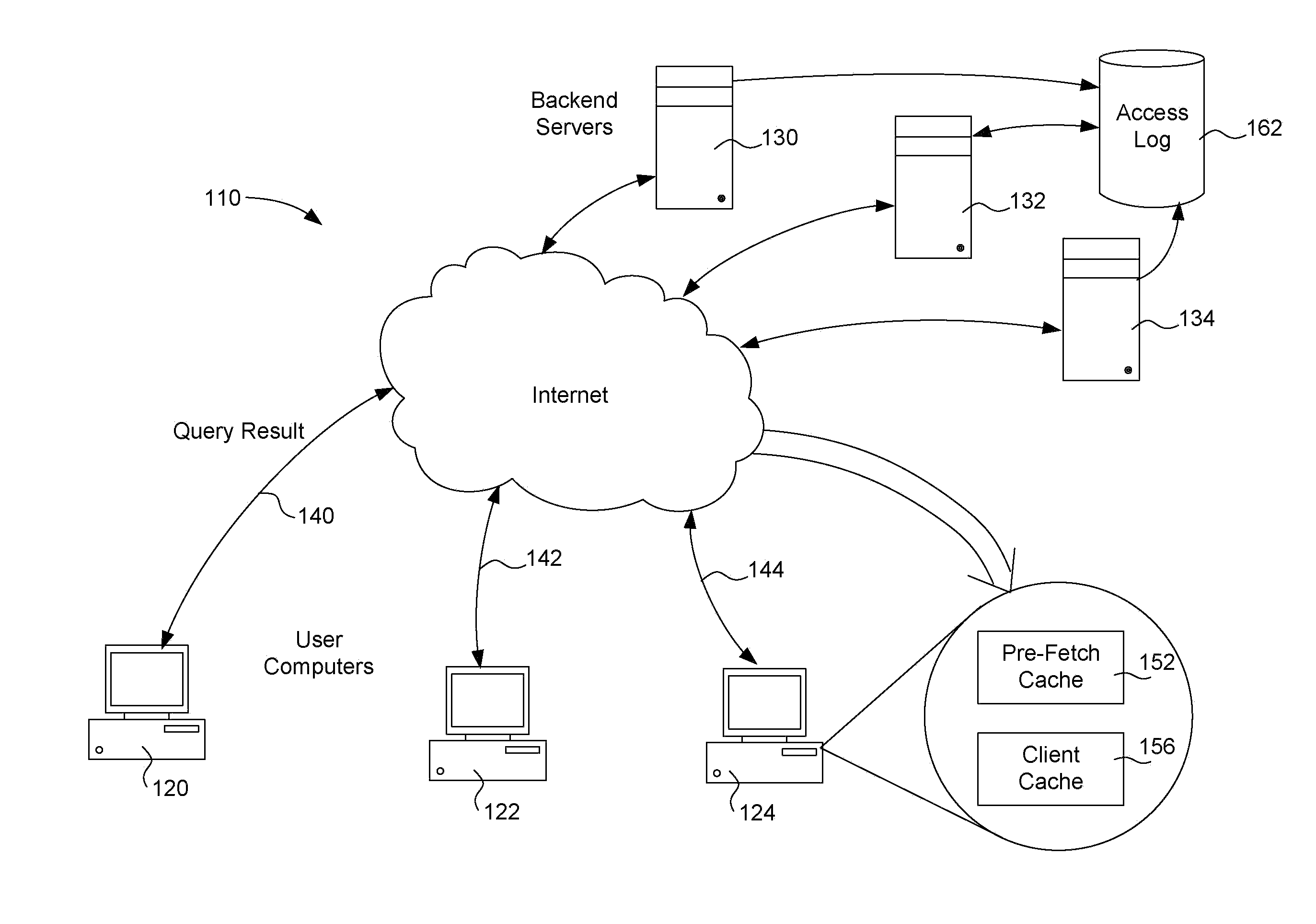
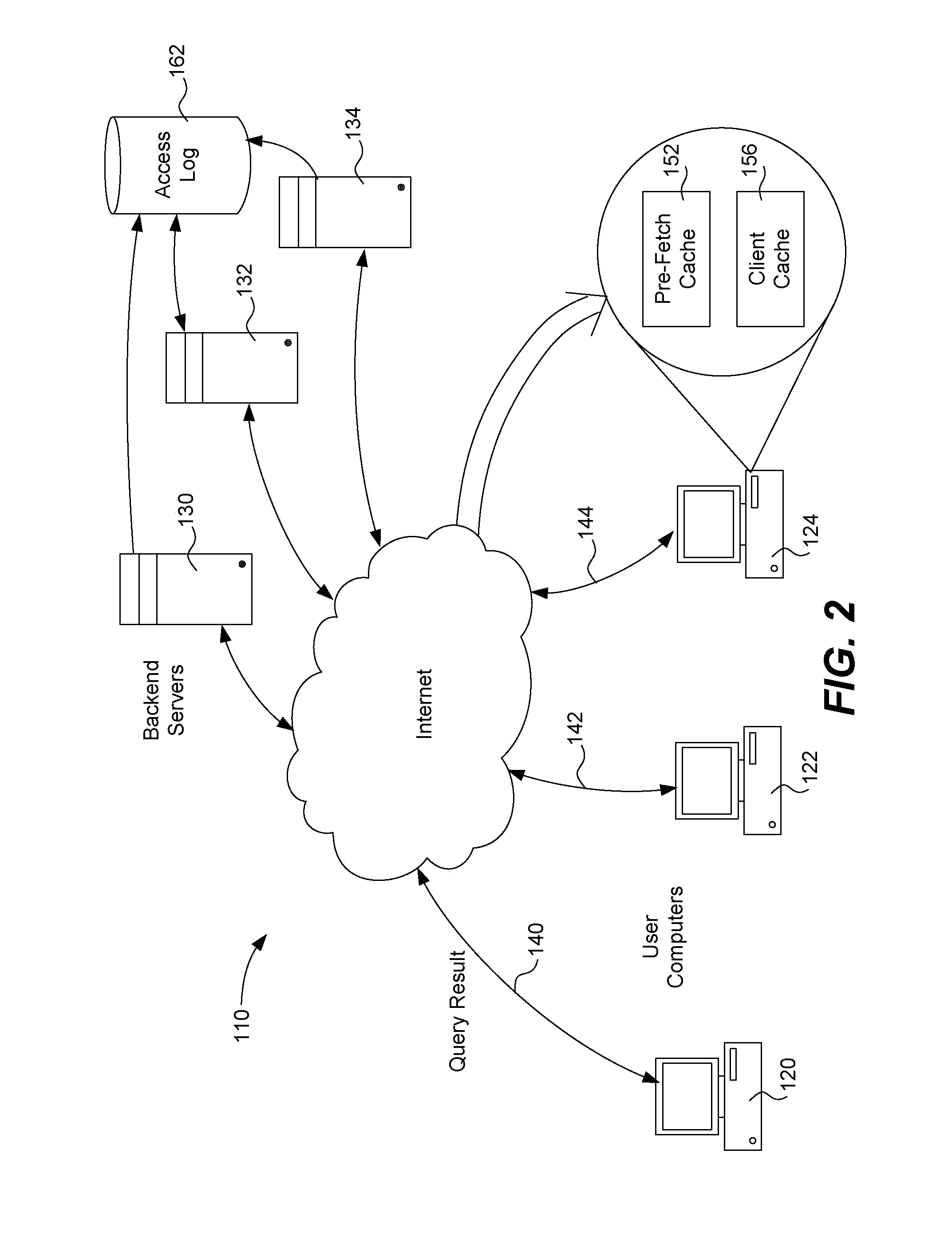
Network traffic reduction
ActiveUS8769691B1Reducing network environment overheadLow costMemory loss protectionDigital data processing detailsMalware analysisBack end server
A server access log includes data records each describing a previous query regarding a suspect computer file of a client computer. Each record includes the CRC code for the suspect computer file, the result of the malware analysis performed on the backend server and other attributes and values. The log is analyzed to retrieve relevant attributes and values from each record. Key attributes and values are generated such as region and continuous query. All CRC codes are grouped according to attribute values. Each group is analyzed to determine the network traffic associated with downloading the entire group to all user computers and the network traffic associated with not downloading the group but responding to future malware queries regarding CRC codes in the group. CRC codes are removed from each group if necessary. CRC code-result pairs for each group are downloaded to all user computers as a pre-fetch cache.
Owner:TREND MICRO INC
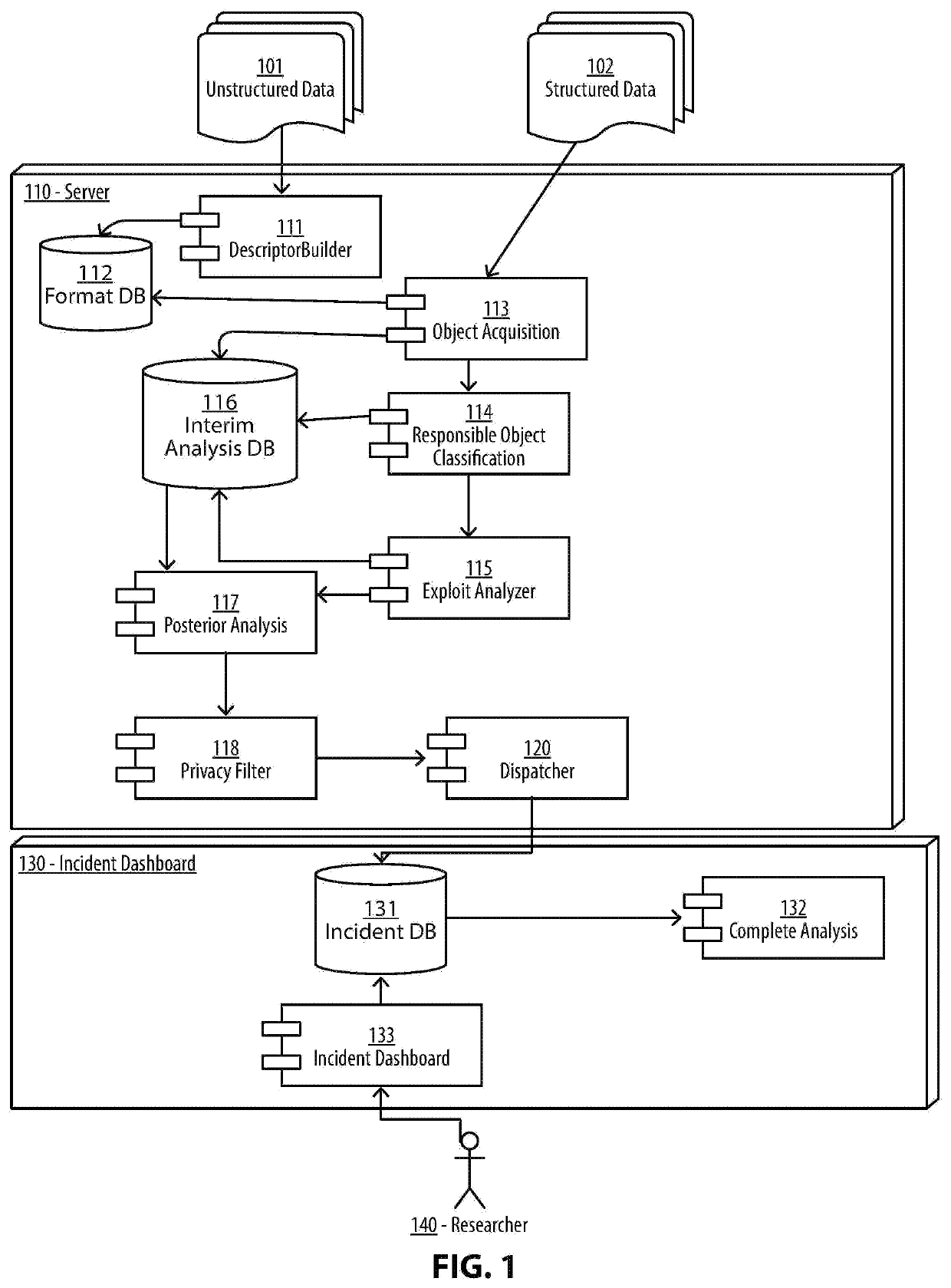
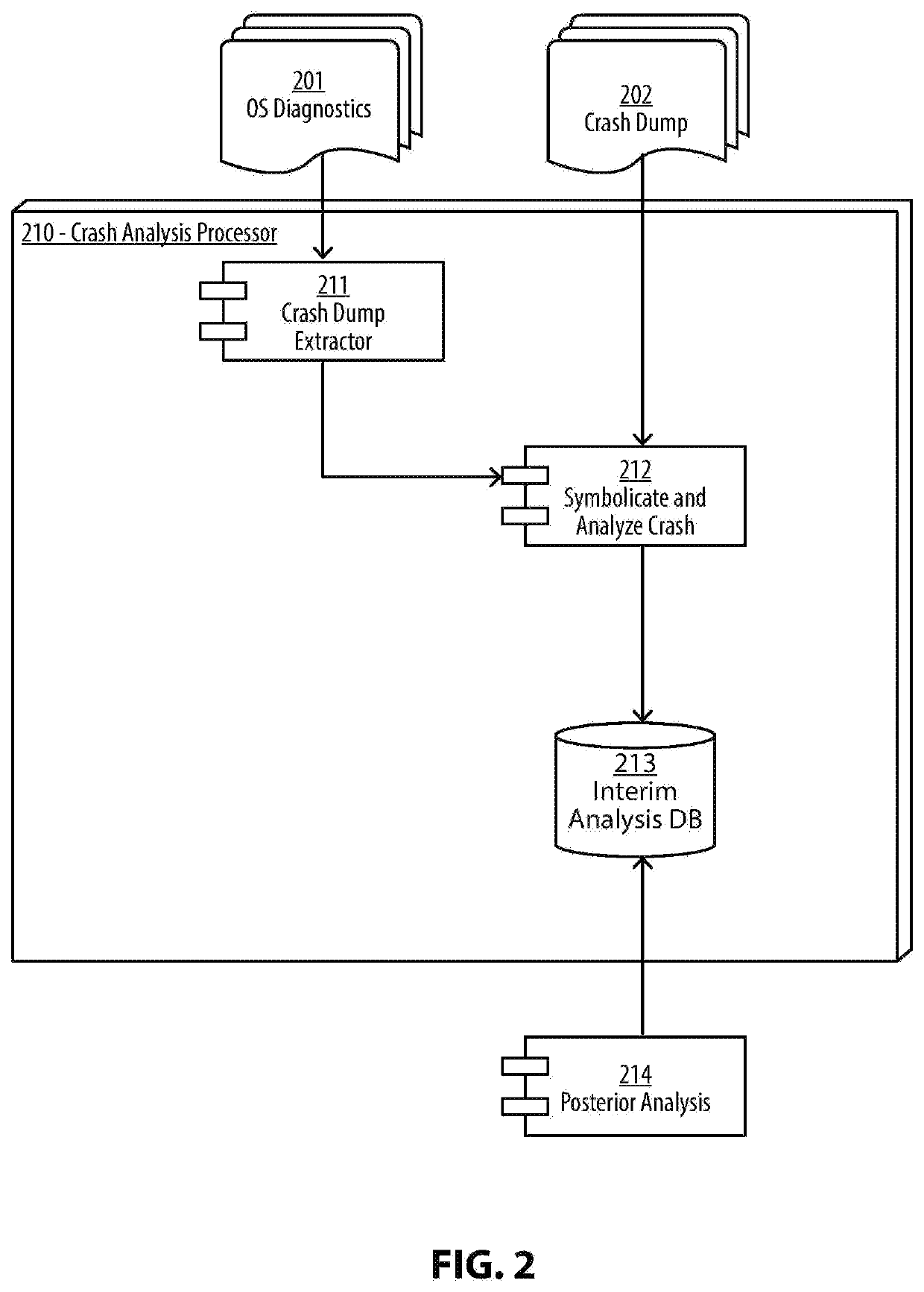
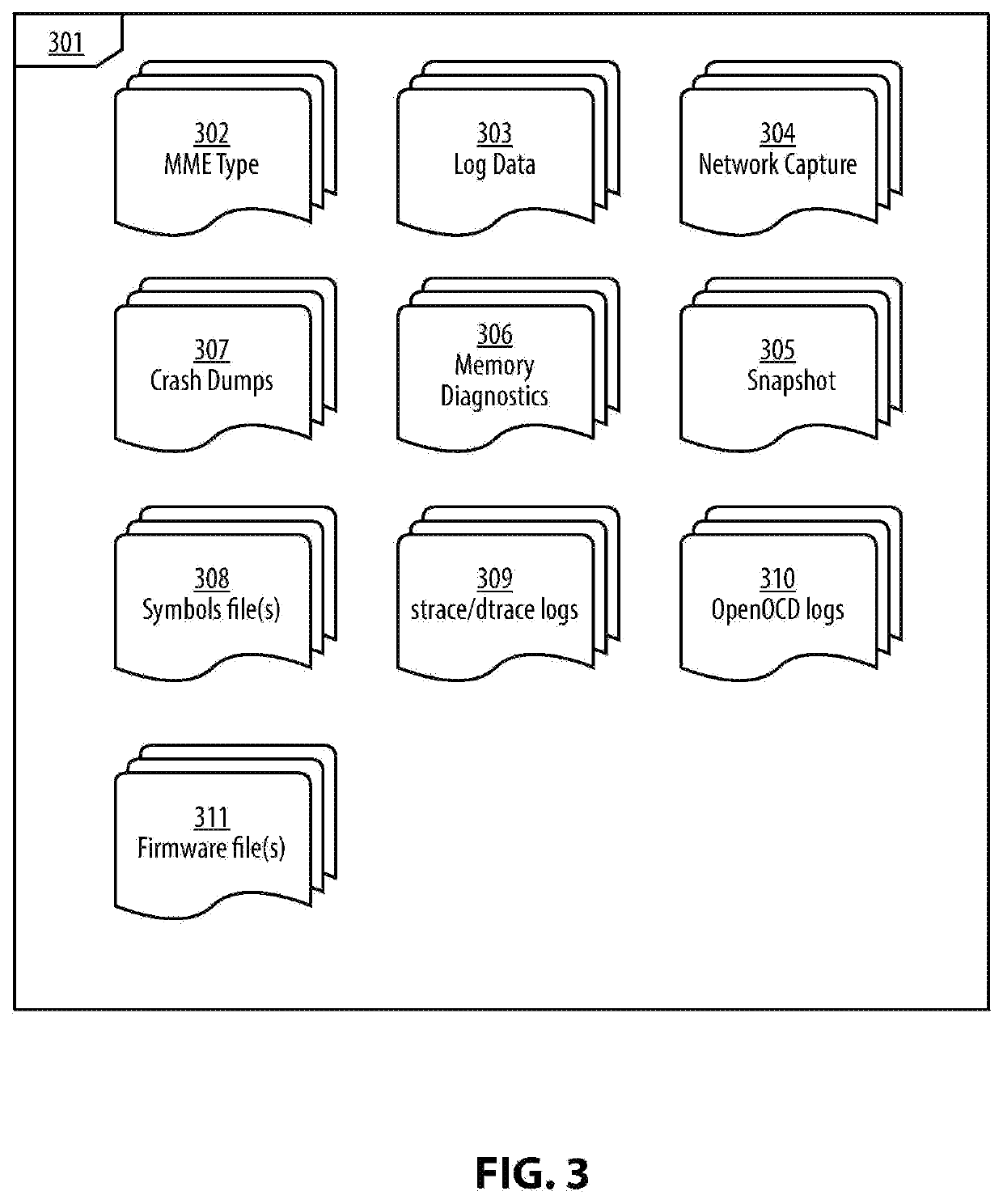
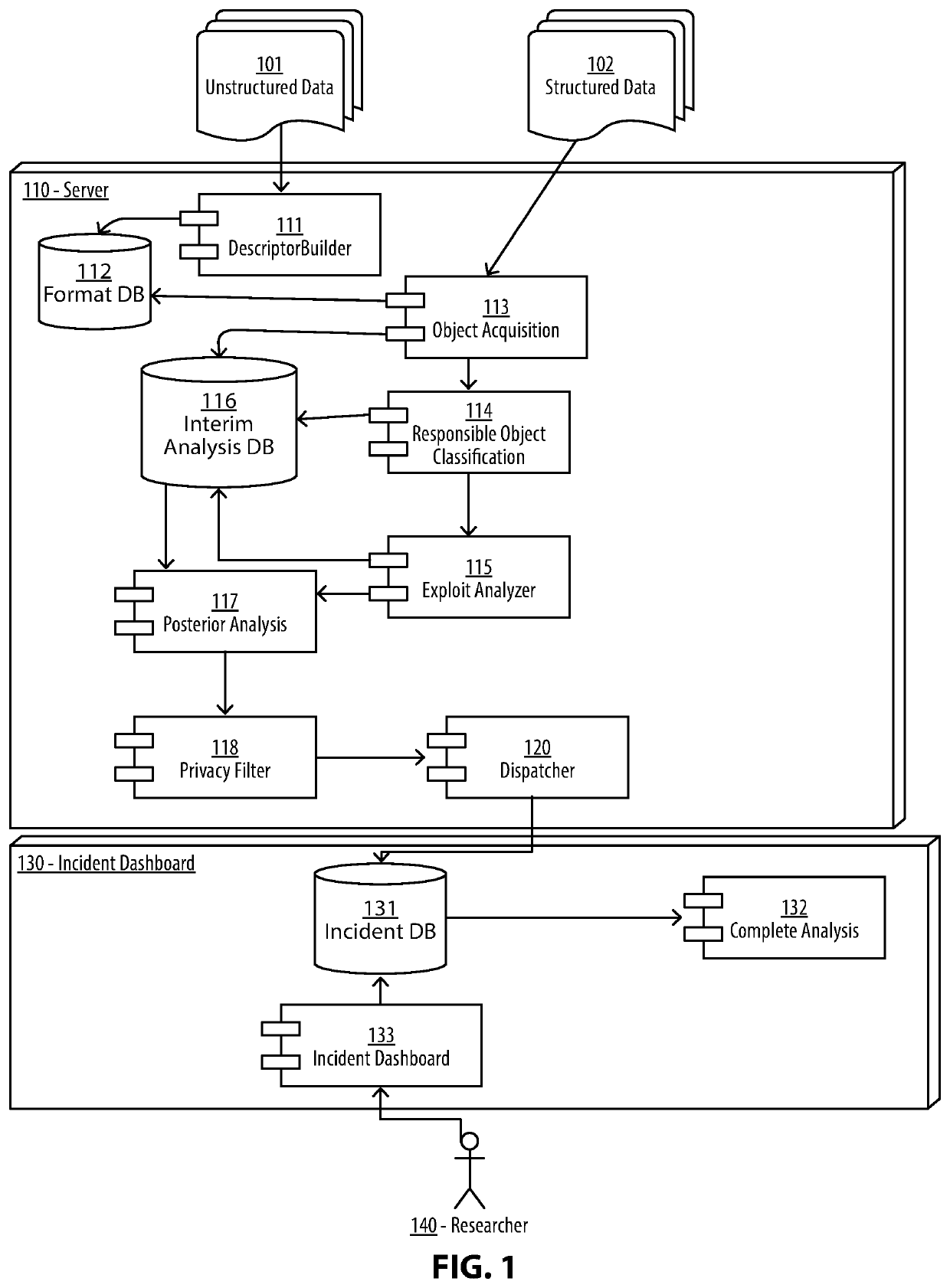
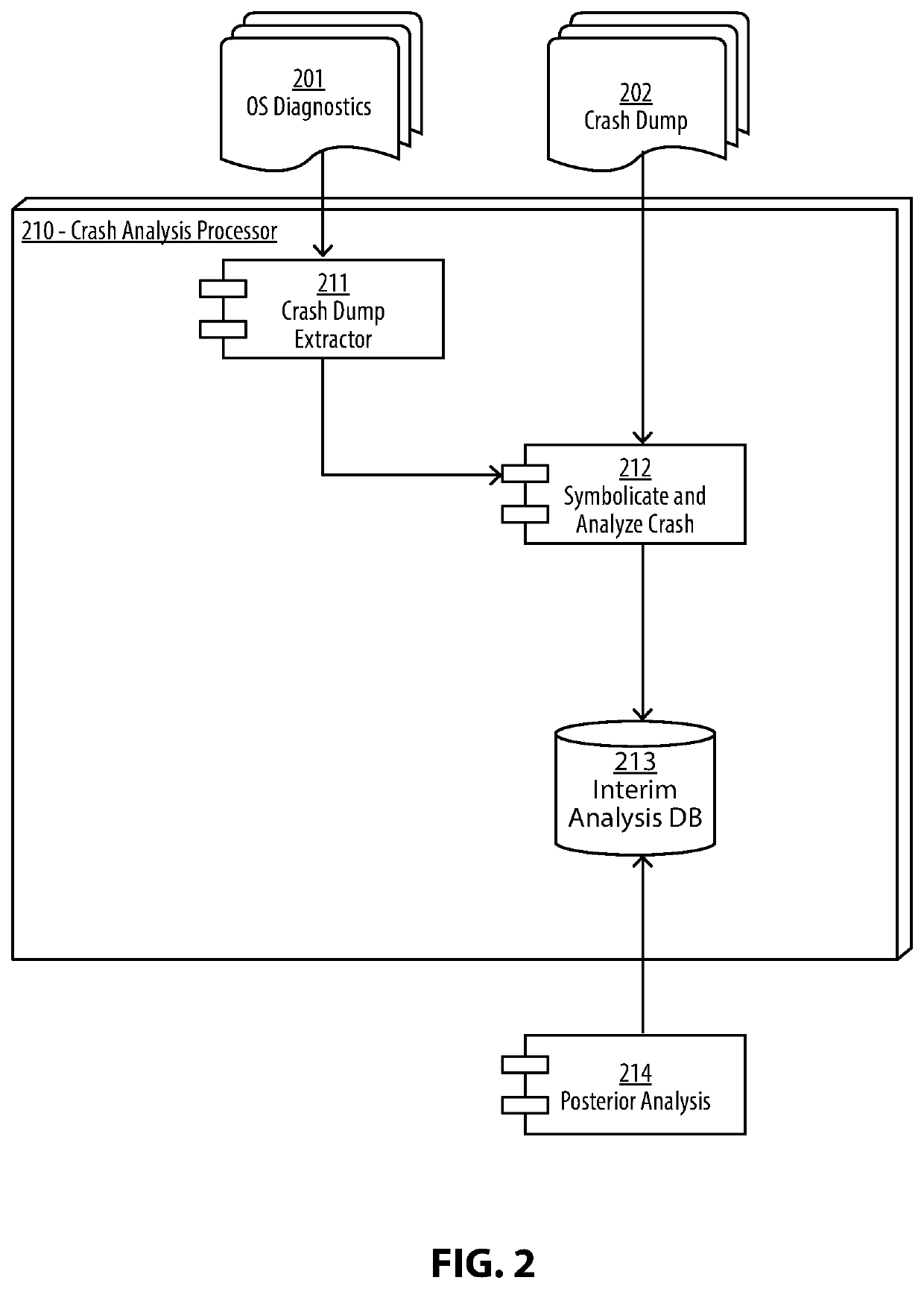
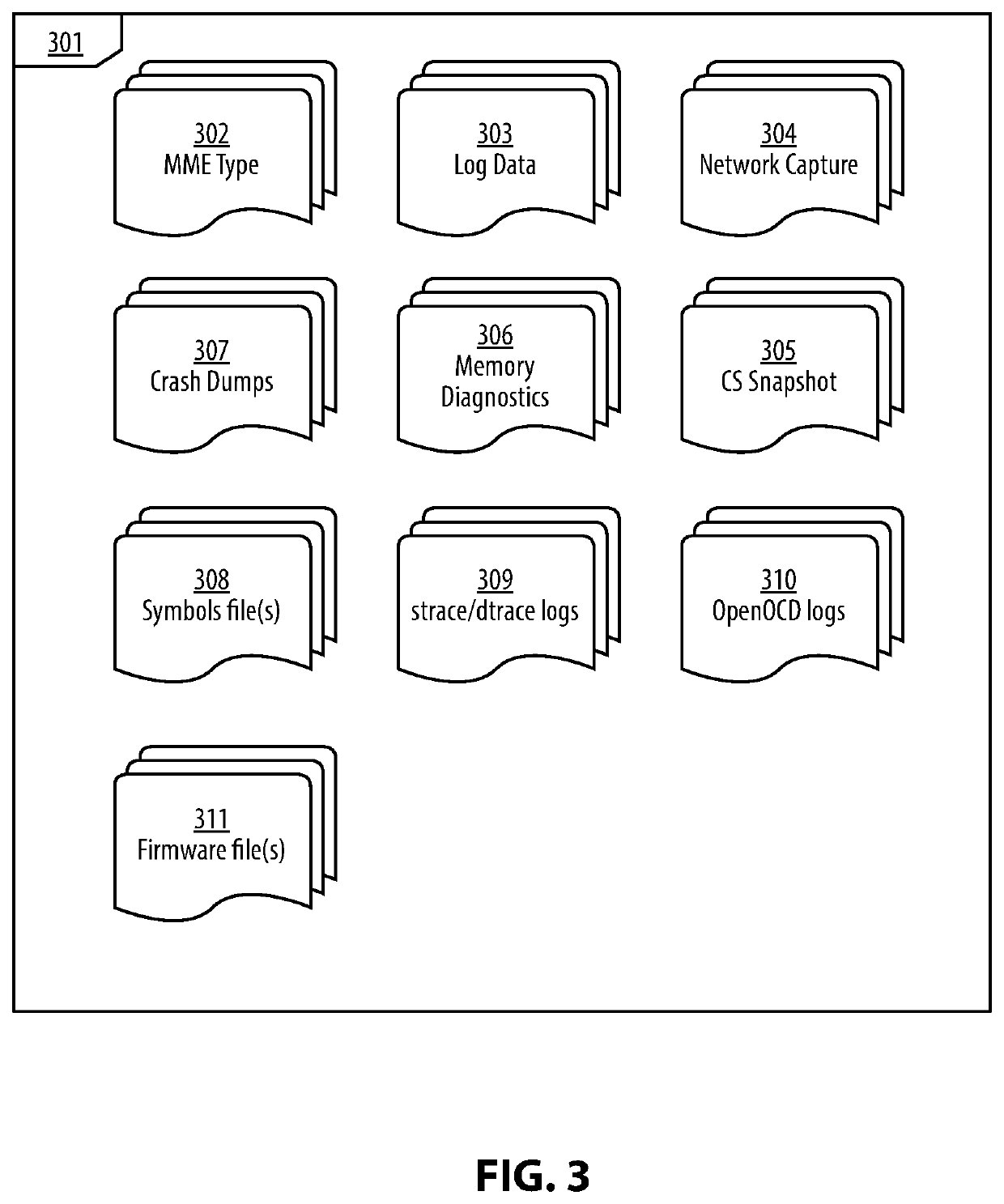
System and Method for an Automated Analysis of Operating System Samples, Crashes and Vulnerability Reproduction
Malware analysis and root-cause analysis, and information security insights based on Operating System sampled data. Sampled data includes structured logs, Operating System Snapshots, programs and / or processes and / or kernel crashes, crash dumps, memory dumps, stackshots, simulated crashes or samples. The sampled data contains payload for extraction for the purpose of detection, evaluation and reproduction of threats, infection vector, threat actors and persistence methods in the form of backdoors or Trojans or exploitable vulnerabilities used for initial infiltration or lateral movement.
Owner:ZECOPS
System and Method for An Automated Analysis of Operating System Samples
InactiveUS20200012793A1Digital data protectionPlatform integrity maintainanceMalware analysisOperational system
Methods and apparatuses for malware analysis and root-cause analysis, and information security insights based on Operating System sampled data such as structured logs, Operating System Snapshots, programs and / or processes and / or kernel crash dumps or samples containing payload for extraction for the purpose of detection and evaluation of threats, infection vector, threat actors and persistence methods in the form of backdoors or Trojans or unknown exploitable vulnerabilities used.
Owner:ZECOPS
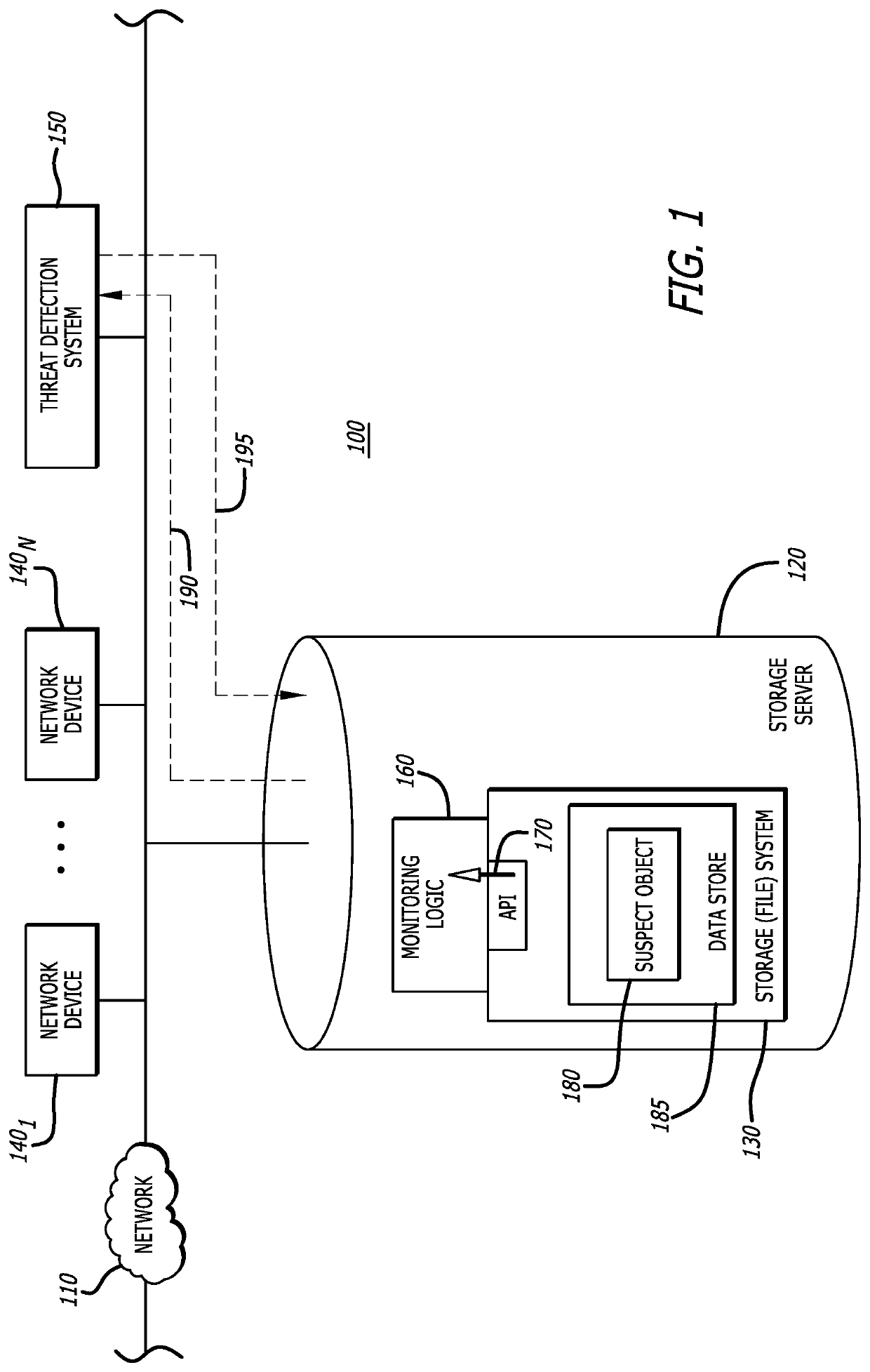
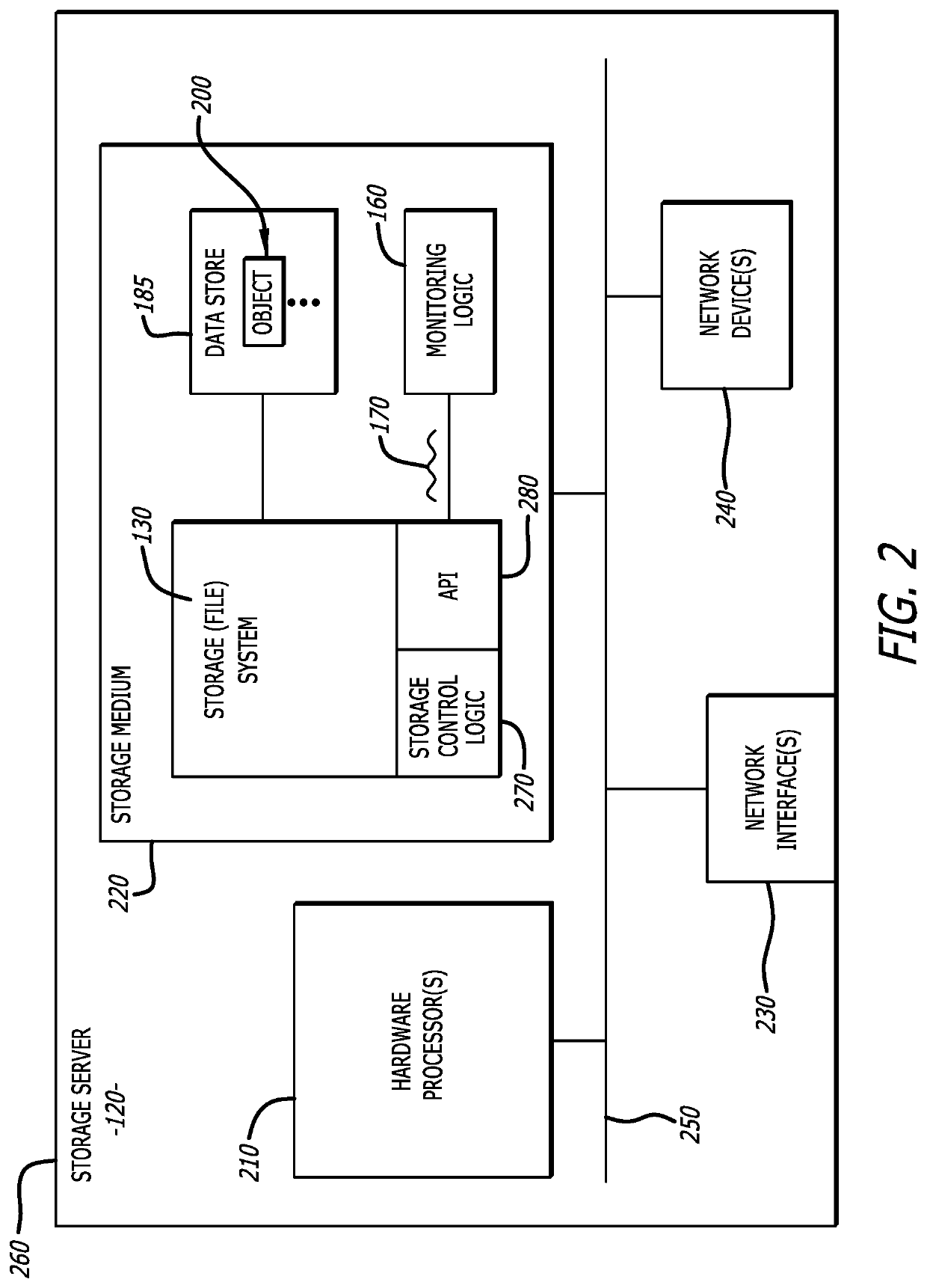
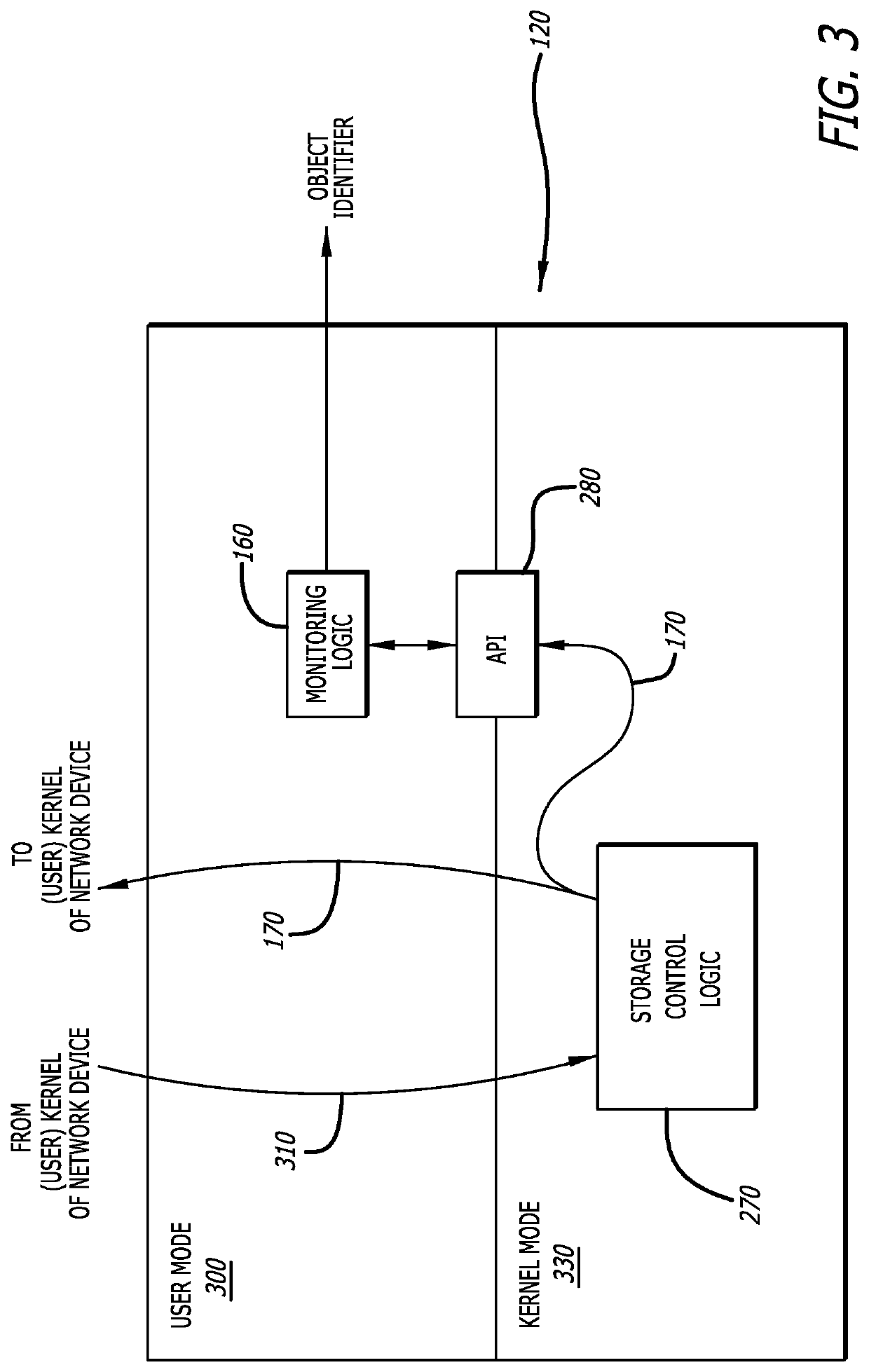
System and method for triggering analysis of an object for malware in response to modification of that object
According to one embodiment, a system featuring one or more processors and memory that includes monitoring logic. During operation, the monitoring logic is configured to monitor for and detect a notification message that is directed to a destination other than the monitoring logic and identify an event associated with a change in state of a data store associated with the file system to occur. The notification message, at least in part, triggers a malware analysis to be conducted on an object associated with the state change event.
Owner:FIREEYE SECURITY HLDG US LLC
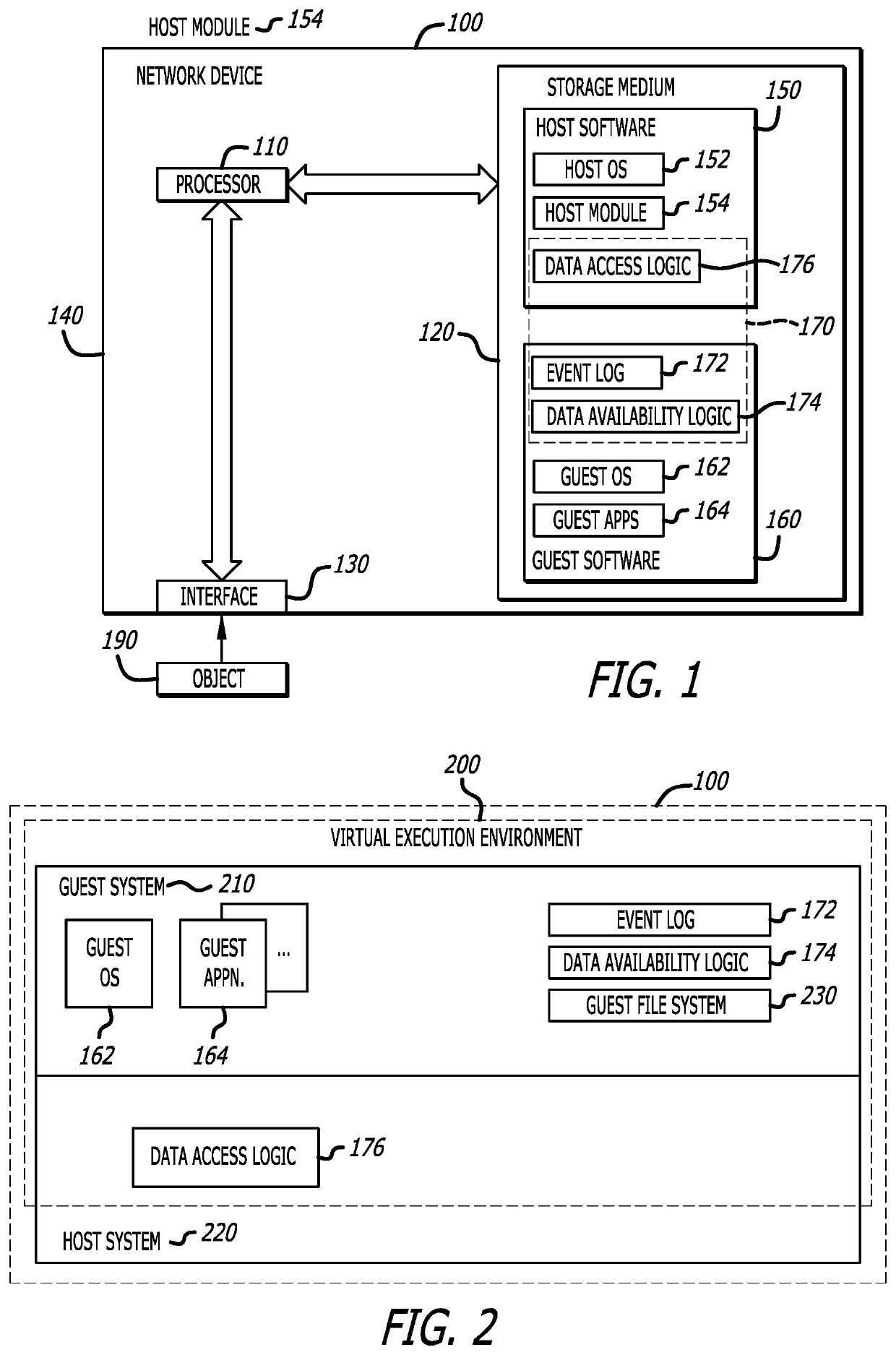
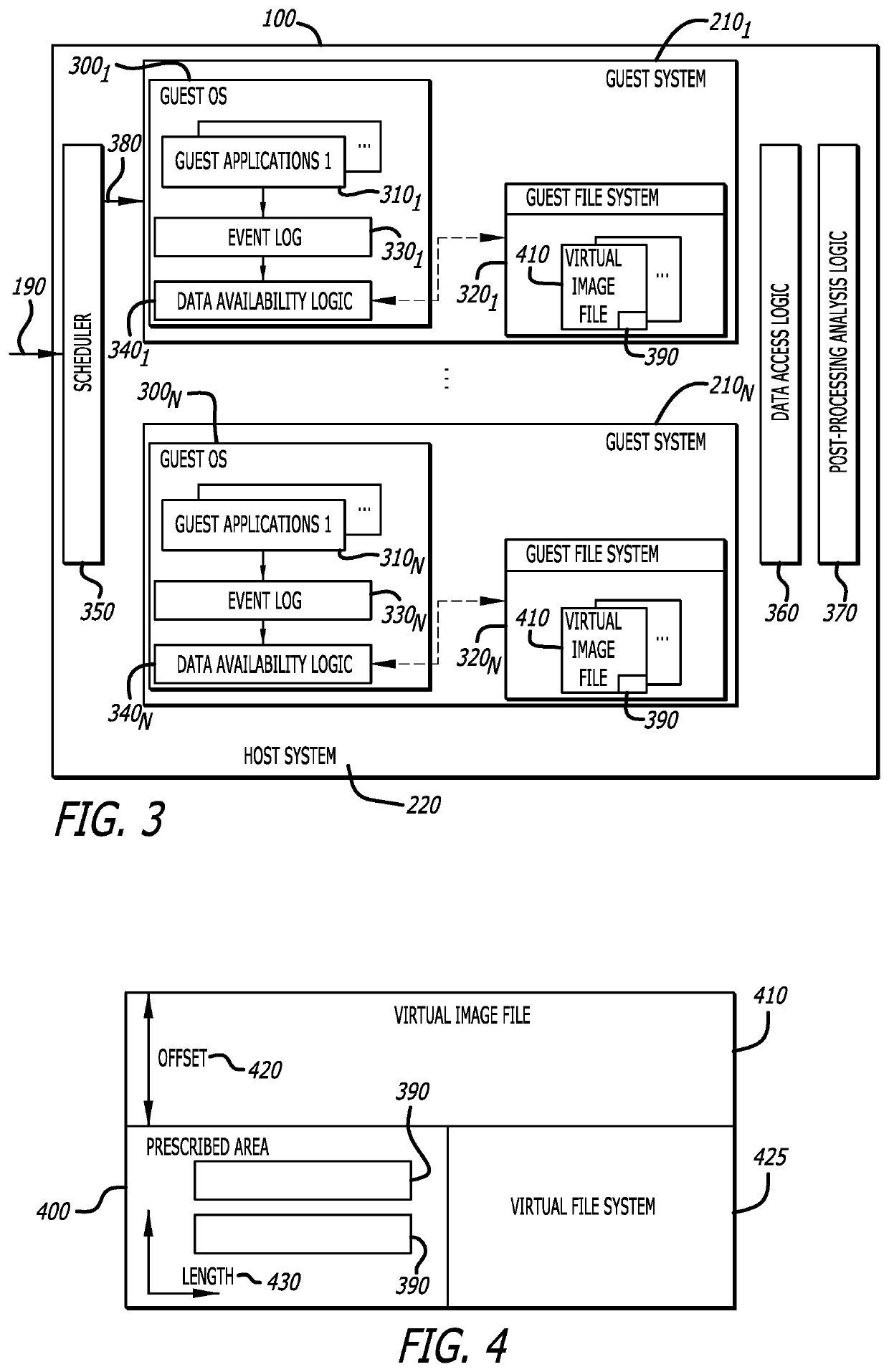
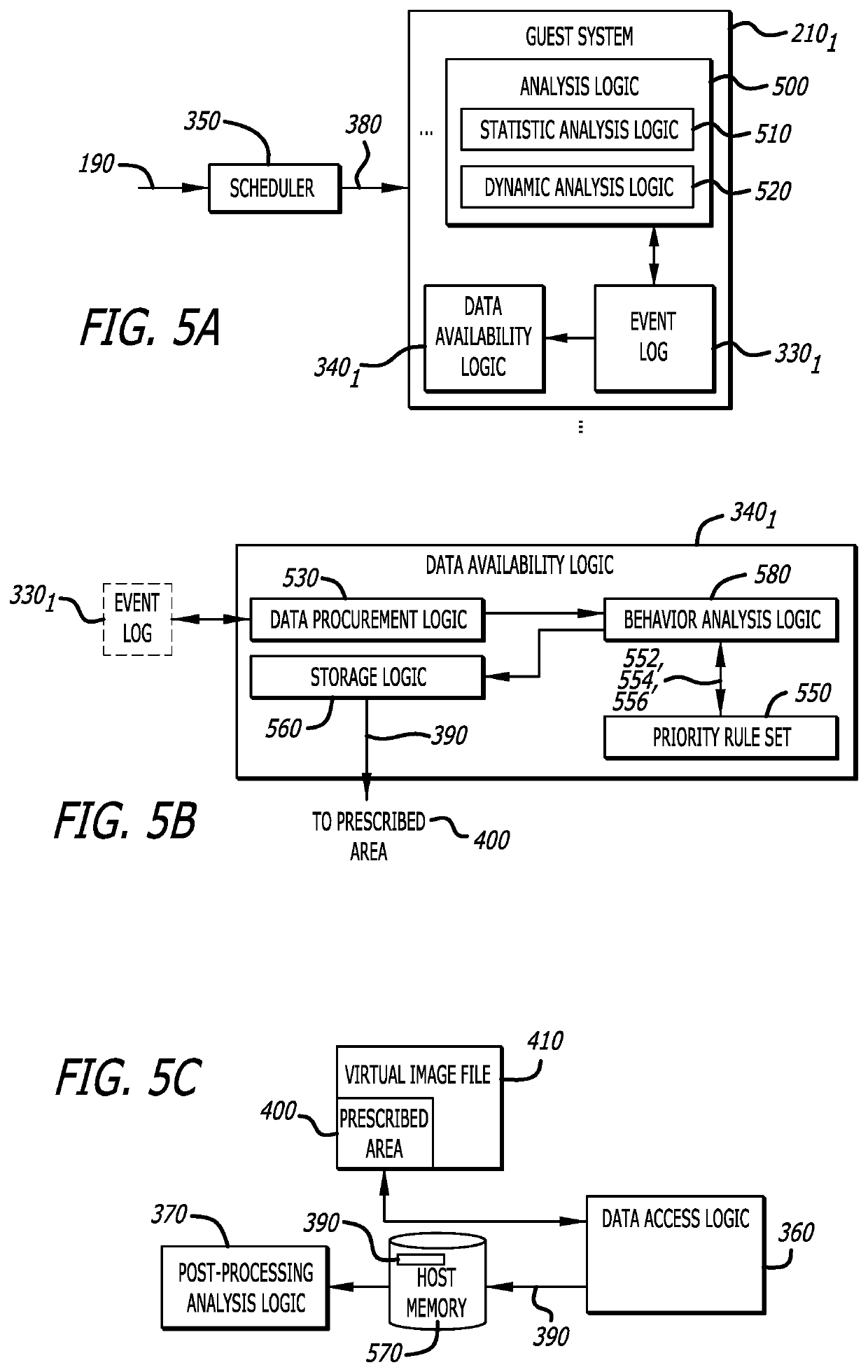
Data extraction system for malware analysis
ActiveUS10902119B1Platform integrity maintainanceSoftware simulation/interpretation/emulationMalware analysisSoftware engineering
According to one embodiment, a computerized method features monitoring behaviors of an object during processing within a guest system of a virtual machine. Within a guest system, a rule-based analysis of data associated with the monitored behaviors is conducted. The rule-based analysis includes prioritizing data associated with the monitored behaviors that correspond to an exception, and thereafter, storing the data associated with the monitored behaviors that correspond to the exception into a prescribed area of a virtual image file. The prescribed area is accessible by (i) logic within the guest system and (ii) logic within a host system of the virtual machine.
Owner:FIREEYE SECURITY HLDG US LLC