Patents
Literature
453 results about "Semantic association" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
What is Semantic Association. 1. A complex relationship between two resources in an RDF graph. Semantic Associations can be a path connecting the resources or two similar paths in which the resources are involved.
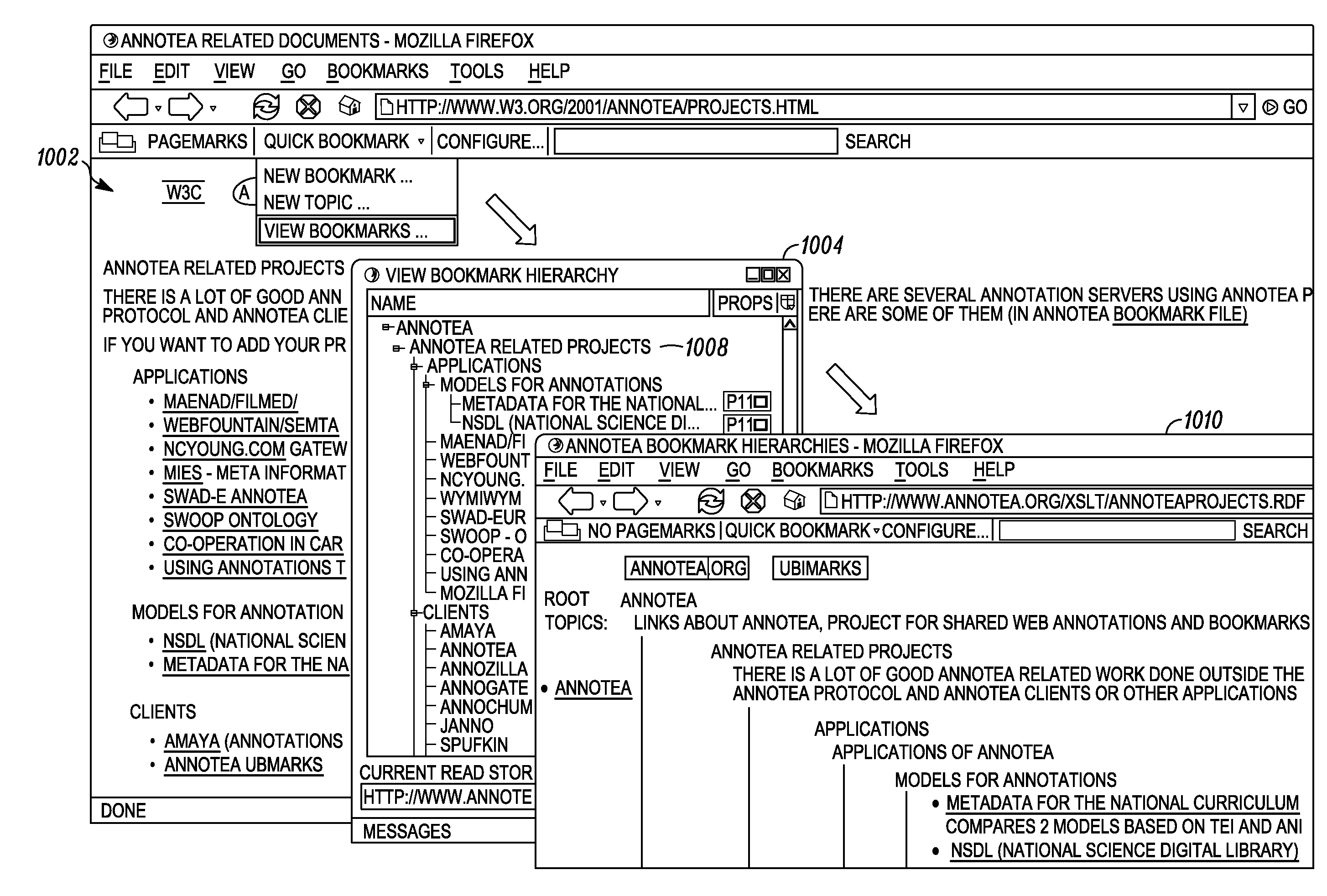
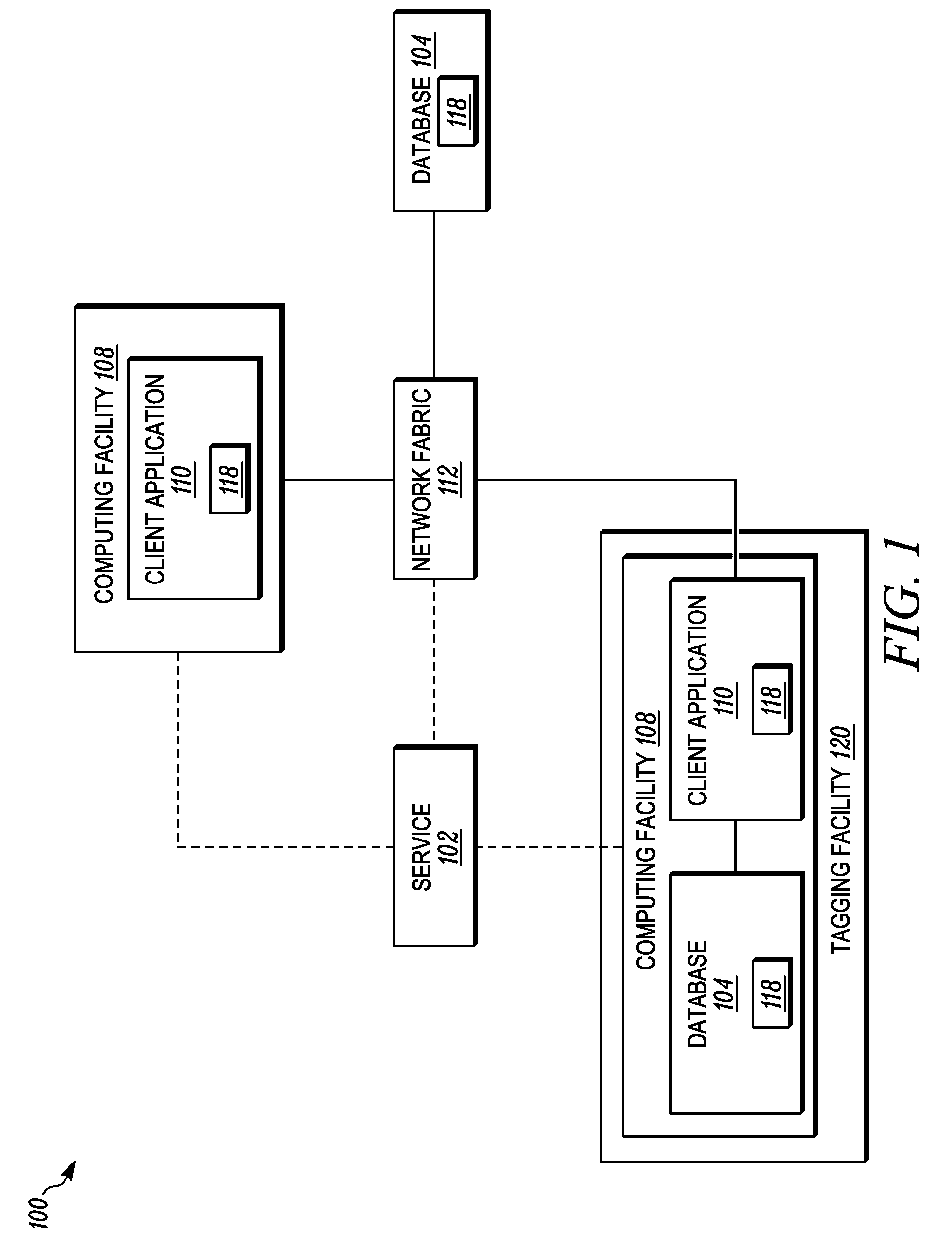
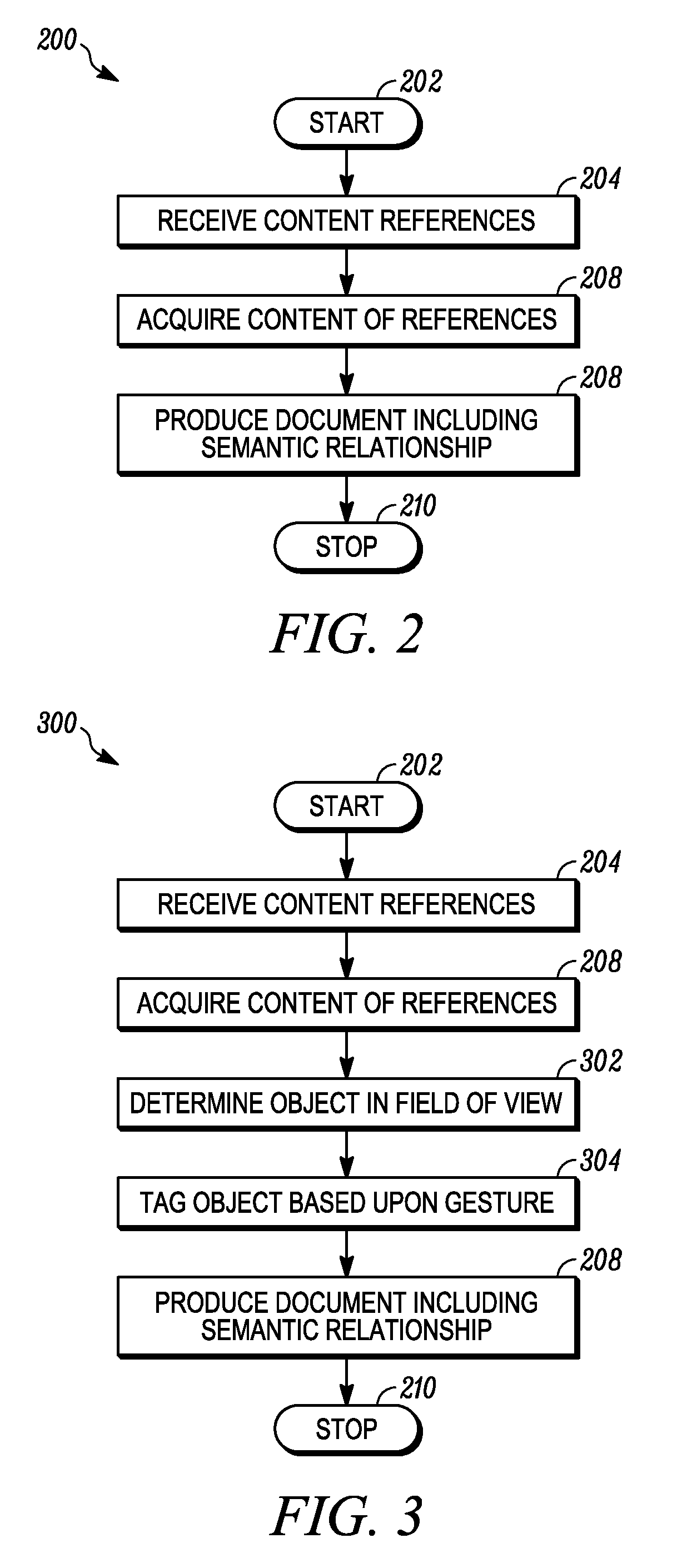
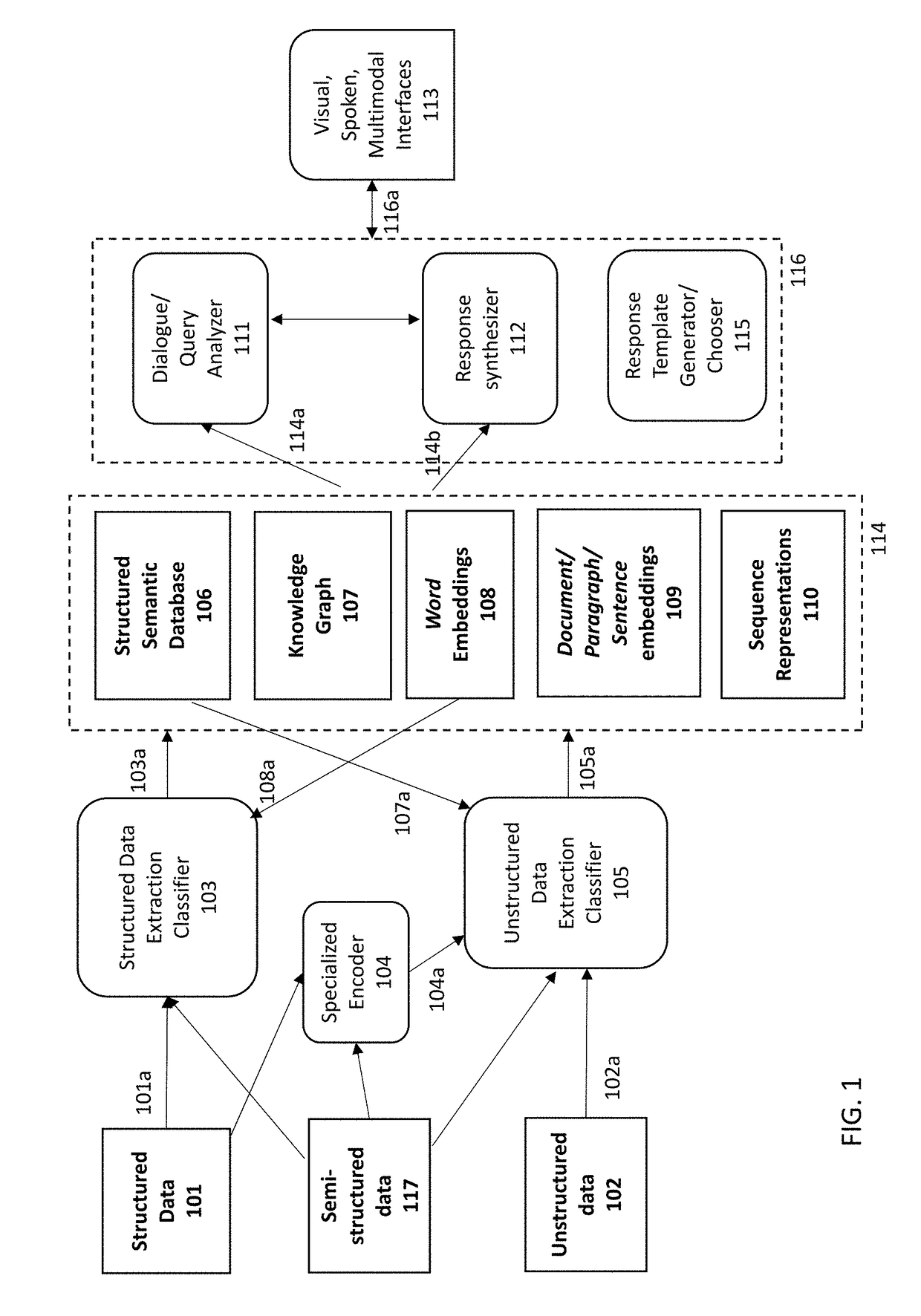
Systems and methods for finding information resources
InactiveUS20090119572A1Easy to combineIncrease usageDigital data information retrievalNatural language data processingInformation resourceHand held
A semantic service system may includes a tagging facility for collecting references to resources thereby providing tagged resources; a semantic database for storing the collected references; a semantic associating facility for determining semantic relationships among the references and the resources thereby providing semantic objects; and a user interface for presenting context-based views of one or more of the semantic objects, the references, and the tagged resources. A handheld tagging device includes a computing facility with a camera for acquiring images of resources and a motion sensor for detecting a tagging gesture.
Owner:INNOMORE
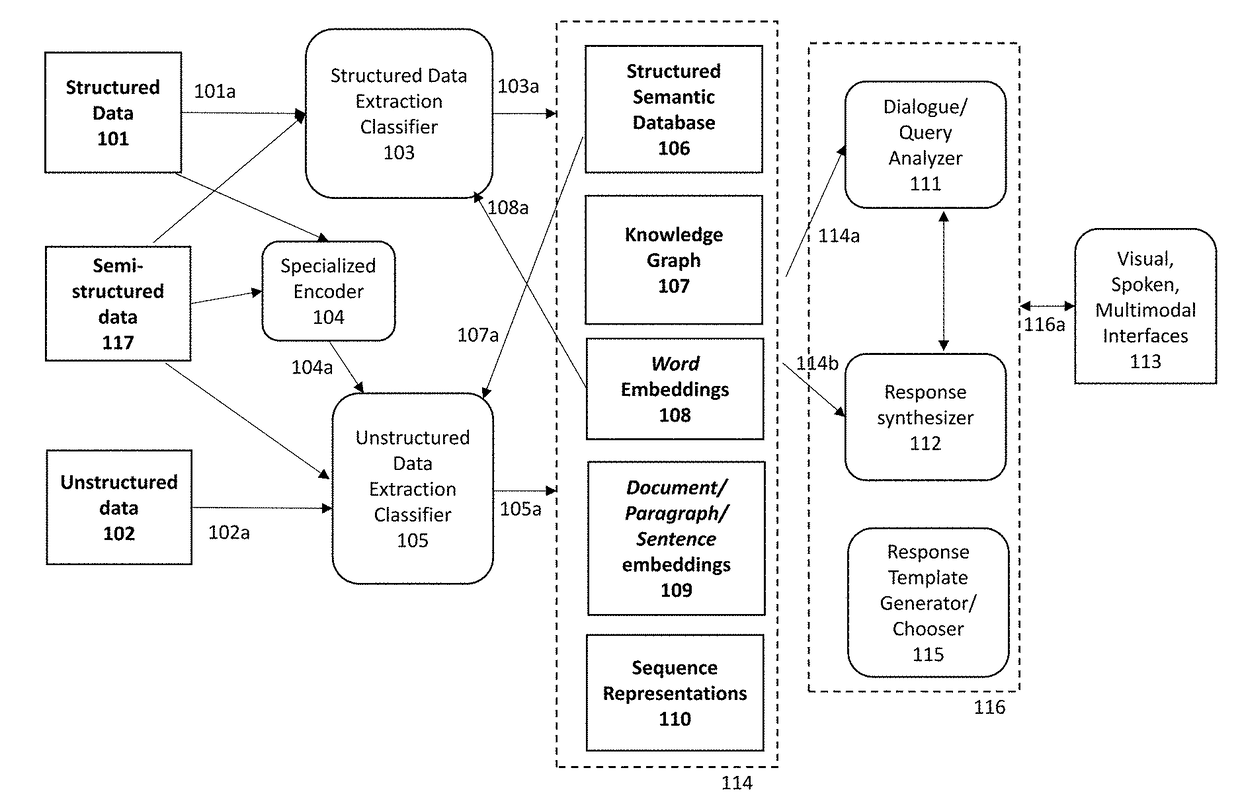
Systems, methods, and computer readable media for visualization of semantic information and inference of temporal signals indicating salient associations between life science entities
ActiveUS20180082197A1Superior visualization systemSemantic analysisBiological modelsData scienceSemantic information
Disclosed systems, methods, and computer readable media can detect an association between semantic entities and generate semantic information between entities. For example, semantic entities and associated semantic collections present in knowledge bases can be identified. A time period can be determined and divided into time slices. For each time slice, word embeddings for the identified semantic entities can be generated; a first semantic association strength between a first semantic entity input and a second semantic entity input can be determined; and a second semantic association strength between the first semantic entity input and semantic entities associated with a semantic collection that is associated with the second semantic entity can be determined. An output can be provided based on the first and second semantic association strengths.
Owner:NFERENCE INC
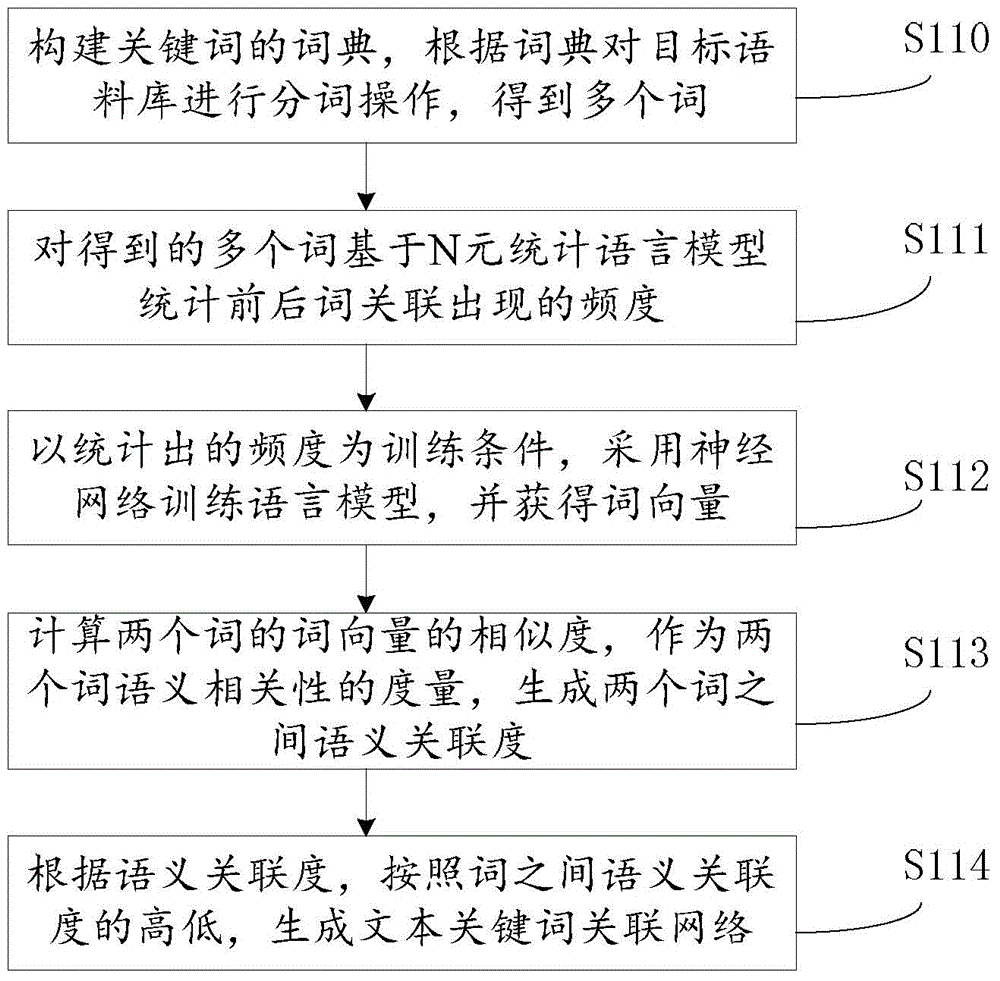
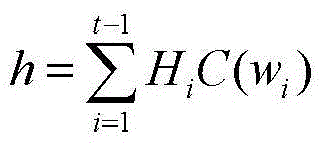
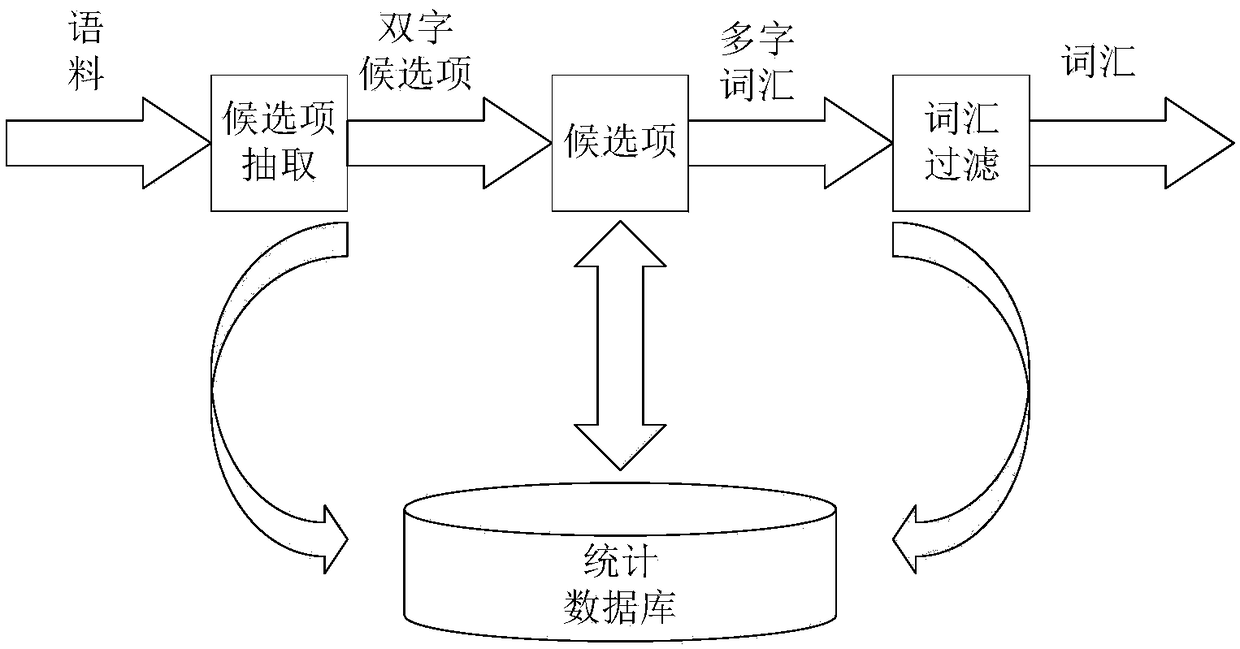
Method for constructing correlation networks of keywords of natural language texts
InactiveCN104391963AHigh precisionSpecial data processing applicationsText database clustering/classificationAlgorithmHuman language
The invention provides a method for constructing correlation networks of keywords of natural language texts. The method includes steps of constructing dictionaries of the keywords and segmenting words of target corpuses according to the dictionaries to obtain a plurality of words; performing statistics on front and rear word correlation frequencies of the multiple obtained words on the basis of N-element statistic language models; training the language models by the aid of neural networks under training conditions which are the frequencies obtained by means of statistics, and acquiring word vectors; computing the similarity degrees of the word vectors of each two corresponding words and generating semantic correlation between each two corresponding words; generating the correlation networks of the keywords of the texts according to the level of the semantic correlation between the corresponding words. The similarity degrees of the word vectors of each two corresponding words are used as measurement for the semantic correlation of the two words. The method has the advantage that the accuracy of the correlation networks of the texts in relevant items can be effectively improved by the aid of the method.
Owner:BEIJING ZHONGKE CHUANGYI TECH CO LTD
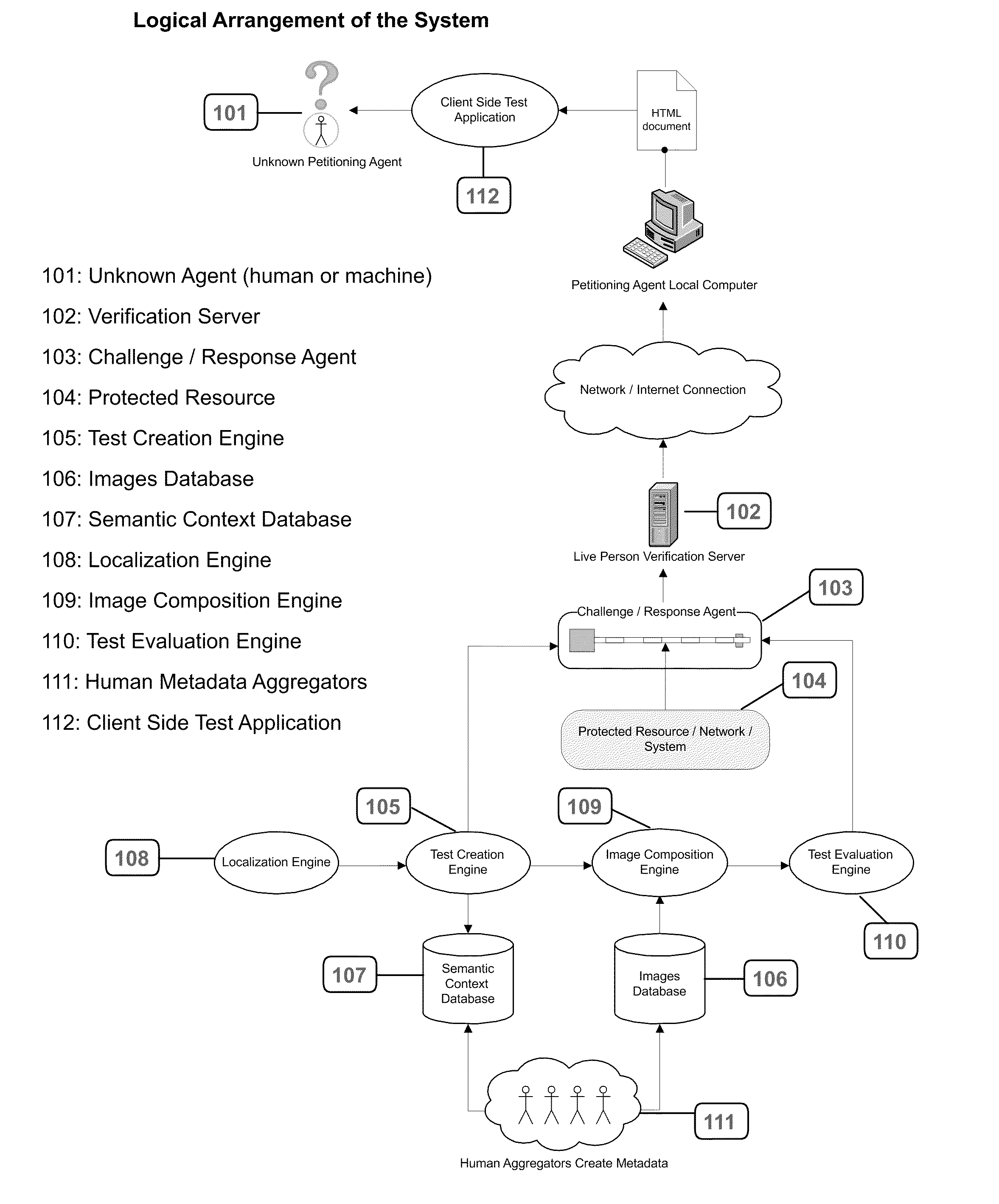
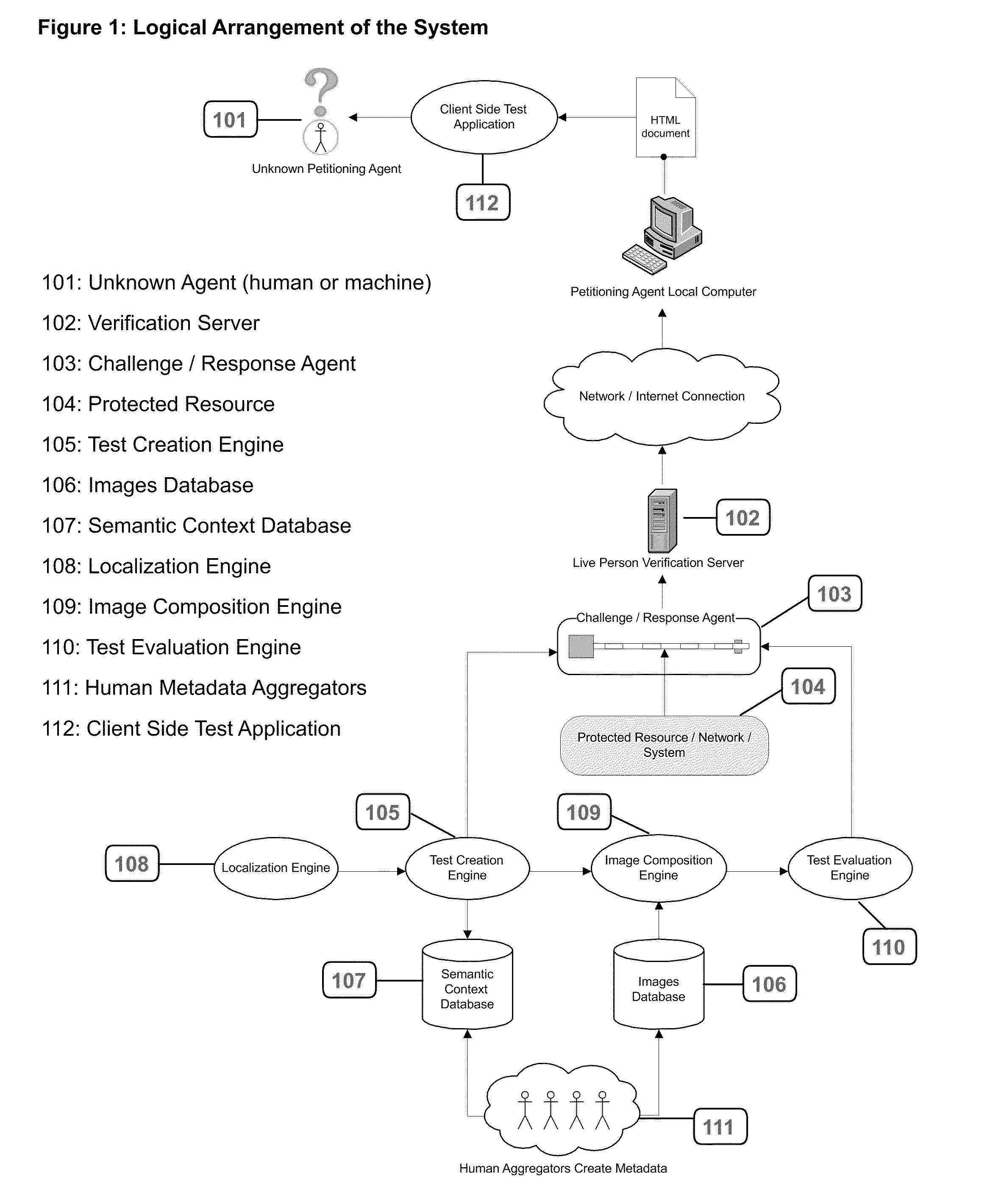
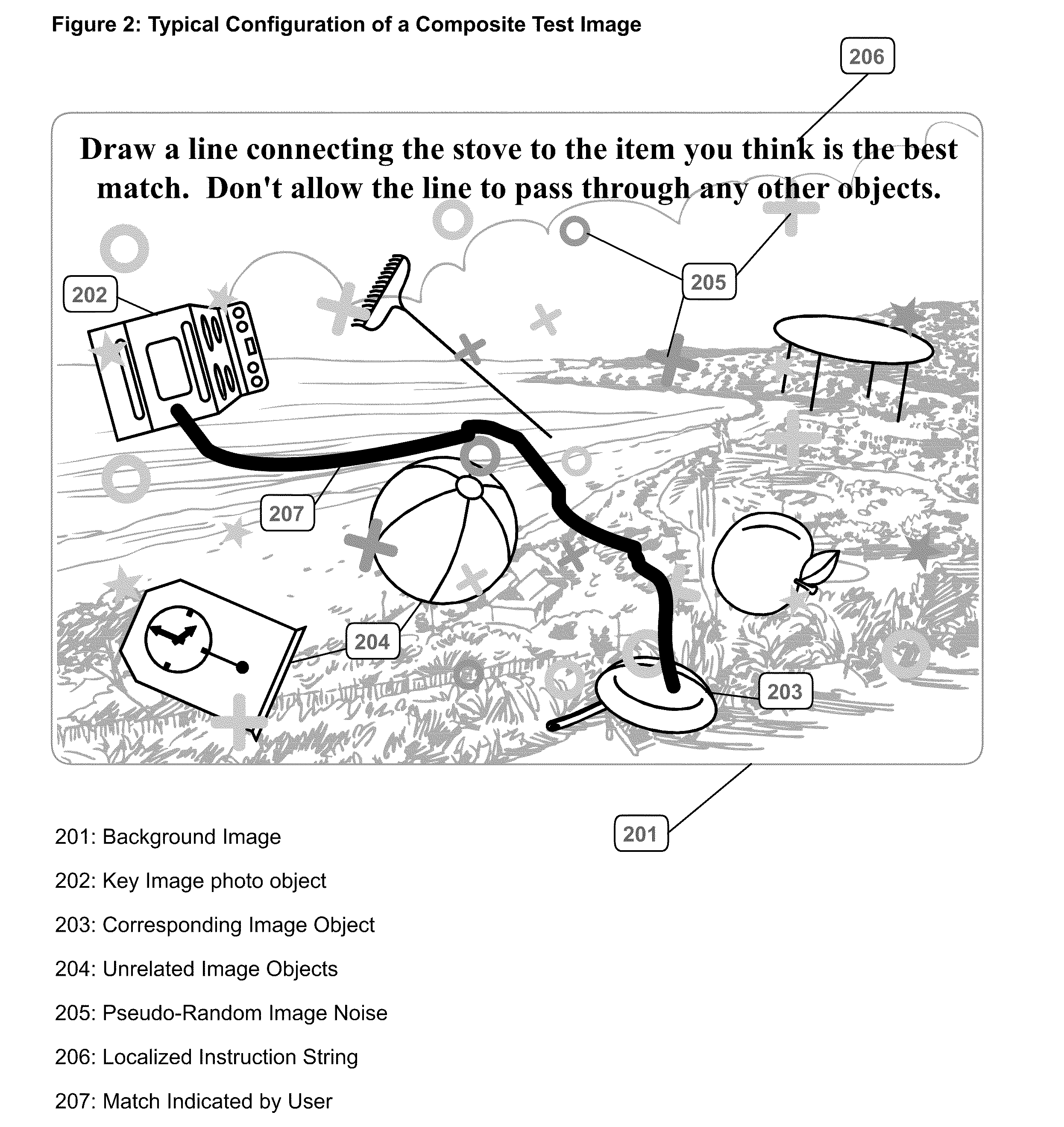
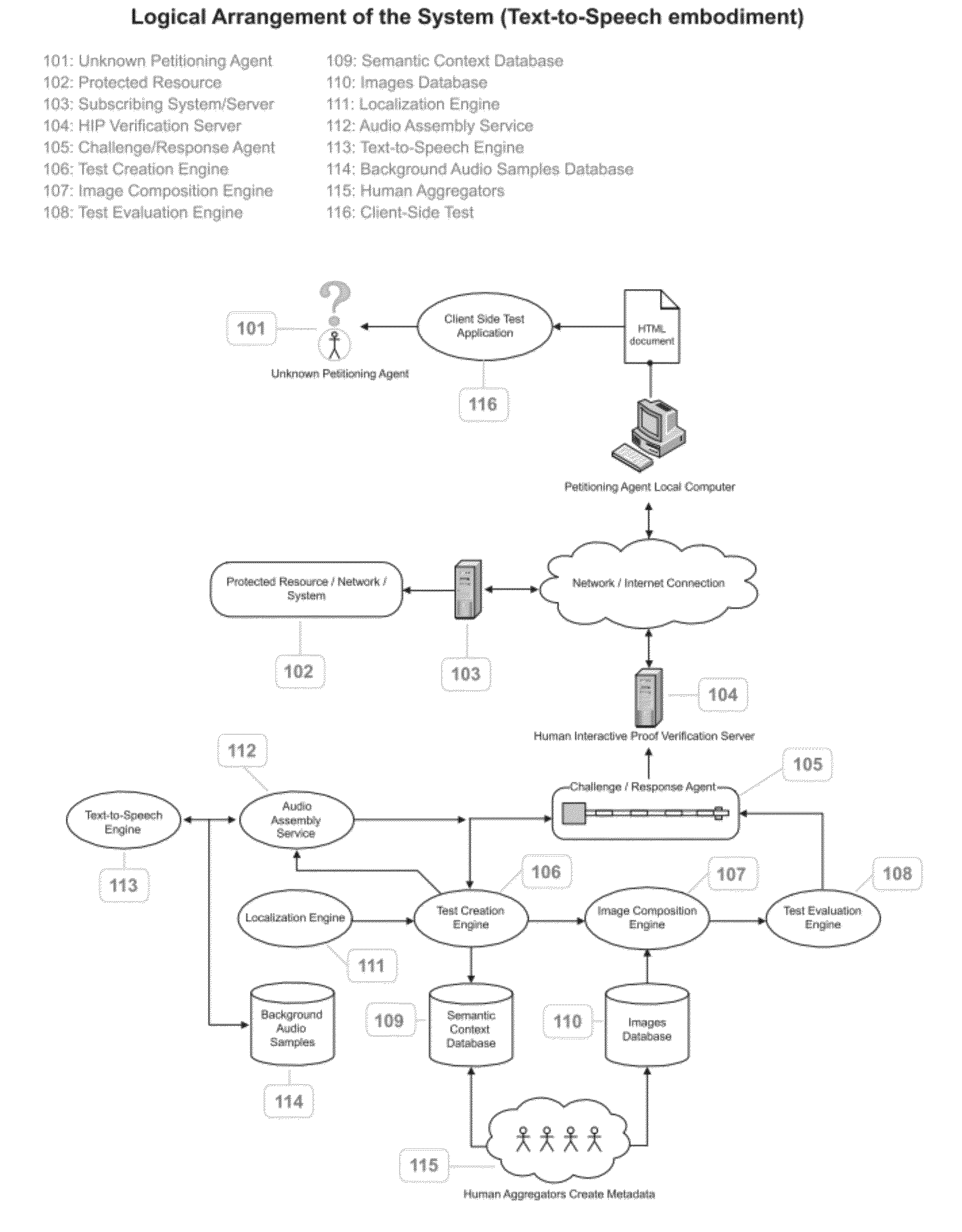
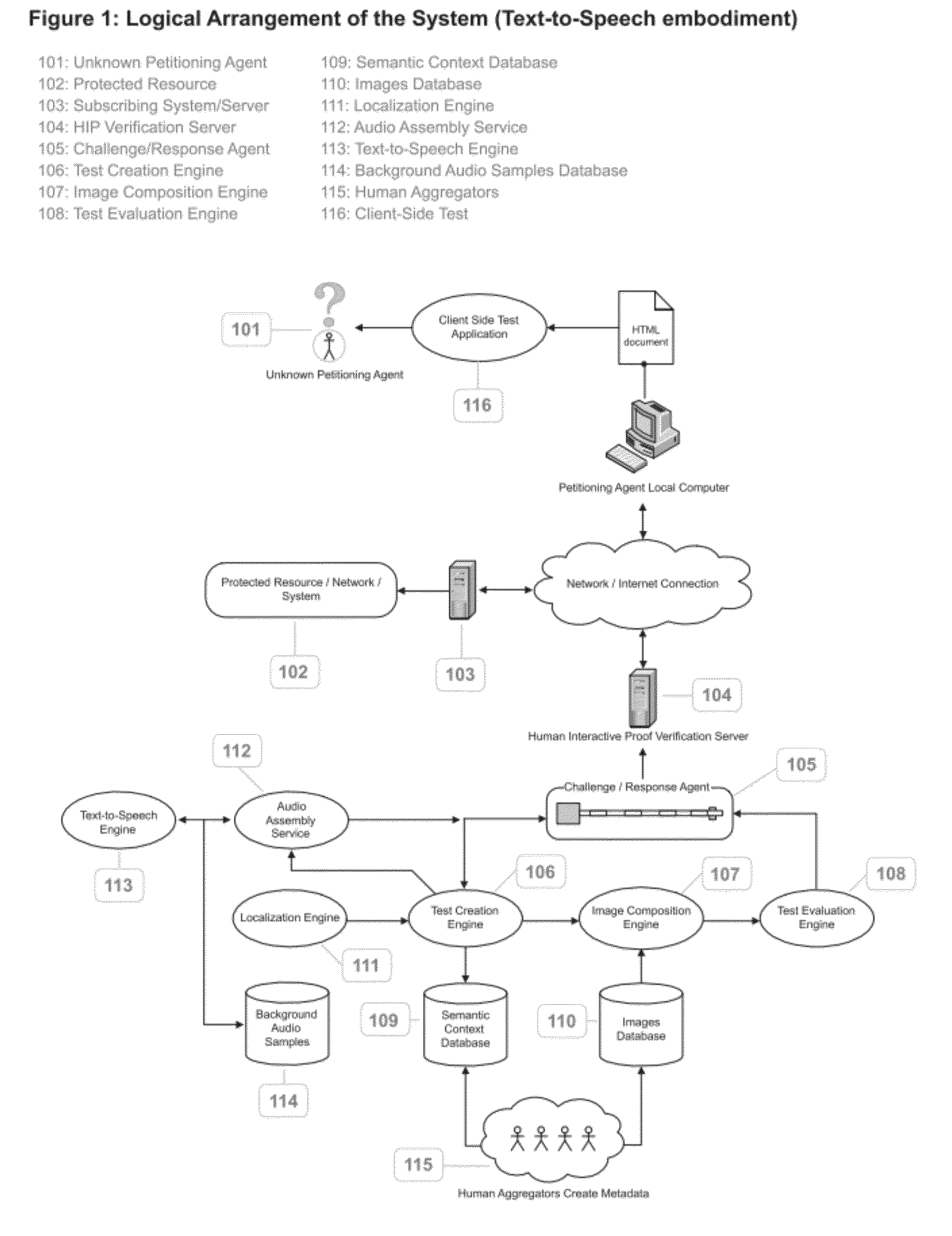
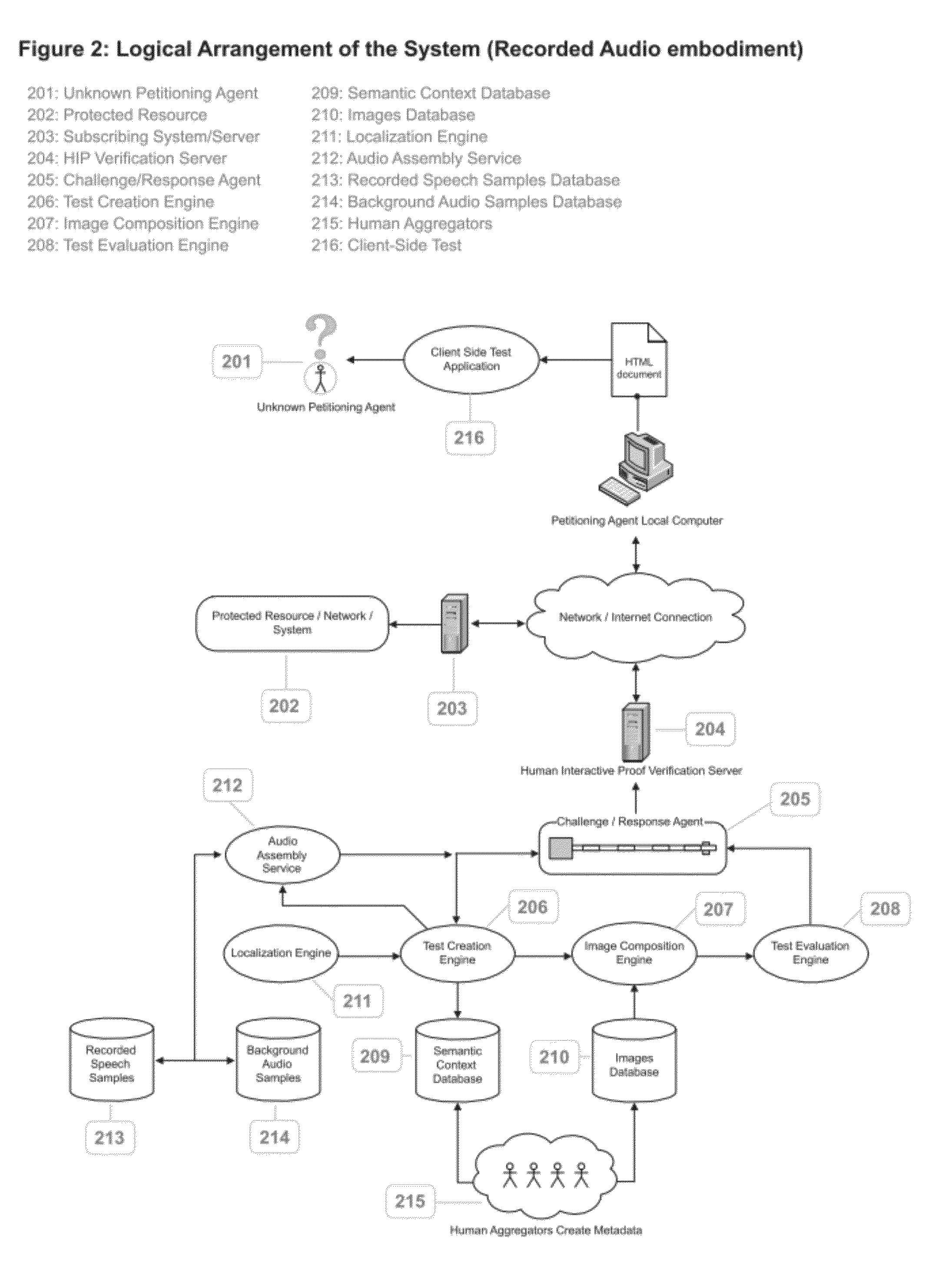
System and Method for Restricting Access to a Computer System to Live Persons by Means of Semantic Association of Images
InactiveUS20110191820A1Preventing executionLimited accessDigital data information retrievalDigital data processing detailsHuman interactionSubject matter
A system and method for restricting access to a computer system, resource, or network to live persons, and for preventing the execution of automated scripts via an interface intended for human interaction.When queried for access to a protected resource, computer system, or network, the system will respond with a challenge requiring unknown petitioners to solve a visual puzzle before proceeding, said puzzle consisting of a collection of apparently random objects, and exploiting the natural human impulse to form semantic or symbolic associations between images of objects.The puzzle objects are assembled into a composite test image which is designed to frustrate machine interpretation but is still easily interpreted by a human being.The subject of the test must either recognize a semantic or symbolic association between two or more objects, or isolate an object that does not belong with the others, indicating their selection with the pointing device on their local computer.If the subject of the test succeeds in passing the test, they are granted access to the requested resource, computer system, or network. If not, they are invited to attempt the test again, up to a configurable maximum retests, after which time their request is simply ignored.
Owner:IVEY CHRISTOPHER LIAM
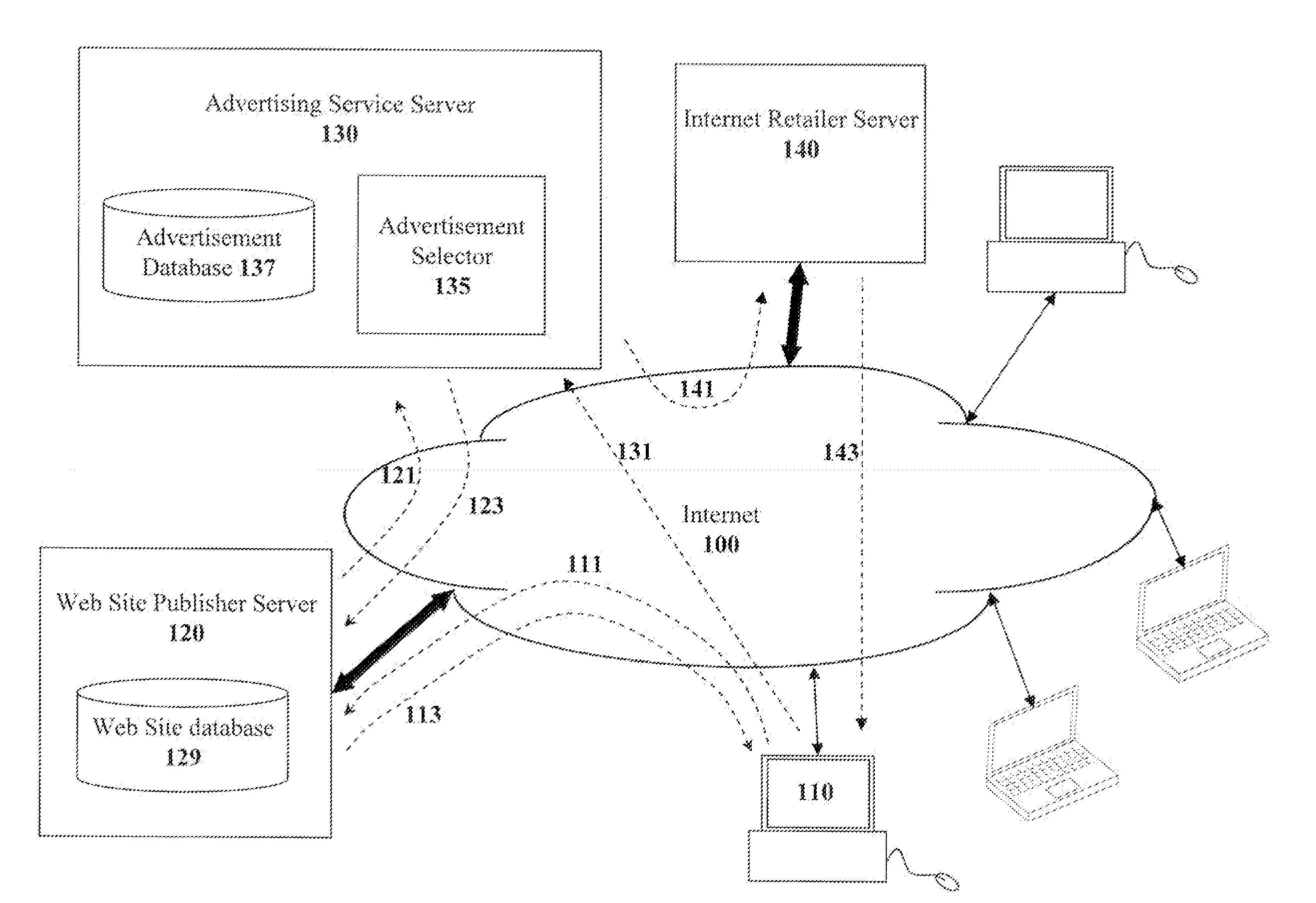
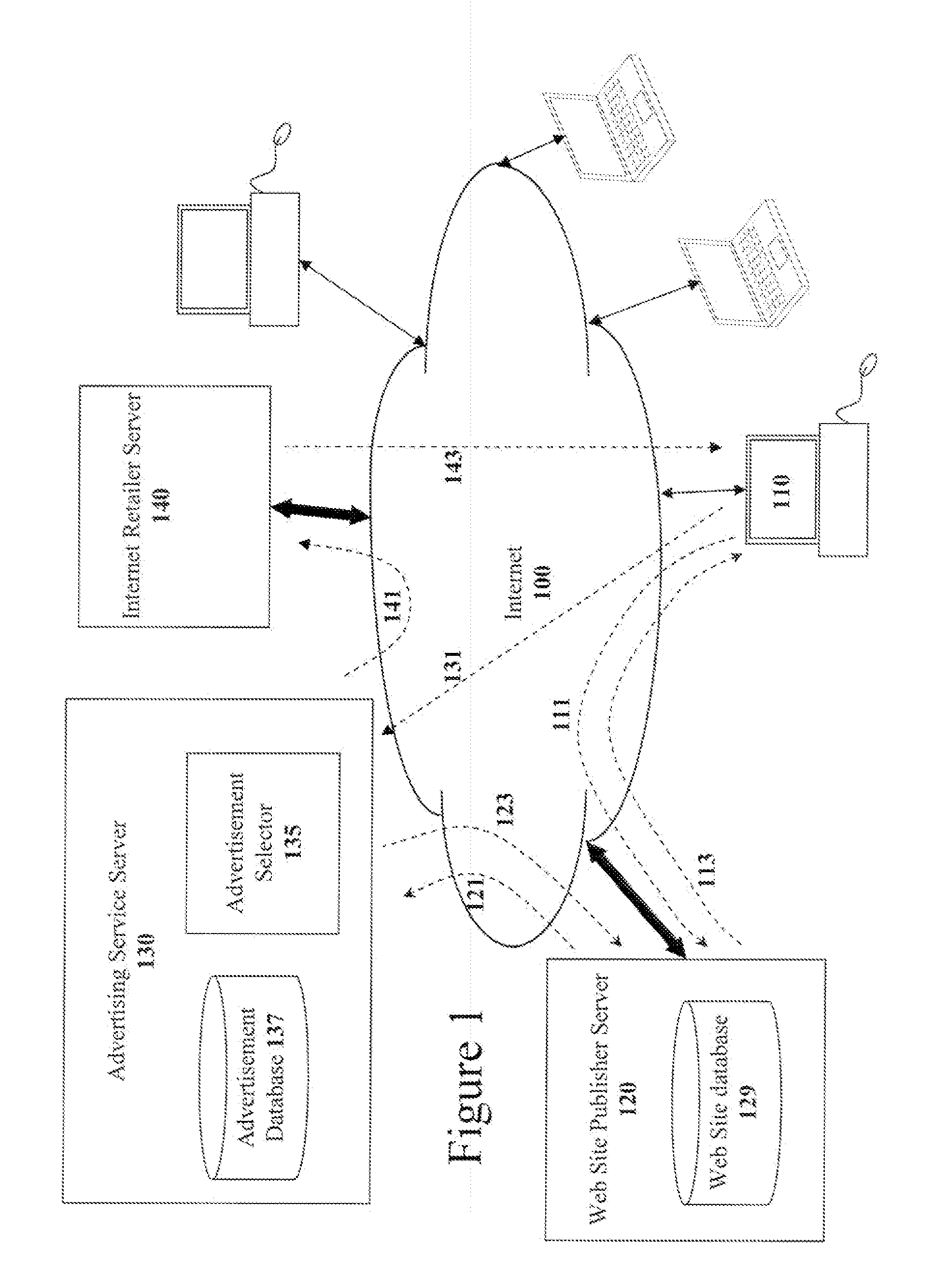
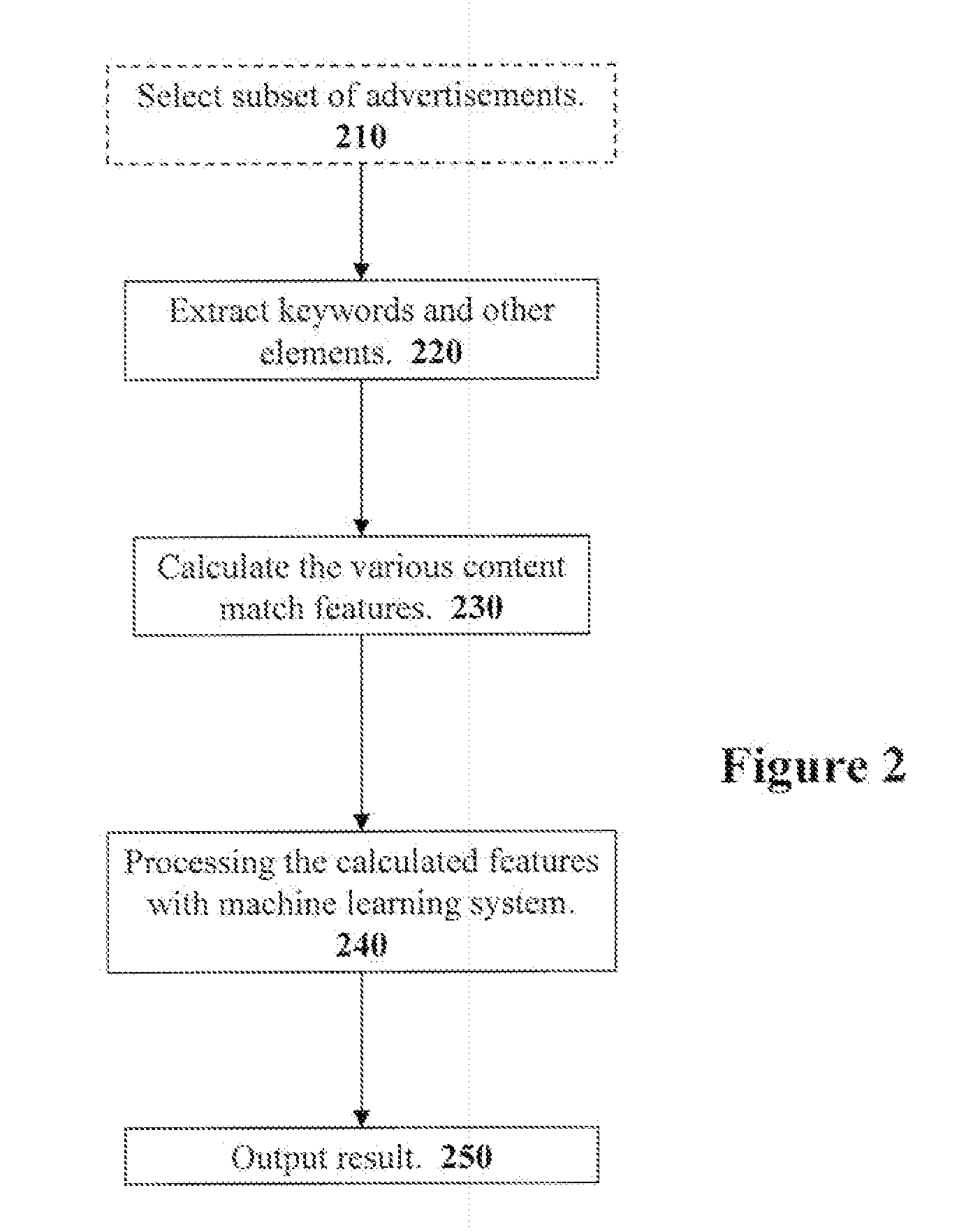
Method For Matching Electronic Advertisements To Surrounding Context Based On Their Advertisement Content
A system for selecting electronic advertisements from an advertisement pool to match the surrounding content is disclosed. To select advertisements, the system takes an approach to content match that focuses on capturing subtler linguistic associations between the surrounding content and the content of the advertisement. The system of the present invention implements this goal by means of simple and efficient semantic association measures dealing with lexical collocations such as conventional multi-word expressions like “big brother” or “strong tea”. The semantic association measures are used as features for training a machine learning model. In one embodiment, a ranking SVM (Support Vector Machines) trained to identify advertisements relevant to a particular context. The trained machine learning model can then be used to rank advertisements for a particular context by supplying the machine learning model with the semantic association measures for the advertisements and the surrounding context.
Owner:R2 SOLUTIONS
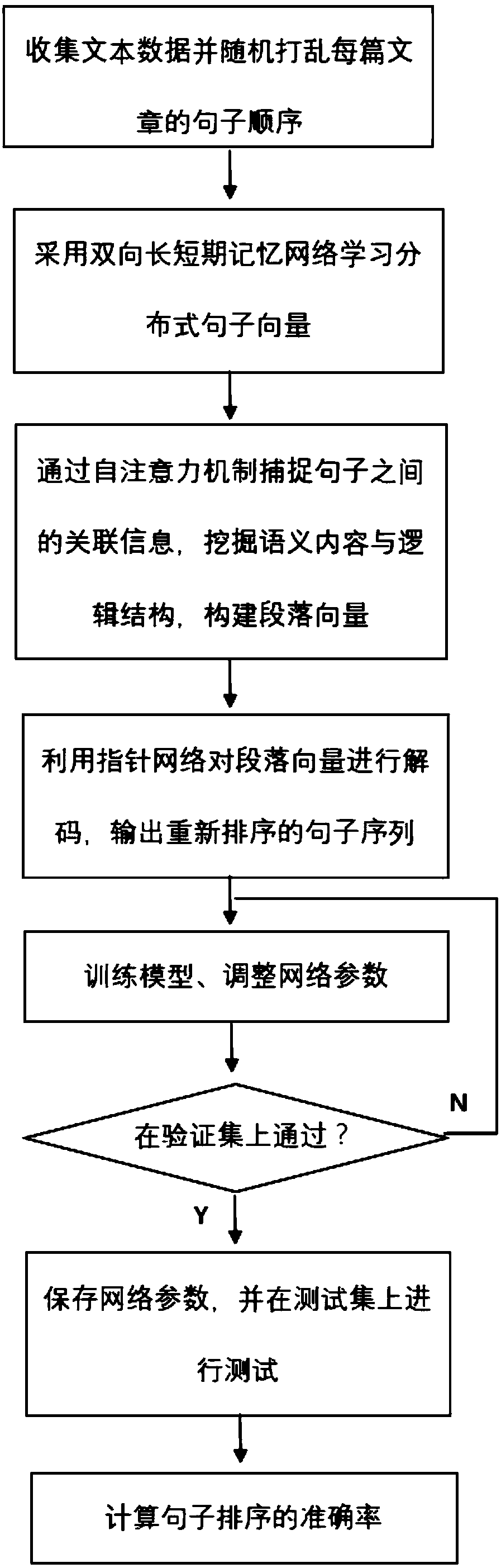
A sentence sorting method based on depth learning self-attention mechanism
ActiveCN109241536AAvoid interferenceAvoid confusionNatural language data processingNeural architecturesShort-term memorySelf attention
The invention discloses a sentence sorting method based on depth learning self-attention mechanism. After a piece of text is input, firstly, each sentence in the text is translated into a distributedvector by using a long-short-term memory network to obtain syntactic information of the sentence. Secondly, the self-attention mechanism is used to learn the semantic association between sentences, and the potential logical structure is explored to preserve important information to form high-level paragraph vectors. The paragraph vector is then input into the pointer network to produce a new sentence order. The method of the invention is characterized in that the method is not influenced by the input sentence order, avoids the problem that the long-term and short-term memory network adds the wrong timing information in the process of generating the paragraph vector, and can effectively analyze the relationship between all sentences. Compared with the existing sentence sorting technology, the method provided by the invention has great improvement in accuracy, and has good practical value.
Owner:ZHEJIANG UNIV
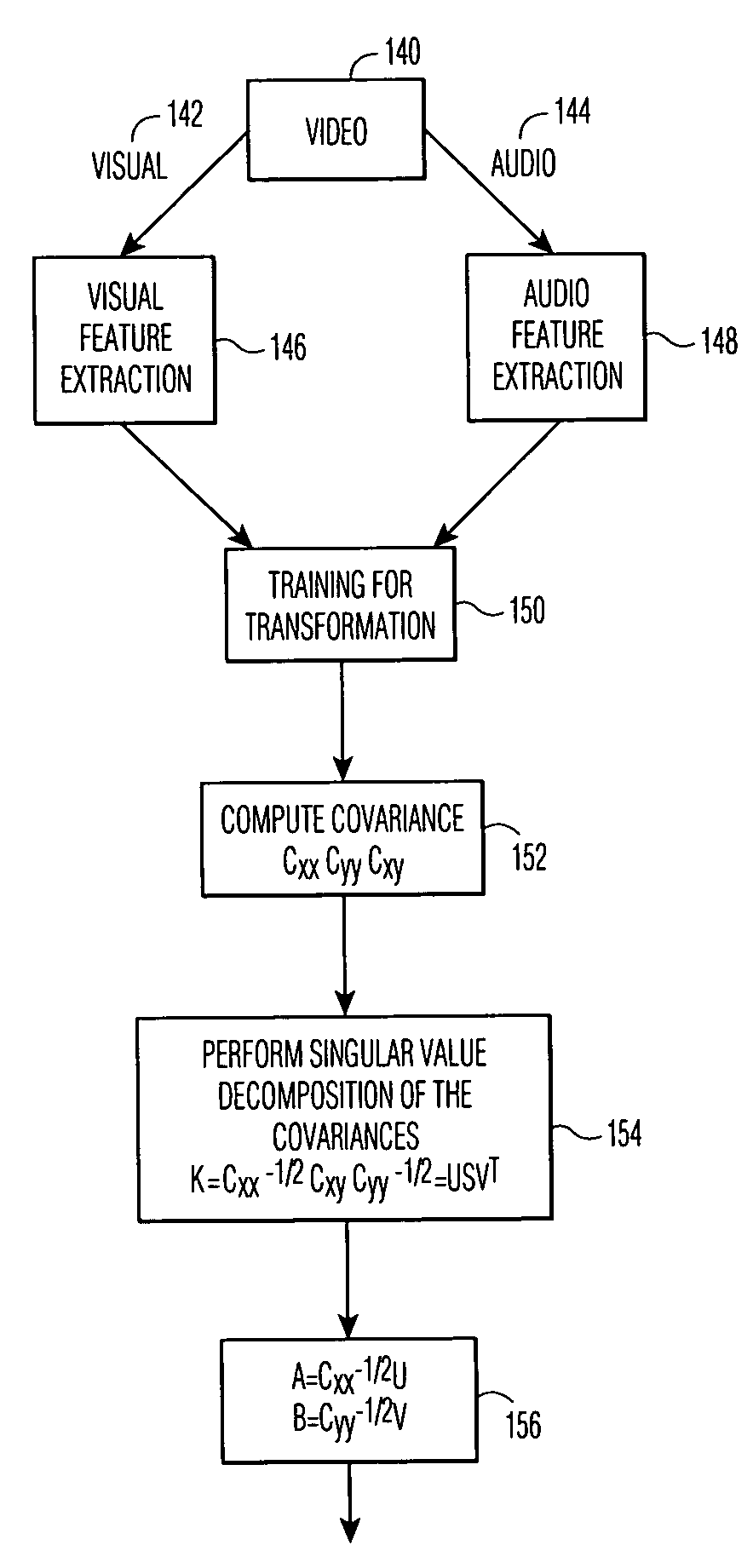
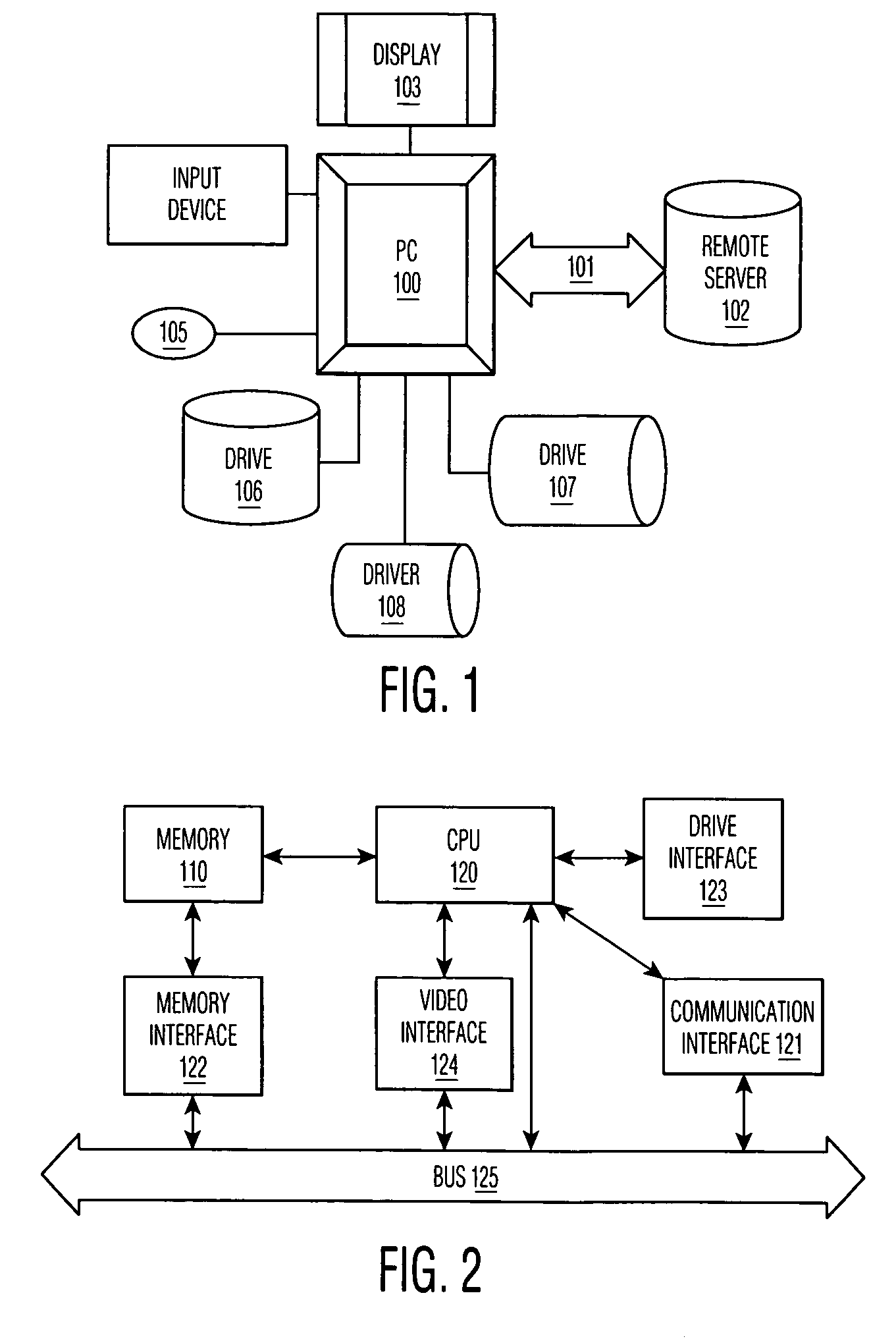
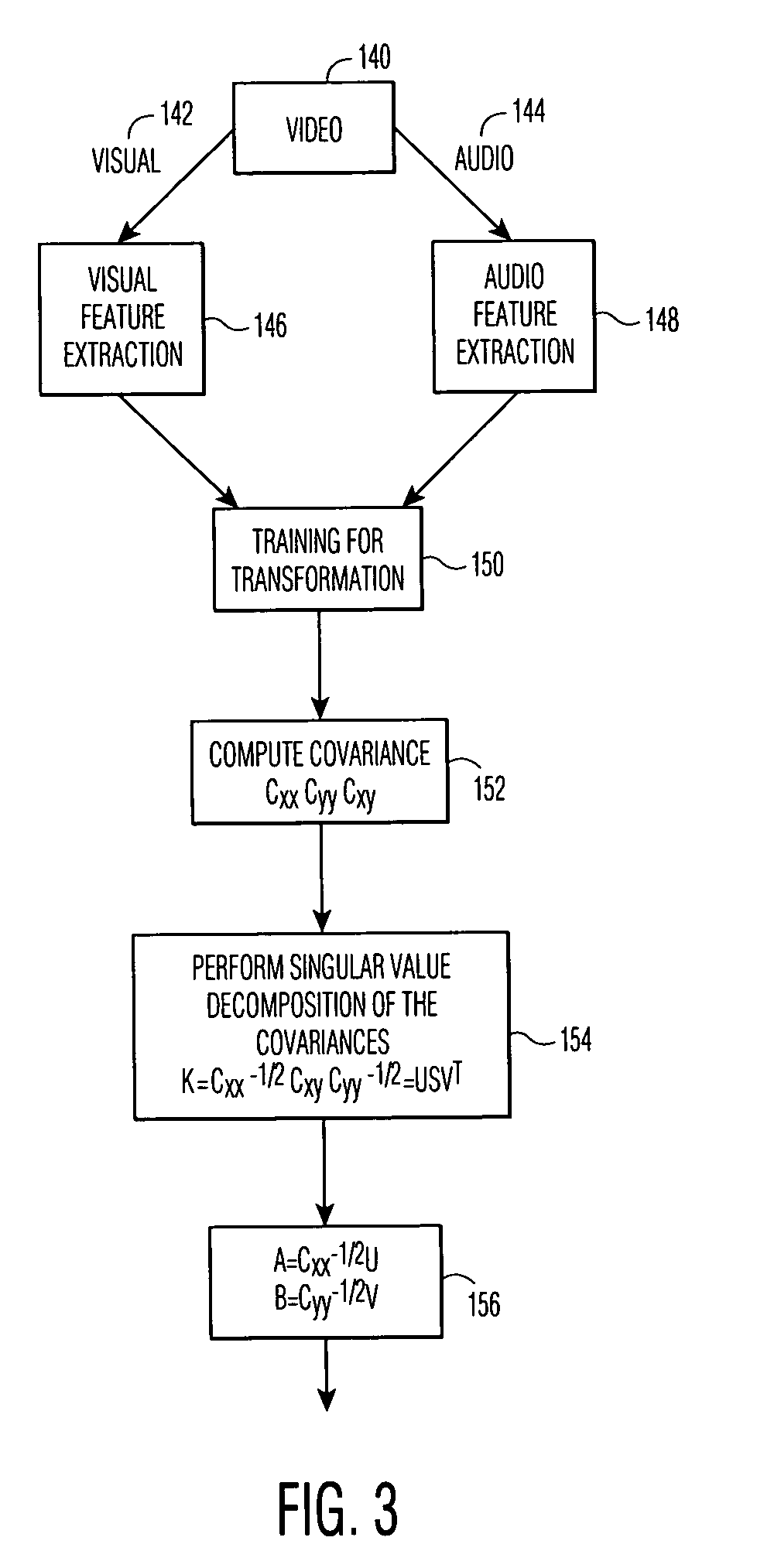
Content retrieval based on semantic association
InactiveUS7120626B2Minimize bandwidthReduce equipment costsData processing applicationsSpeech analysisContent retrievalData mining
A method and system which enable a user to query a multimedia archive in one media modality and automatically retrieve correlating data in another media modality without the need for manually associating the data items through a data structure. The correlation method finds the maximum correlation between the data items without being affected by the distribution of the data in the respective subspace of each modality. Once the direction of correlation is disclosed, extracted features can be transferred from one subspace to another.
Owner:KONINKLIJKE PHILIPS ELECTRONICS NV
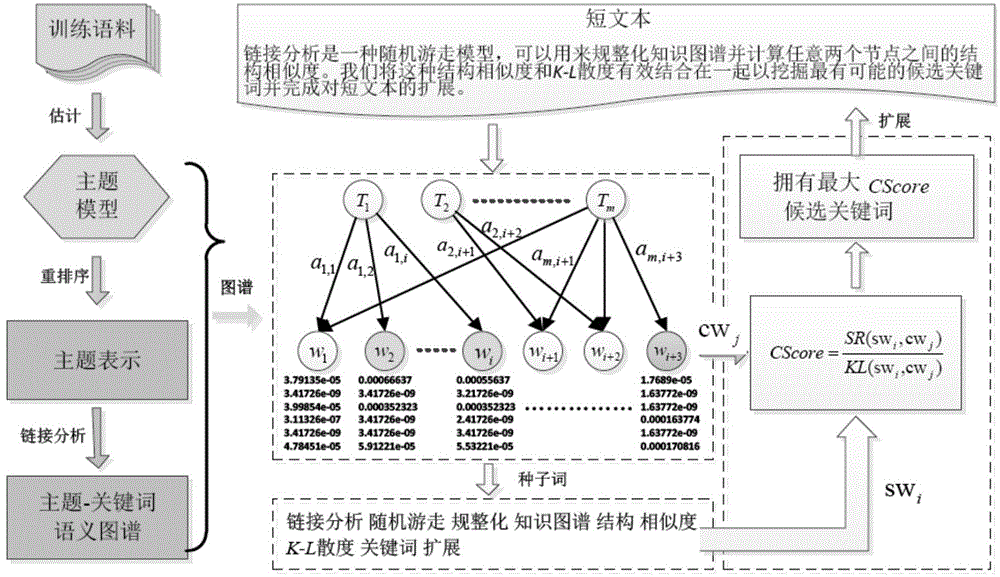
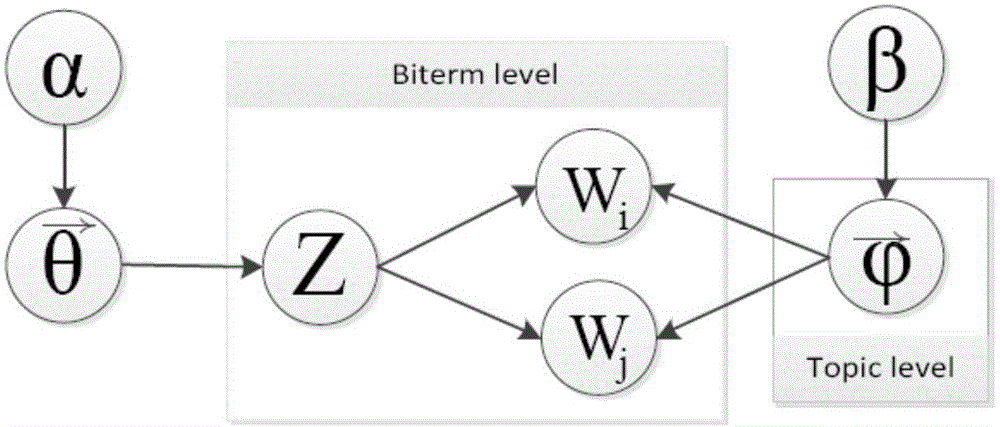
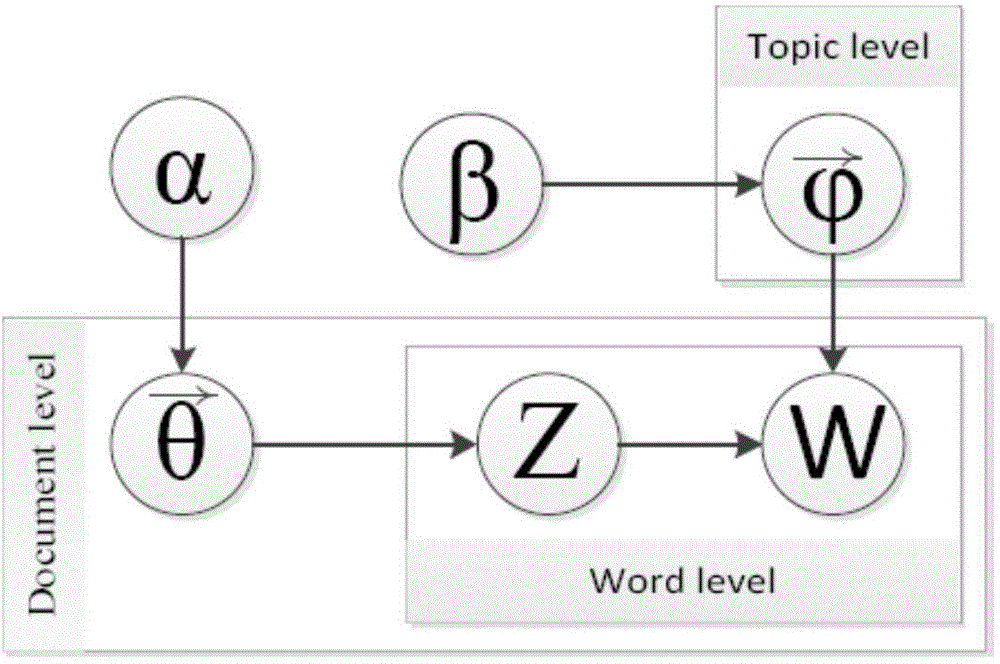
Short text characteristic expanding method based on semantic atlas
ActiveCN104391942AImprove classification performanceSolve the sparsity problemSemantic analysisSpecial data processing applicationsGraph spectraData set
The invention discloses a short text characteristic expanding method based on a semantic atlas. The method includes the steps: performing subject modeling by the aid of a training data set of a short text, and extracting subject term distribution; reordering the subject term distribution; building a candidate keyword dictionary and a subject-keyword semantic atlas; calculating comprehensive similarity degree evaluation of candidate keywords and seed keywords based on a link analysis method, and selecting the most similar candidate keywords to finish expanding the short text. Compared with a short text characteristic representation method based on a language model, the method is simple to operate and high in execution efficiency, and semantic correlation information between the keywords is sufficiently used. Compared with a traditional short text characteristic representation method based on a word bag model, the problems of data sparseness and semantic sensitivity are effectively relieved, and the method is independent of external large-scale auxiliary training corpus or a search engine.
Owner:INST OF AUTOMATION CHINESE ACAD OF SCI
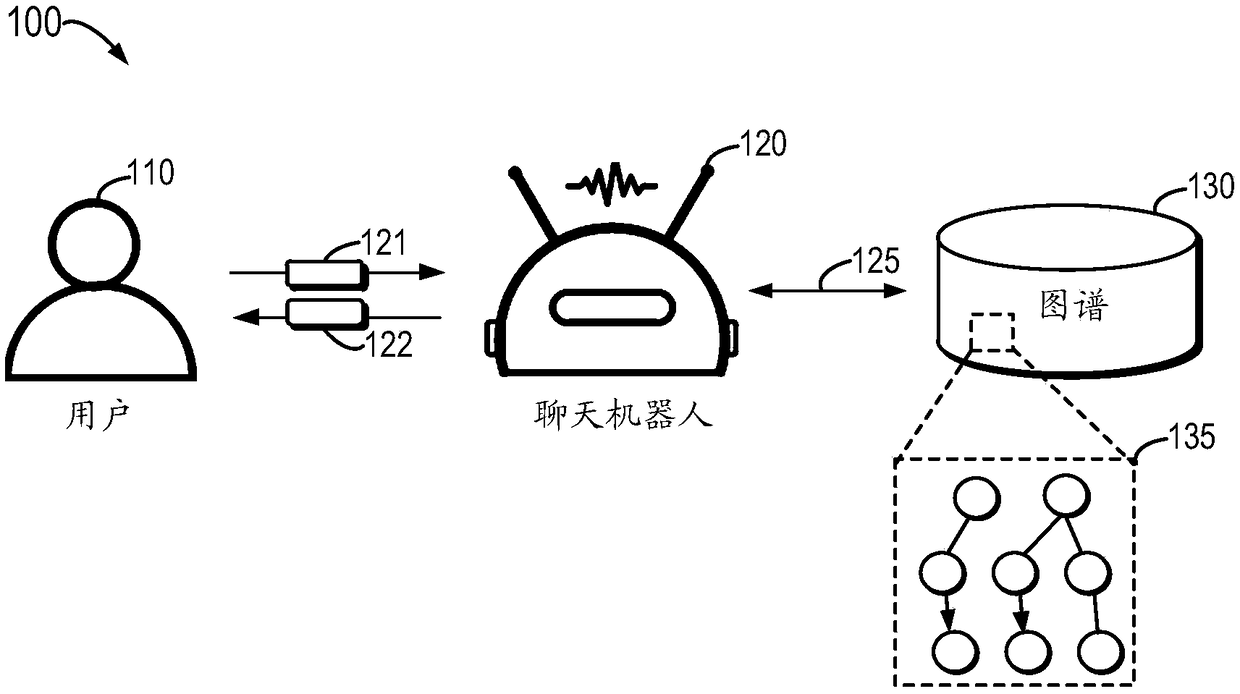
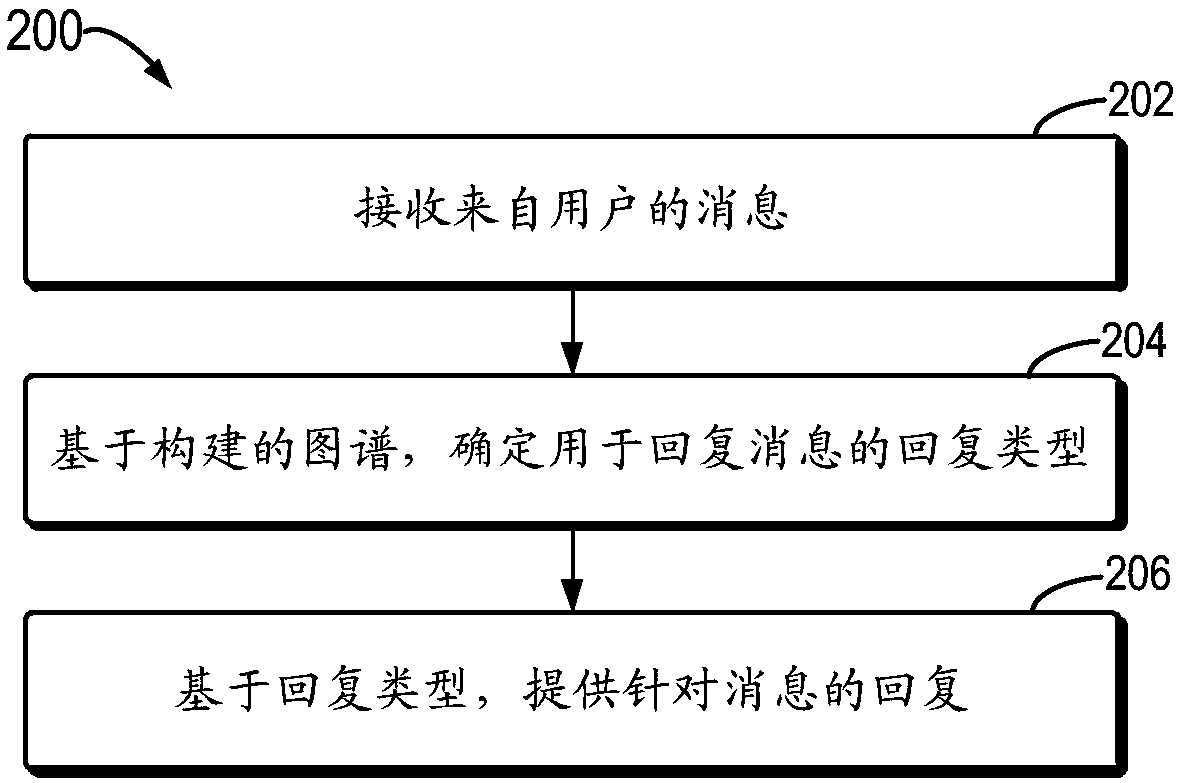
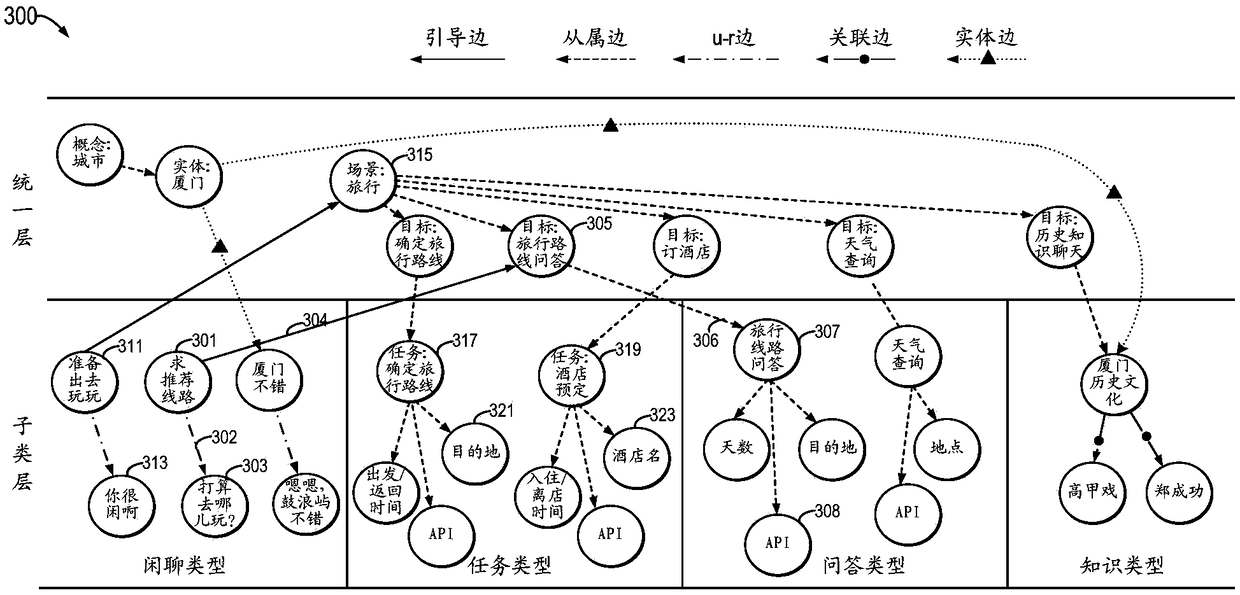
Method and device for cross-type conversation, apparatus, and computer-readable storage medium
According to an example embodiment of the present disclosure, there is provided a method and a device for cross-type conversation, an apparatus, and a computer-readable storage medium. The method includes receiving a message from a user and determining a reply type for the reply message based on the constructed map, wherein nodes in the map represent semantic content and edges in the map representsemantic associations between nodes. In addition, the method includes providing a reply to the message based on the reply type. According to an embodiment of the present disclosure, by using a prioriknowledge in a map to assist in determining a reply type, it is possible to reduce the dependence of a chat robot on training data, so that the chat robot can actively guide a cross-type conversationand maintain the logicality of the semantic content of the conversation.
Owner:BEIJING BAIDU NETCOM SCI & TECH CO LTD
System and Method for Delivering a Human Interactive Proof to the Visually Impaired by Means of Semantic Association of Objects
InactiveUS20120232907A1Reinforcing awareness of brandPreventing executionDigital data authenticationSpeech synthesisHuman interactionComputerized system
A system and method for delivering a Human Interactive Proof, or reverse Turing test to the visually impaired; said test comprising a method for restricting access to a computer system, resource, or network to live persons, and for preventing the execution of automated scripts via an interface intended for human interaction.When queried for access to a protected resource, the system will respond with a challenge requiring unknown petitioners to solve an auditory puzzle before proceeding, said puzzle consisting of an audio waveform representative of the names or descriptions of a collection of apparently random objects.The subject of the test must either recognize a semantic or symbolic association between two or more objects, or isolate an object that does not belong with the others, indicating their selection by typing the name of the object with their keyboard.
Owner:IVEY CHRISTOPHER LIAM
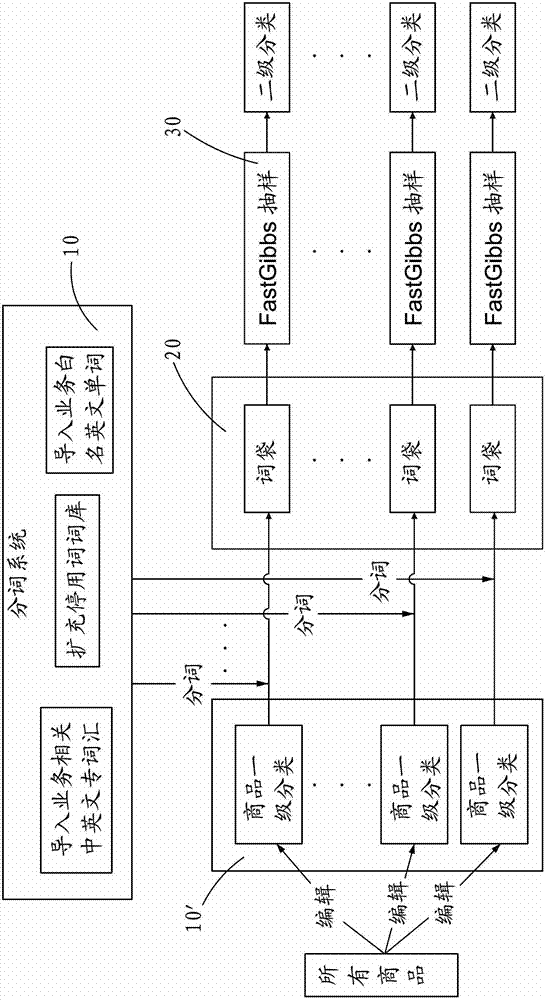
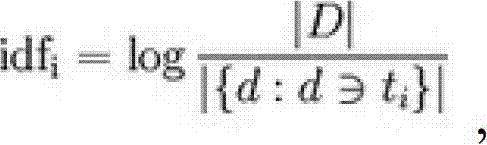
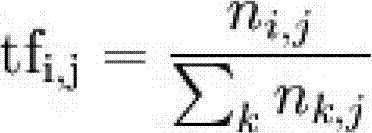
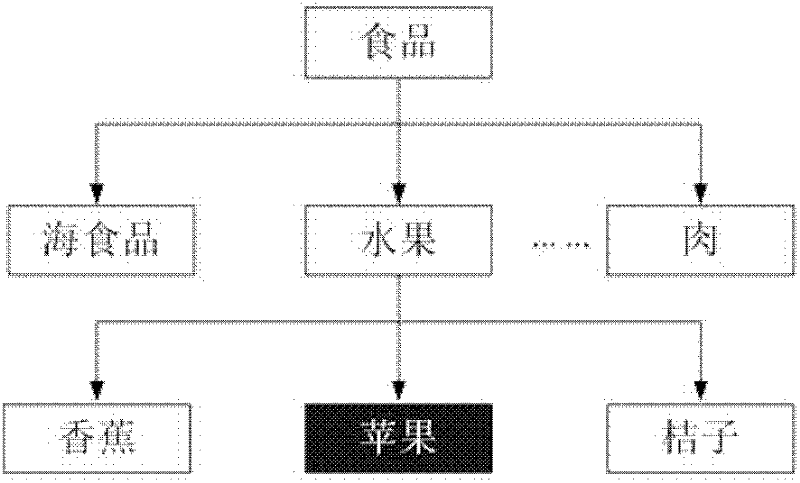
Text-subject-model-based data processing method for commodity classification
ActiveCN102929937AReduce the influence of subjective factorsAccurate classificationSpecial data processing applicationsAlgorithmSemantics
The invention provides a text-subject-model-based data processing method for commodity classification. The method comprises the following steps of: importing Chinese and English vocabulary related to a service into a universal word library of a word segmentation system, and importing white name English words related to the service for brands and common commodity English; further expanding a stop word library of the word segmentation system; segmenting words for a description text part of a commodity, so that each commodity can have a bag of words which is not related to sequence; counting word segmentation results to acquire uncommon vocabulary with high frequency, and thus constructing a preferential word library; and appointing a general classification quantity, setting related parameters, executing quick Gibbs sampling, acquiring potential semantic association, comparing the latent semantic association with the preferential word library, the universal word library and the stop word library respectively, calculating comparison results to obtain the most possible classification of the commodity, and marking the classification by using the bags of words. In consideration of latent semantics, the influence of subjective factors of editorial staff is reduced, so that the commodity classification is accurate.
Owner:BAIDU COM TIMES TECH (BEIJING) CO LTD
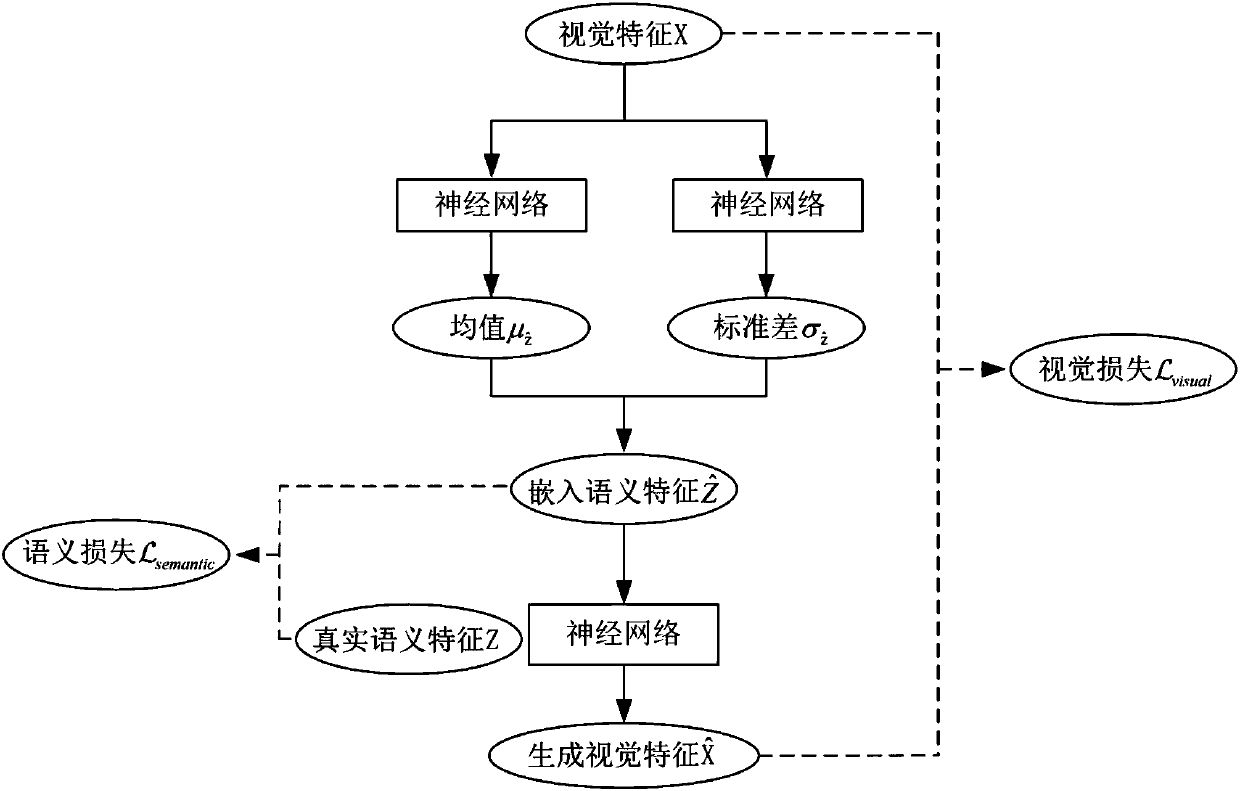
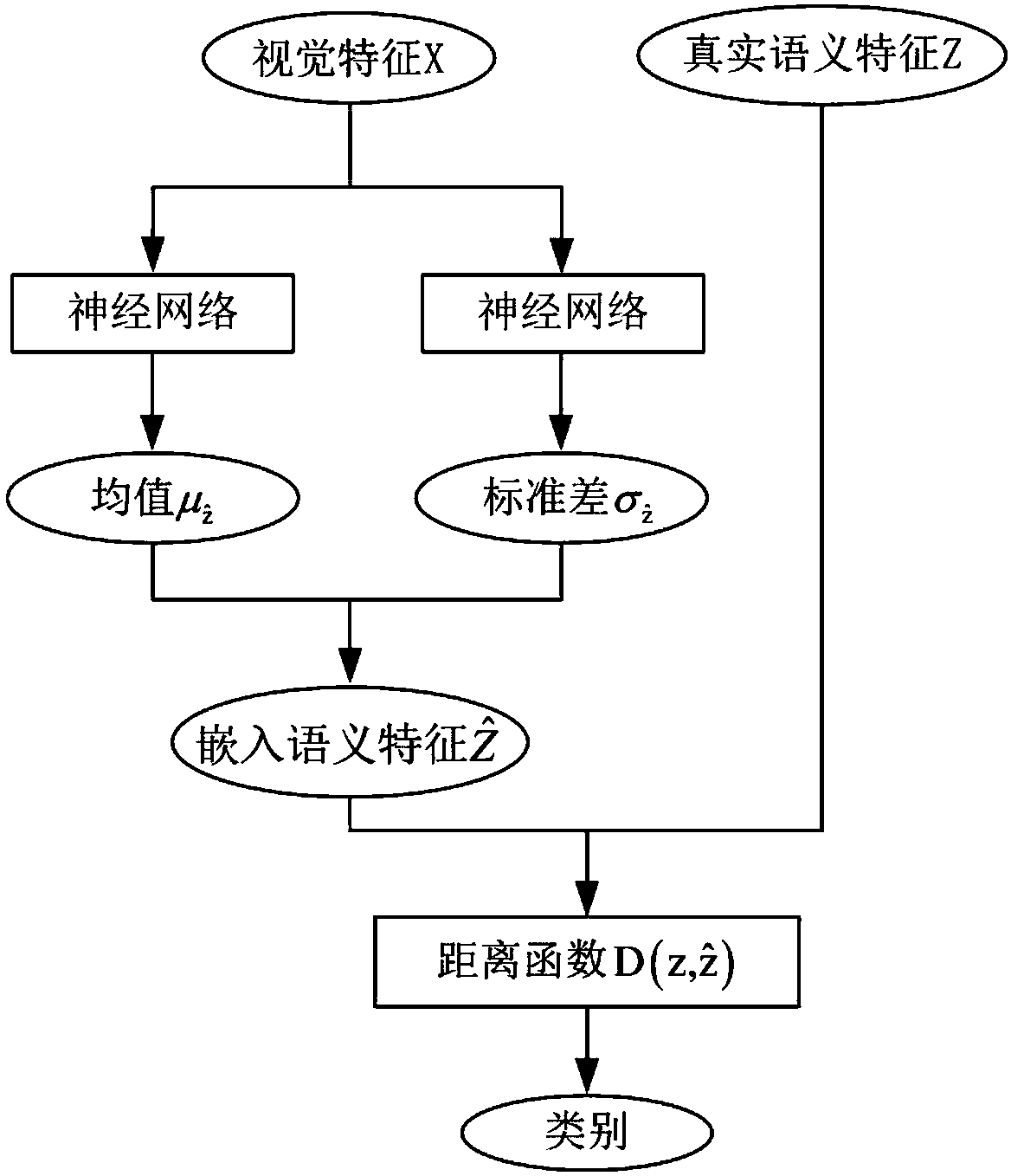
Variational automatic encoder-based zero-sample image classification method
InactiveCN107679556AEffective semantic associationFully consider the probability distribution characteristicsCharacter and pattern recognitionNeural architecturesClassification methodsSample image
The present invention relates to a zero-sample classification technology in the computer vision field, in particular, a variational automatic encoder-based zero-sample image classification method. Asto the zero-sample image classification method, the distribution of the mappings of semantic features and visual features of categories in a semantic space is fitted, and more efficient semantic associations between the visual features and category semantics are built. According to the variational automatic encoder-based zero-sample image classification method, a variational automatic encoder is adopted to generate embedded semantic features on the basis of the visual features; it is regarded that the variational automatic encoder has a latent variable Z<^>; the latent variable Z<^> is adoptedas an embedded semantic feature; as for a zero-sample image classification task and the visual feature xj of a category-unknown sample, the encoding network of the variational automatic encoder whichis trained on visual categories is utilized to calculate a latent variable Z<^>j which is generated through encoding; the latent variable Z<^>j is adopted as an embedded semantic feature, cosine distances between the latent variable Z<^>j and the semantic feature of each invisible category are calculated, wherein the semantic feature of each invisible category is represented by a symbol describedin the descriptions of the invention; and a category of which the semantic feature is separated from the latent variable Z<^>j by the smallest distance is regarded as the category of the vision sample. The method of the present invention is mainly applied to video classification conditions.
Owner:TIANJIN UNIV
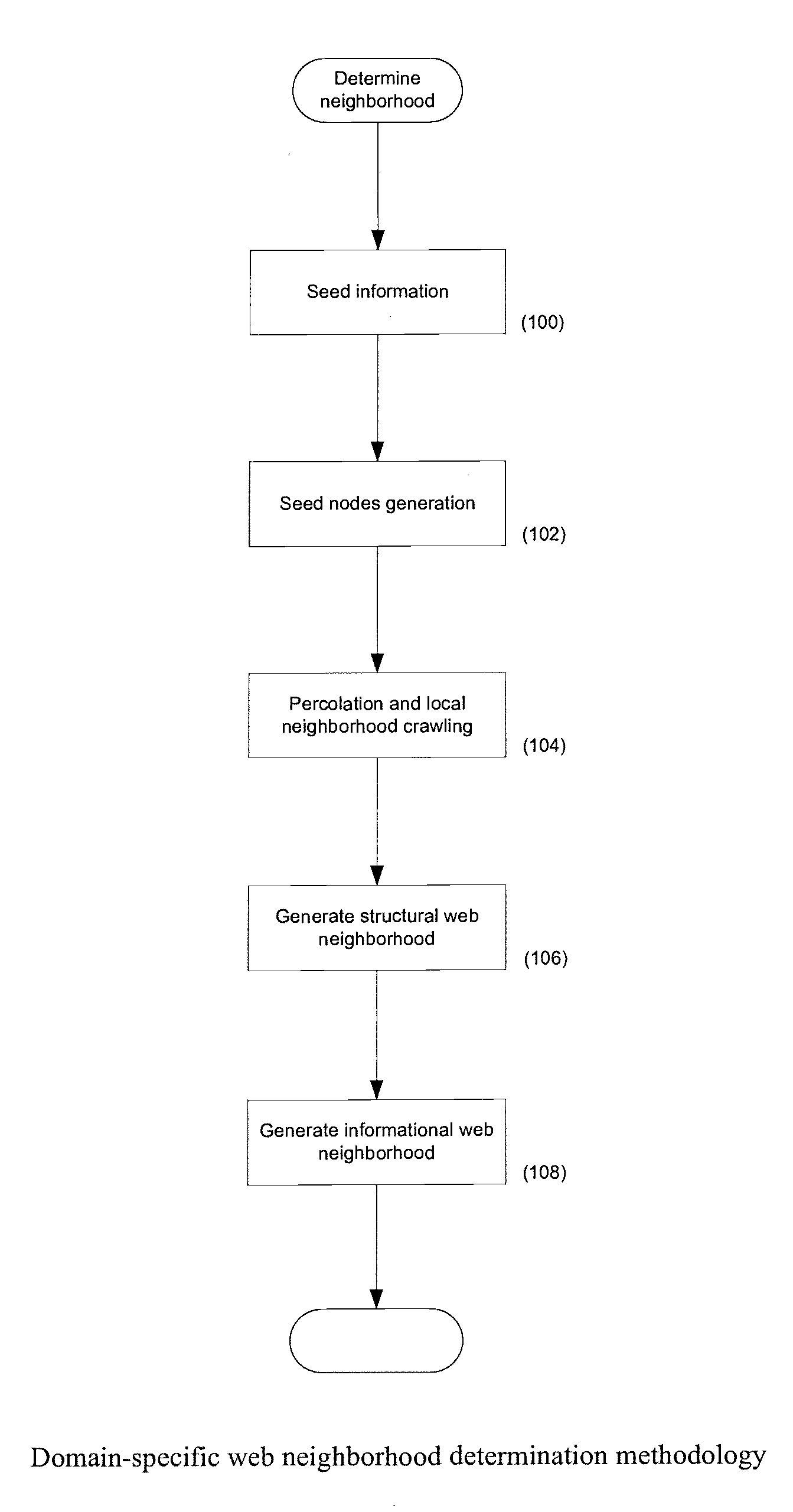
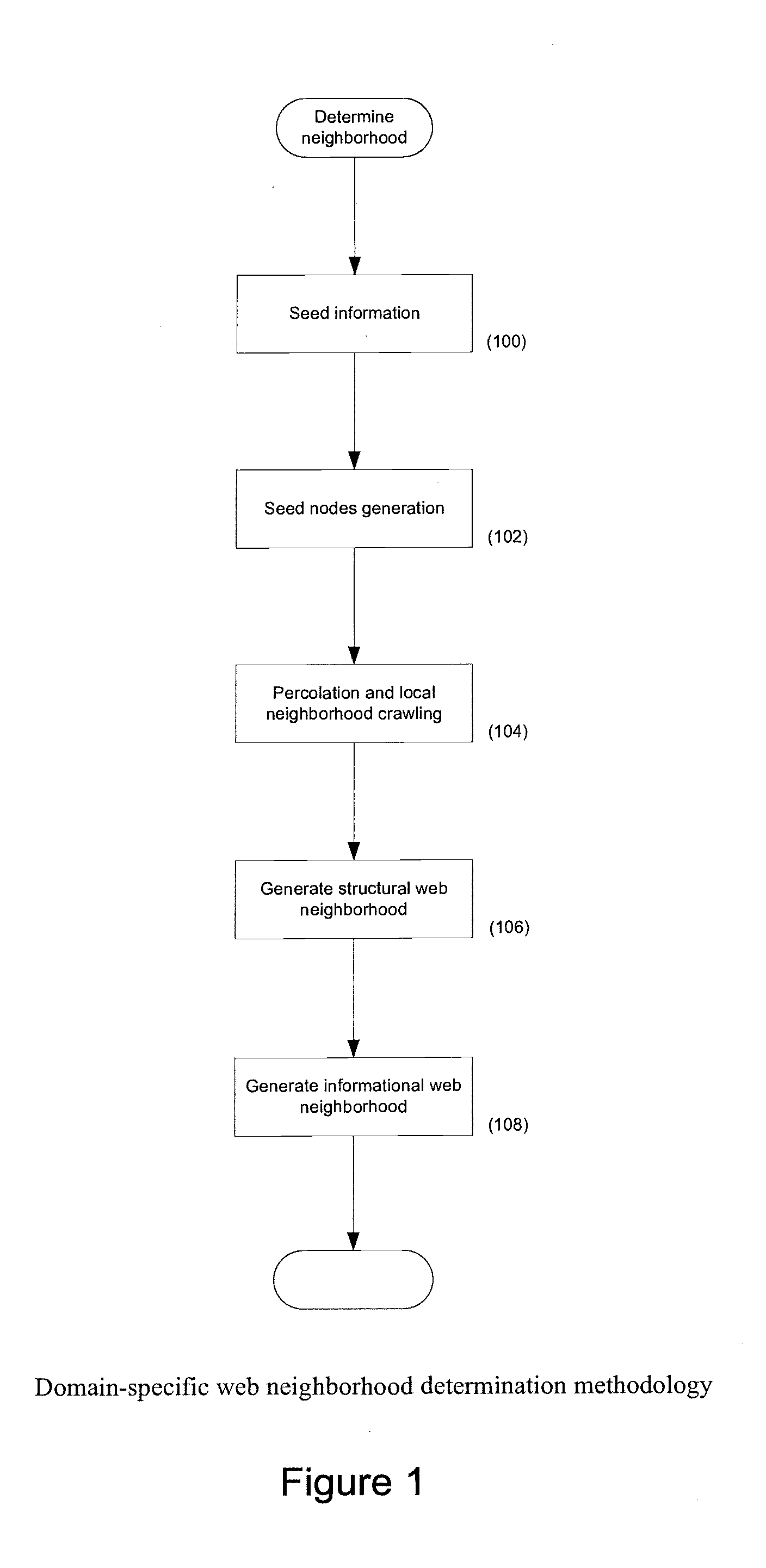
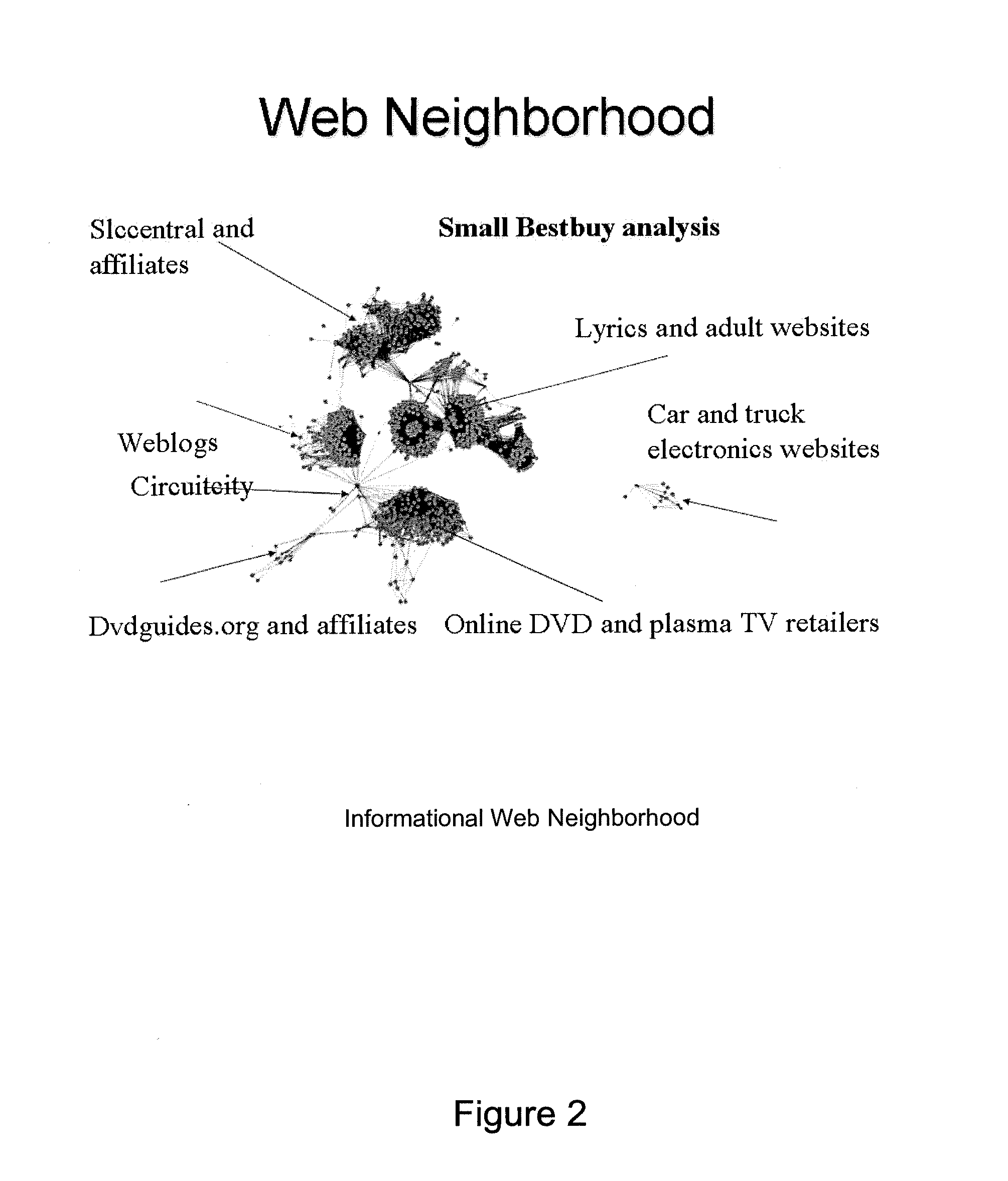
Systems and methods for creating, navigating, and searching informational web neighborhoods
Systems and methods are described for the creation of hierarchical networks of overlapping informational Web neighborhoods, where each neighborhood comprises a set of closely linked pages that share a common set of concepts and intent and purpose. A general description of a category of information can be used to generate a network of overlapping communities of web pages and objects, where the neighborhoods represent pages or objects that share a common set of underlying concepts and semantic associations. Each such neighborhood can be semantically tagged. Overlaps among neighborhoods and the hierarchical structure of the network capture complex relationships among the concepts that the corresponding informational neighborhoods represent. All informational neighborhoods of the web can be mapped. The systems and methods can be adapted for any digital content and constitute a hybrid network of contents and their relationships.
Owner:NETABEER
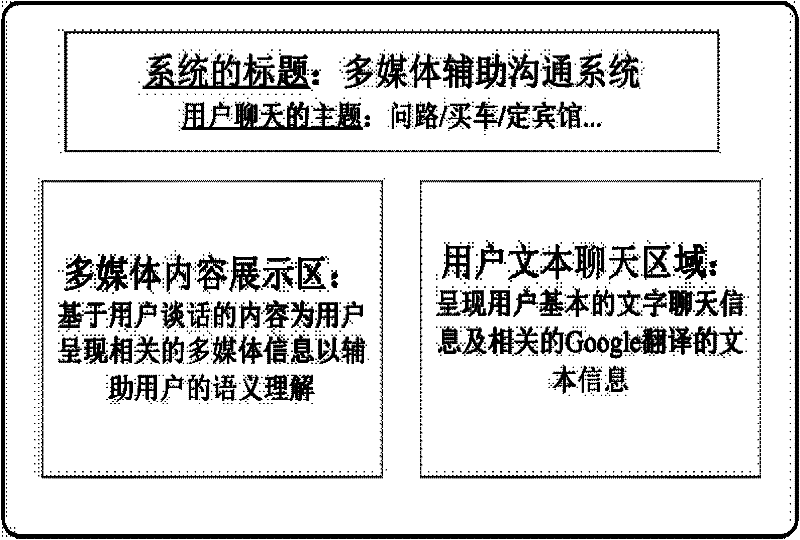
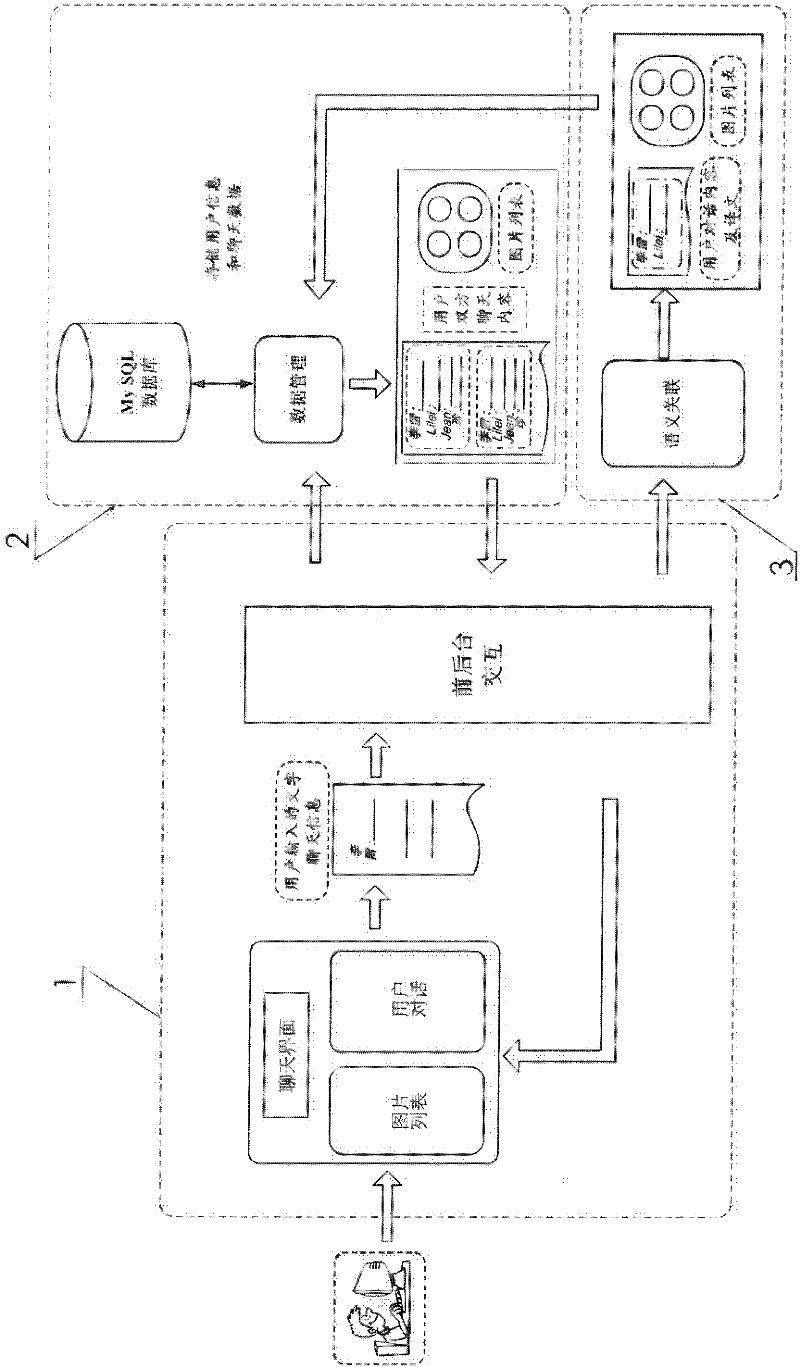
System and method for realizing cross-language communication based on multimodal assistance
InactiveCN102262624AReduce ambiguityMeet individual needsSpecial data processing applicationsCommunications systemData management
The present invention proposes a cross-language communication system and method based on multi-modal assistance. The method utilizes the foreground interaction module, data management module and semantic association module in the cross-language communication system to analyze conversation content and use natural language processing tools It can automatically extract the central topic and keywords in the conversation, and the semantic association module can automatically search for relevant pictures and video clips based on the detected central topic and keyword information, and provide them to both parties in an appropriate way, so as to promote mutual understanding and communication. Here, the pictures and videos used as aids in understanding can be automatically picked up from the Internet by searching, or directly obtained from a pre-marked multimedia library. Finally, the system generates a multimodal conversation summary based on the text chat information of the two parties in the conversation and the corresponding picture and video content.
Owner:INST OF AUTOMATION CHINESE ACAD OF SCI
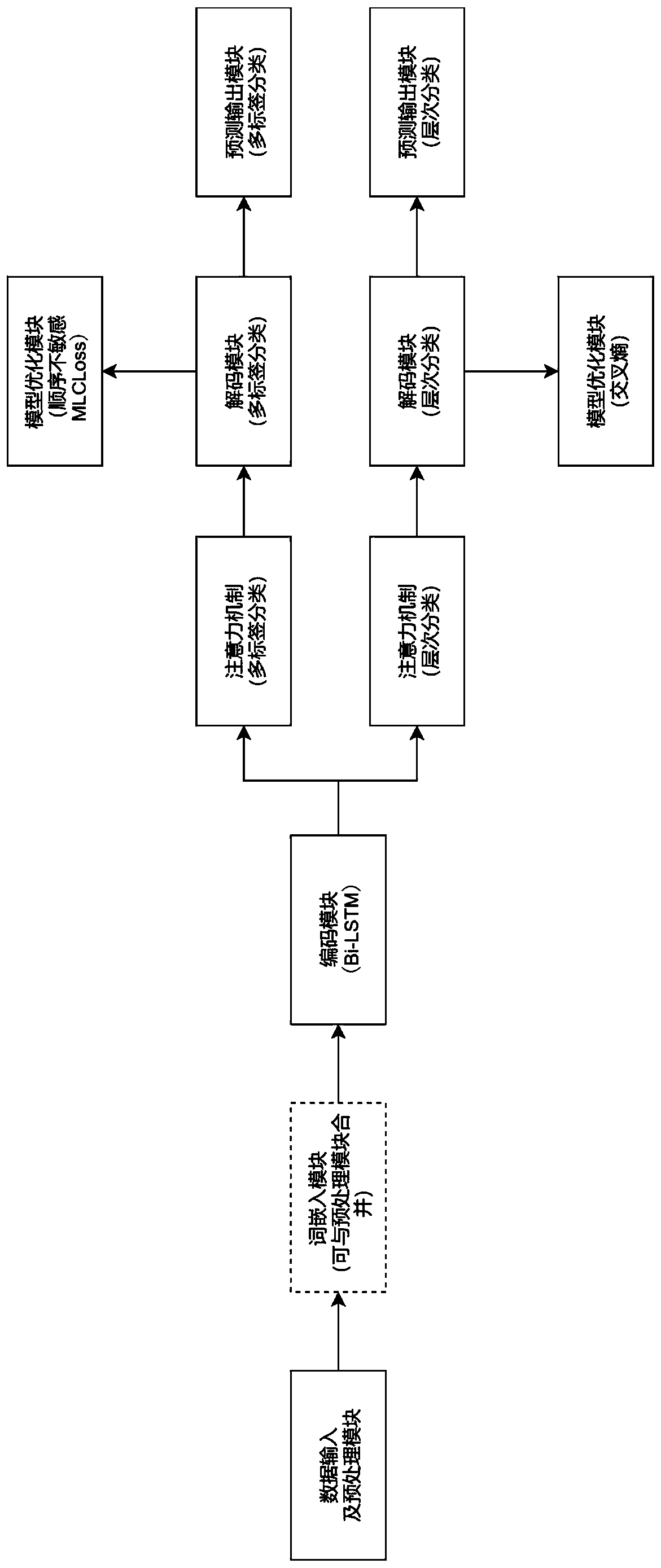
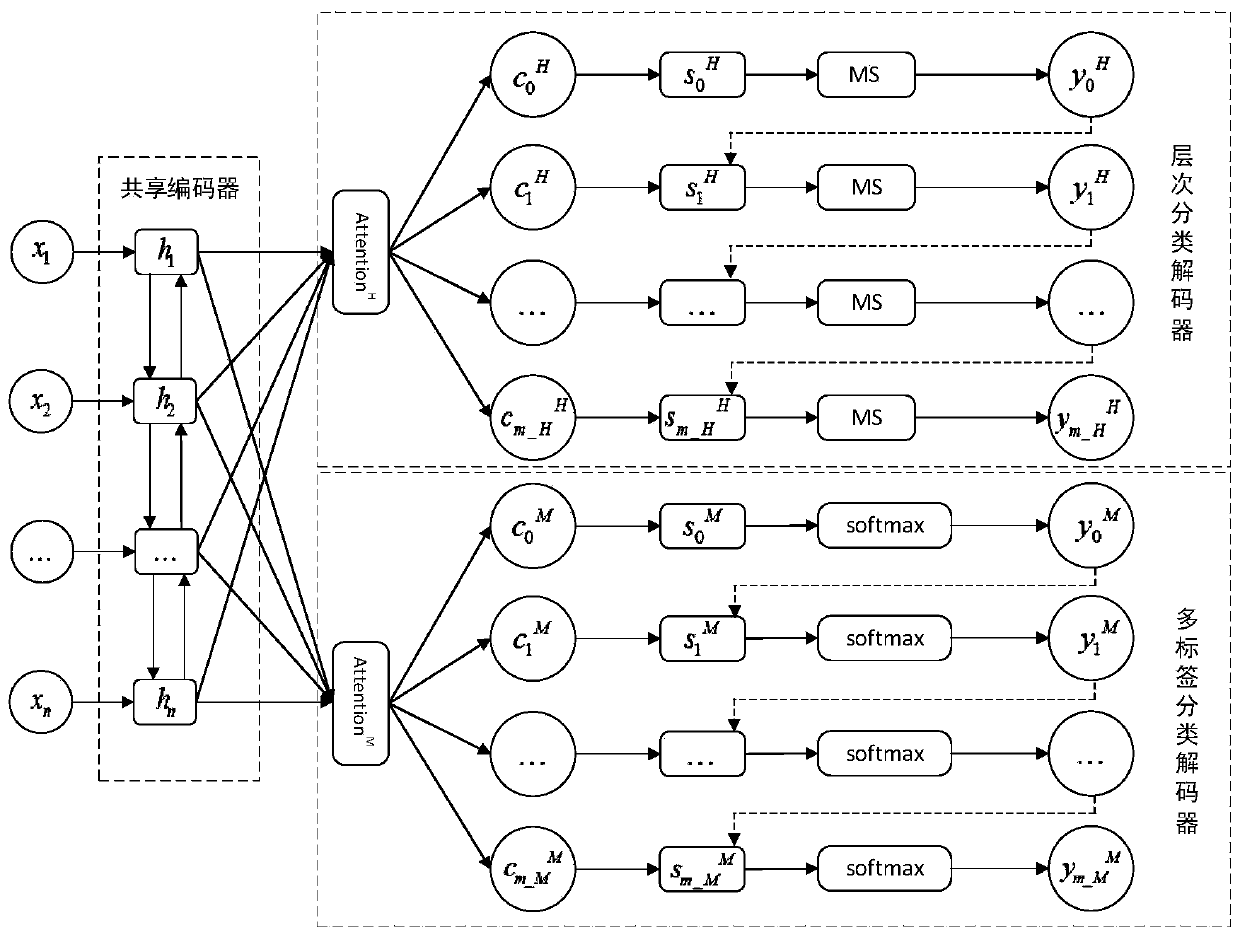
Text classification method based on generative multi-task learning model
ActiveCN110347839AEnhanced Semantic RelevanceImprove classification performanceSpecial data processing applicationsText database clustering/classificationFeature vectorMulti-label classification
The invention discloses a text classification method based on a generative multi-task learning model, and the method comprises the steps: alternately decoding a multi-task classification model througha training set according to a multi-label classification task and a hierarchical classification task, obtaining a current-moment semantic feature related to a coding moment feature vector through decoding, and carrying out the training of the current-moment semantic feature; optimizing the multi-task classification model according to the training result and the real label set to obtain an optimized multi-task classification model; inputting data in a to-be-detected set into the optimized multi-task classification model, and respectively obtaining classification labels to finish classification. The semantic association between the multi-label classification model and the hierarchical classification model is constructed through a multi-task mechanism in the training process of the model, sothat the semantic association between two sub-task prediction results can be enhanced, and the purpose of improving the sub-task classification performance is achieved.
Owner:湖南数定智能科技有限公司
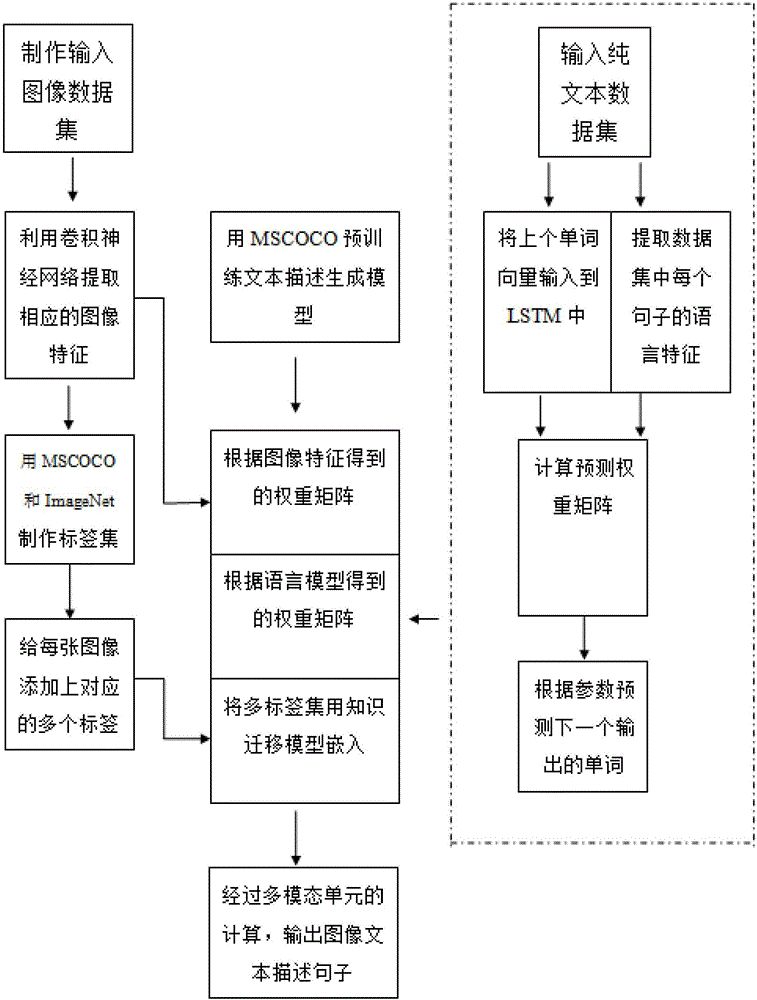
Image text description method based on knowledge transfer multi-modal recurrent neural network
ActiveCN106650756AAccurate descriptionSemantically appropriateCharacter and pattern recognitionPattern recognitionSemantics
The invention provides an image text description method based on a knowledge transfer multi-modal recurrent neural network. According to the method, by a knowledge transfer model in a multi-modal unit, identification capacity of an existing image classifier on most of objects and grammatical structures and semantic association in an existing corpus are well utilized, a target object in an image can be more accurately described, and generated sentence descriptions can be richer in grammatical structure, appropriate in semantics, and higher in readability.
Owner:SYSU CMU SHUNDE INT JOINT RES INST +1
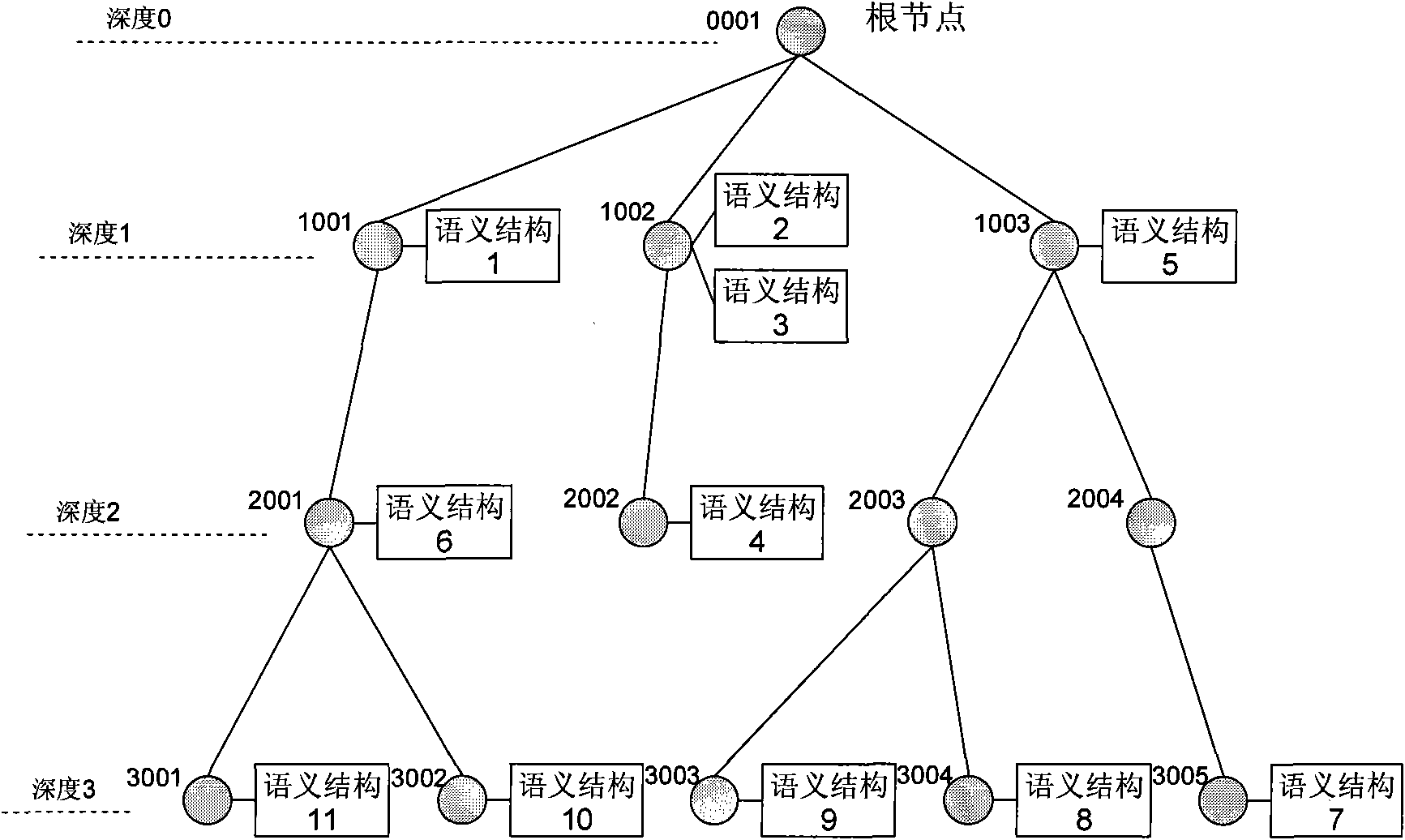
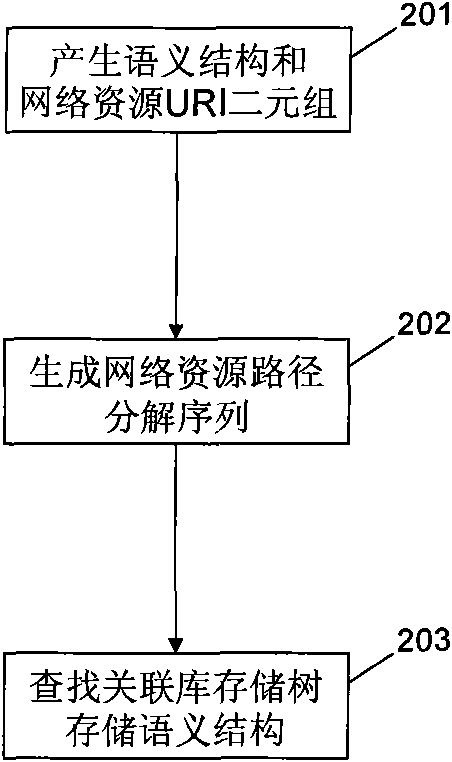
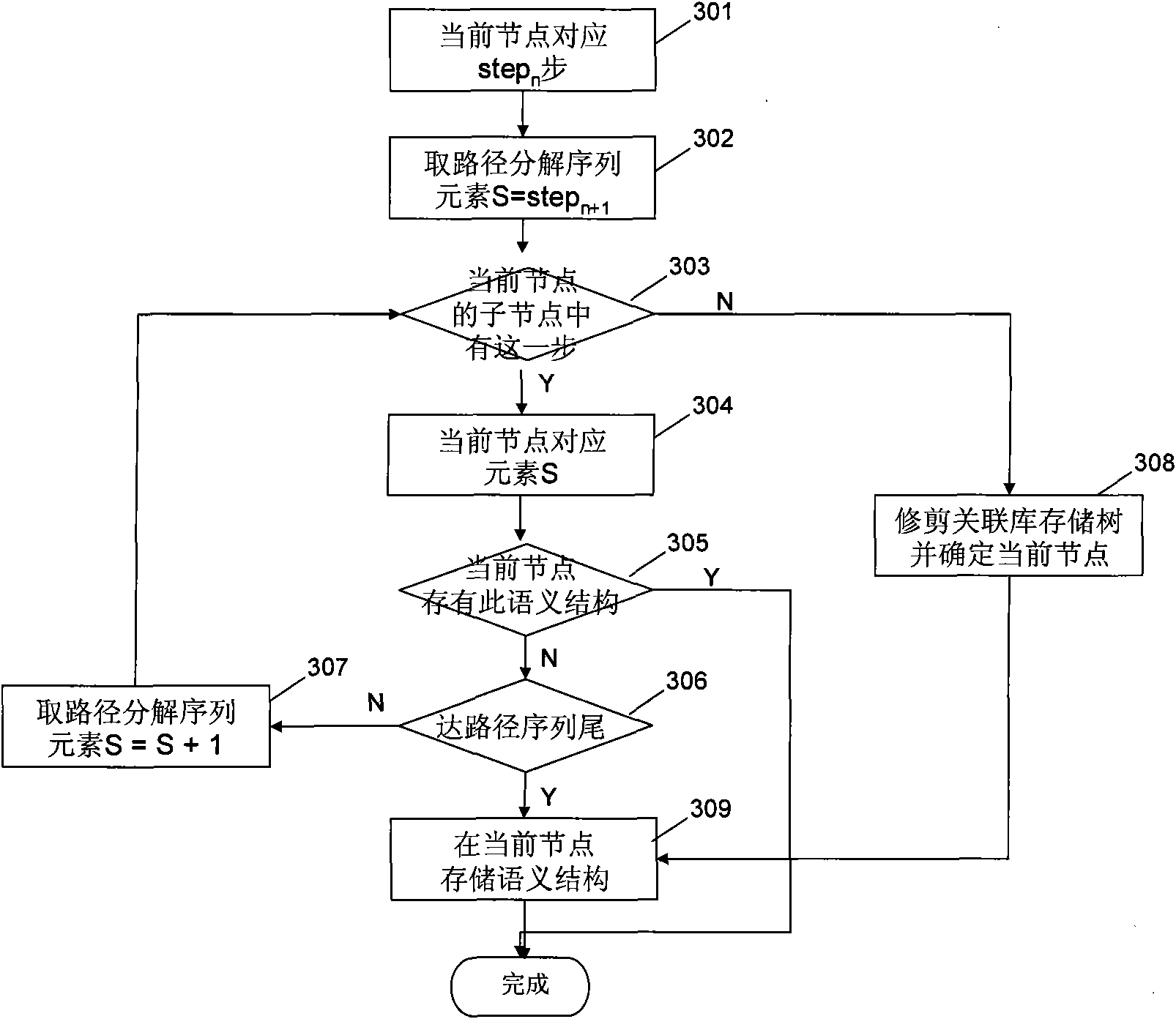
Method and device for searching information object
InactiveCN101655862ARefine search resultsSpecial data processing applicationsFull text searchInformation object
The invention discloses a method and a device for searching an information object. The information object is information content with semantic structure, comprising a plurality of information properties with semantic correlative relation, wherein the information properties are units of different semantic aspect content of information objects; and the semantic structure is collection of semantic metadata. Target webpage URI can be utilized to query correlative library to obtain semantic structure by establishing semantic structure and network resource URI or correlative library of prefix of network resource URI; webpage information is formatted and indexes are established with the guidance of semantic structure; user request is responded, searching results are provided according to correlation order, and simultaneously layering semantic navigation trees are provided; and refine searching results are provided to a user when the user clicks the node of the semantic navigation tree. The invention belongs to the technical field of computer science, is applicable to the application fields of network information extraction, full text search, semantic search, mobile phone search and the like.
Owner:华天清 +1
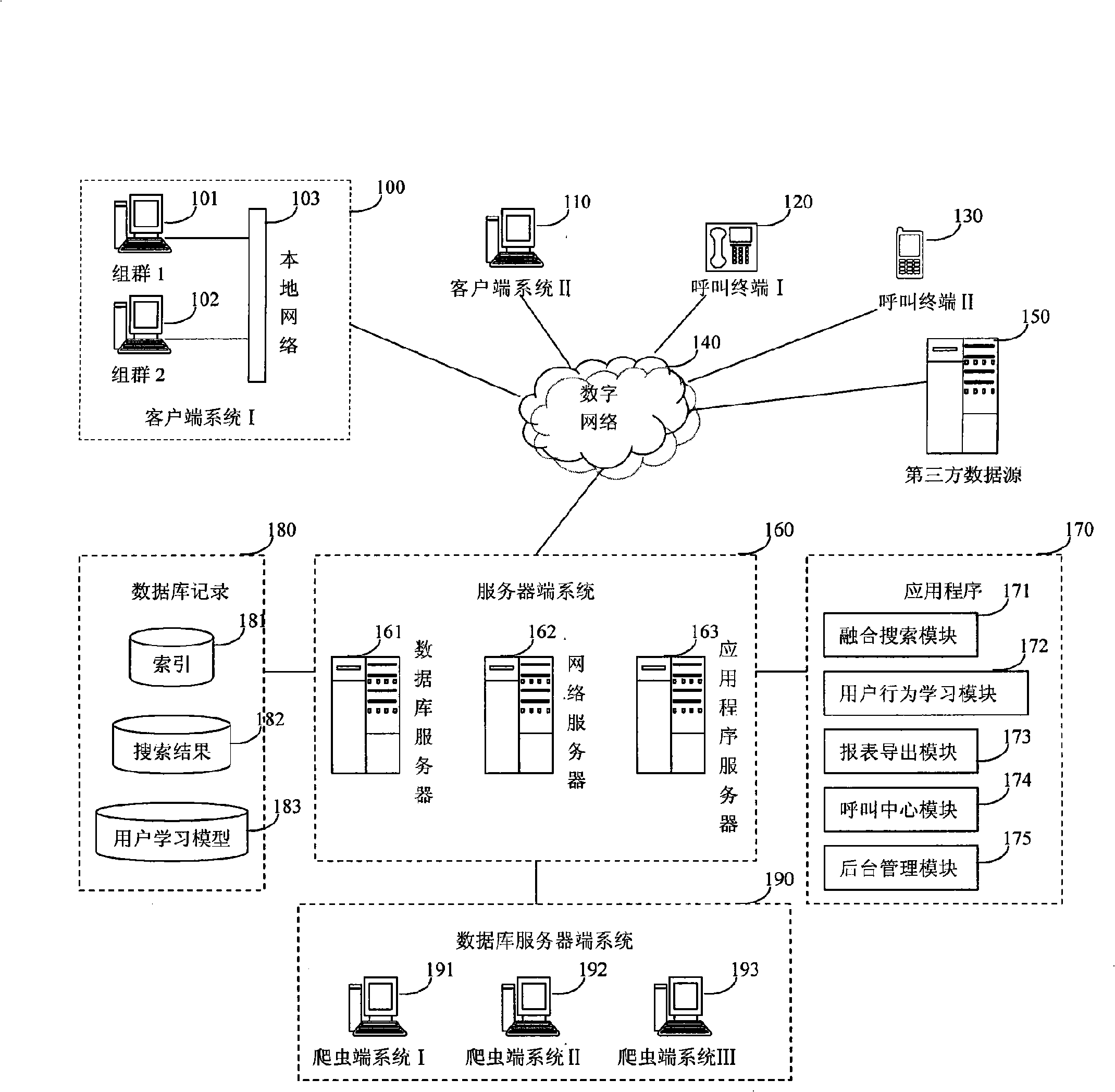
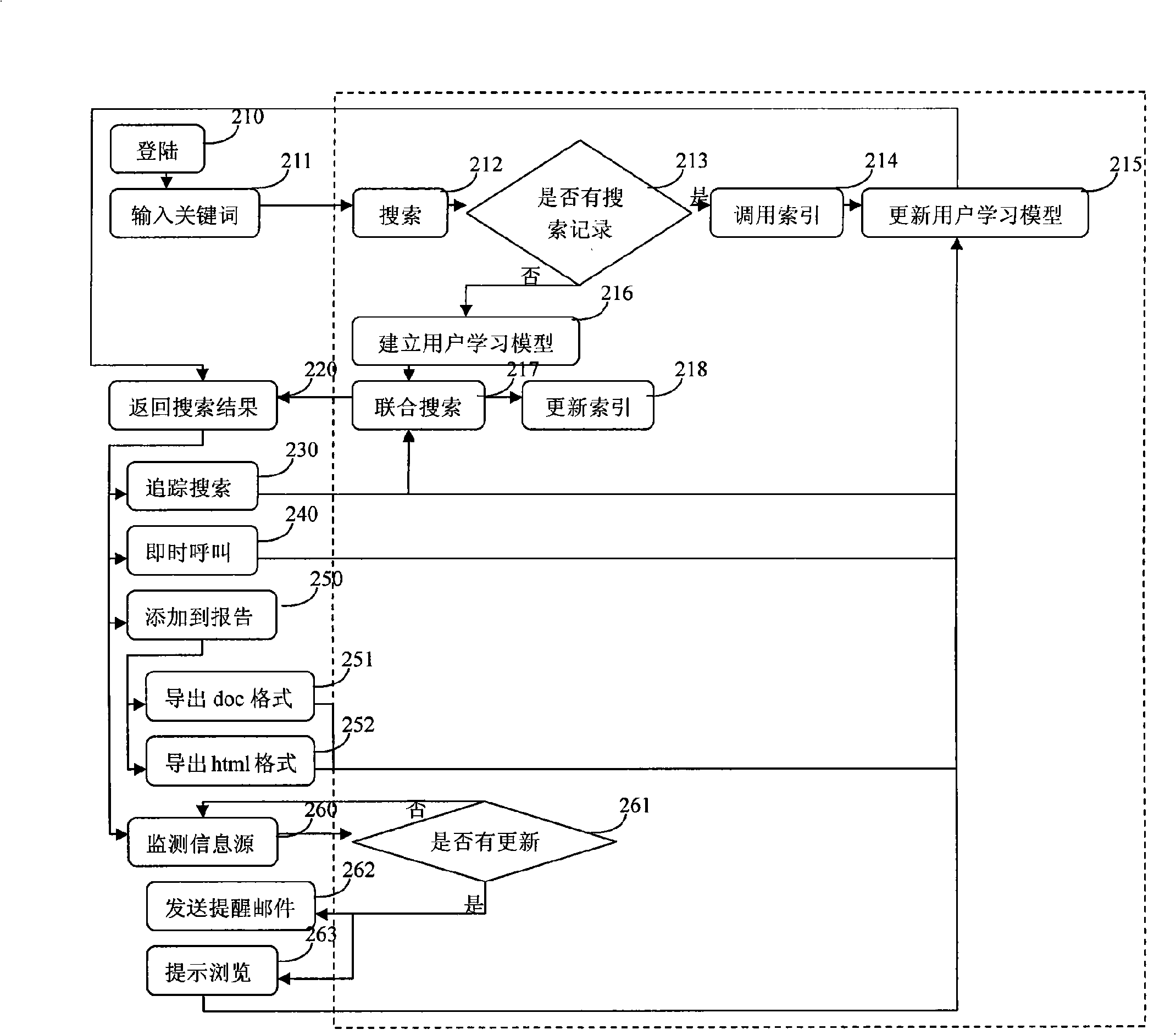
Computer auxiliary report and knowledge base generation method
InactiveCN101334784AImprove acquisitionImprove the efficiency of classifying informationSpecial data processing applicationsInformation resourceComputer-aided
The invention relates to a computer assistant reporting and knowledge-base generation method including the following steps: a server system receives requests of information search from users and searches all structured and unstructured web pages and websites matching the search requirements of users on the internet and a third-party database and also feeds the search results back to a client digital terminal system after classification, de-emphasis and compilation while matching the third-party database; the server system records the search behavior of a user and detects the updating of information resource and catches and classifies the updated information in real time so as to remind the user of the updating of the information resource when the user goes on line; the user selects the required information from the search results and collects the information into the system and the knowledge mining method is adopted to generate reports and derive files. The invention has the beneficial effects that the efficiency of searching, collecting and classifying the information is enhanced for the user, and the unstructured information can be converted into structured information and the semantic relevance between information can be preserved by human-computer interaction.
Owner:施章祖 +1
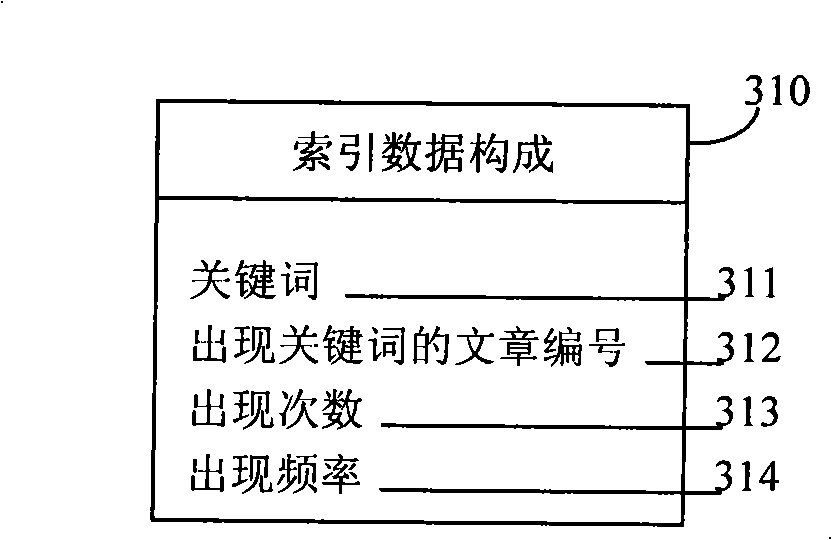
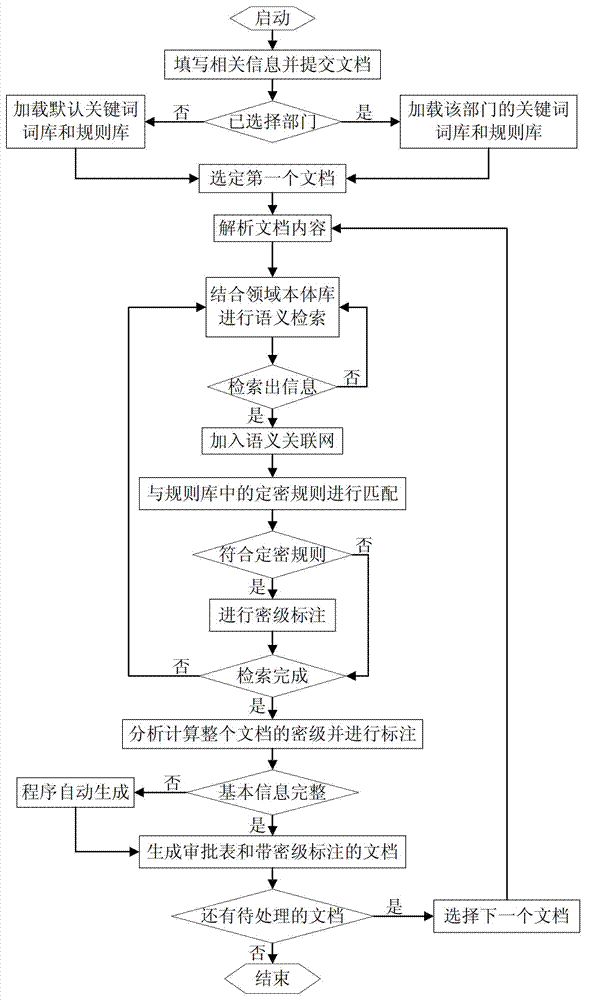
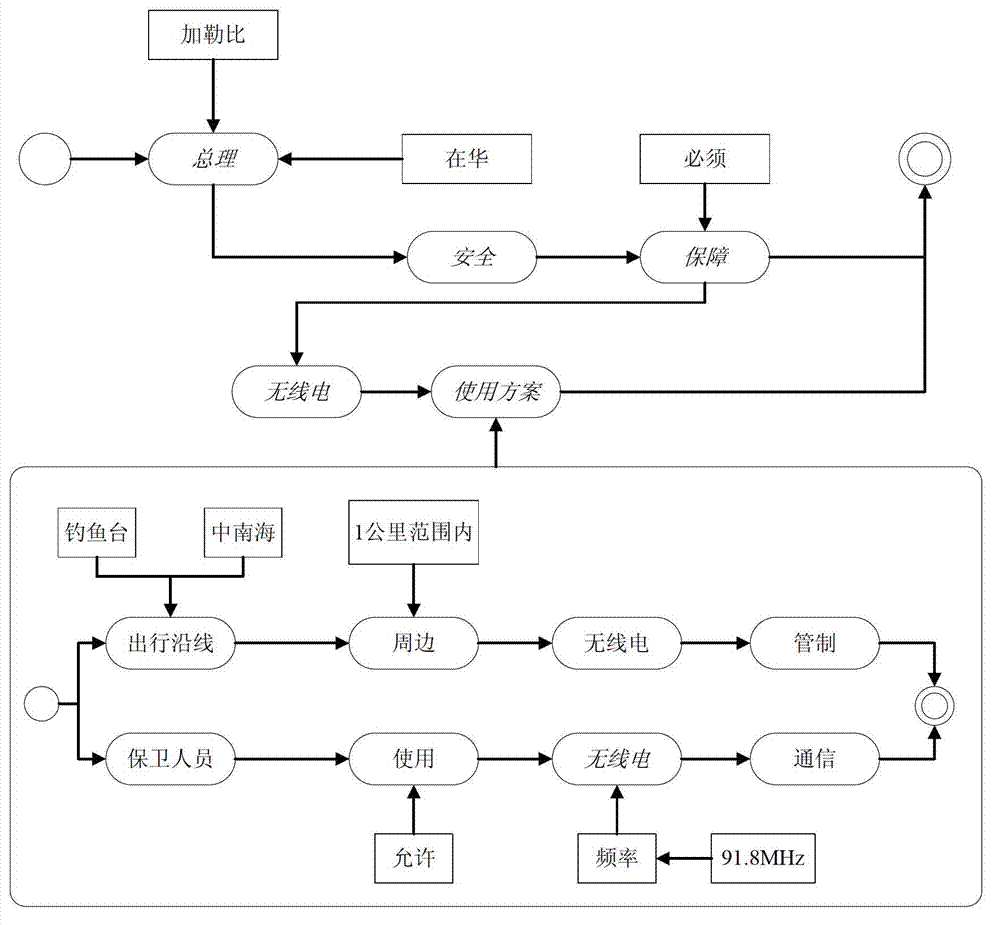
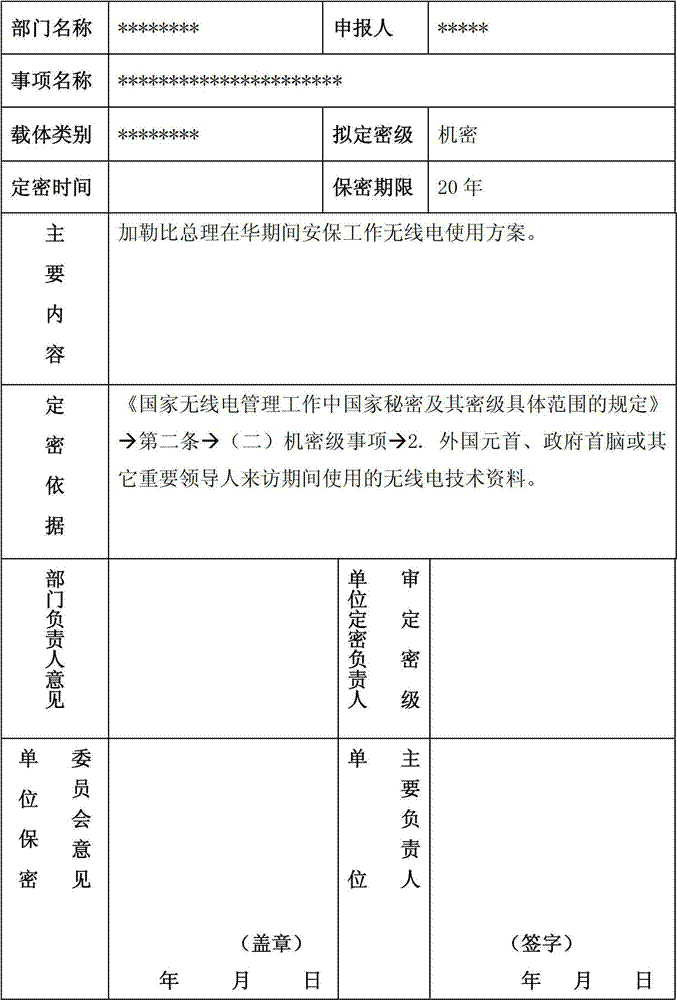
Method for retrieving confidential information of file and judging and marking security classification based on content correlation
InactiveCN102819604AAccurate and comprehensive searchEfficient searchSpecial data processing applicationsInternet privacyContent retrieval
A method for retrieving confidential information of a file and judging and marking the security classification based on content correlation is mainly characterized by comprising the following steps of: selecting corresponding confidential keywords and a matched rule base according to the range to which a document belongs; accurately and comprehensively searching confidential information in the document by carrying out word segmenting operation on the document contents and constructing a semantic correlation network; carrying out security classification judgment and encryption processing on each confidential information point according to a secret-level setting rule in a secret-level setting rule base; then giving out corresponding security classifications by integrating the security classifications of various confidential information points; and finally, marking related confidential information in the documents. According to the method, the confidential information in the document can be efficiently searched and the security classification of the document is accurately judged, so that the workload of manual secret-level setting is reduced, the efficiencies of secret-level setting work and the security classification appraisal work are increased, the random secret-level setting phenomenon in the secret-level setting process is effectively prevented and new confidential keywords and matching rules can be automatically learned, and further the precision of retrieval and security classification judgment is continuously improved.
Owner:徐亮 +1
Local spline embedding-based orthogonal semi-monitoring subspace image classification method
InactiveCN101916376APreserve the eigenstructure of the manifold spaceAvoid difficultiesCharacter and pattern recognitionHat matrixData set
The invention discloses a local spline embedding-based orthogonal semi-monitoring subspace image classification method. The method comprises the following steps of: 1) selecting n samples serving as training sets and the balance serving as testing sets from image data sets, wherein the training sets comprise marked data and unmarked data; 2) building an extra-class divergence matrix and an intra-class divergence matrix by using the marked data; (3) training data characteristic space distribution by using a whole and building a Laplacian matrix in a local spline embedding mode; 4) according to a local spline, embedding an orthogonal semi-monitoring subspace model, and searching a projection matrix to perform dimensionality reduction on the original high dimension characteristic; 5) building a classifier for the training samples after the dimensionality reduction by using a support vector machine; and 6) performing the dimensionality reduction on the testing sets by using the projection matrix and classifying the testing sets after the dimensionality reduction by using the classifier. In the method, the information, such as image sample marking, characteristic space distribution and the like, is fully utilized; potential semantic relevance among image data can be found out; and image semantics can be analyzed and expressed better.
Owner:ZHEJIANG UNIV
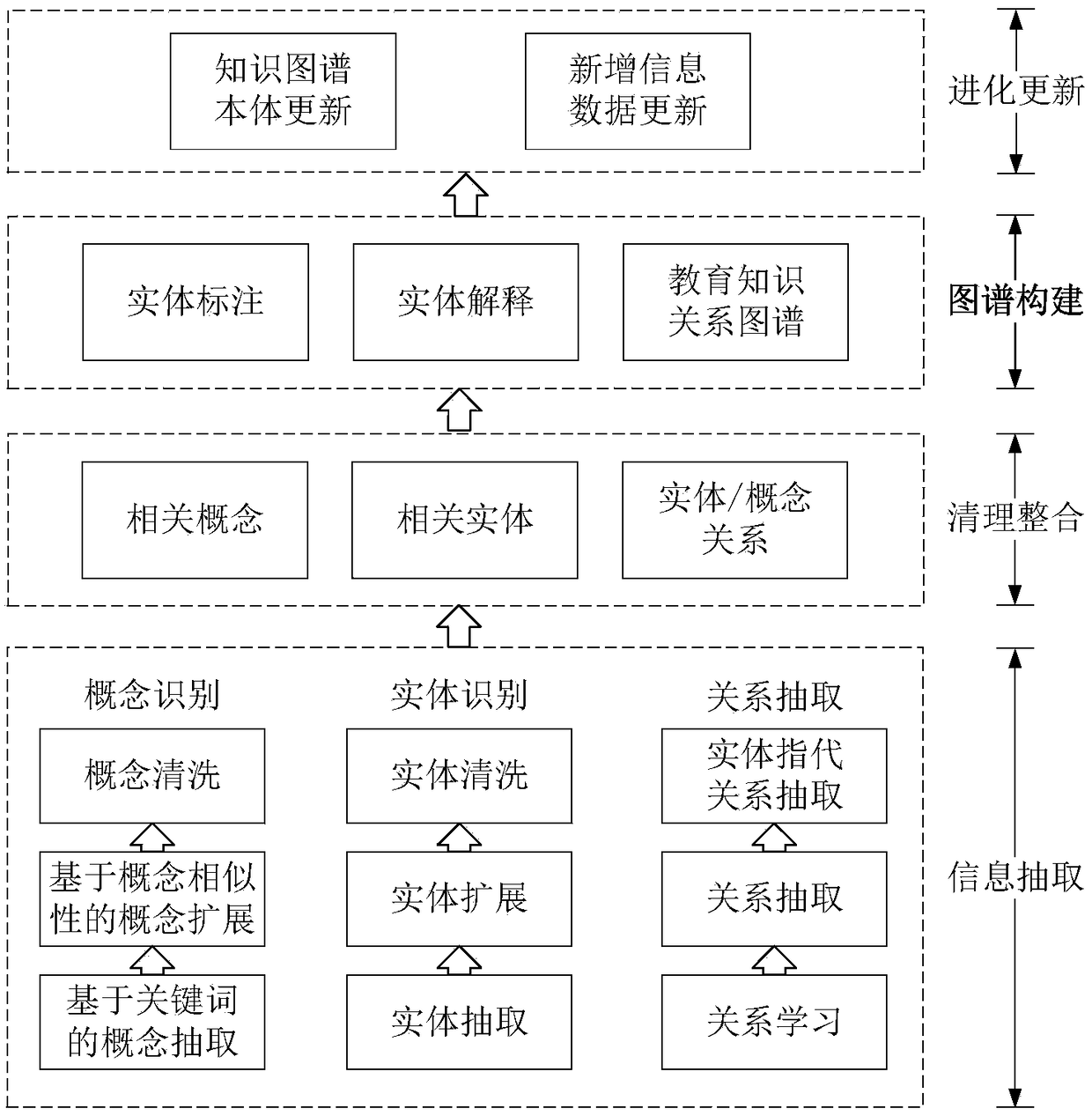
Knowledge mapping construction method for subject education resources
InactiveCN108664615AImprove connectionSpecial data processing applicationsTacit knowledgeHuman resource management
The invention discloses a knowledge mapping construction method for subject education resources. The method comprises the following steps that 1, information of entities and relation information in the subject education resources are extracted; 2, cleaning integration is carried out on the information, information redundancy and wrong information are eliminated, thereby ensuring the quality of theinformation; 3, classification and semantic association are carried out on the information to form a knowledge representation form of 'entity-relation-entity' triples, and a visual tool is utilized to construct a subject resource knowledge mapping; 4, tacit knowledge is further excavated through a knowledge inference, evolution and update are carried out on the knowledge mapping, thereby enriching and extending a knowledge base. The knowledge mapping construction method for the subject education resources has the advantages that the knowledge mapping for constructing subject resources is provided, the continuity and consistency of subject resource content are achieved, the systematized and systematic subject knowledge mapping is provided for learners, thereby promoting the practical application of a knowledge mapping technology in the fields of education resource management, information retrieval, knowledge recommendation and the like.
Owner:HUAZHONG NORMAL UNIV
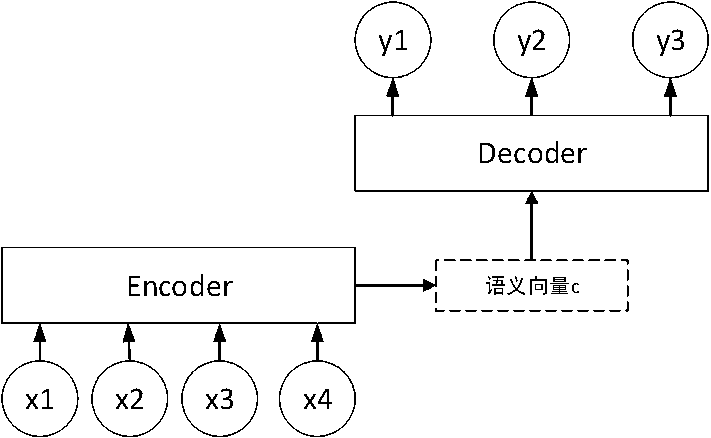
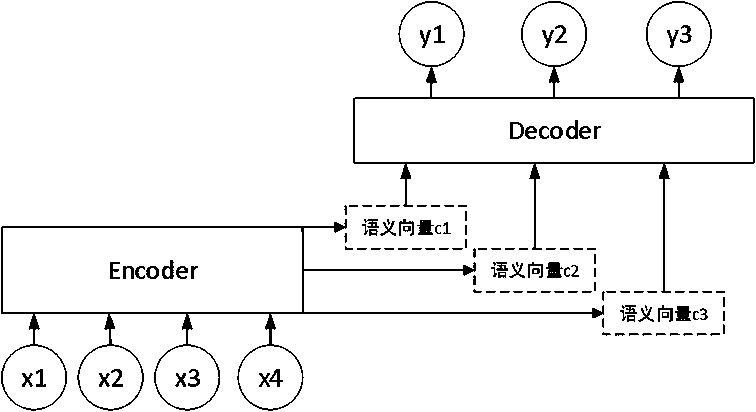
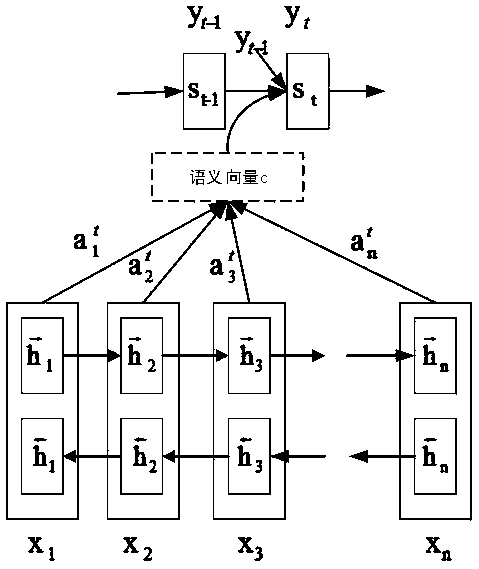
A text summarization model generation algorithm that fuses information selection and semantic association
ActiveCN109145105AReduce generationImprove semantic relevanceSemantic analysisSpecial data processing applicationsCopying mechanismSemantic association
The invention relates to a text abstract model generation algorithm for fusing information selection and semantic association. Firstly, based on the Decoder model, the attention mechanism is combinedto obtain enough information of input sequence. Secondly, a copy mechanism and a coverage mechanism are used to solve the problem of non-login words and clause repetition in summary generation. Then aselective network is designed to encode the original text twice to filter the redundant information. Finally, by comparing the semantic relevance of the original text and the abstract, the semantic relevance of the abstract can be corrected, and the semantic relevance of the abstract and the original text can be enhanced.
Owner:FUZHOU UNIV
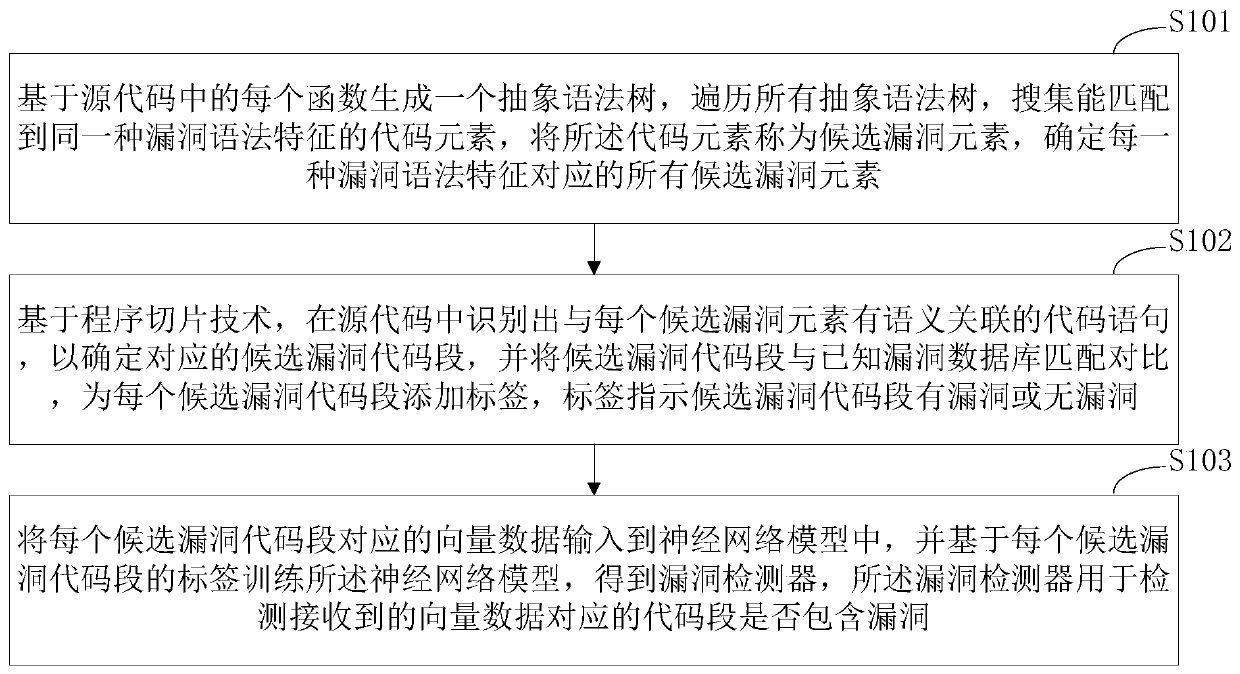
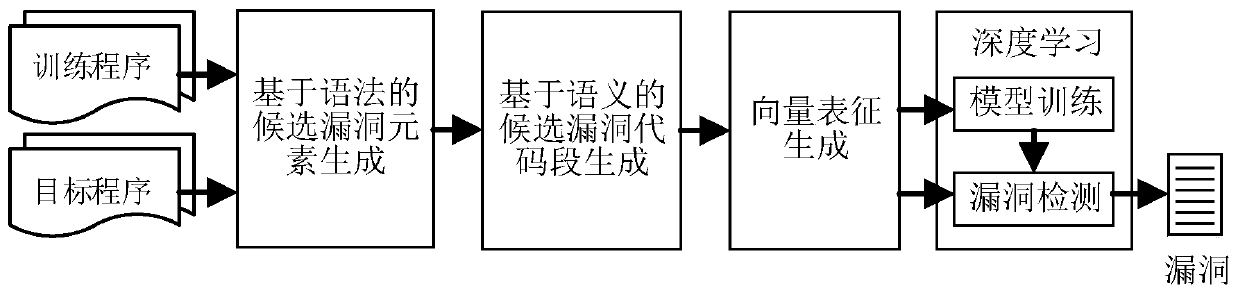
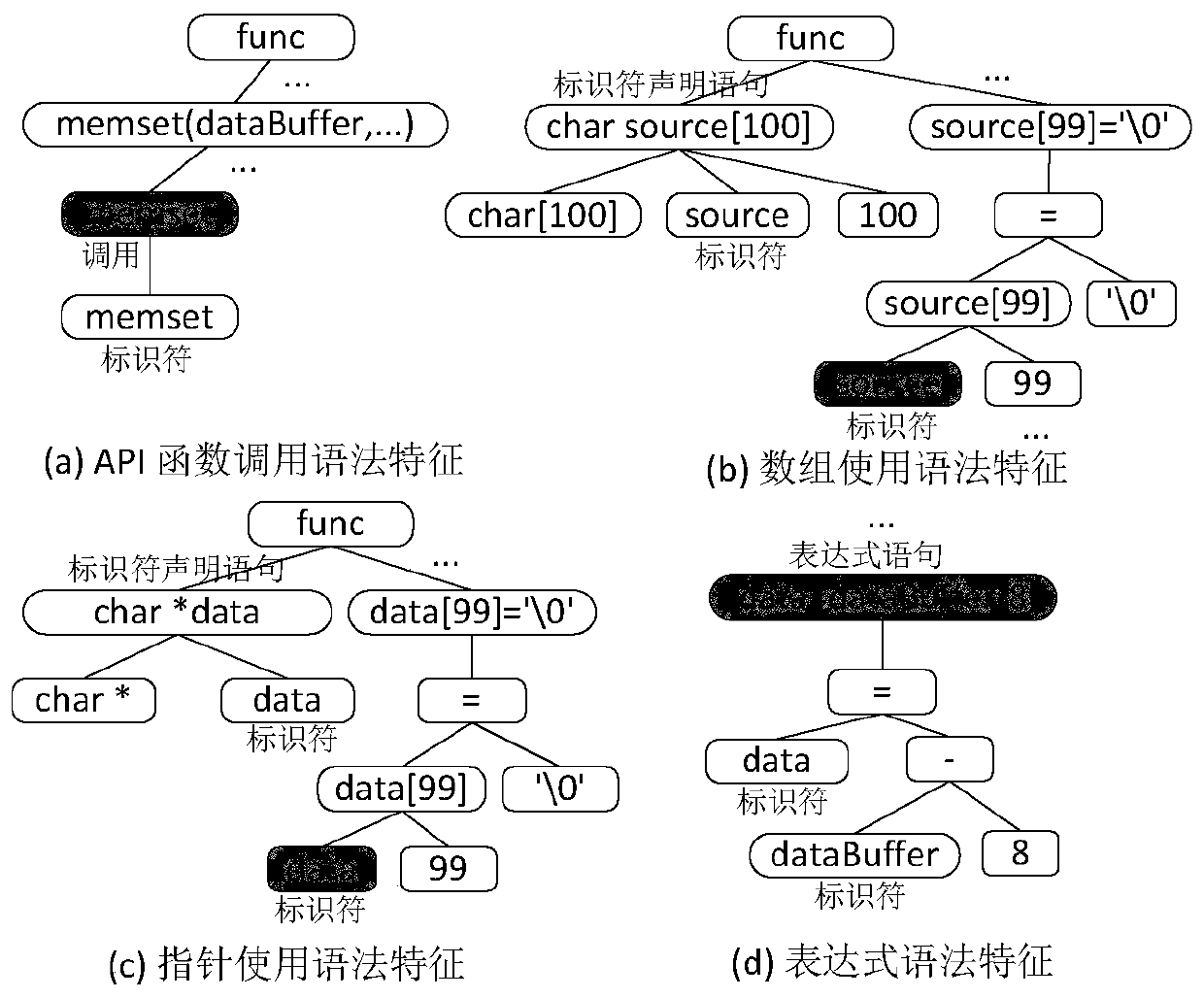
Source code vulnerability detection method, detector and training method and system thereof
ActiveCN110245496ATraining accuratelyImprove classification accuracyCharacter and pattern recognitionPlatform integrity maintainanceNerve networkCoded element
The invention discloses a source code vulnerability detection method, a detector and a training method and system thereof. The method comprises the steps of generating an abstract syntax tree based on each function in a source code, traversing all the abstract syntax trees, searching the code elements capable of being matched with the same vulnerability syntax feature, calling the code elements as the candidate vulnerability elements, and determining all the candidate vulnerability elements; based on a program slicing technology, identifying the code statements in semantic association with each candidate vulnerability element in the source code to determin the corresponding candidate vulnerability code segments, and adding the vulnerability labels to the candidate vulnerability code segments; and inputting the vector data corresponding to each candidate vulnerability code segment into a neural network model, and training the neural network model based on the label of each candidate vulnerability code segment to obtain a vulnerability detector. Based on the deep neural network, the vulnerability syntax features are extracted through a universal framework, the method is not limited to the vulnerability types and is high in expandability.
Owner:HUAZHONG UNIV OF SCI & TECH +1
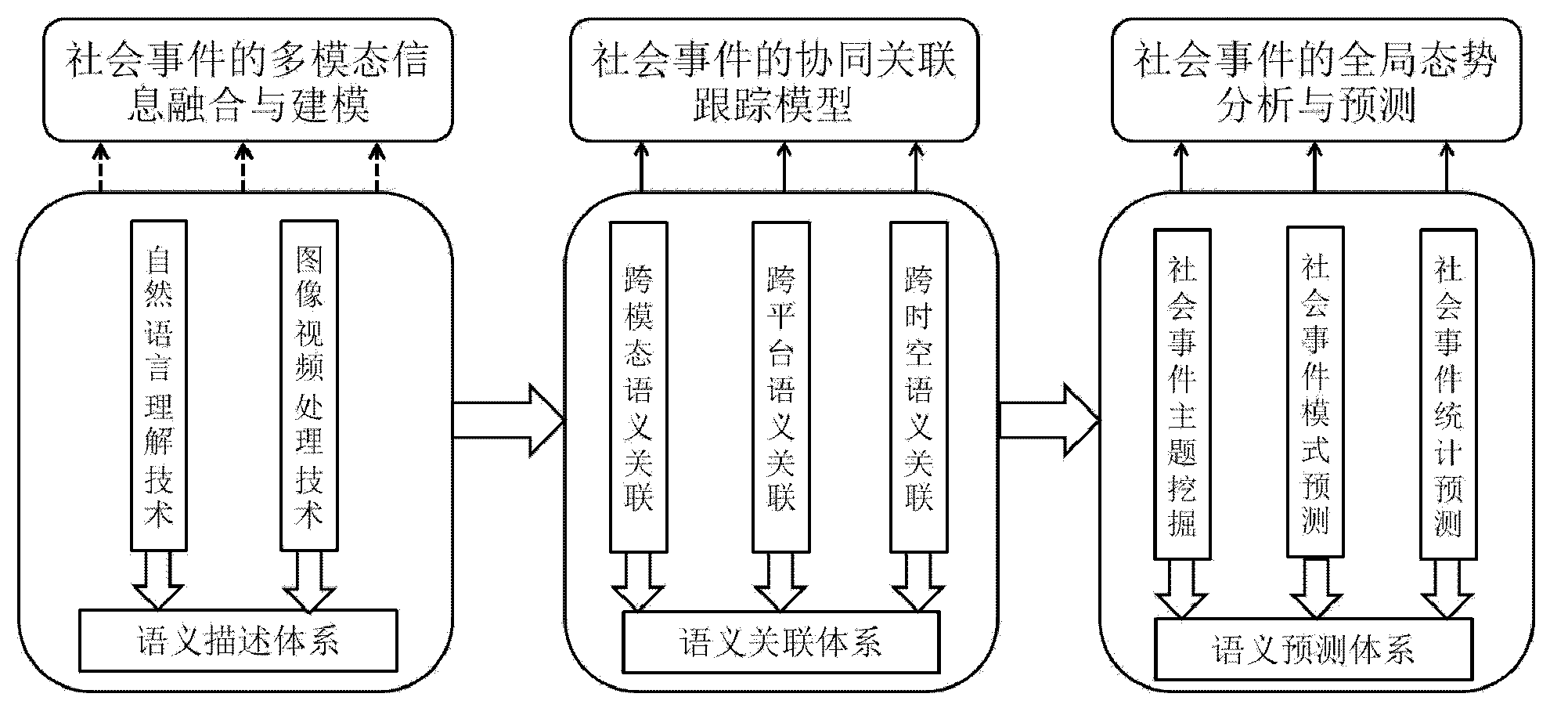
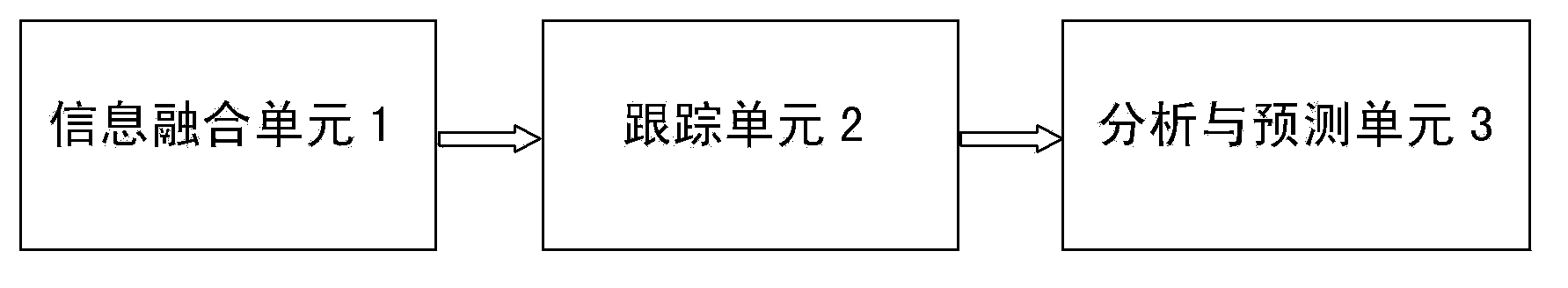
Analysis and prediction system for cooperative correlative tracking and global situation of network social events
InactiveCN103455705AImprove tracking accuracyEasy to understandSpecial data processing applicationsSpace - propertyInformation integration
The invention relates to an analysis and prediction system for cooperative correlative tracking and global situation of network social events. The system comprises an information fusion unit, a tracking unit, and an analysis and prediction unit. The information fusion unit is used for fusing multimodal features of network social event data to obtain fused information of the multimodal data of social events, thus establishing a semantic description model for the multimodal data of cross-social events. The tracking unit is connected with the information fusion unit and is used for acquiring sematic correlative tracking data of the social events on each aspect according to cross-modal property, cross-platform property and trans-time-and-space property of the network social events in face of network contents including rich multimedia information on the basis of the semantic description model for the multimodal data of the cross-social events. The analysis and prediction unit connected with the tracking unit is used for acquiring social-event-based global situation analysis and prediction data on the basis of the semantic correlative tracking data.
Owner:INST OF AUTOMATION CHINESE ACAD OF SCI
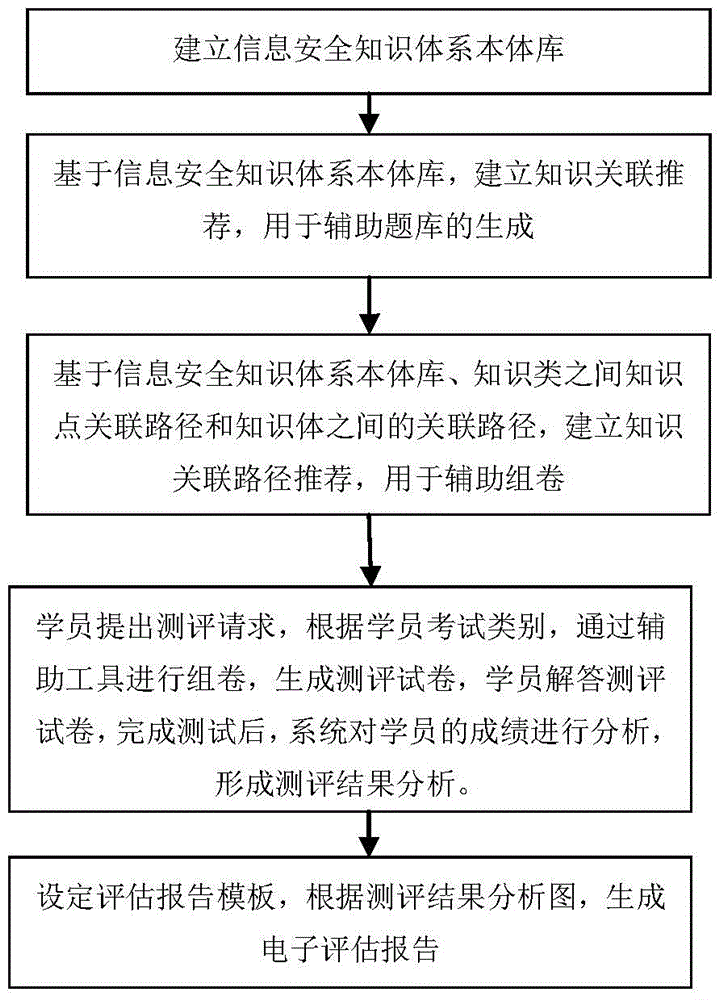
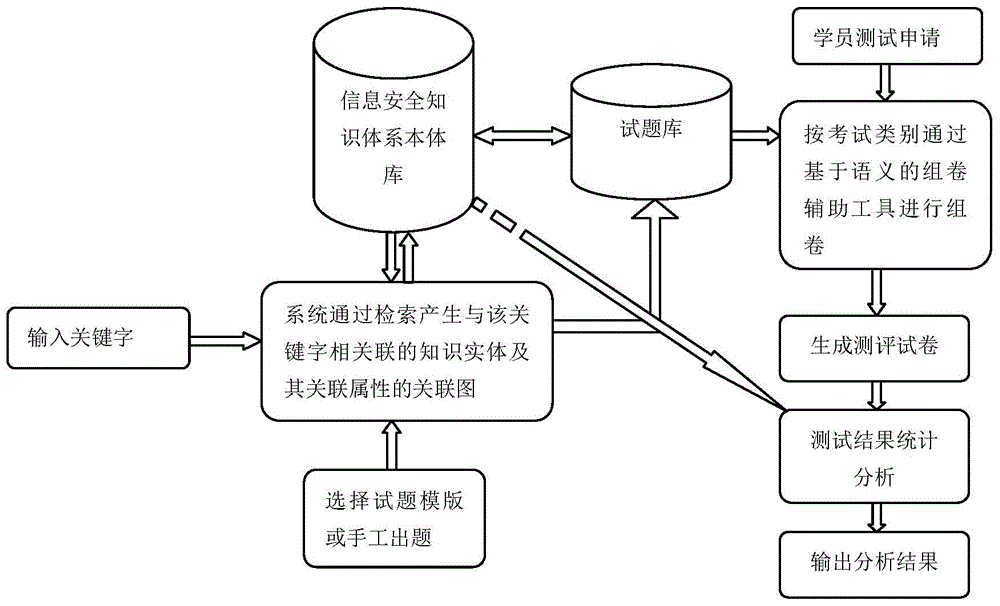
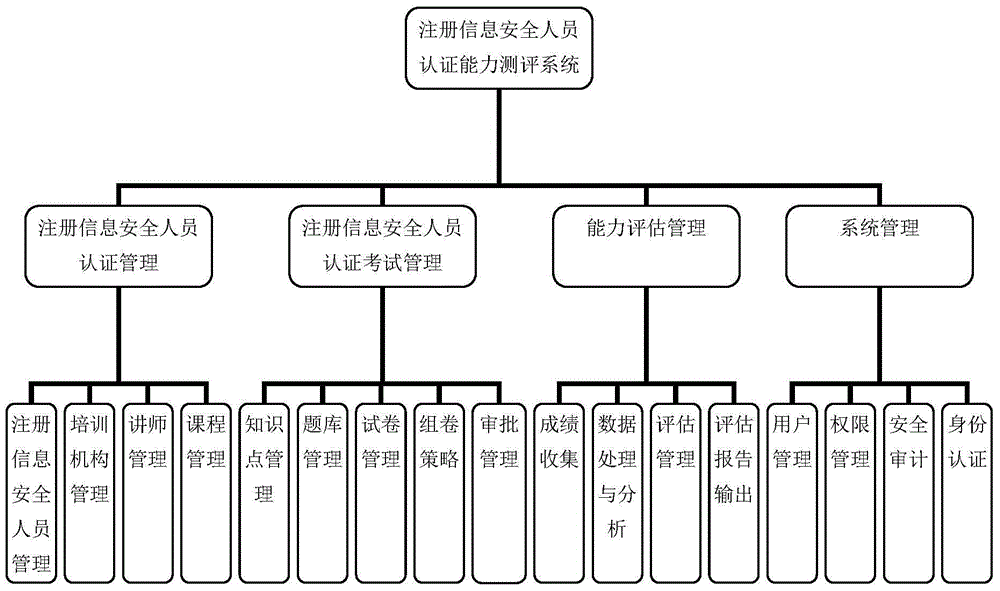
Semantics-based registration information security officer authentication capability evaluation method and system
InactiveCN104462228ATargetedComprehensive orientationData processing applicationsElectrical appliancesEvaluation resultSystems management
The invention provides a semantics-based registration information security officer authentication capability evaluation method and system and relates to the field of information security. The method comprises the steps of establishing an information security knowledge system ontology library, establishing a knowledge association recommendation, establishing a knowledge association path recommendation based on the ontology library, a knowledge point association path between knowledge classes and an association path between knowledge bodies, conducting evaluation on students, giving a general statistical analysis semantics-based analysis result and forming an electronic report. The system comprises an authentication management module, an authentication examination module, a capability assessment management module and a system management module. According to the method and system, semantic association between evaluated knowledge points is considered in all the steps from knowledge system establishment to evaluation result analysis, so that the mechanical properties, caused by automatic processing, of evaluation are reduced, evaluation efficiency and quality are improved, the reasonability of a final evaluation result is guaranteed, and then the purpose of capability evaluation is better achieved.
Owner:CHINA INFORMATION TECH SECURITY EVALUATION CENT
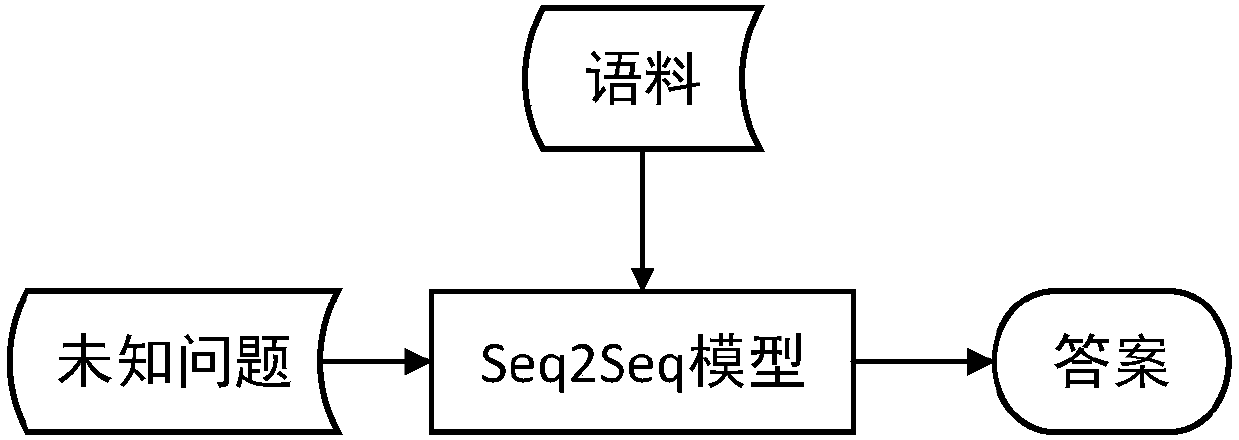
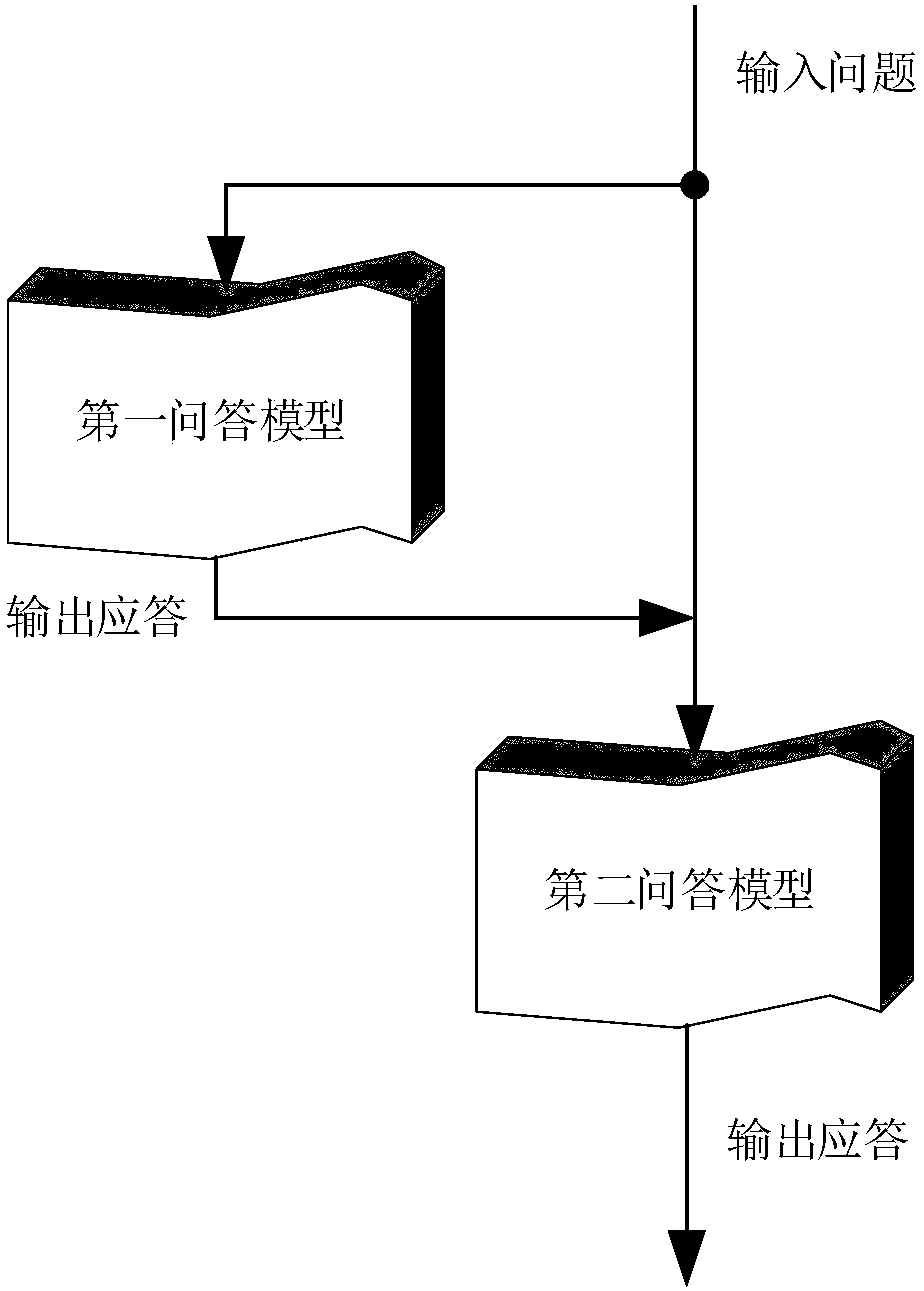
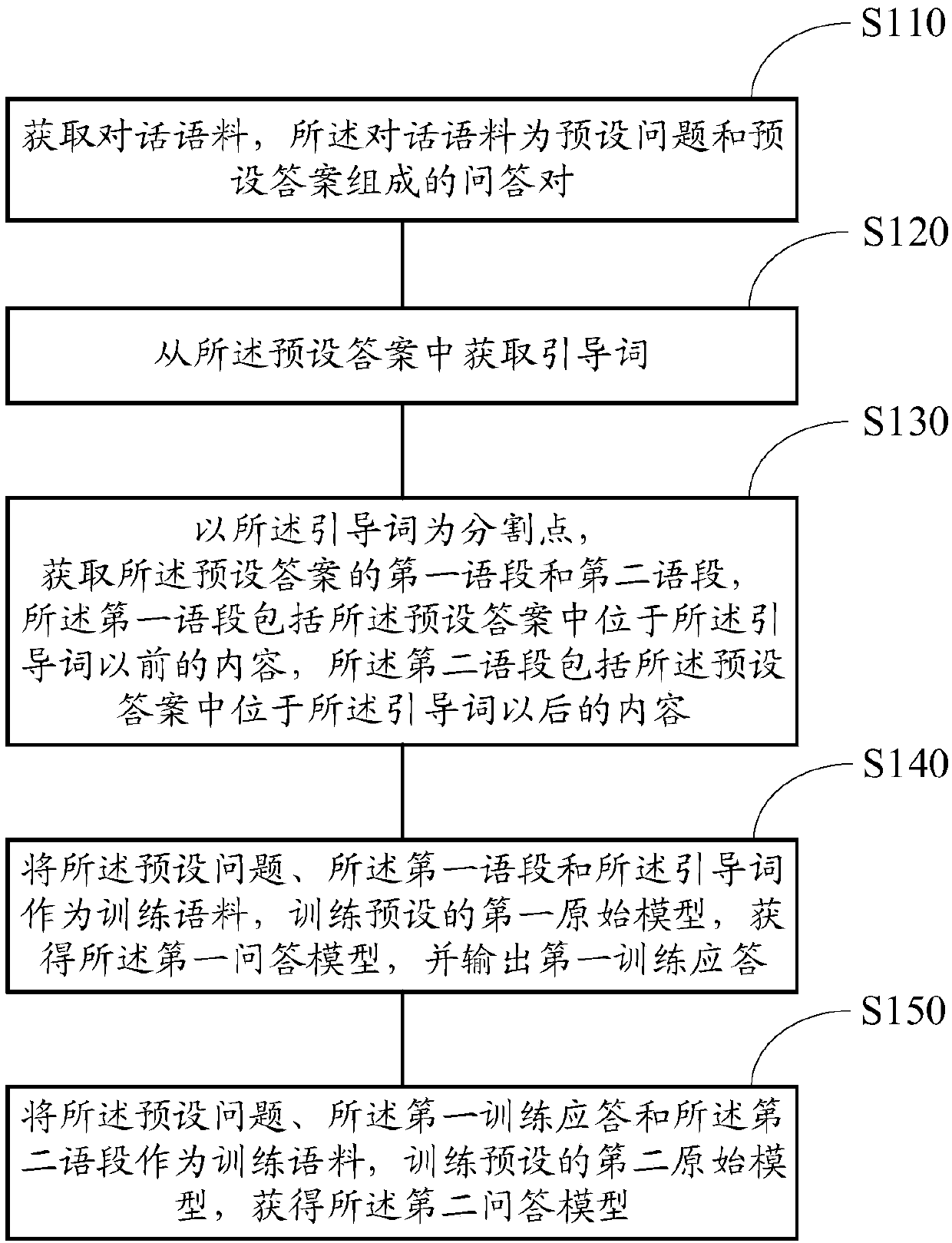
Dialogue system construction method and semantic controlled response method and device
ActiveCN107798140AHigh semantic relevanceSpecial data processing applicationsDialog systemResponse method
The invention provides a dialogue system construction method and a semantic controlled response method and device. A dialogue system comprises a first question-answer model and a second question-answer model. When a user inputs a question, firstly, an introducer associated with question semanteme is obtained from the question; then, the first question-answer model is used for generating a first response to the question, wherein the first response comprises partial response content of the dialogue system to the question; then, the second question-answer model is used for generating a second response to the question, wherein the second response comprises all responses of the dialogue system to the question. The introducer can control the output of a first response model and the output of a second response model, so that the semanteme of the first response and the semanteme of the second response are controlled. Therefore, by means of the semantic controlled response method, the semanticassociation degree of the responses generated for unknown questions and the questions is high; in addition, along with the change of the introducer, the responses generated for the unknown questions can also be changed, so that the diversity of the question responses is improved.
Owner:ZHONGKE DINGFU BEIJING TECH DEV
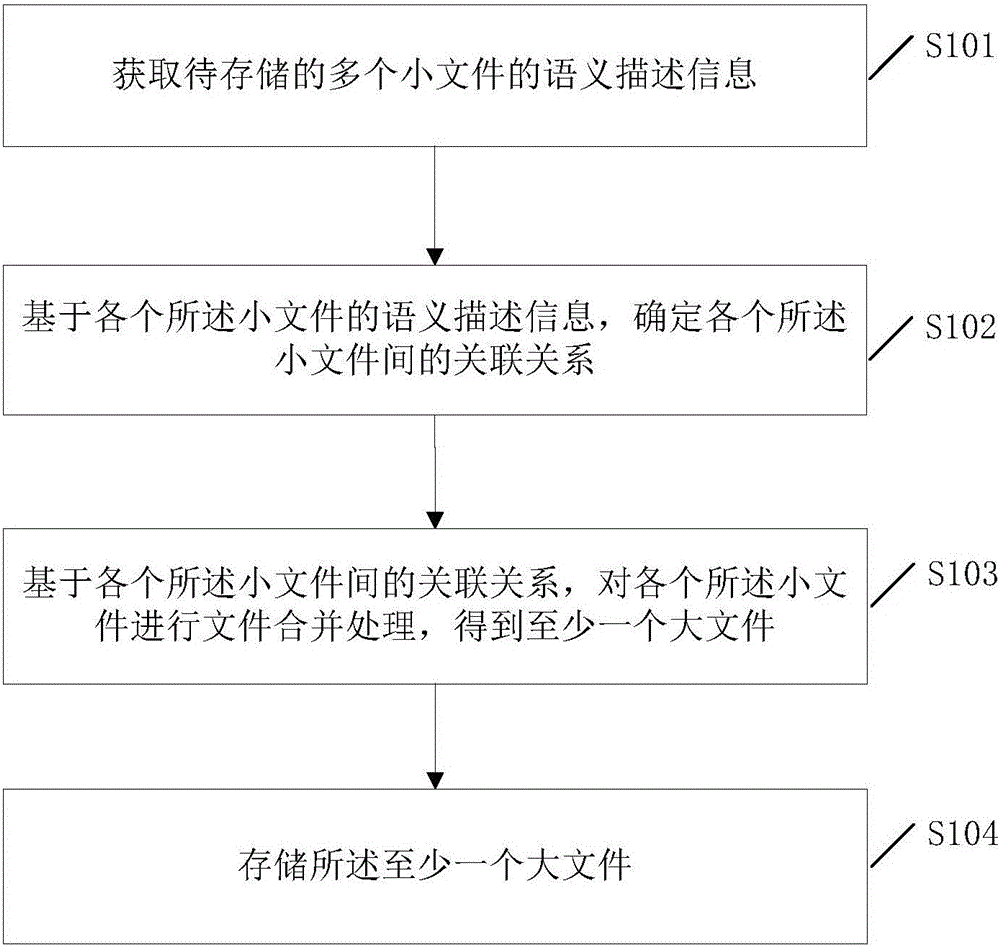
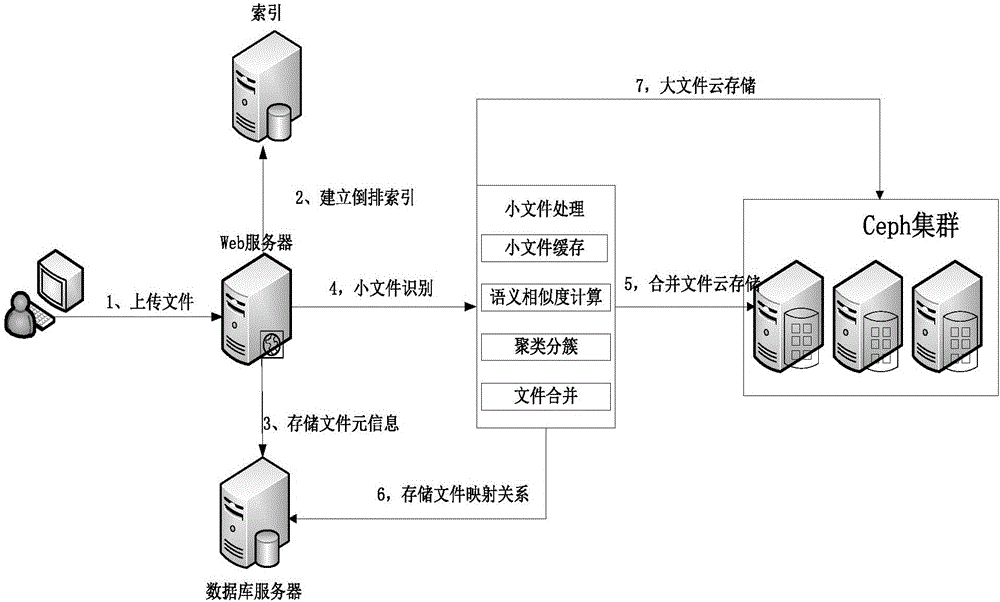
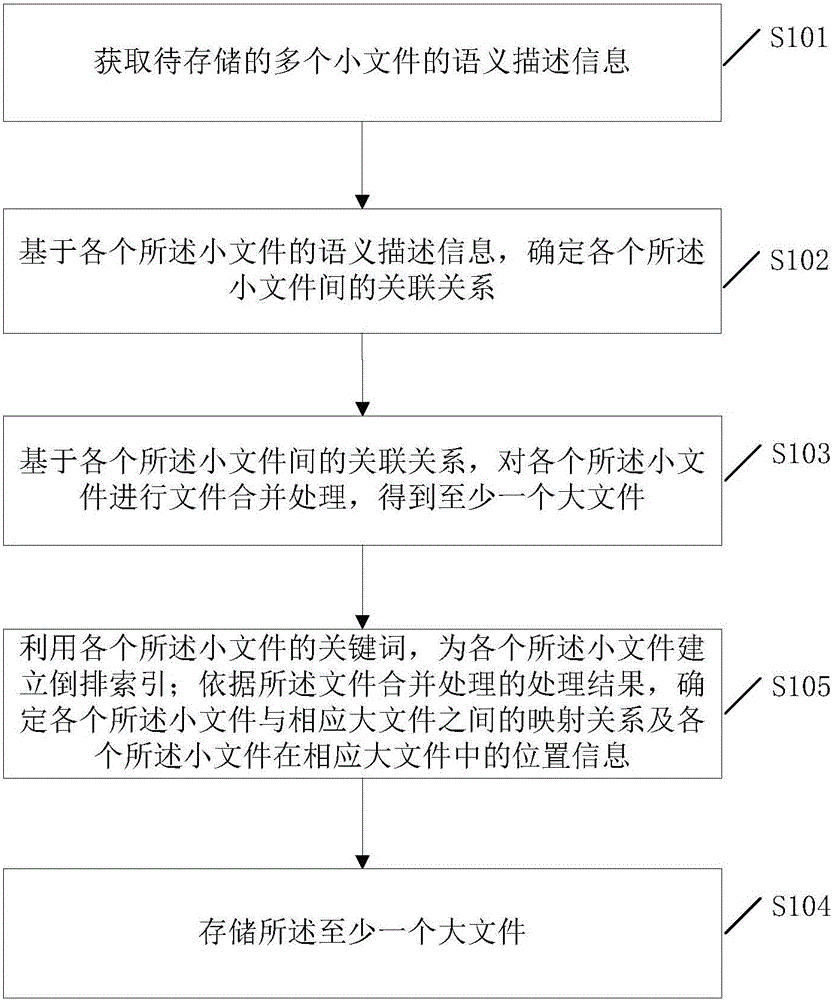
Small file storing method and system
InactiveCN105843841ARealize the mergerImprove reading efficiencyRelational databasesSpecial data processing applicationsSmall filesSemantic association
The invention discloses a small file storing method and system. According to the invention, association relations among all small files are determined based on semantic description information of each to-be-stored small file. On this basis, merging and storing of each to-be-stored small file are achieved based on the determined association relations among all small files. Thus, the invention provides a small file merging and storing strategy based on a semantic association angle and by applying the small file storing method and system, closely associated small files can be merged, thereby effectively increasing reading efficiency of the small files.
Owner:QINGDAO TECHNOLOGICAL UNIVERSITY
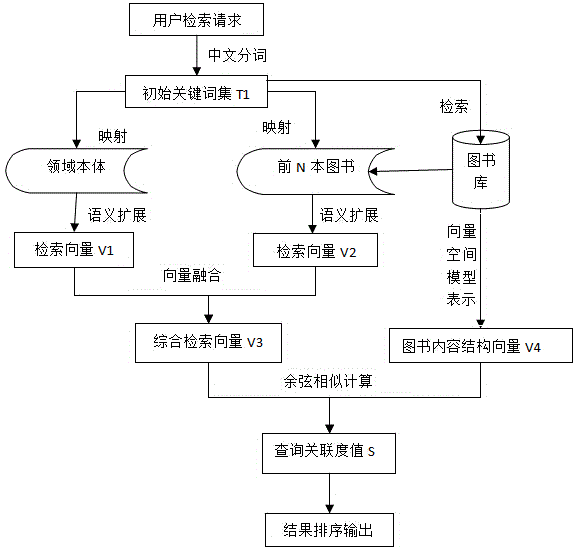
Book semantic retrieval method based on content structures
ActiveCN105117487AFully understand the query intentImprove mechanical fitWeb data indexingSpecial data processing applicationsUser inputSemantic search
The invention provides a semantic association retrieval method based on book content structures. In consideration of the difference of contribution degrees of the theme name, catalogue and abstract of a book to the main content of the book and the difference of importance degrees of the chapter titles and section titles of the catalogue in reflecting the content of the book, the book content structures, including the book title, the catalogue structure and the abstract structure, are subjected to Chinese word segmentation and stop word removal processing through a domain dictionary and subjected to synonym expansion through domain ontology to obtain a group of keywords, different weights are given to the keywords in different structures of the book, and the book content with the structure weights is stored through a vector space model. Semantic association expansion is performed on a query word input by a user through the domain ontology, and the similarity between a user retrieval intention vector and a book content structure vector is calculated to more accurately acquire a book most associated with user query content. The method increases the recall ratio and the precision ratio and improves mechanical keyword matching in book retrieval in the prior art.
Owner:杭州淘艺数据技术有限公司
Semantic associations in data
InactiveUS20120179680A1Improving searching possibilityRaise the possibilityDigital data information retrievalDigital data processing detailsComputing systemsDatabase
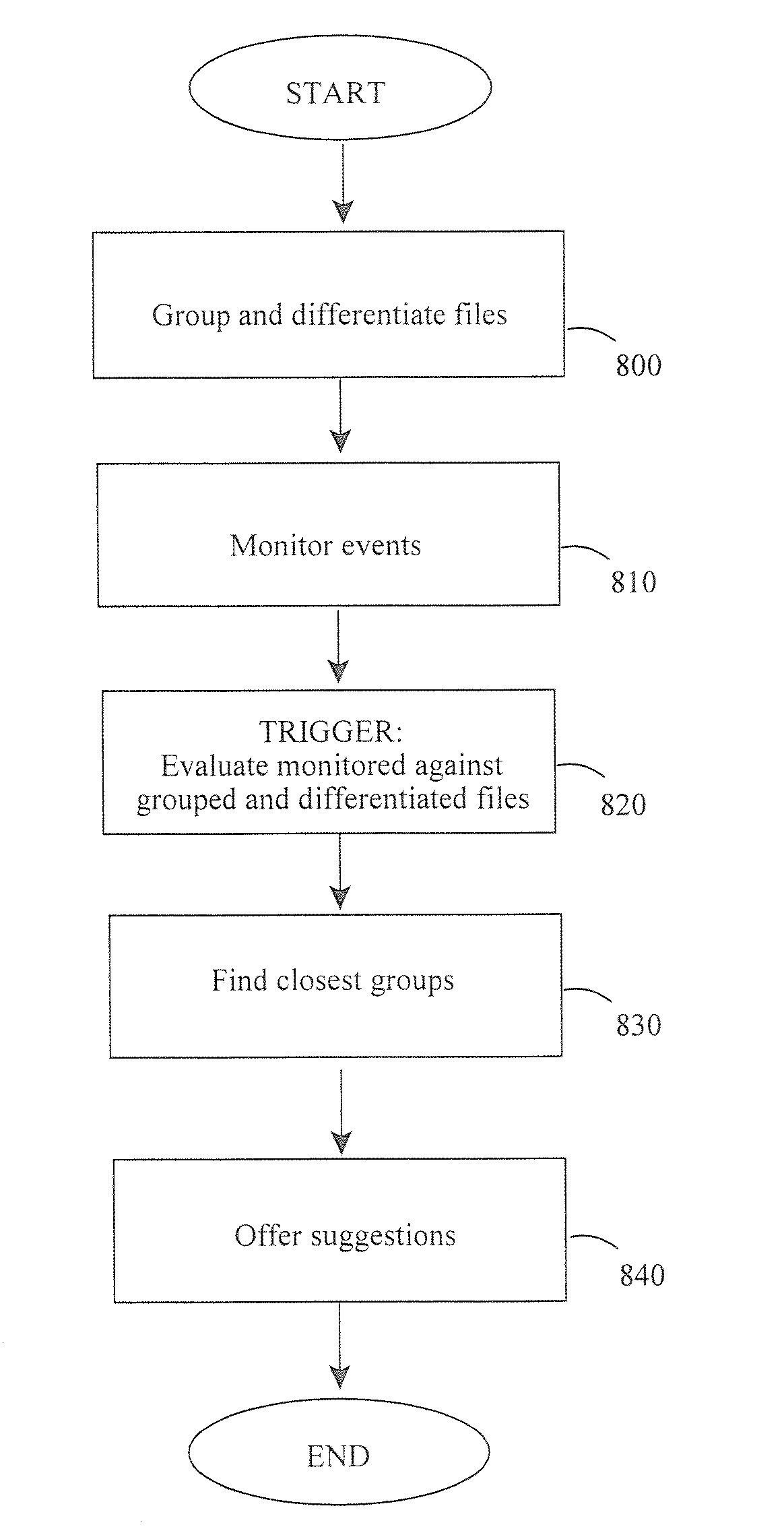
Methods and apparatus teach providing semantic associations between data available on one or more computing devices, including grouping together related files and creating an association between the related grouped files and at least one anchor file to provide a semantic association for the grouped files. Also is taught configuring an agent on the one or more computing devices to undertake the grouping and to create the association without a user request. Also is taught triggering an evaluation of current files against related grouped files, and creating an association between the current files and at least one of the related grouped files and the at least one anchor file. Information may be added to the created association to create additional semantic associations for one or more of the grouped files and the current files. In turn, computer program products and computing systems for accomplishing the foregoing are provided.
Owner:MICRO FOCUS SOFTWARE INC
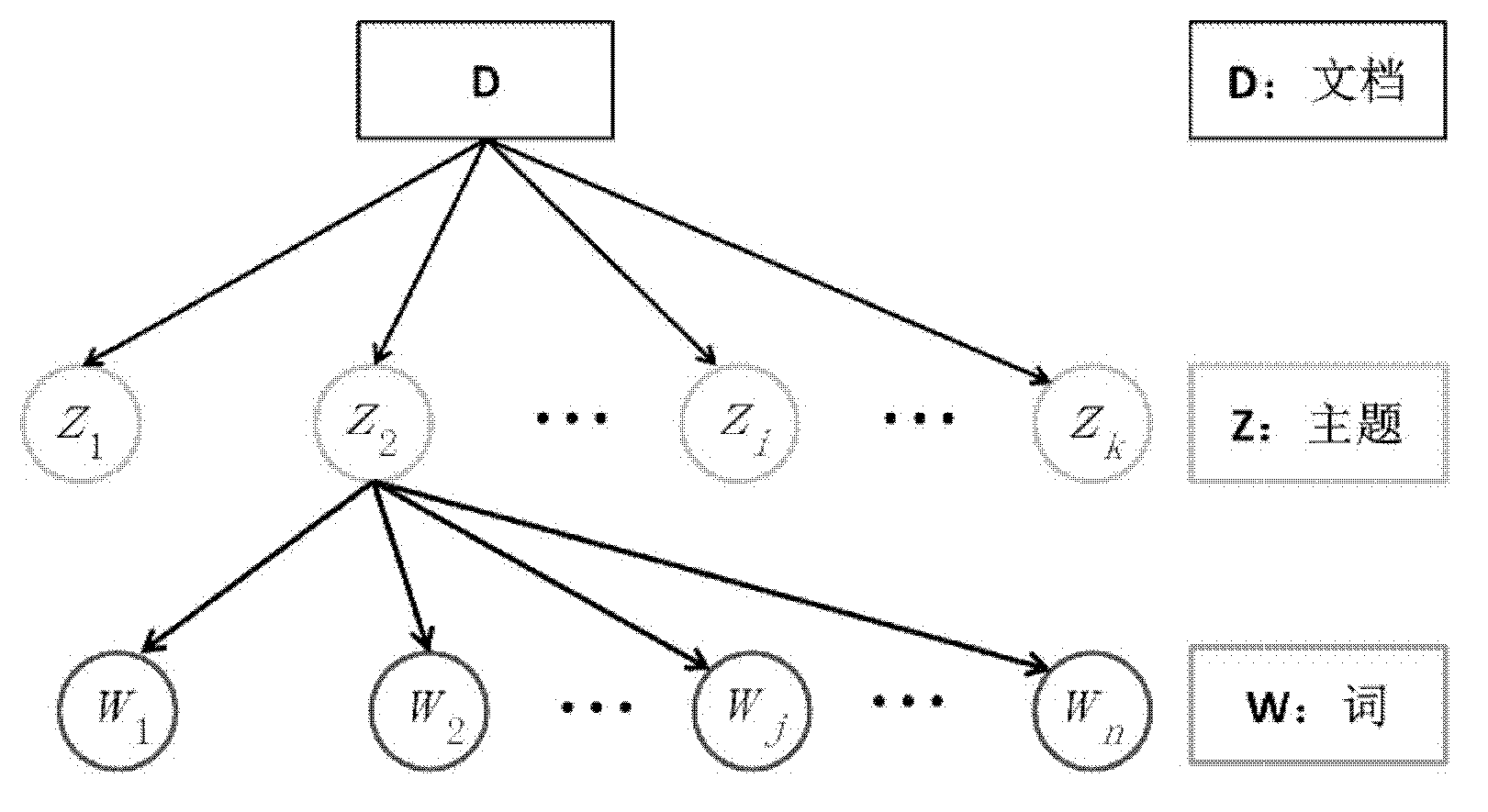
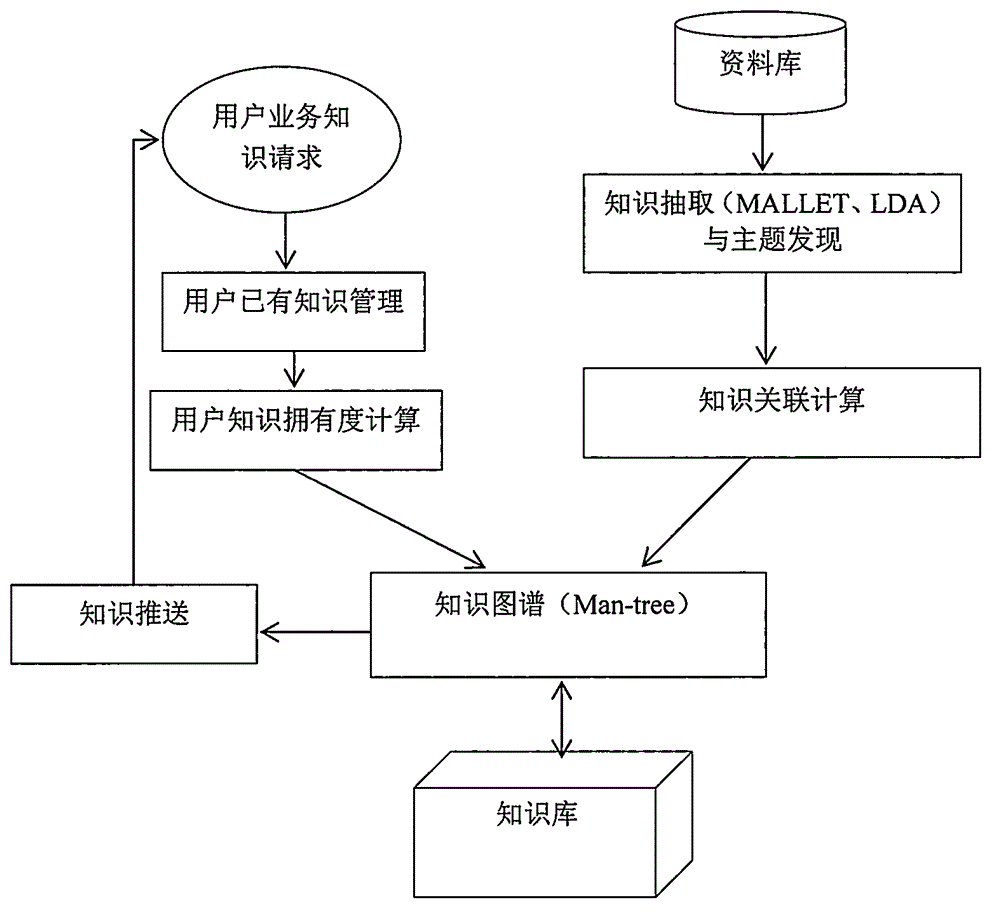
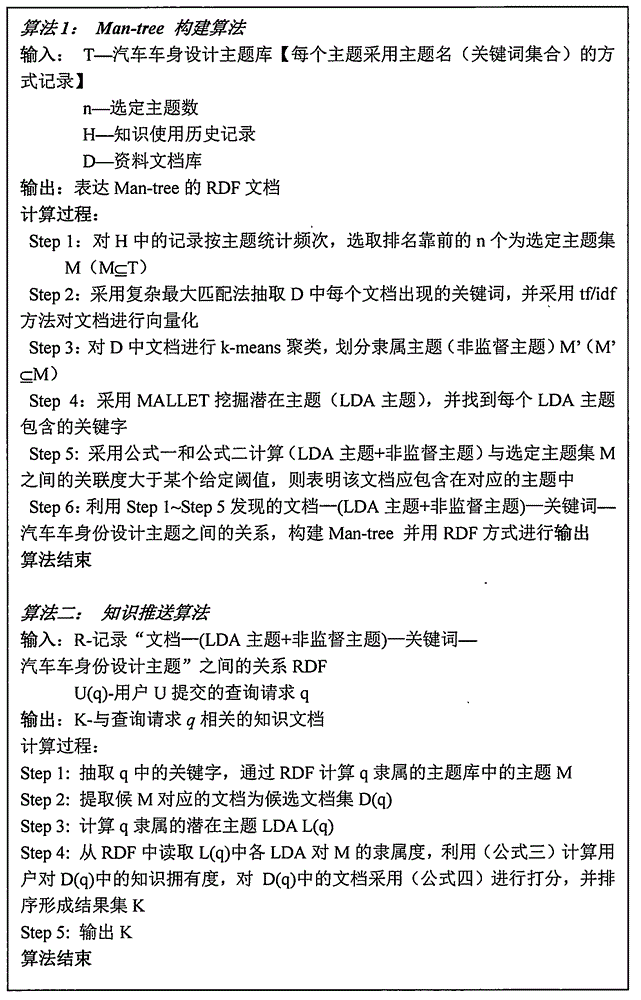
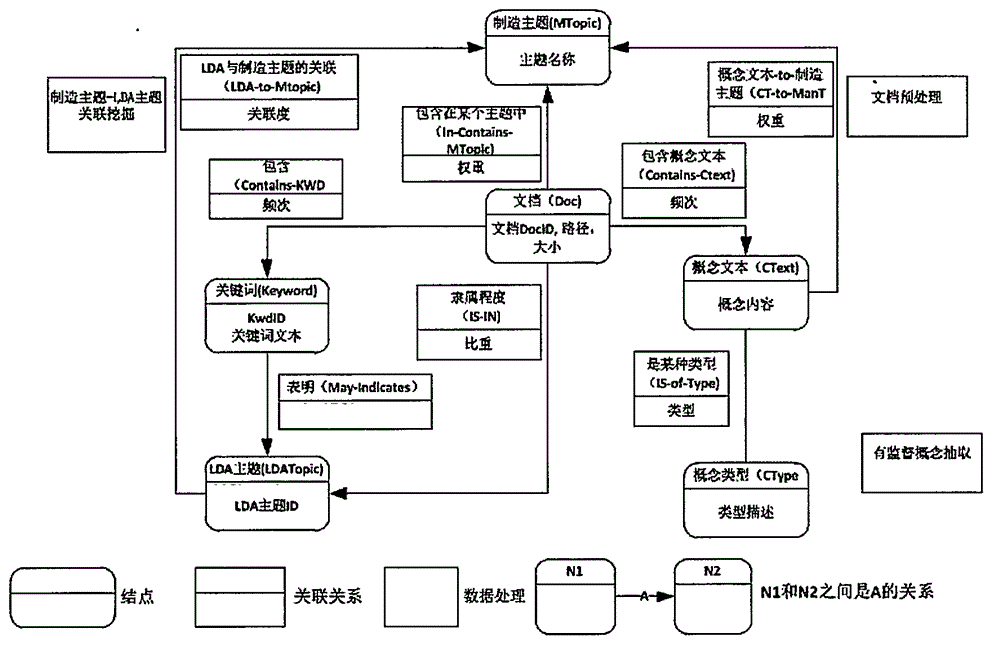
Manufacturing design knowledge individualized pushing method based on knowledge graph (Man-tree)
InactiveCN106156090AGood answerProof of feasibilitySpecial data processing applicationsPersonalizationKnowledge modelling
The invention belongs to the technical field of knowledge management and knowledge pushing oriented to manufacturing enterprises, particularly relates to a novel and efficient knowledge management and knowledge pushing method based on a knowledge graph and discloses a knowledge pushing method based on a manufacturing design knowledge graph structure (Man-tree). By means of the method, the comprehensiveness and accuracy of enterprise knowledge pushing can be effectively improved. The knowledge pushing method comprises the step that a knowledge modeling module, a knowledge extracting and subject discovering module, a knowledge graph Man-tree establishing module, a user knowledge possess degree calculation module and a knowledge pushing module are established by introducing an LDA method. By quantitatively evaluating the degree of the knowledge processed by a user, the knowledge graph is expanded, and semantic association between knowledge and the user is established. According to the specific technology, formation of a database, extraction of knowledge, discovery of knowledge association, knowledge storage design, and a quantitative calculating method for the degree of the knowledge processed by a user are included. The novel method for knowledge pushing in the manufacturing design field is given on the basis that the manufacturing design graph is proposed.
Owner:上海宽文是风软件有限公司