Patents
Literature
44 results about "Minimal access" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
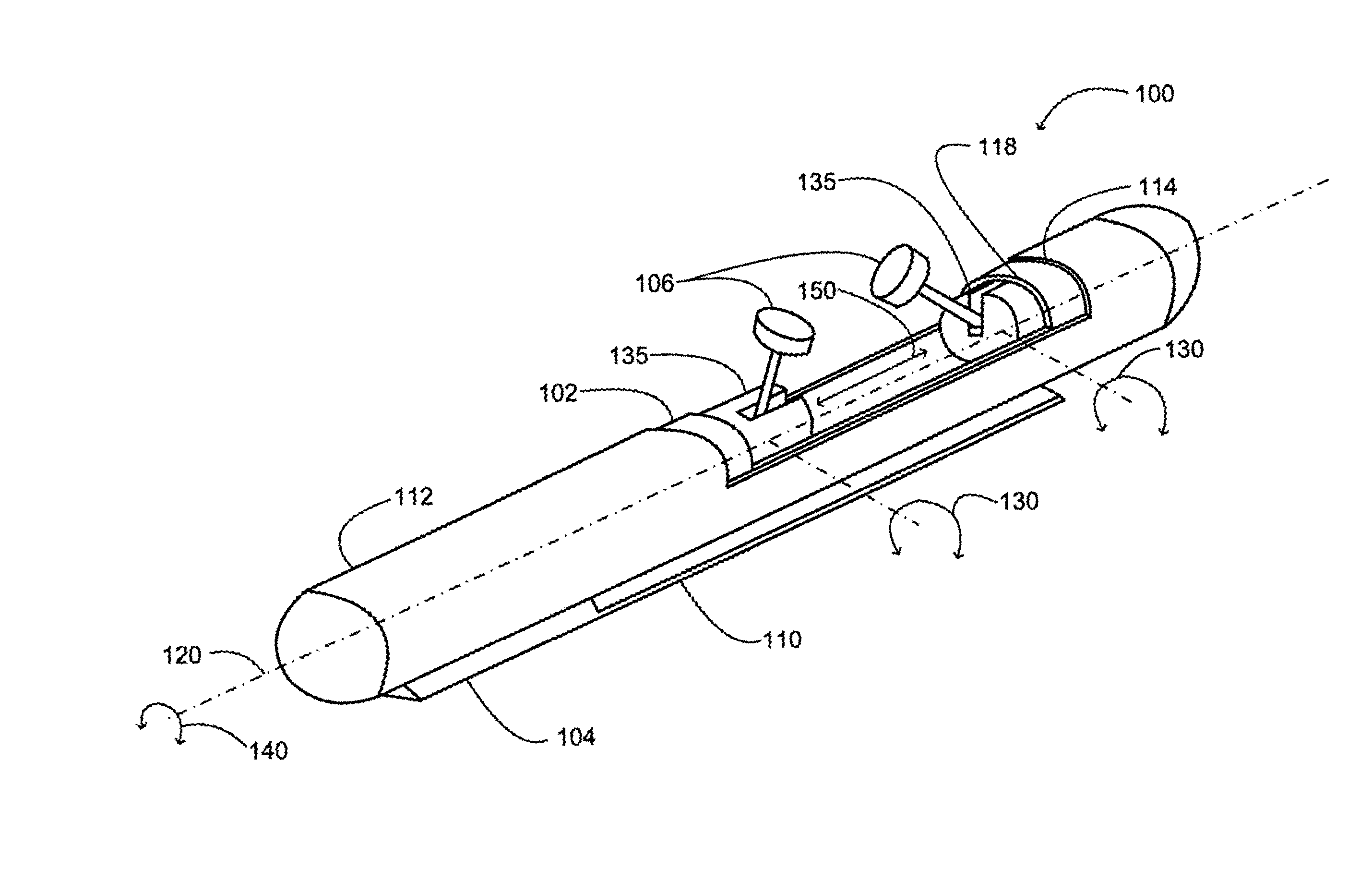
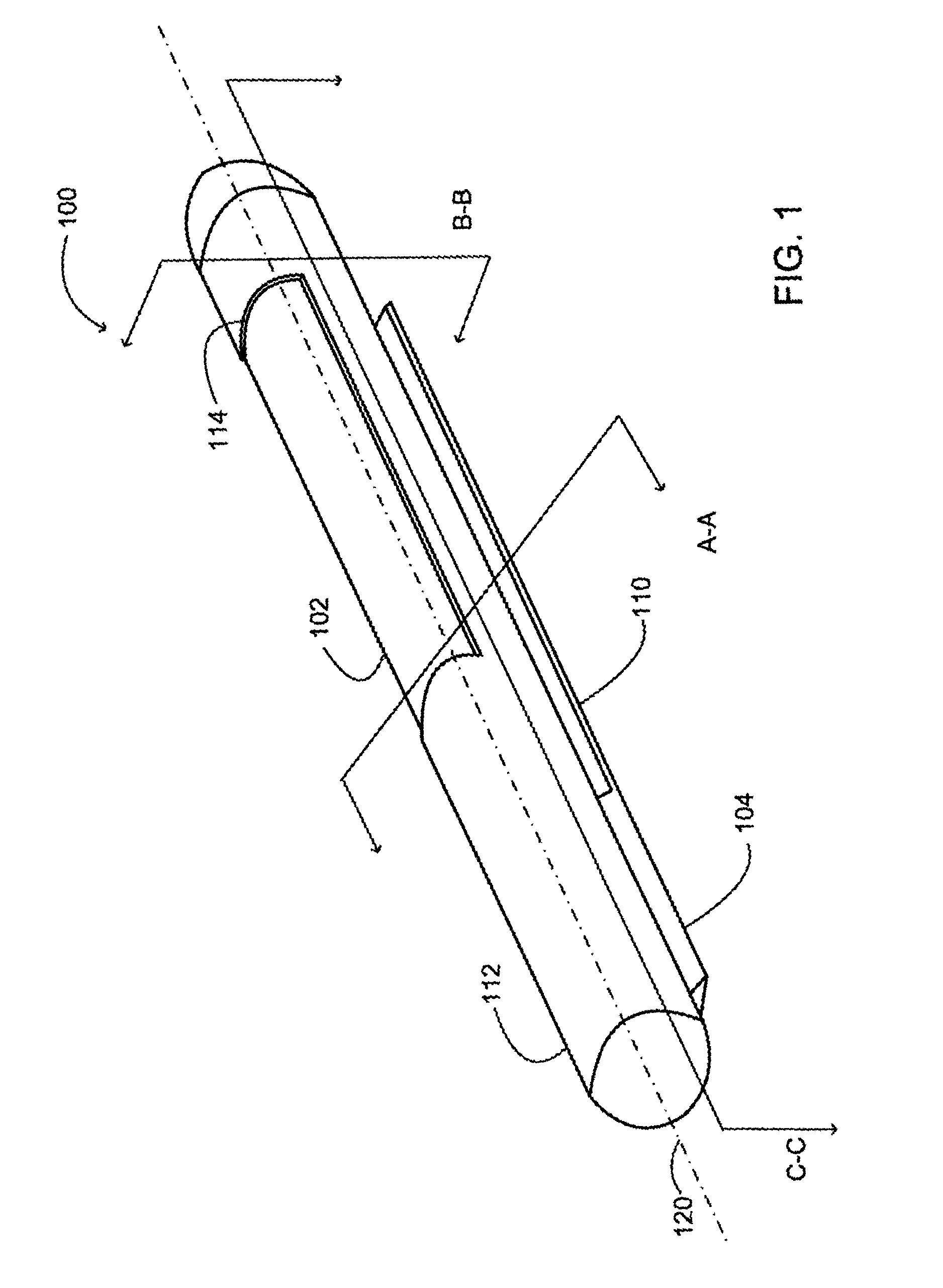
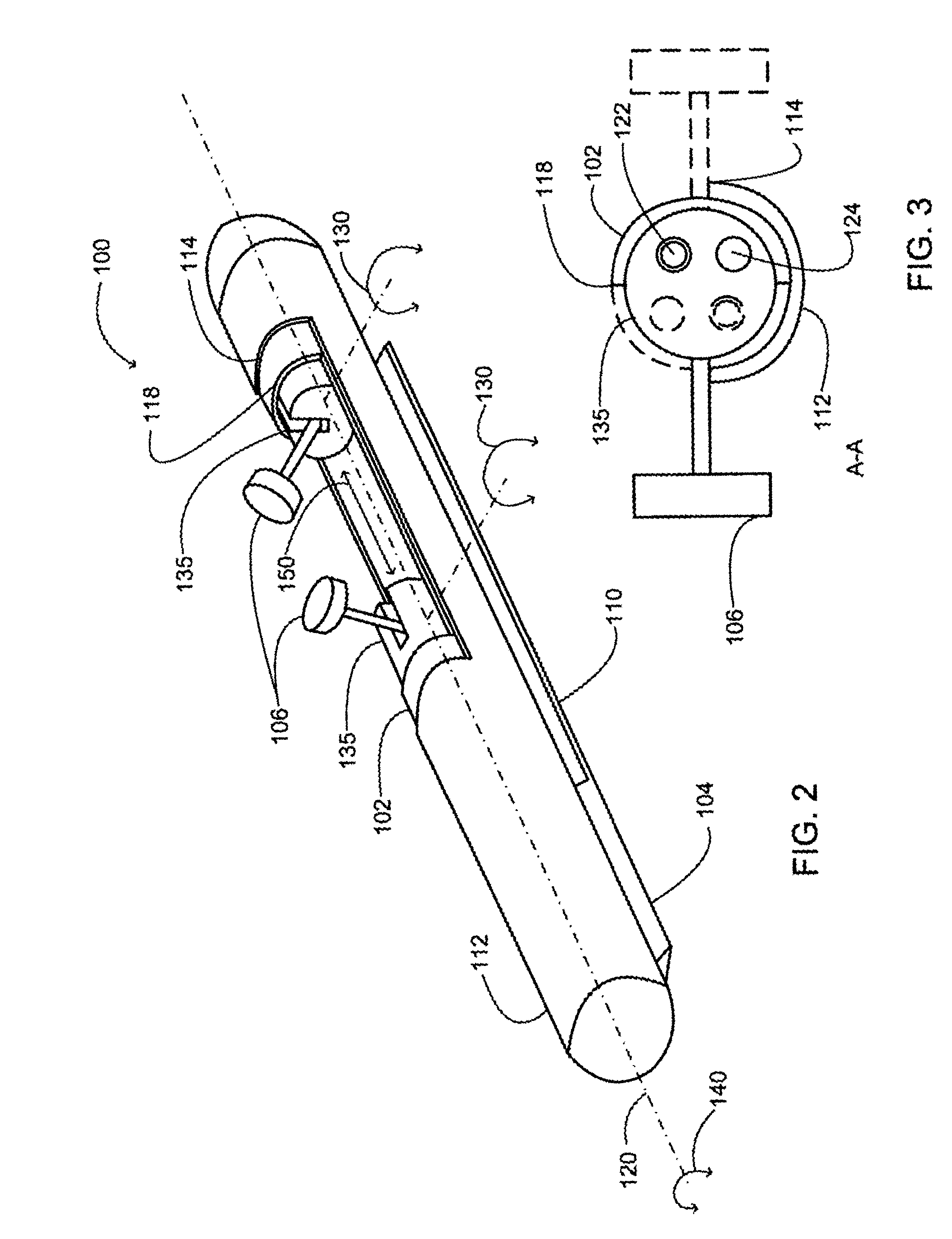
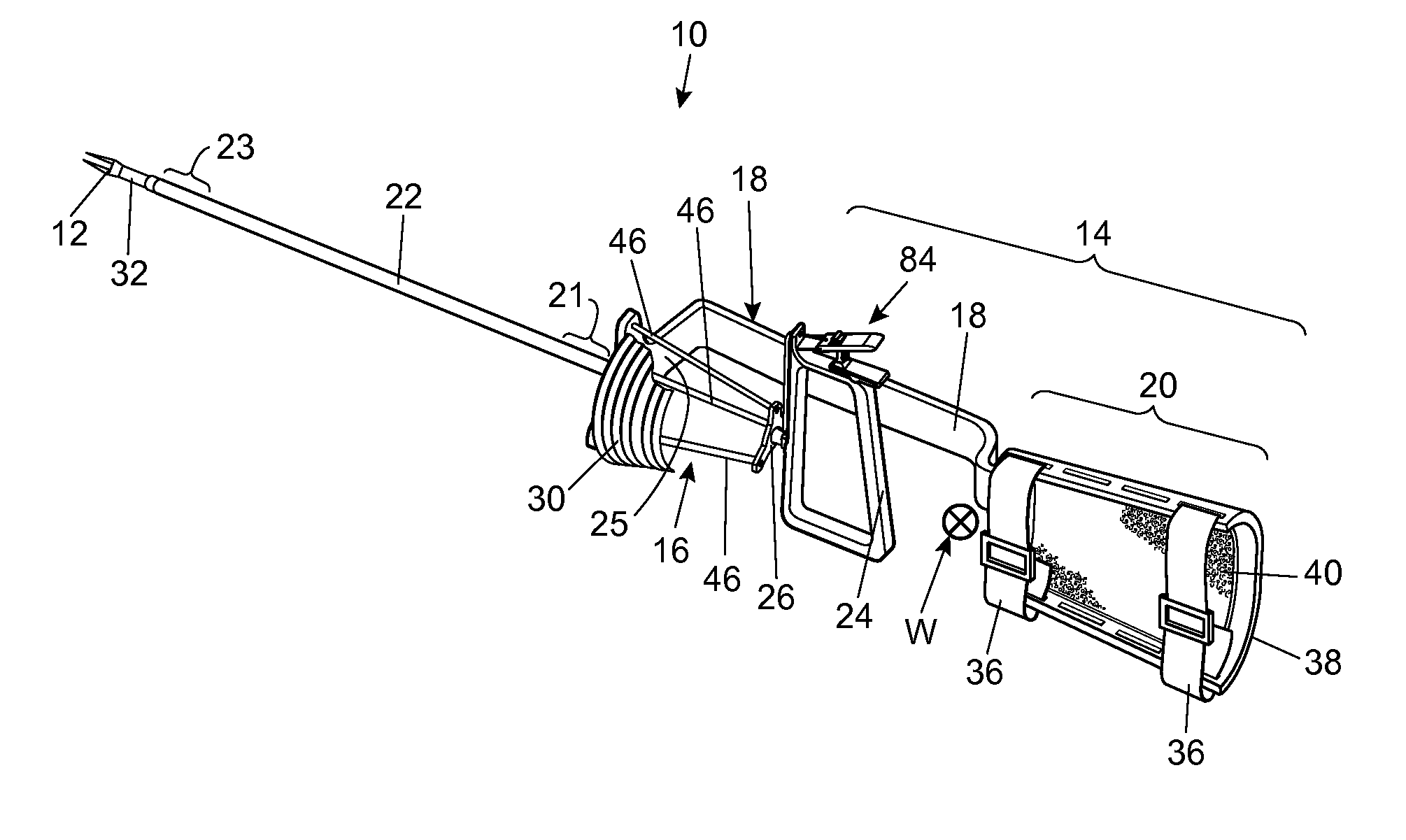
Insertable device and system for minimal access procedure
ActiveUS7066879B2Limited mobilityWide field of viewEndoscopesLaproscopesAbdominal cavityProcedure Indication
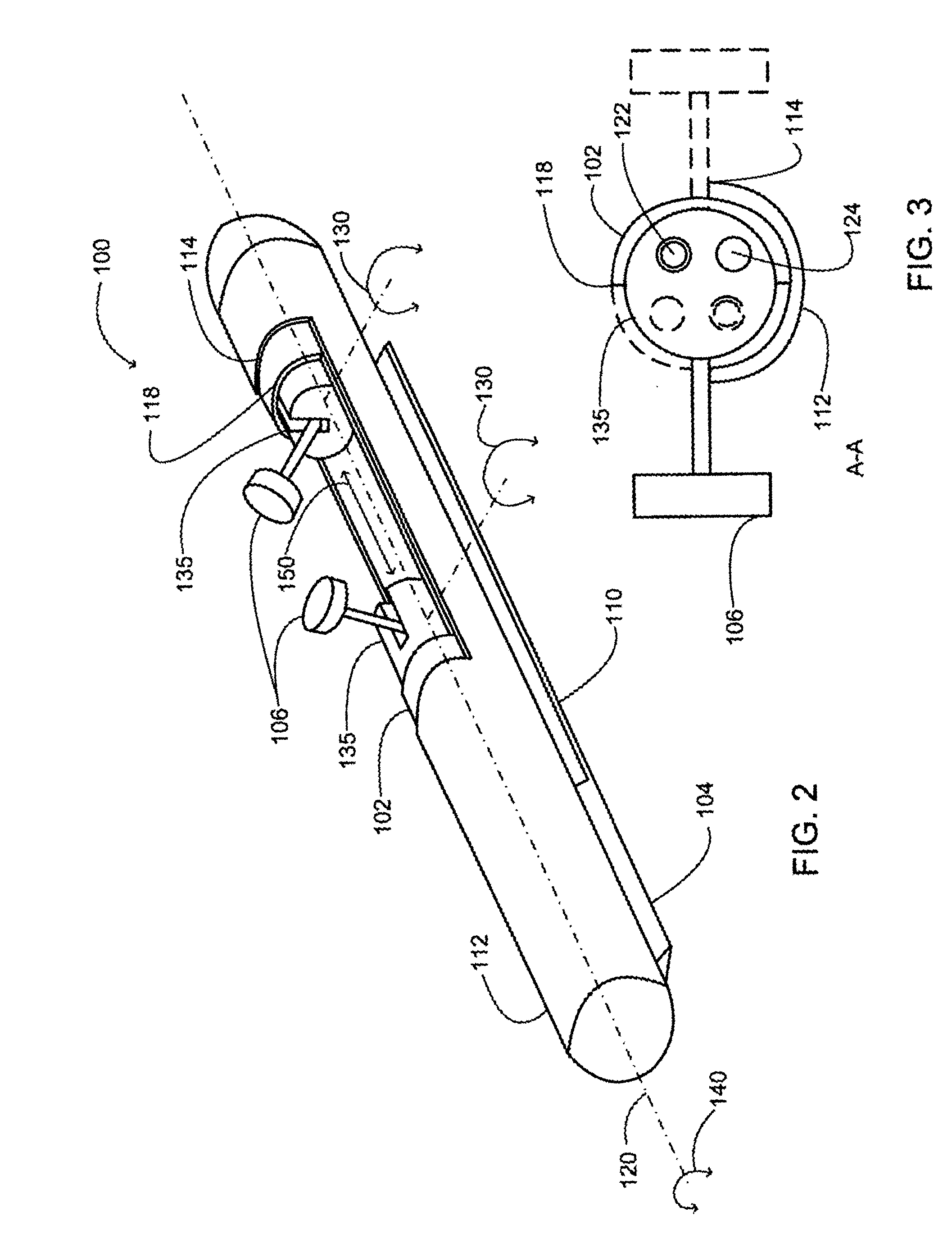
The present invention provides a system and single or multi-functional element device that can be inserted and temporarily placed or implanted into a structure having a lumen or hollow space, such as a subject's abdominal cavity to provide therewith access to the site of interest in connection with minimally invasive surgical procedures. The insertable device may be configured such that the functional elements have various degrees of freedom of movement with respect to orienting the functional elements or elements to provide access to the site from multiple and different orientations / perspectives as the procedure dictates, e.g., to provide multiple selectable views of the site, and may provide a stereoscopic view of the site of interest.
Owner:THE TRUSTEES OF COLUMBIA UNIV IN THE CITY OF NEW YORK
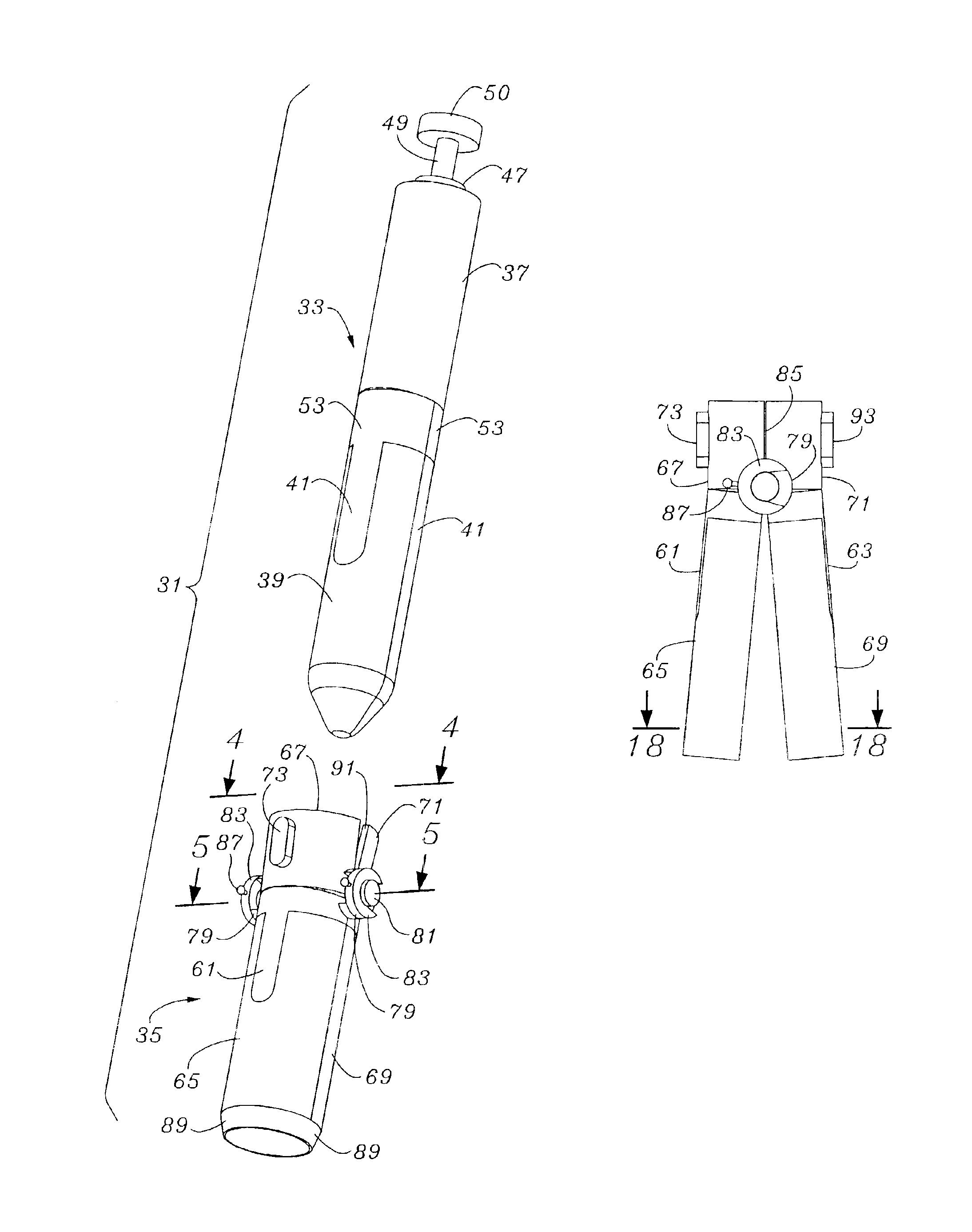
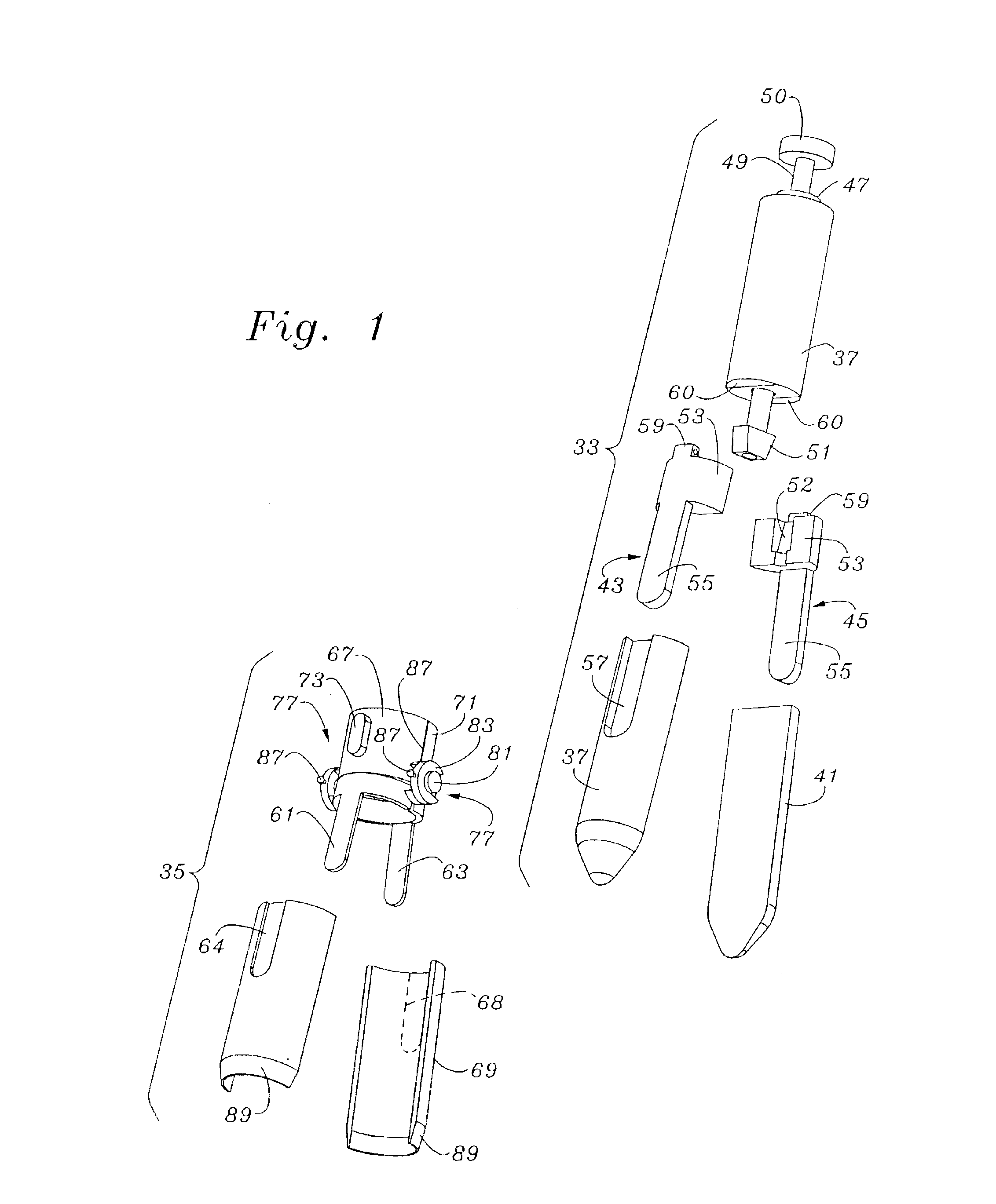
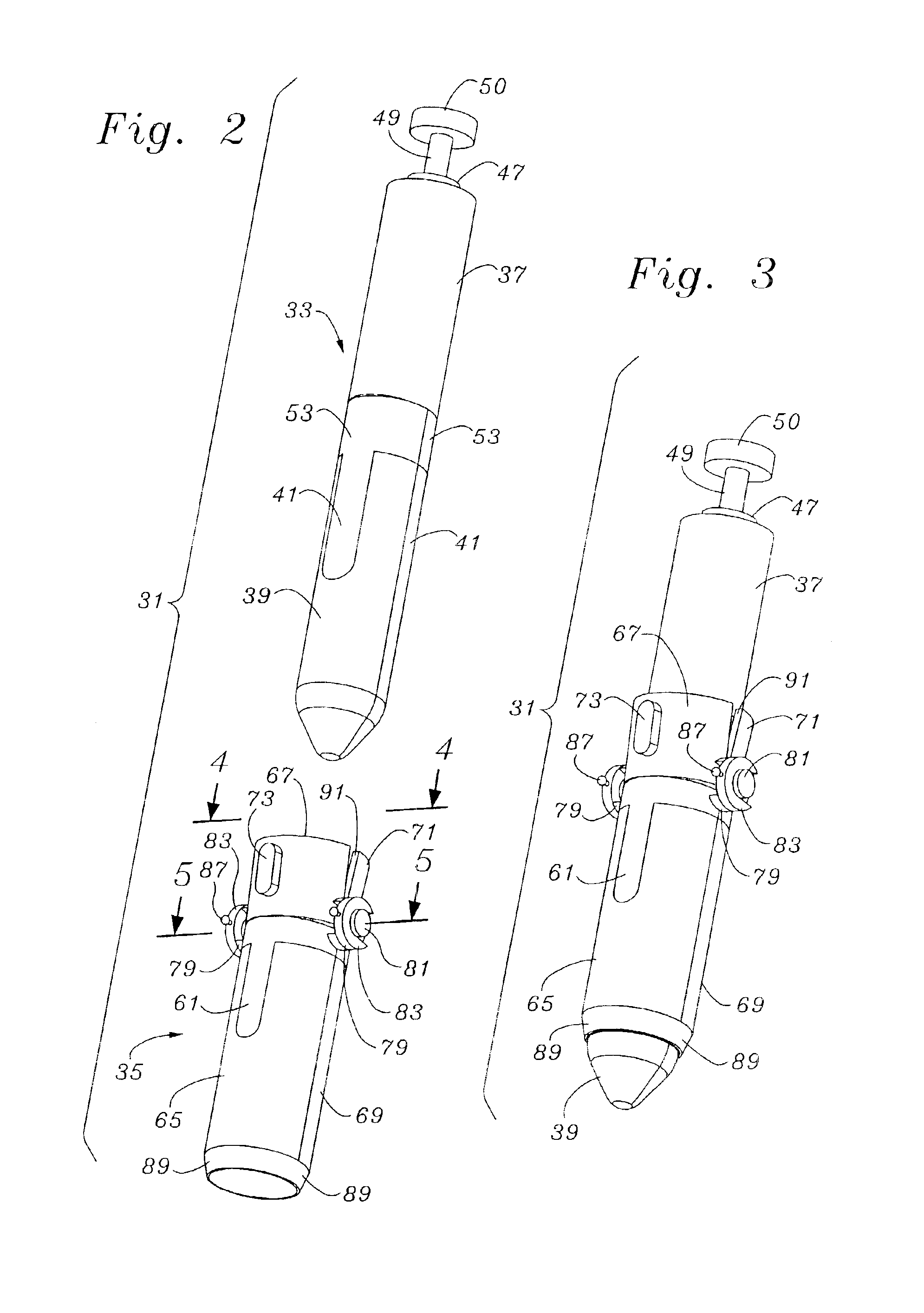
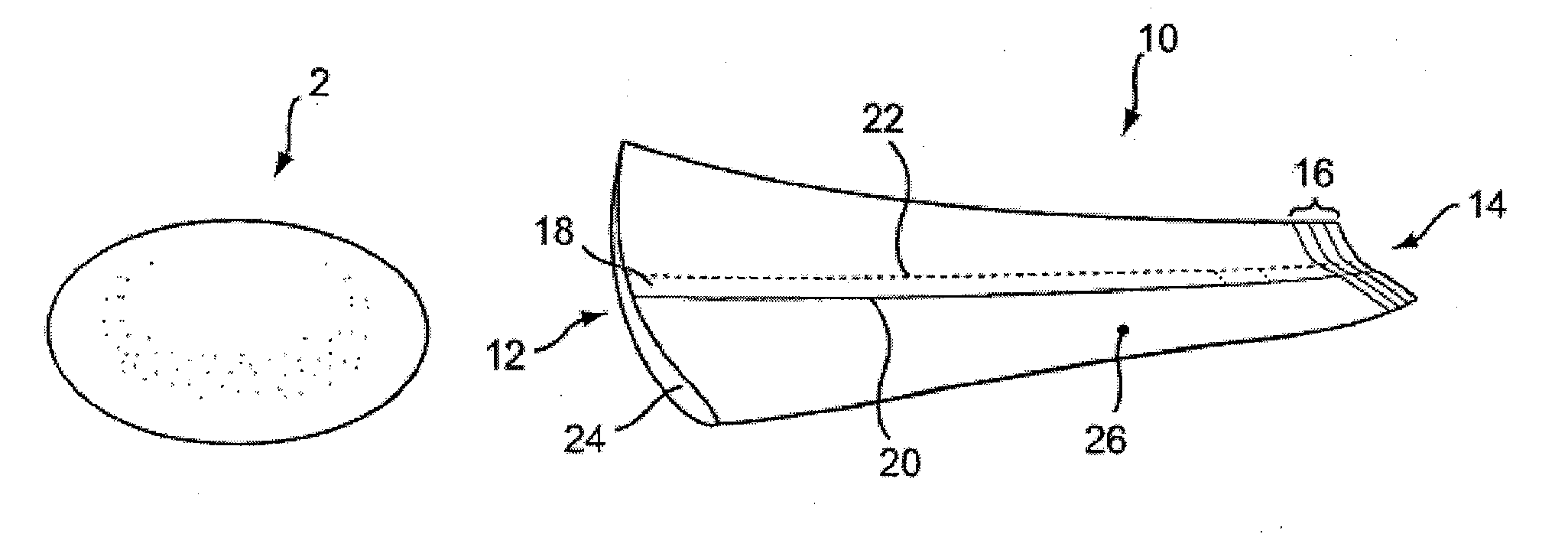
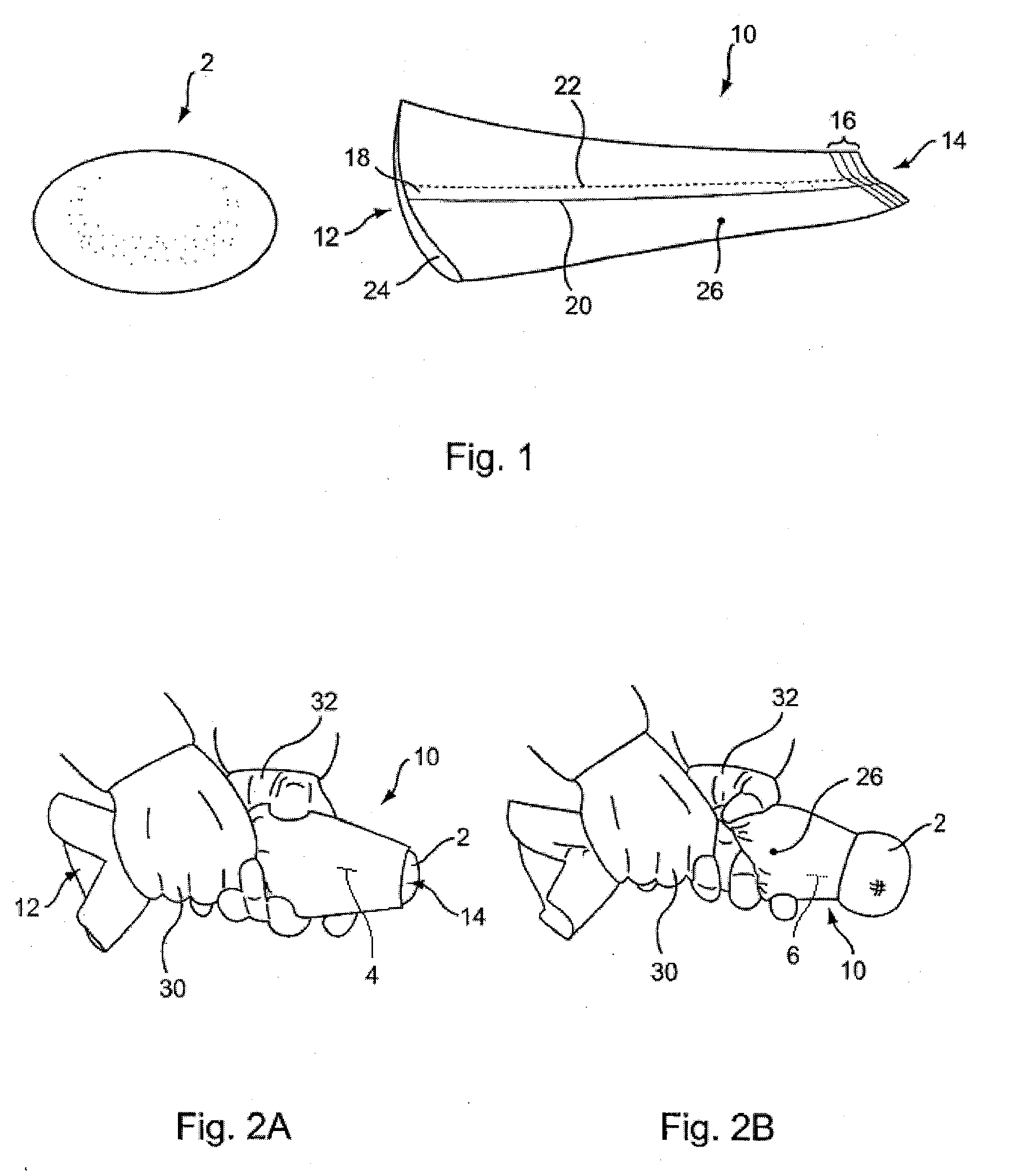
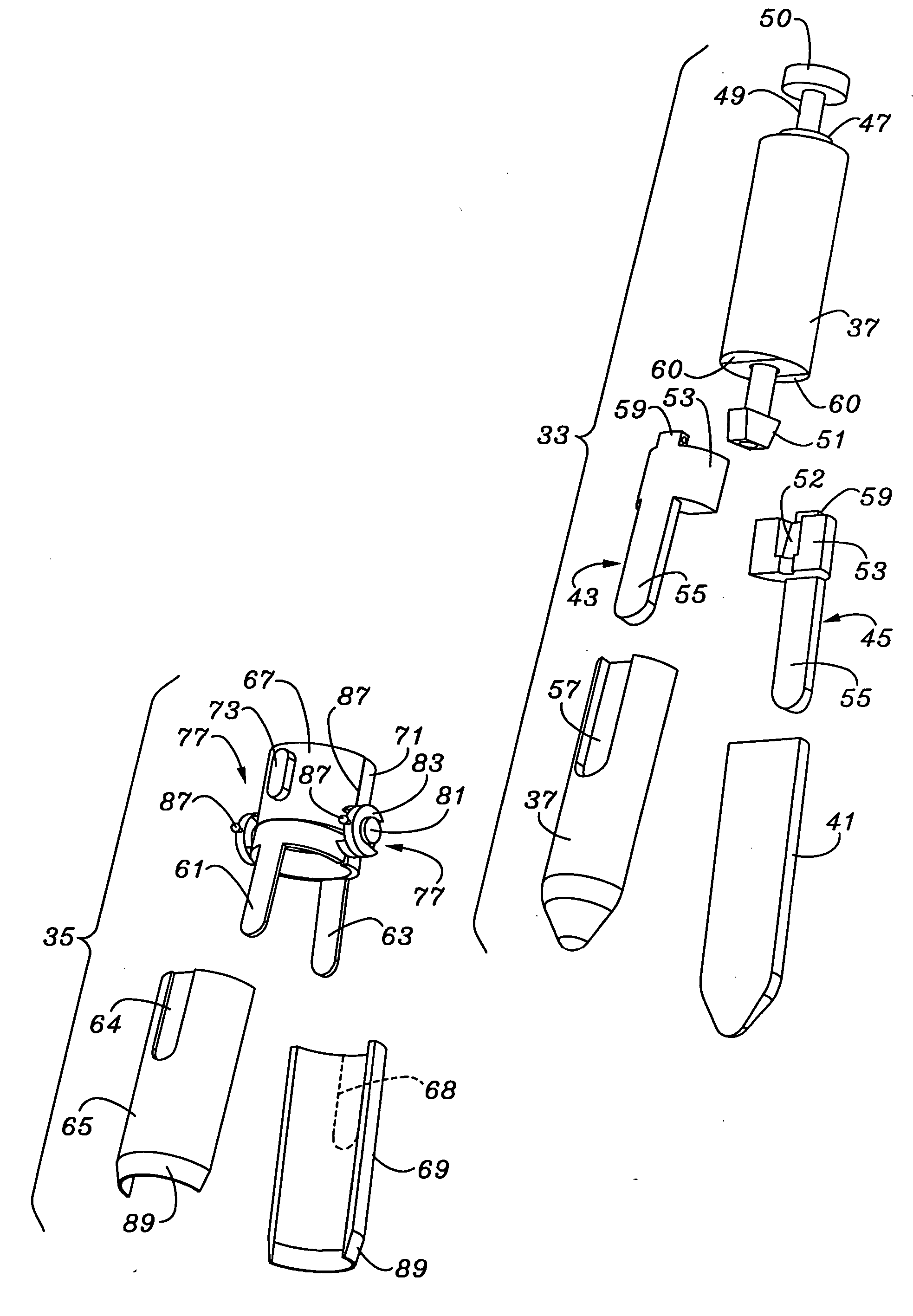
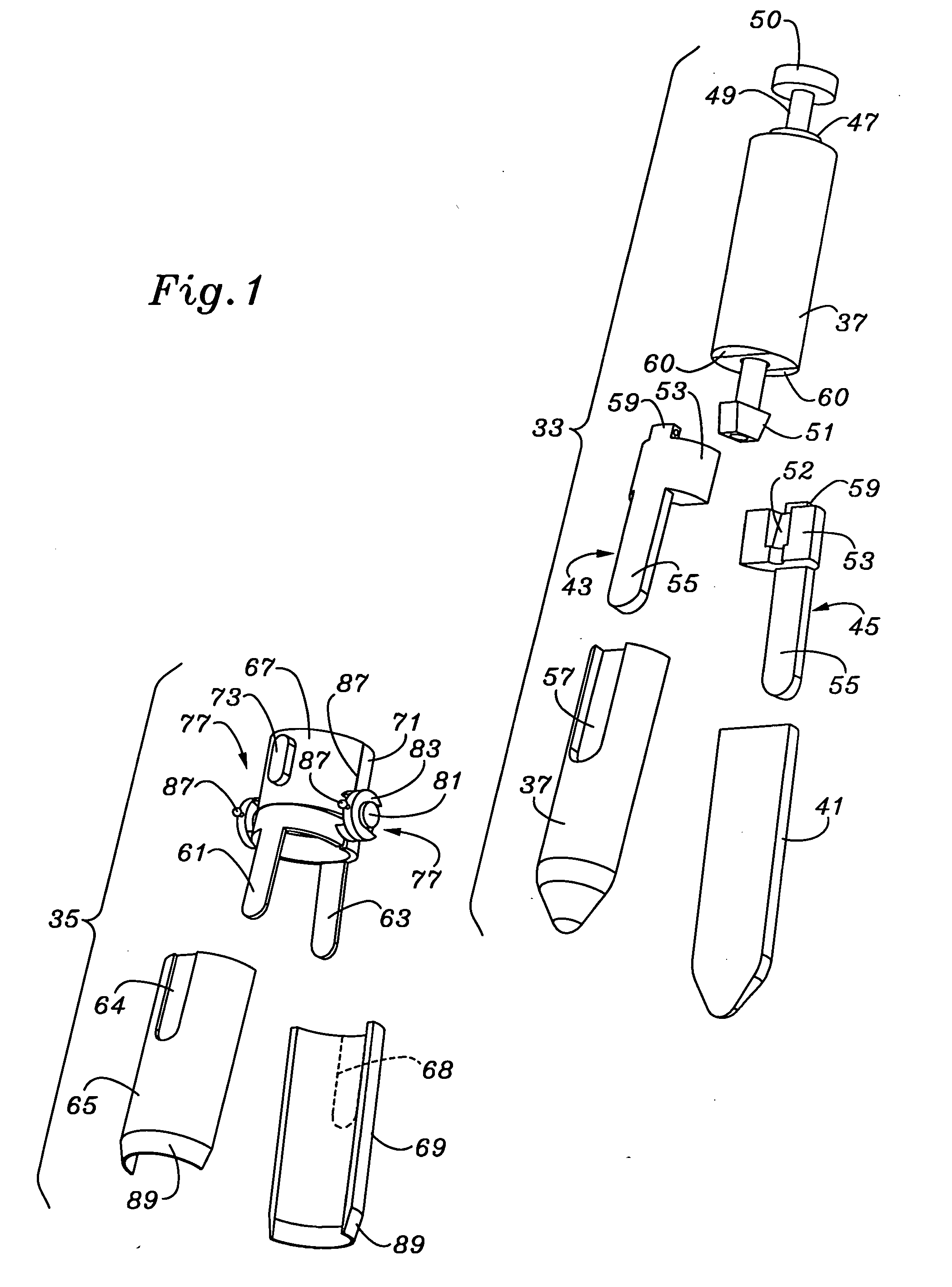
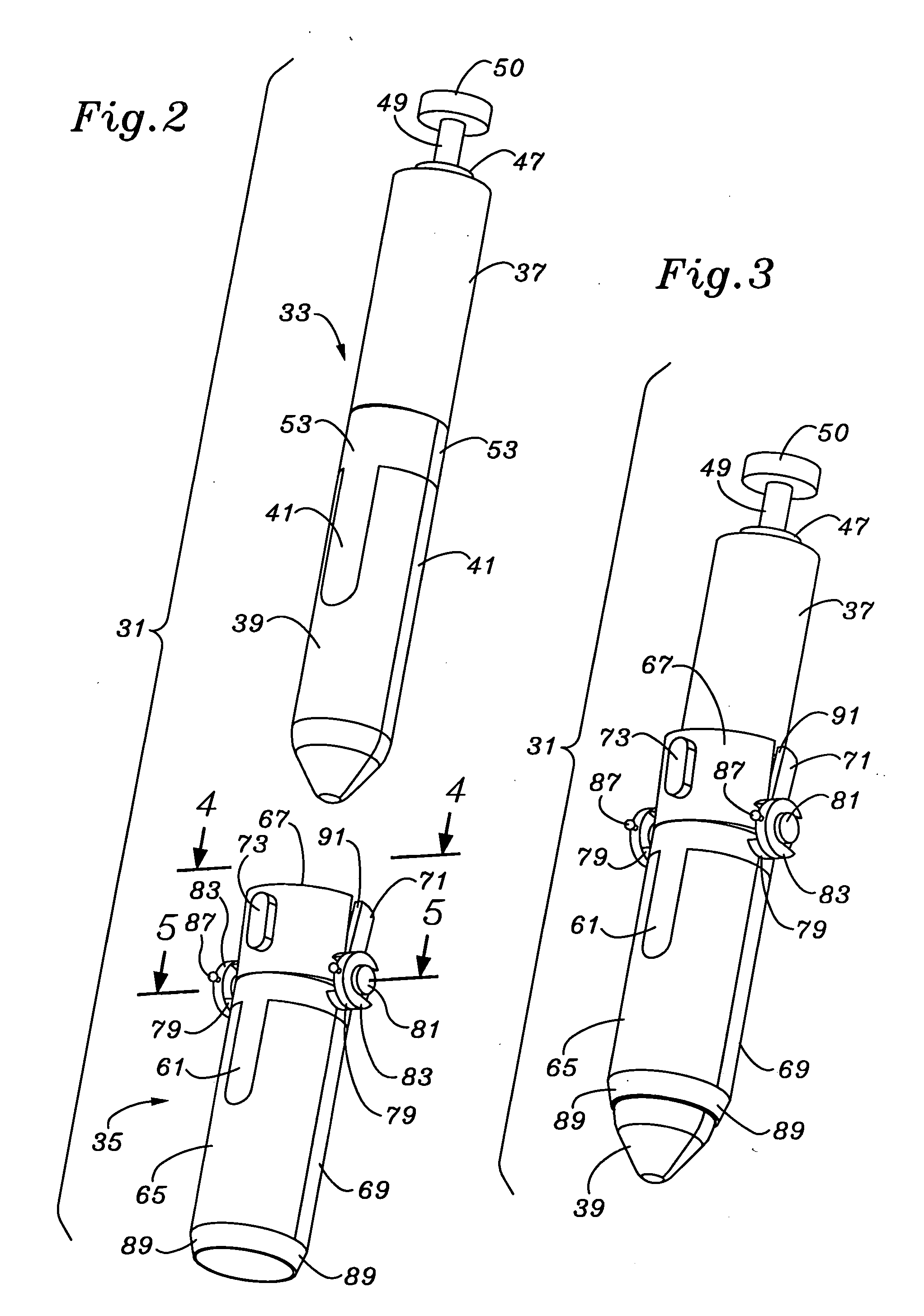
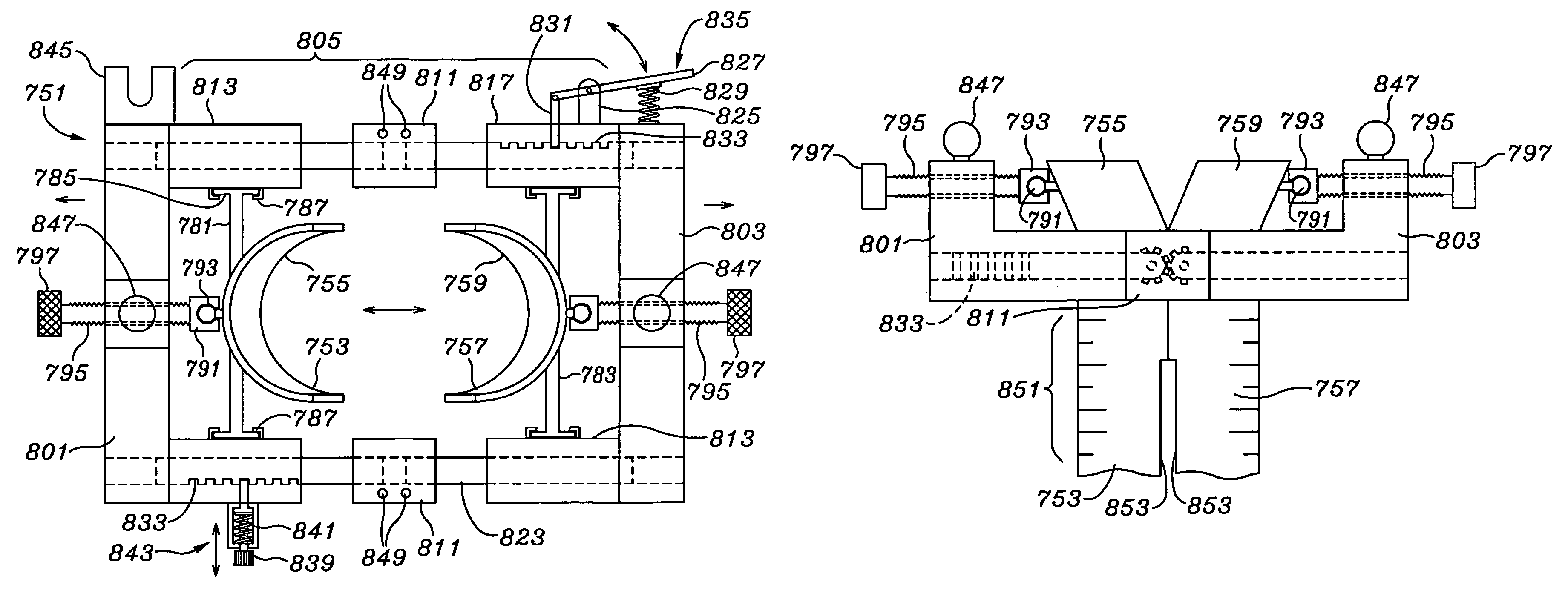
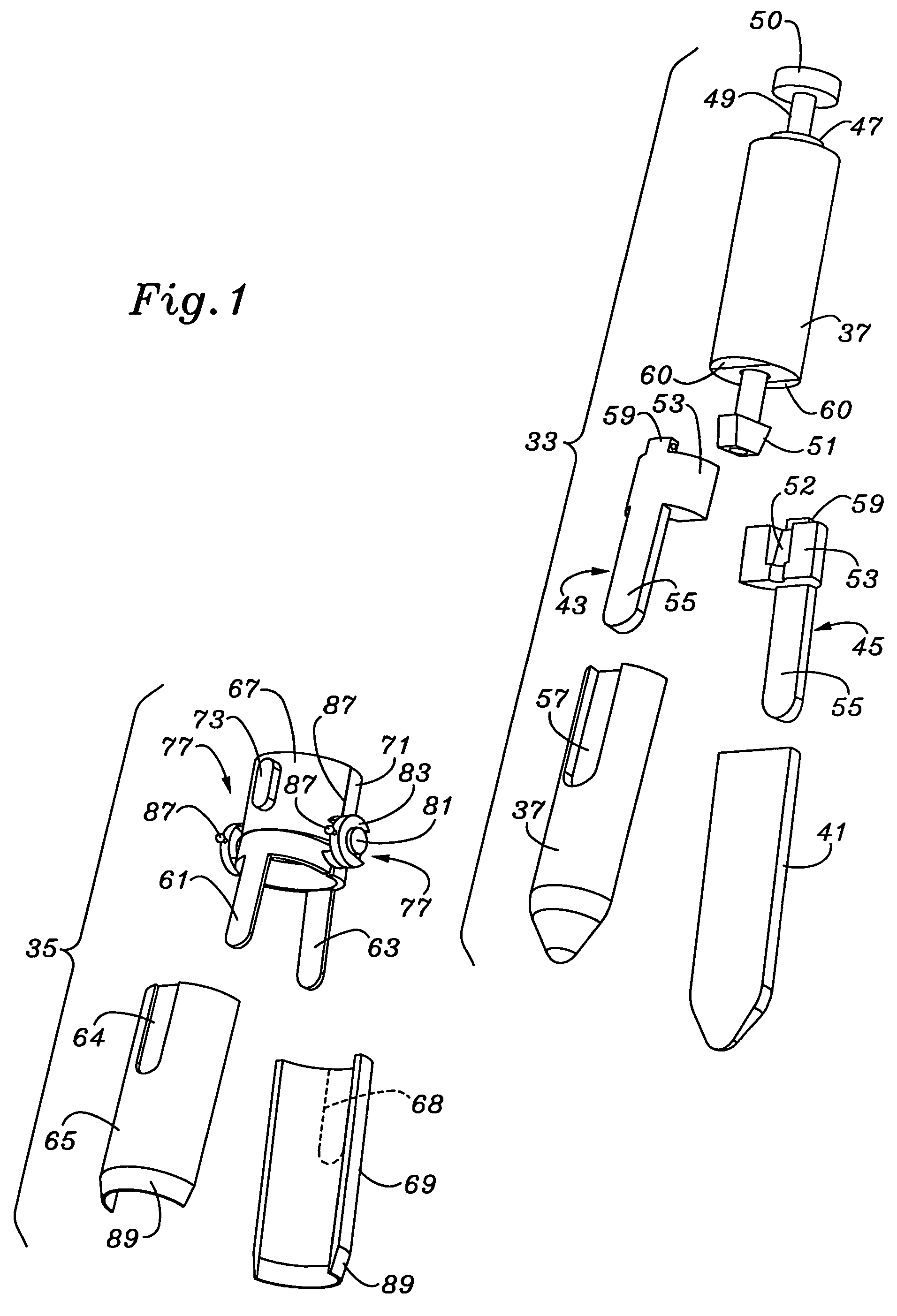
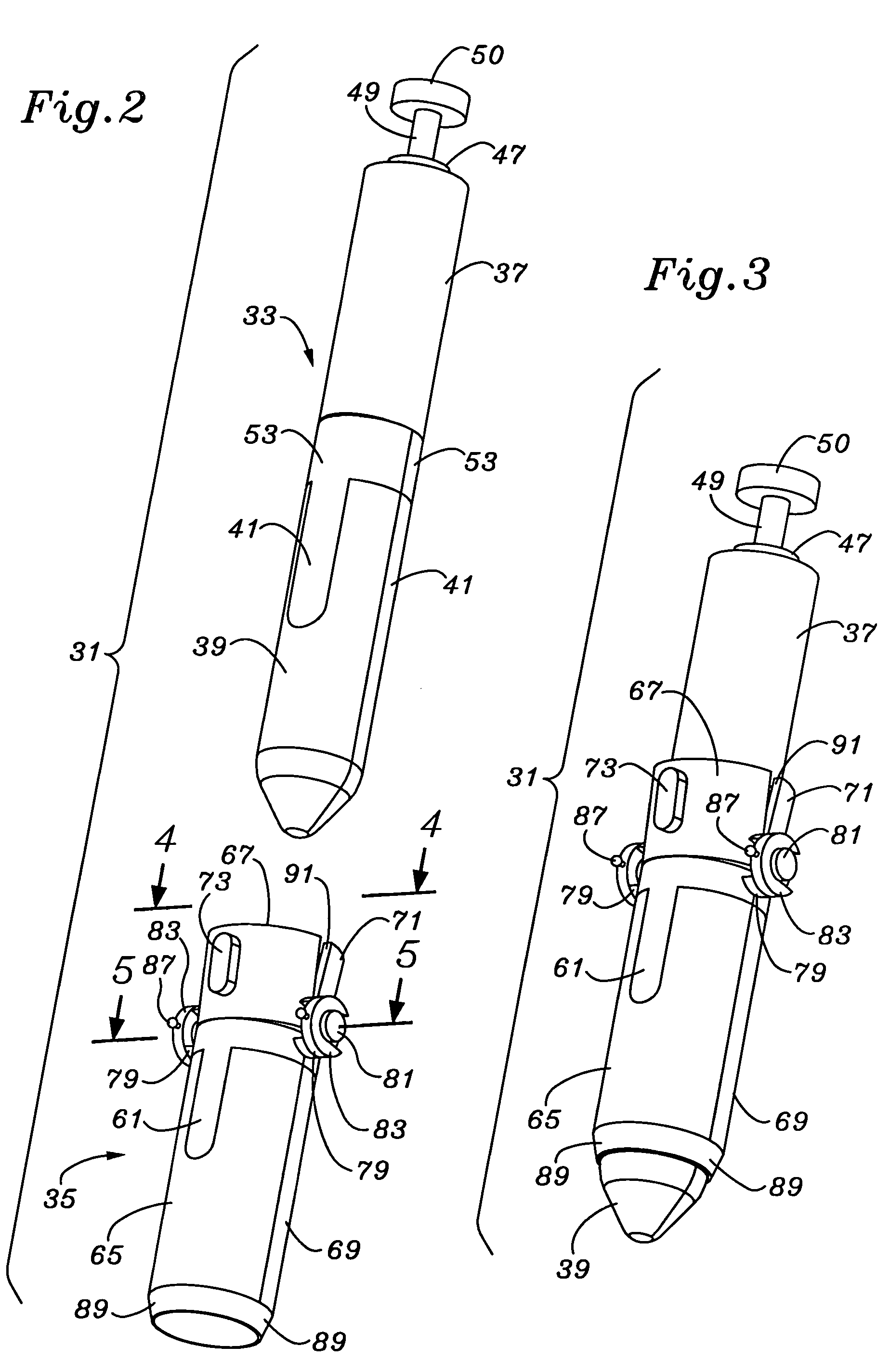
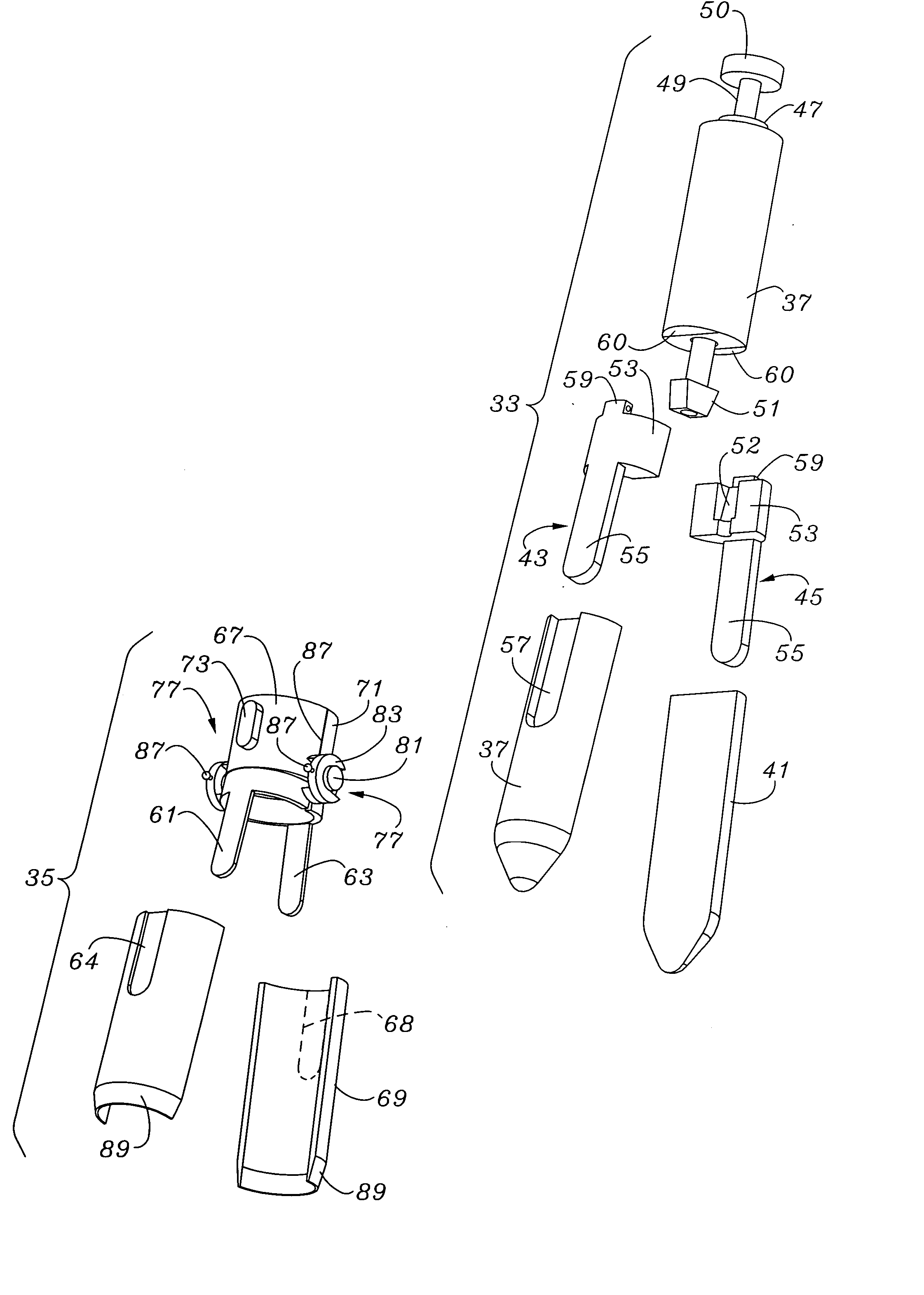
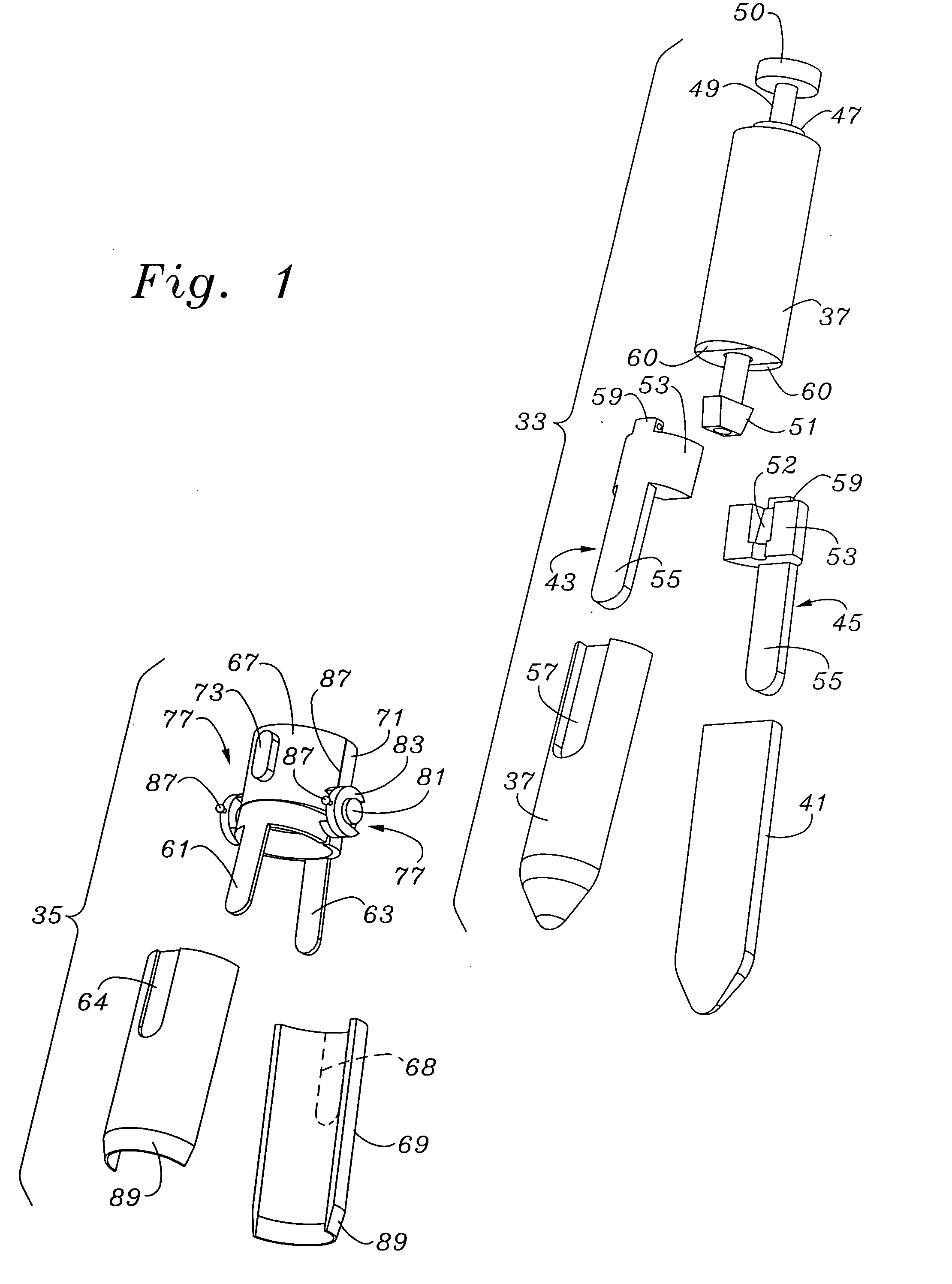
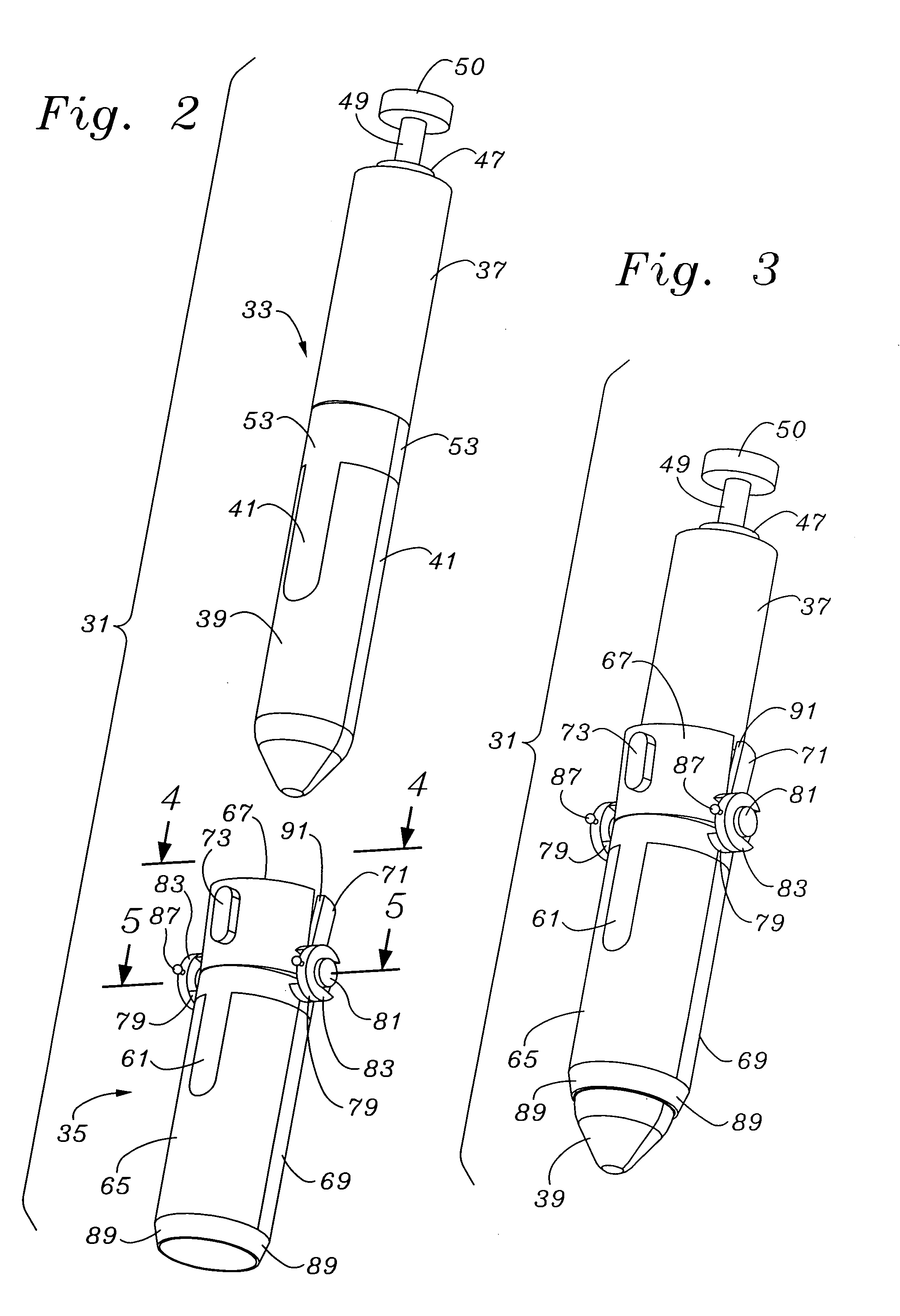
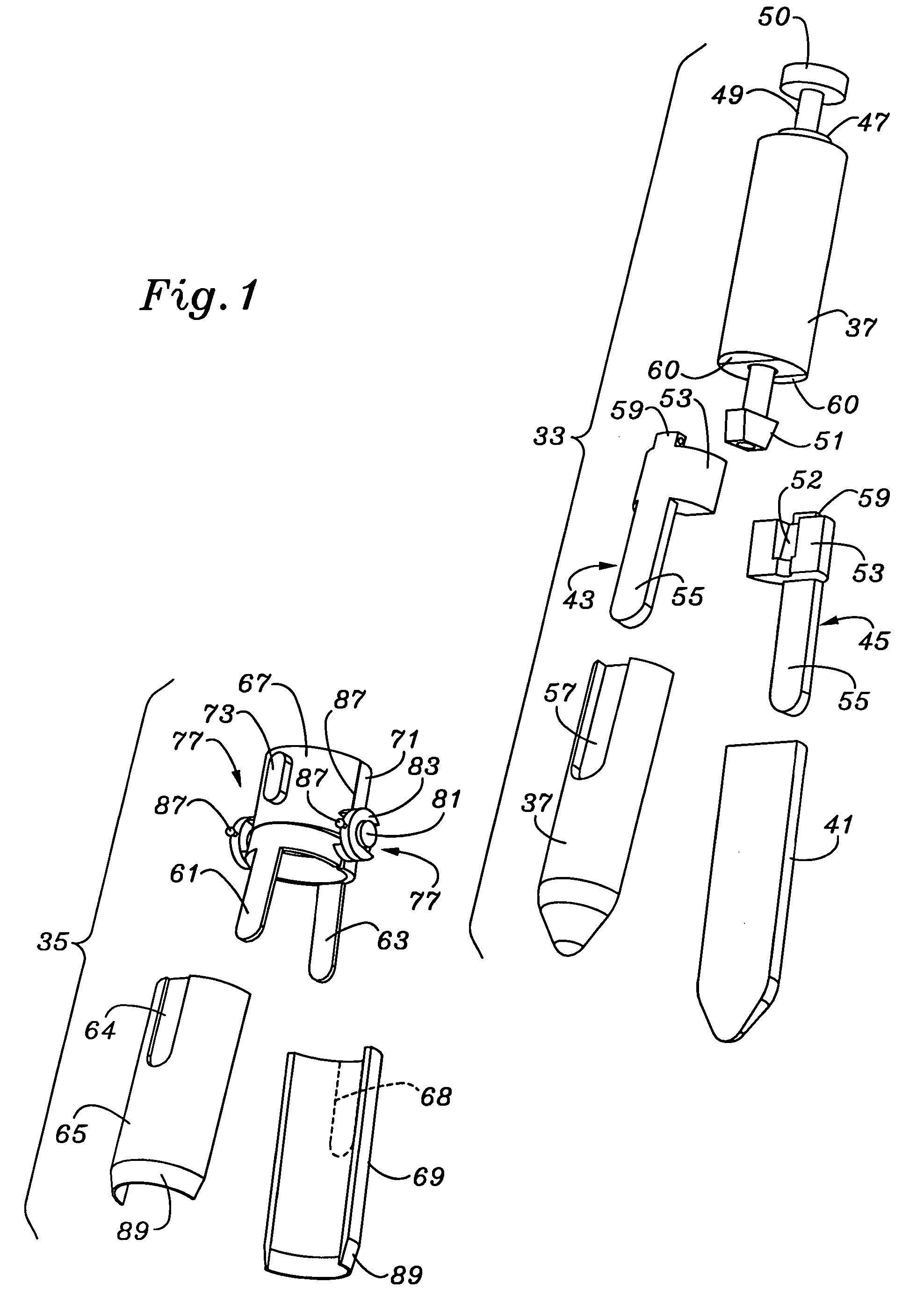
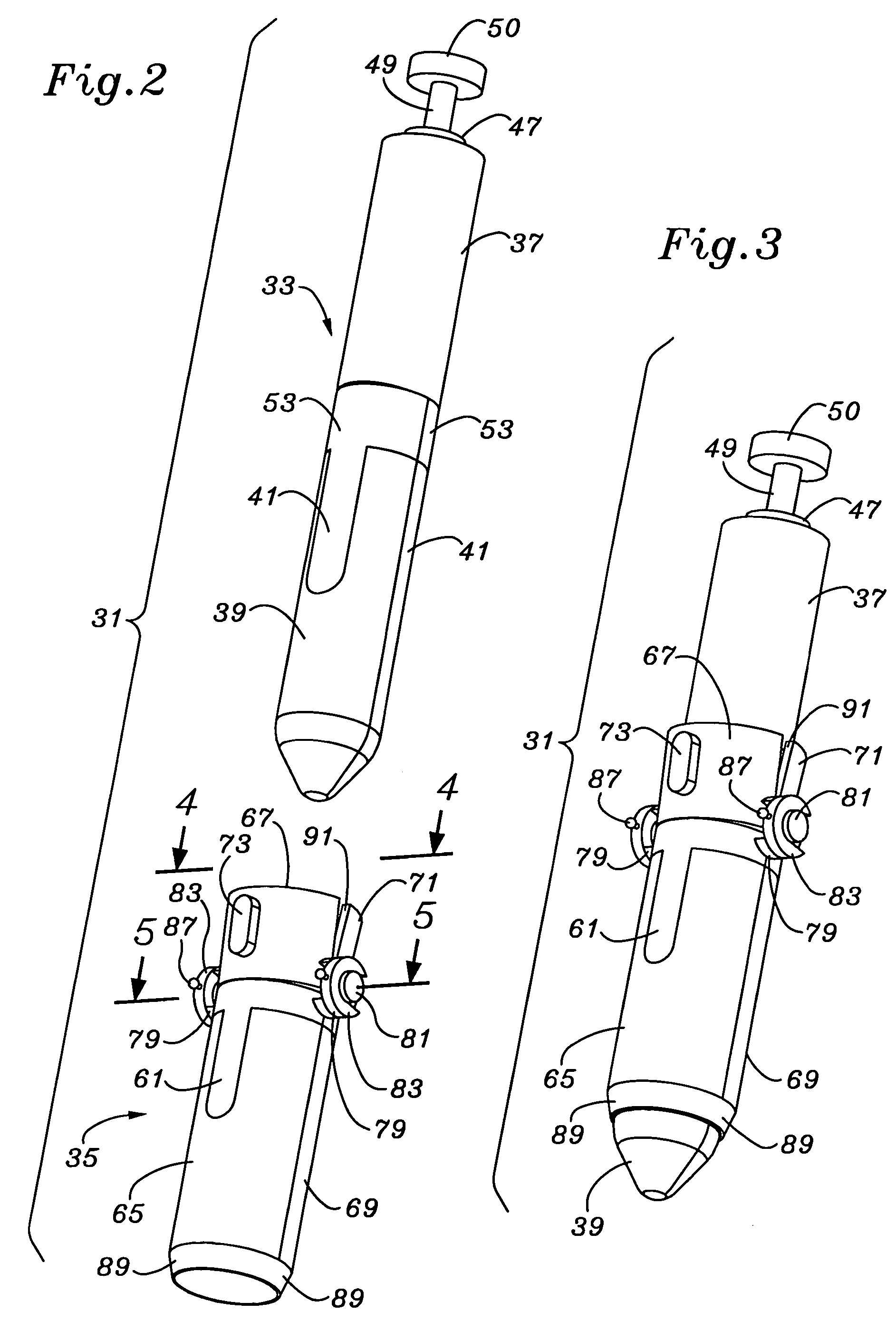
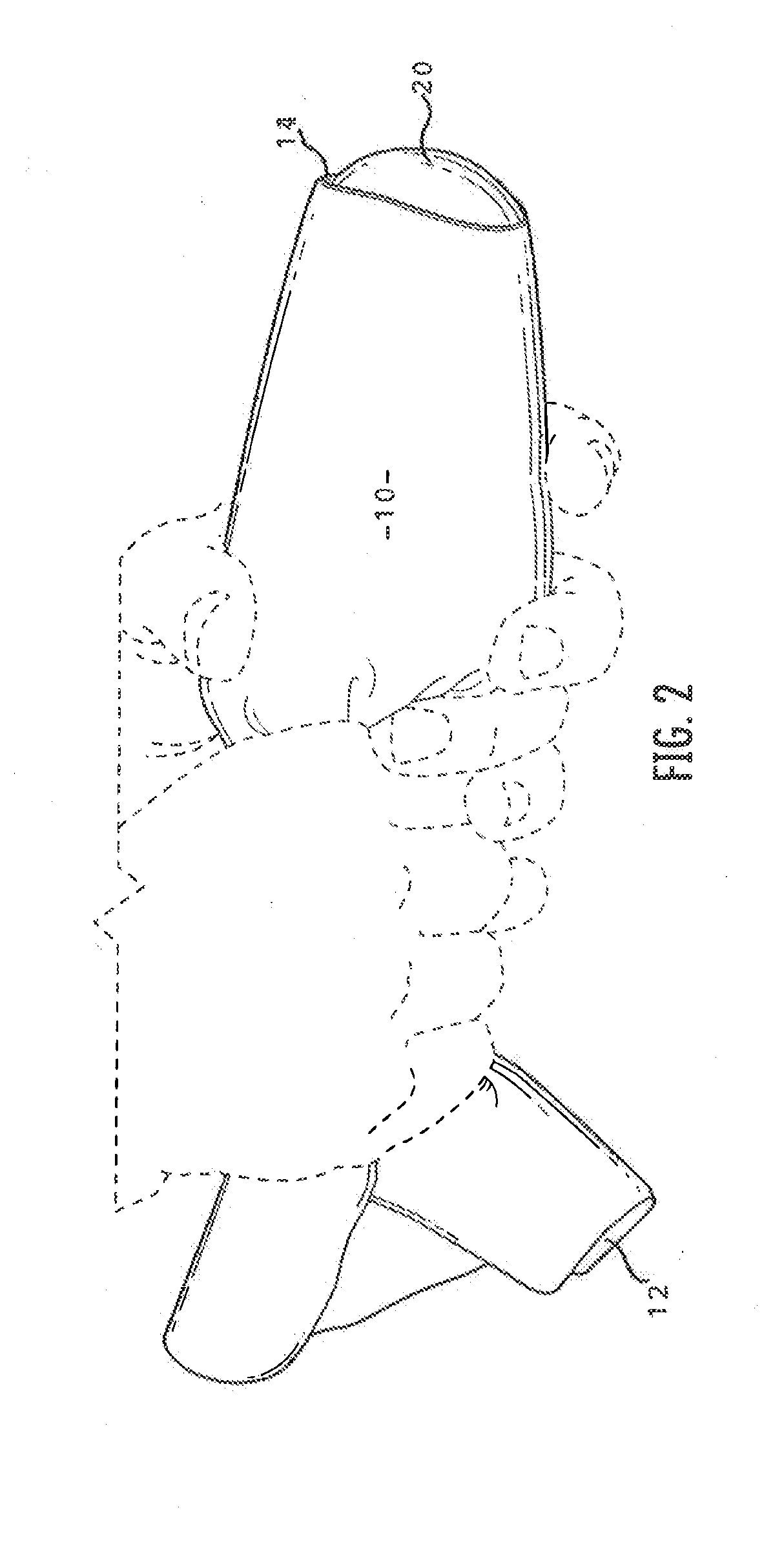
Minimal access lumbar diskectomy instrumentation and method
InactiveUS6849064B2Prevent surfaceEasy to separateCannulasInfusion syringesMuscle tissueSkin surface
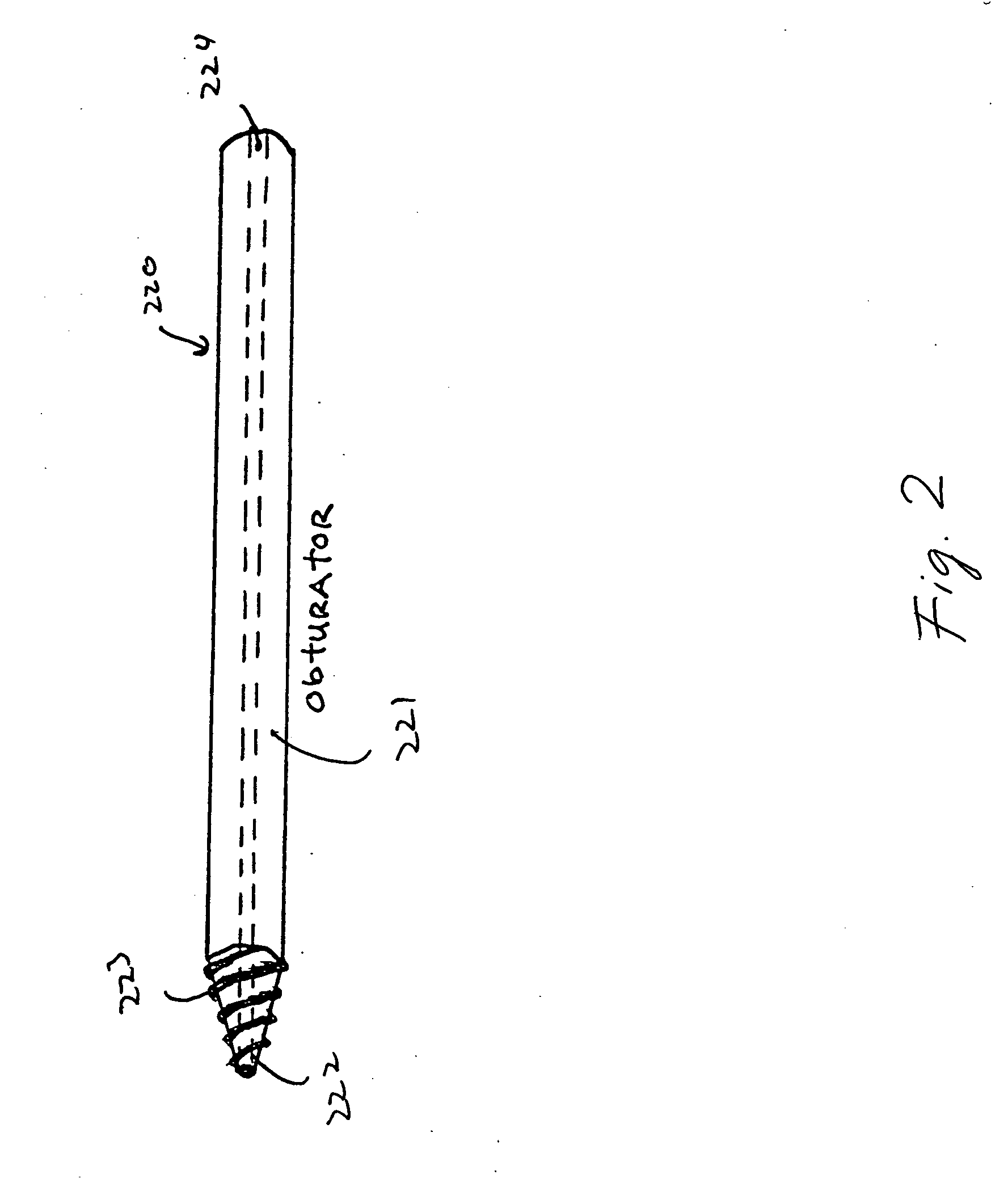
A minimal incision maximal access system allows for maximum desirable exposure along with maximum access to the operative field utilizing a minimum incision as small as the METRx and Endius systems. Instead of multiple insertions of dilating tubes the design is is a streamlined single entry device to avoid repetitive skin surface entry. The system offers the capability to expand to optimum exposure size for the surgery utilizing hinged bi-hemispherical or oval working tubes applied over an introducer obturator which is controllably dilated to slowly separate muscle tissue. Deeper end working and visualization areas with maximum proximal access and work dimensions are provided to makes the operative procedure safer in application and shorten the surgeons's learning curve because it most closely approximates the ability to use open microdiskectomy techniques.
Owner:K2M
Insertable device and system for minimal access procedure
ActiveUS20050014994A1Expand accessMinimal incisionEndoscopesLaproscopesAbdominal cavityDegrees of freedom
The present invention provides a system and single or multi-functional element device that can be inserted and temporarily placed or implanted into a structure having a lumen or hollow space, such as a subject's abdominal cavity to provide therewith access to the site of interest in connection with minimally invasive surgical procedures. The insertable device may be configured such that the functional elements have various degrees of freedom of movement with respect to orienting the functional elements or elements to provide access to the site from multiple and different orientations / perspectives as the procedure dictates, e.g., to provide multiple selectable views of the site, and may provide a stereoscopic view of the site of interest.
Owner:THE TRUSTEES OF COLUMBIA UNIV IN THE CITY OF NEW YORK
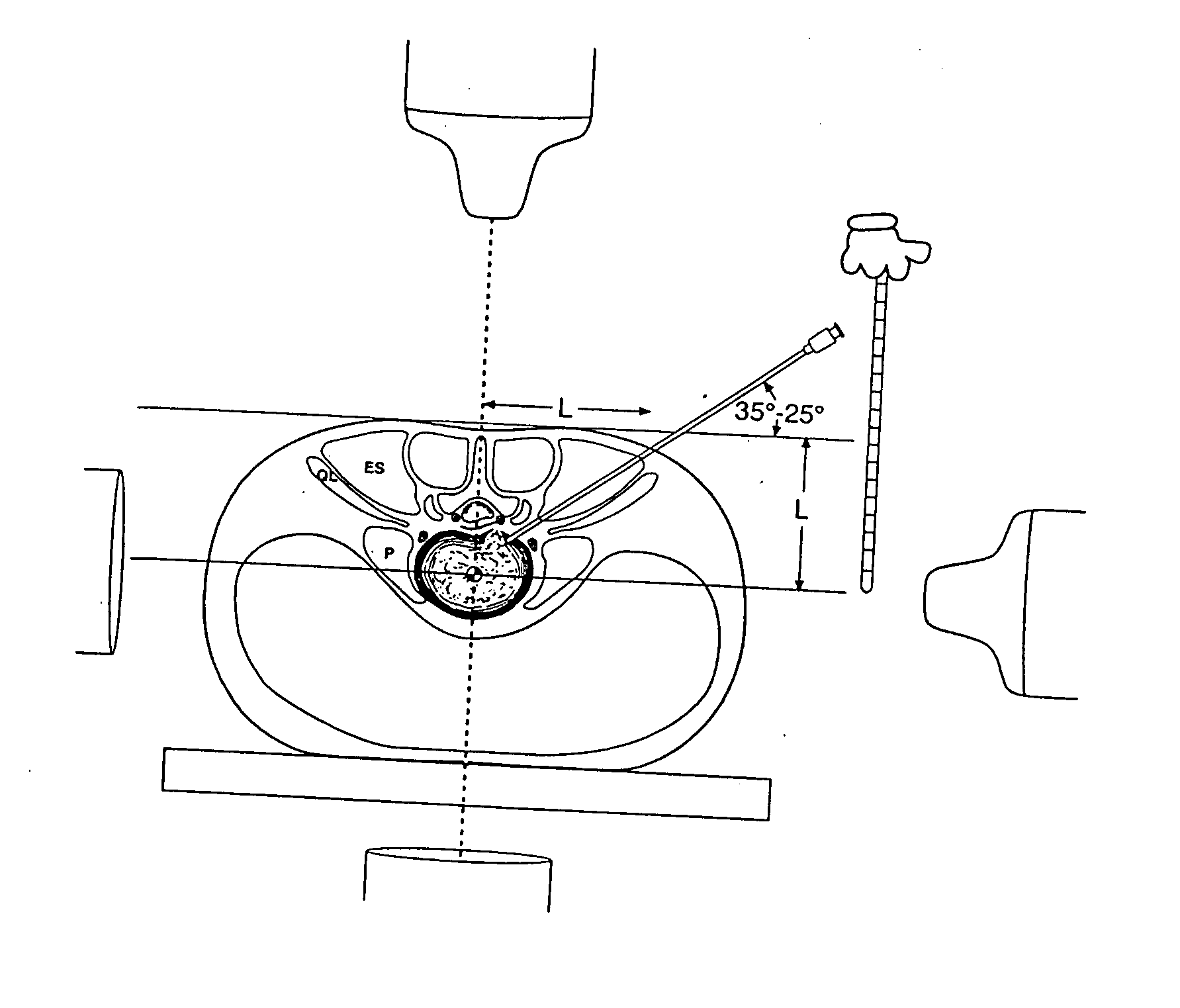
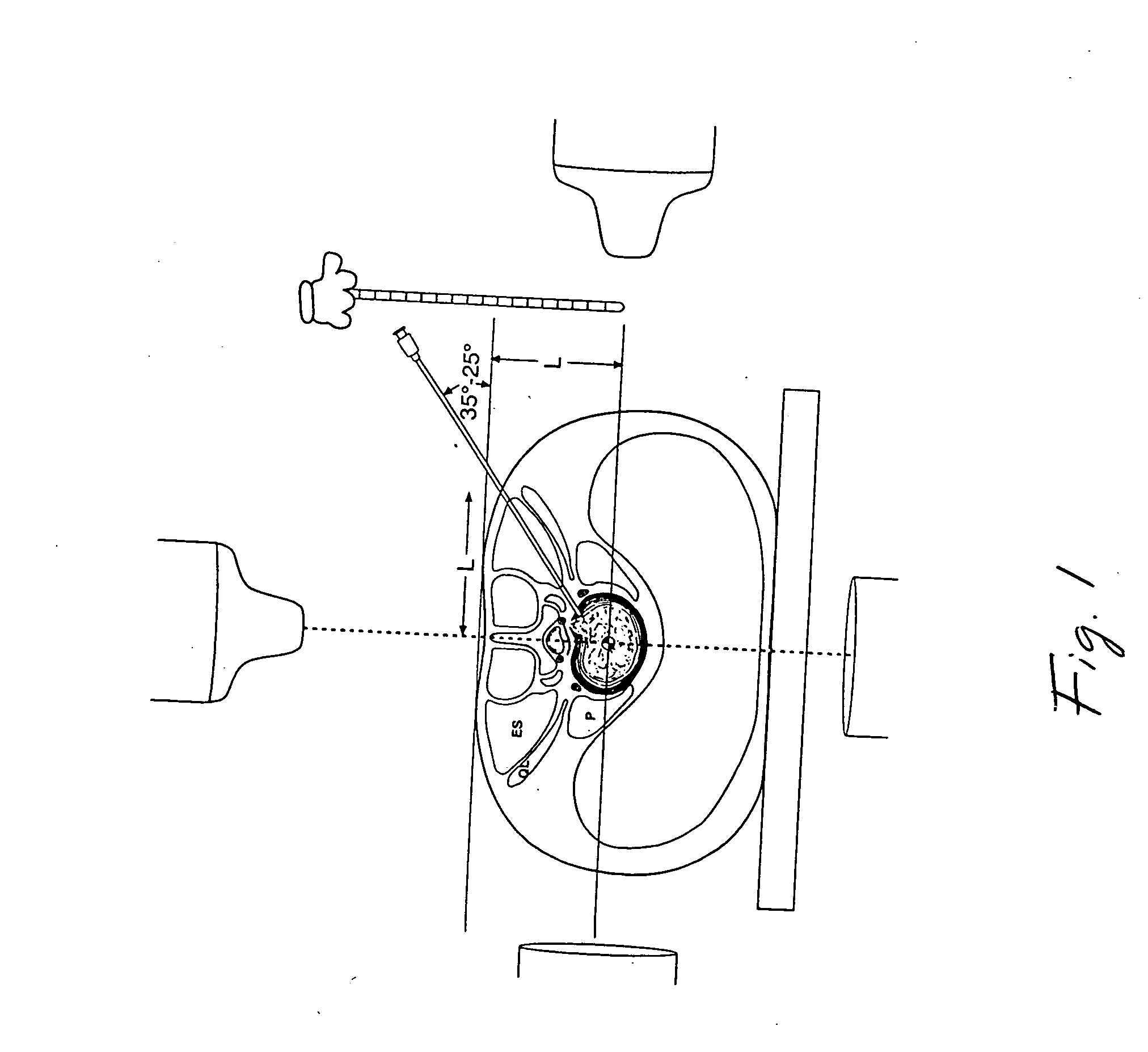
Minimal access apparatus for endoscopic spinal surgery
A system for minimal access soft tissue dilating and retracting and nucleus pulposus excision tools for endoscopic spinal surgery, includes elements to seek the appropriate trajectory, creation of soft tissue tunnel space, and retractors for the tunnels.
Owner:TSOU PAUL M
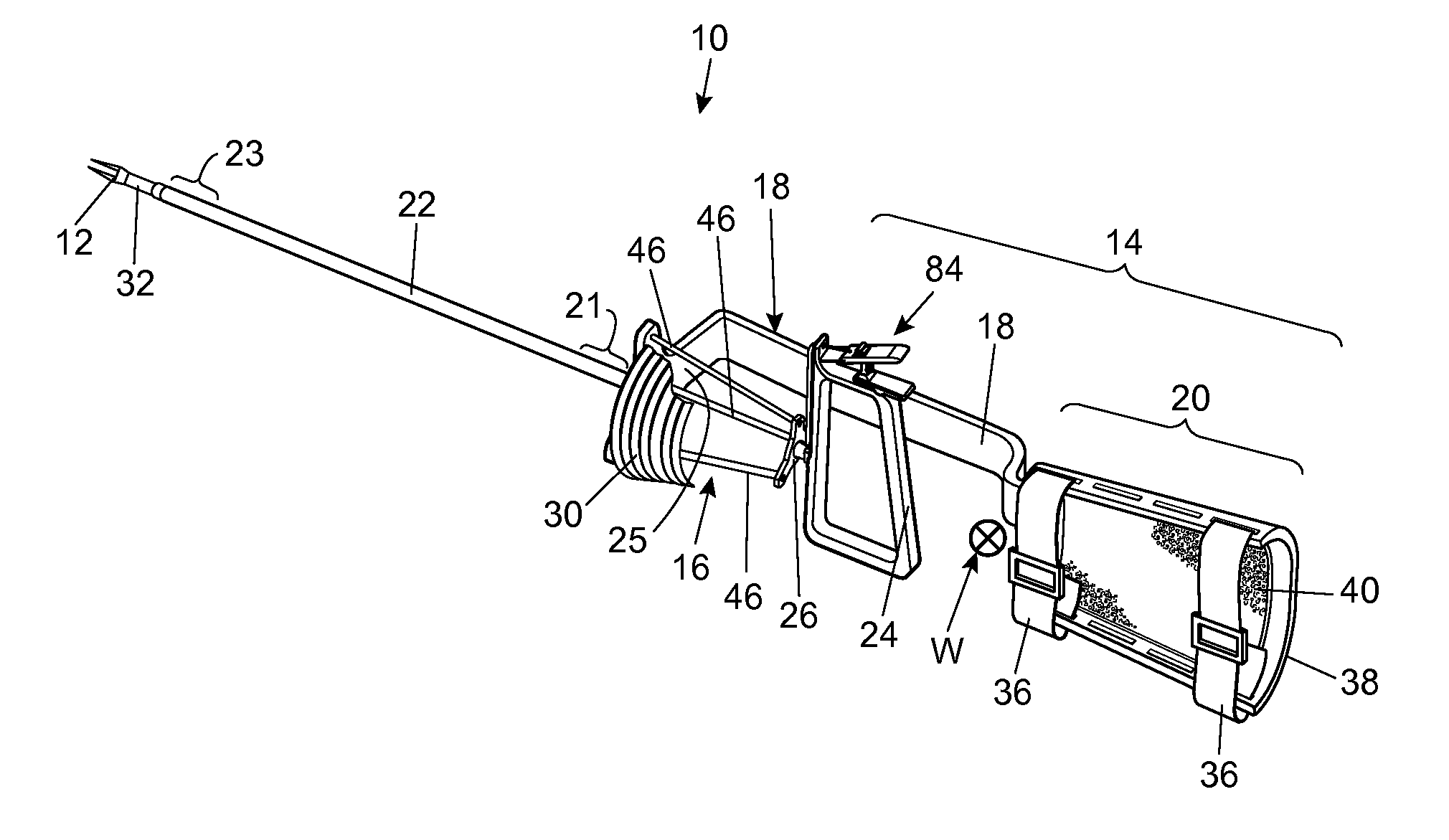
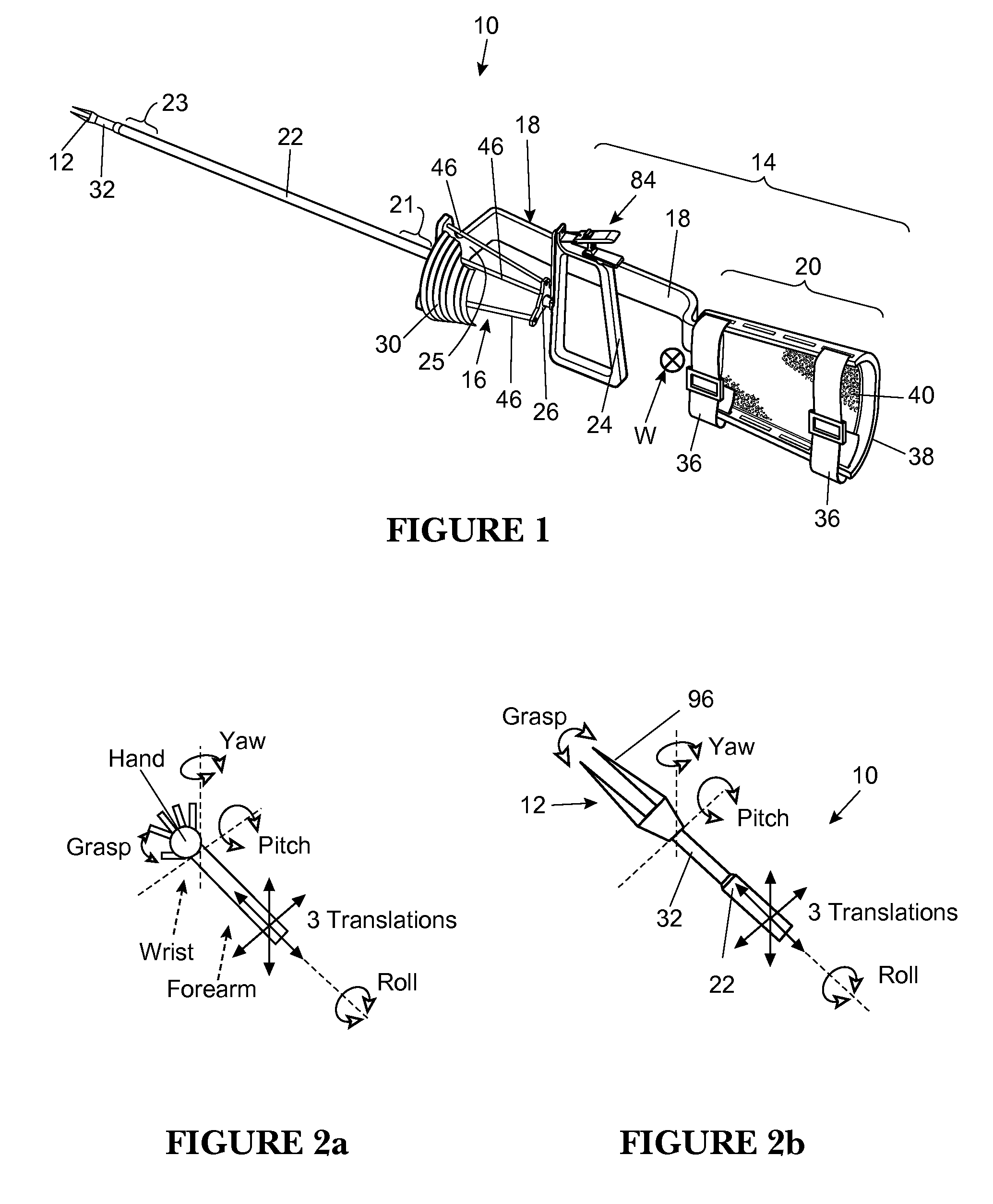
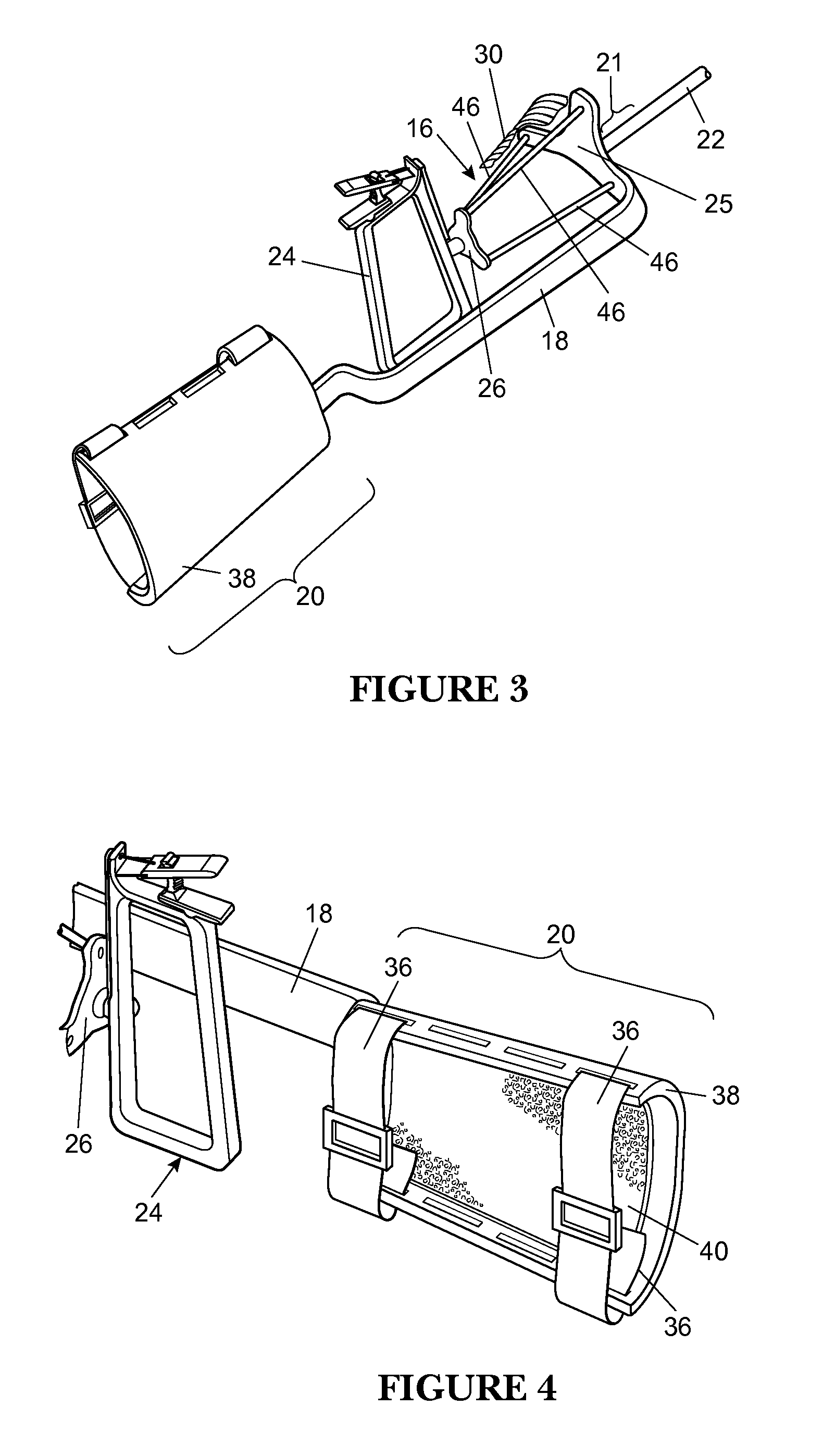
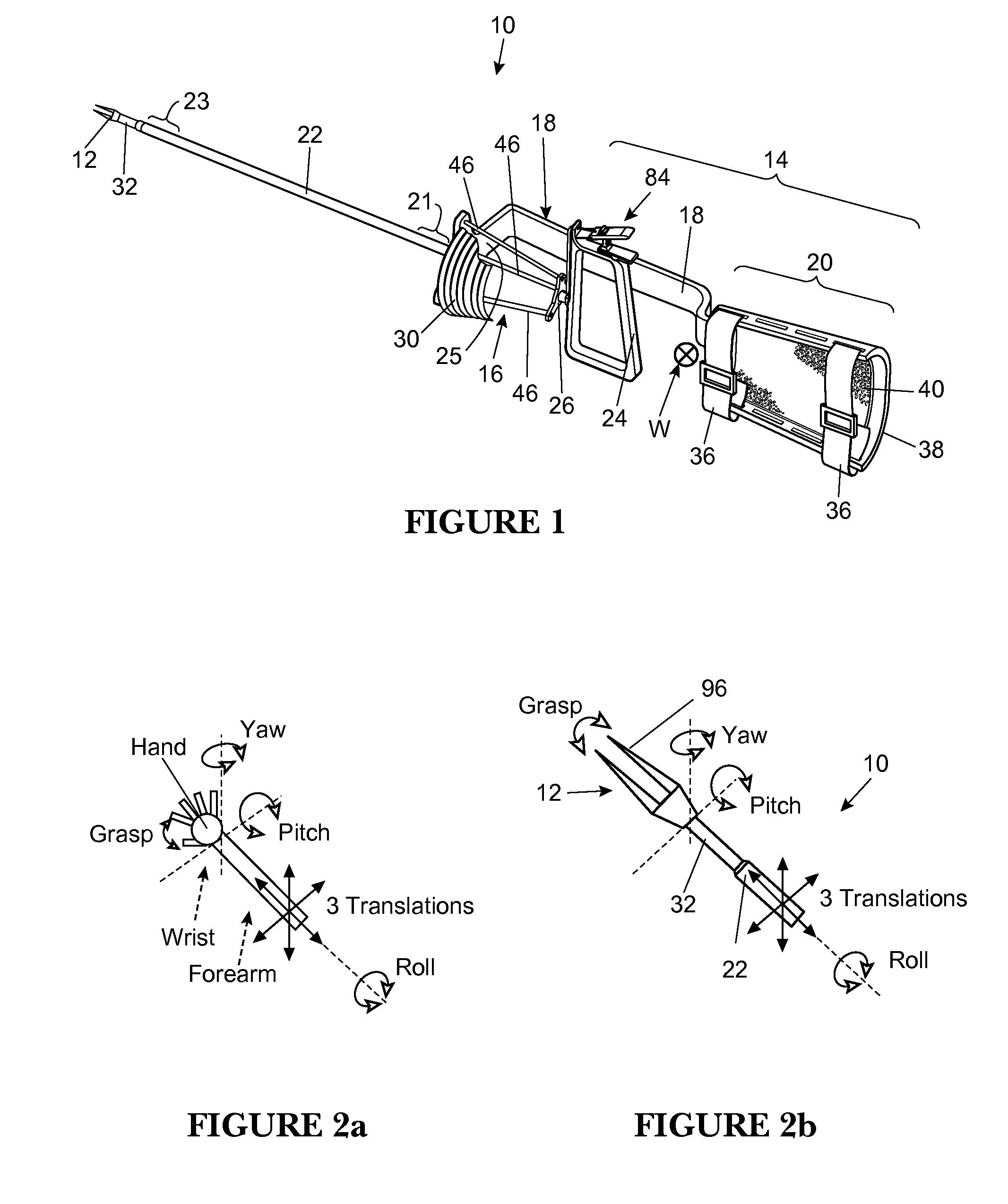
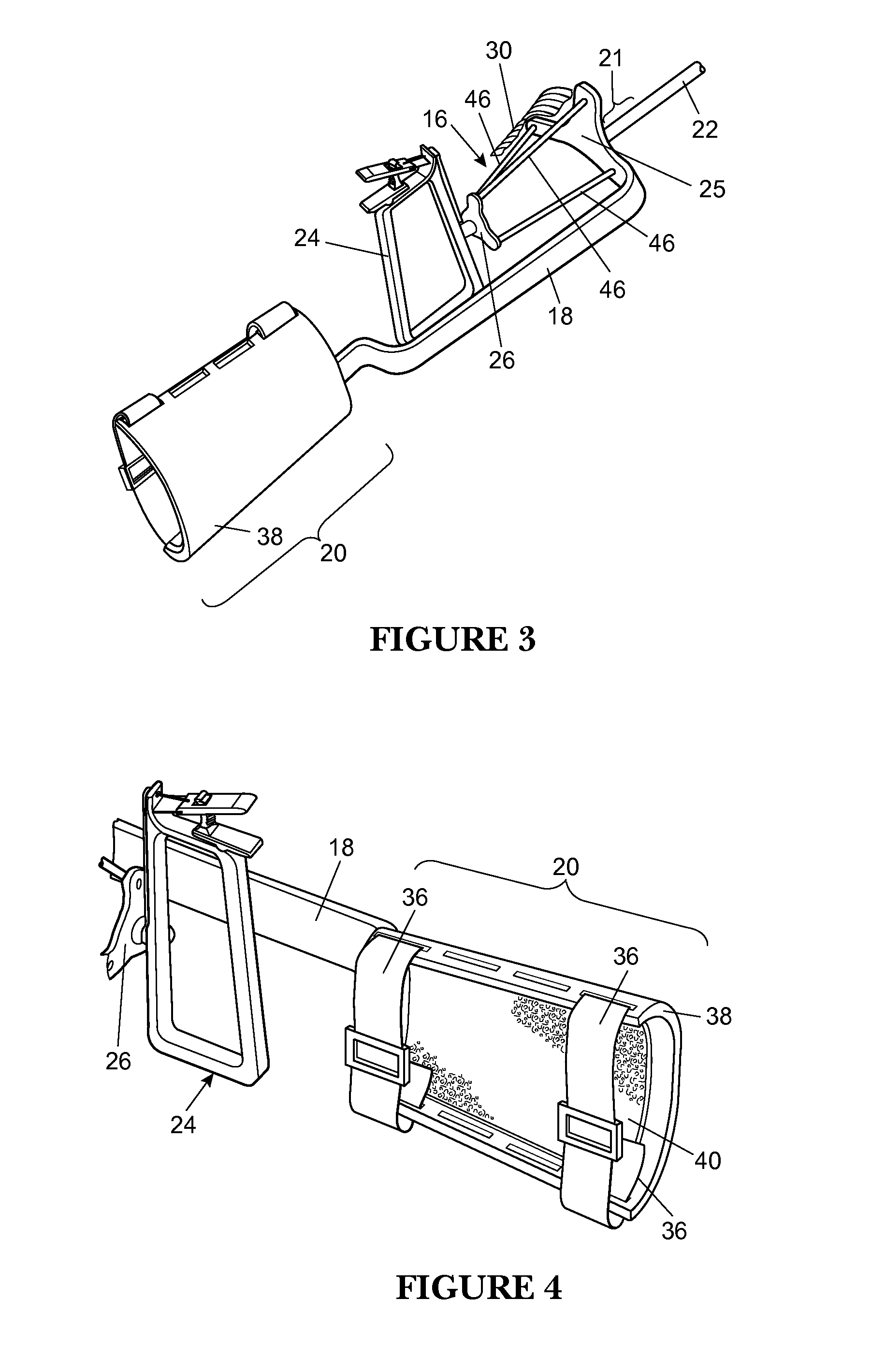
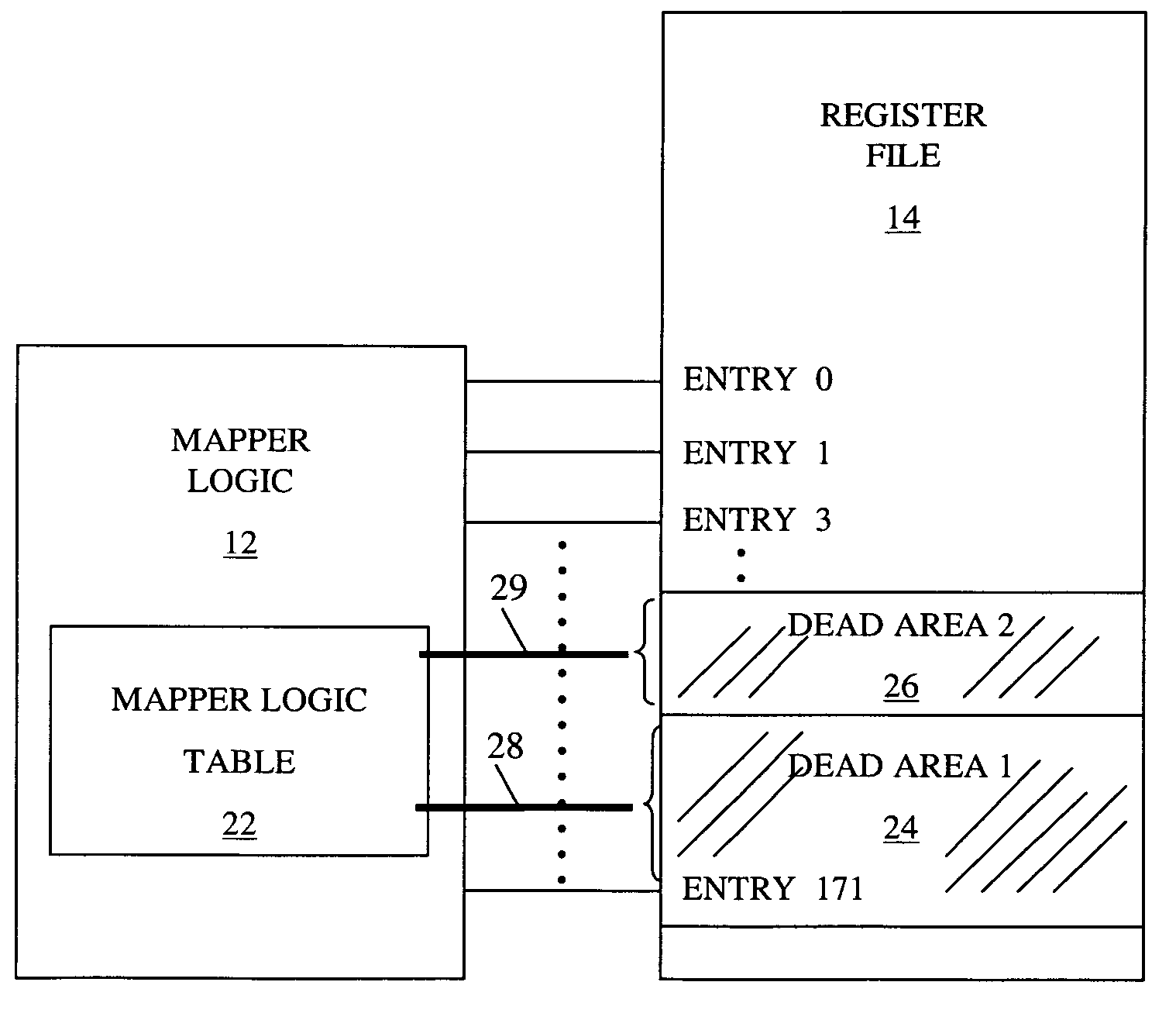
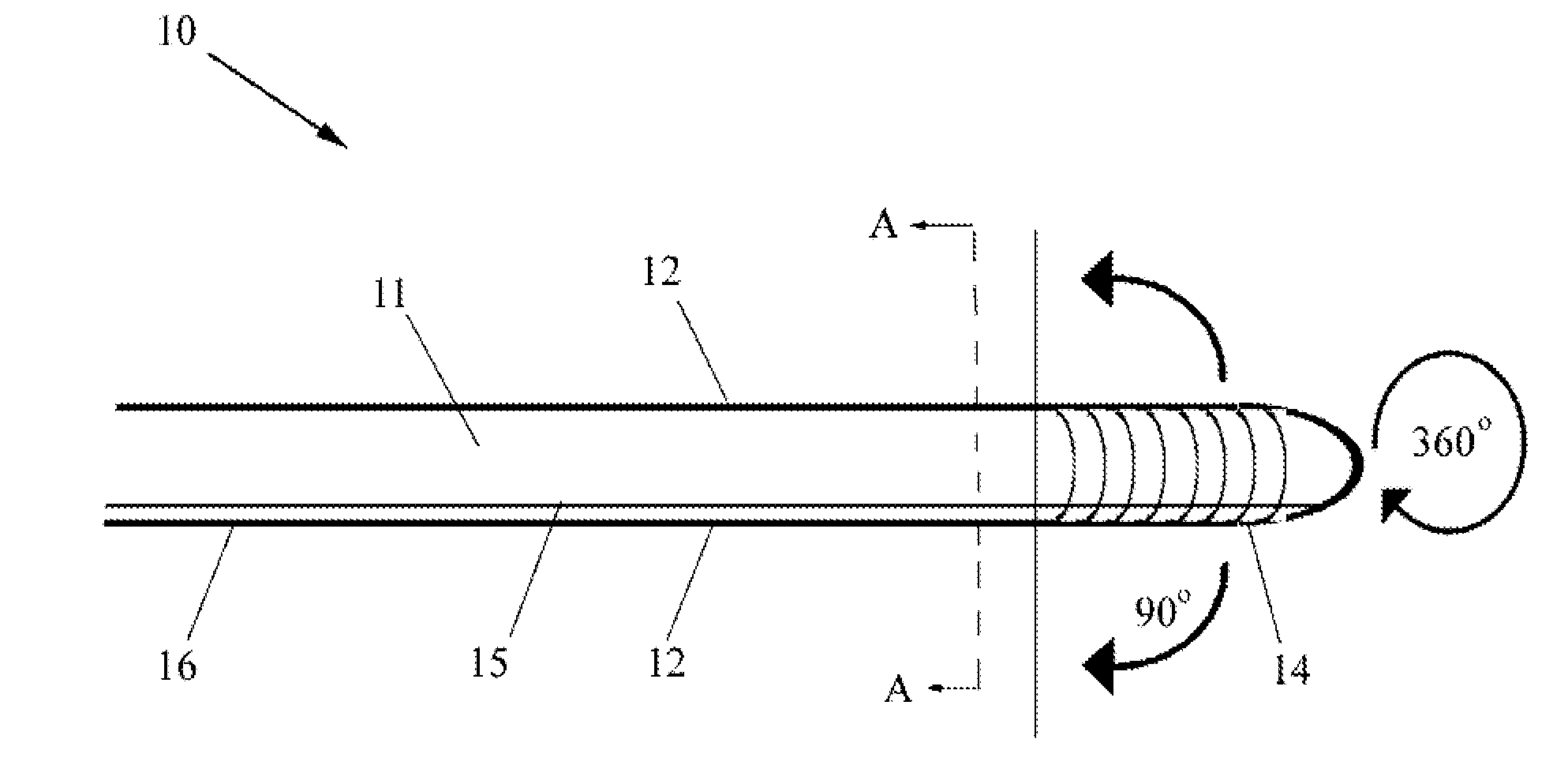
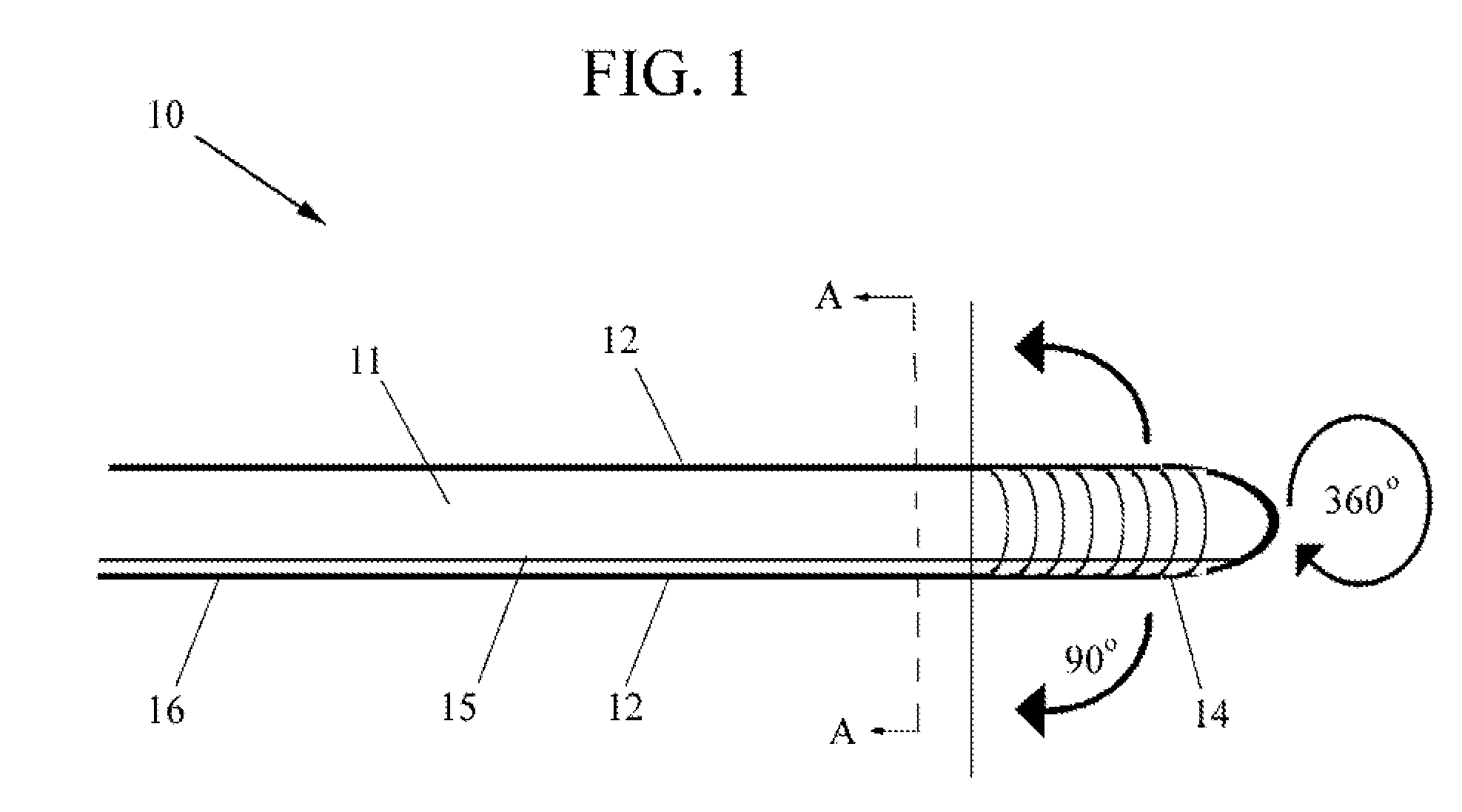
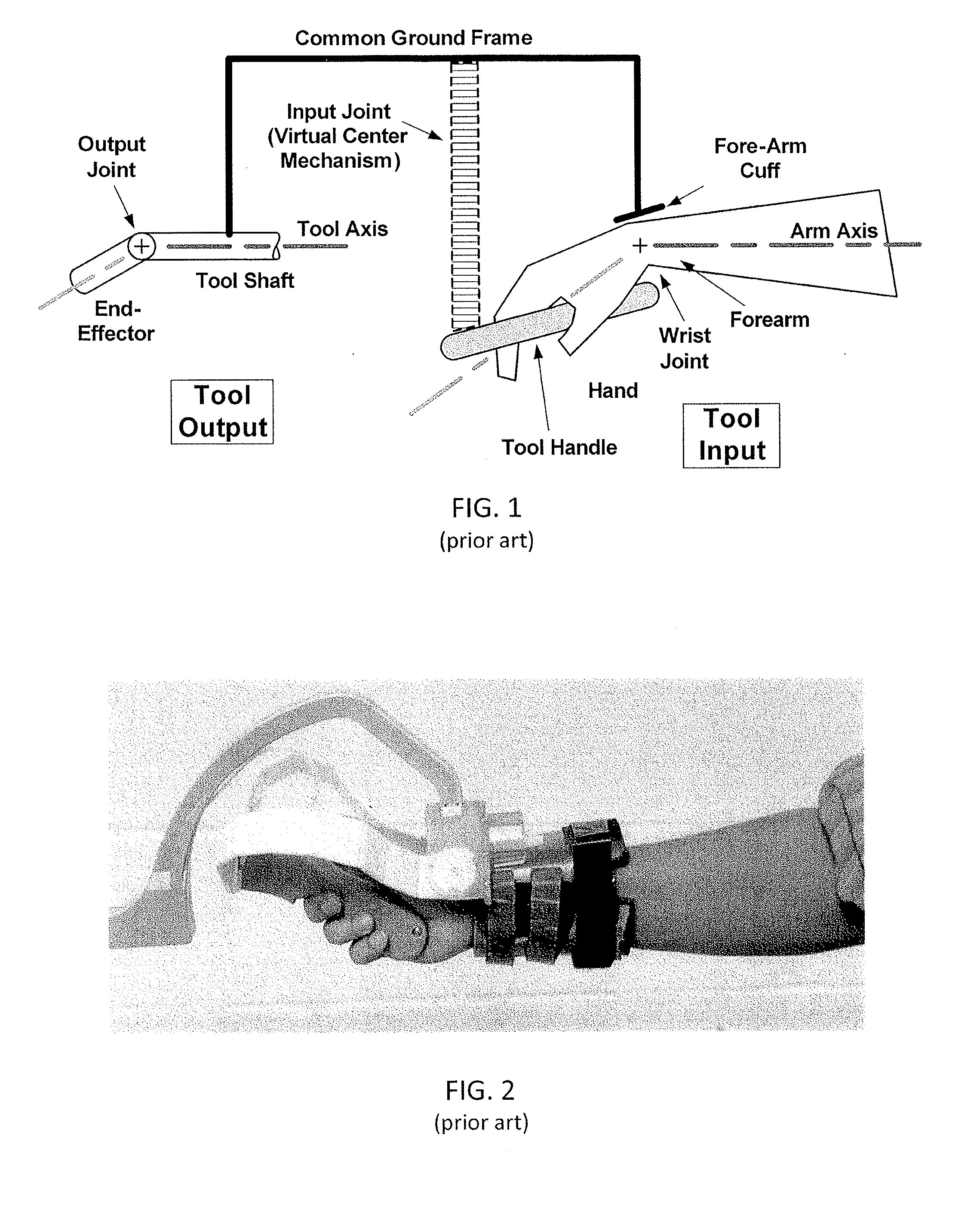
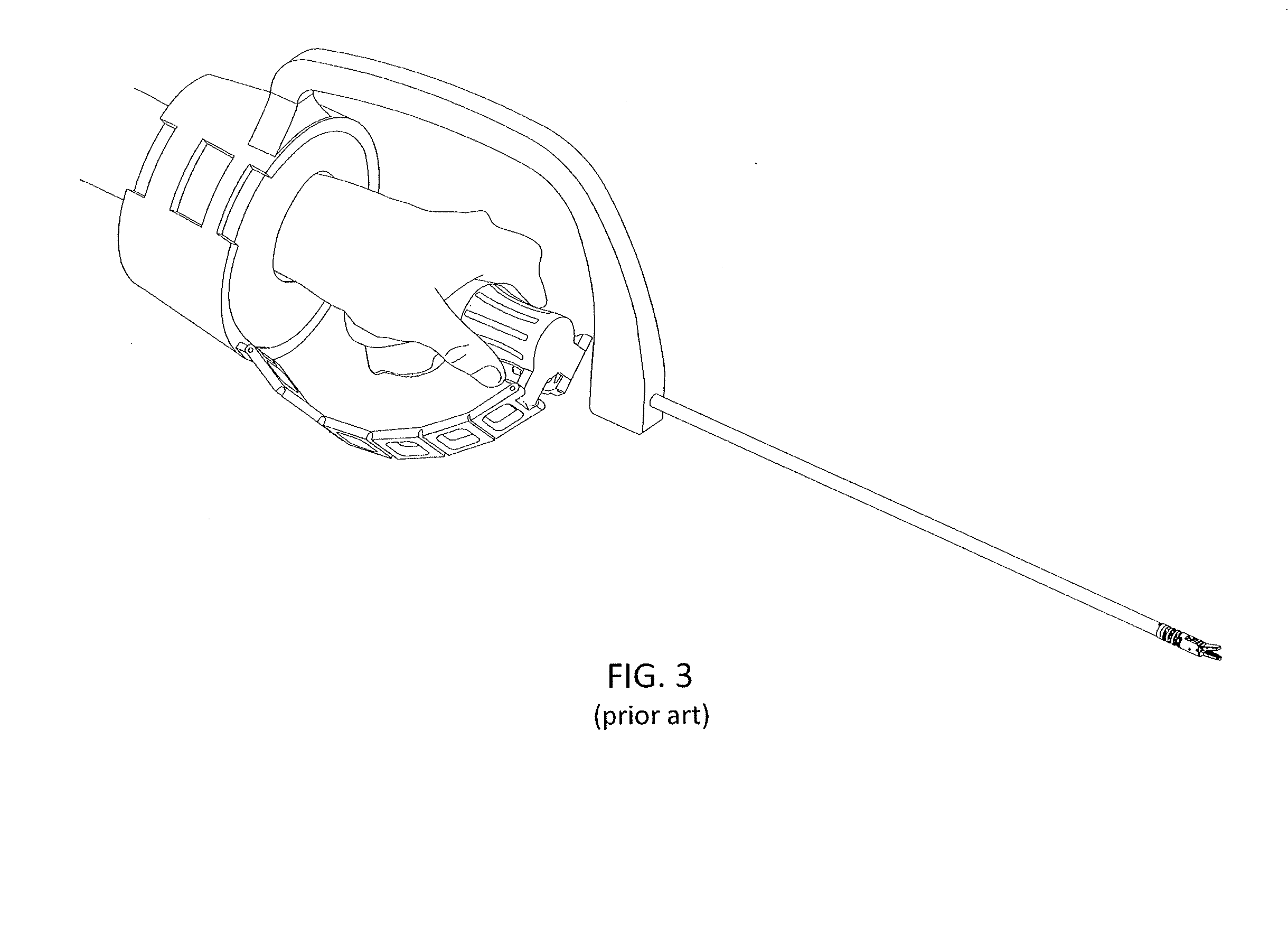
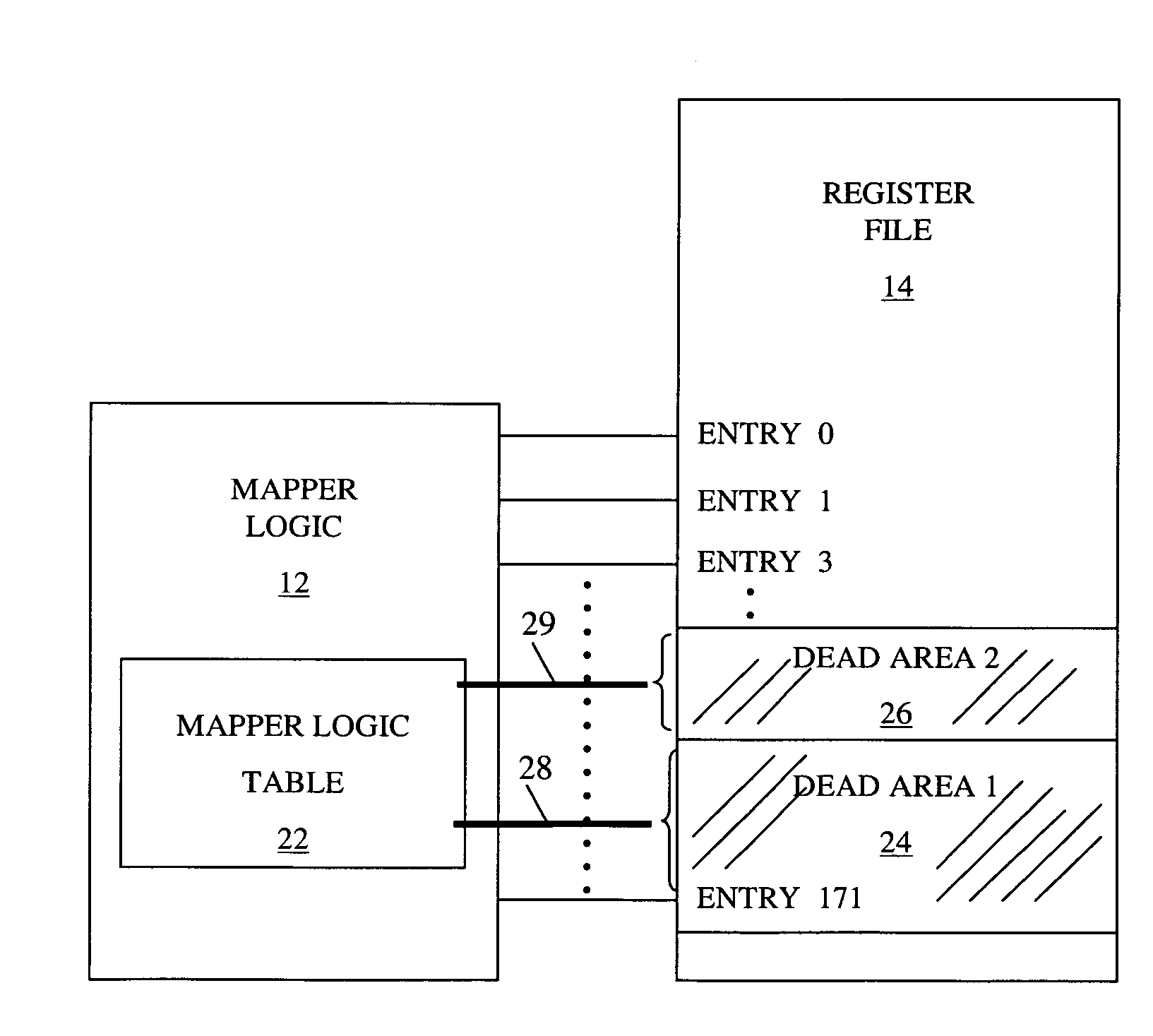
Minimal access tool
A minimal access tool includes a frame arranged to be attached to an arm of a user, a tool shaft having a proximal end and a distal end, where the tool shaft proximal end is connected to the frame. The tool further includes an input joint having a first end connected to the frame and a second end arranged to receive user input, the input joint including a virtual center-of-rotation (VC) mechanism which provides a center of rotation that generally coincides with a wrist joint of the user. An output joint is connected to the tool shaft distal end, where the output joint is coupled to the input joint via a mechanical transmission connected therebetween to correlate motion of the input joint to motion of the output joint.
Owner:RGT UNIV OF MICHIGAN
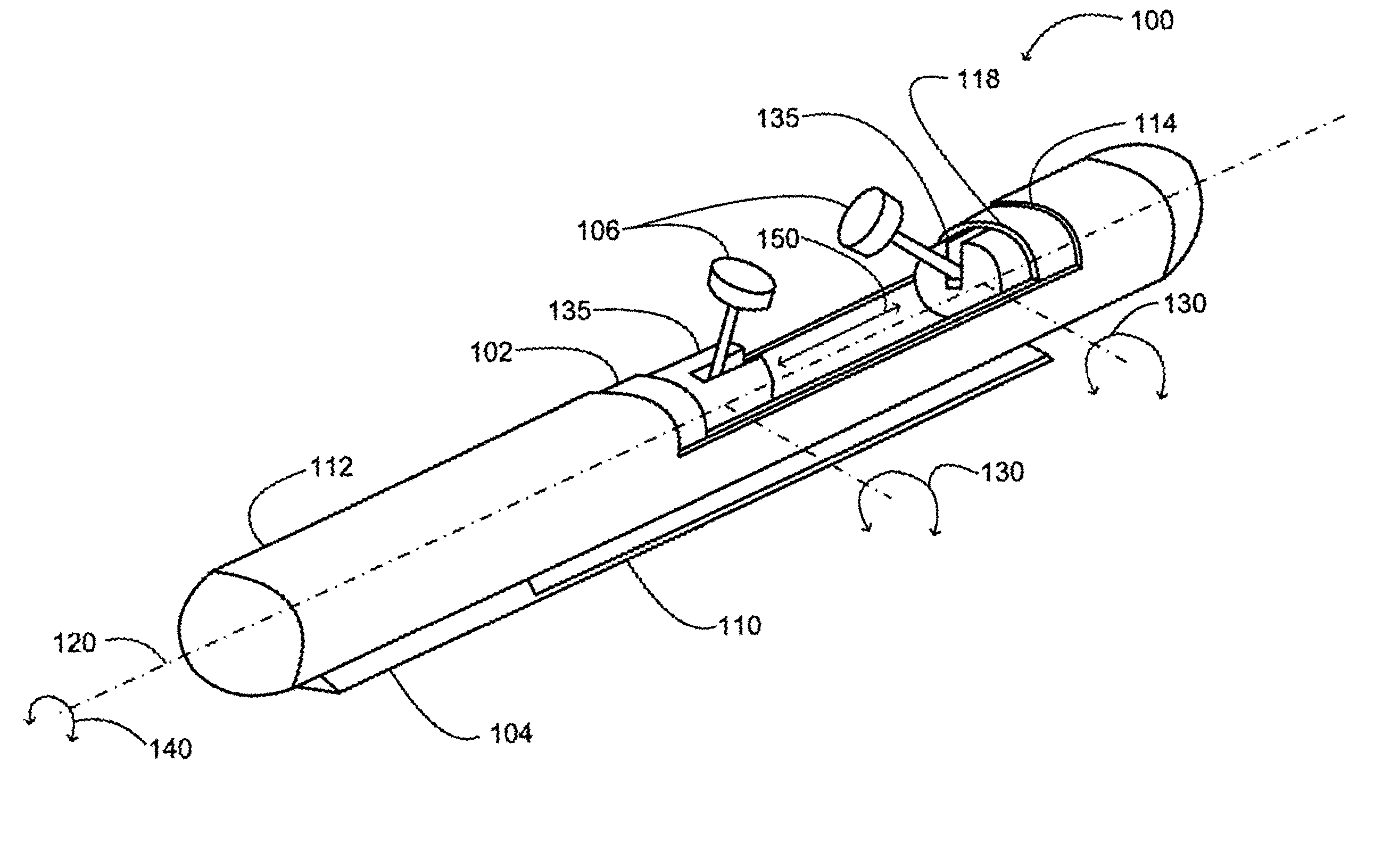
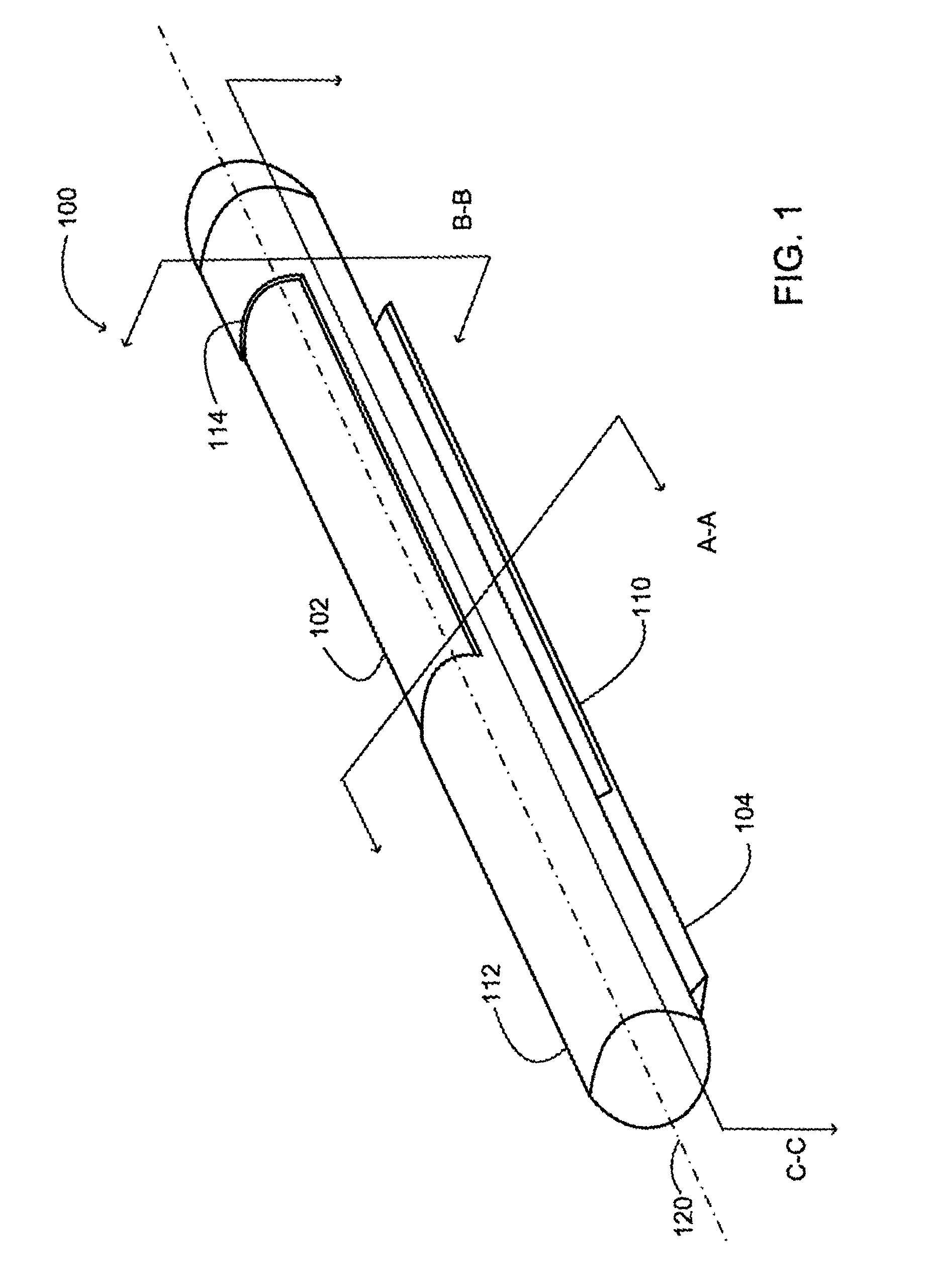
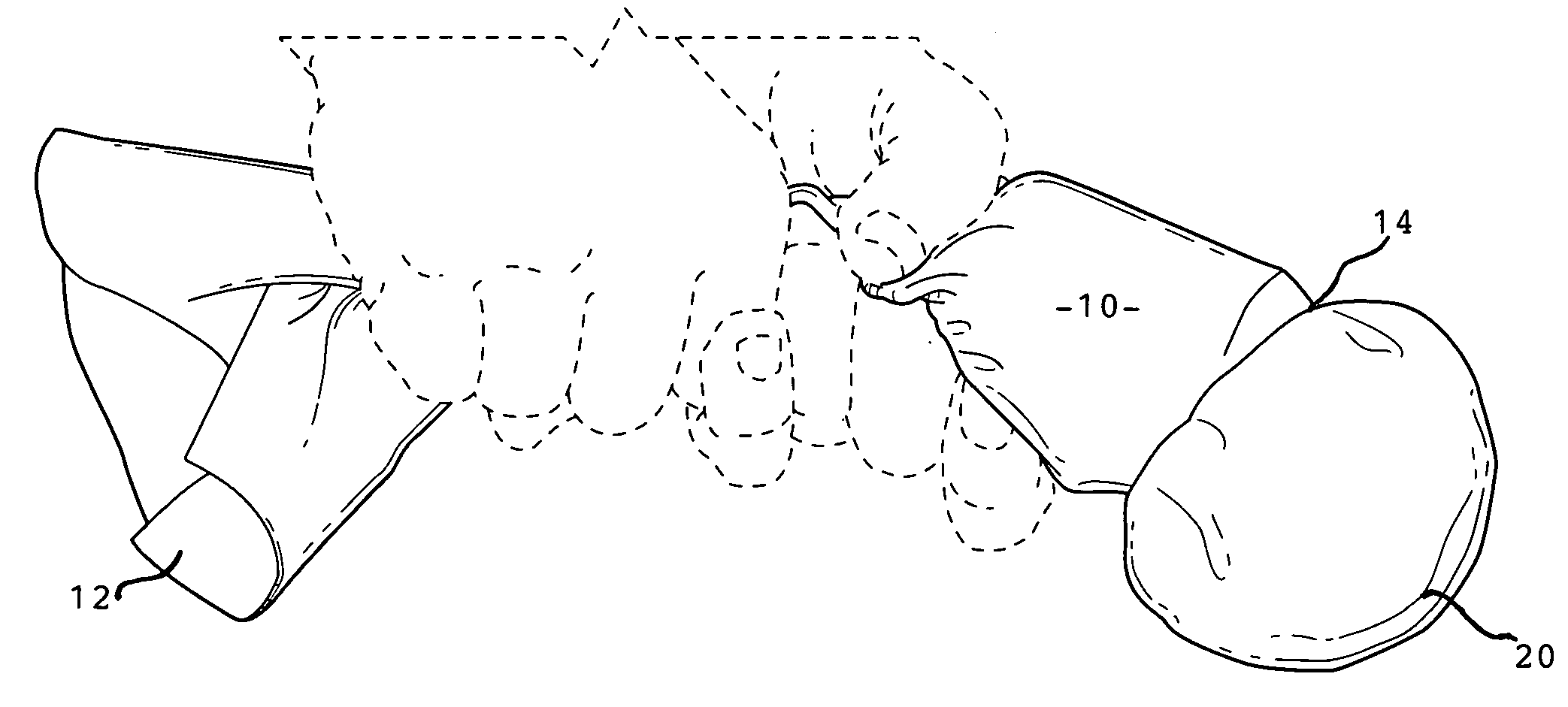
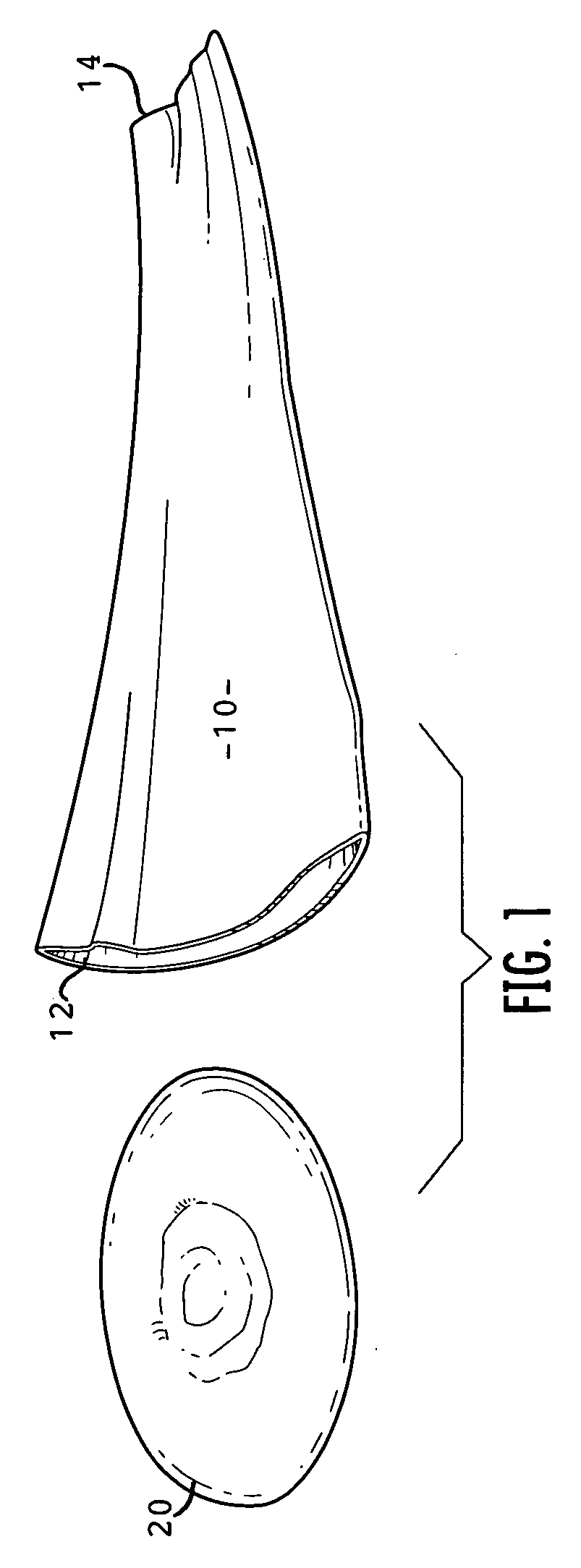
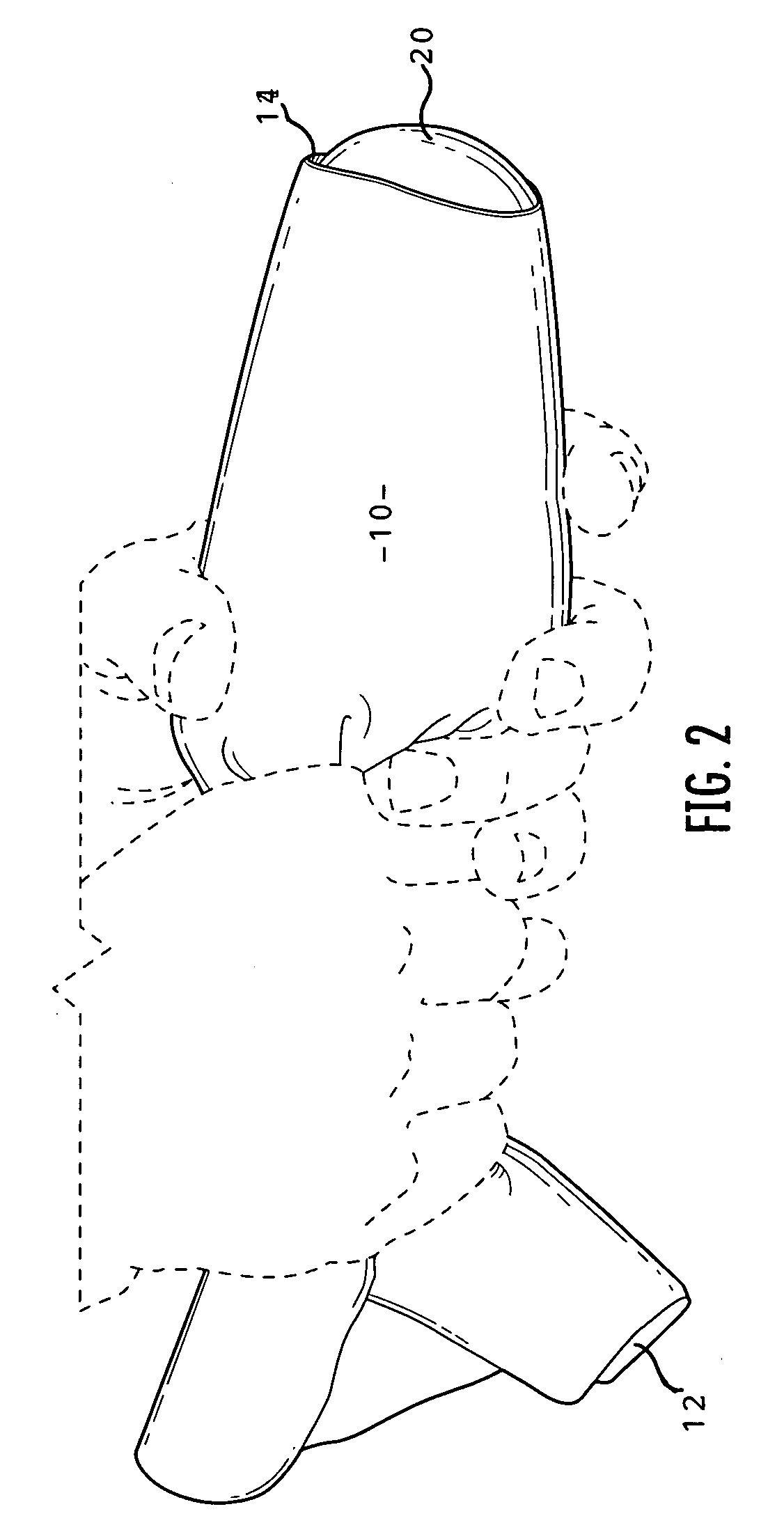
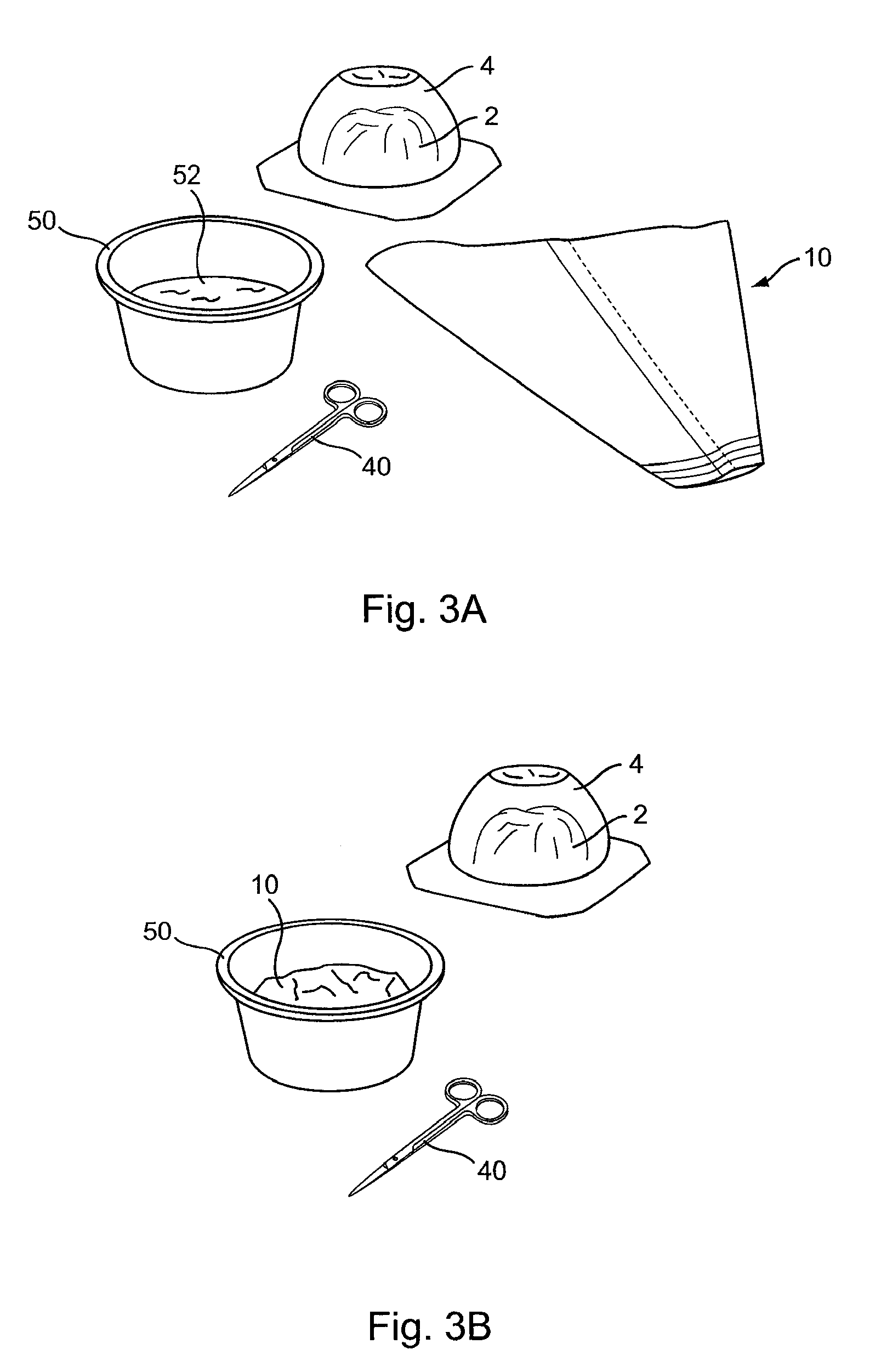
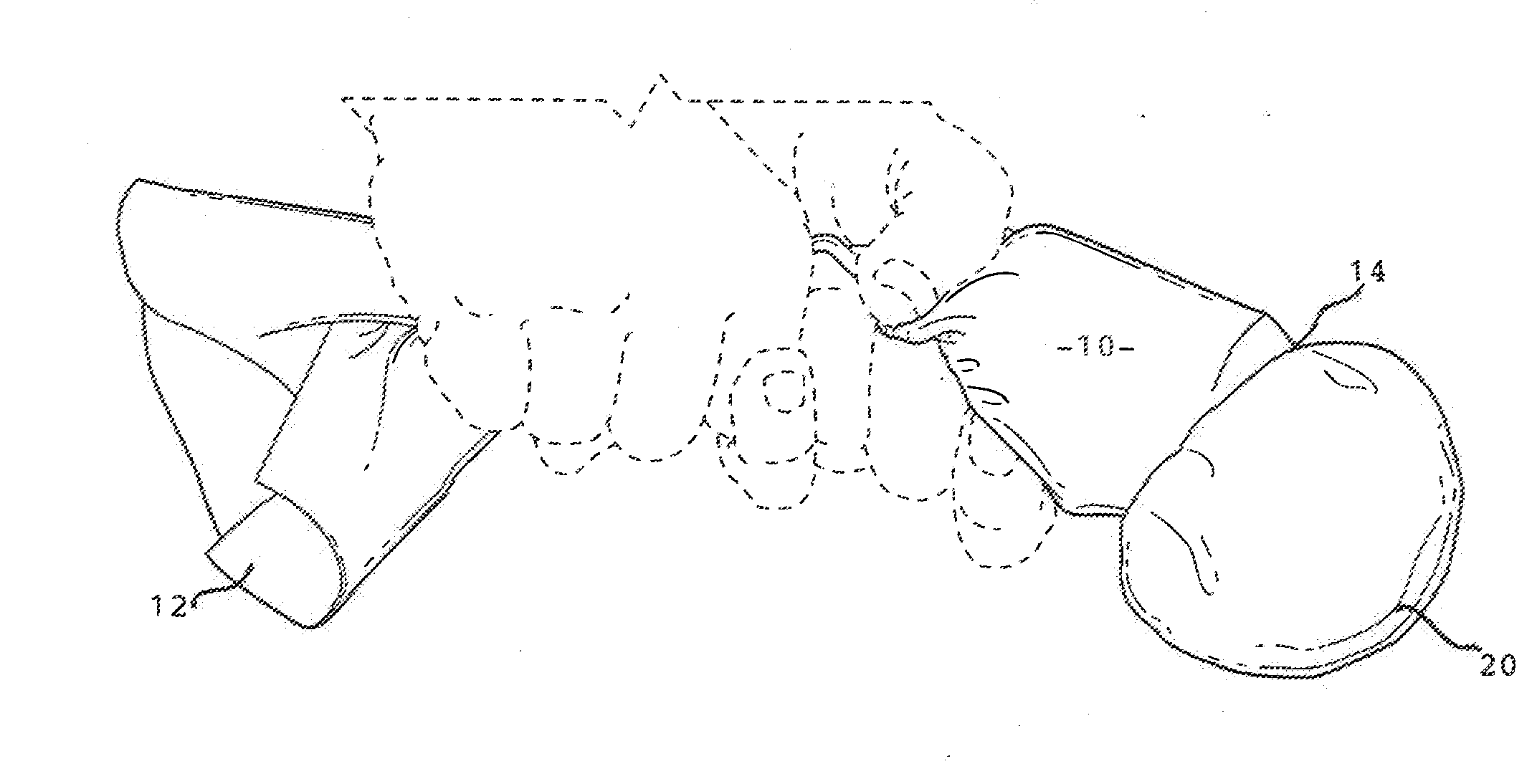
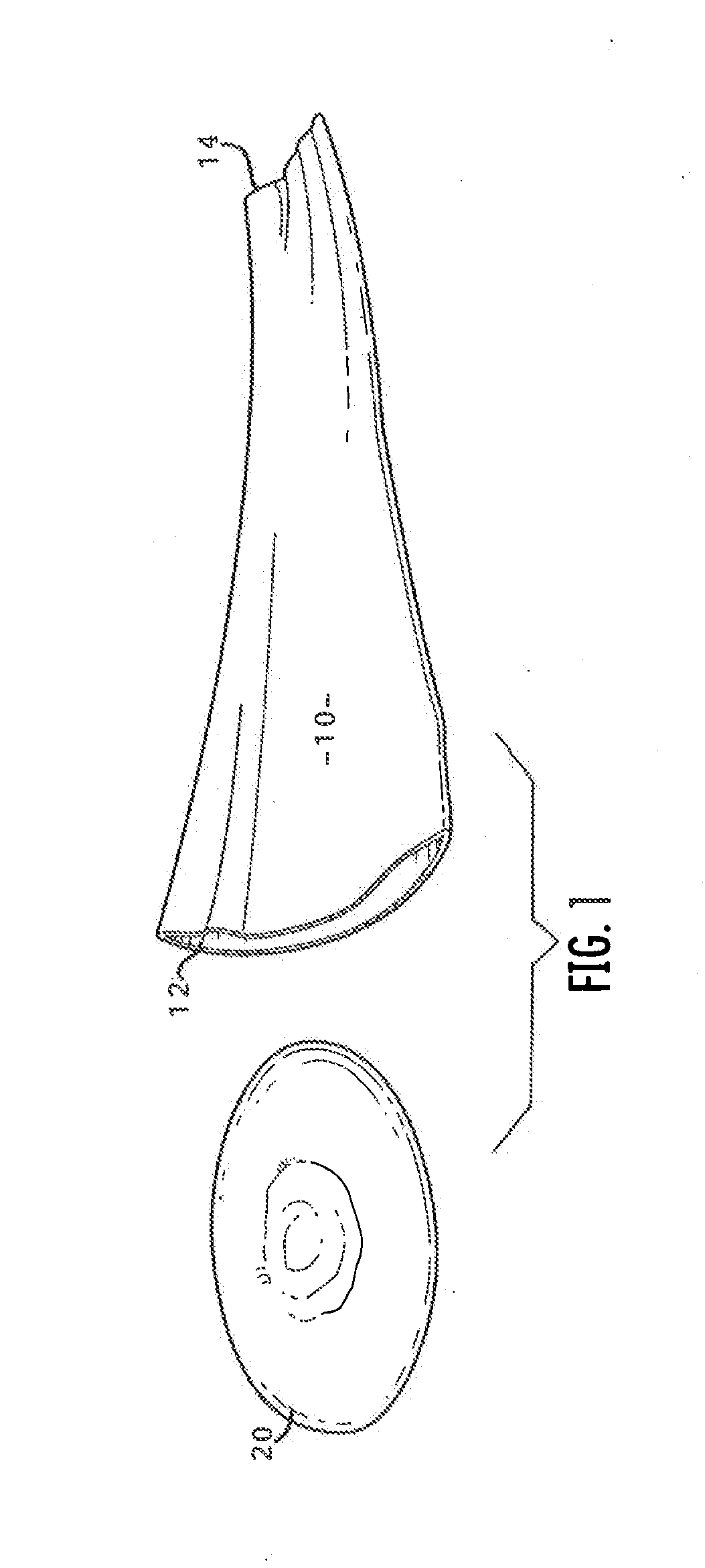
Apparatus and process for delivering a silicone prosthesis into a surgical pocket
ActiveUS20090204107A1Reduce deliveryEasy to installBronchoscopesMammary implantsBreast implantProsthesis
A tapered sleeve is provided that includes a lubricating coating on an inner surface. An implant (e.g., a pre-filled silicon breast implant) is introduced into a large end of the sleeve and extruded into a surgical pocket of minimal access incision size through a small-sized end of the apparatus.
Owner:KELLER MEDICAL
Fail-Safe Silicone Breast Implant Delivery Device
ActiveUS20110035003A1Avoid damageEasy to prepareMammary implantsSilicone breast implantBiomedical engineering
A tapered sleeve is provided for implant delivery. An implant (e.g., a pre-filled silicone breast implant) is introduced into a large proximal end of the sleeve and extruded into a surgical pocket of minimal access incision size through a small-sized distal end of the device. Sized appropriately to the implant, the sleeve remains intact during implant run-through of the sleeve.
Owner:KELLER MEDICAL
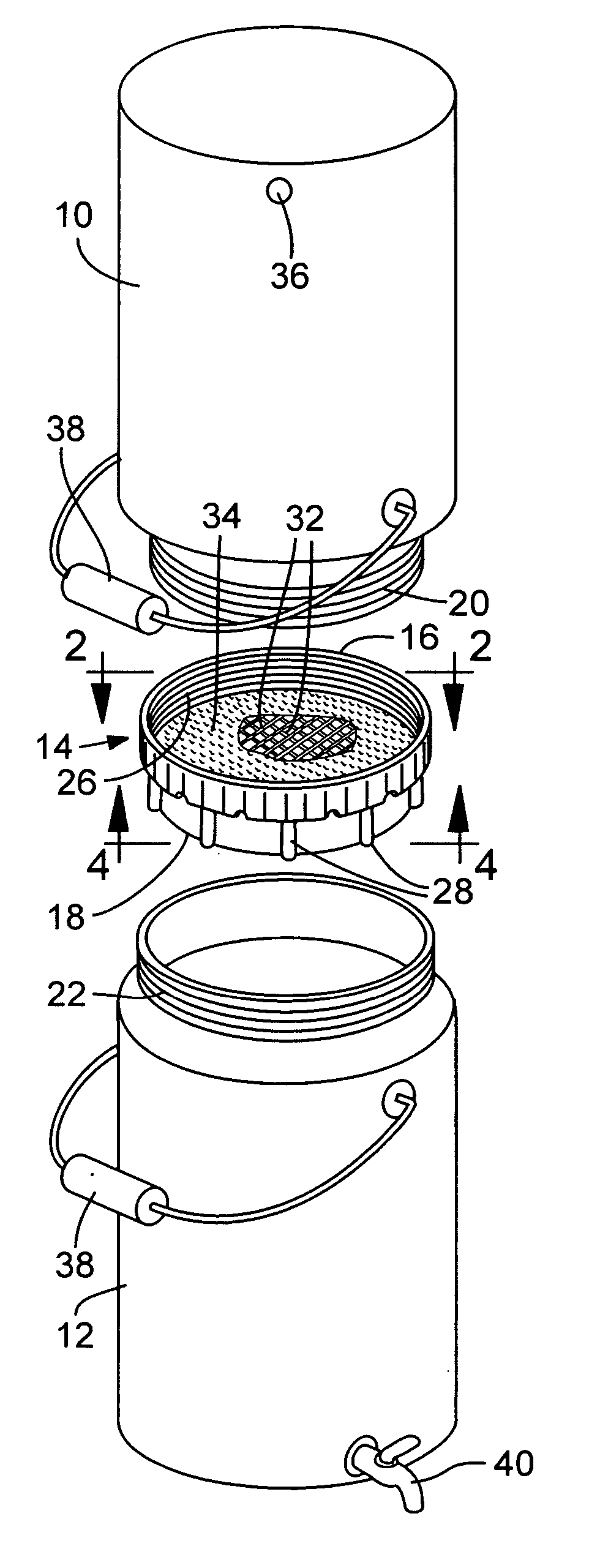
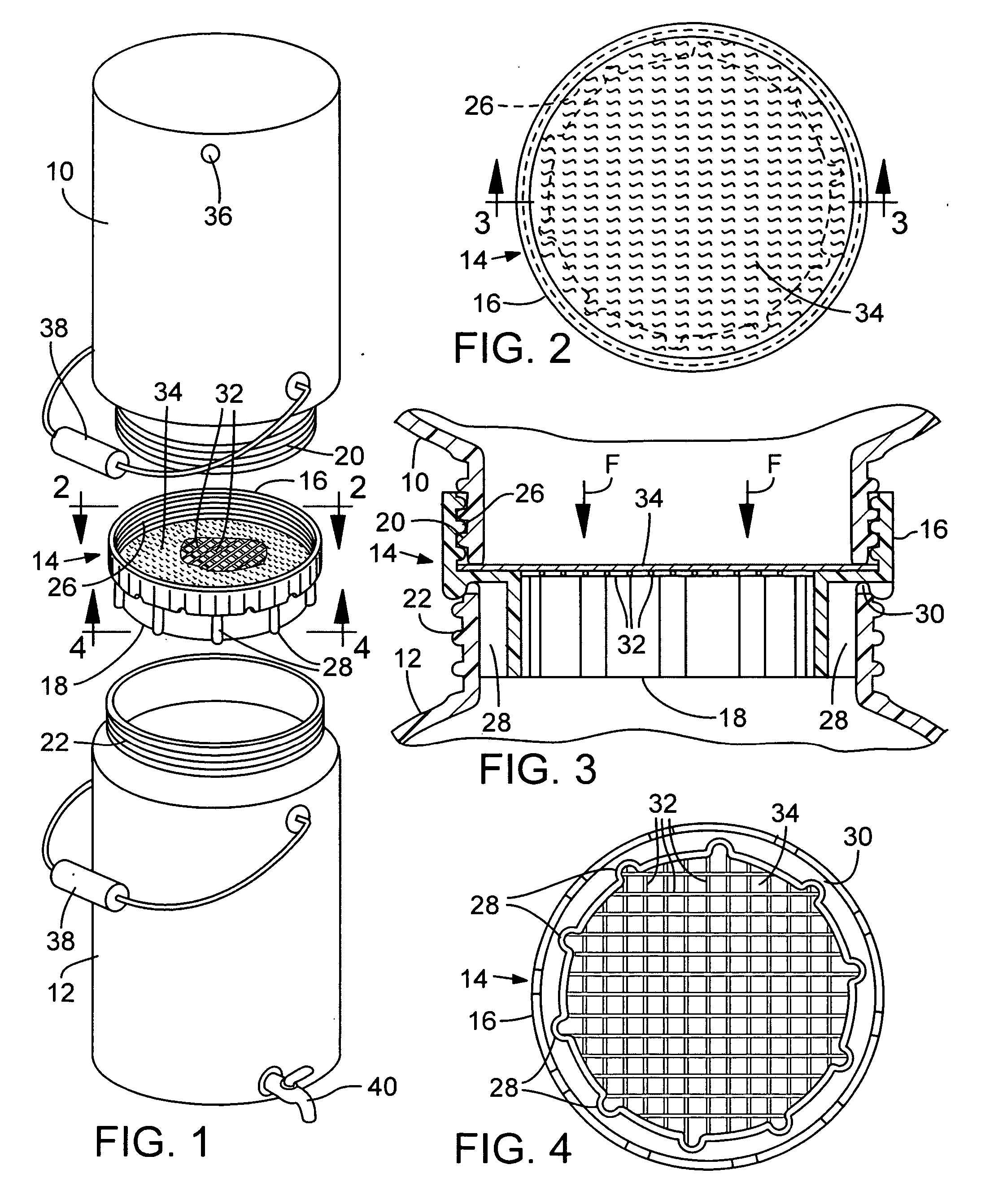
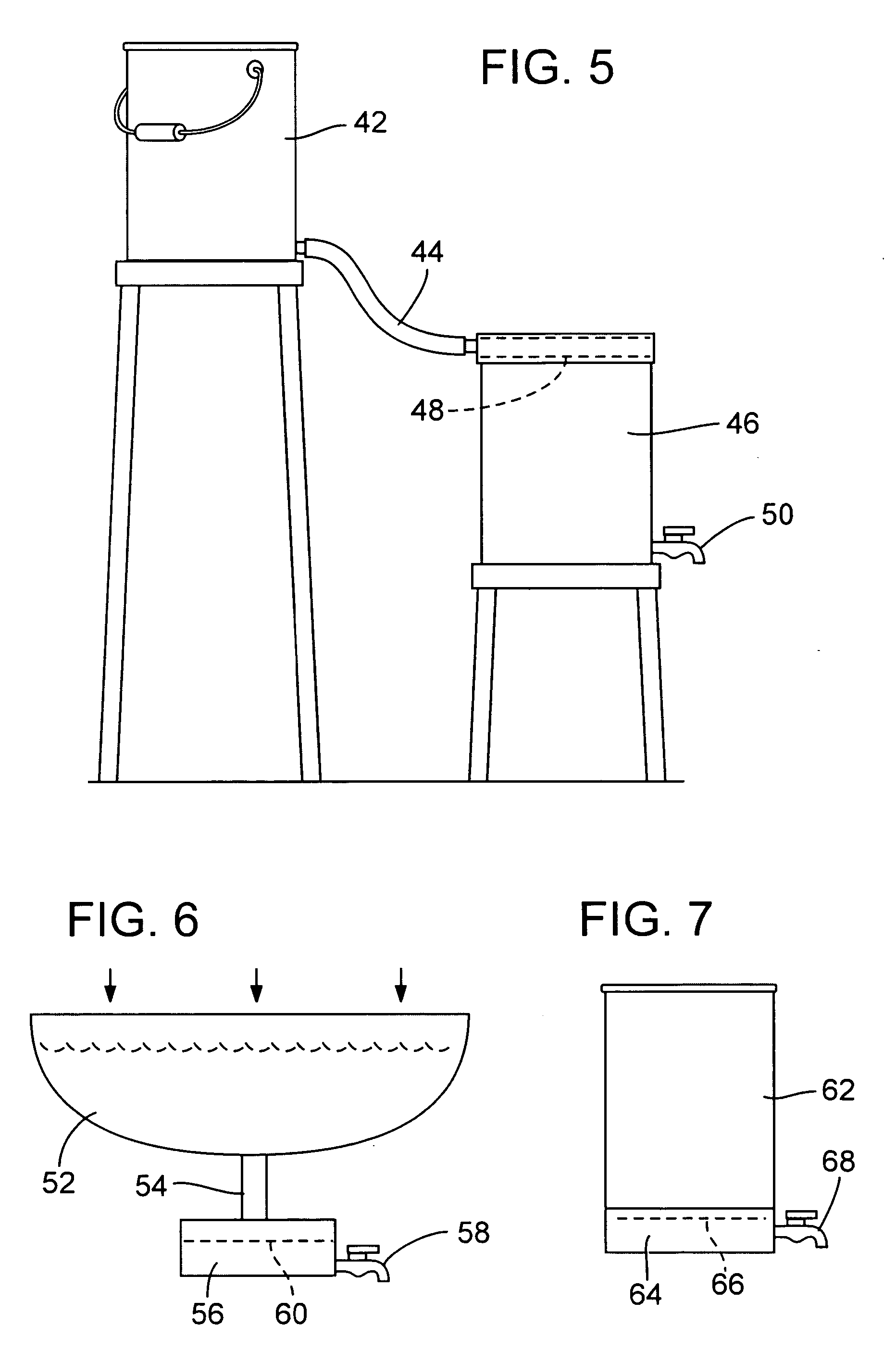
Water purification system
A system for providing purified drinking water for populations and persons having minimal access to modern water purification systems and therefore rely on water sources which contain microorganisms known to cause illness and death to large segments of such populations. Membranes are known which are pervious to water and impervious to the contaminants in such drinking water. The invention provides for gravity flow passage of water from the dirty (contaminated) water containment area to a clean (purified) water containment area and a filter including such a membrane whereby the flow of water has to penetrate through the membrane and in the process filters out the illness-producing microorganisms. The invention enables the use of commonly available jugs or jars requiring only a gravity flow passage between the jugs or jars and the filter contained in the passage.
Owner:GLOBAL WATER
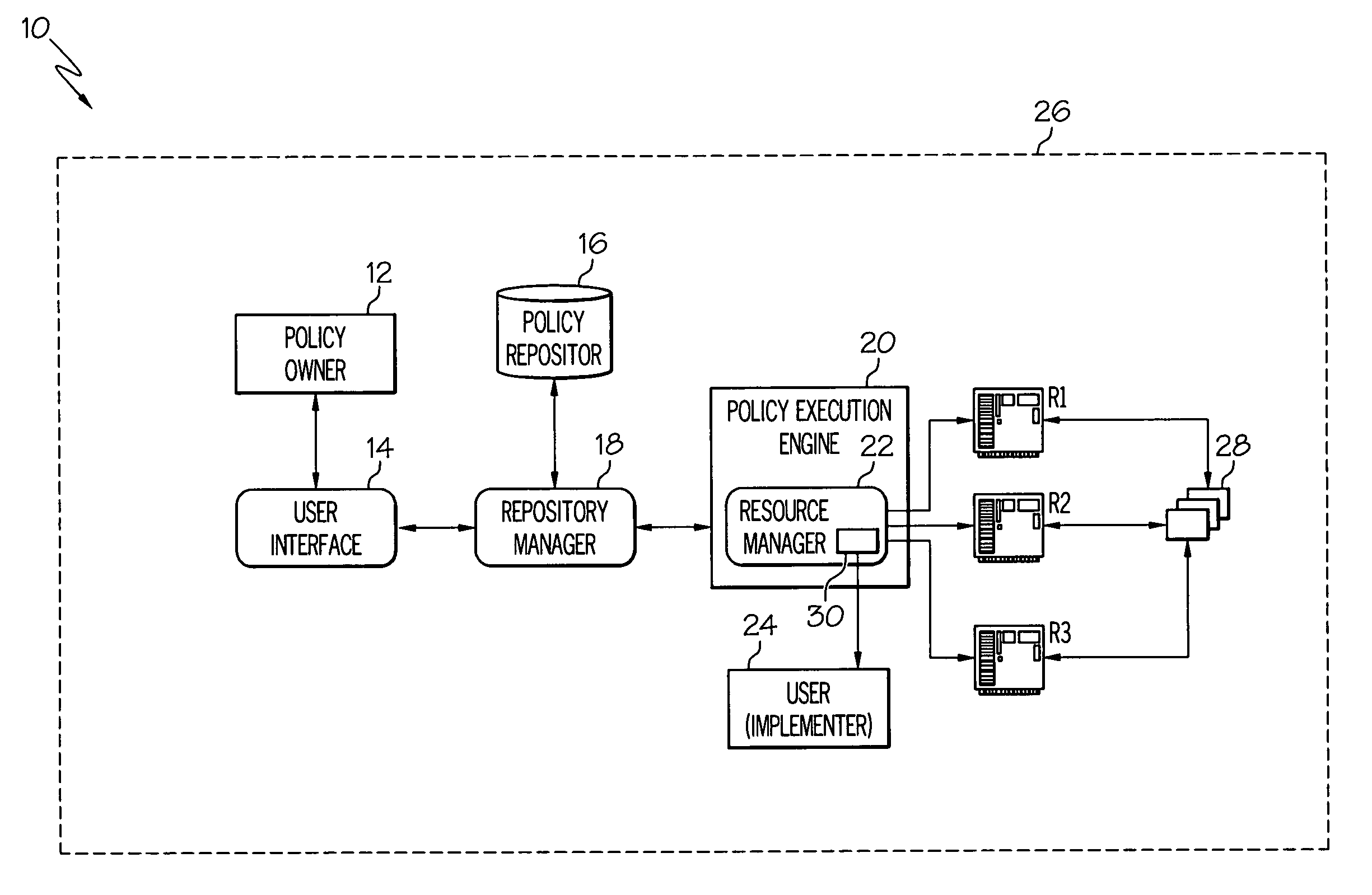
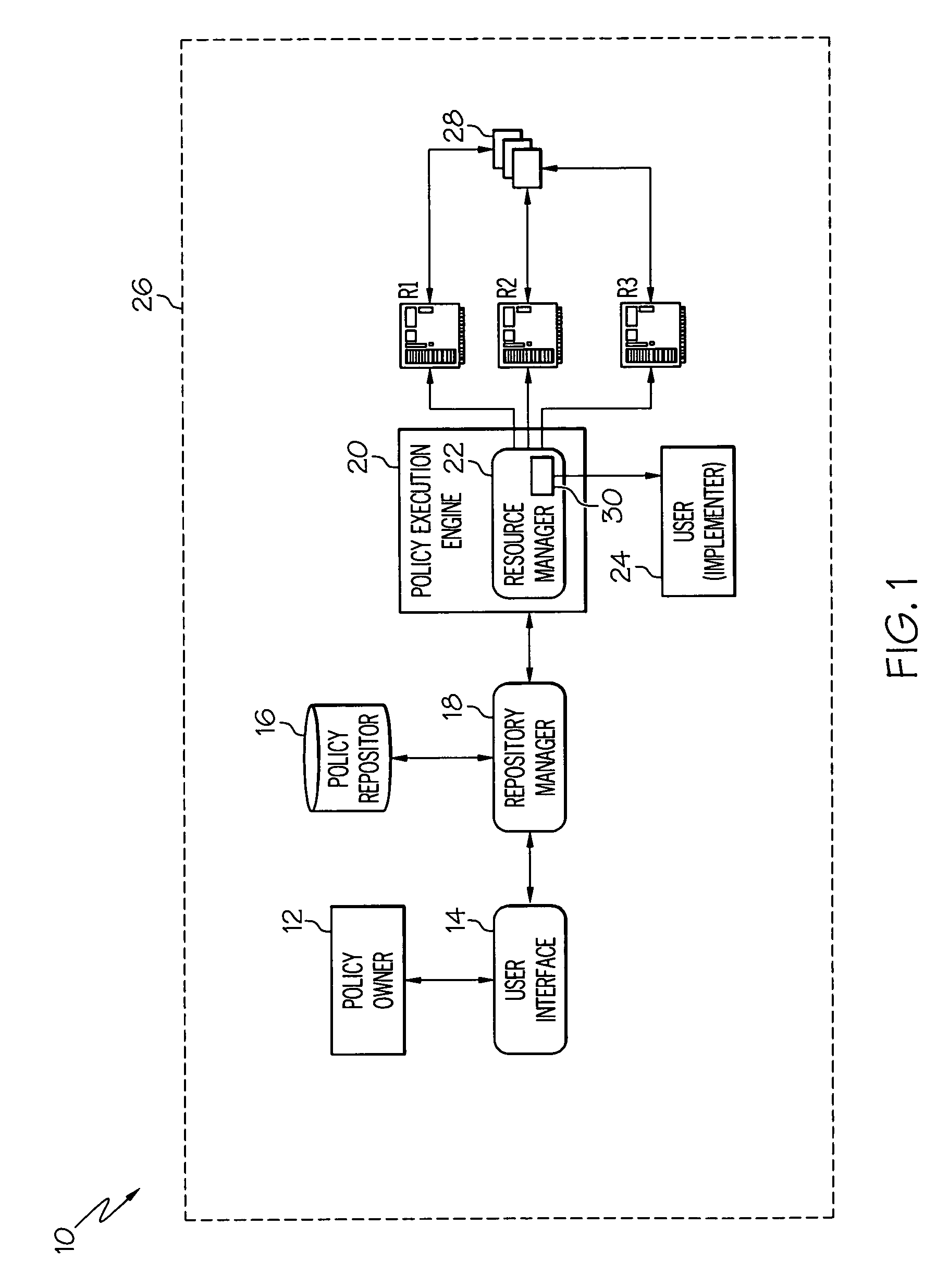
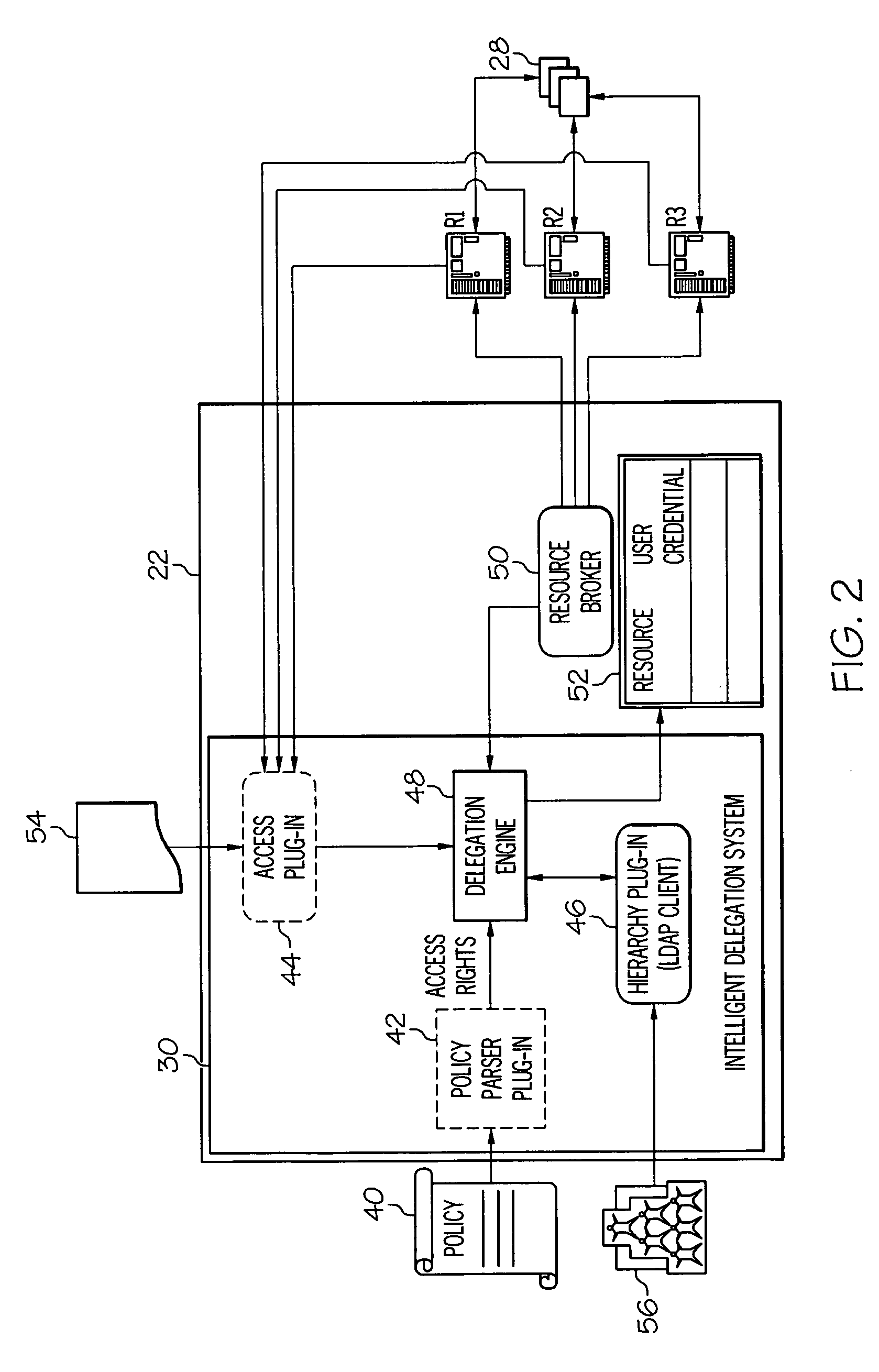
Policy implementation delegation
InactiveUS20060277594A1Digital data processing detailsUser identity/authority verificationAnalytical hierarchyAccess control list
The present invention allows a user (e.g., a policy implementer) to be identified and delegated responsibility for implementing a policy. This can occur, implicitly, semi-implicitly or explicitly. In a typical embodiment, a policy provided (e.g., by a policy owner) is automatically parsed to determine a minimum set of access rights needed to implement the policy. For example, the policy might indicate that an implementing user only needs simple read privileges. Alternatively, the policy might require read / write privileges. In any event, a list (e.g., an access control list) will be analyzed to identify a set (e.g., one or more) of users of a computerized resource subject to the policy that meets the minimum set of access rights. Once this set of users has been identified, a hierarchy can be optionally analyzed to determine who among the set of users is permitted to implement the policy.
Owner:IBM CORP
Minimal access tool
A minimal access tool includes a frame arranged to be attached to an arm of a user, a tool shaft having a proximal end and a distal end, where the tool shaft proximal end is connected to the frame. The tool further includes an input joint having a first end connected to the frame and a second end arranged to receive user input, the input joint including a virtual center-of-rotation (VC) mechanism which provides a center of rotation that generally coincides with a wrist joint of the user. An output joint is connected to the tool shaft distal end, where the output joint is coupled to the input joint via a mechanical transmission connected therebetween to correlate motion of the input joint to motion of the output joint.
Owner:RGT UNIV OF MICHIGAN
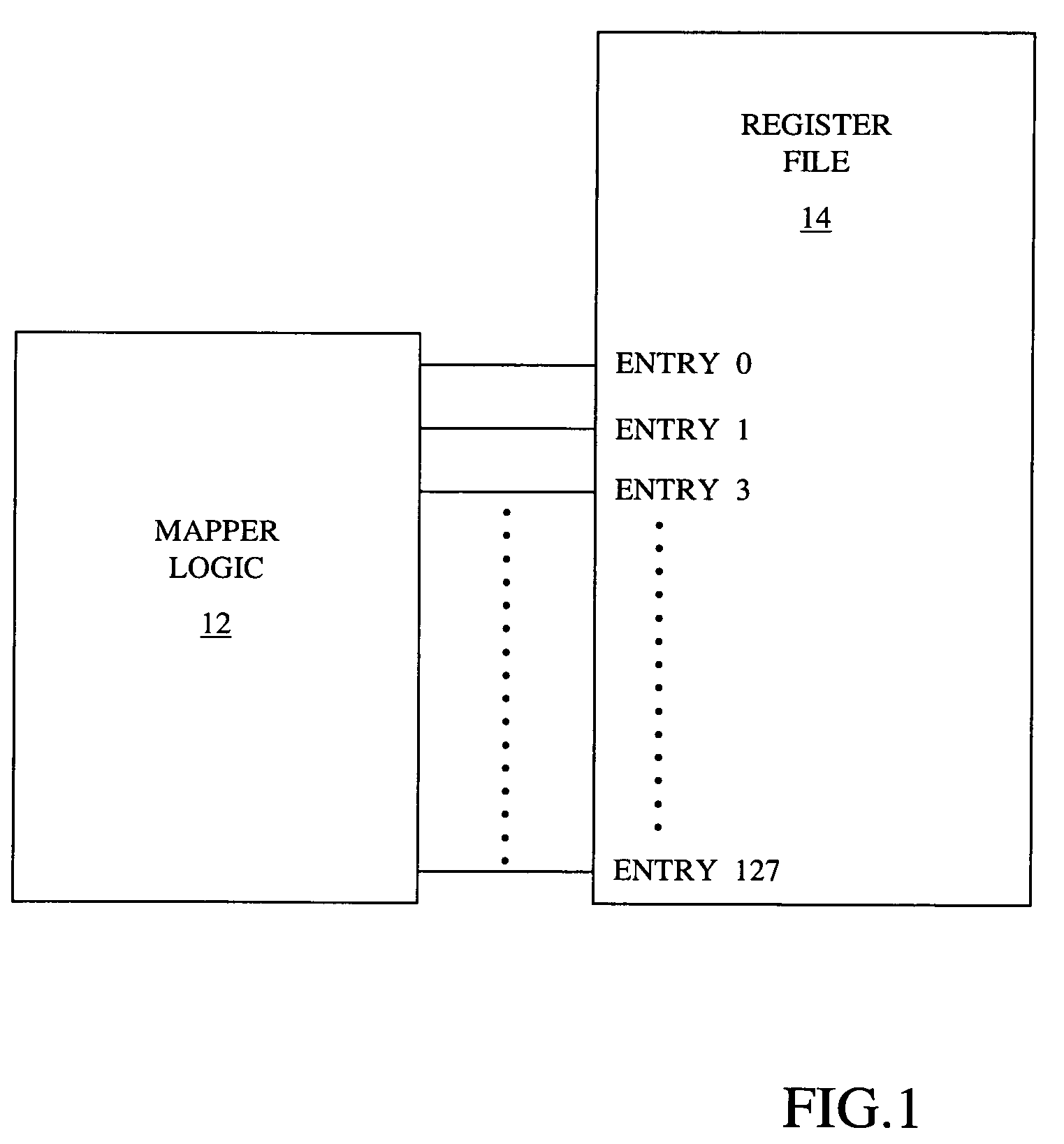
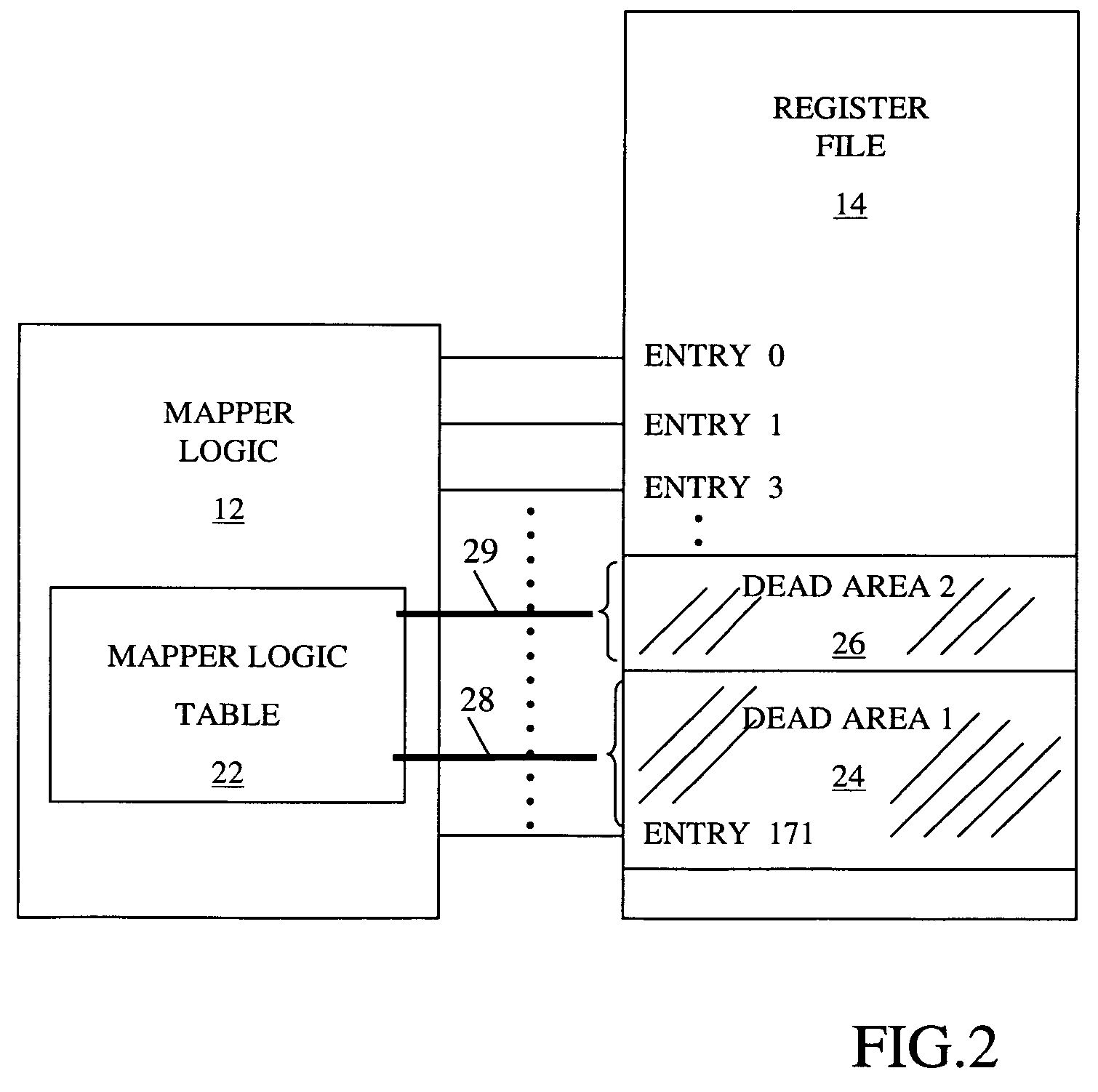
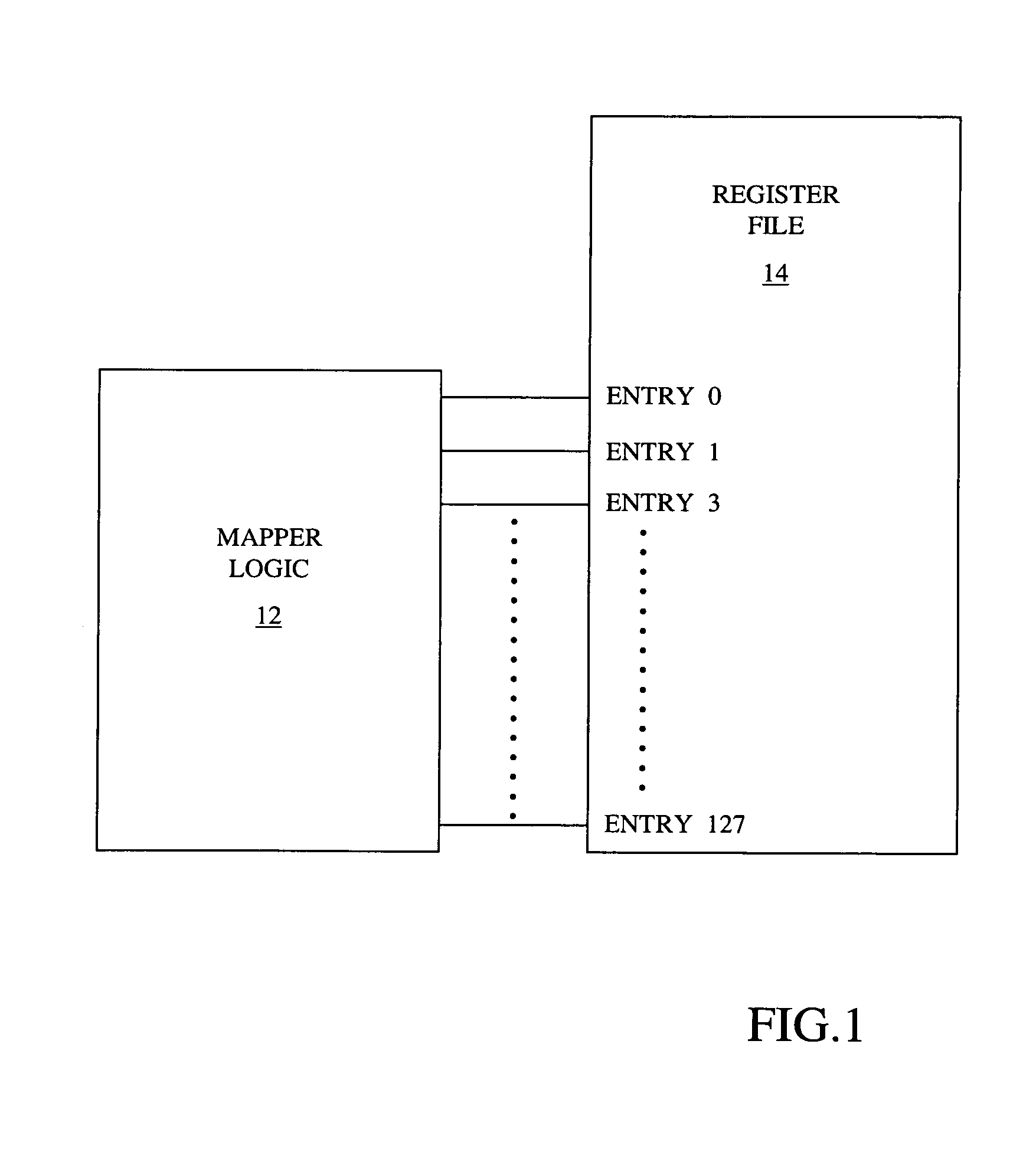
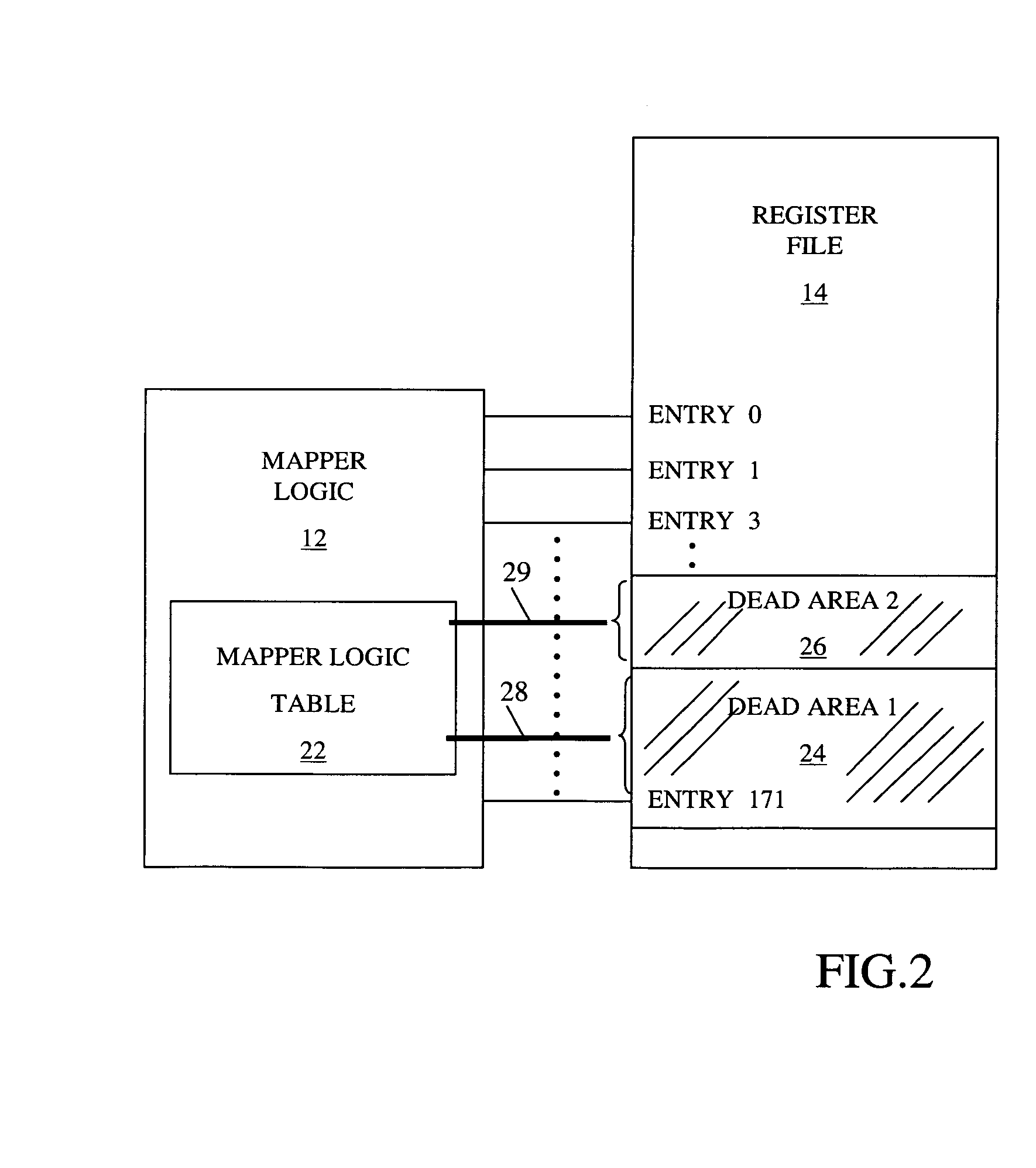
Method to reduce power consumption of a register file with multi SMT support
InactiveUS8046566B2Reduce in quantityResource allocationDigital computer detailsProcessor registerControl register
A method for reducing the power consumption of a register file of a microprocessor supporting simultaneous multithreading (SMT) is disclosed. Mapping logic and associated table entries monitor a total number of processing threads currently executing in the processor and signal control logic to disable specific register file entries not required for currently executing or pending instruction threads or register file entries not meeting a minimum access threshold using a least recently used algorithm (LRU). The register file utilization is controlled such that a register file address range selected for deactivation is not assigned for pending or future instruction threads. One or more power saving techniques are then applied to disabled register files to reduce overall power dissipation in the system.
Owner:INT BUSINESS MASCH CORP
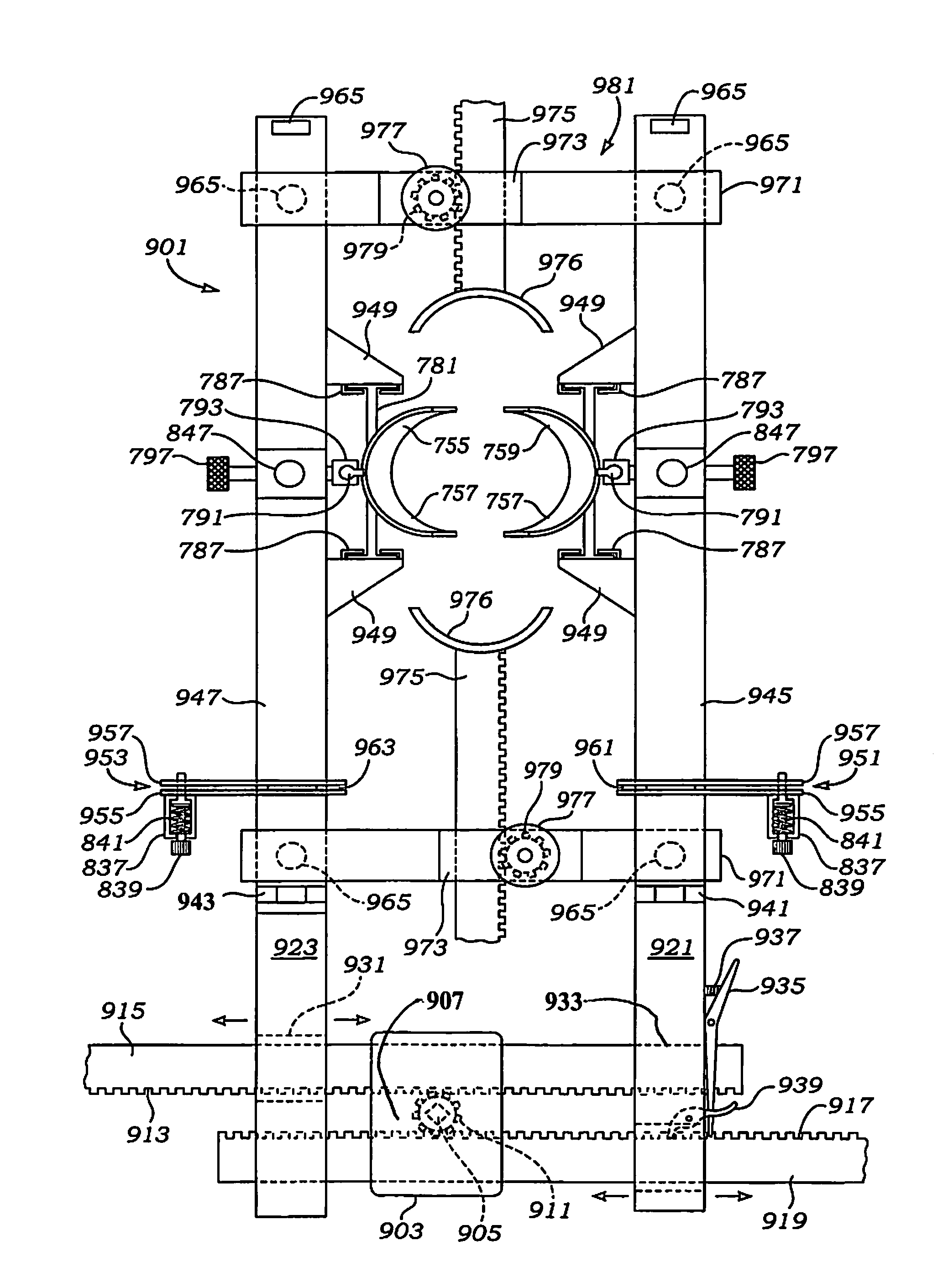
Minimal access lumbar diskectomy instrumentation and method
A minimal incision maximal access system allows for maximum desirable exposure along with maximum access to the operative field utilizing a minimum incision as small as the METRx and Endius systems. Instead of multiple insertions of dilating tubes the design is a streamlined single entry device to avoid repetitive skin surface entry. The system offers the capability to expand to optimum exposure size for the surgery utilizing hinged bi-hemispherical or oval working tubes applied over an introducer obturator which is controllably dilated to slowly separate muscle tissue. Deeper end working and visualization areas with maximum proximal access and work dimensions are provided to makes the operative procedure safer in application and shorten the surgeons's learning curve because it most closely approximates the ability to use open microdiskectomy techniques. a dual frame system enables full or partial spreading of a working tube set, while an open frame facilitates a four point retraction system.
Owner:K2M
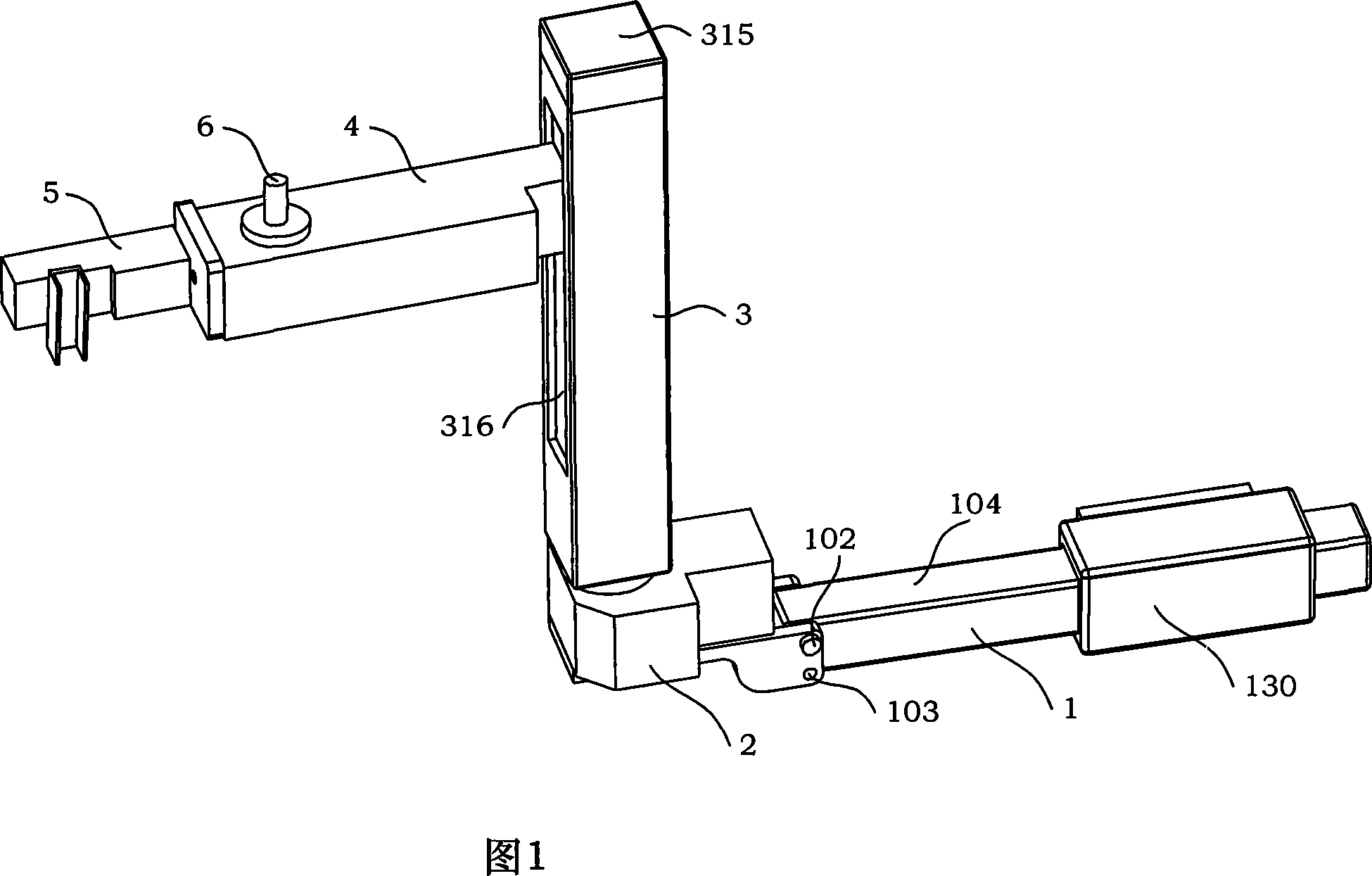
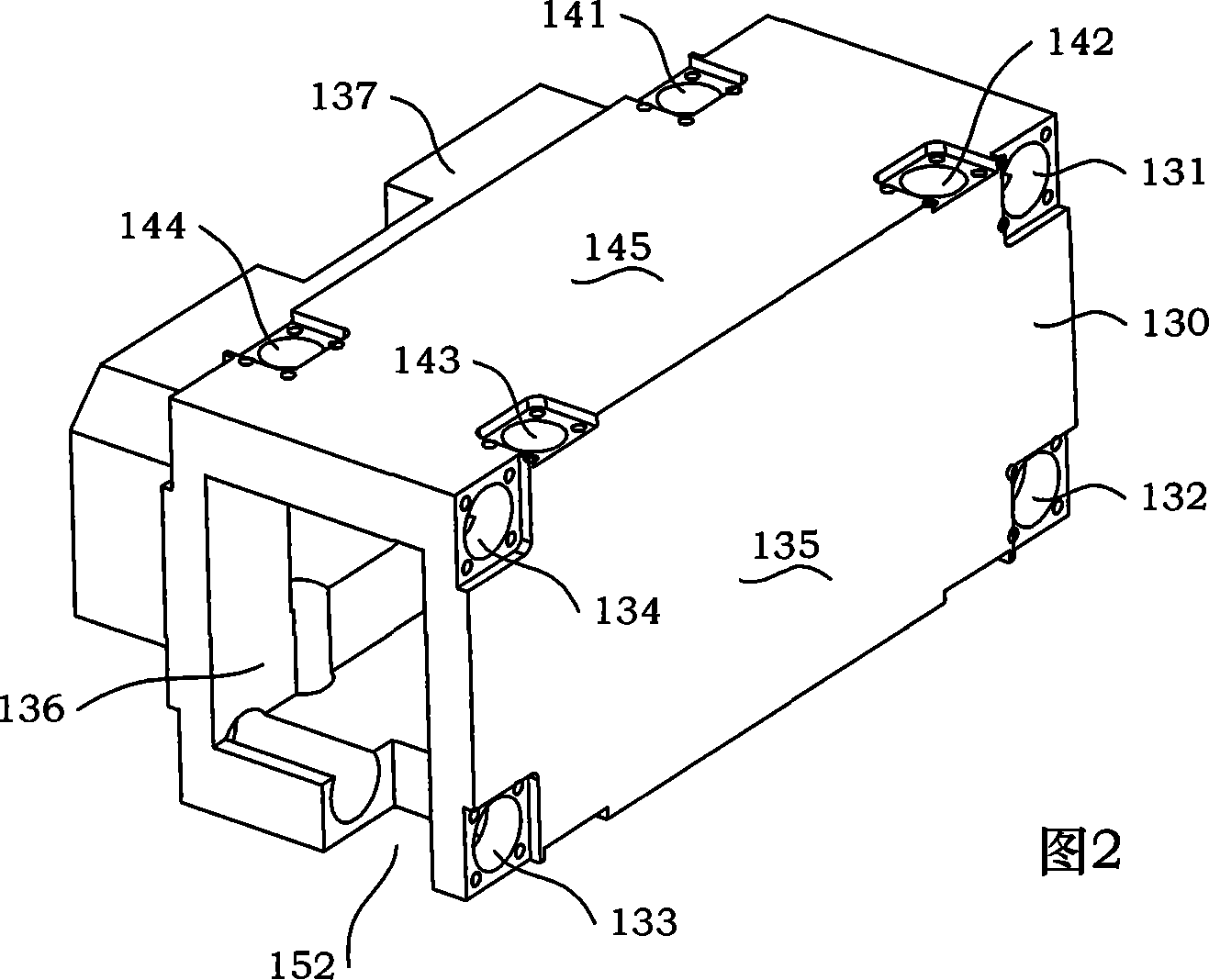
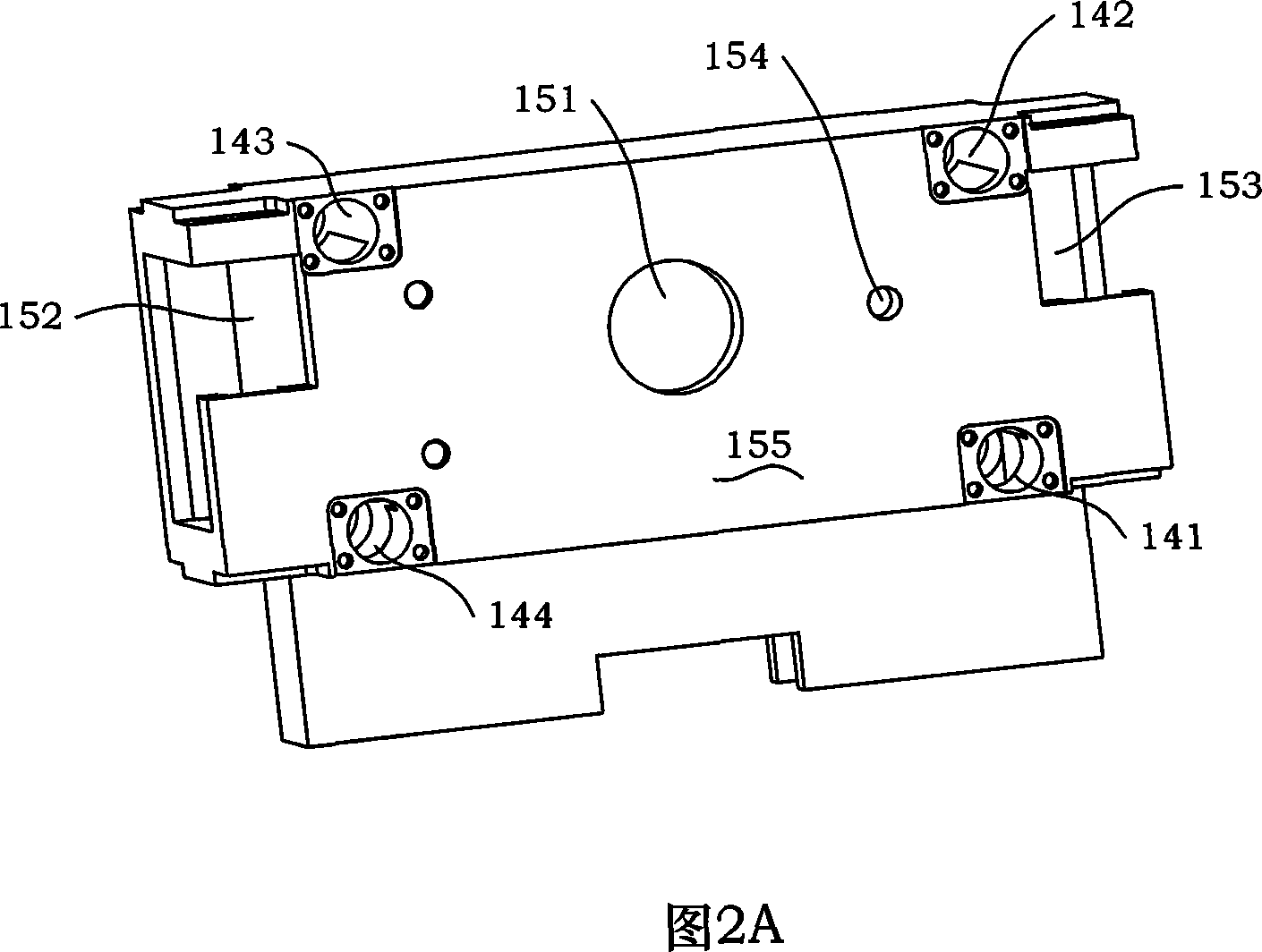
Minimal access bone operating robot based on 3D mouse operation
The invention is concerned with minimally invasive orthopaedics operation robot operated with 3D mouse, relating to landscape orientation moving groupware, reducer groupware, fluctuation moving groupware, small arm groupware, wrist groupware and 3D mouse. The 3D mouse sets on the small arm's shell of small arm groupware, the machine seat of reducer groupware connects with revolving flange of landscape orientation moving groupware, the fixing base seat of fluctuation moving groupware connects with the joint of reducer groupware through two lock poles, the sliding groove of small arm groupware connects with the C sliding groove of fluctuation moving groupware and slides in the groove, and the flange of wrist groupware connects with the output axis of reducer to small arm groupware. The robot is fit for the demand of clinic and operation with practicability and applicability. It is a orthopaedics operation robot with initiative restriction and passivity safety ensure.
Owner:BEIHANG UNIV
Minimal access lumbar diskectomy instrumentation and method
A minimal incision maximal access system allows for maximum desirable exposure along with maximum access to the operative field utilizing a minimum incision as small as the METRx and Endius systems. Instead of multiple insertions of dilating tubes the design is a streamlined single entry device to avoid repetitive skin surface entry. The system offers the capability to expand to optimum exposure size for the surgery utilizing hinged bi-hemispherical or oval working tubes applied over an introducer obturator which is controllably dilated to slowly separate muscle tissue. Deeper end working and visualization areas with maximum proximal access and work dimensions are provided to makes the operative procedure safer in application and shorten the surgeons's learning curve because it most closely approximates the ability to use open microdiskectomy techniques. A dual frame system enables full or partial spreading of a working tube set, while an open frame facilitates a four point retraction system.
Owner:K2M
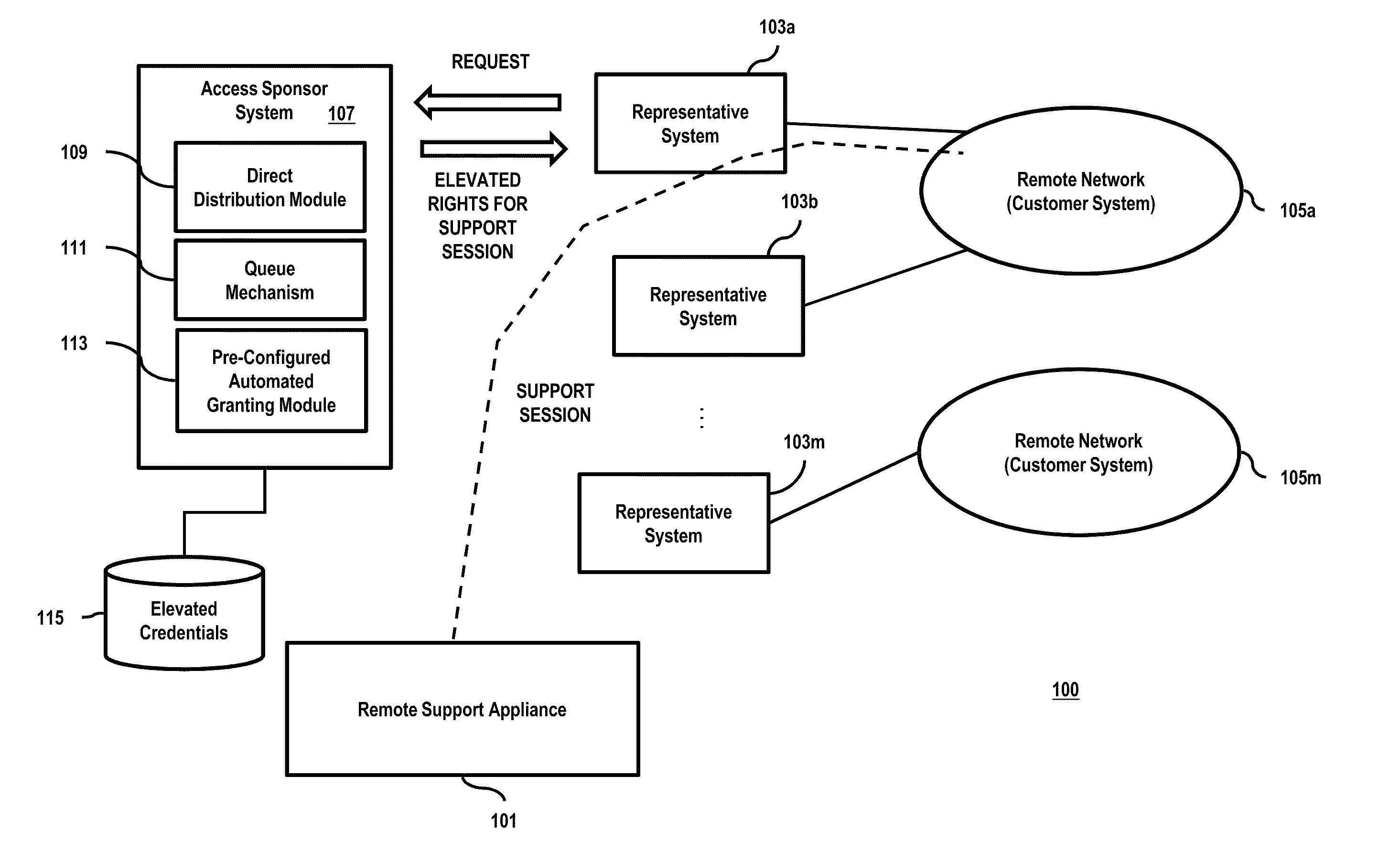
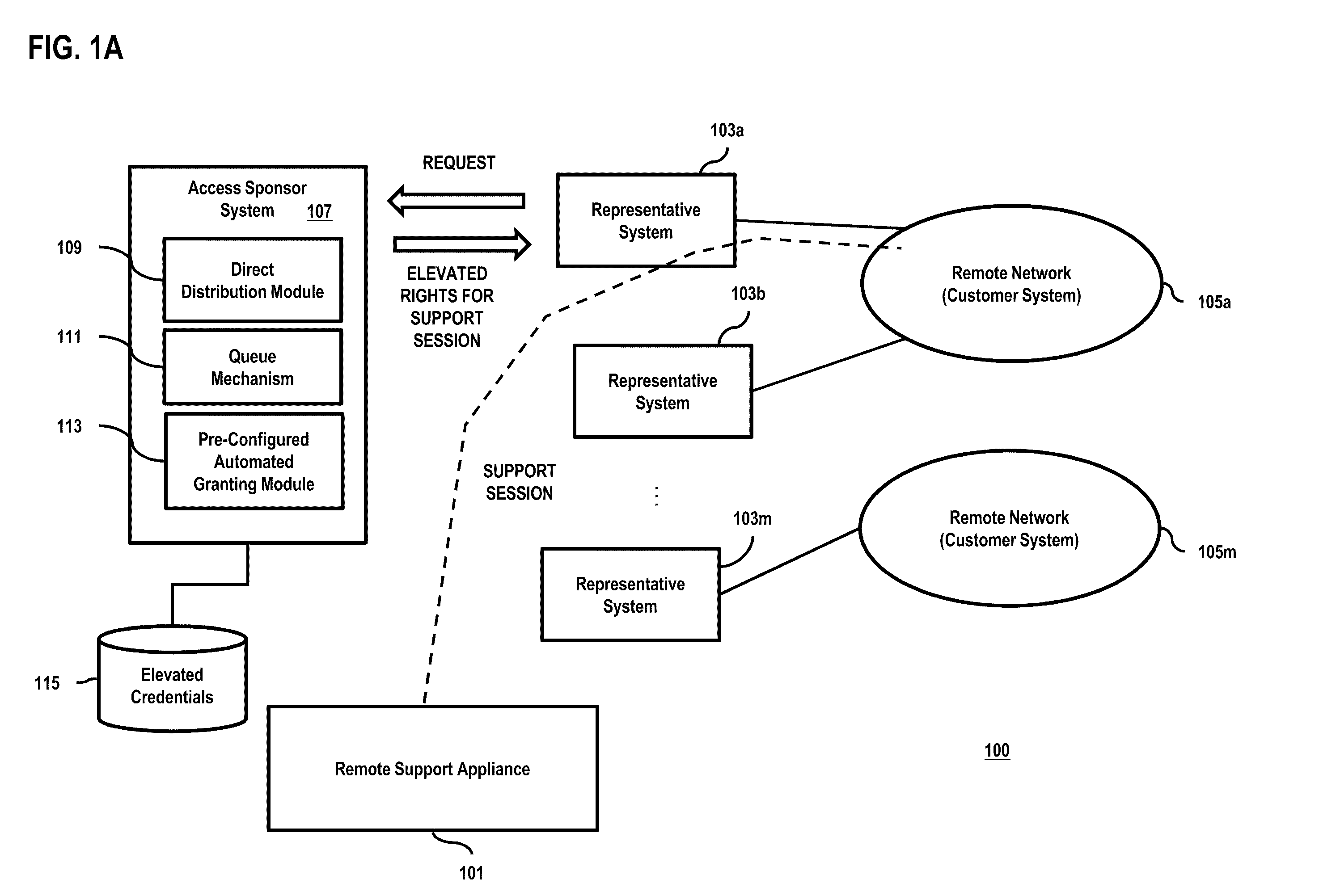
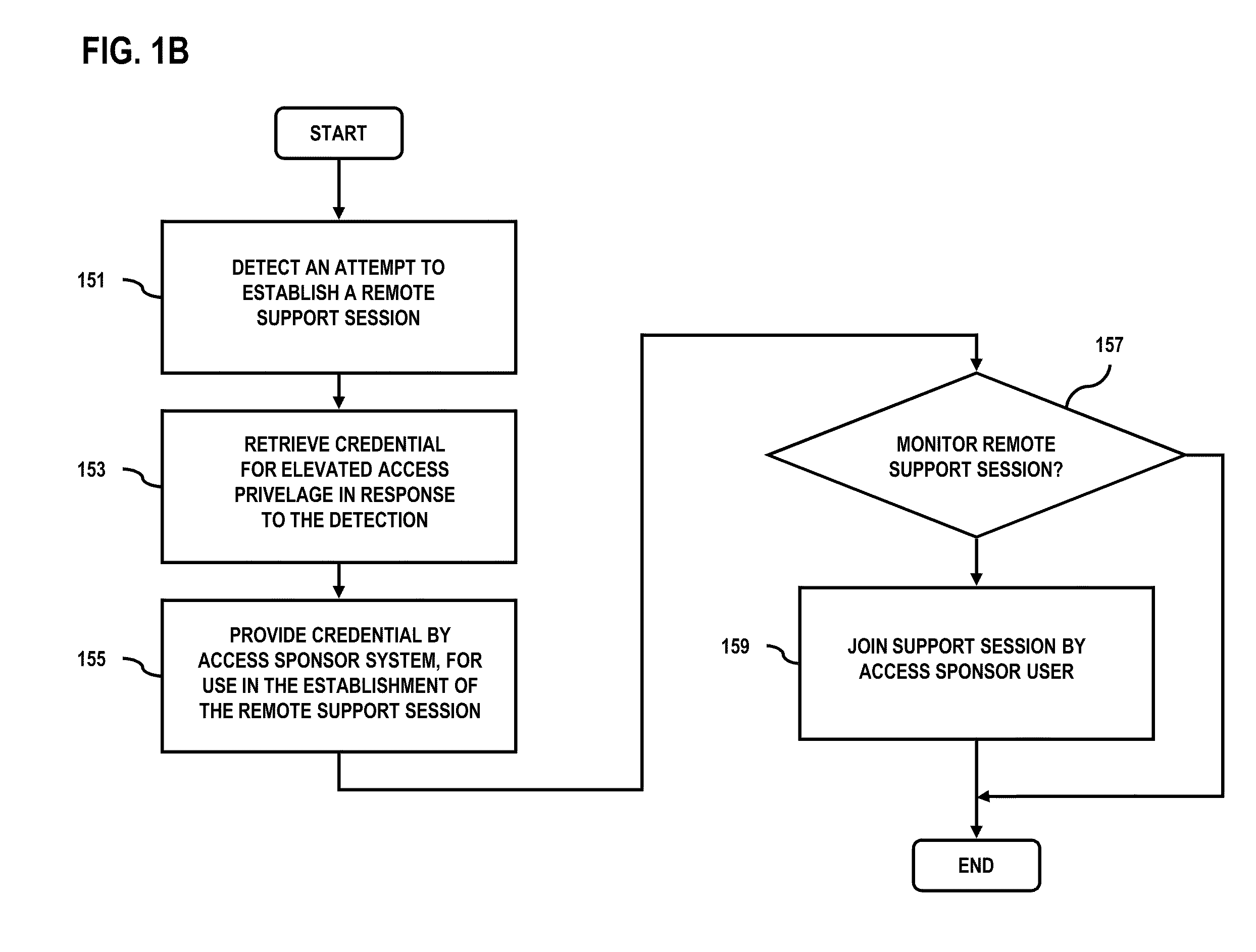
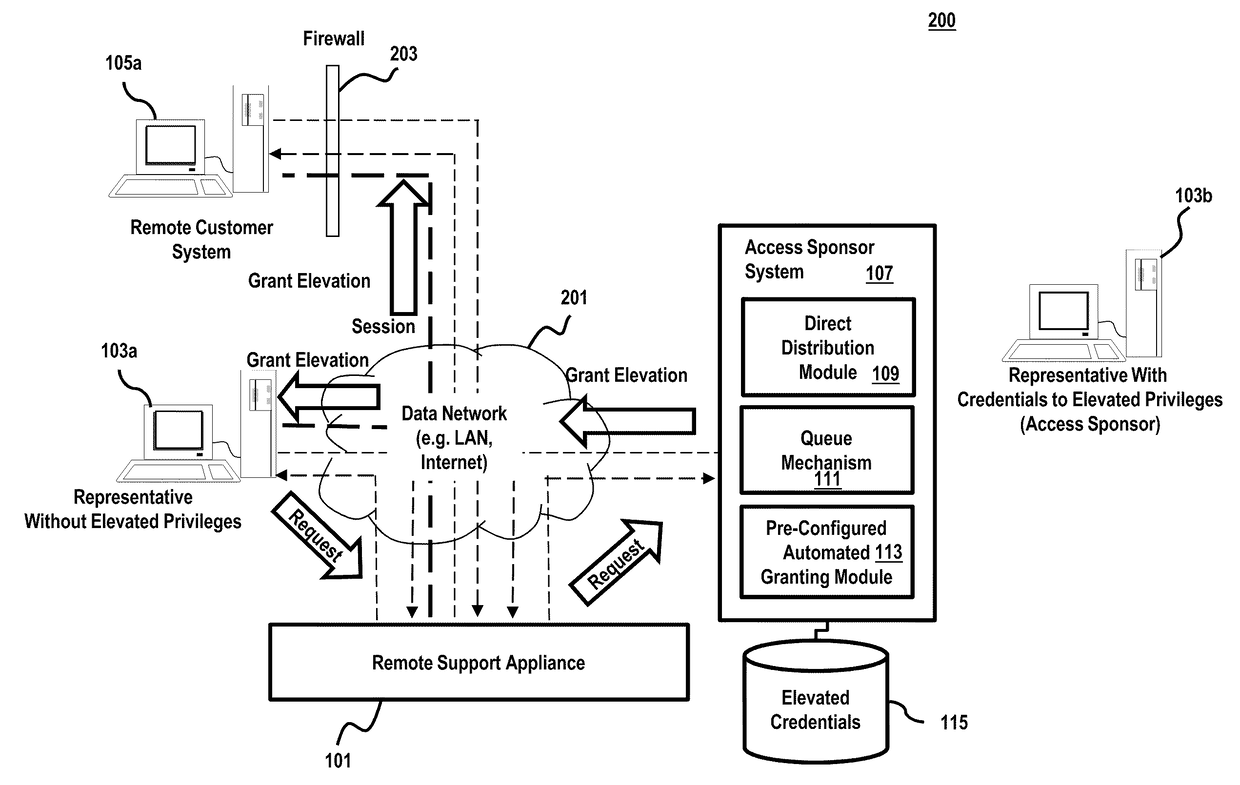
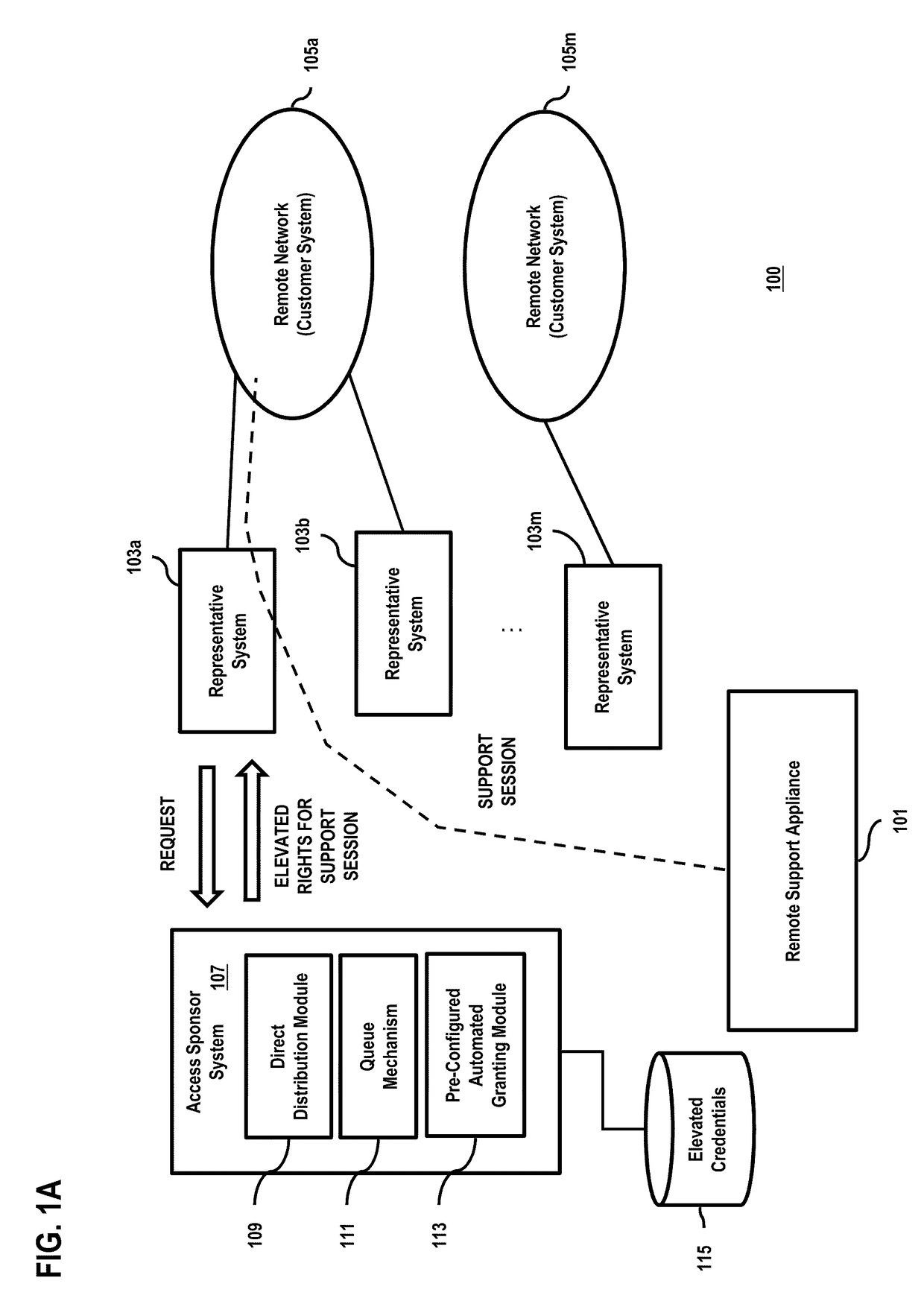
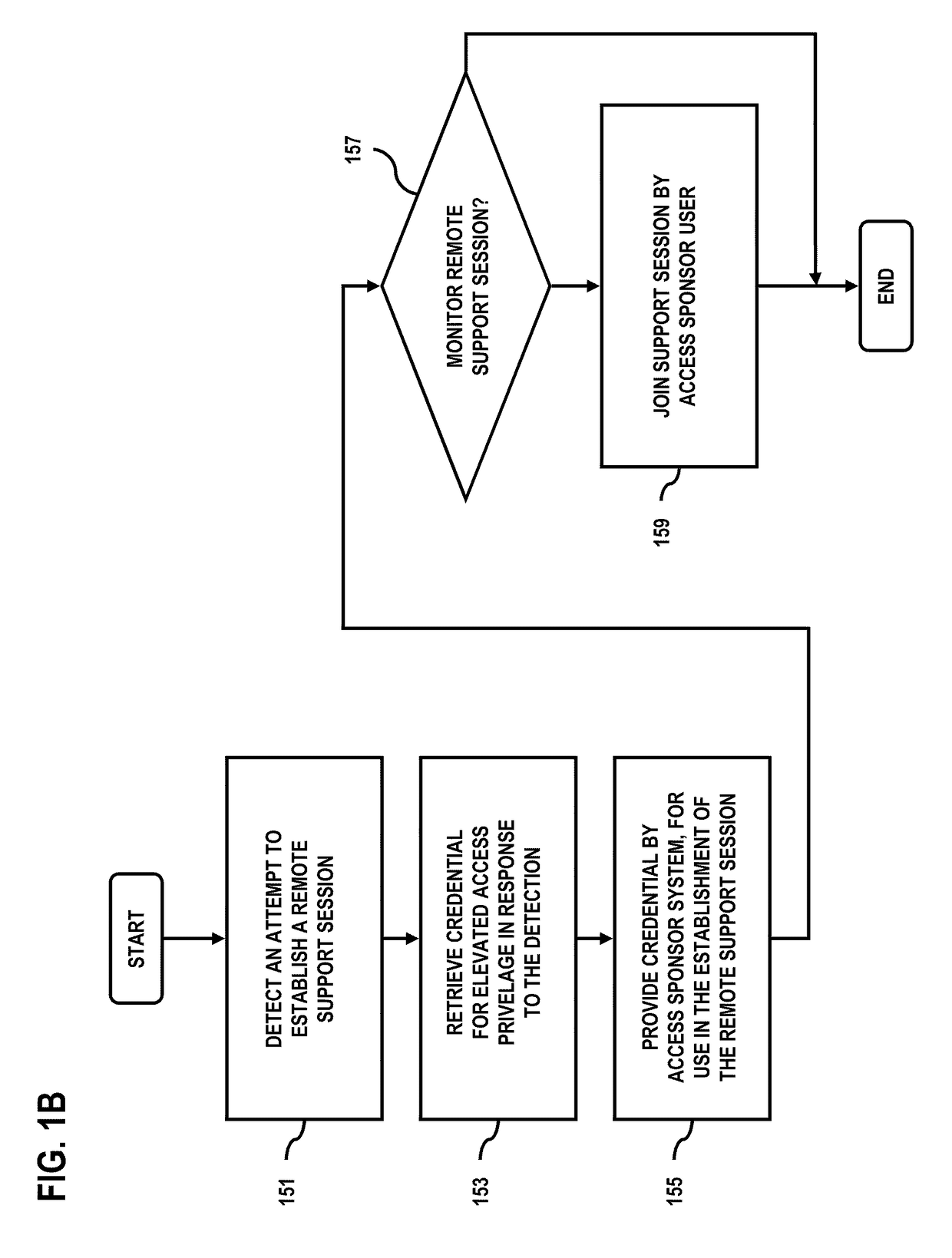
Method and apparatus for securely providing access and elevated rights for remote support
ActiveUS20100257596A1Digital data processing detailsUser identity/authority verificationComputer networkRemote system
An approach is provided to allow remote support representatives to carry out remote support session with minimal access and privileges to remote systems. An attempt is detected to establish a remote support session via a remote support appliance that is configured to establish the remote support session between a first device associated with a support representative and a second device associated with a user. A credential that provides an elevated access privilege is retrieved in response to the detection. The credential is provided to the first device for use in the establishment of the remote support session.
Owner:BEYONDTRUST CORP
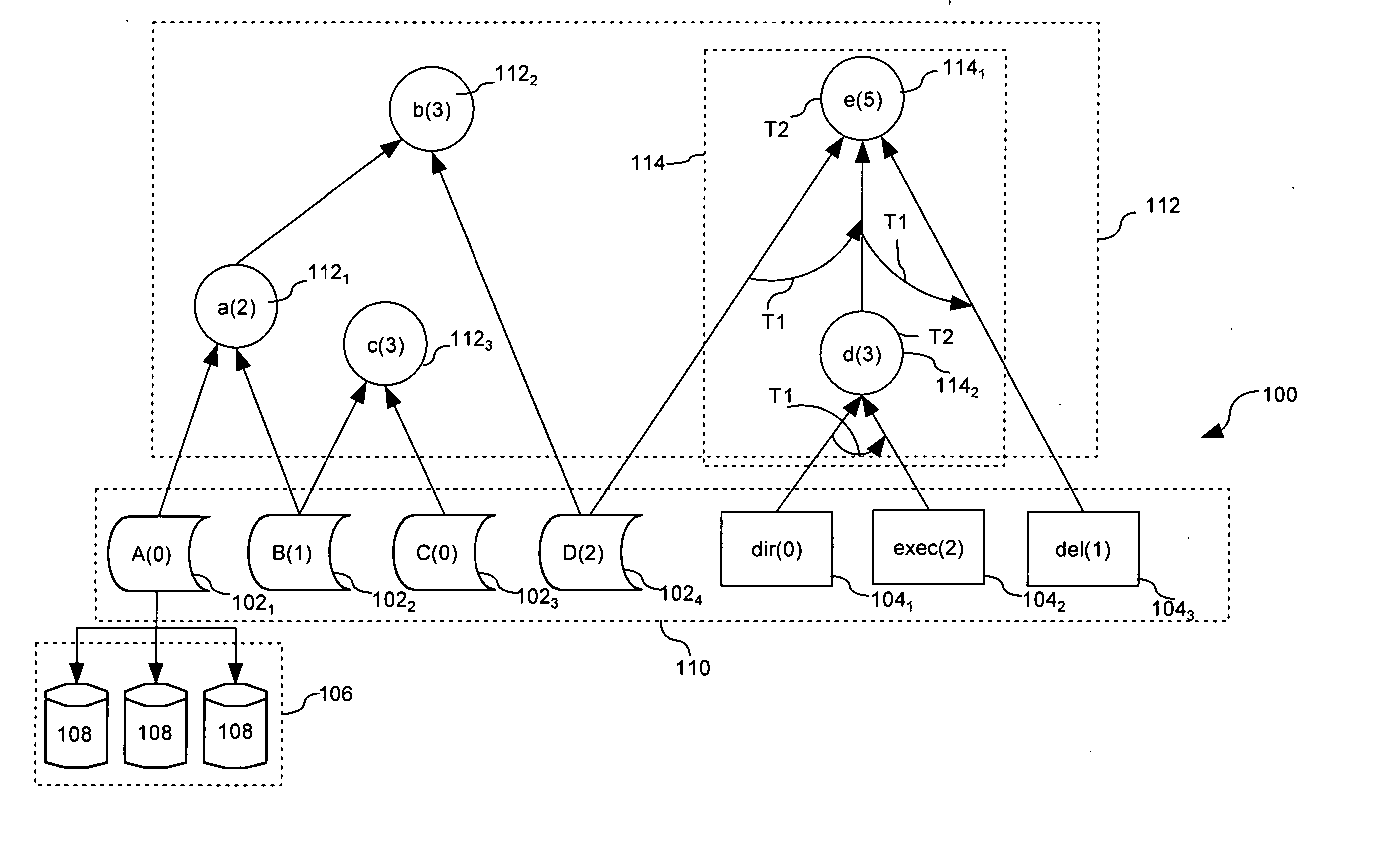
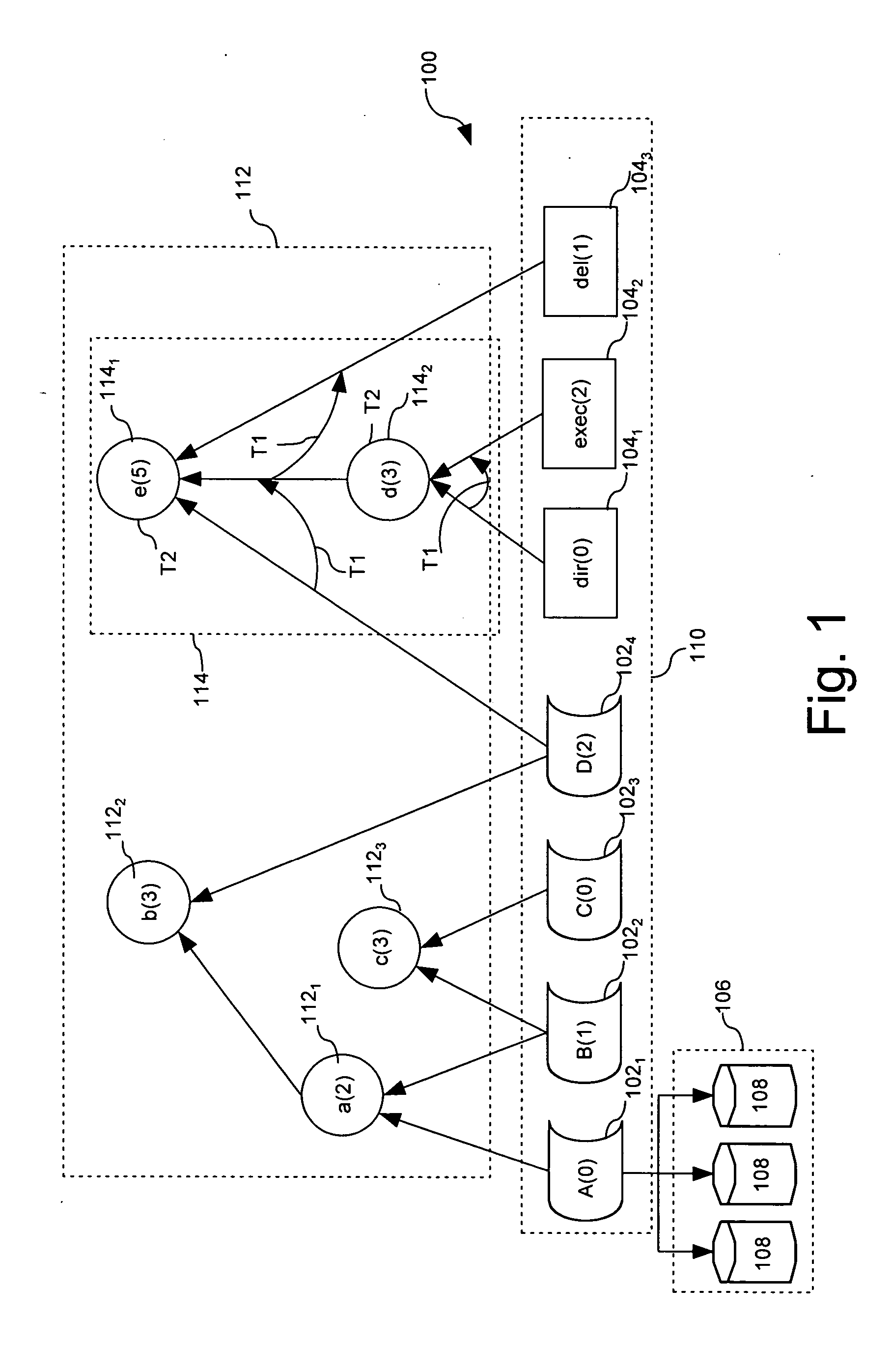
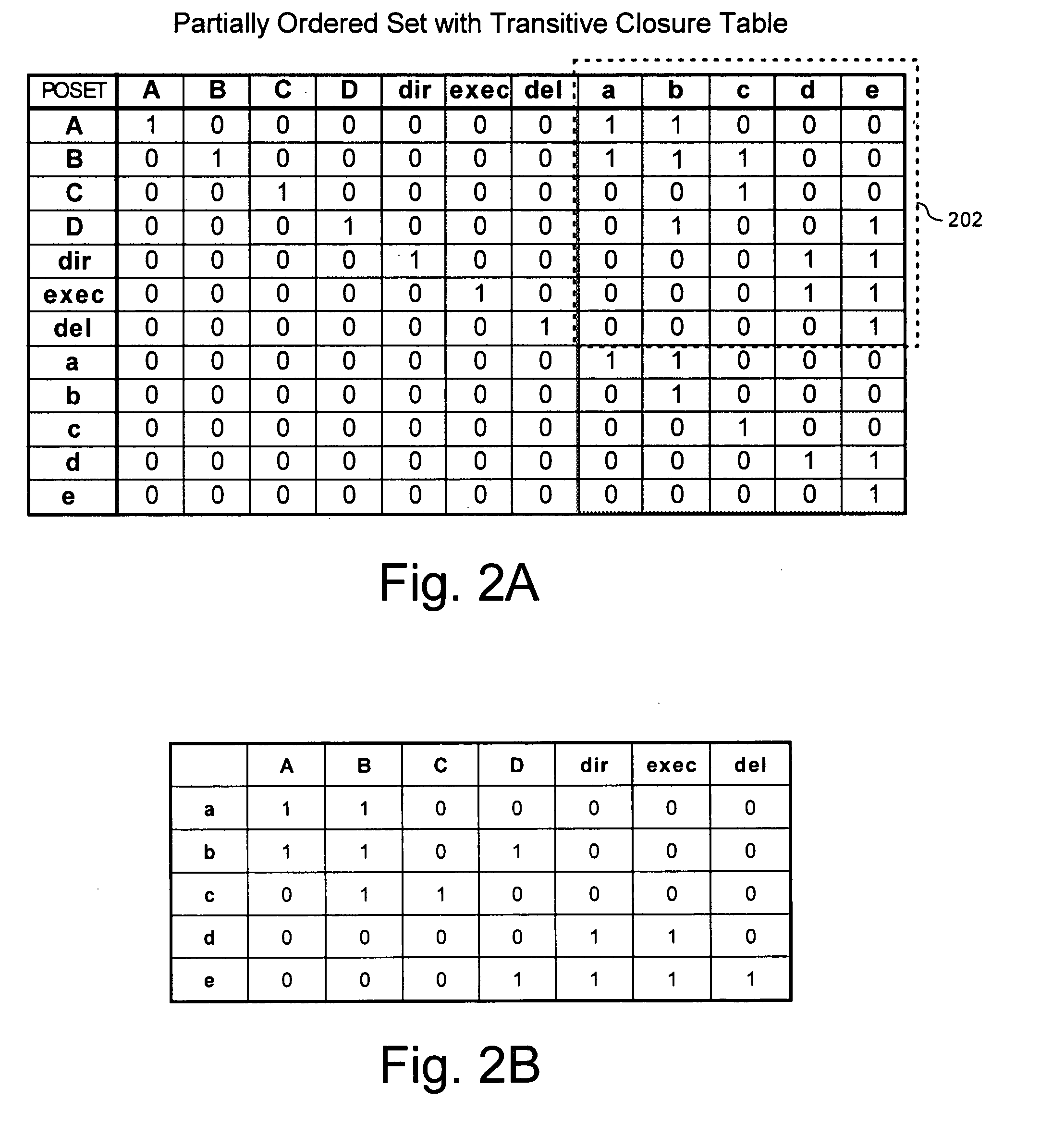
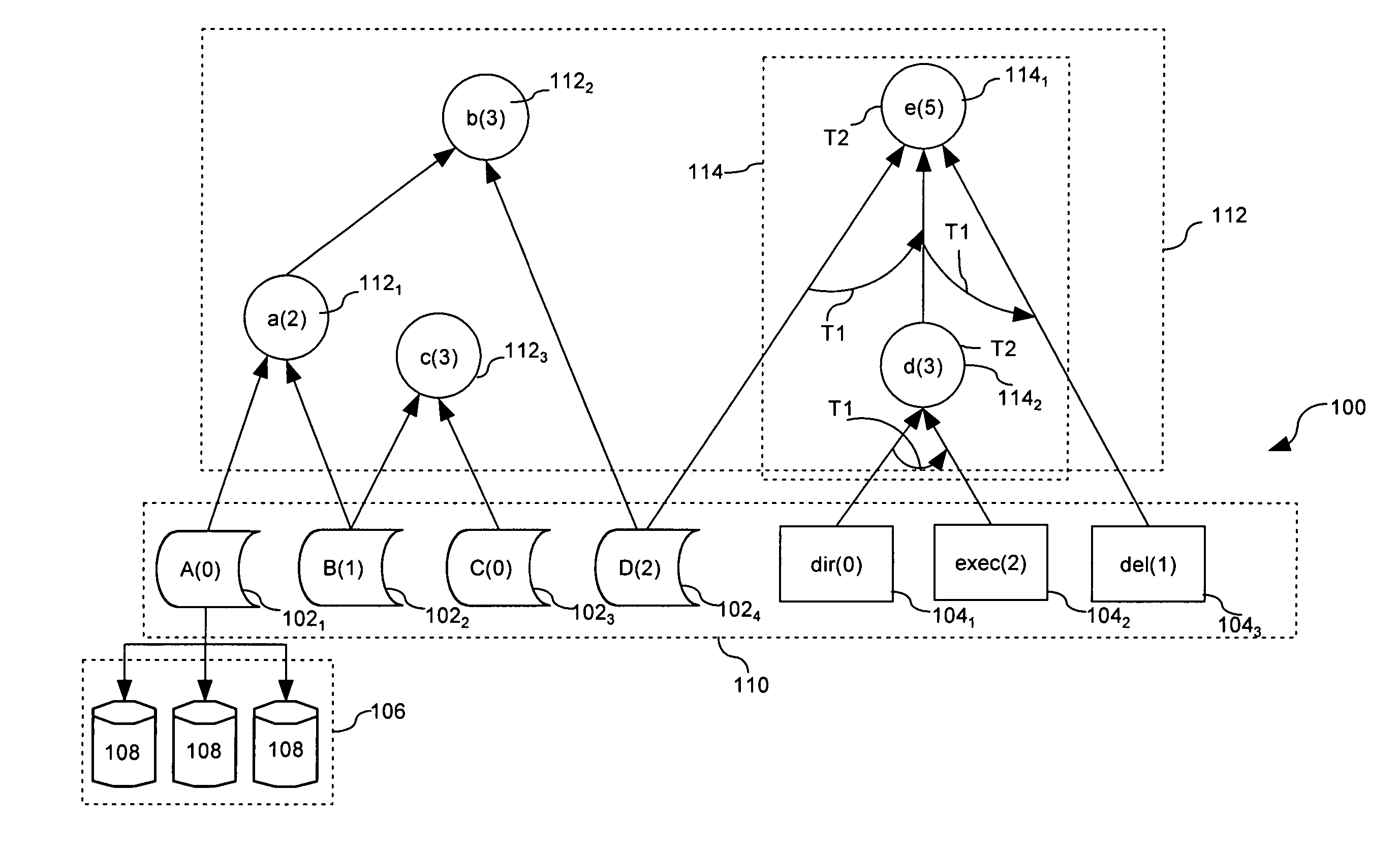
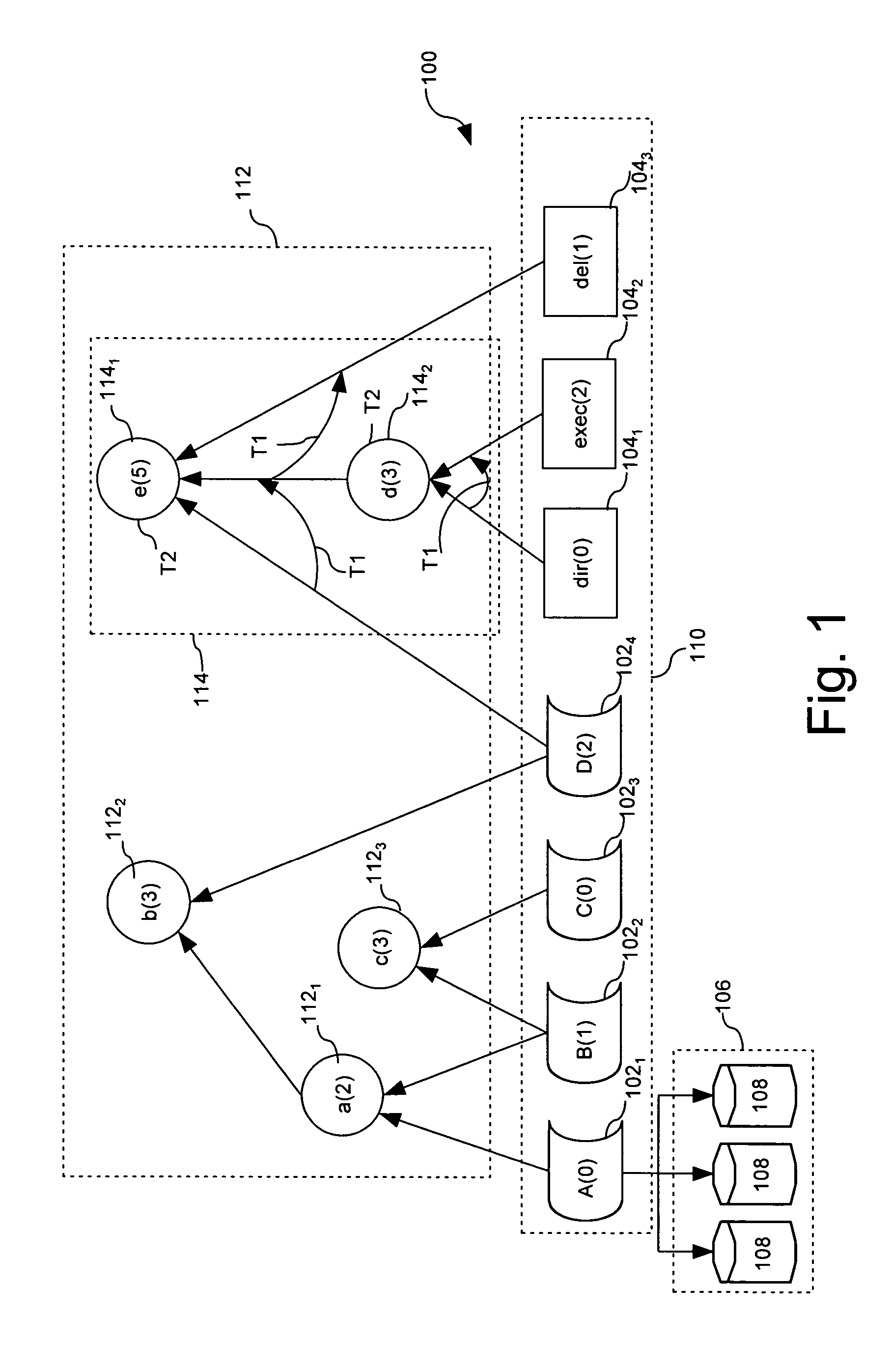
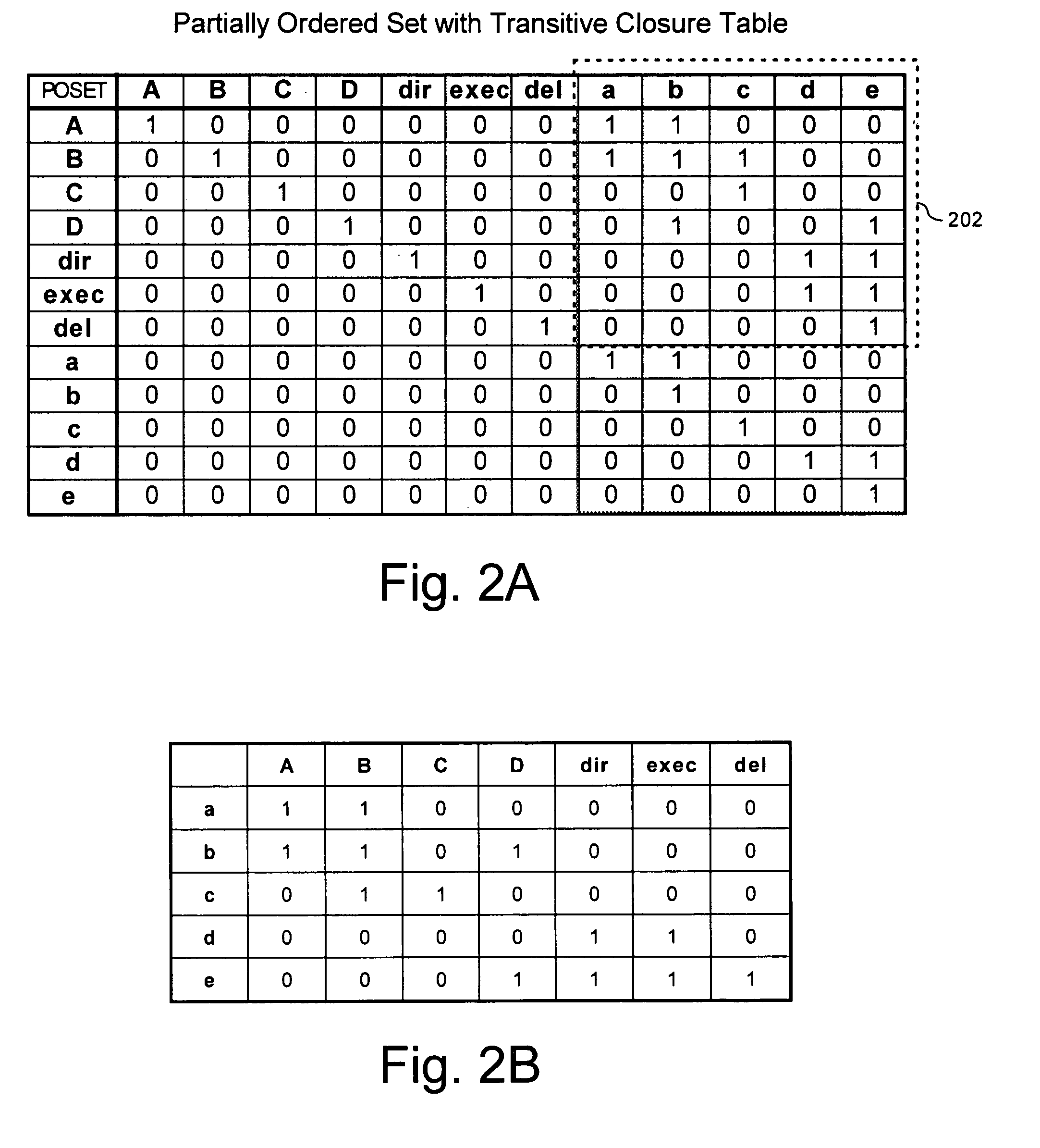
Enforcing computer security utilizing an adaptive lattice mechanism
ActiveUS20050204131A1Unauthorized memory use protectionDigital data protectionInformation typeComputerized system
Method and apparatus for ensuring secure access to a computer system (1000). The method can begin with the step of receiving in the computer system a request from an entity (using 1002). The entity can have a predetermined access authorization level for access to a first base node (110) representing an information type (102) or a computer system function (104). The system determines if the access request completes a prohibited temporal access pattern for the entity. The system also compares a minimum access level established for the first base node to the predetermined access authorization level assigned to the entity. Thereafter, the system can grant the access request only if the minimum access level for the first base node does not exceed to the predetermined access authorization level.
Owner:LIONRA TECH LTD
Flexible Cryogenic Probe Tip
InactiveUS20110184402A1Facilitate proper placementPromote contraction and expansionCatheterSurgical instruments for coolingMedicineLinearity
One embodiment of the invention is a flexible cryogenic probe tip. The flexible probe tip has a linear freeze zone at a distal end of the probe that allows for its placement and precisely controlled movements. The flexible cryogenic probe tip precisely conforms to the target tissue surface to create a linear lesion. In addition, the probe tip is steerable to facilitate proper placement with minimal access points into a patient's body. Various configurations of the flexible probe tip allow it to conform and ablate tissue of many sizes, shapes, and / or dimensions. Methods of utilizing the cryogenic probe tip include steps of positioning the distal end at a tissue site for at least one ablative procedure, maneuvering the distal end to the tissue site, directing a cryogen from the supply source to the distal end, controlling a flow of cryogen from the supply source to the distal end and back to the supply source, and segmenting control of the distal end mechanically or through the step of controlling the flow of cryogen.
Owner:ENDOCARE
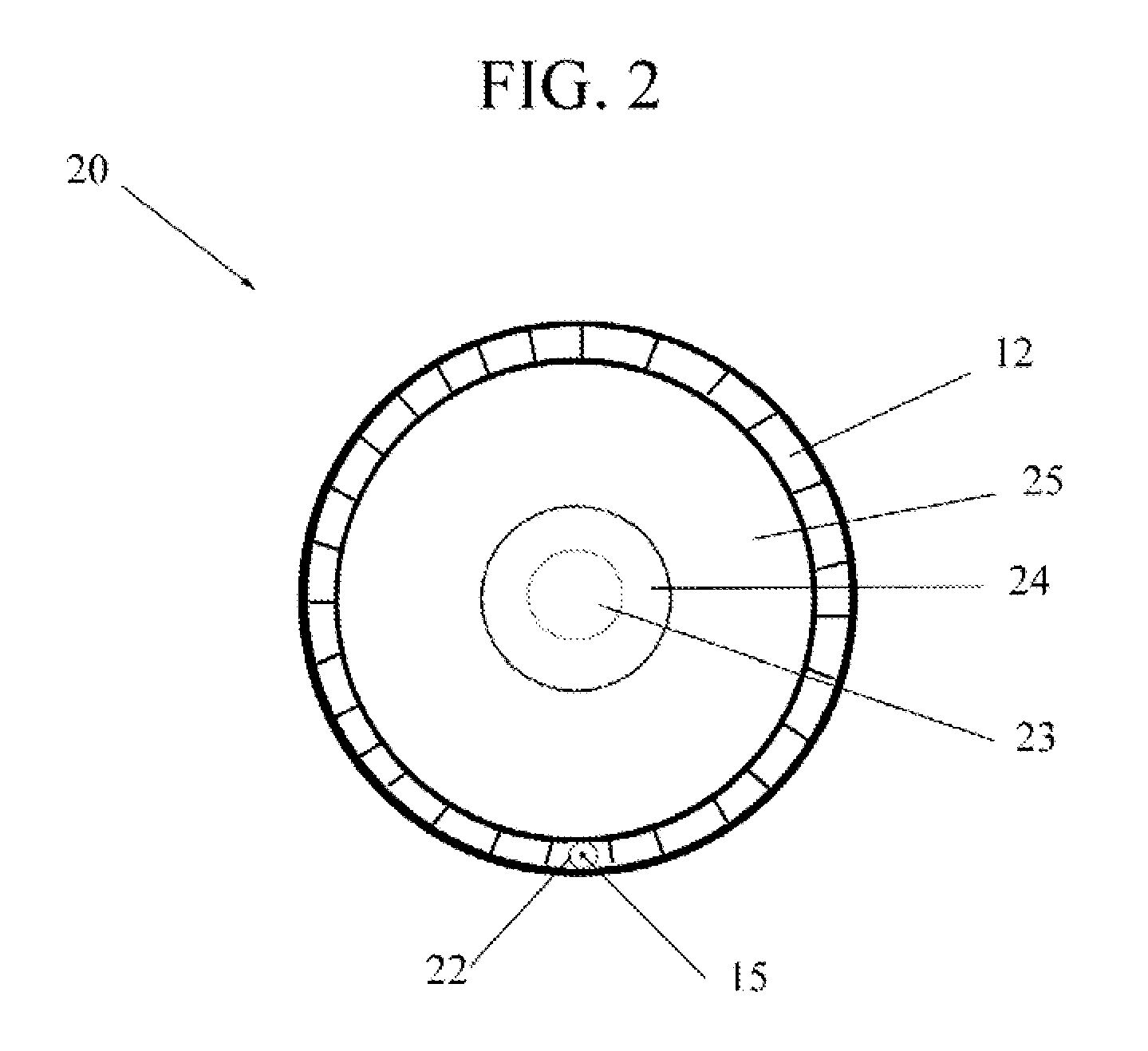
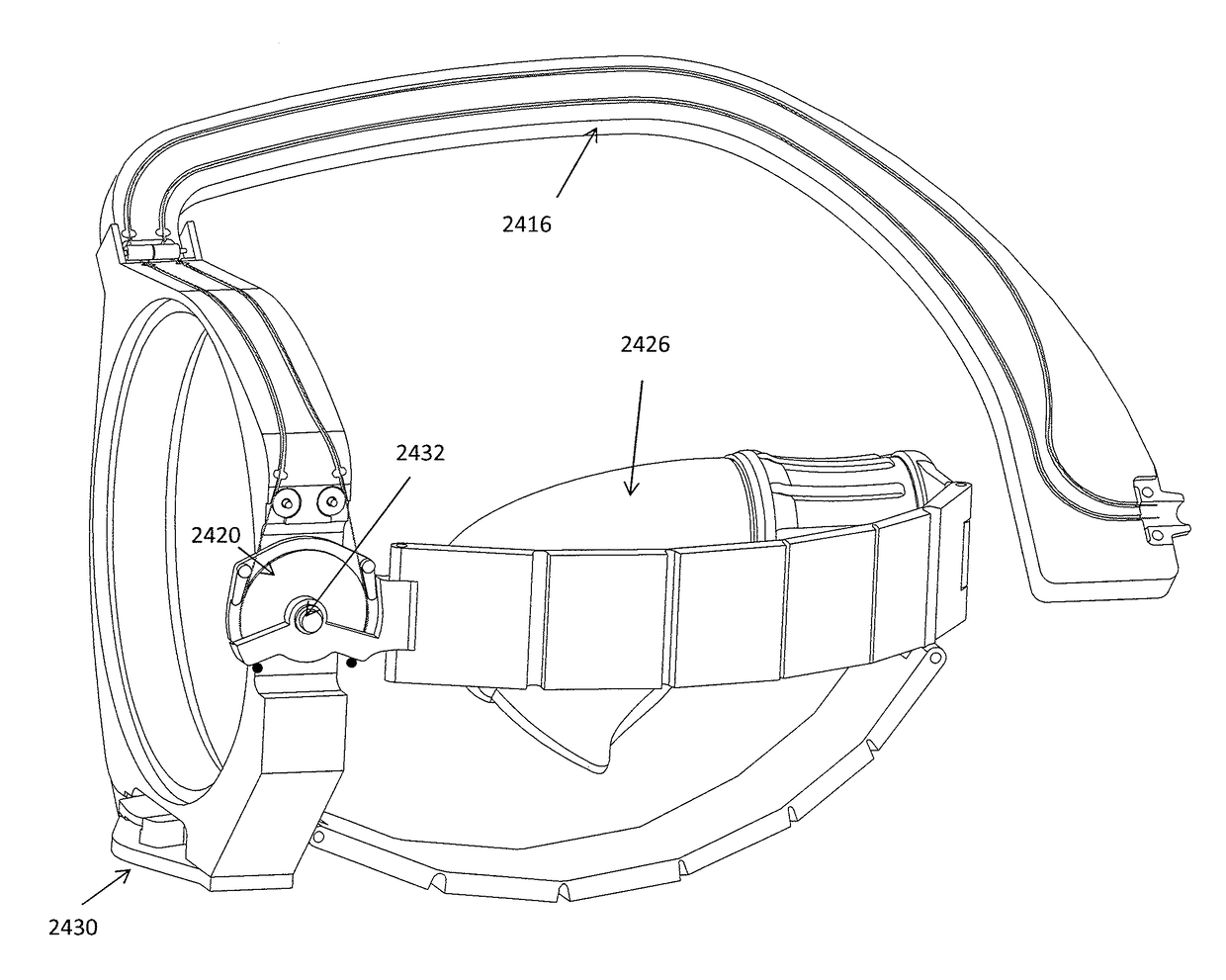
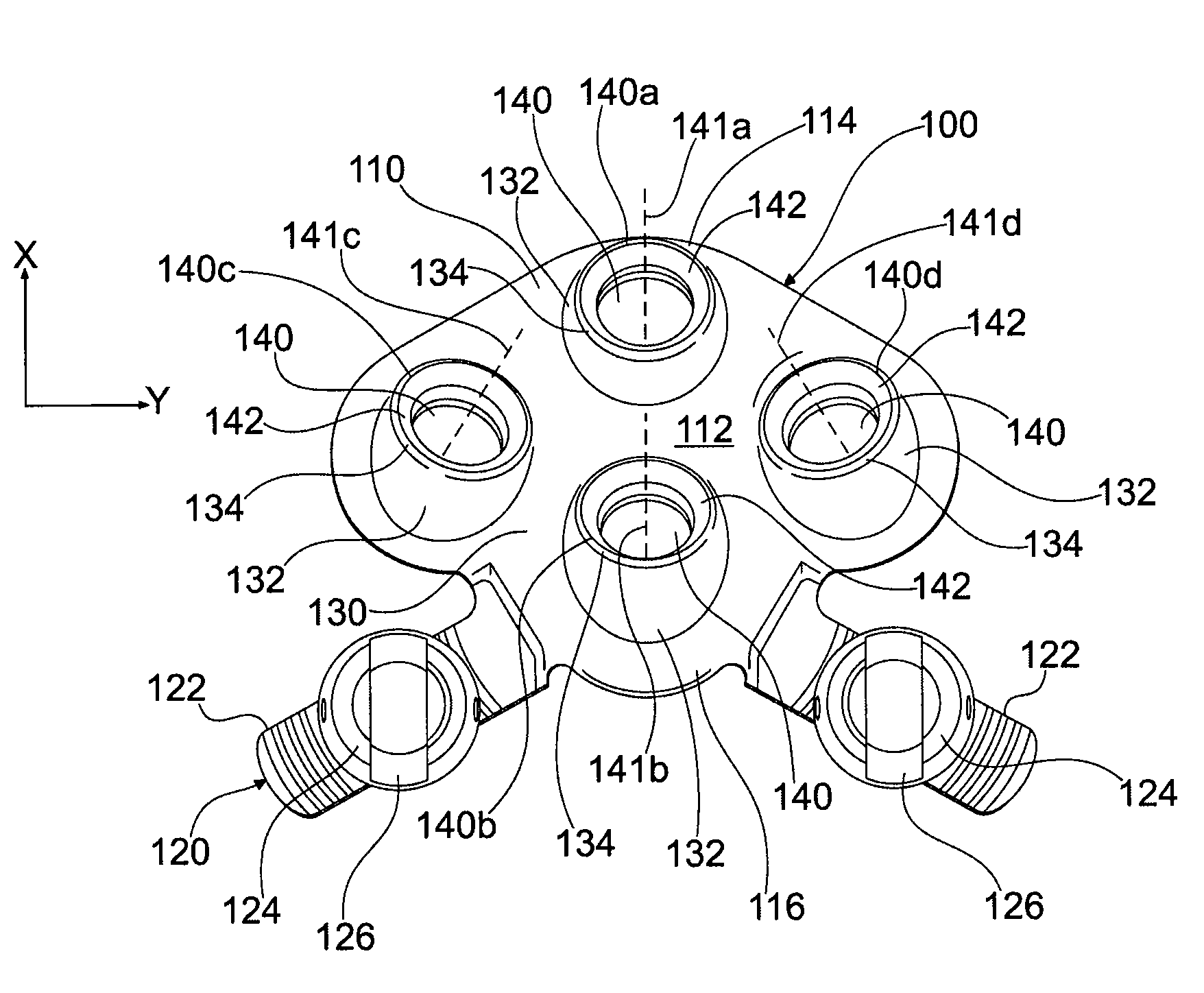
Attachment apparatus for remote access tools
ActiveUS20160303734A1Improve comfortImprove fitMachine supportsDiagnosticsCouplingDegrees of freedom
Apparatuses and methods for attaching a minimal access tool to a user's boy (e.g., wrist or forearm) so that movements of the user's forearm, wrist, hand and fingers can control movements at a distal end of the minimal access tool. In particular, described herein are forearm attachment devices (which may be used with or integrated into) a minimal access tool including a cuff configured to secure to the user's forearm and a coupling joint configured to connect the cuff to the frame so that the cuff may move relative to the frame with between 1 and 4 degrees of freedom.
Owner:FLEXDEX INC
Method to Reduce Power Consumption of a Register File with Multi SMT Support
InactiveUS20090292892A1Reduce in quantityMemory adressing/allocation/relocationDigital computer detailsProcessor registerControl register
A method for reducing the power consumption of a register file of a microprocessor supporting simultaneous multithreading (SMT) is disclosed. Mapping logic and associated table entries monitor a total number of processing threads currently executing in the processor and signal control logic to disable specific register file entries not required for currently executing or pending instruction threads or register file entries not meeting a minimum access threshold using a least recently used algorithm (LRU). The register file utilization is controlled such that a register file address range selected for deactivation is not assigned for pending or future instruction threads. One or more power saving techniques are then applied to disabled register files to reduce overall power dissipation in the system.
Owner:IBM CORP
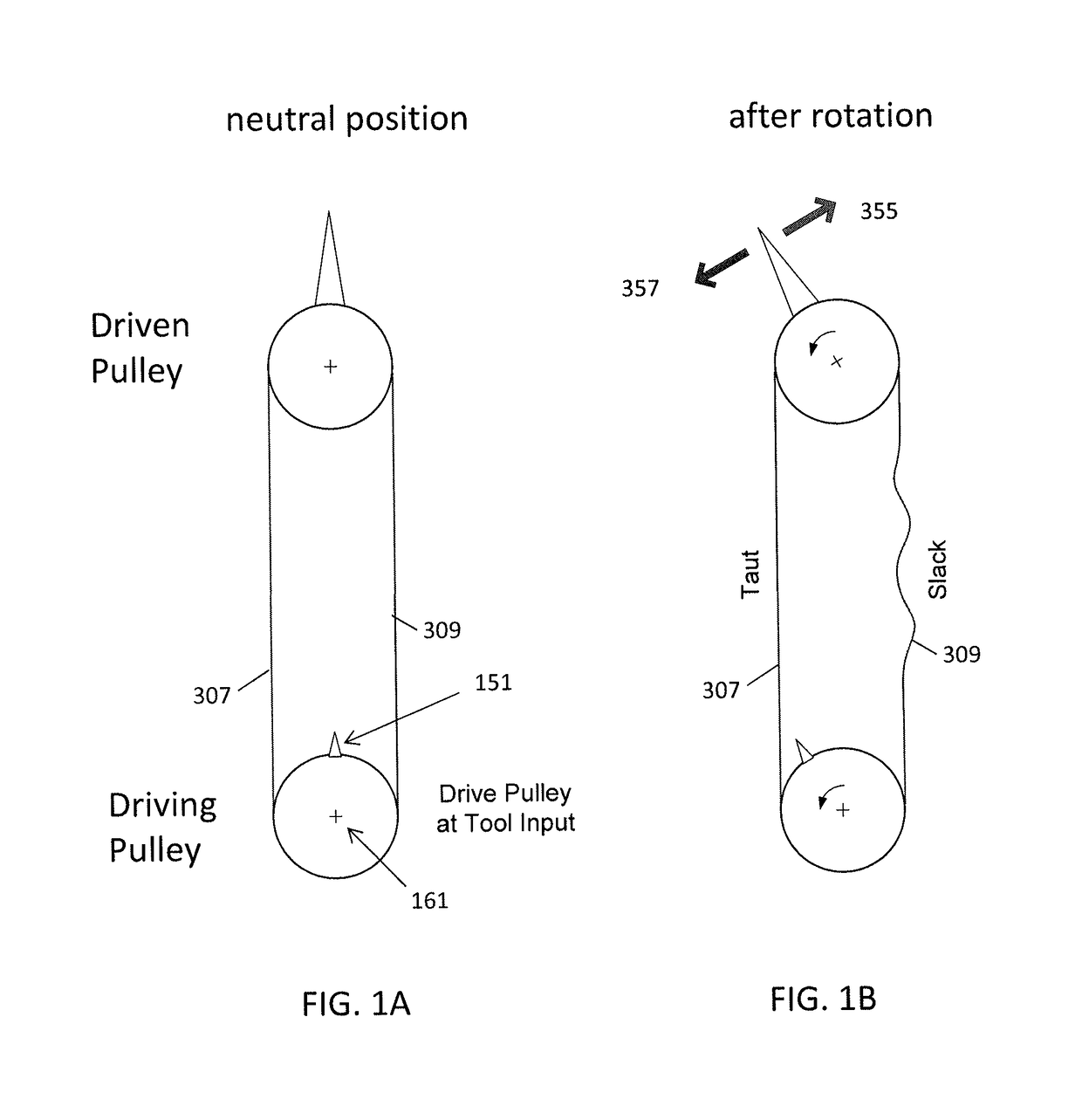
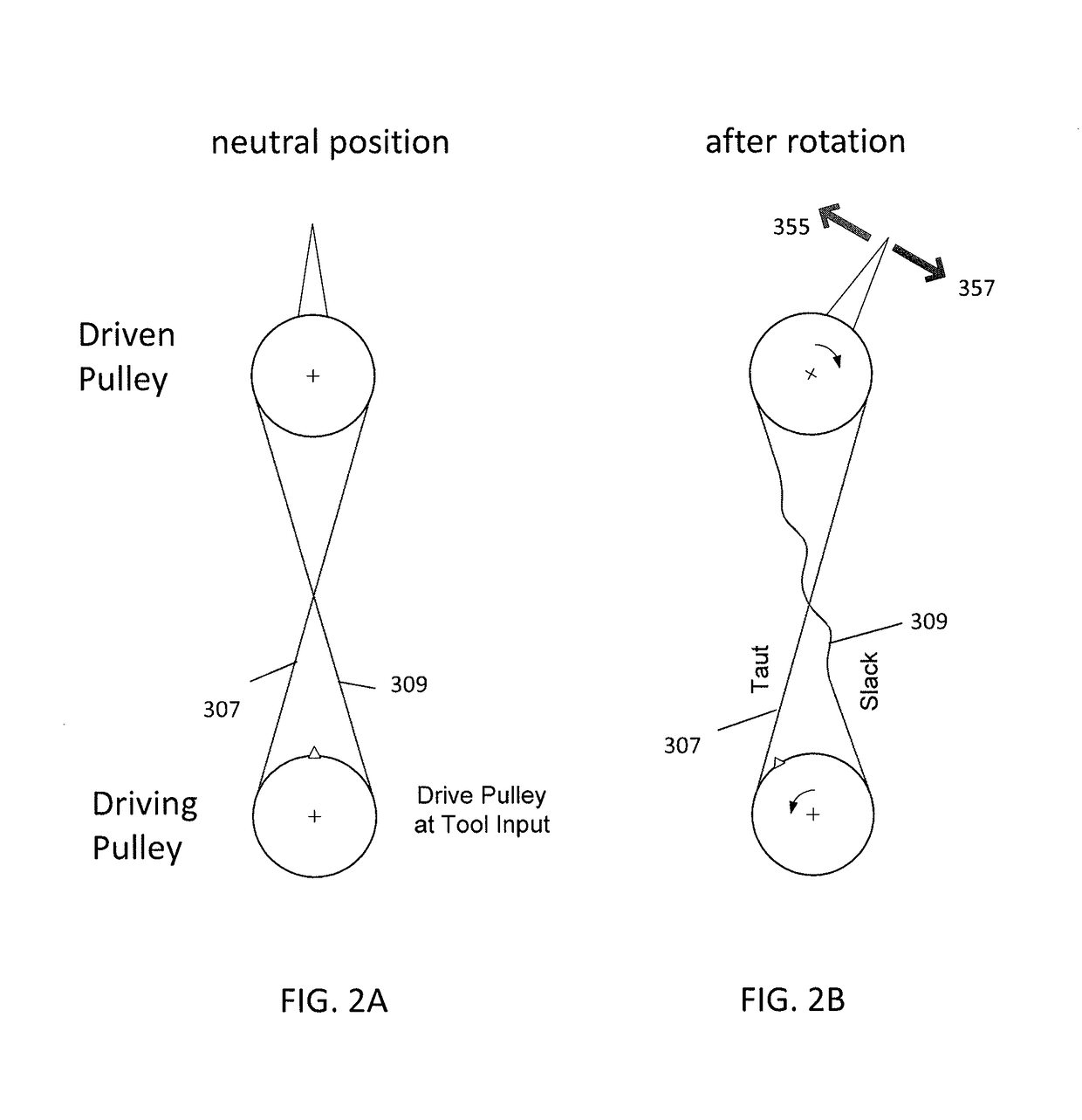
Tension management apparatus for cable-driven transmission
ActiveUS20180080533A1Reduce and eliminate slackIncrease wrap angleEndoscopesLaproscopesPath lengthEngineering
Slack-compensating pulleys, transmission systems including slack-compensating pulleys, and methods of operating these. In general, slack-compensating pulleys include a pulley body onto which a cable can wind, and one or more (e.g., two) slack take-up surfaces that rotate with the pulley body that are configured to remove slack form an outgoing length of cable by increasing the cable path length and wrap angle. In particular, described herein are minimal access tools having slack-compensating transmissions.
Owner:RGT UNIV OF MICHIGAN
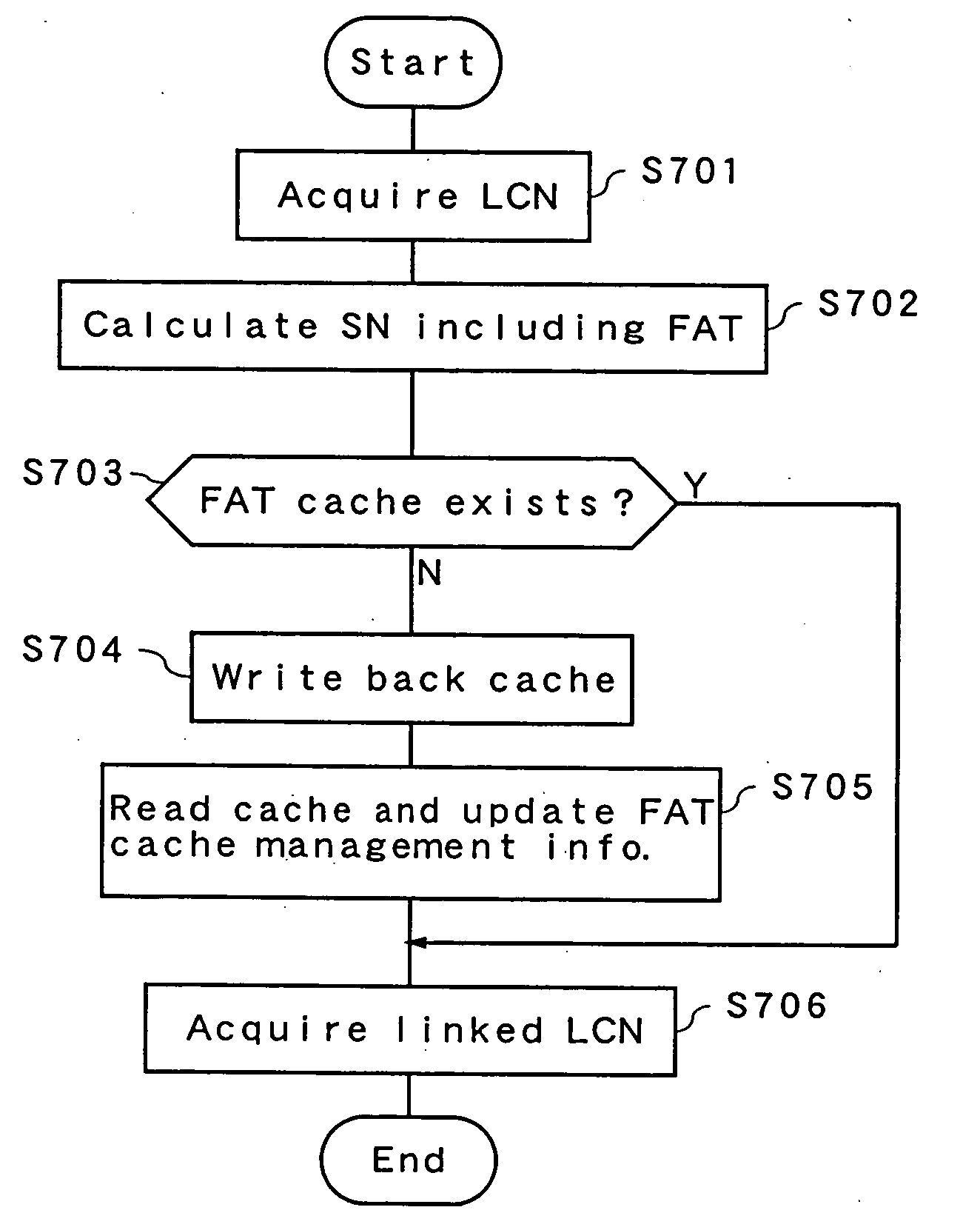
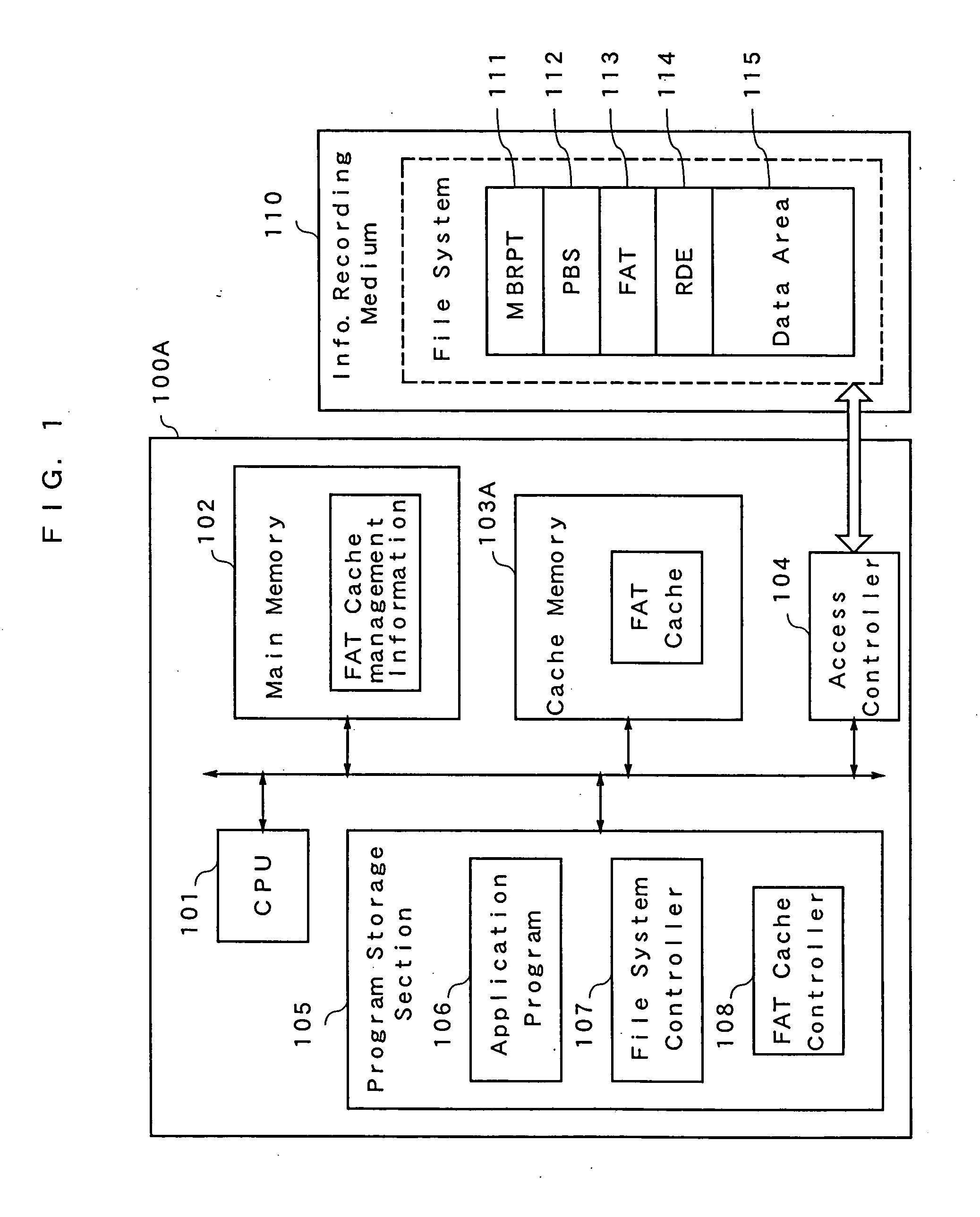
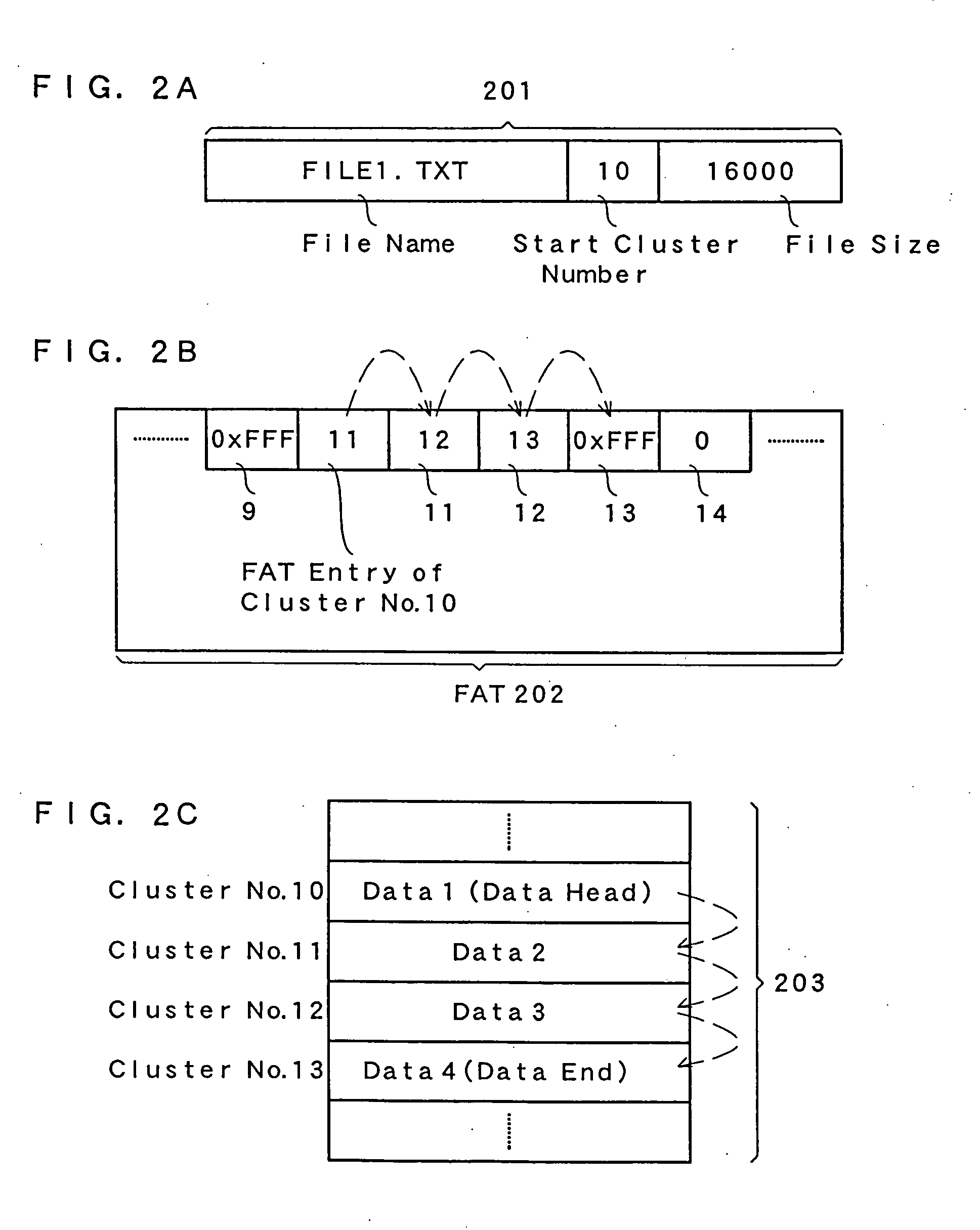
Data area managing method in information recording medium and information processor employing data area managing method
ActiveUS20070174550A1Reduce accessMemory architecture accessing/allocationInput/output to record carriersComputer hardwareInformation processor
Area management information is cached in a cache memory by controlling the access size when an information processor accesses the area management information in an information recording medium. When the processing content of the information processor is to retrieve an free area from the area management information, a physical management block size determined from the physical characteristics of the information recording medium is used. When the processing content is to acquire a link destination from the area management information, minimum access unit of the information recording medium is used. Consequently, overhead can be lessened when the area management information is accessed.
Owner:PANASONIC CORP
Minimal access lumbar diskectomy instrumentation and method
ActiveUS20050101985A1Prevent surfaceEasy to separateCannulasInfusion syringesMuscle tissueEngineering
A minimal incision maximal access system allows for maximum desirable exposure along with maximum access to the operative field utilizing a minimum incision as small as the METRx and Endius systems. Instead of multiple insertions of dilating tubes the design is is a streamlined single entry device to avoid repetitive skin surface entry. The system offers the capability to expand to optimum exposure size for the surgery utilizing hinged bi-hemispherical or oval working tubes applied over an introducer obturator which is controllably dilated to slowly separate muscle tissue. Deeper end working and visualization areas with maximum proximal access and work dimensions are provided to makes the operative procedure safer in application and shorten the surgeons's learning curve because it most closely approximates the ability to use open microdiskectomy techniques.
Owner:K2M
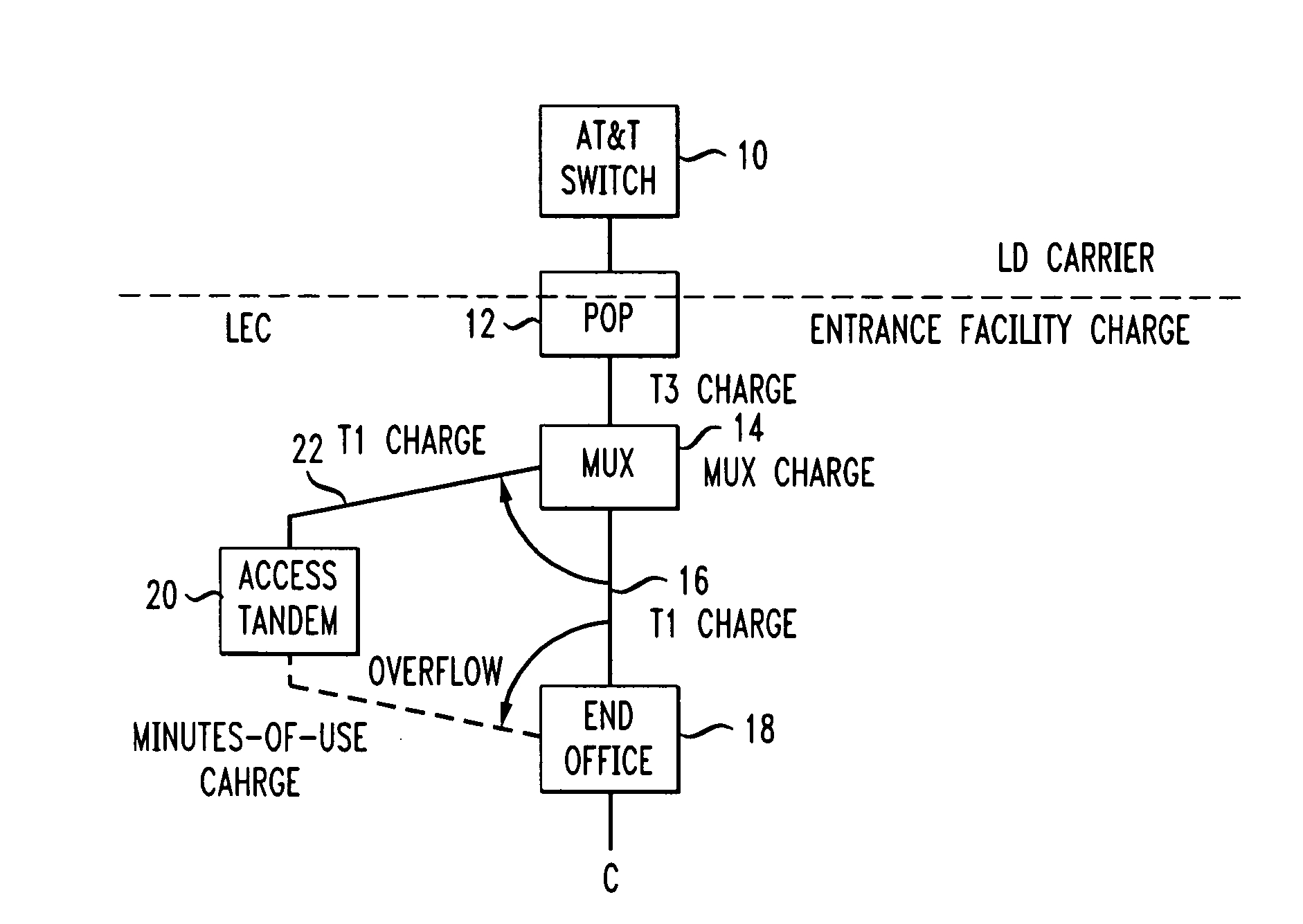
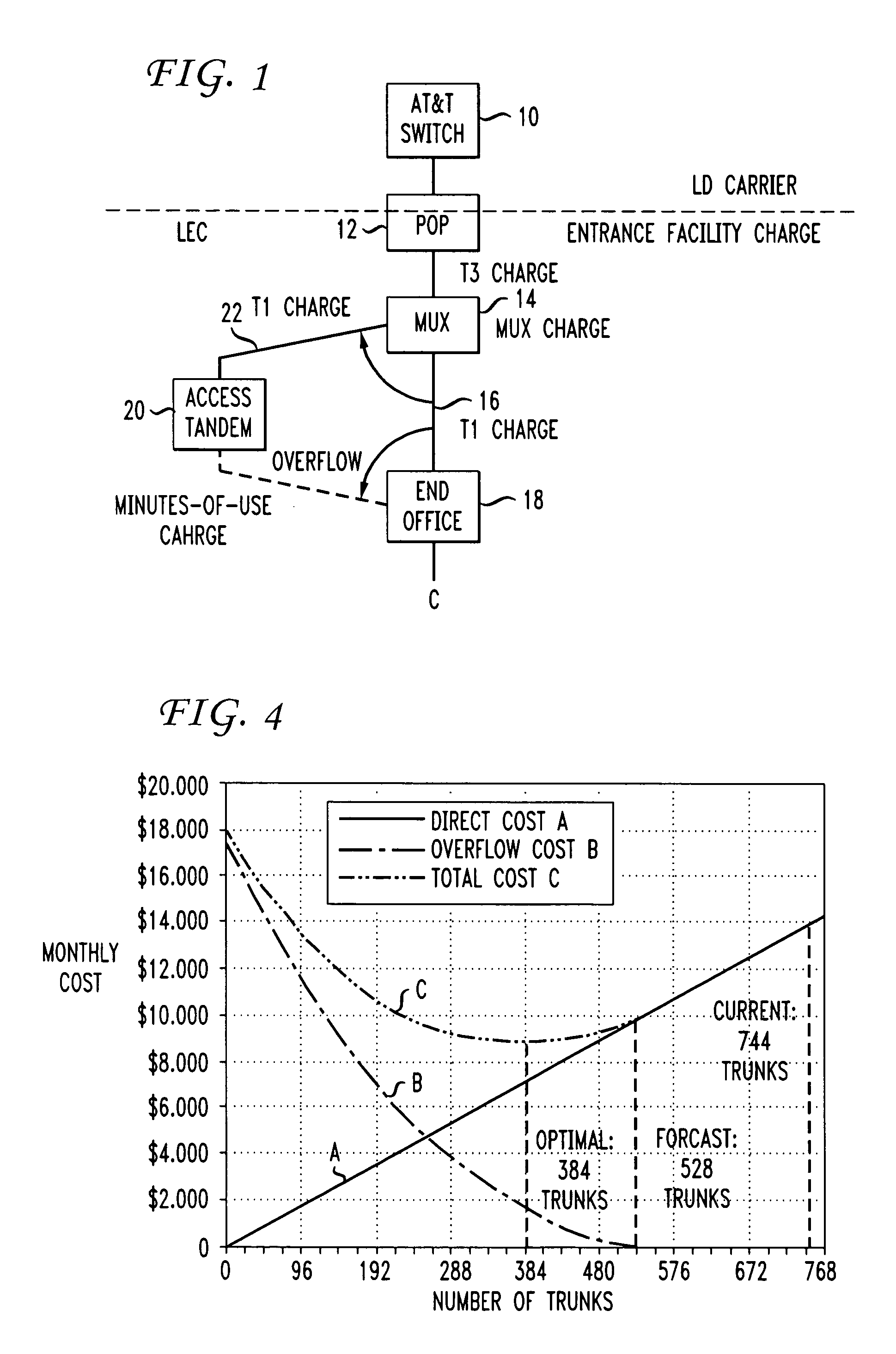
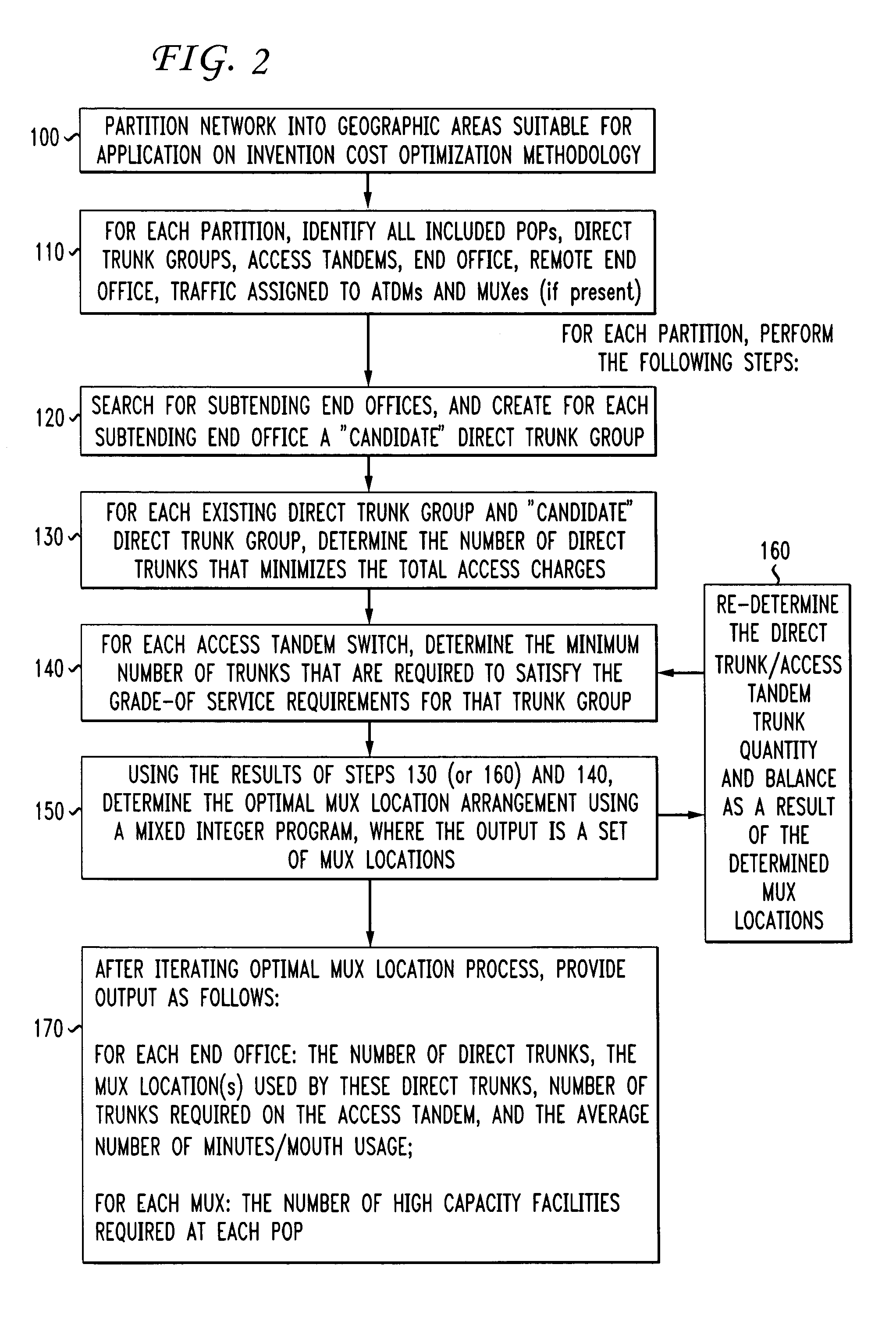
Switched-access network optimization methodology
InactiveUS7583795B1Methodology to be enhancedMultiplex system selection arrangementsInterconnection arrangementsAccess networkEngineering
A methodology for optimizing the access charges paid by a long distance carrier involves the use of a “sizing” operation to determine the optimal balance between direct trunks and access tandems (on a per LATA basis) so as to provide minimal access charges. Once the sizing has been completed, a mixed integer program is used to find the optimal MUX assignments for each LATA. The sizing operation is then re-visited, based on the MUX assignments, to determine if adjustments are required to reduce costs. Any changes in the sizing are then reviewed in the MUX assignment mixed integer program. The end result is a definition of the quantity of direct trunks, access tandem trunks and overflow minutes-of-use charges for each end office, as well as the number of high capacity facilities required for each MUX.
Owner:AMERICAN TELEPHONE & TELEGRAPH CO
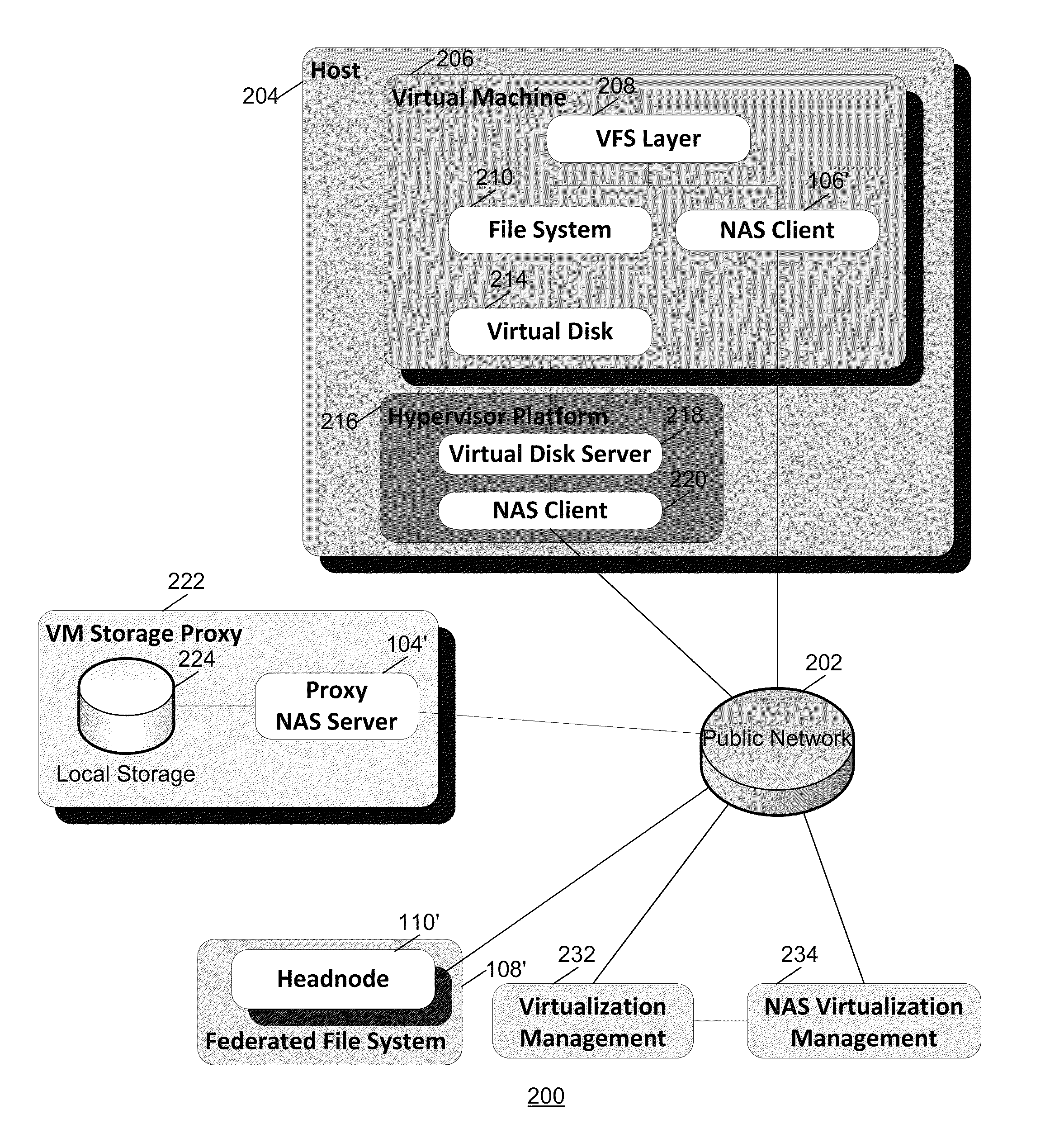
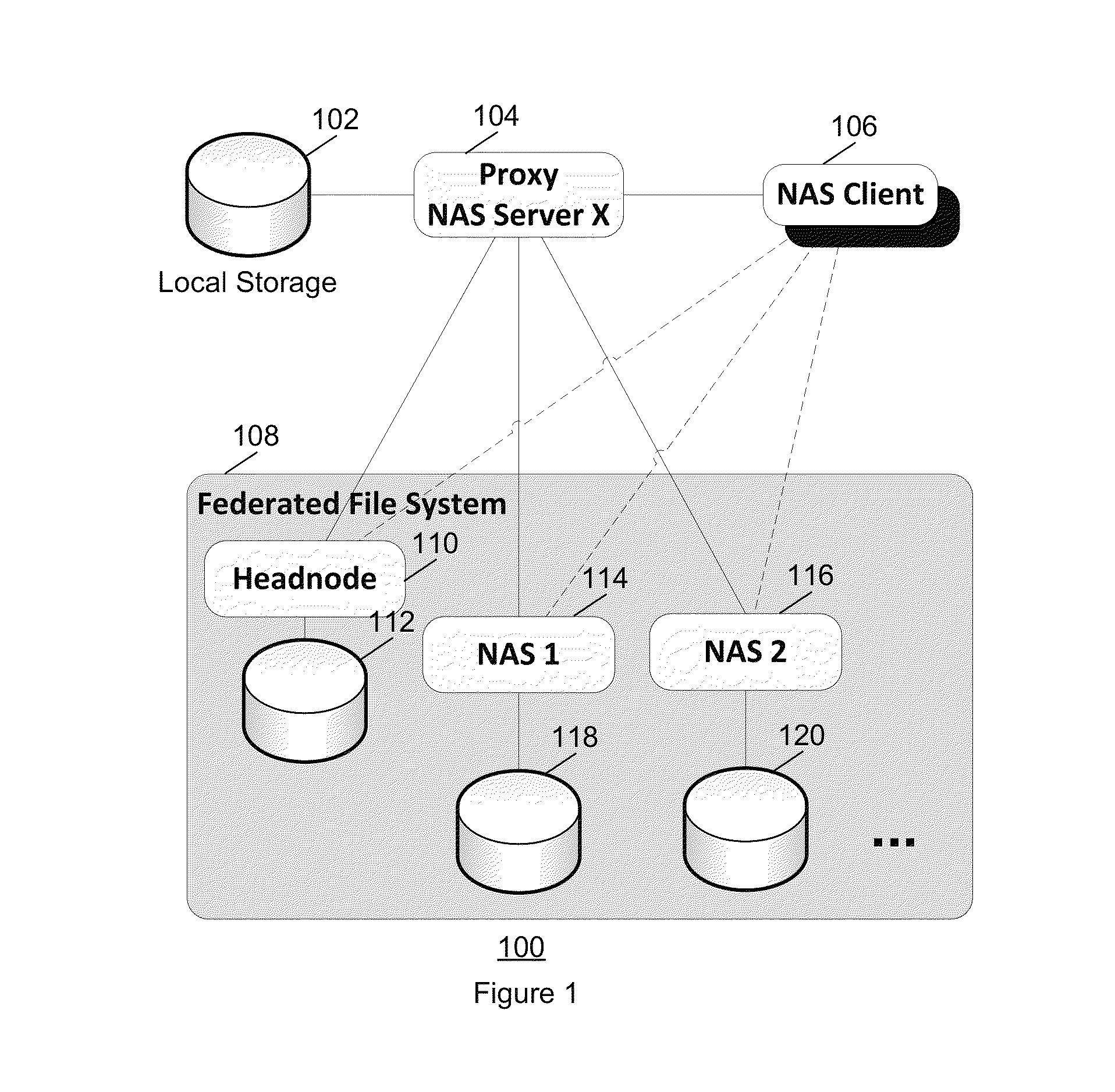
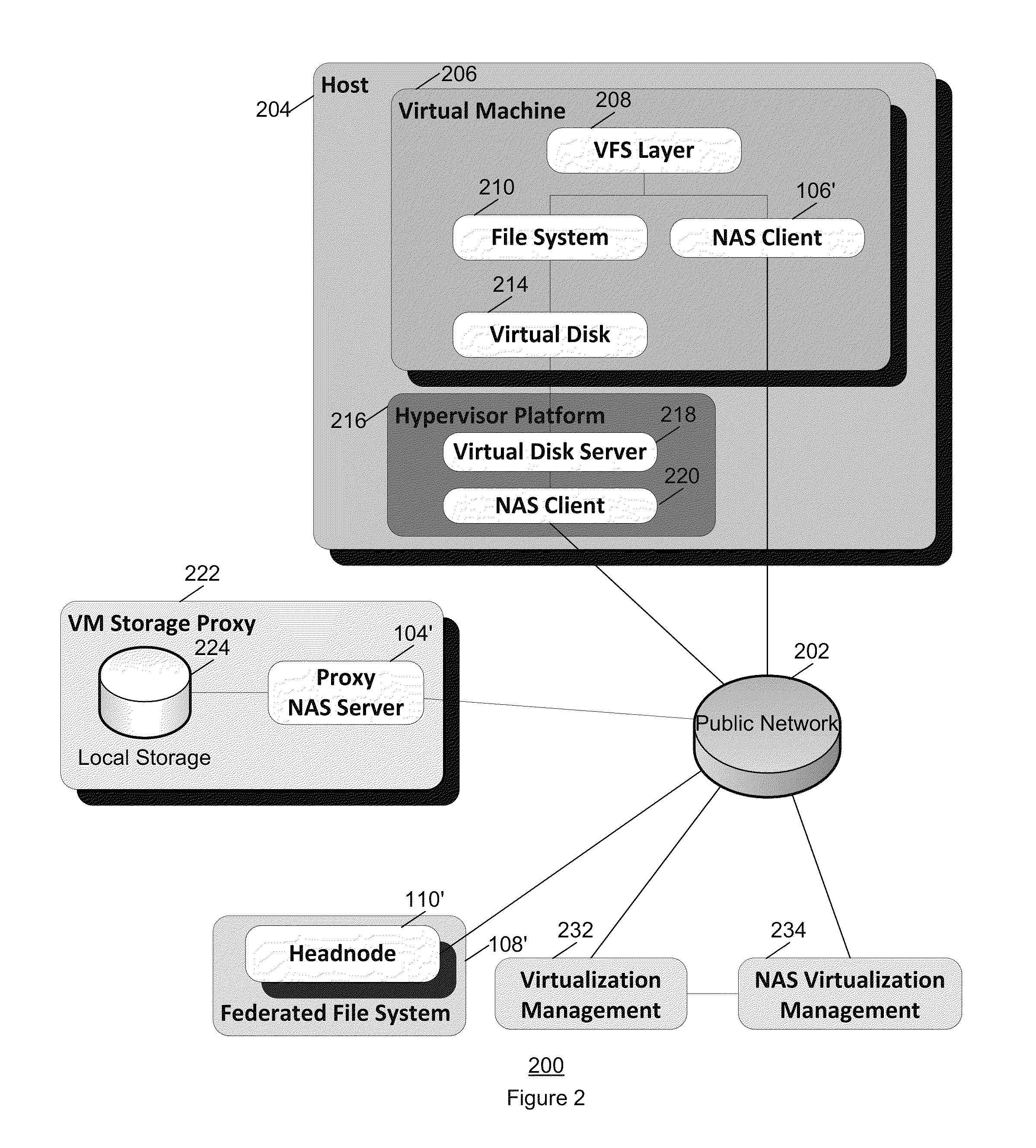
Scalable storage for virtual machines
ActiveUS8812566B2Digital data information retrievalSpecial data processing applicationsControl selectionClient-side
A method and system is disclosed for providing storage services to Virtual Machines (VMs) and the Hypervisor Platforms that host them. NAS referrals are used to control selection of NAS proxy servers that are optimized for the support of VMs and the Hypervisor Platforms accessing directories that are exclusively used in conjunction of a single VM. Referrals are dynamically controlled in a manner specific to the target environment to provide an optimal combination of local and network storage in support of VMs. A method of using named attributes allows referrals to subsets of a directory. The overhead of using a NAS proxy is tailored to the smallest set of accesses required to gain beneficial result from the use of local storage, and using direct access to shared network storage when local storage is not allocated. Most of the new suggested techniques are transparent to the existing NAS clients; some techniques may require modification of the NAS client software.
Owner:NEXENTA BY DDN INC
Enforcing computer security utilizing an adaptive lattice mechanism
ActiveUS7302708B2Digital data processing detailsDigital computer detailsInformation typeComputerized system
Owner:LIONRA TECH LTD
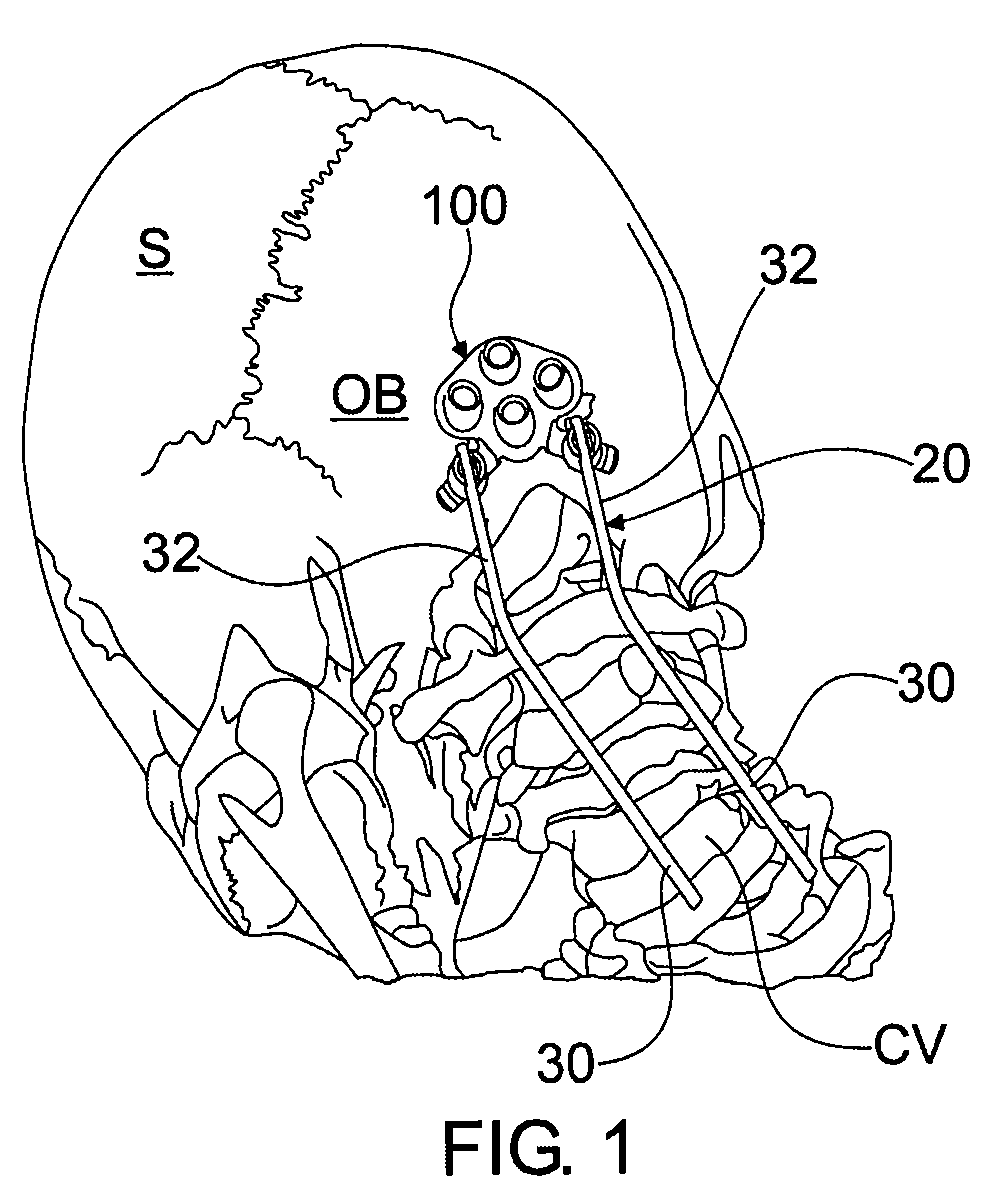
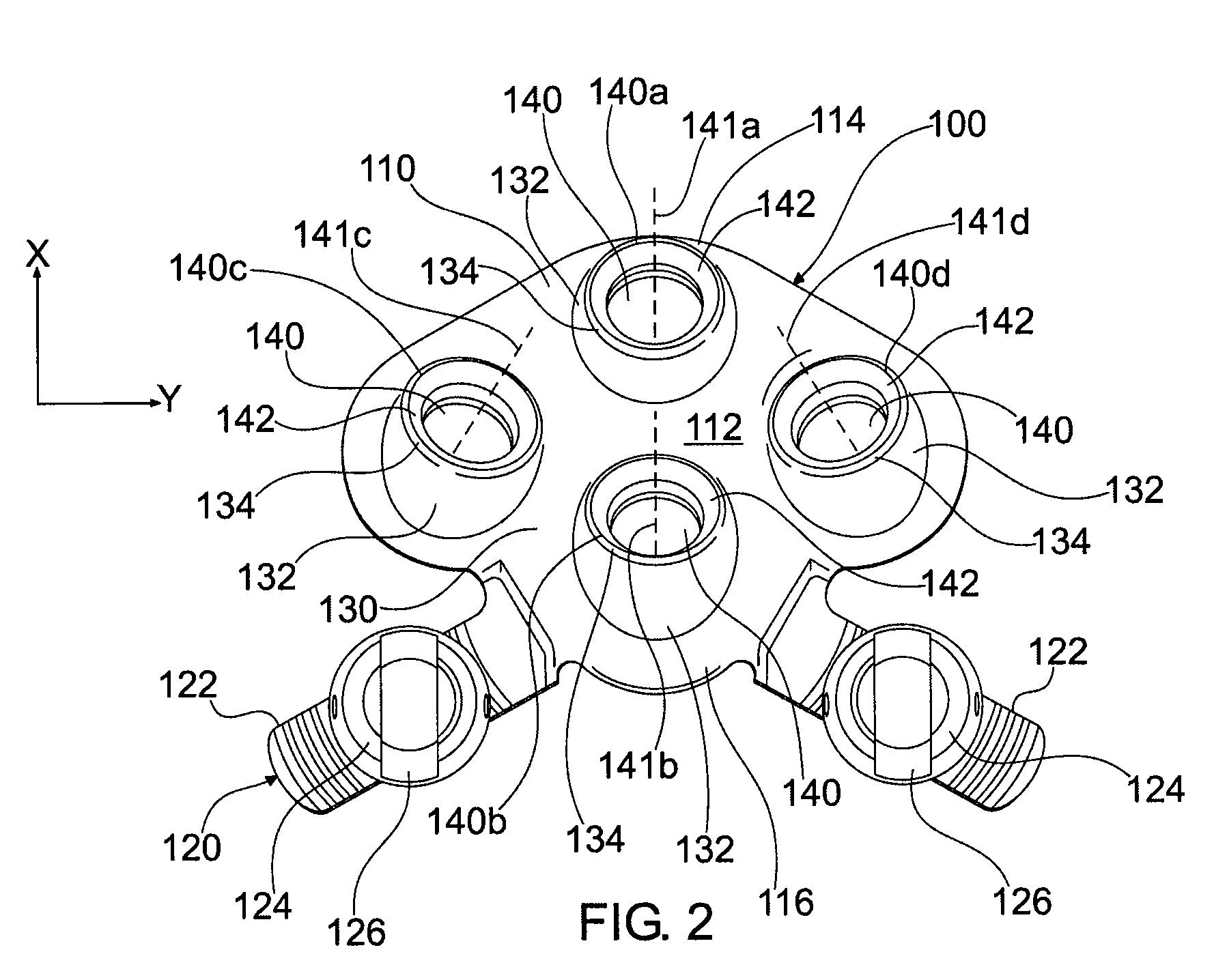
Minimal access occipital plate
Owner:AESCULAP IMPLANT SYST
Minimal access lumbar diskectomy instrumentation and method
A minimal incision maximal access system allows for maximum desirable exposure along with maximum access to the operative field utilizing a minimum incision as small as the METRx and Endius systems. Instead of multiple insertions of dilating tubes the design is a streamlined single entry device to avoid repetitive skin surface entry. The system offers the capability to expand to optimum exposure size for the surgery utilizing hinged bi-hemispherical or oval working tubes applied over an introducer obturator which is controllably dilated to slowly separate muscle tissue. Deeper end working and visualization areas with maximum proximal access and work dimensions are provided to makes the operative procedure safer in application and shorten the surgeons's learning curve because it most closely approximates the ability to use open microdiskectomy techniques. a dual frame system enables full or partial spreading of a working tube set, while an open frame facilitates a four point retraction system.
Owner:K2M
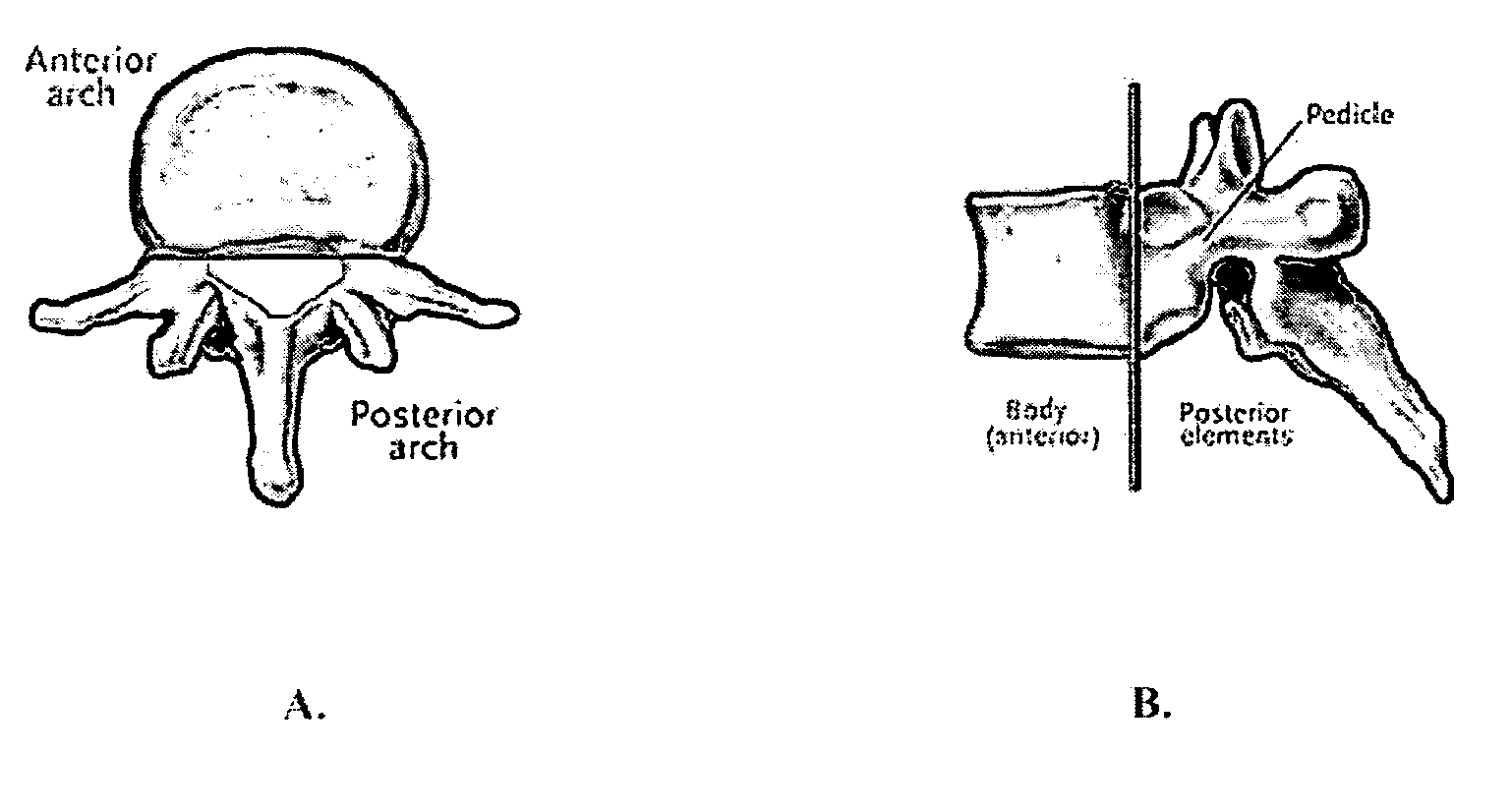
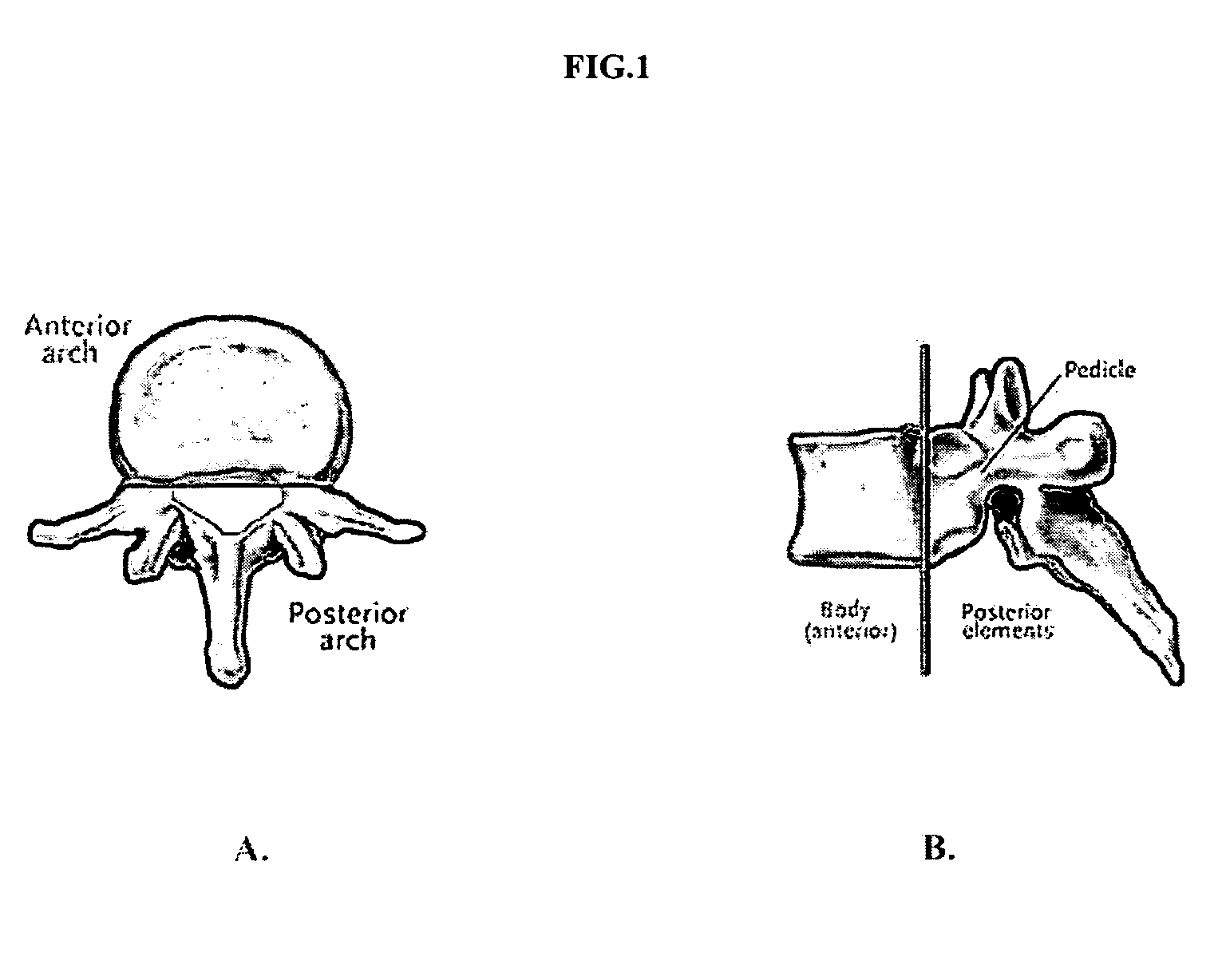
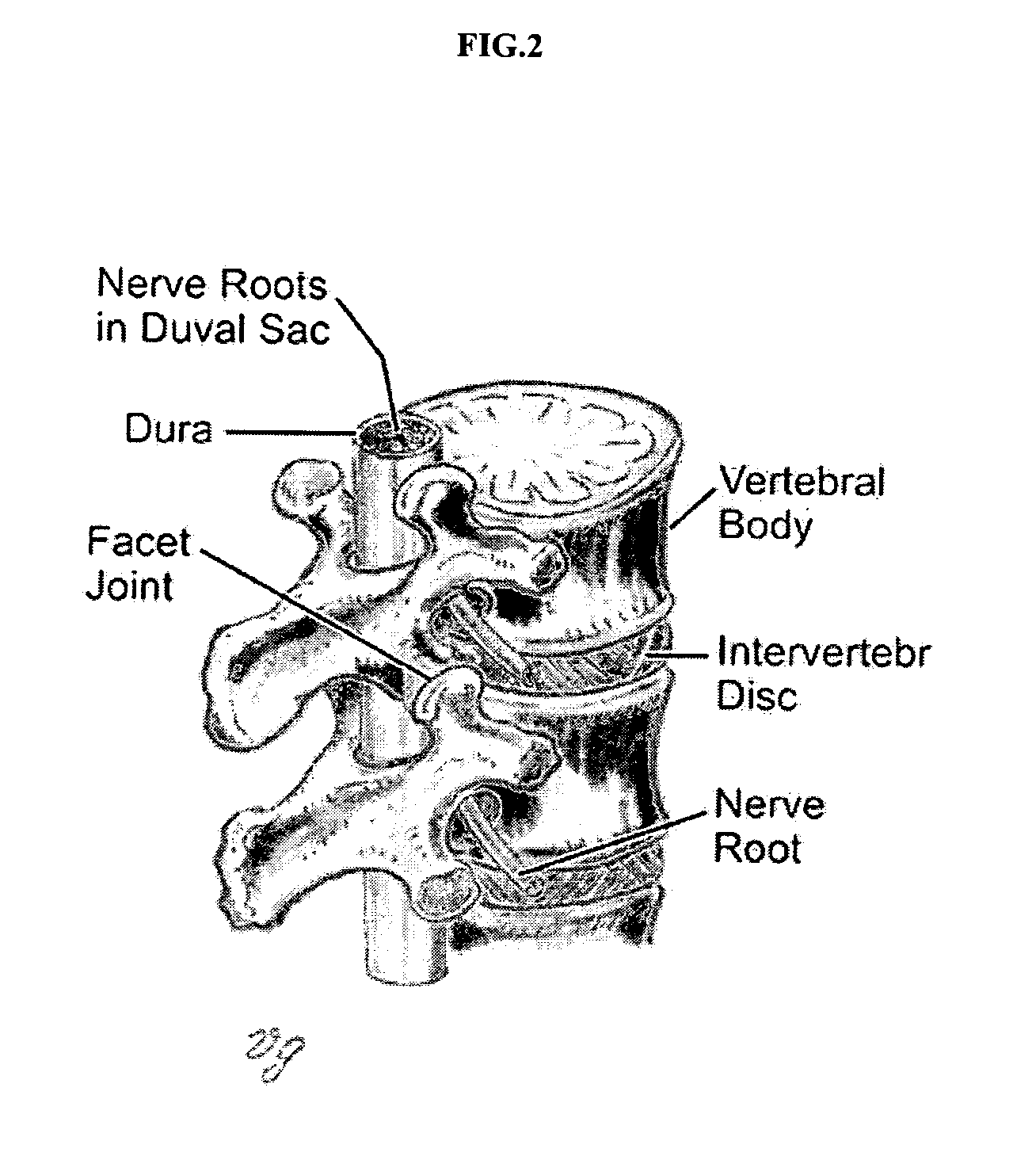
Methods of employing calcium phosphate cement compositions and osteoinductive proteins to effect vertebrae interbody fusion absent an interbody device
ActiveUS20080109003A1Fast stabilizationRapid strengthInternal osteosythesisBone implantMedicineBone-Inducing Protein
A minimal access method for mammalian vertebrae interbody fusion without the employment of an interbody device is described which comprises injecting a porous CaPC into an anterior portion of a disc space, and injecting an effective amount of fast-setting non-porous CaPC into an anterior portion of the disc space to rapidly produce a strong and stable interbody fusion without the employment of an interbody device. Methods are further described wherein at least one of the CaPCs comprises an effective amount of at least one osteoinductive protein. A minimal access method for vertebroplasty is described which comprises injecting an effective amount of a viscous non-porous CaPC into a vertebrae fracture channel to provide rapid stabilization and strength, and injecting a porous CaPC into trabecular bone space adjacent to the vertebrae fracture channel. Kits which relate to the methods of the present invention are described as well.
Owner:WARSAW ORTHOPEDIC INC
Method and apparatus for securely providing access and elevated rights for remote support
ActiveUS9742779B2Digital data processing detailsDigital data protectionComputer networkRemote system
An approach is provided to allow remote support representatives to carry out remote support session with minimal access and privileges to remote systems. An attempt is detected to establish a remote support session via a remote support appliance that is configured to establish the remote support session between a first device associated with a support representative and a second device associated with a user. A credential that provides an elevated access privilege is retrieved in response to the detection. The credential is provided to the first device for use in the establishment of the remote support session.
Owner:BEYONDTRUST CORP
Apparatus and Process for Delivering a Silicone Prosthesis into a Surgical Pocket
ActiveUS20120143331A1Reduce deliveryEasy to installMammary implantsDiagnosticsBreast implantProsthesis
A tapered sleeve is provided that includes a lubricating coating on an inner surface. An implant (e.g., a pre-filled silicon breast implant) is introduced into a large end of the sleeve and extruded into a surgical pocket of minimal access incision size through a small-sized end of the apparatus.
Owner:KELLER MEDICAL