Patents
Literature
224results about How to "View accurately" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
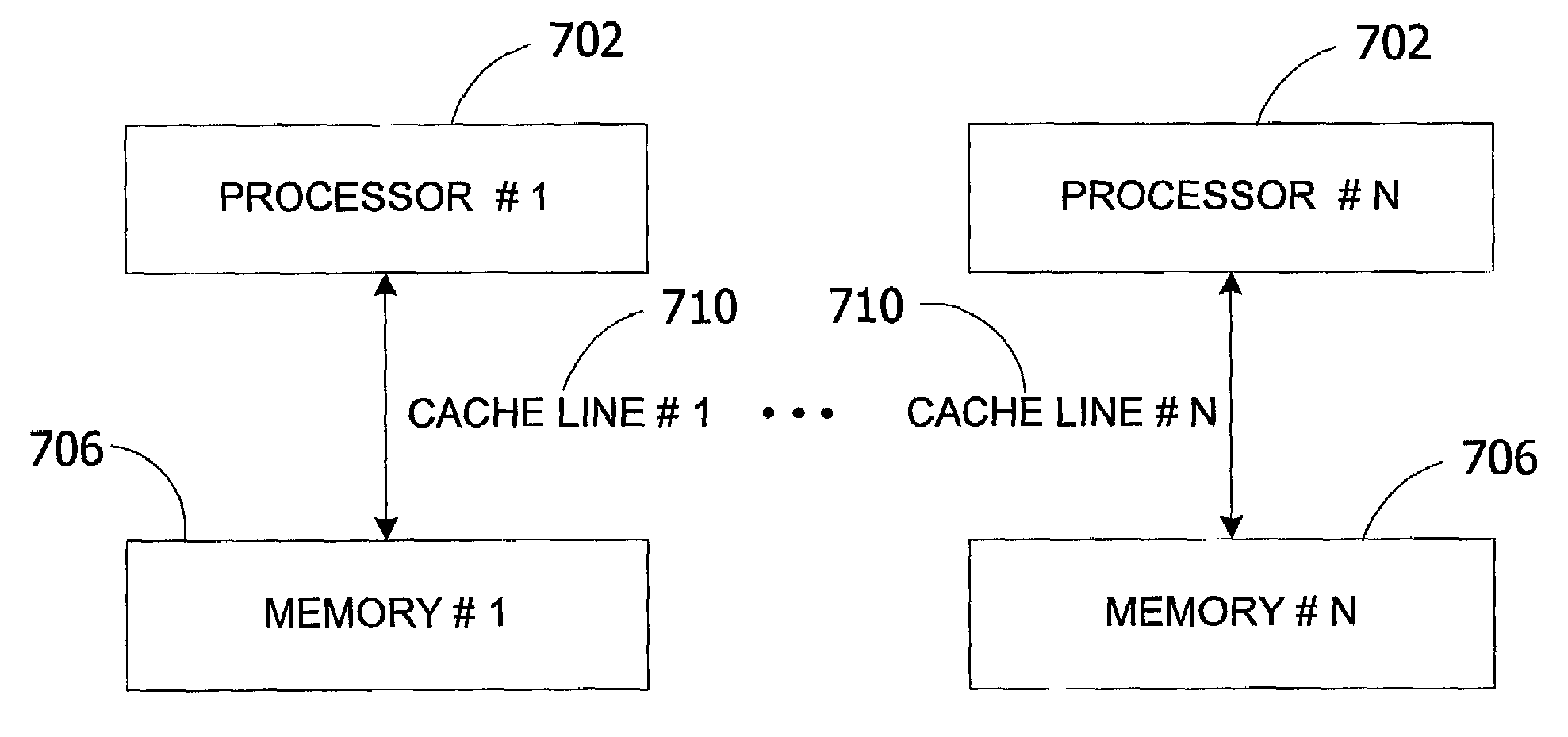
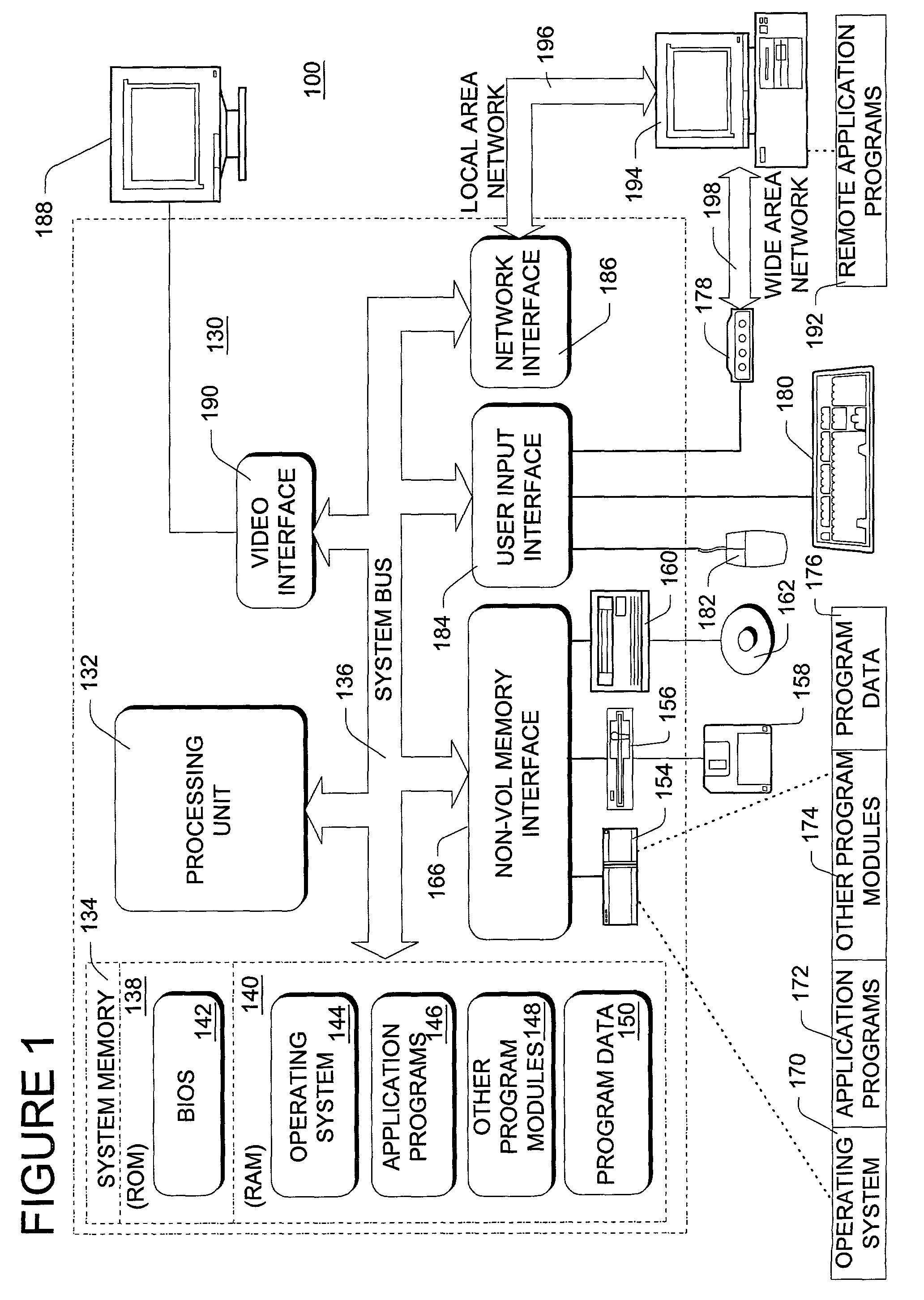
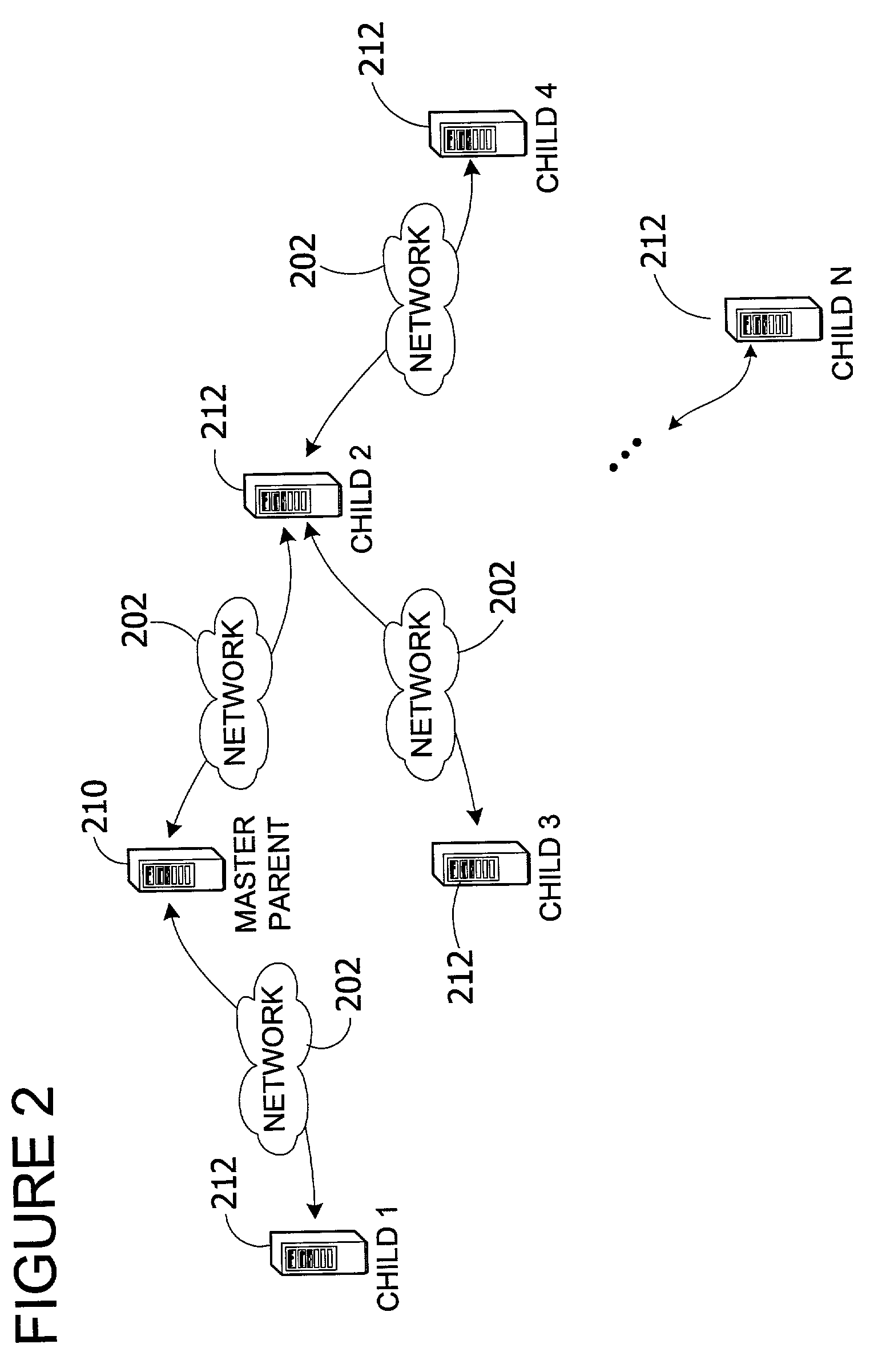
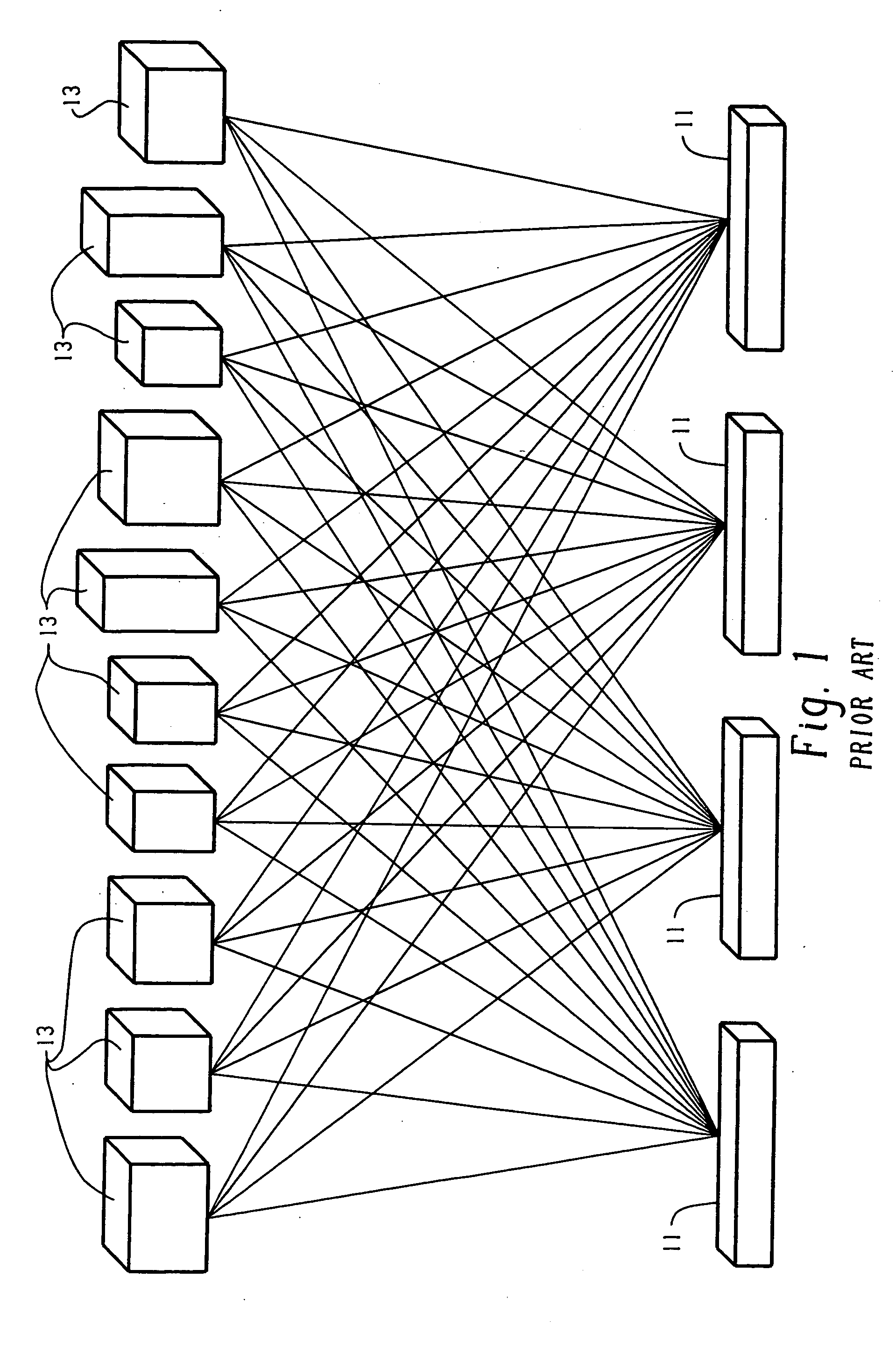
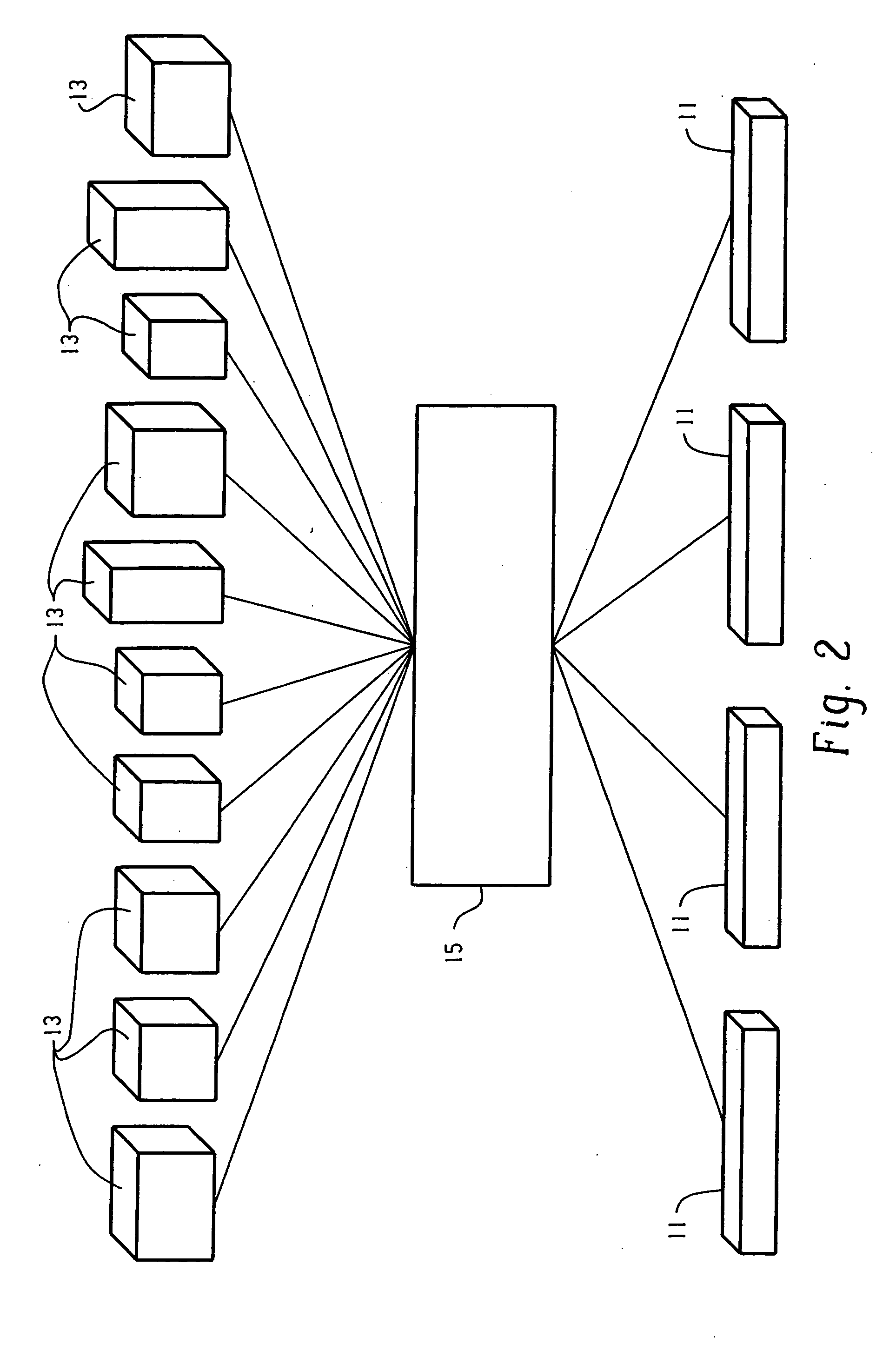
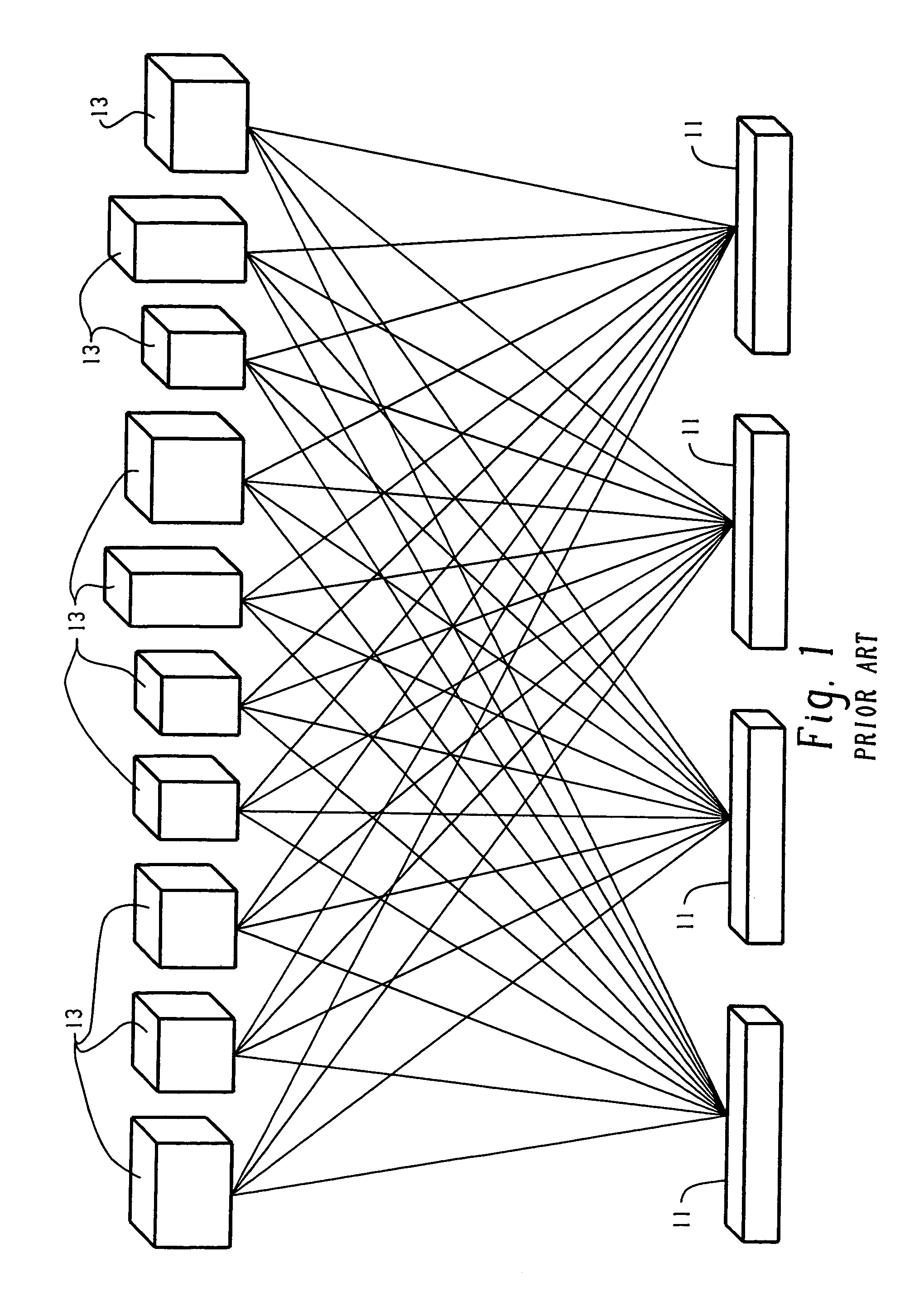
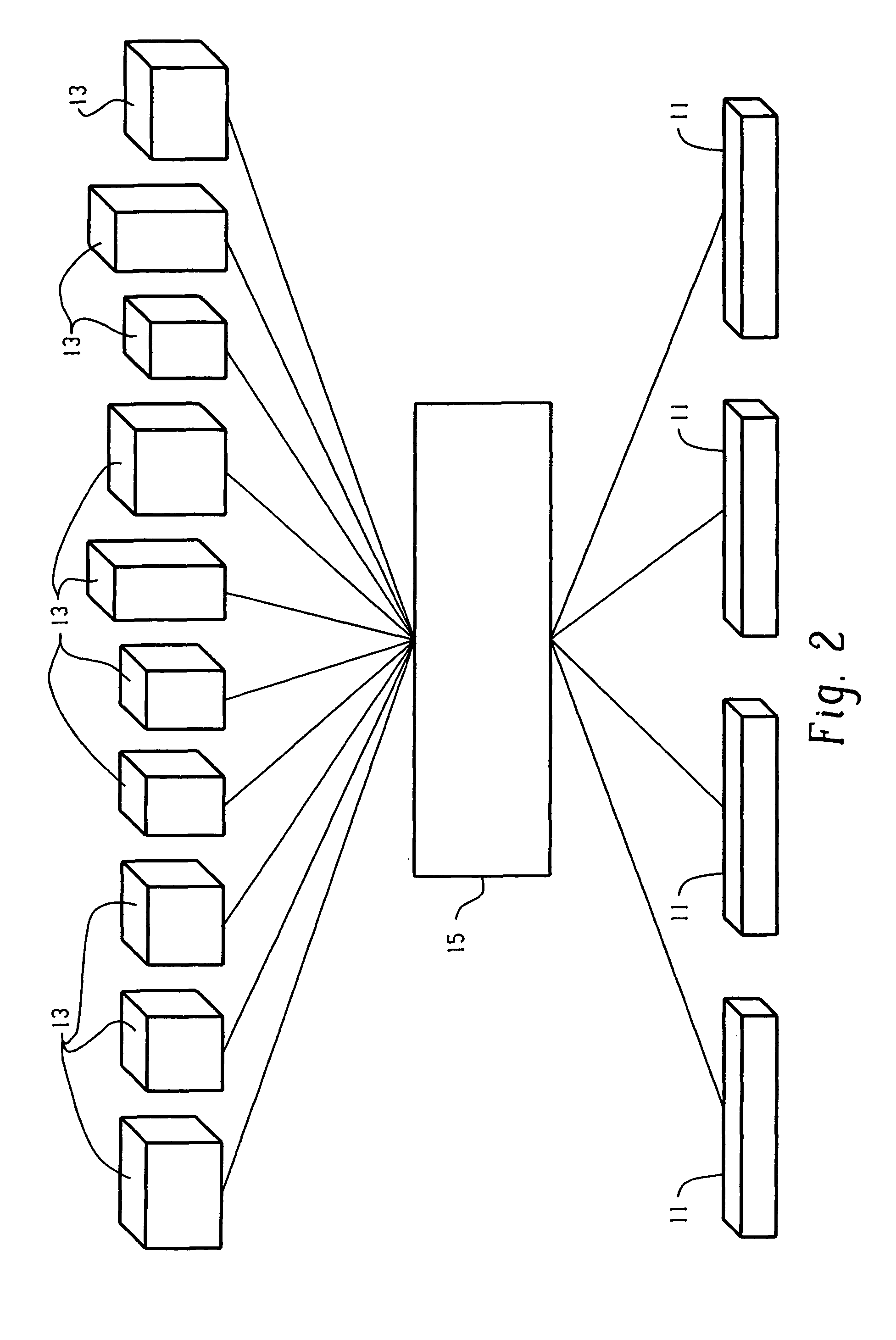
Distributed variable synchronizer
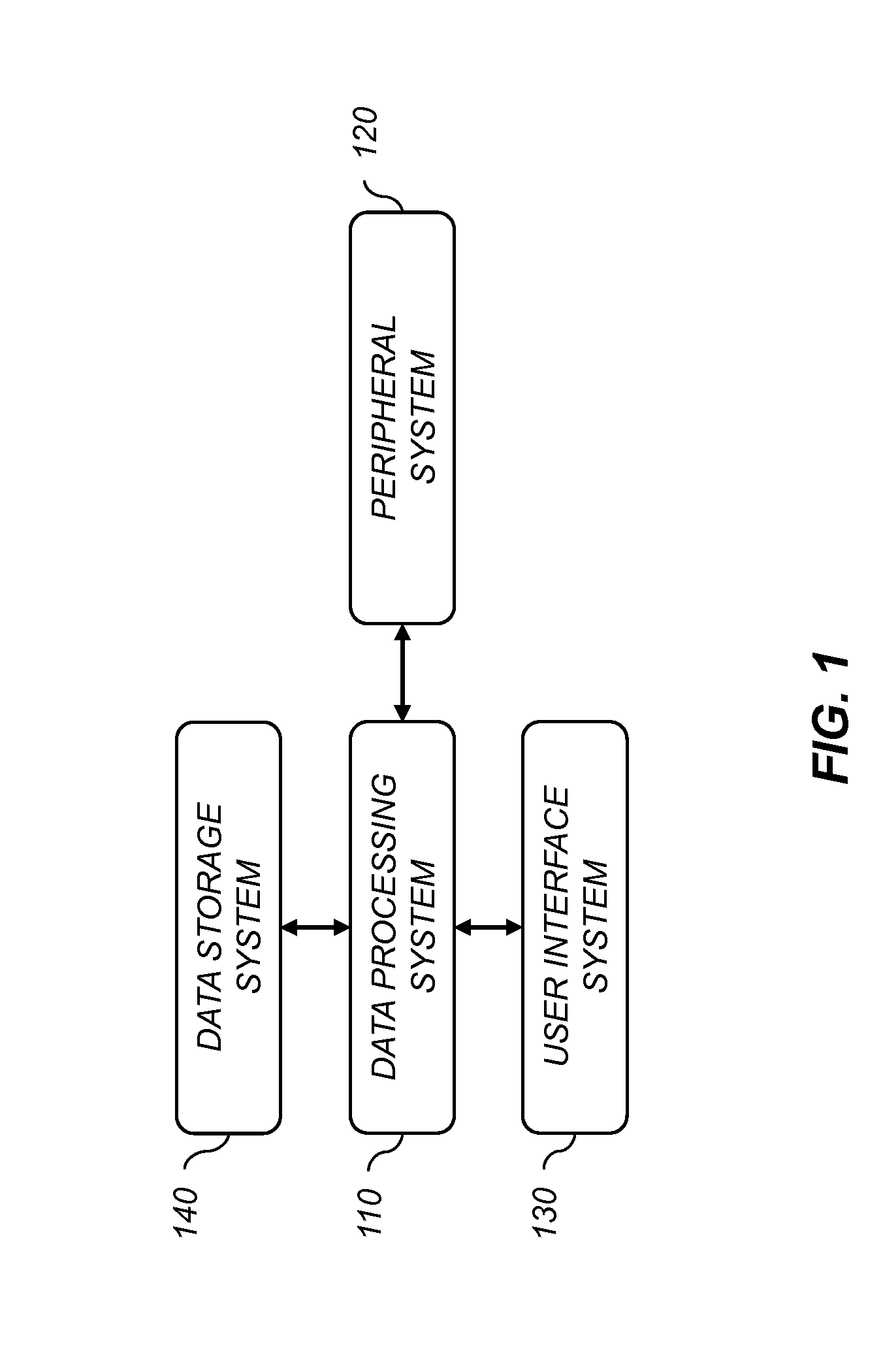
InactiveUS6968372B1Accurate global viewMinimizing applicationMultiple digital computer combinationsTransmissionMessage passing
A system and method of synchronizing at least one variable such as a counter among a network of distributed computers where the computers communicate via asynchronous message passing. The distributed computers are organized as nodes in a tree. Each computer in the tree is capable of functioning as a parent, child, or both. For each variable to be synchronized, each parent receives a contribution from a child which includes contributions from any children of the child and returns other contributing values to the child. The child then updates the local value of the variable with the returned contributing values. The returned contributing values include contributions to the variable from all computers in the tree other than the child and other than any children subordinate to the child in the tree. Each computer can have multiple children.
Owner:MICROSOFT TECH LICENSING LLC
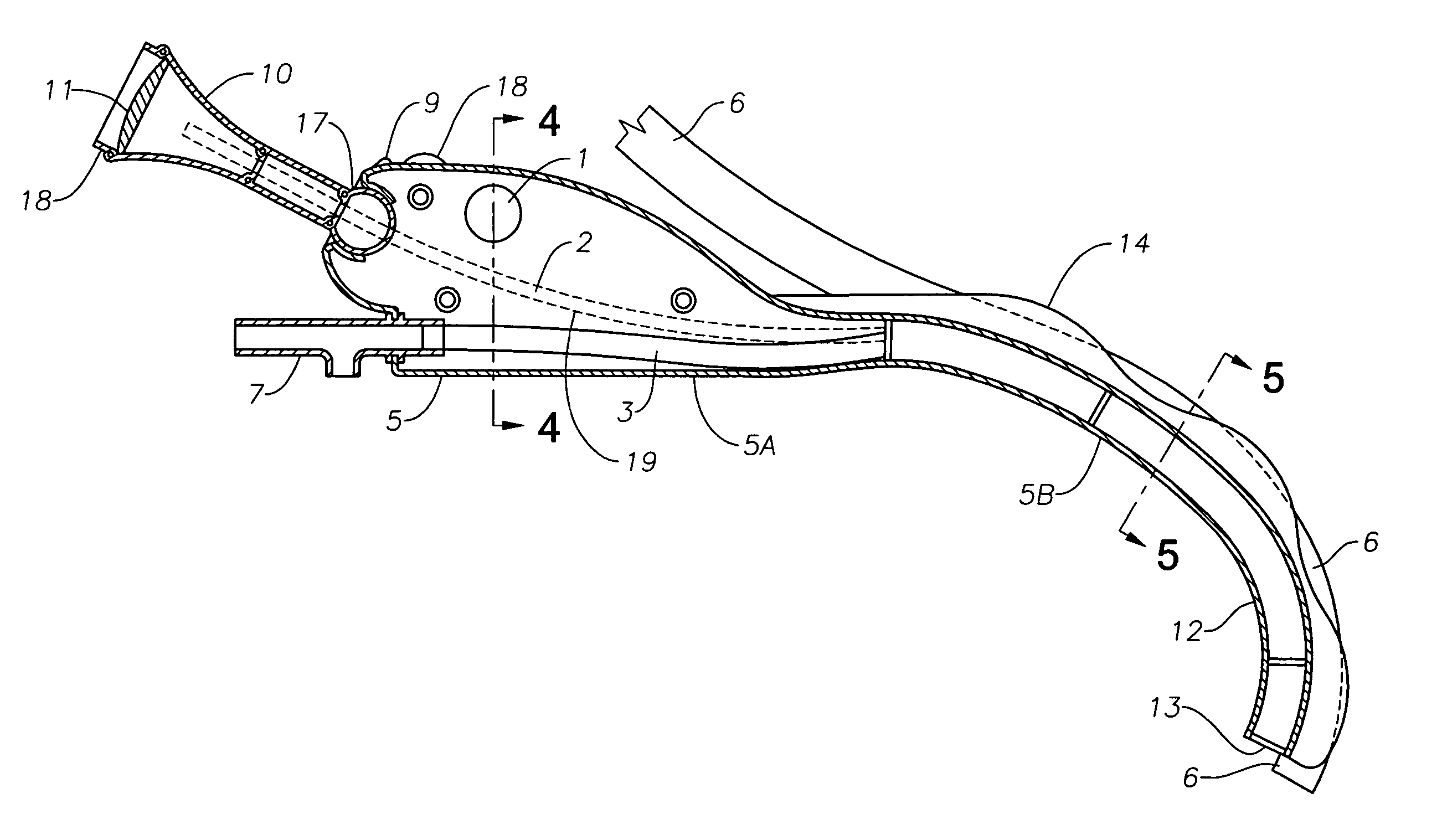
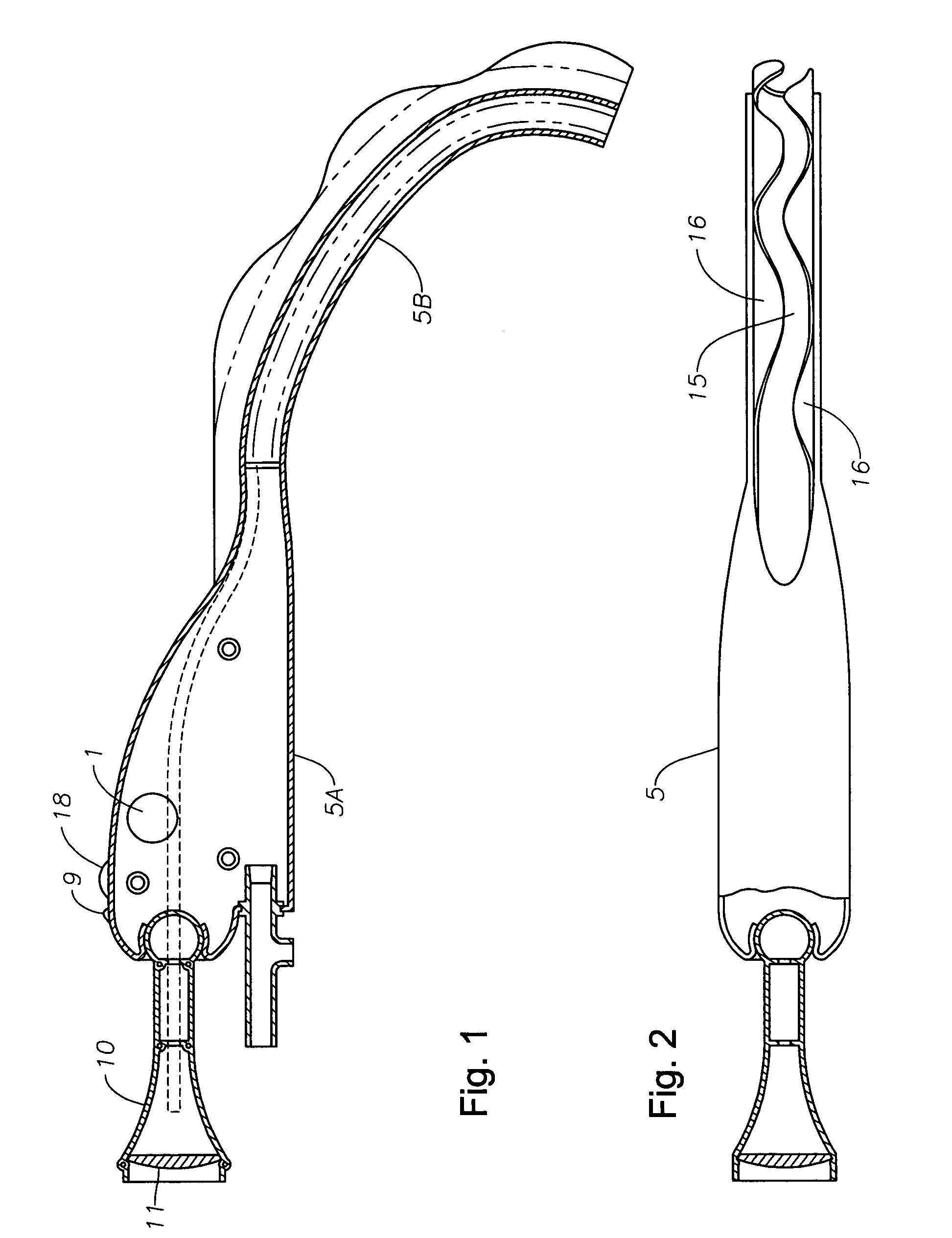
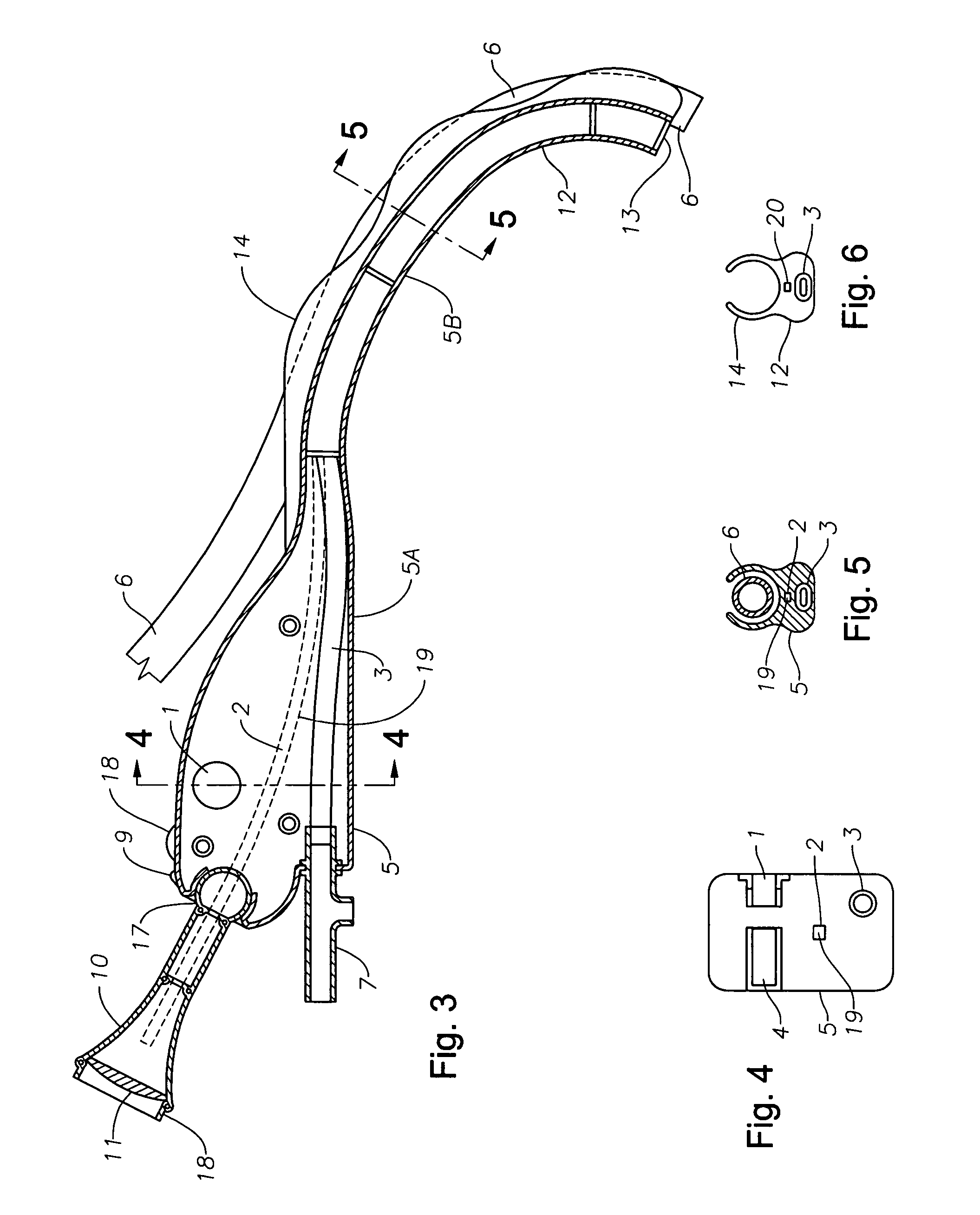
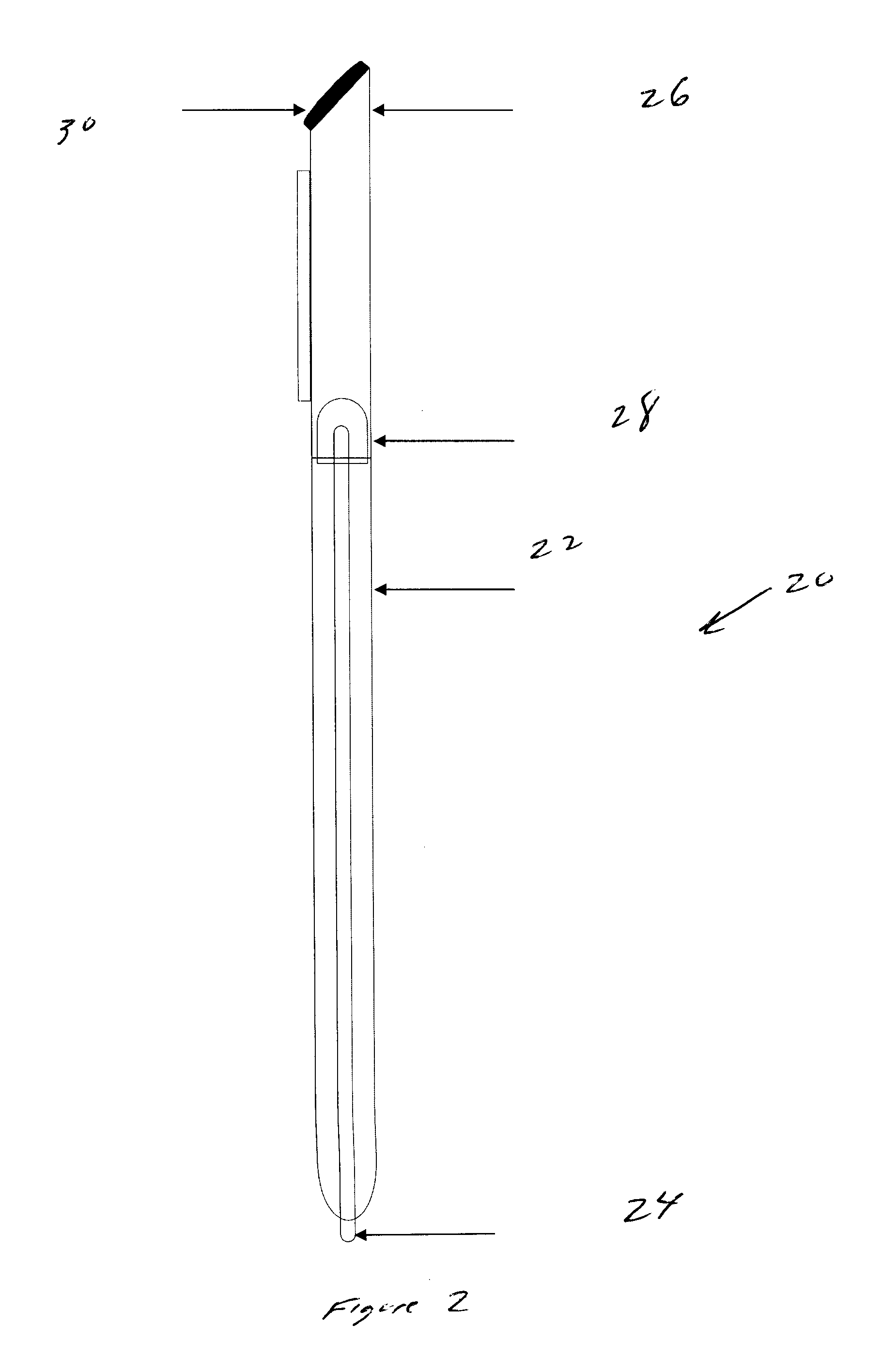
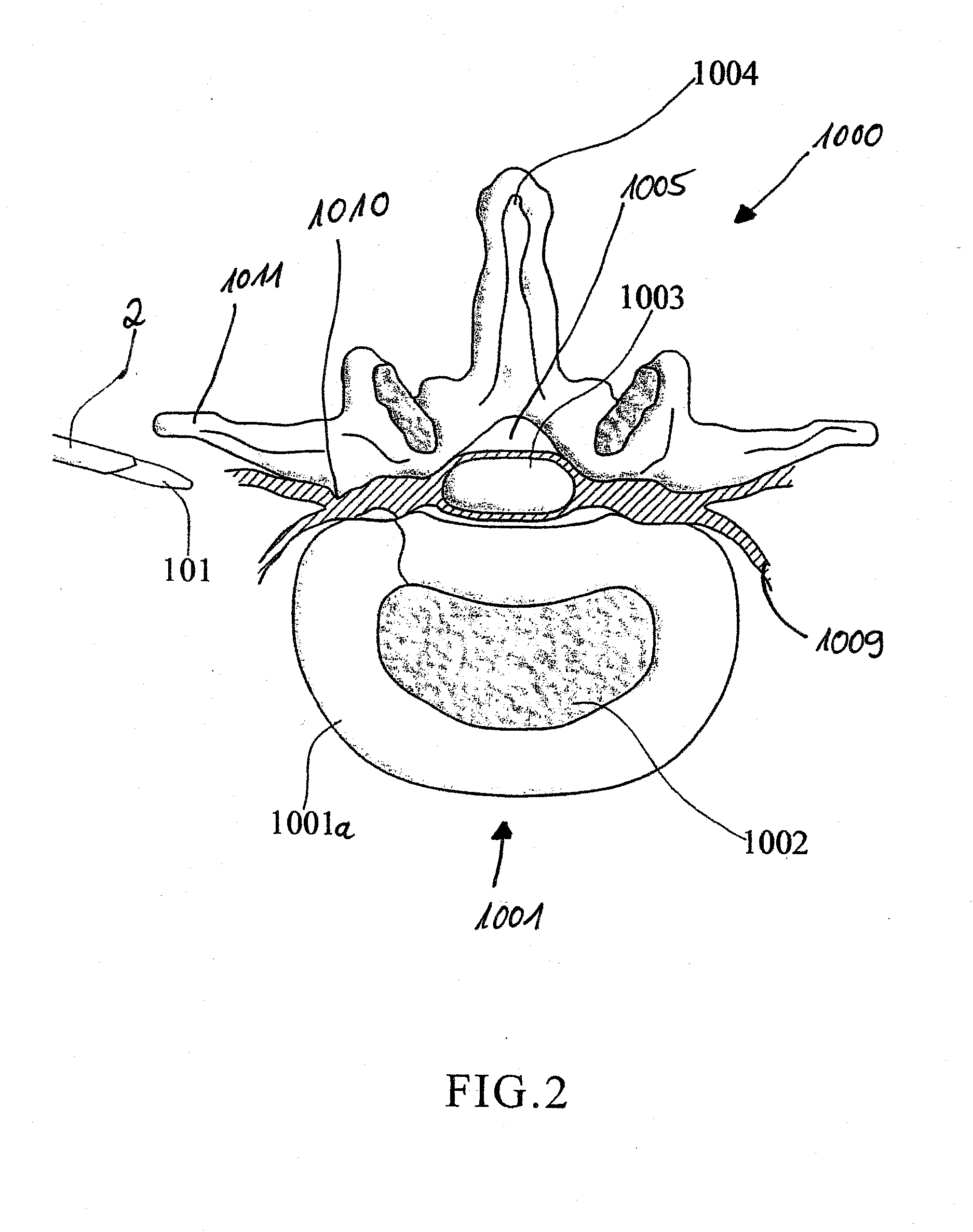
Res-Q-Scope
A multiple function laryngoscope to be used for the safe intubation of a patient's trachea during a respiratory emergency or as an elective procedure. A two section instrument. Proximally, a reusable handle that houses a rechargeable battery, electronic circuits that feed a distal digital image to variable position LCD screen or viewing port, switches and low battery indicator light. Distally, the handle electrically couples with a disposable curved scabbard. The scabbard features a dorsal endotracheal tube channel with a wavy opening which allows preloading and gentle extraction of different size endotracheal tubes once the patient's trachea has been intubated. The scabbard's distal end strategically houses a distal sweeper that engages the epiglottis and exposes the glottis, an opening for the exit of a preloaded endotracheal tube, a LED light, a suction / oxygenation port, and a lens coupled with a digital imaging system (CMOS) to digitize and transport a distant wide field of view. Safe LCD view of one or serial rapid intubations are possible by rapidly replacing for a clean disposable scabbard in case of multiple emergencies.
Owner:CUBB ANTHONY
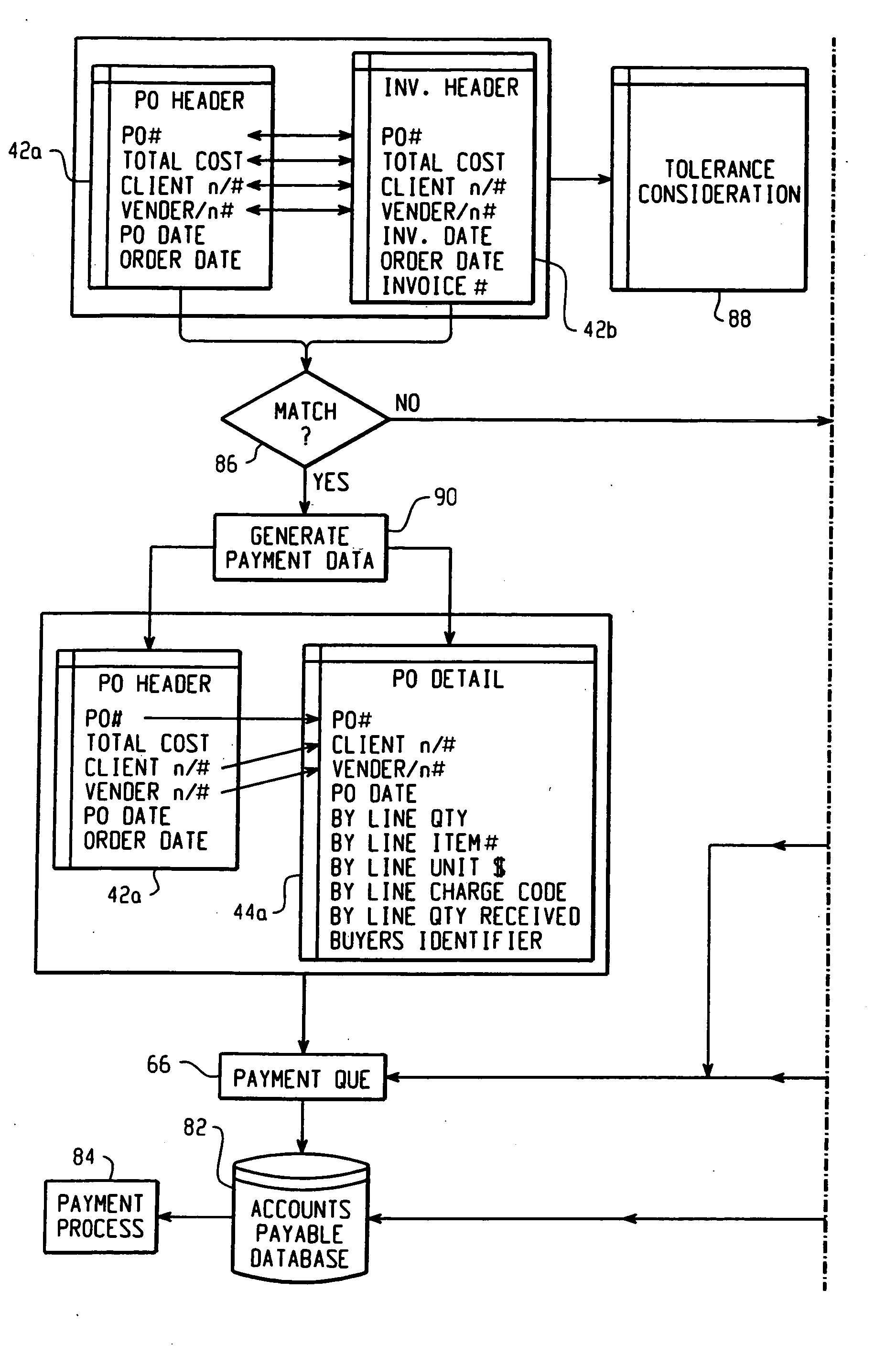
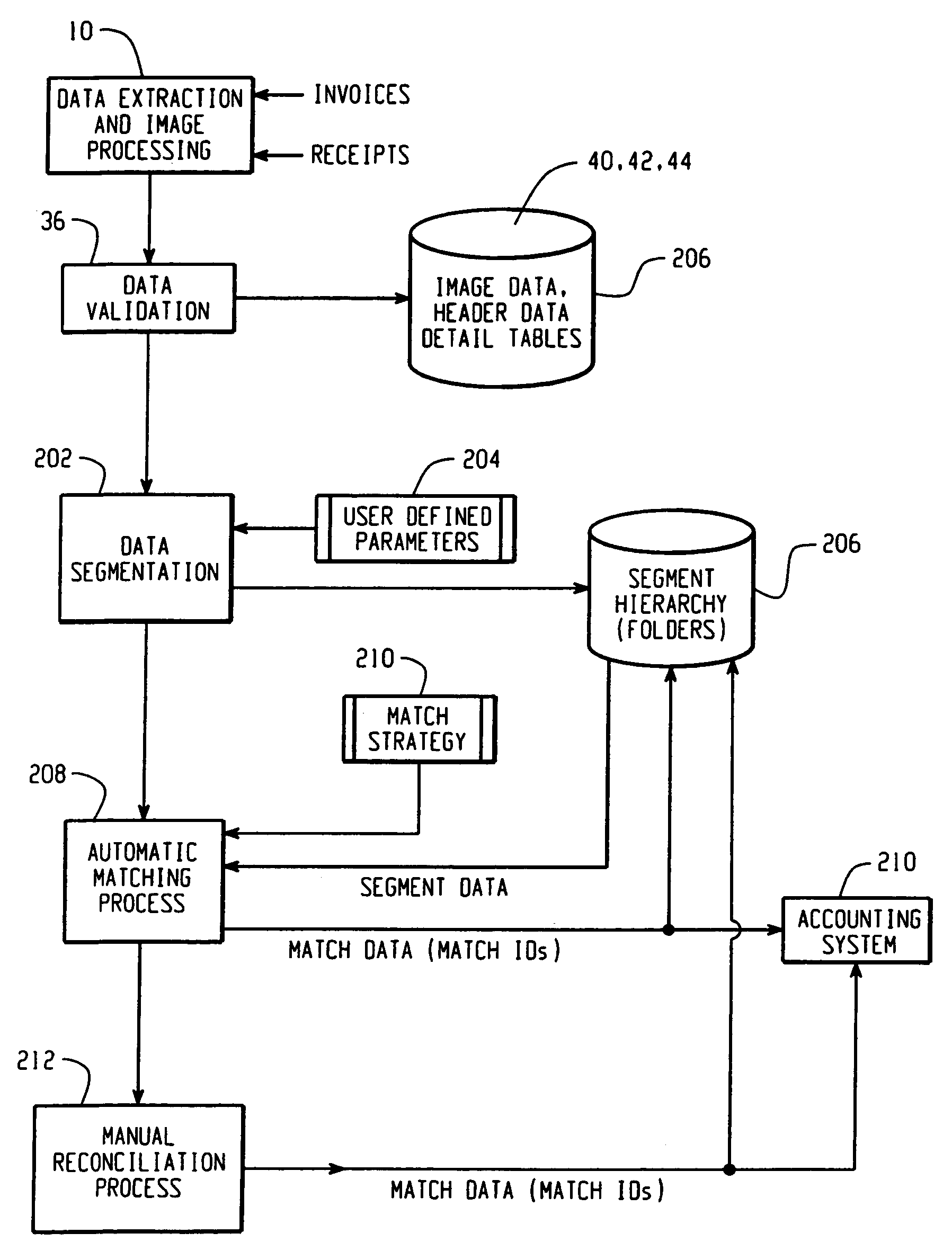
Method and system for processing transactions
A system and method is provided for processing transactions between at least one buying company and at least one selling company which results in the creation of a new collaborative data set. In one embodiment, the method comprises providing a central datastore accessible to users from the buying company and users from the selling company. Purchase order and invoice data are obtained and compared via a computer, to identify a matched record having purchase order data and corresponding invoice data. A collaborative data set in the central datastore is created, based in part on the matched record and storing in the datastore detailed settlement data regarding settlement of the matched record of purchase order data and corresponding invoice data. The method stores a complete settlement transaction history by providing for storage of additional settlement data in the central datastore, wherein credit memos, debit memos regarding the invoice, the purchase order of the matched record, and / or other documents related to the transaction are stored as part of the collaborative data set.
Owner:ORACLE INT CORP
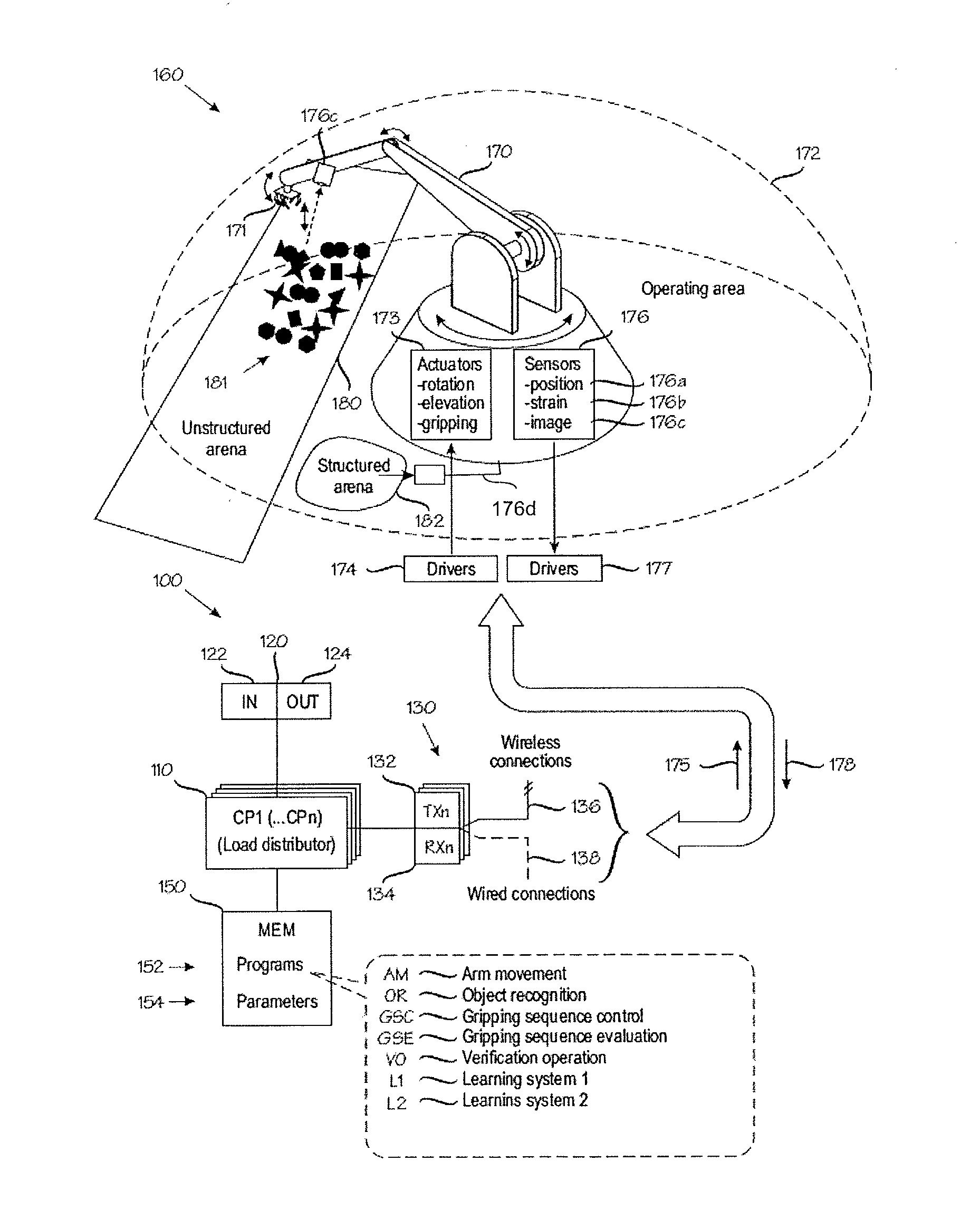
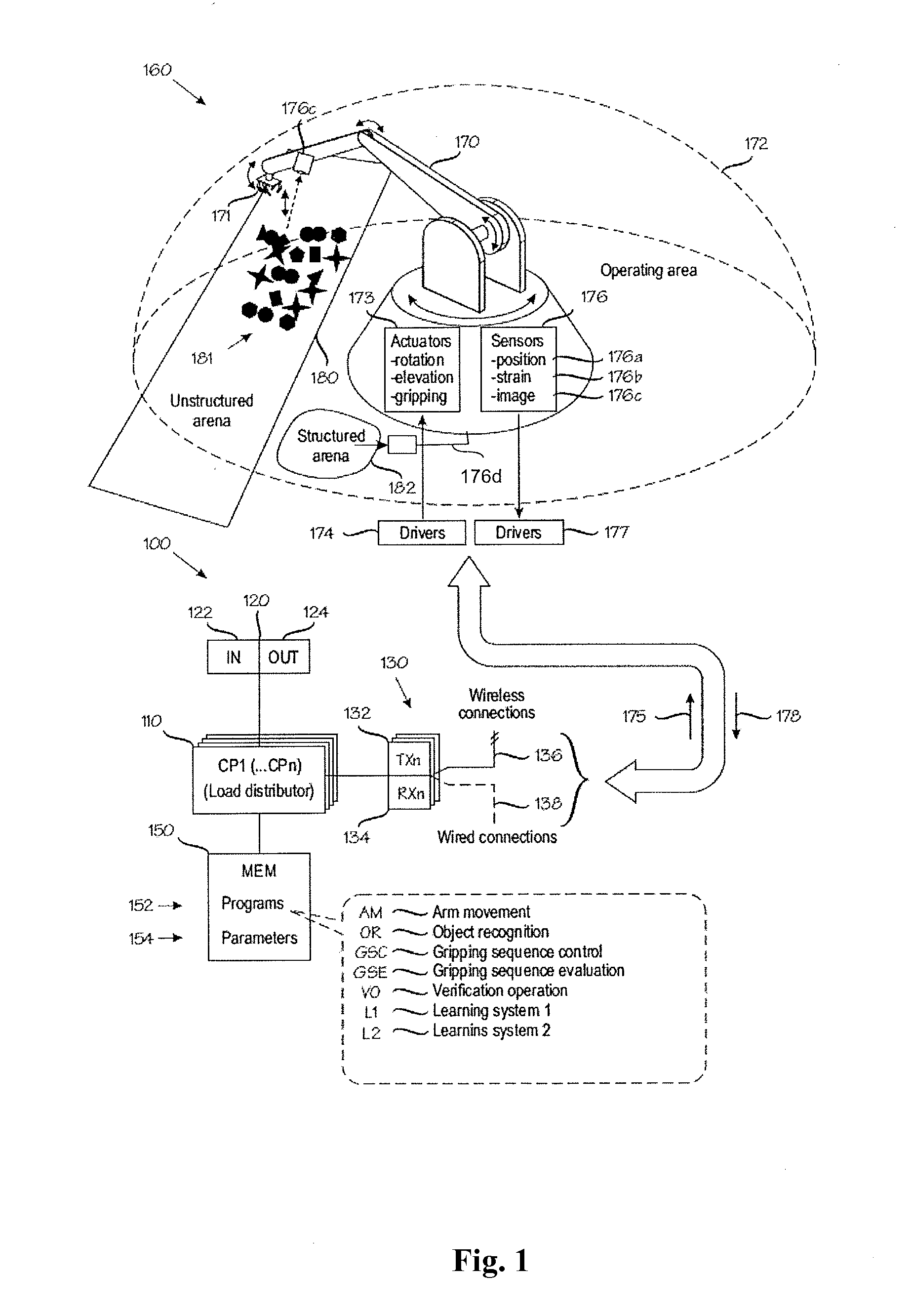
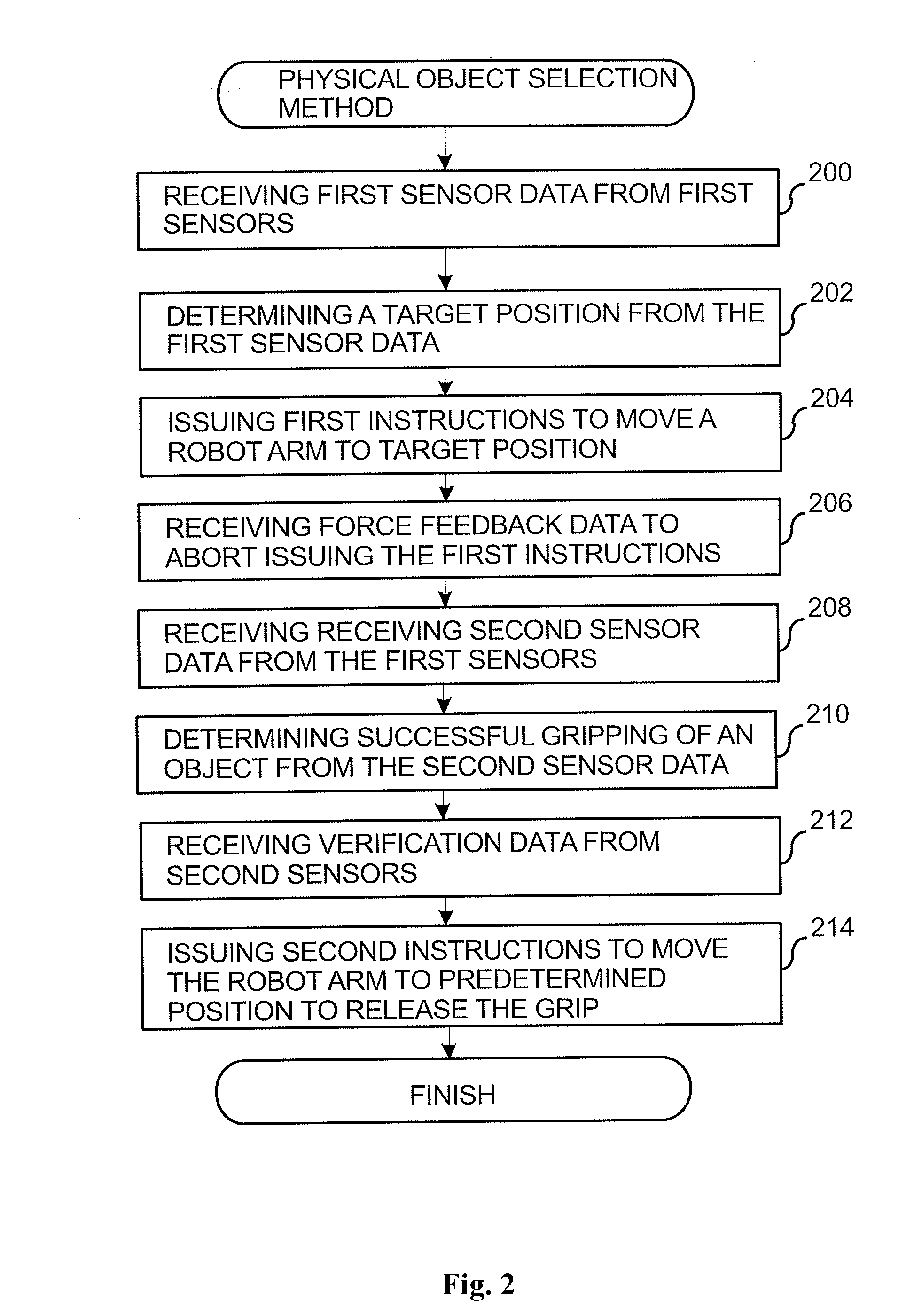
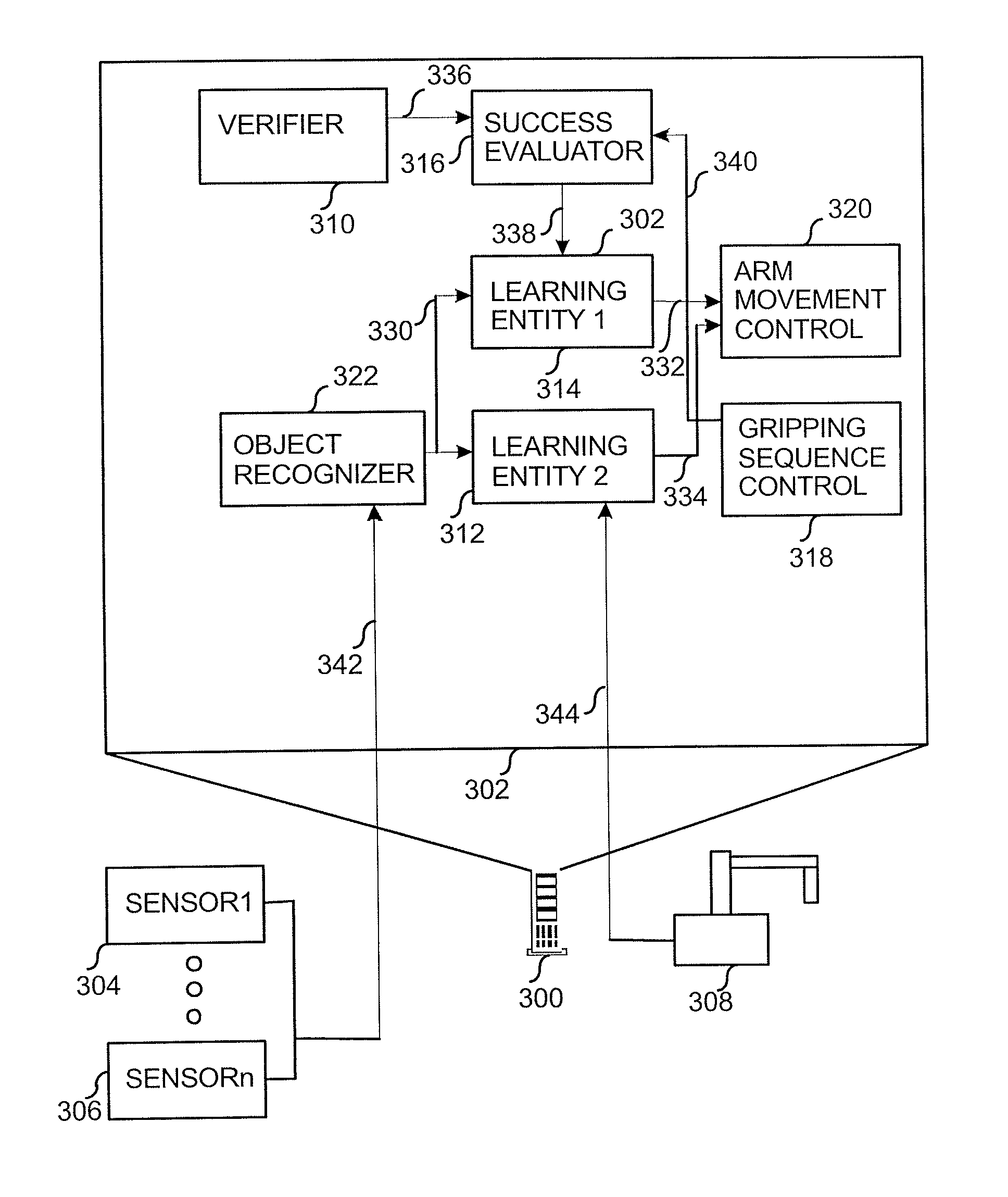
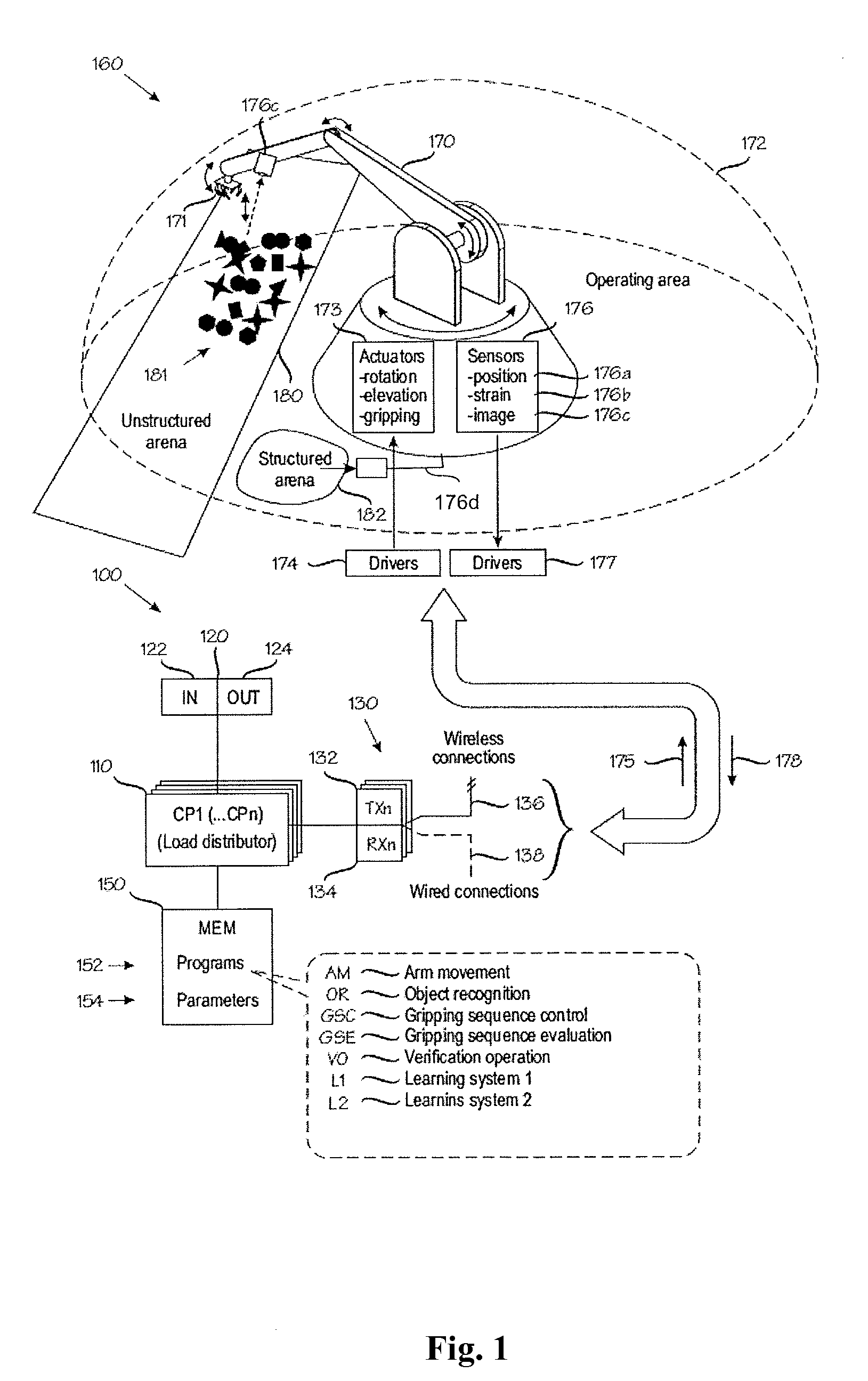
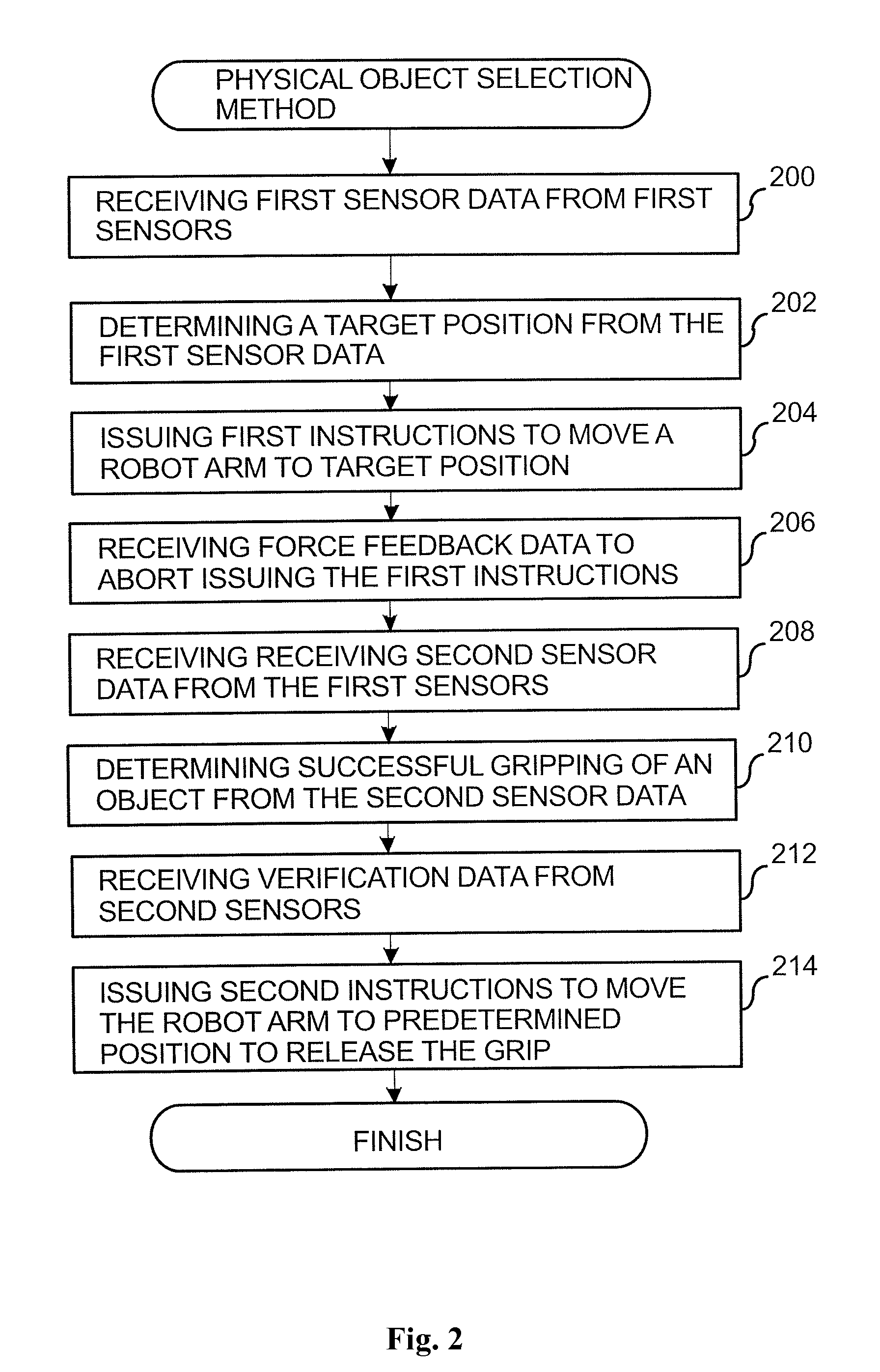
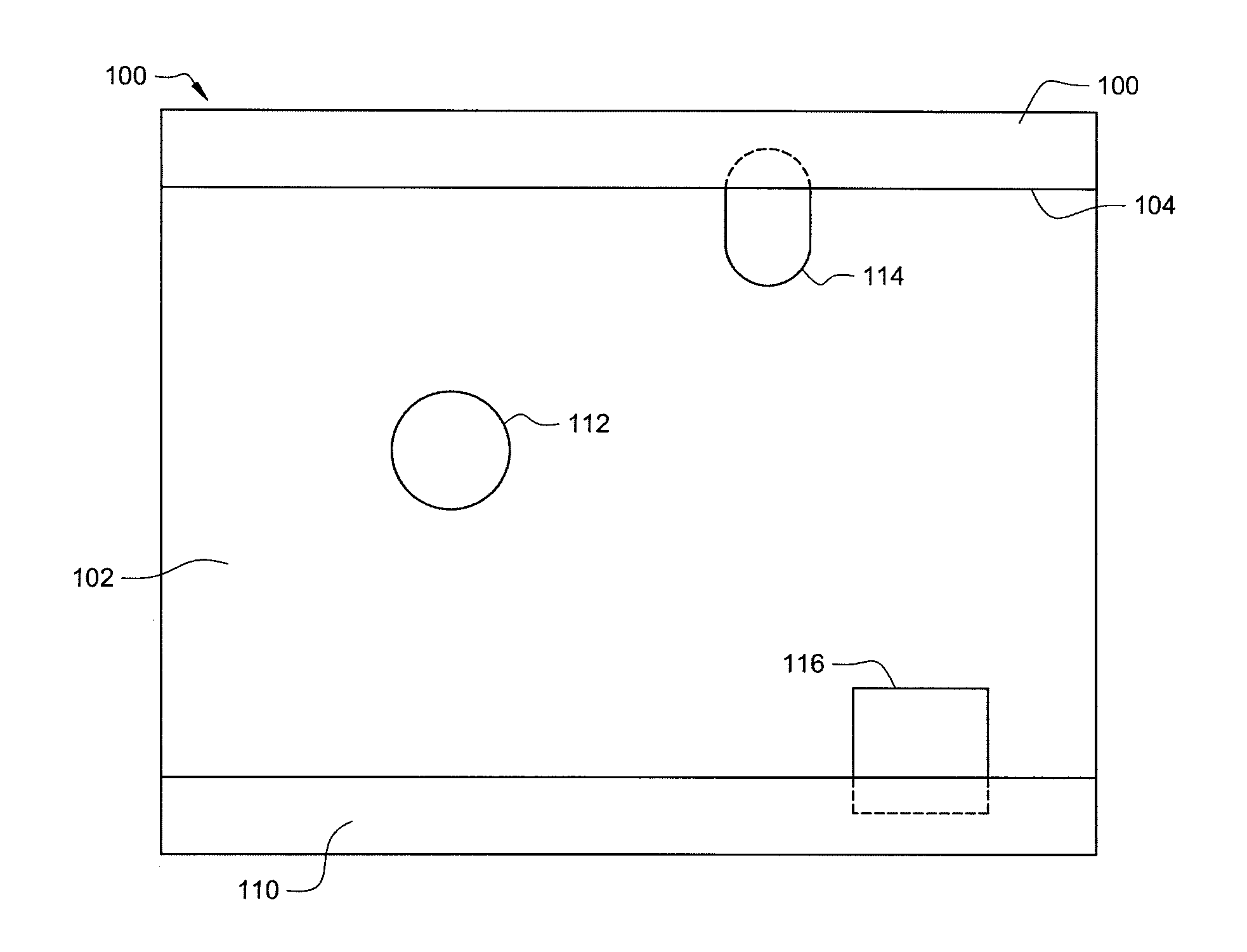
Method for the selection of physical objects in a robot system
ActiveUS20130151007A1Improve qualityView accuratelyProgramme controlProgramme-controlled manipulatorGrippersEngineering
A method in which an apparatus receives first sensor data from first sensors and determines a target position from the data, the target position may be a position in space or an orientation of a gripper in a robot arm First instructions are issued to the robot arm or the gripper in order to move a gripper to the target position. Force feedback sensor data is received from force feedback sensors associated with either the robot arm or the gripper or from the first sensors. A failure in carrying out the first instructions is determined Second sensor data is received from the at least one first sensor. Successful gripping of an object is determined from the second sensor data.
Owner:MP ZENROBOTICS OY
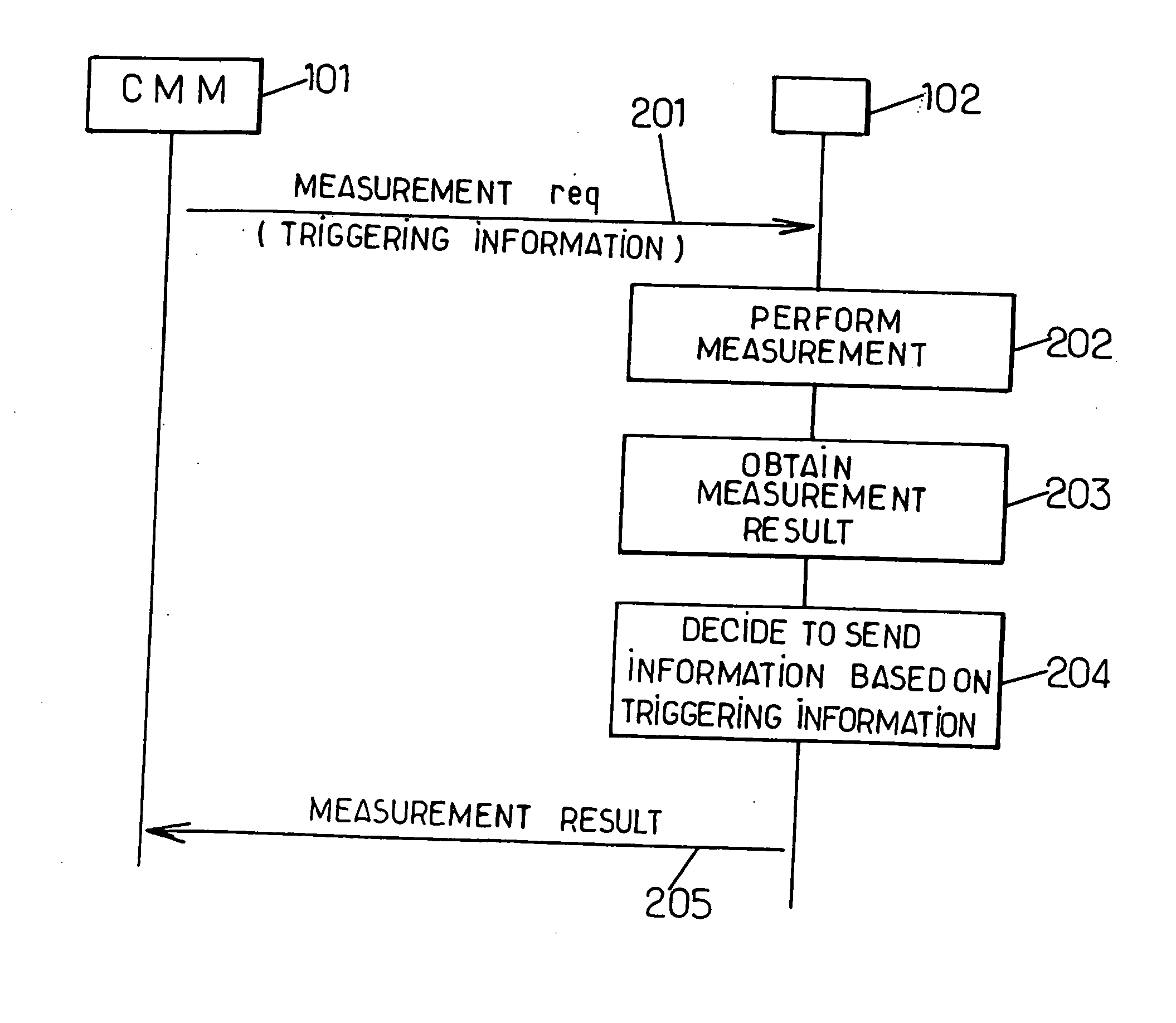
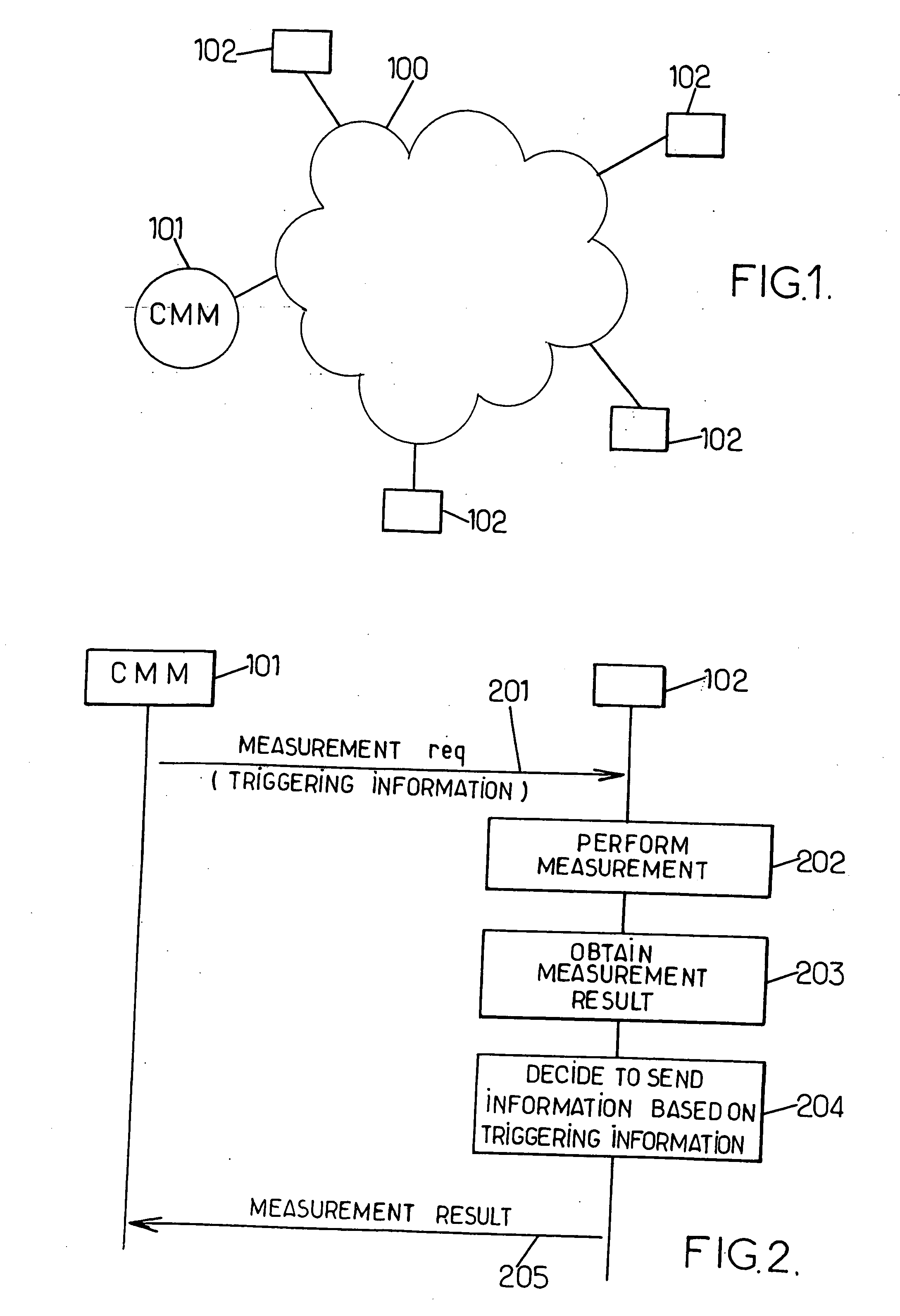
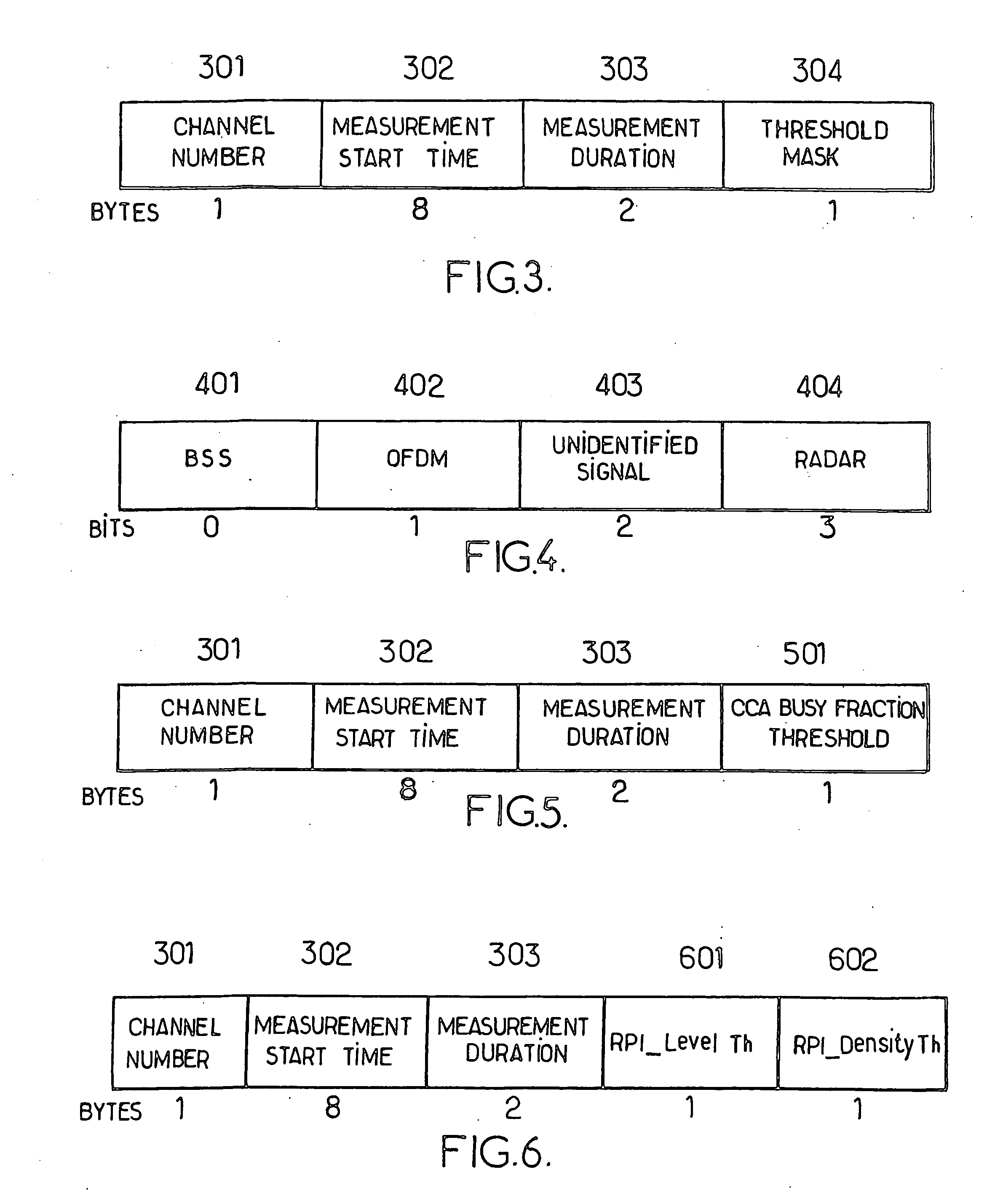
Method and device for managing signal measurements in a wireless network
InactiveUS20060264179A1View accuratelyLimiting bandwidth consumptionRadio transmissionTransmission monitoringComputer networkTelecommunications
A wireless network comprises at least one station (102) adapted to perform measurements of at least one given type in the network, and a Centralised Measurement Manager (CMM) unit (101) for handling measurements of said type. CMM unit sends a measurement request message (201) requesting that this station (102) perform a measurement of the given type, this request message comprising a triggering information (304, 501, 601-602). Upon reception of the measurement request message (201), the station performs (202) a measurement and obtains (203) corresponding measurement result. Then, it is decided (204) whether at least part of the measurement results is to be sent to the CMM unit based on the triggering information. If yes, the station sends the corresponding part of the measurement result to the CMM unit.
Owner:MITSUBISHI ELECTRIC CORP
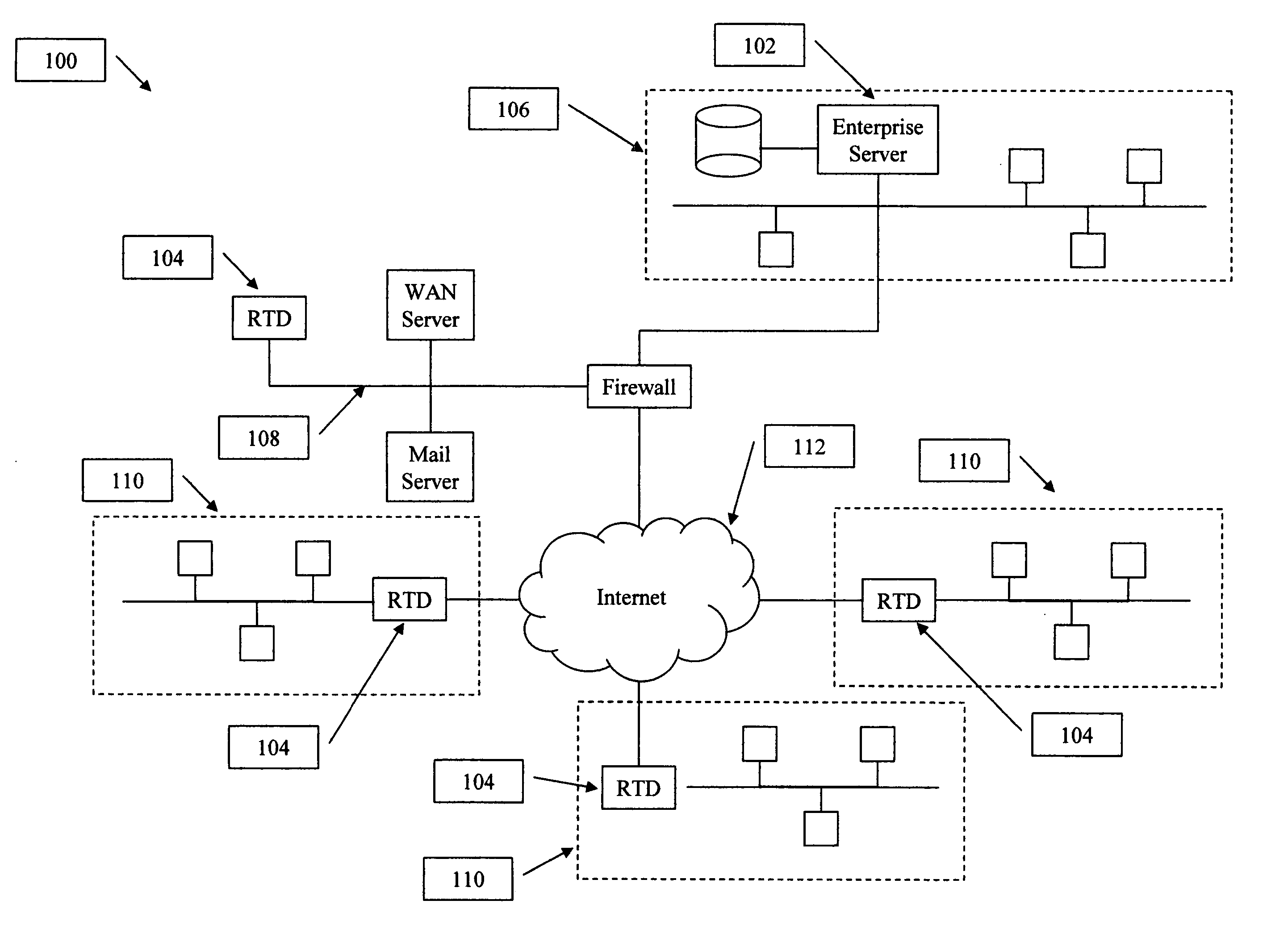
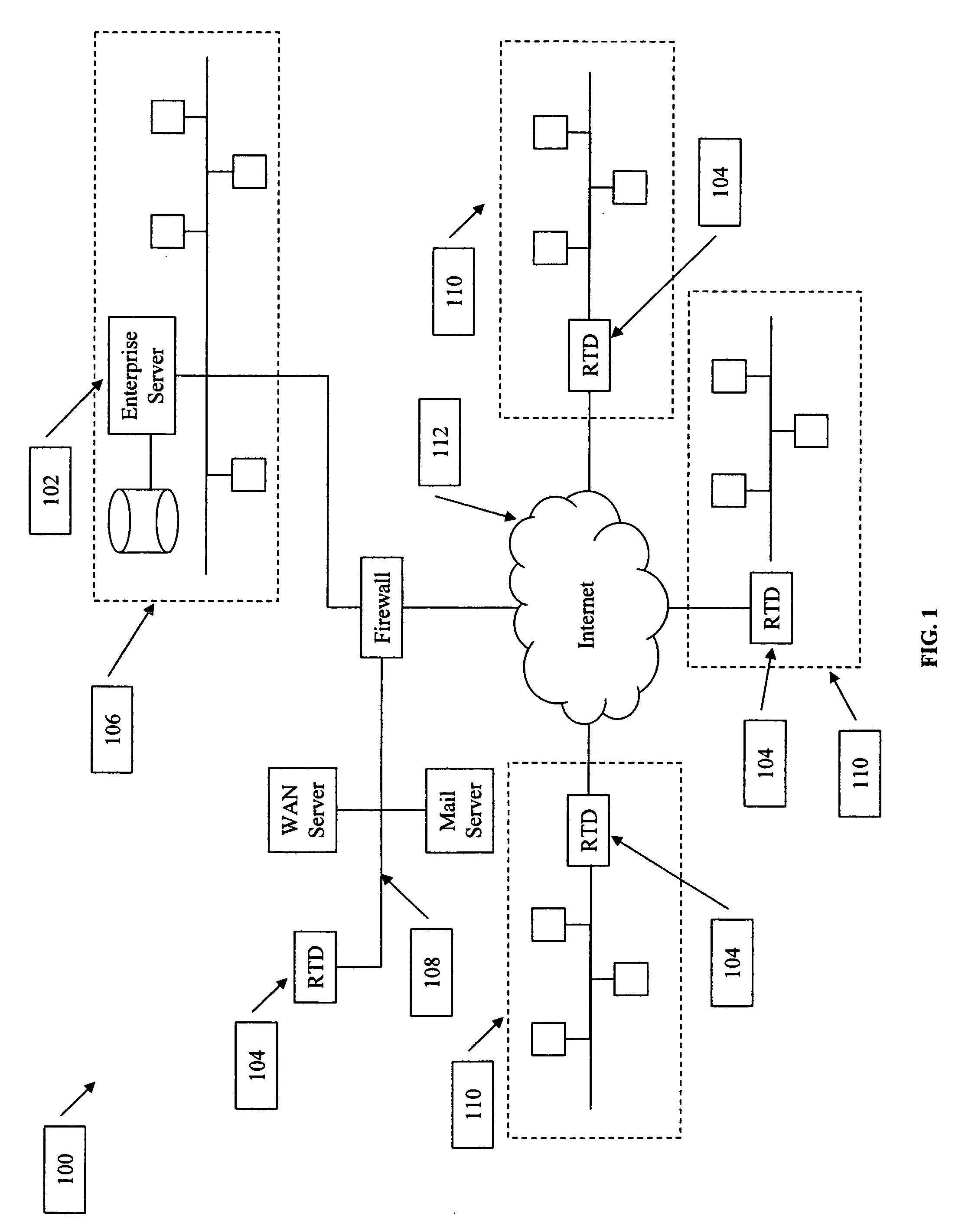
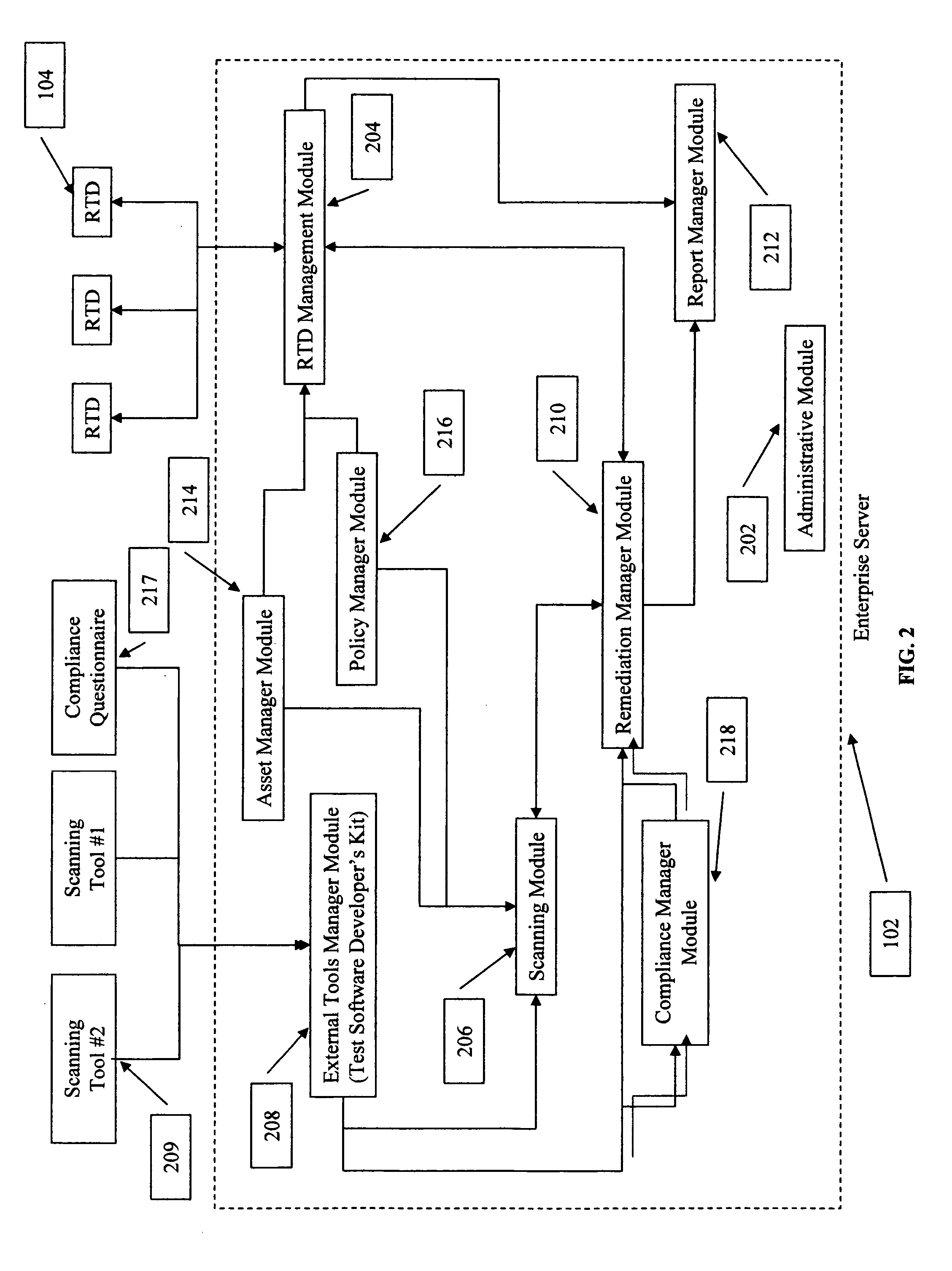
Method to manage network security over a distributed network
InactiveUS20060101520A1View accuratelyMemory loss protectionError detection/correctionManagement systemInformation control
The present invention provides a system with a first controller device that exercises control over one or more secondary controller devices and one or more remote testing devices. The remote testing devices accomplish all scanning of the distributed networks but remain under the control and management of the controller device. To complete a vulnerability assessment of the entire distributed network, the controller device schedules scans for each of the remote testing devices. The remote testing devices scan the network to which they are attached. Each remote testing device reports the results of the several scans to the controller device. The controller device also manages regulatory compliance information for the system. The controller device may consolidate the results to create an organization-wide vulnerability and compliance database.
Owner:SCHUMAKER TROY T +1
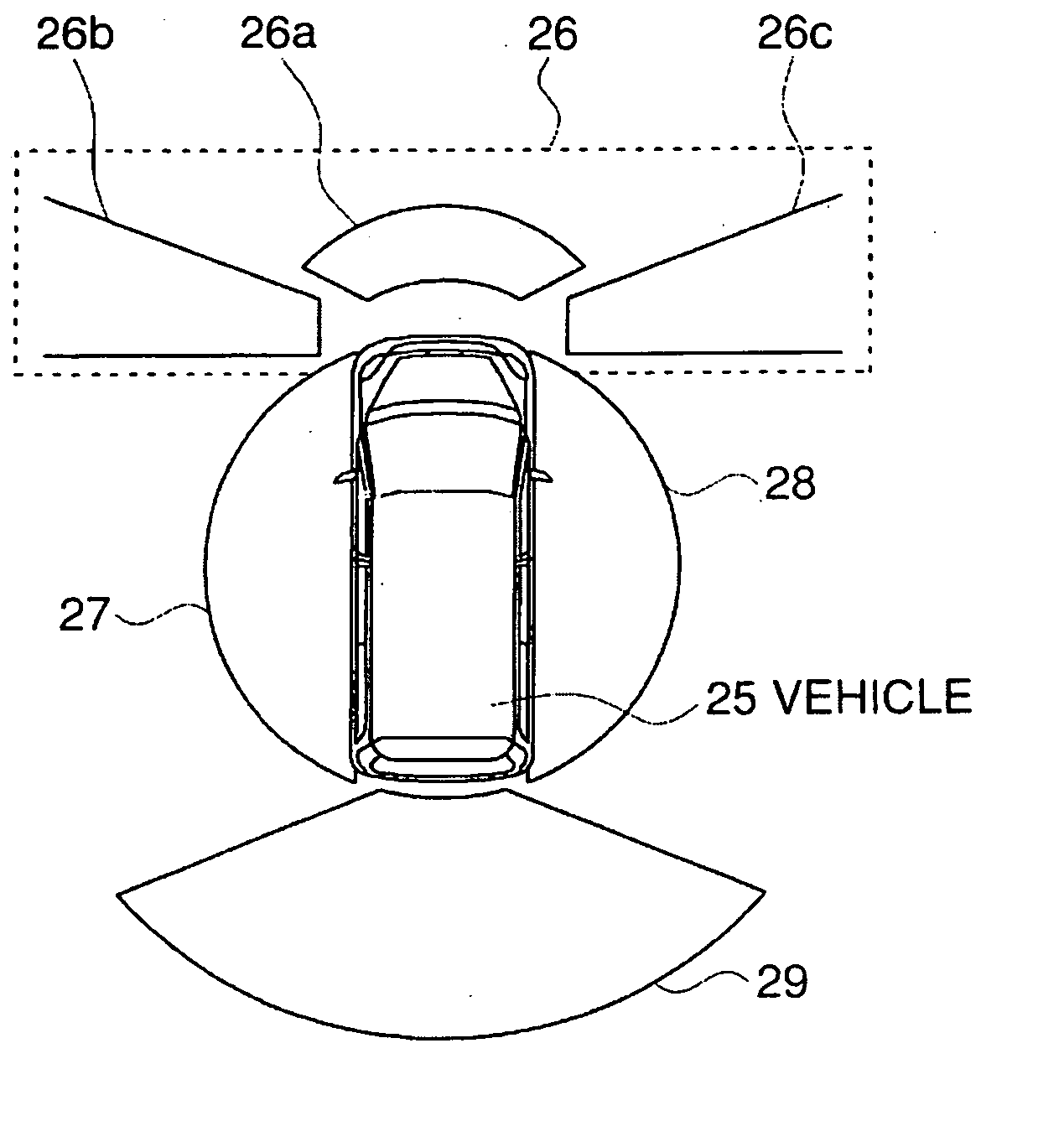
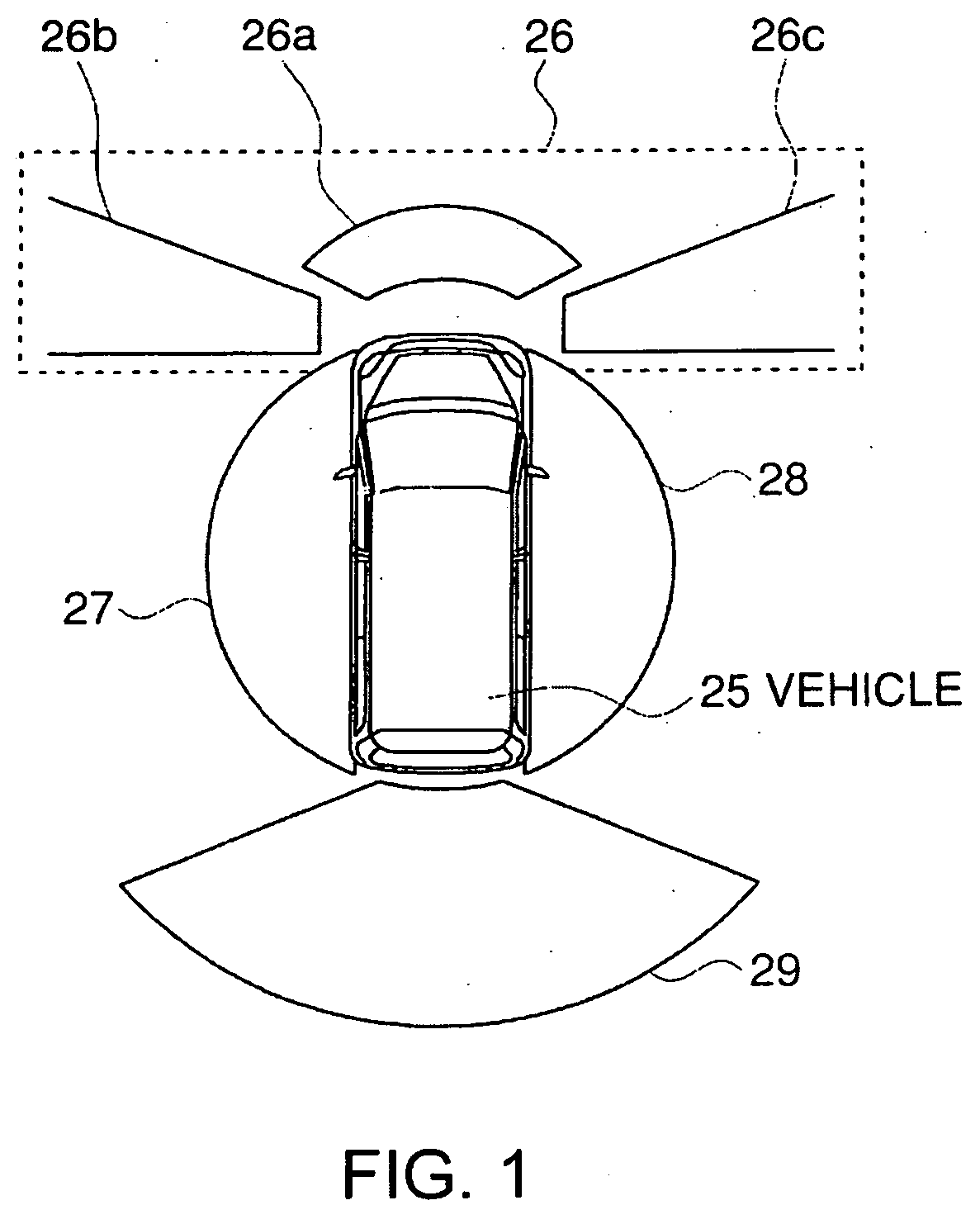
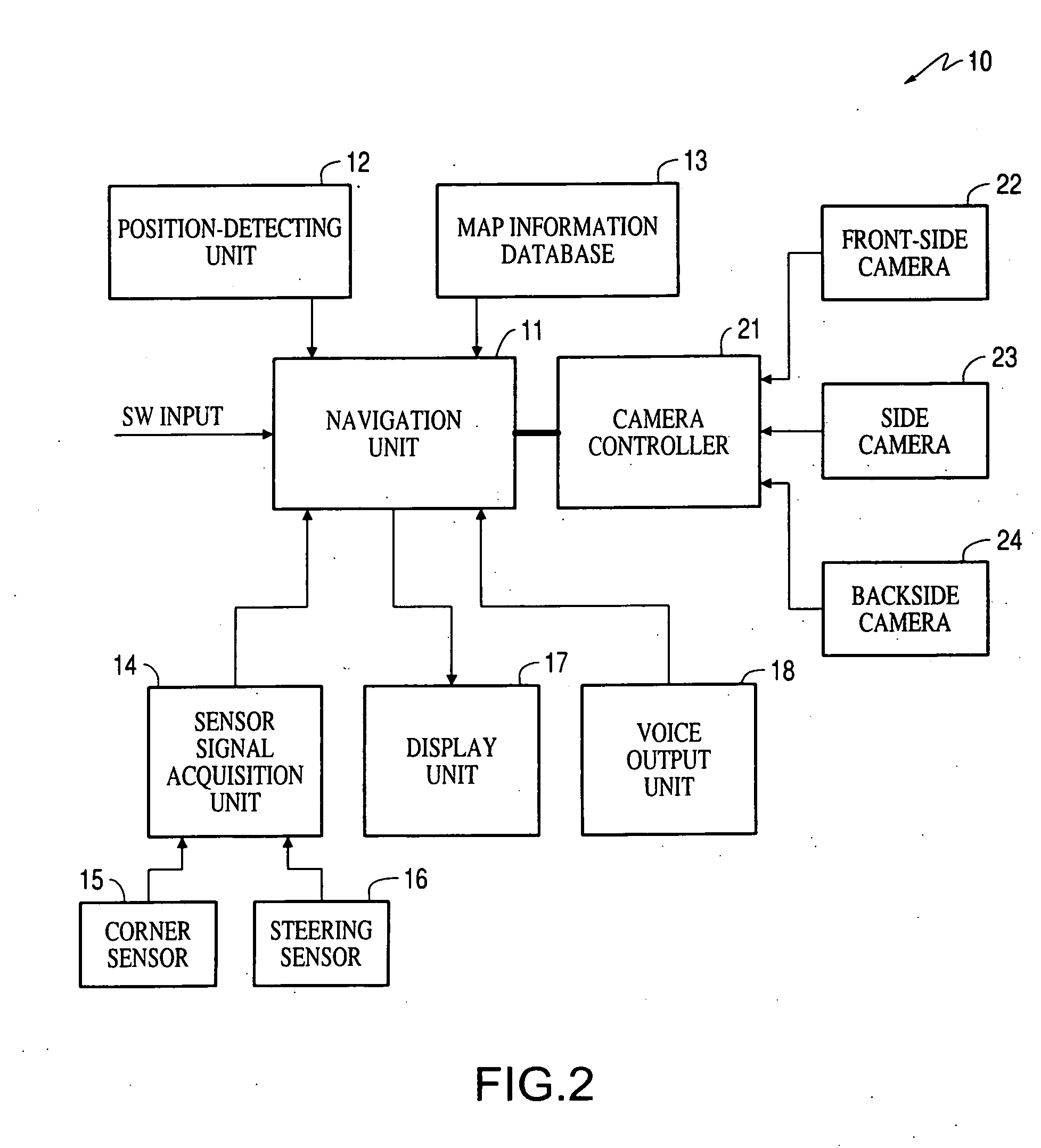
Visual recognition apparatus, methods, and programs for vehicles
InactiveUS20060215020A1Simple and safe processView accuratelyAnti-collision systemsColor television detailsDriver/operatorDisplay device
Around-vehicle visual recognition apparatus, methods, and programs acquire circumstances of a vehicle, including the vehicle's location and cause a camera to take images around the vehicle. The apparatus, methods, and programs determine at least one first area around the vehicle that is more relevant to a driver based on the circumstances of the vehicle than another area around the vehicle and display an image of the at least one first area on a display.
Owner:AISIN AW CO LTD
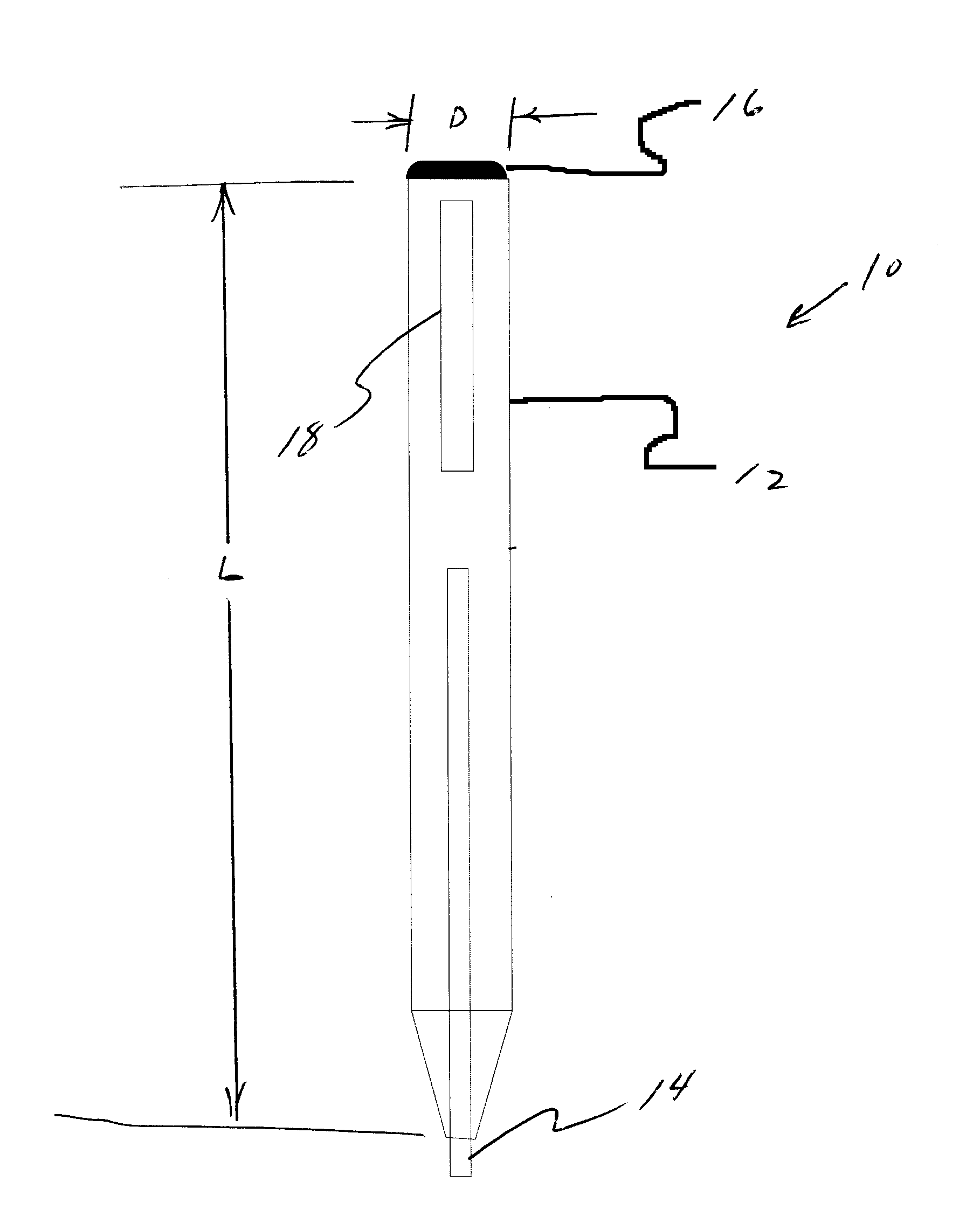
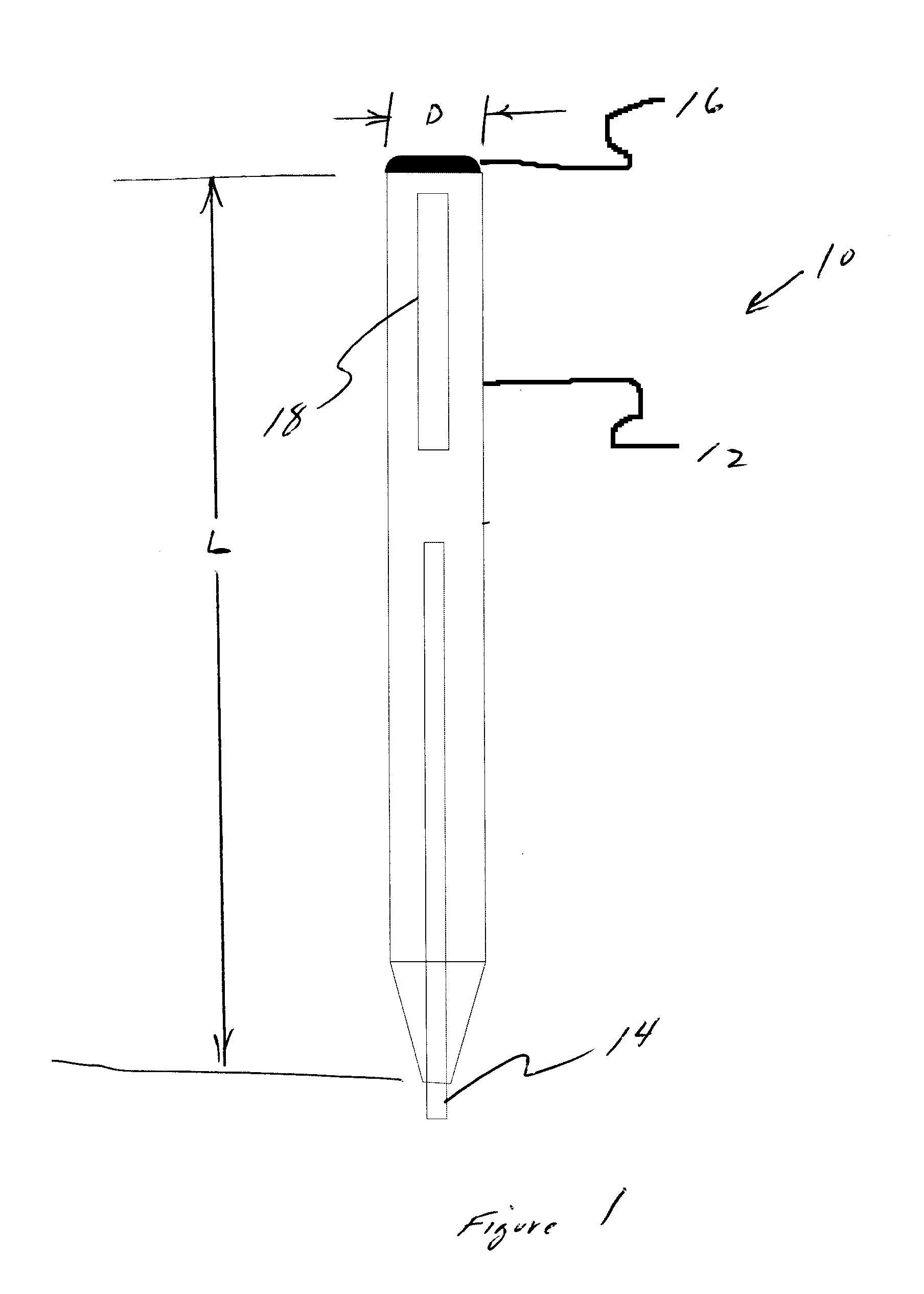
Multifunctional writing apparatus with capacitive touch screen stylus
InactiveUS20120086664A1View accuratelyEfficient use ofWriting connectorsPropelling pencilsCapacitive couplingElectrically conductive
A multifunctional writing apparatus includes a writing device and a stylus operable to control a capacitive touch screen display device. The multifunctional apparatus includes an electrically conducting body having a first end and a second end. The first end includes a writing device such as a pen or pencil which allows a user to write on a paper or another type of media. The second end of the body comprises an electrically conductive portion which, when in contact with a capacitive based touch screen display device, allows a user to make a capacitive coupling and operate the touch screen display device.
Owner:GLT TECHNOVATIONS
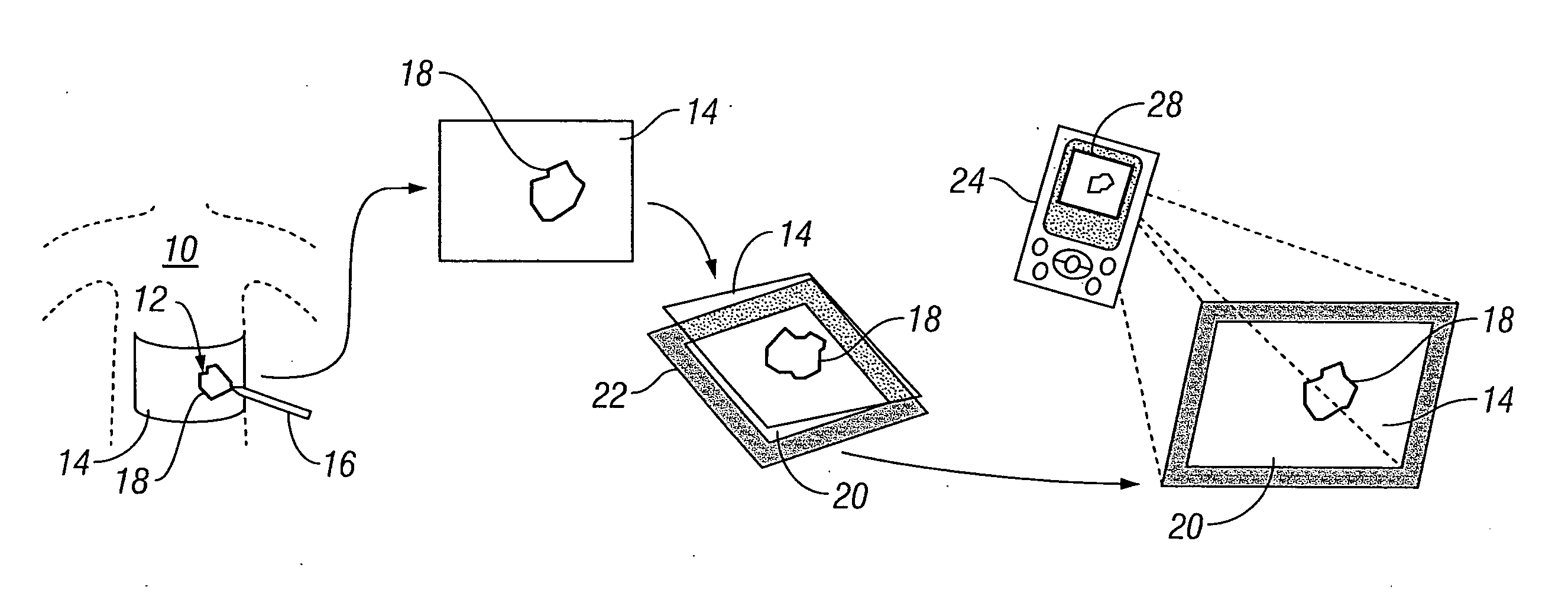
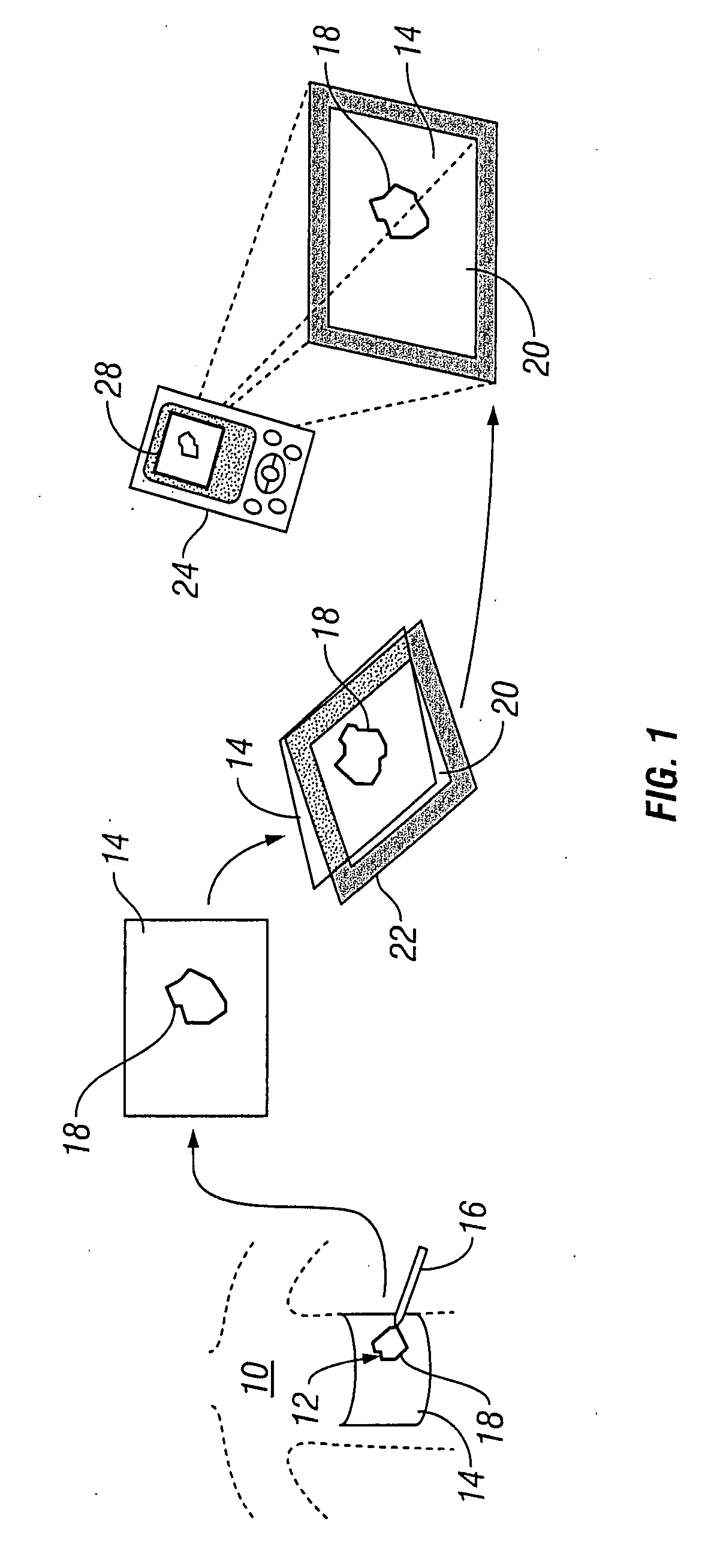
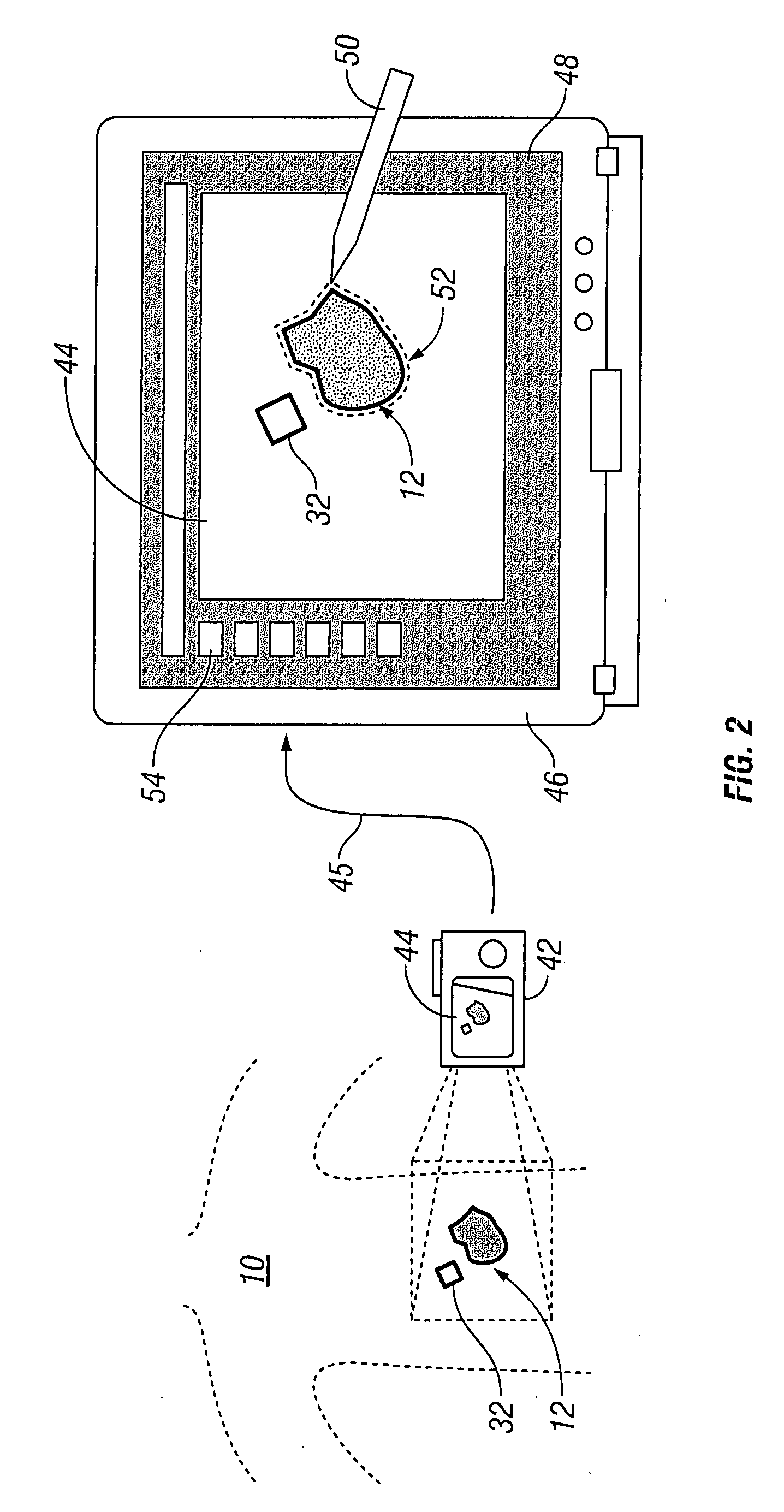
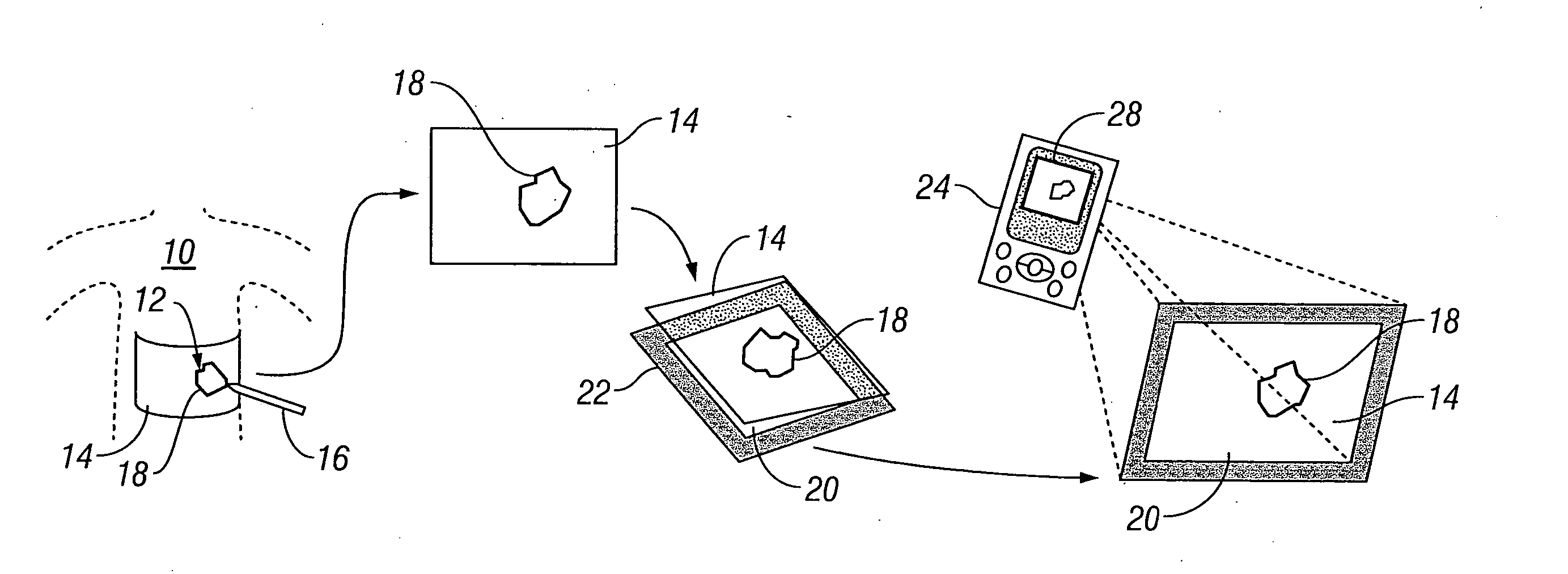
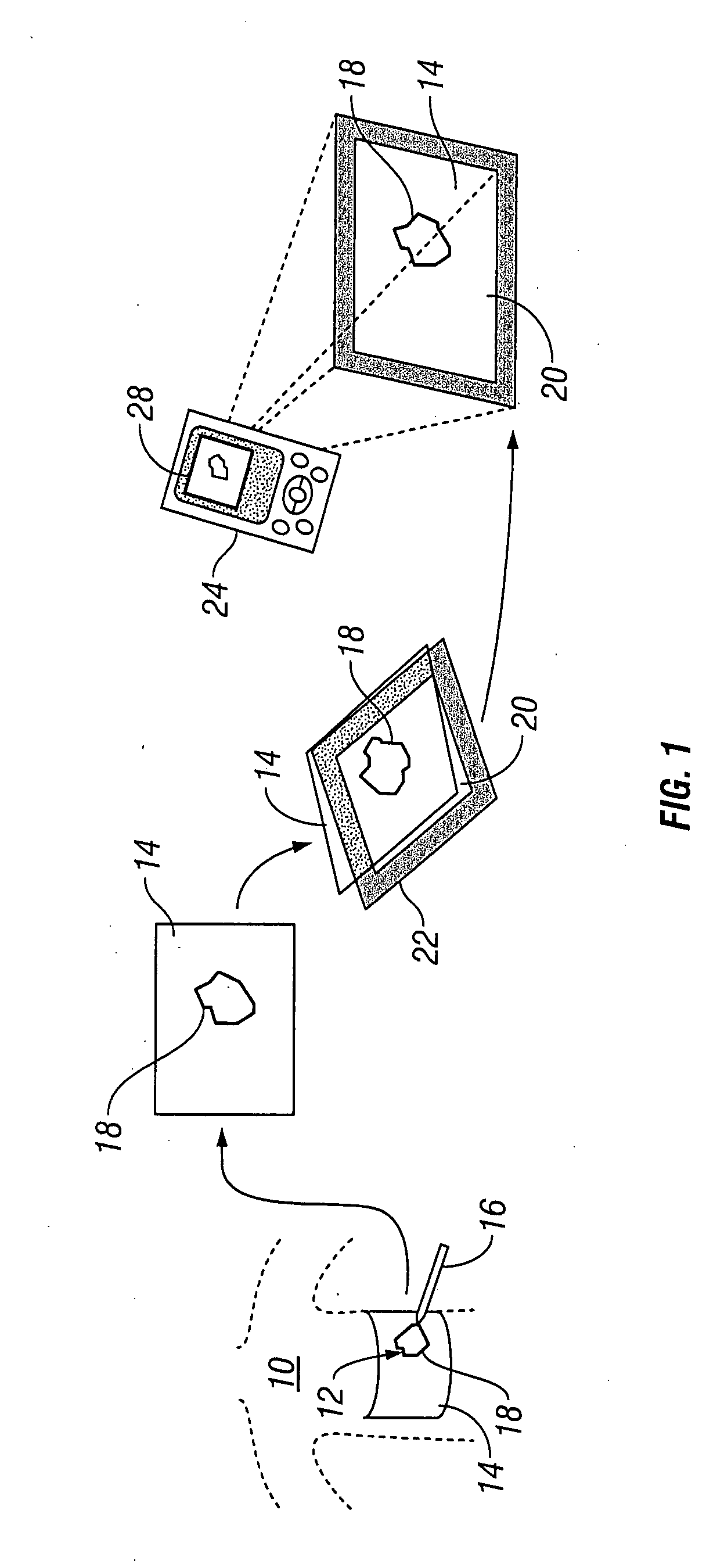
Systems and methods for wound area management
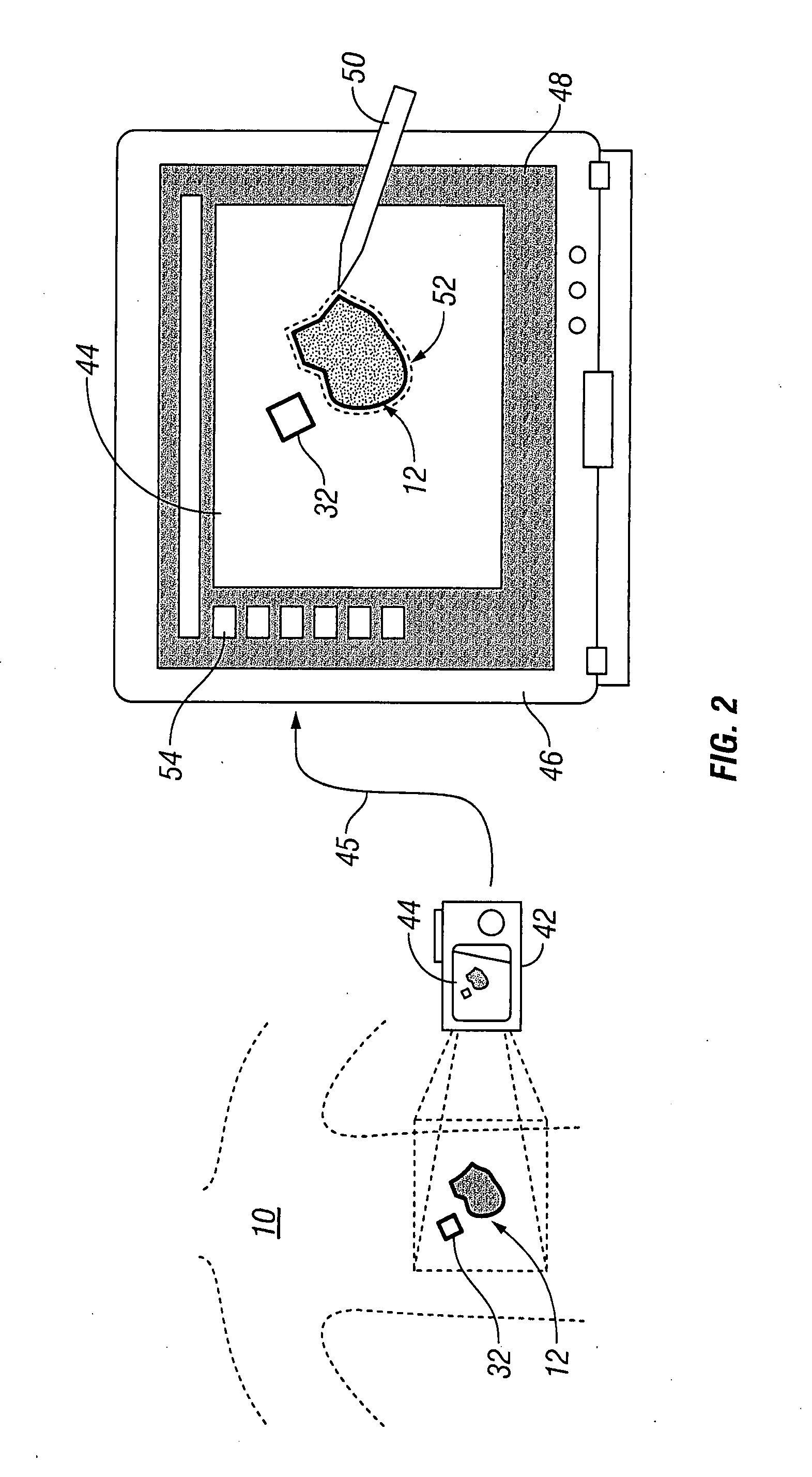
InactiveUS20070276309A1Repeatability, non-invasivenessCost effectivenessProjector film strip handlingCamera film strip handlingData setDigital imaging
Systems and methods for capturing and digitizing an image of a wound and / or a wound trace from a patient and determining there from a degree of change in the characteristics of the wound. A first embodiment includes a transparent / translucent film onto which a dark outline of the wound is traced. The film is fixed to a reference template that provides a geometrically defined reference area. The film / template assembly is imaged with a digital imaging device associated with a handheld digital processor (such as a PDA). The digital image of the template and the wound trace are analyzed to identify the wound tracing and quantify the area within the closed curve. A second embodiment includes imaging the wound site with a reference tag and viewing the image on a display with an associated graphical data input device. A trace of the wound perimeter is made on display with the graphical data input device to establish a data set for the wound perimeter. The data set for the wound trace and the reference tag are analyzed to identify and quantify the wound area. In each embodiment, the system includes a display for providing both a view of the wound trace and the calculated data associated with the wound area.
Owner:KCI LICENSING INC
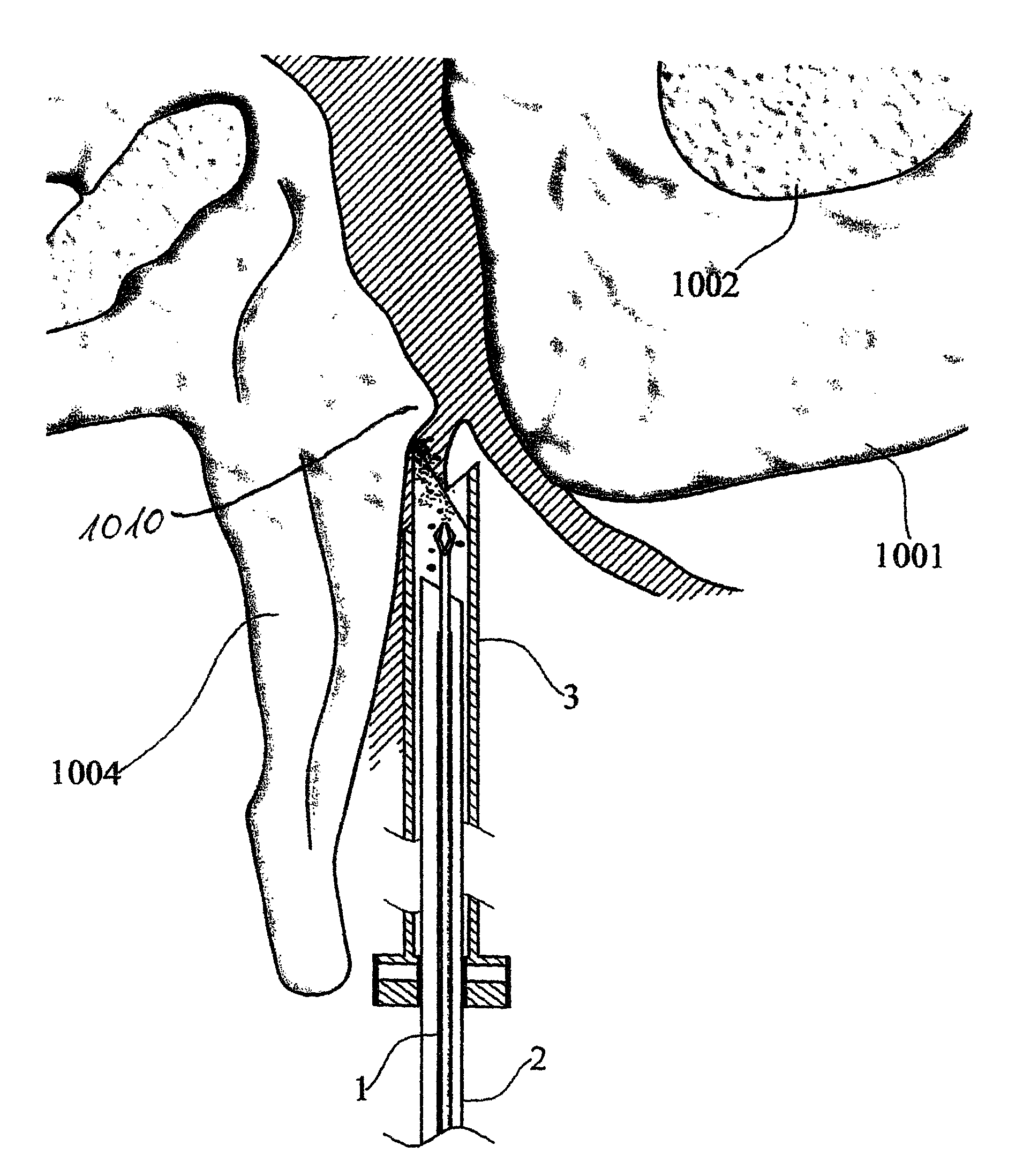
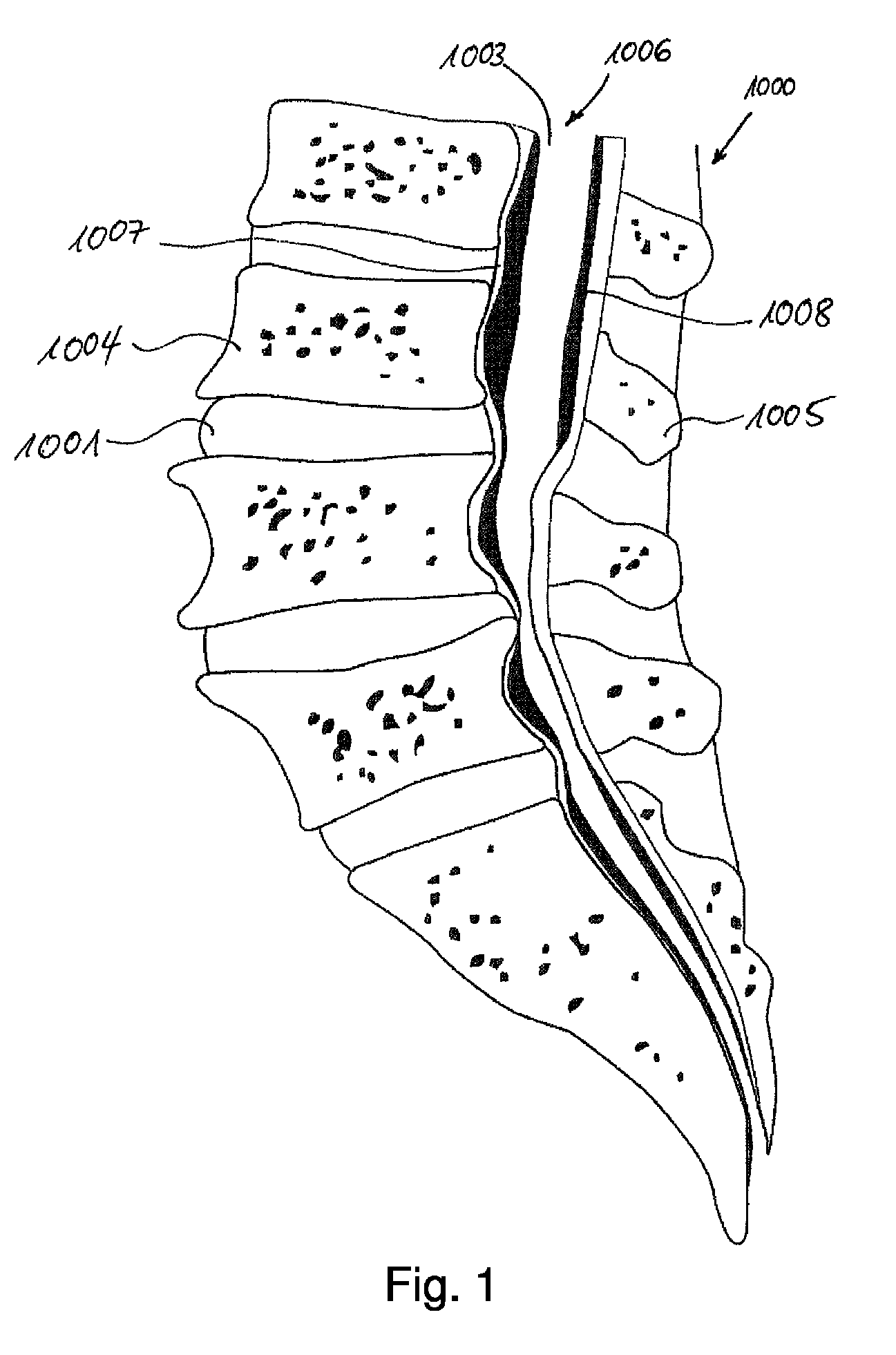
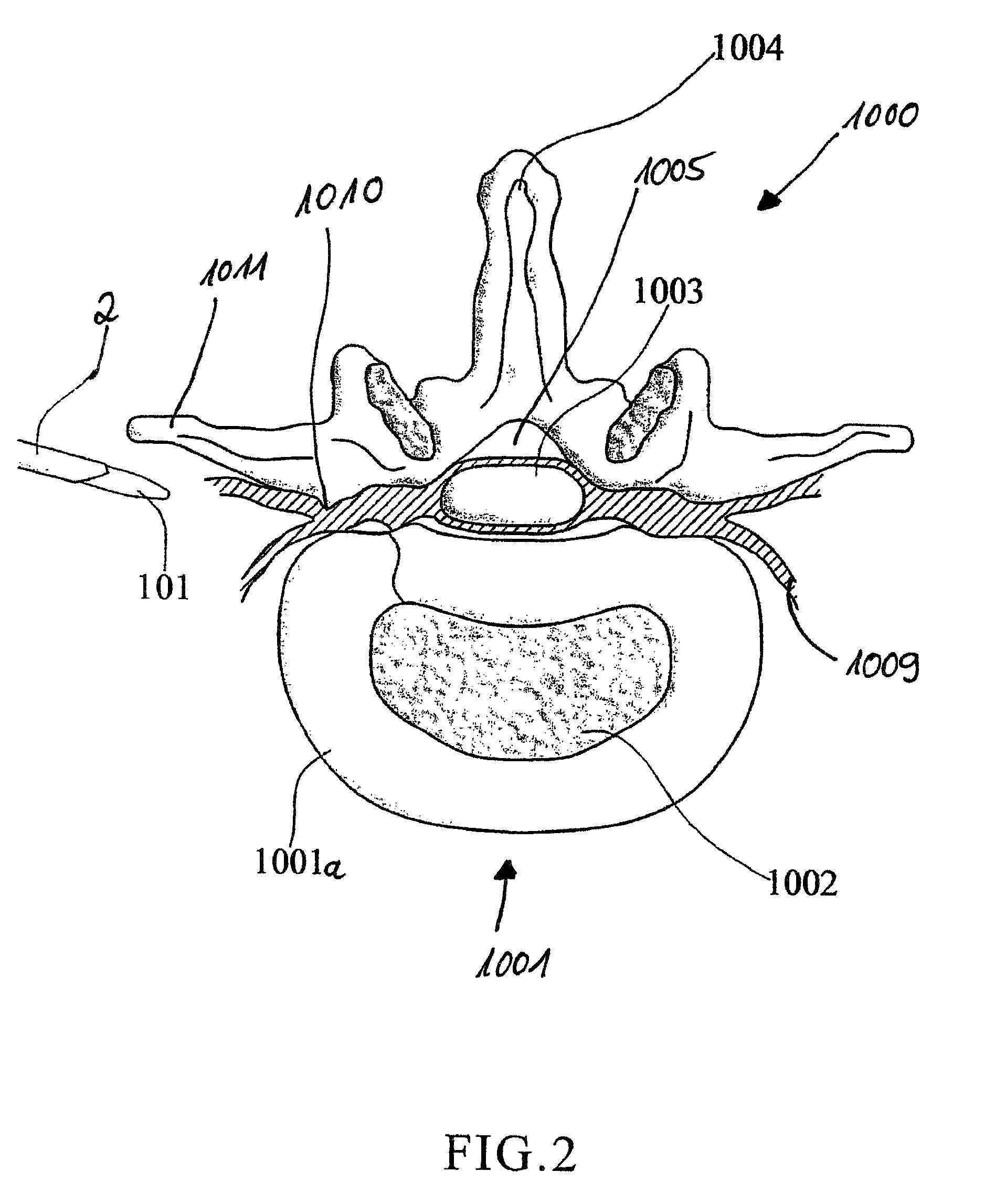
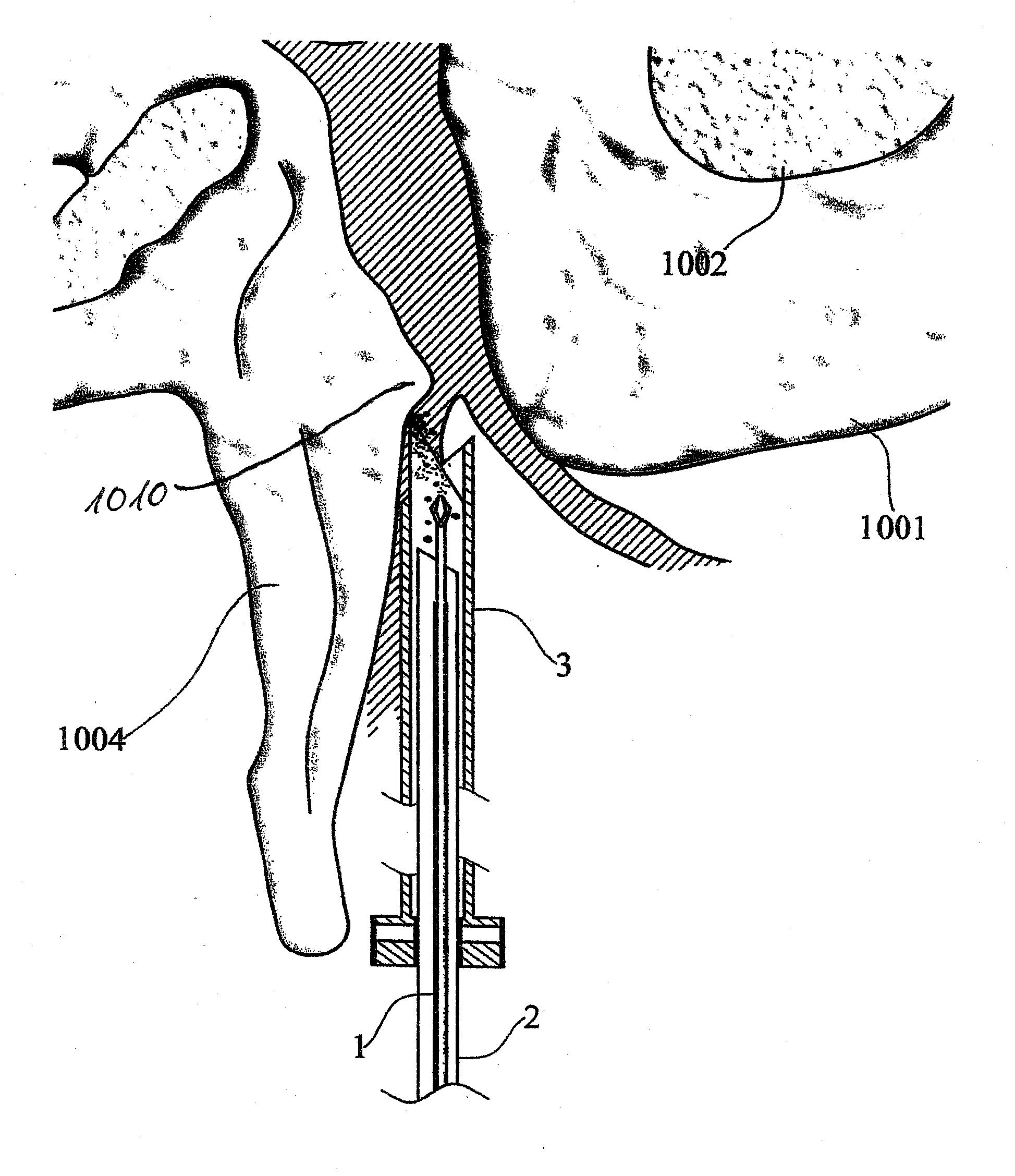
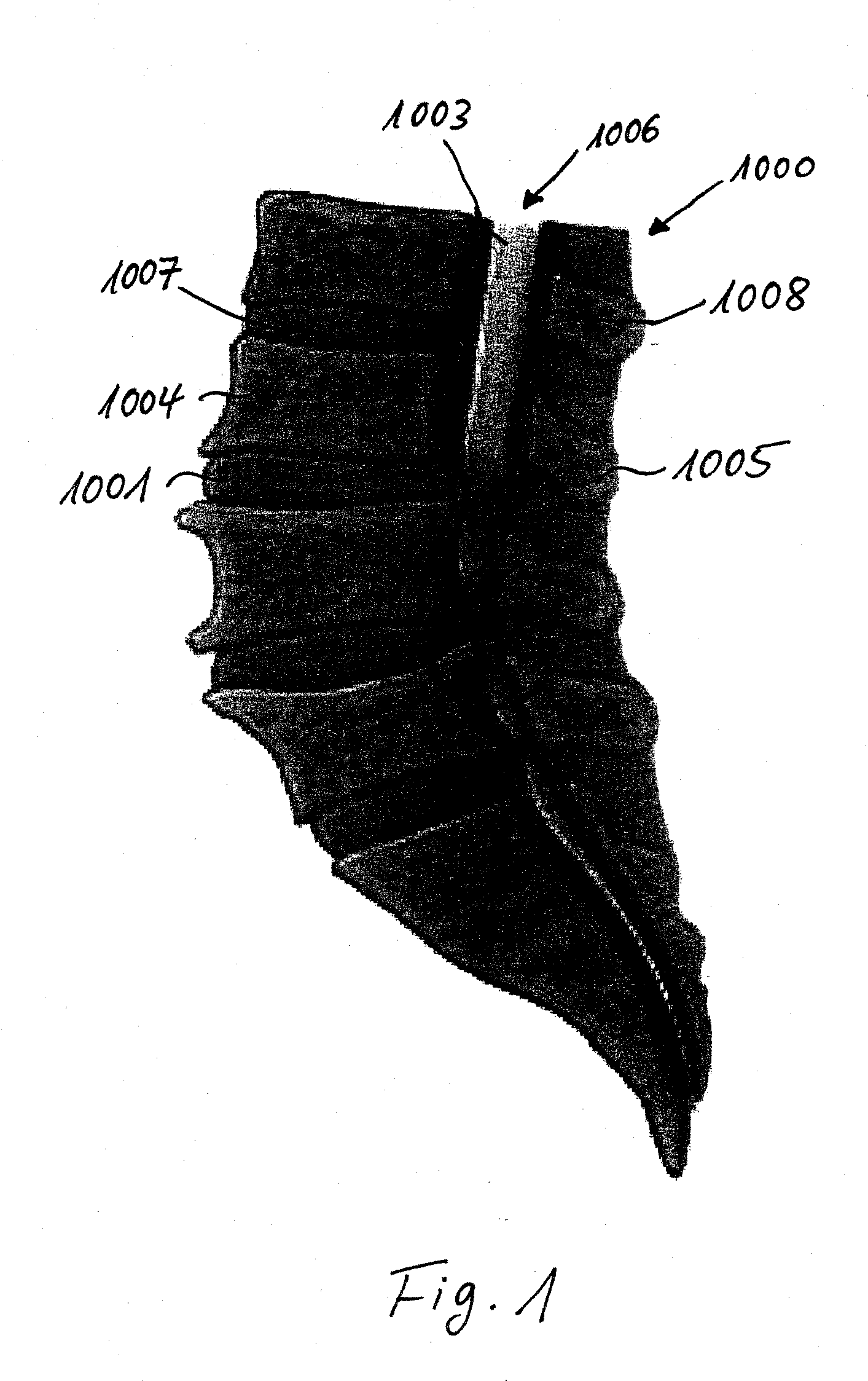
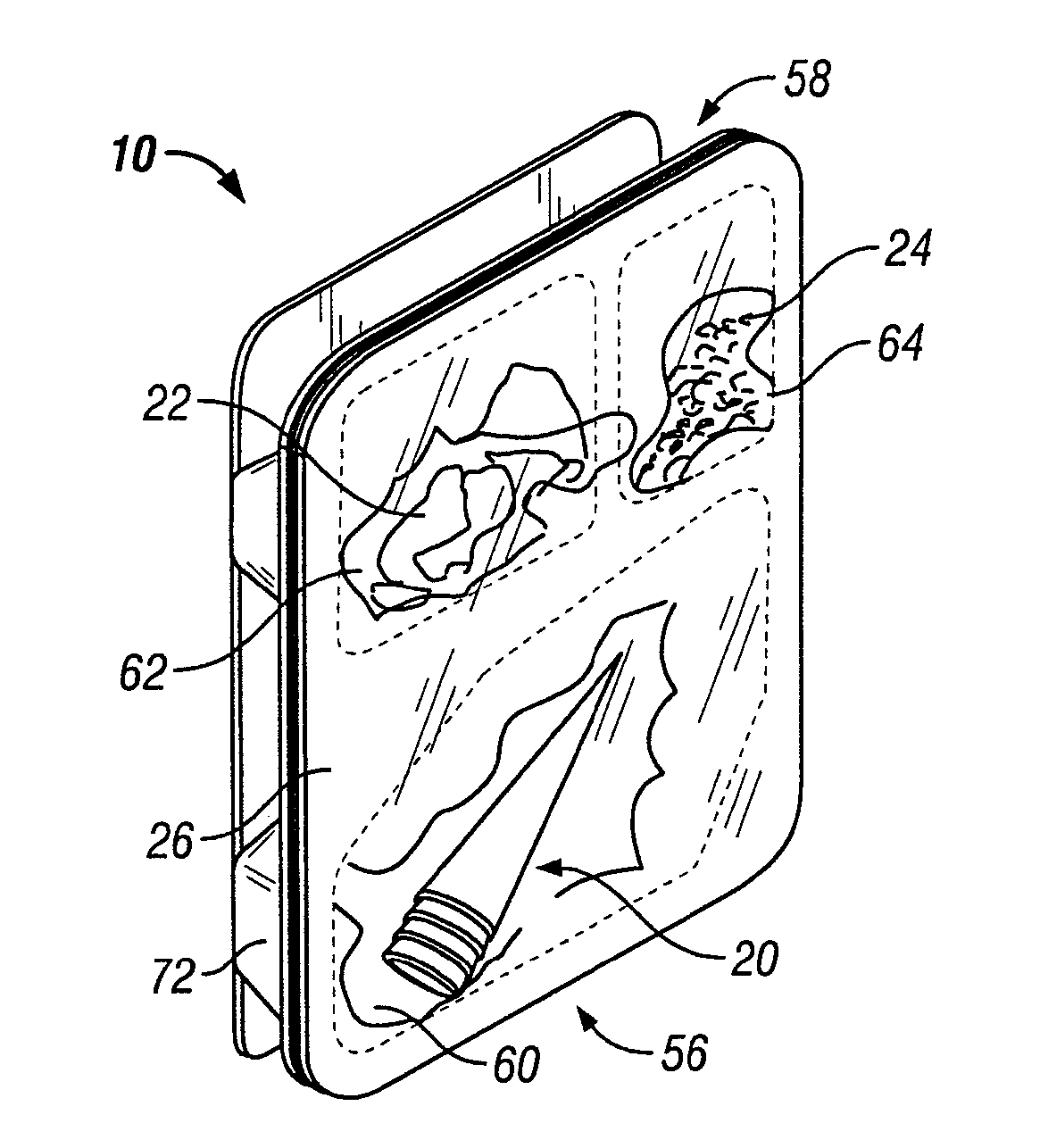
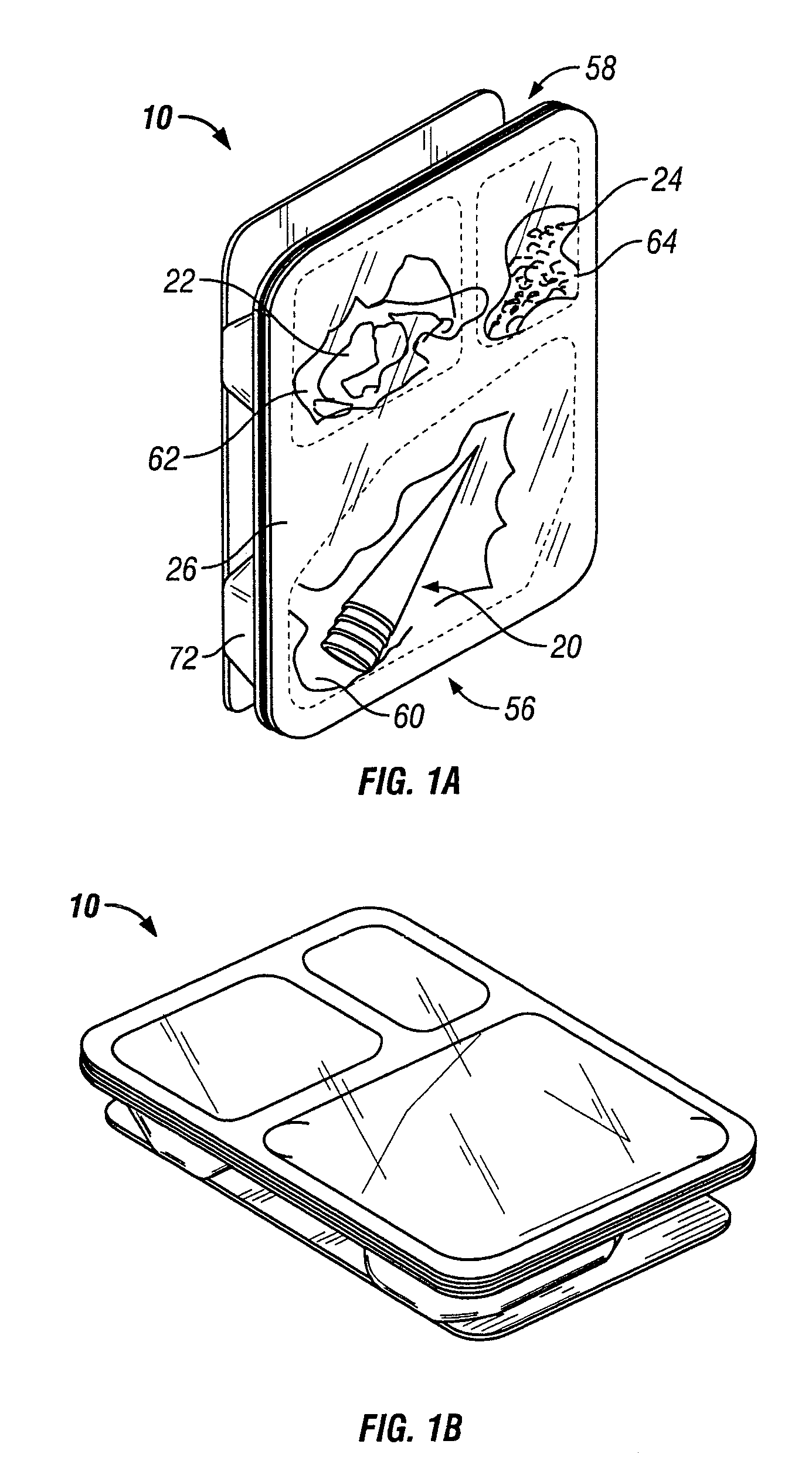
Device and method for minimally invasive spinal intervention
The invention proposes a device for minimally invasive intervention in the skeletal region, in particular on the spinal column, having at least a cannula with a distal end generally bevelled in shape relative to a symmetrical axis of the cutting tool and an optical probe (endoscope) for insertion through the cavity of the cannula. The device is further characterized in that the cannula takes the form of a hollow cutting tool, in which the most distal region of the distal end comprises a cutting edge, which is incorporated into the edge of the wall of the cutting tool.
Owner:JOIMAX GMBH
Systems and methods for wound area management
InactiveUS20070276195A1Repeatability, non-invasivenessCost effectivenessPrintersProjectorsData setDigital imaging
Systems and methods for capturing and digitizing an image of a wound and / or a wound trace from a patient and determining there from a degree of change in the characteristics of the wound. A first embodiment includes a transparent / translucent film onto which a dark outline of the wound is traced. The film is fixed to a reference template that provides a geometrically defined reference area. The film / template assembly is imaged with a digital imaging device associated with a handheld digital processor (such as a PDA). The digital image of the template and the wound trace are analyzed to identify the wound tracing and quantify the area within the closed curve. A second embodiment includes imaging the wound site with a reference tag and viewing the image on a display with an associated graphical data input device. A trace of the wound perimeter is made on display with the graphical data input device to establish a data set for the wound perimeter. The data set for the wound trace and the reference tag are analyzed to identify and quantify the wound area. In each embodiment, the system includes a display for providing both a view of the wound trace and the calculated data associated with the wound area.
Owner:KCI LICENSING INC
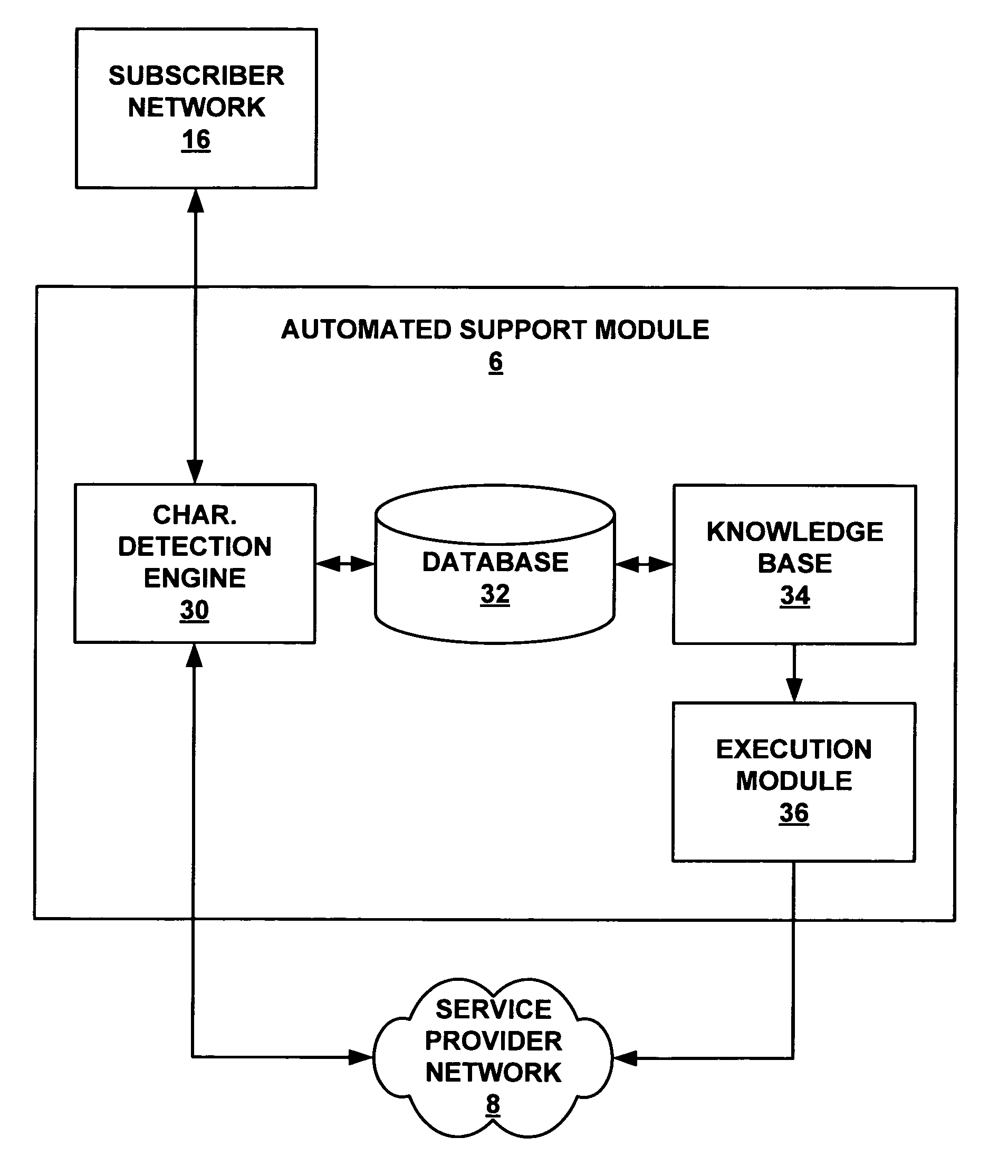
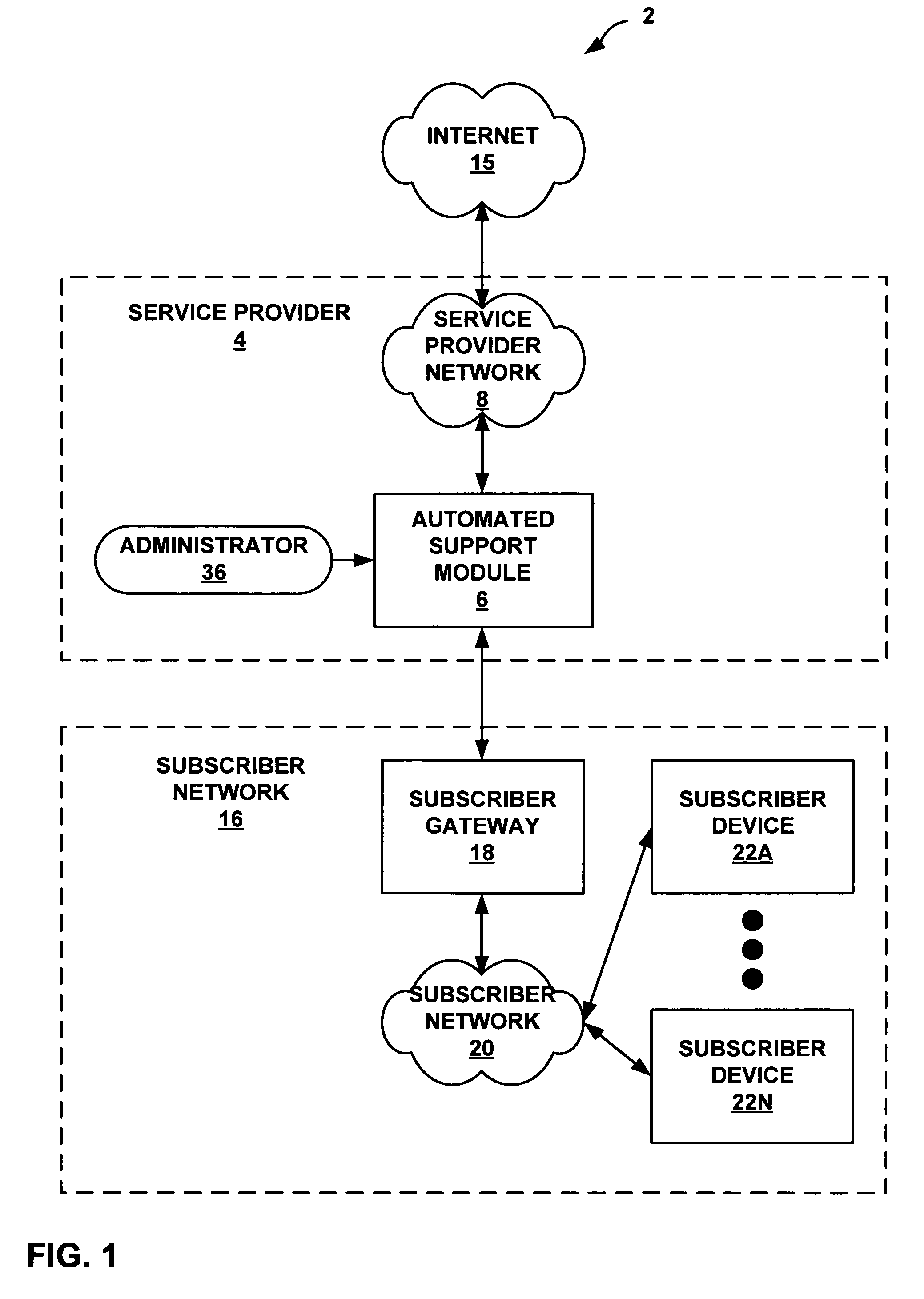
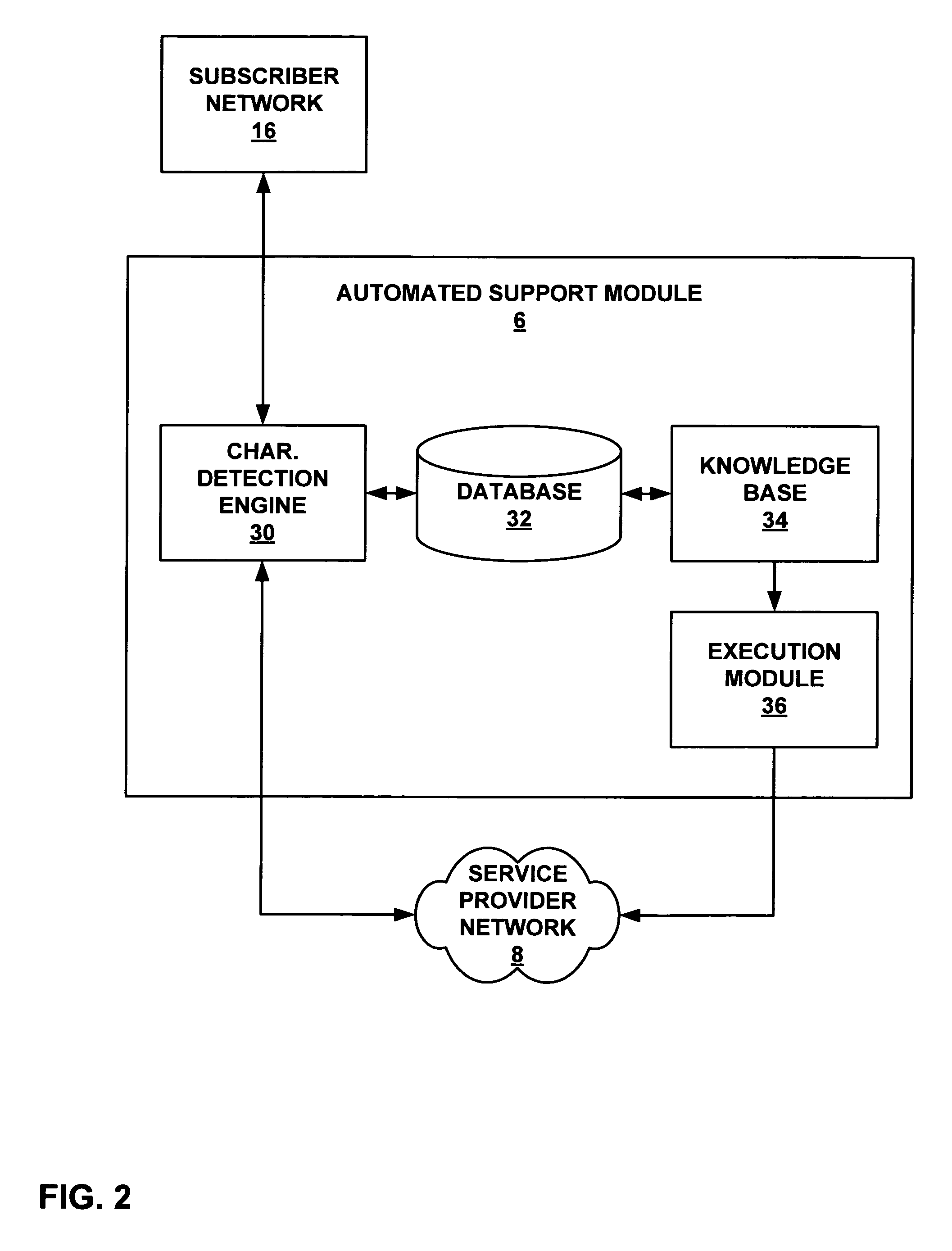
Analyzing network traffic to diagnose subscriber network errors
ActiveUS7916652B1View accuratelyError preventionFrequency-division multiplex detailsTraffic capacityPacket loss
A service provider network includes an automated support module that receives stream of network packets from subscribers and separates this streams into packet flows for analysis. The automated support module may be an intermediate device that examines each packet flow to detect subscriber characteristics for each subscriber. The automated support module may apply a set of analysis rules to the detected characteristics to aid diagnosis of reported or potential network errors.
Owner:JUMIPER NETWORKS INC
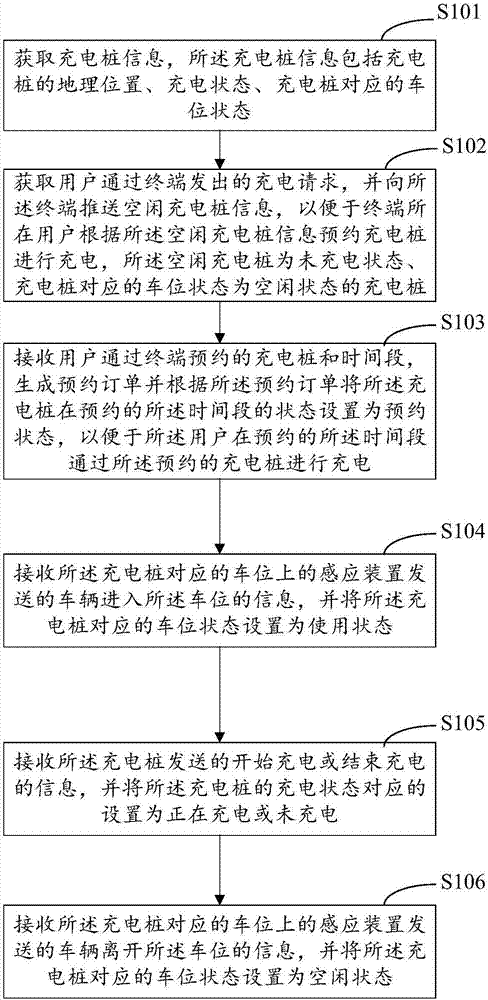
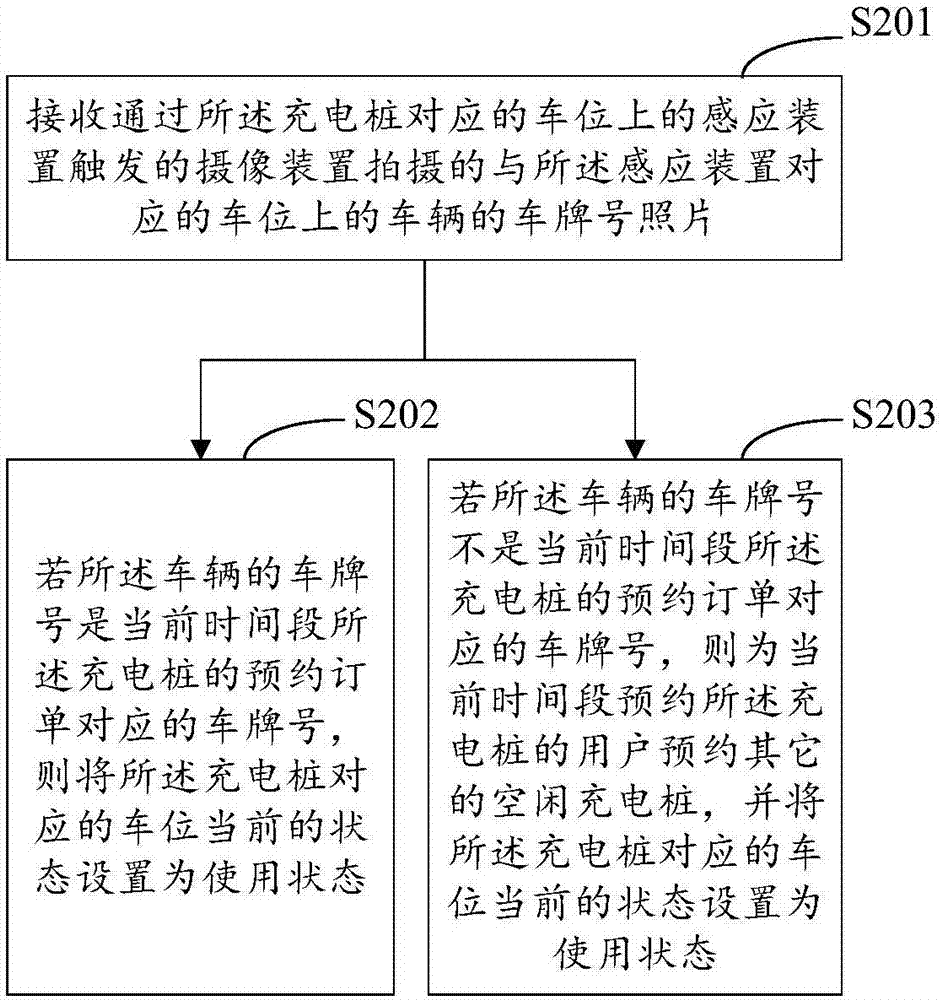
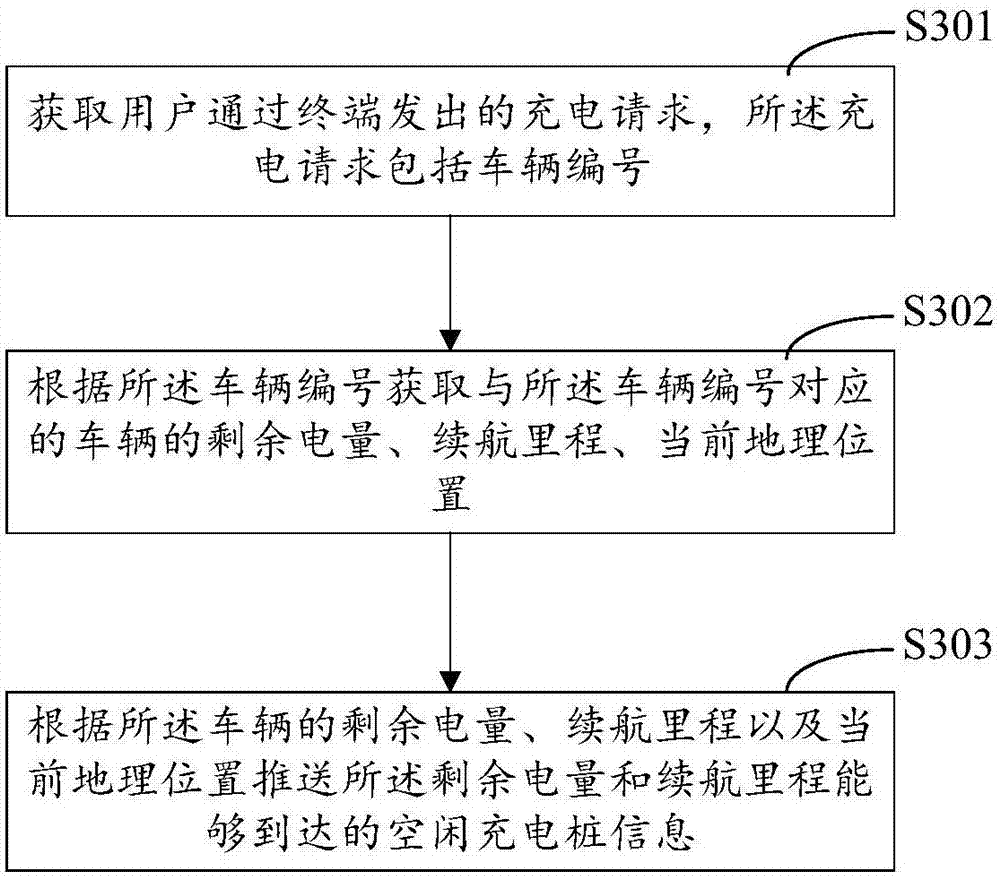
Method for reserving charging pile for charging and server
InactiveCN107368902AImprove efficiencyAccurate informationTicket-issuing apparatusReservationsInternet of ThingsParking space
The invention belongs to the technical field of the Internet of Things, and provides a method for reserving a charging pile for charging and a server. First information of charging piles is obtained, then idle charging pile information is pushed to a user according to a charging request sent by the user, the user can reserve for charging according to the pushed charging pile information, and after the user succeeds in reservation, the user enters a parking space corresponding to the reserved charging pile to perform charging according to a reservation order. The problem that the user cannot find an idle charging pile when needing charging can be solved, and the efficiency of the user searching for the idle charging pile is improved. Through the charging state of the charging pile and the parking space state sent by an induction device of the parking space corresponding to the charging pile, whether the current charging pile can charge a vehicle can be accurately obtained in real time, so that charging pile information obtained by the user is accurate, and the charging state of the reserved charging pile and the corresponding parking space sate can be checked in real time. The time of user for searching for a charging pile is reduced, and the efficiency of the user searching for the charging pile to perform charging is improved.
Owner:SHENZHEN SHENGLU IOT COMM TECH CO LTD
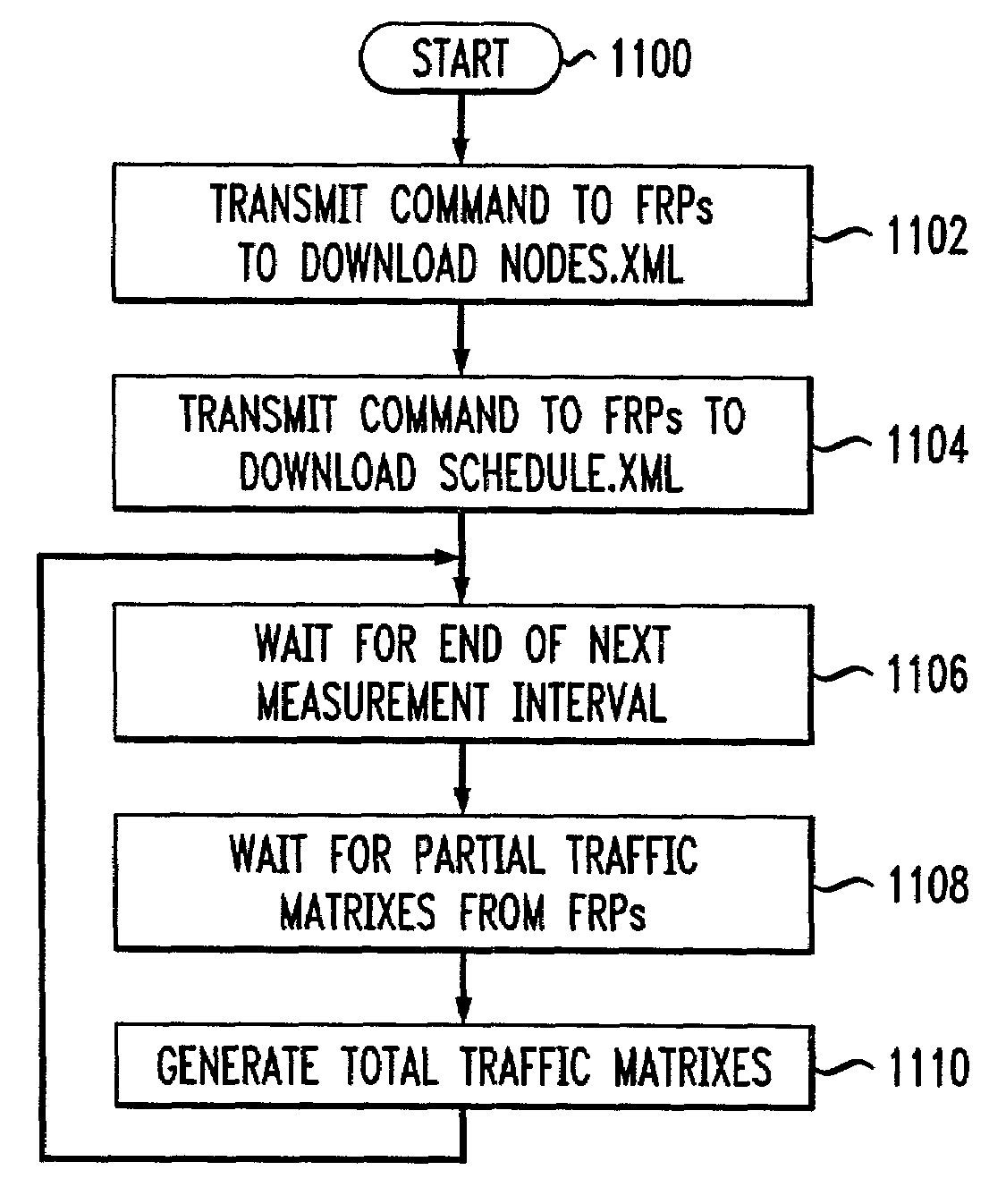
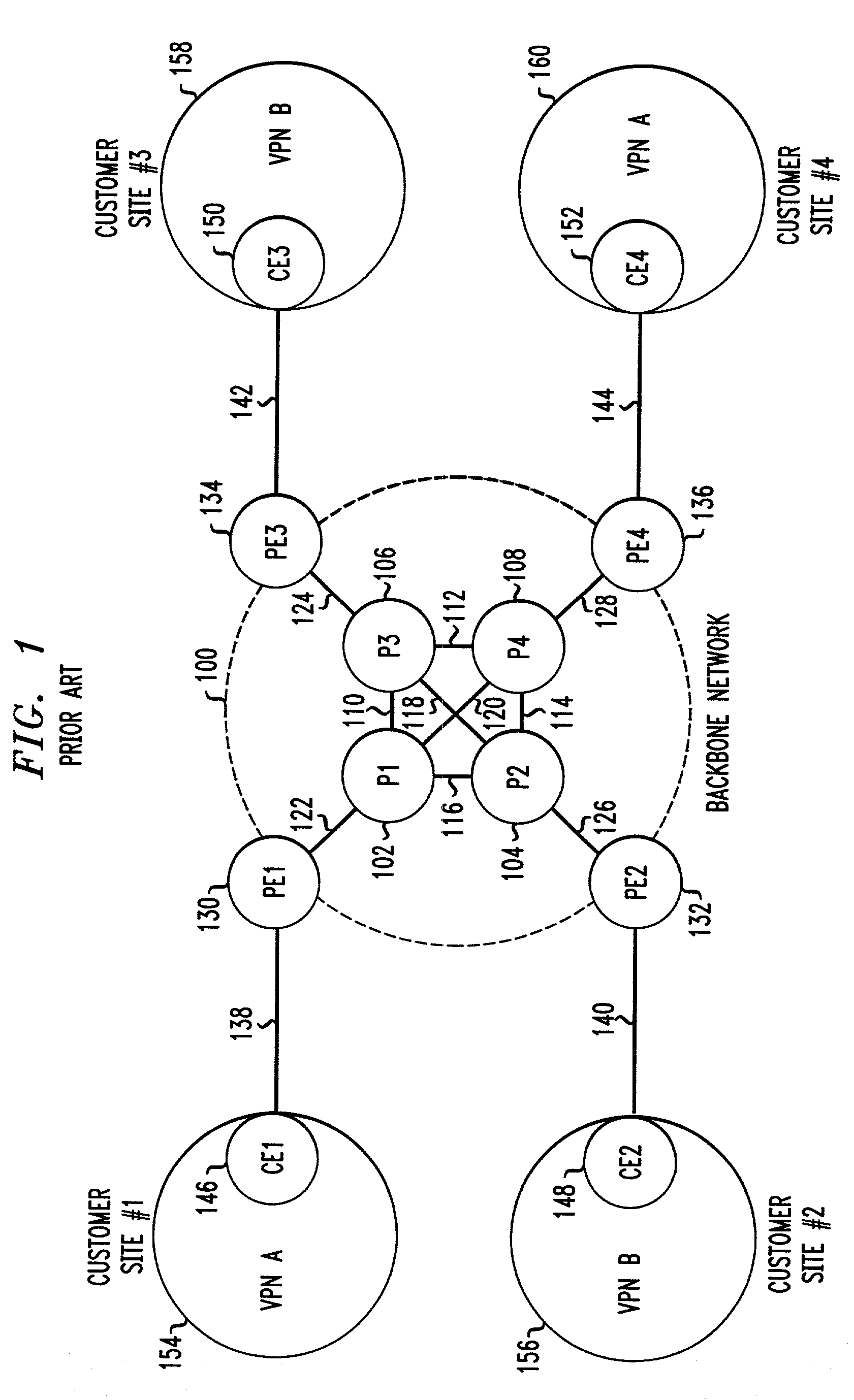
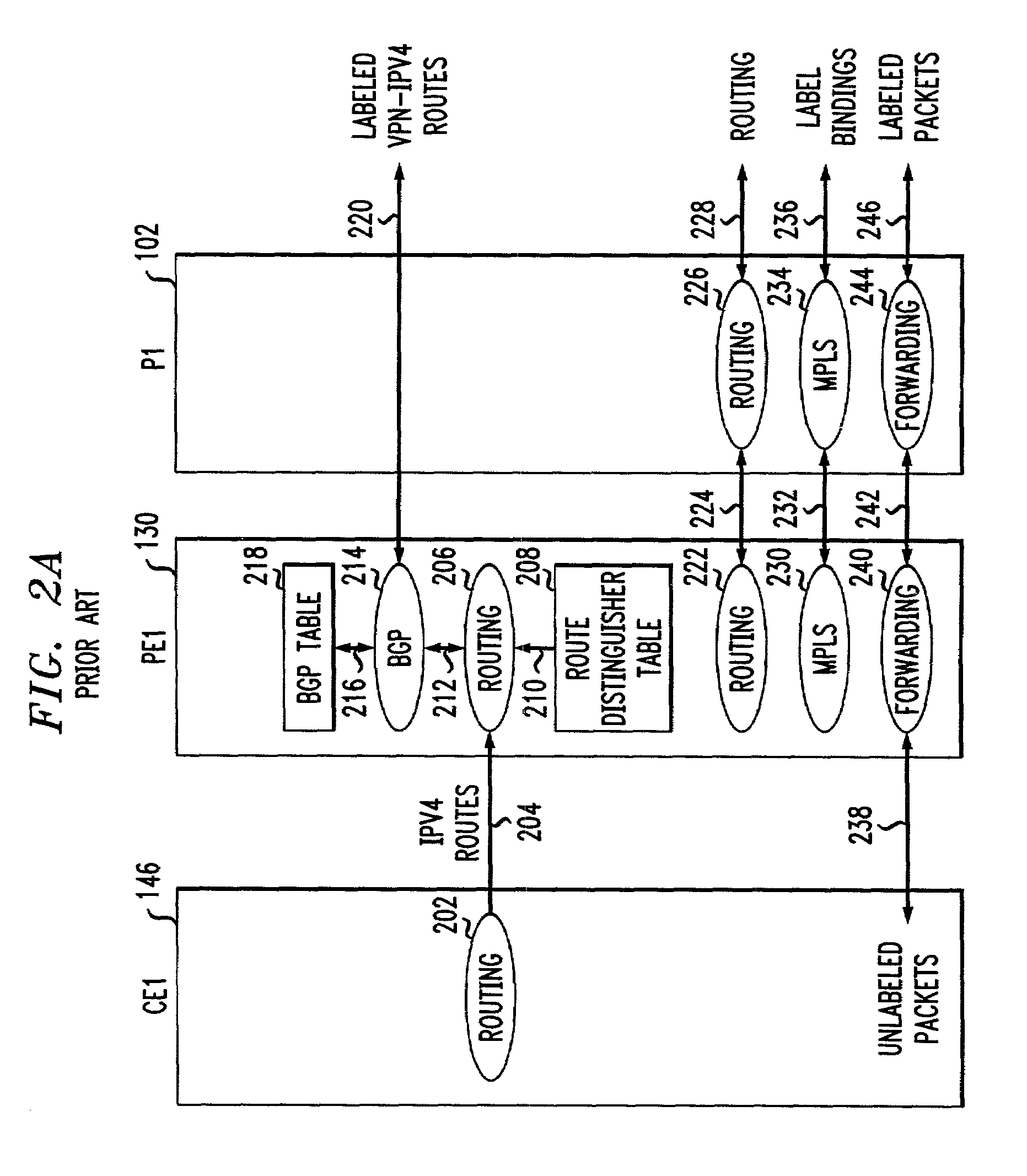
Traffic matrix computation for a backbone network supporting virtual private networks
InactiveUS7027396B1Shorten the timeView accuratelyError preventionTransmission systemsTraffic capacityInternet traffic engineering
This invention provides a more effective method for capacity planning and traffic engineering of packet networks that connect Virtual Private Network (VPN) sites. A distributed architecture efficiently computes traffic matrixes that show the number of bytes and / or packets exchanged among provider edge (PE) routers and / or service nodes. Each PE router in a service node is exports flow records to a Flow Record Processor (FRP) in the same location. The FRPs use these records in conjunction with configuration data extracted from the PE routers to compute partial traffic matrixes. The partial traffic matrixes are uploaded to a Matrix Generator to create a total traffic matrix. The total traffic matrix is essential input for capacity planning or traffic engineering tools.
Owner:AMERICAN TELEPHONE & TELEGRAPH CO
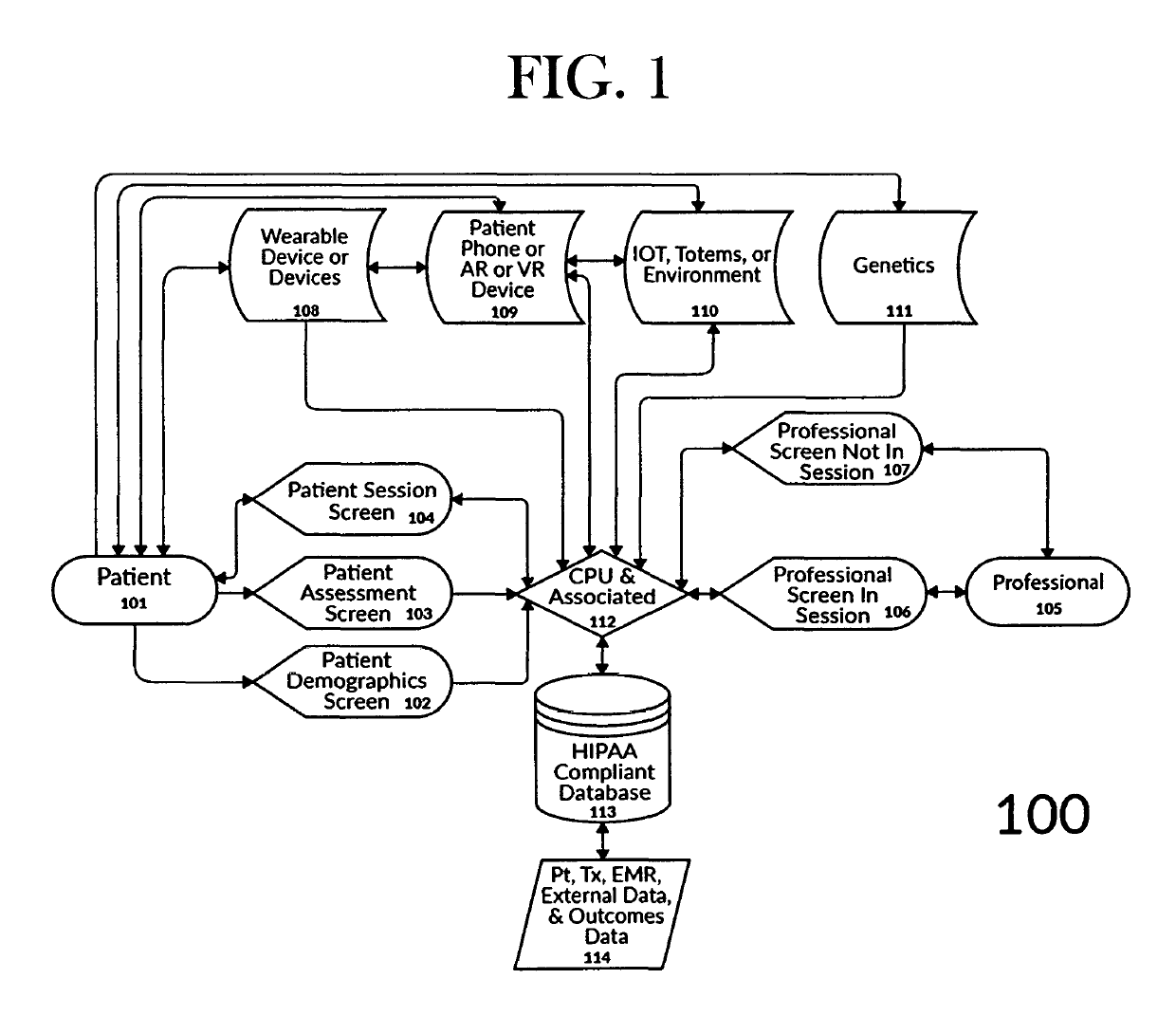
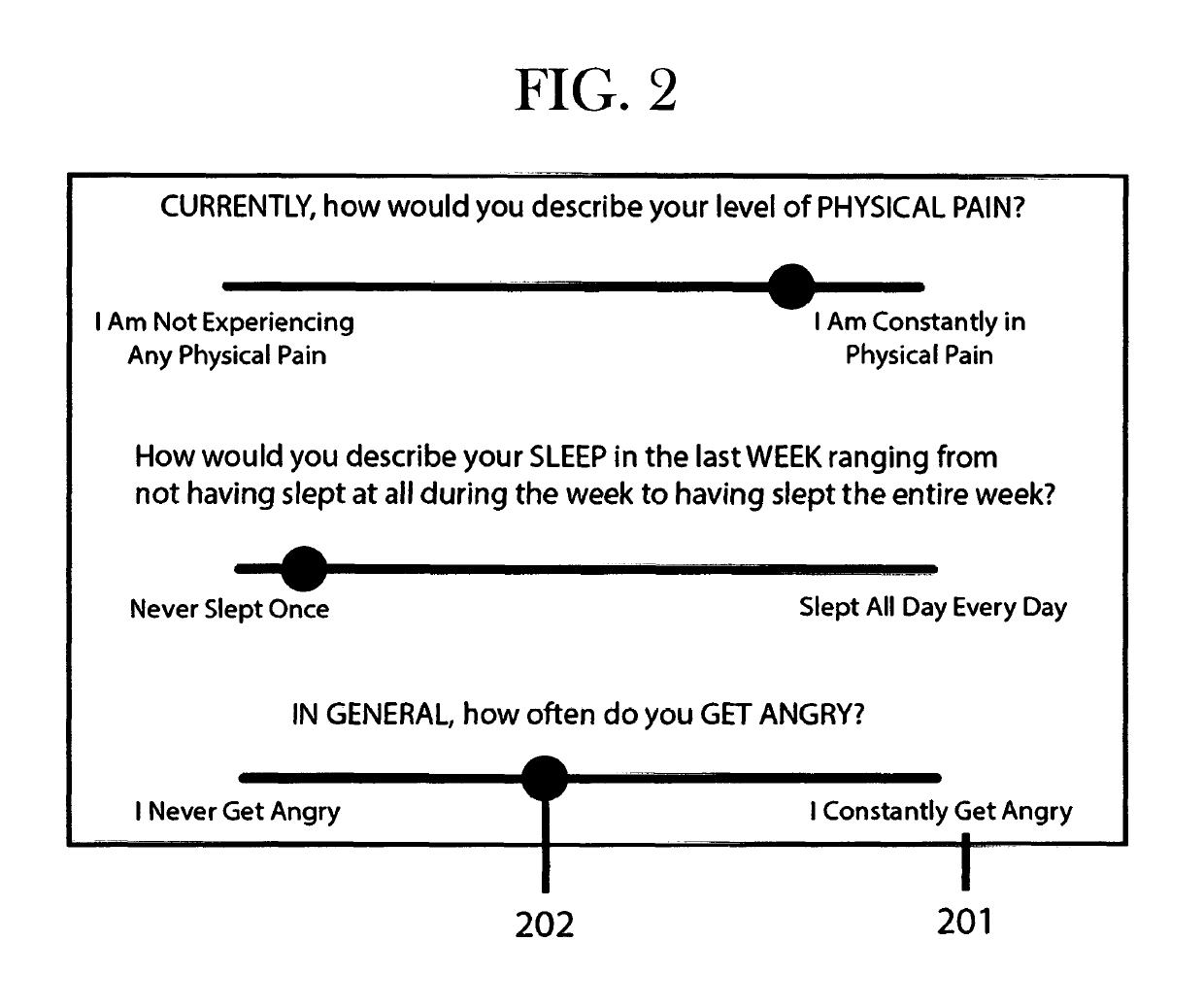
Treatment intelligence and interactive presence portal for telehealth
ActiveUS10325070B2Optimize outcomeOptimize satisfactionMedical imagesMachine learningComputerized systemSmart objects
Owner:THE LIVE NETWORK INC
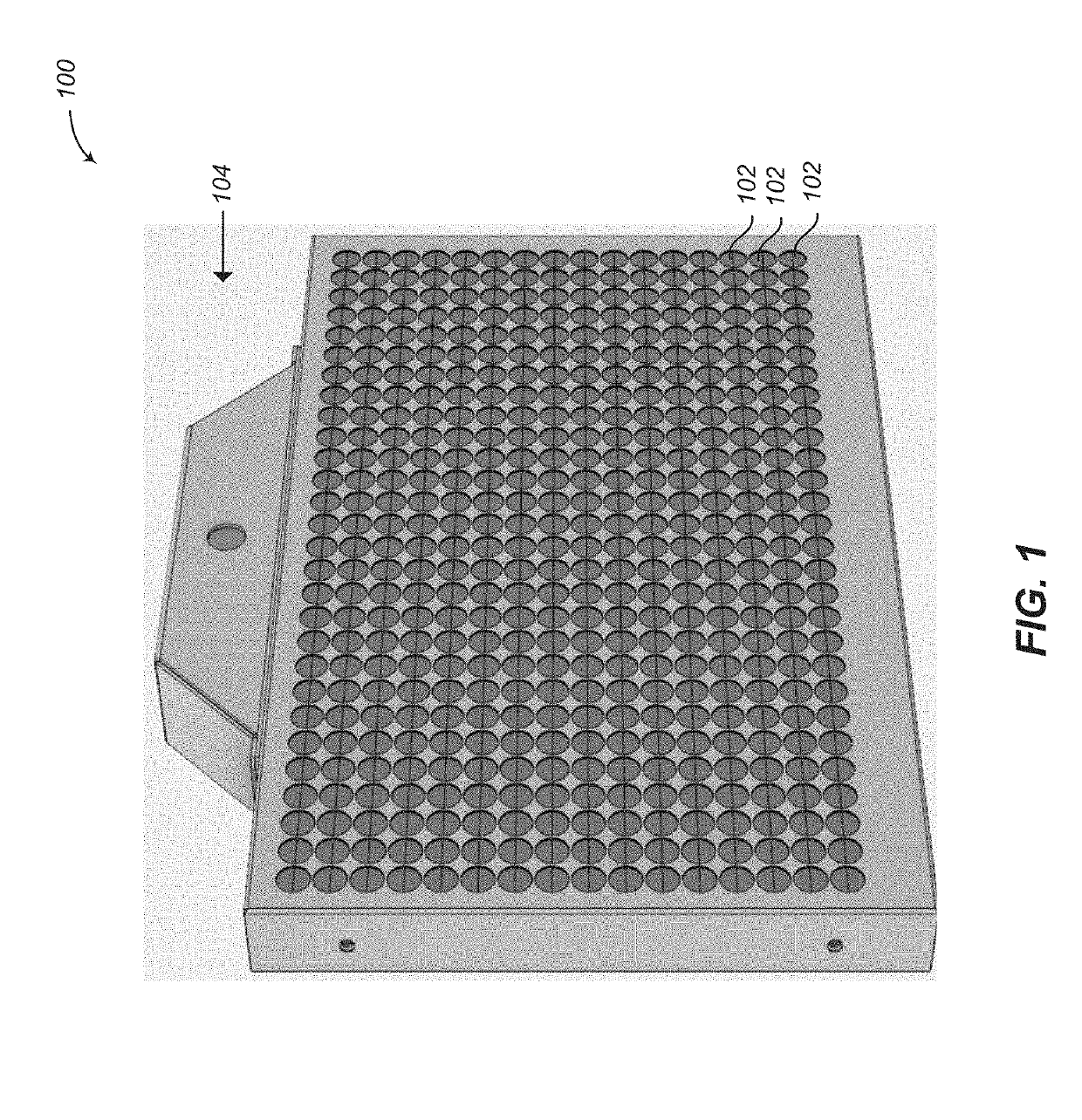
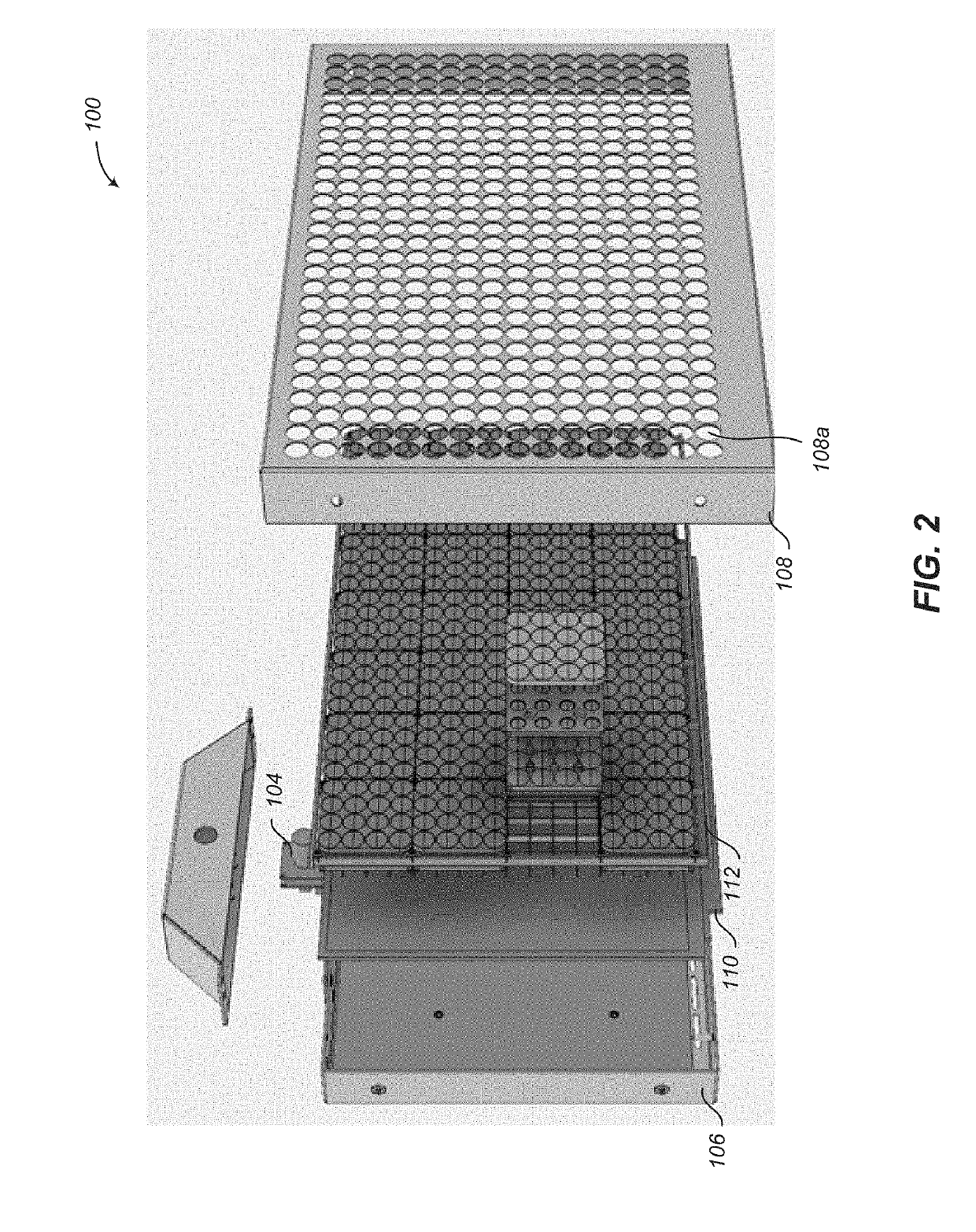
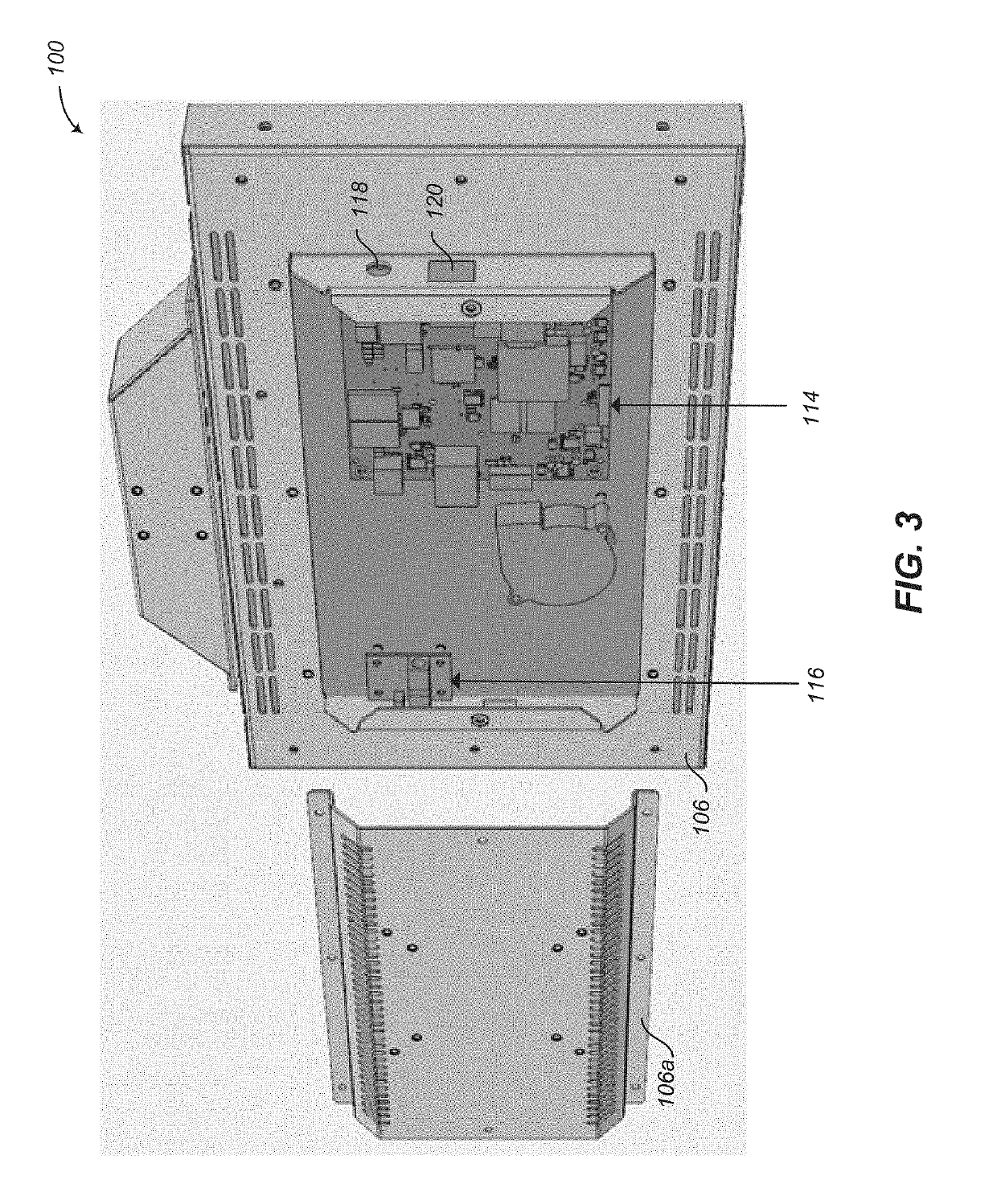
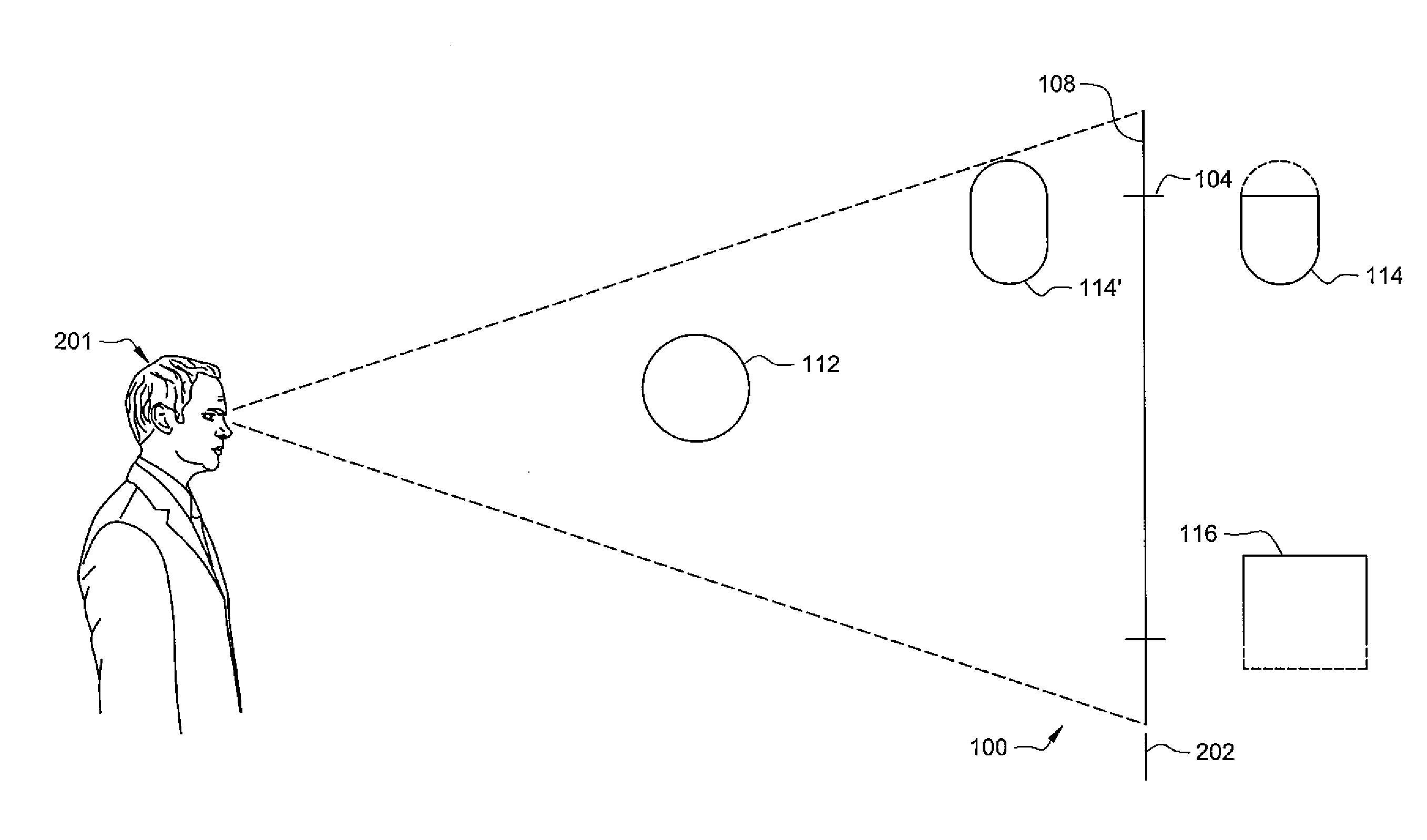
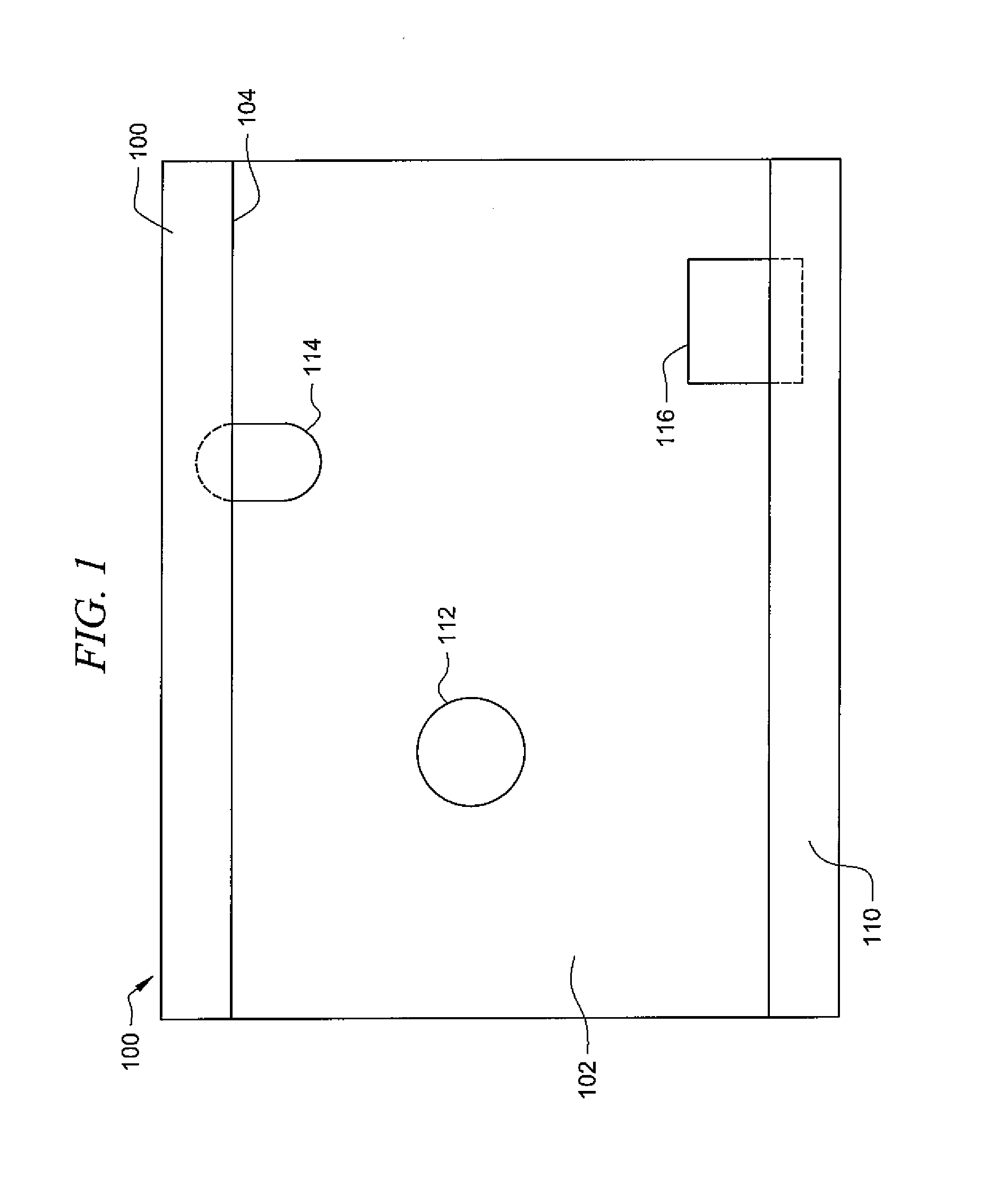
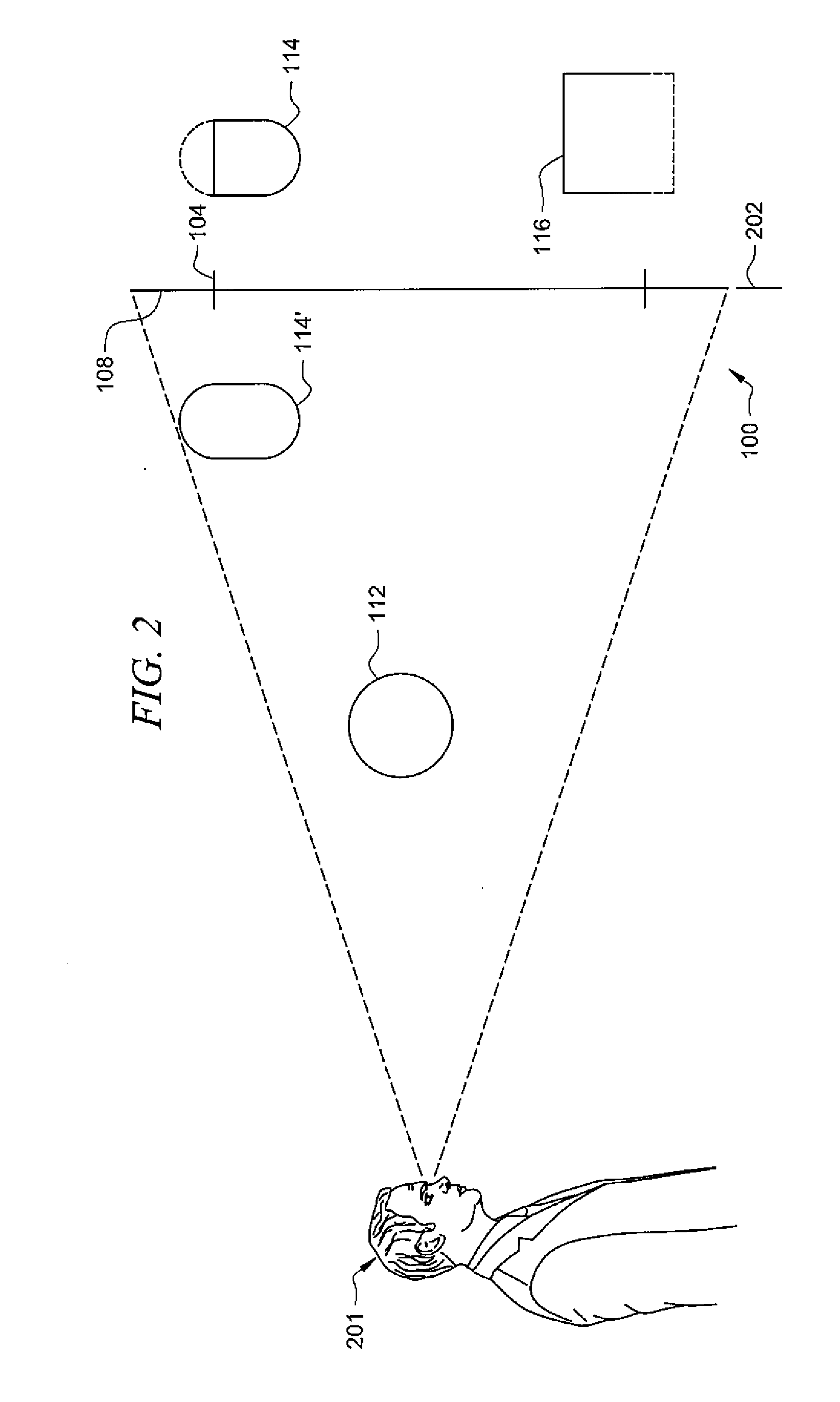
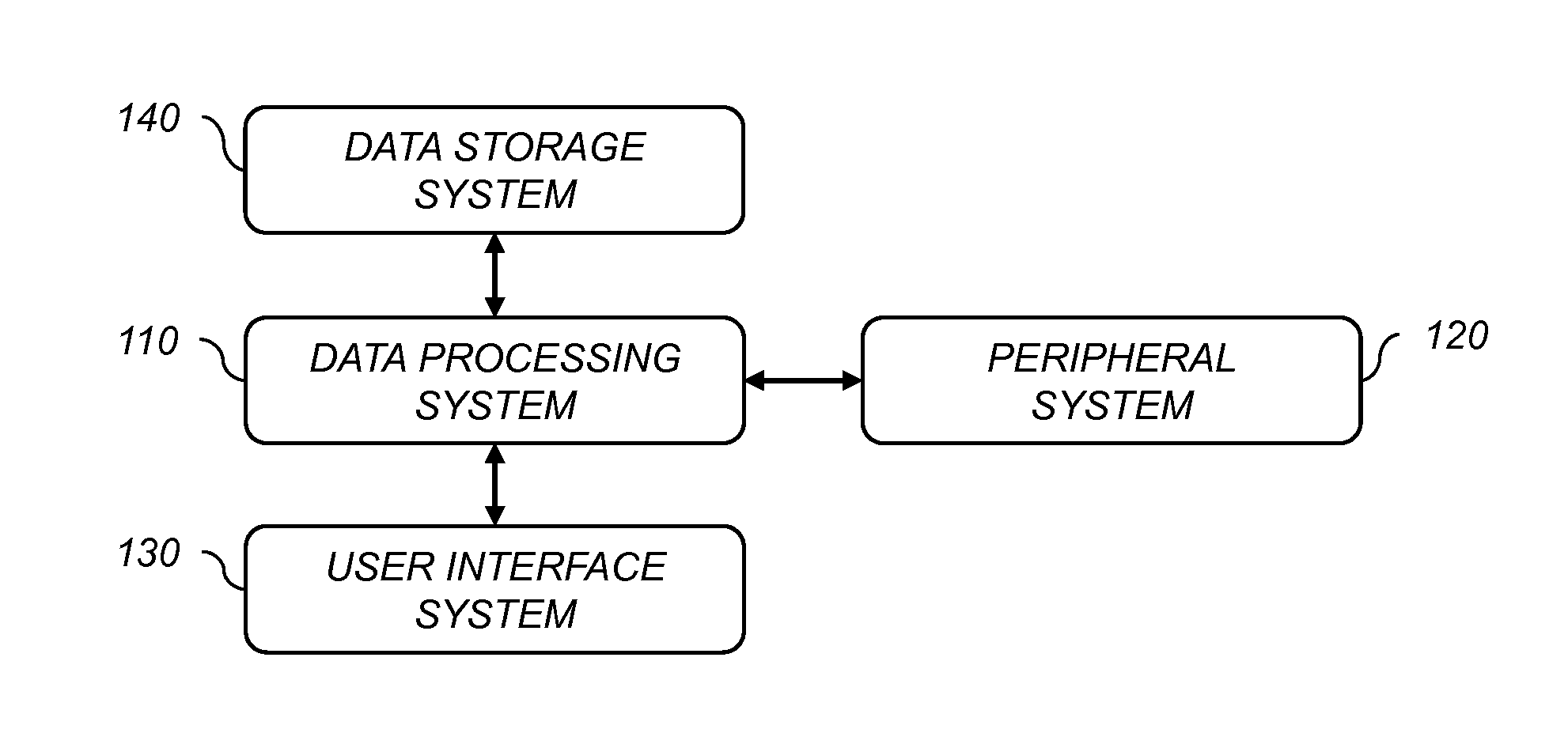
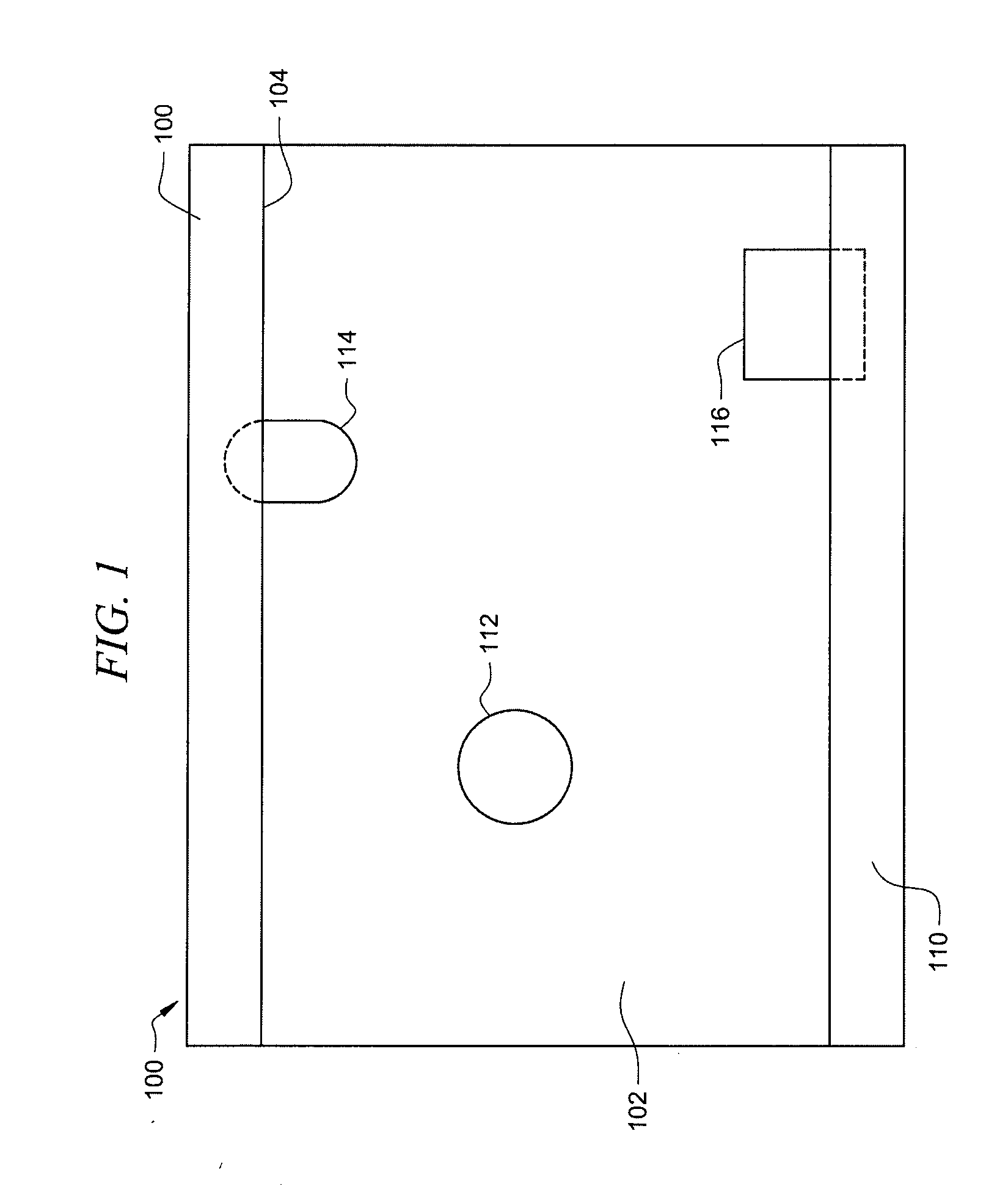
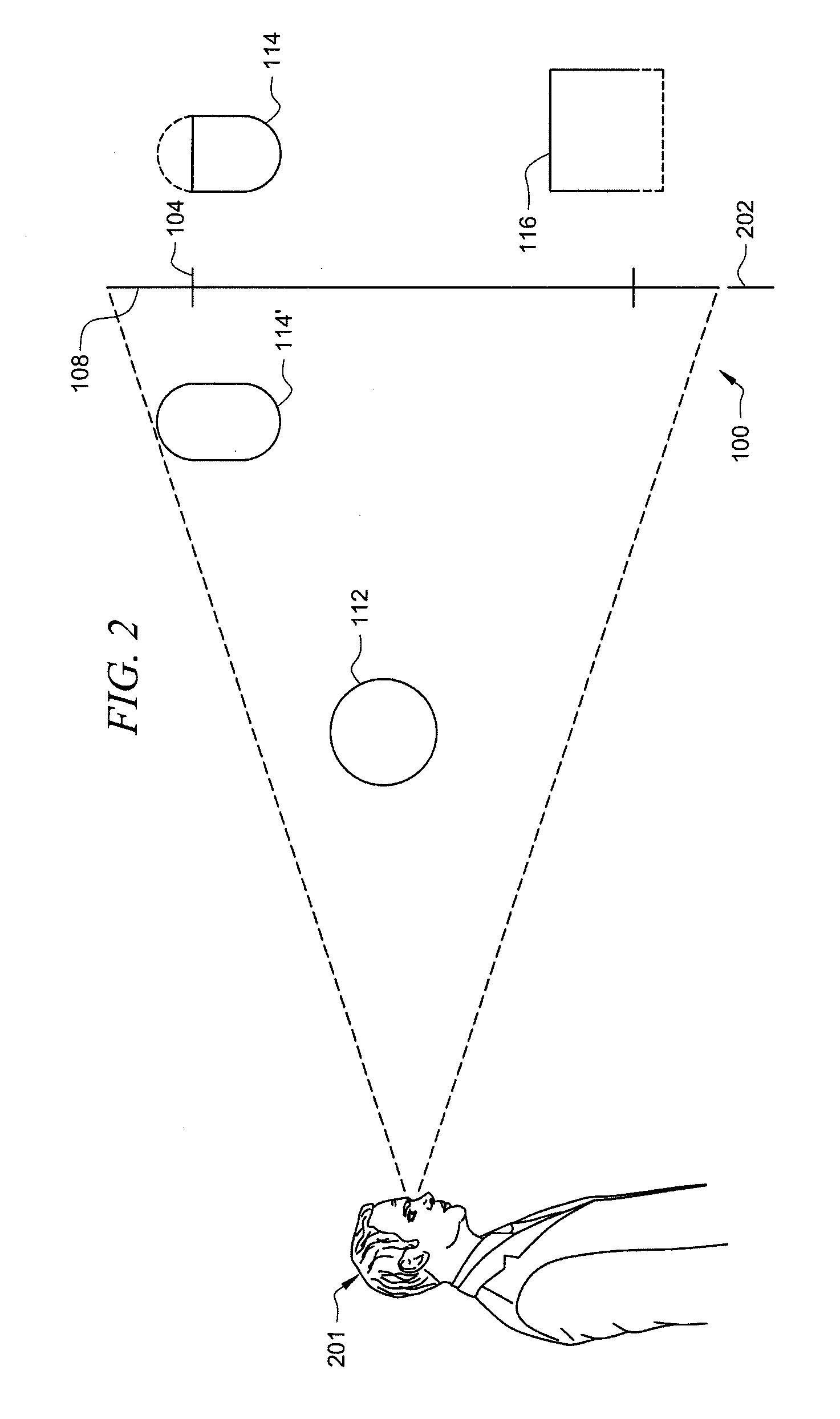
Precision multi-view display
ActiveUS20190149808A1Precise positioningTiling easy and efficientAdvertisingDisplay meansGraphicsWide field
A precision multi-view (MV) display system can accurately and simultaneously display different content to different viewers over a wide field of view. The MV display system may include features that enable individual MV display devices to be easily and efficiently tiled to form a larger MV display. A graphical interface enables a user to graphically specify viewing zones and associate content that will be visible in those zones in a simple manner. A calibration procedure enables the specification of content at precise viewing locations.
Owner:MISAPPLIED SCI INC
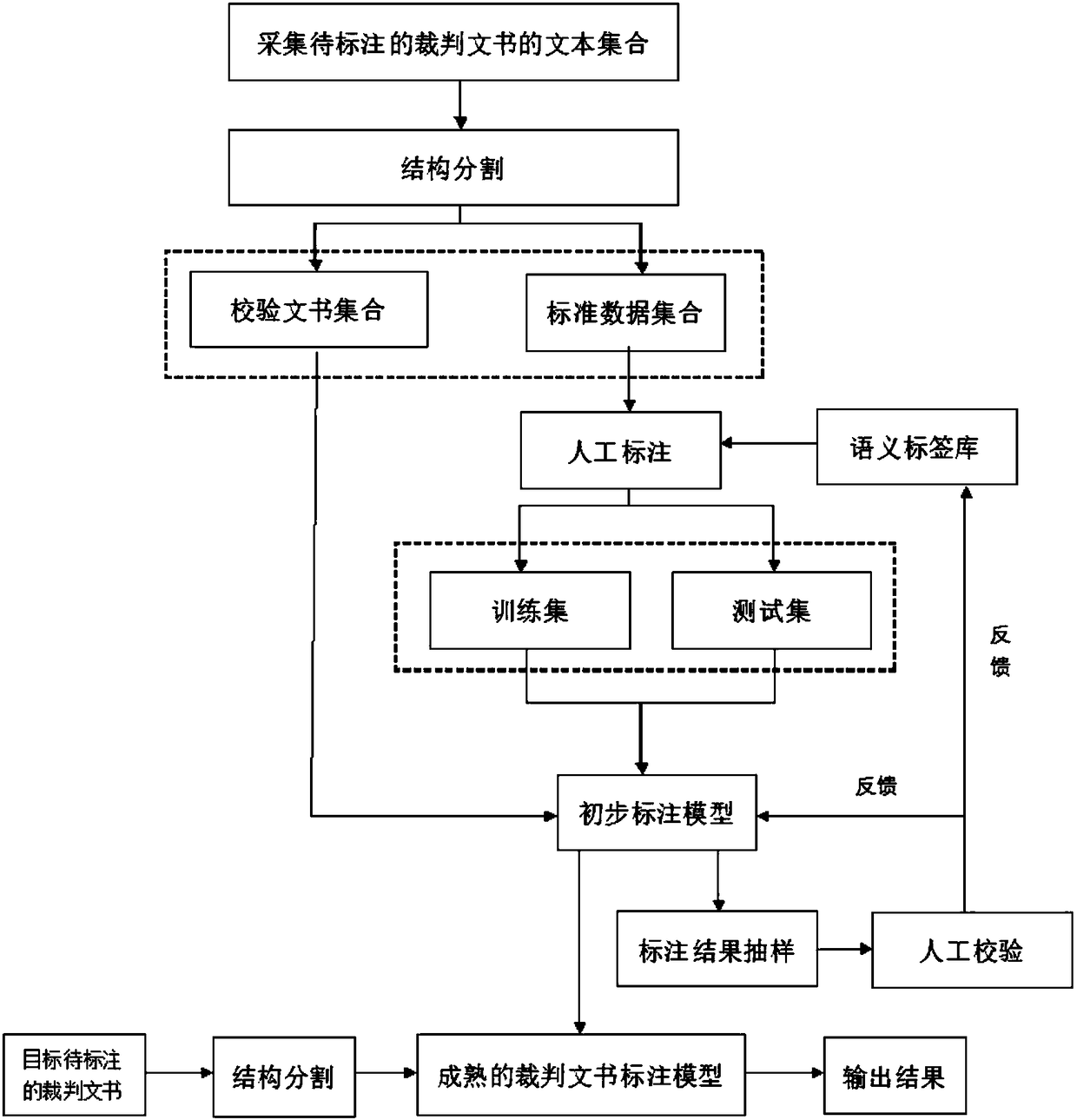
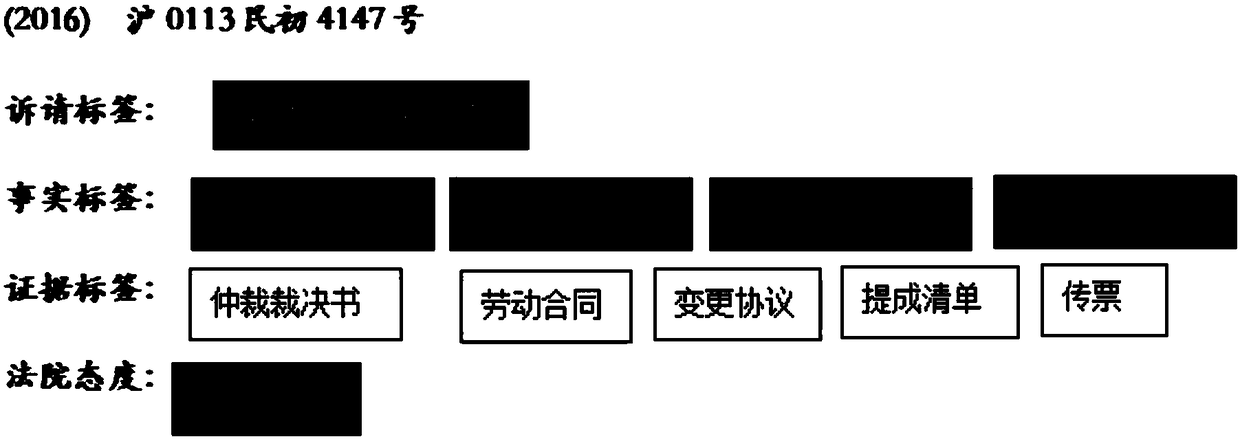
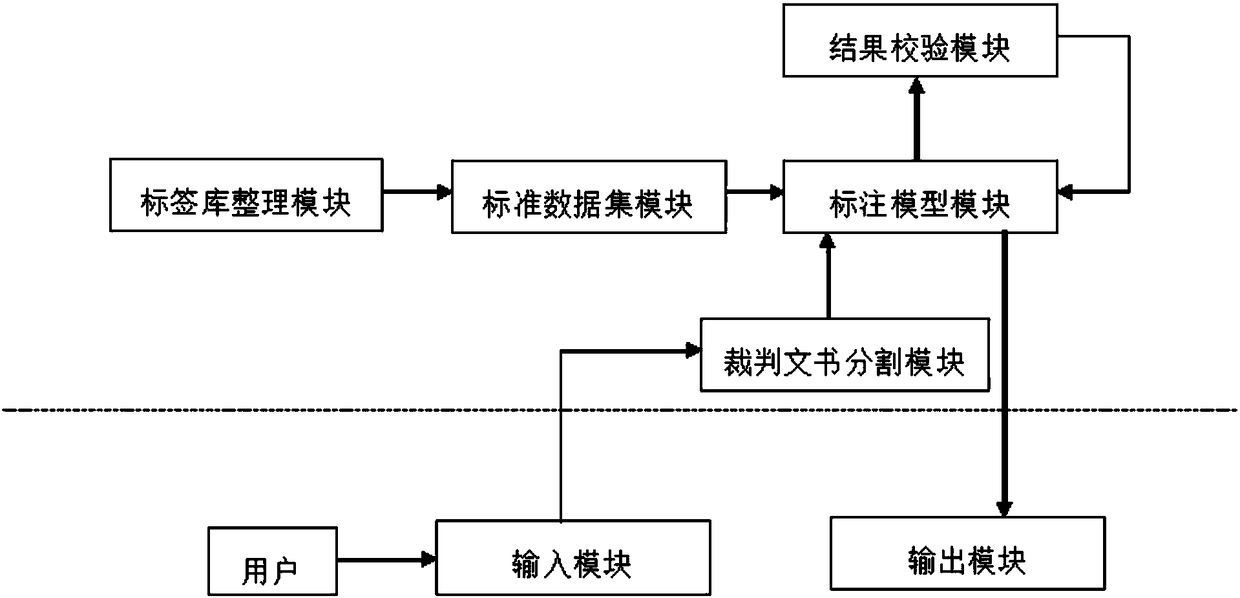
Adjudication document annotation method and device based on machine learning algorithm
ActiveCN108334500AEasy to see visuallyView accuratelySemantic analysisSpecial data processing applicationsManual annotationDocument model
The invention discloses an adjudication document annotation method and device based on a machine learning algorithm. The method comprises the following steps that: collecting the text set of adjudication documents to be annotated; carrying out structure segmentation on texts in the text set; establishing a semantic tag library; on the basis of the semantic tag library, carrying out manual annotation on the adjudication documents to be annotated; selecting parts of adjudication documents subjected to the manual annotation as a standard dataset to be handed for machine learning, and training andoptimizing a preliminary annotation model; selecting residual parts of adjudication document models subjected to the manual annotation to obtain a mature adjudication document annotation model; and after a target adjudication document to be annotated is segmented, inputting into the mature adjudication document annotation model to obtain an annotation result. Through the method, the problem in the relevant art that adjudication document legal elements are not completely extracted and case information extraction accuracy is low is solved.
Owner:江西思贤数据科技有限公司
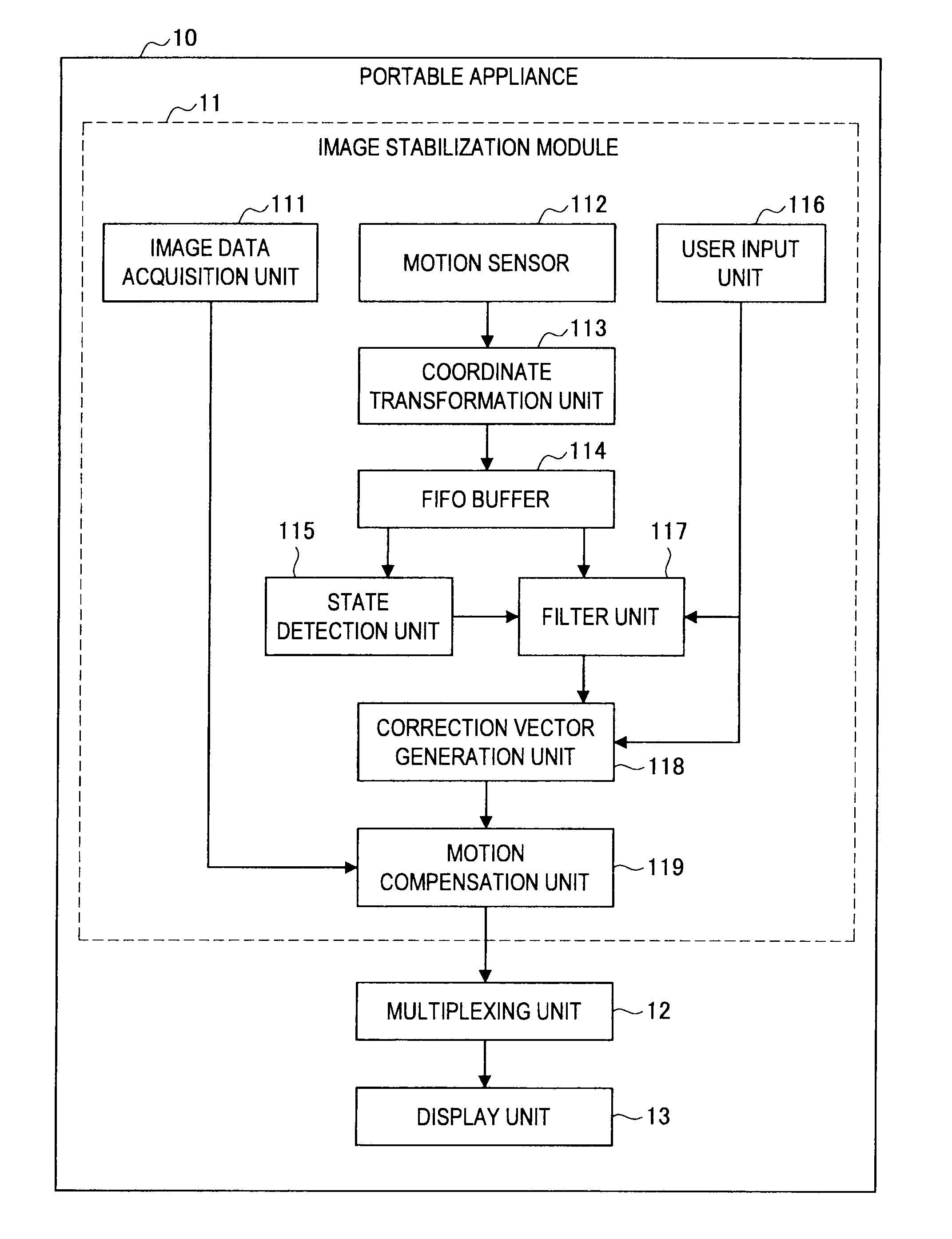
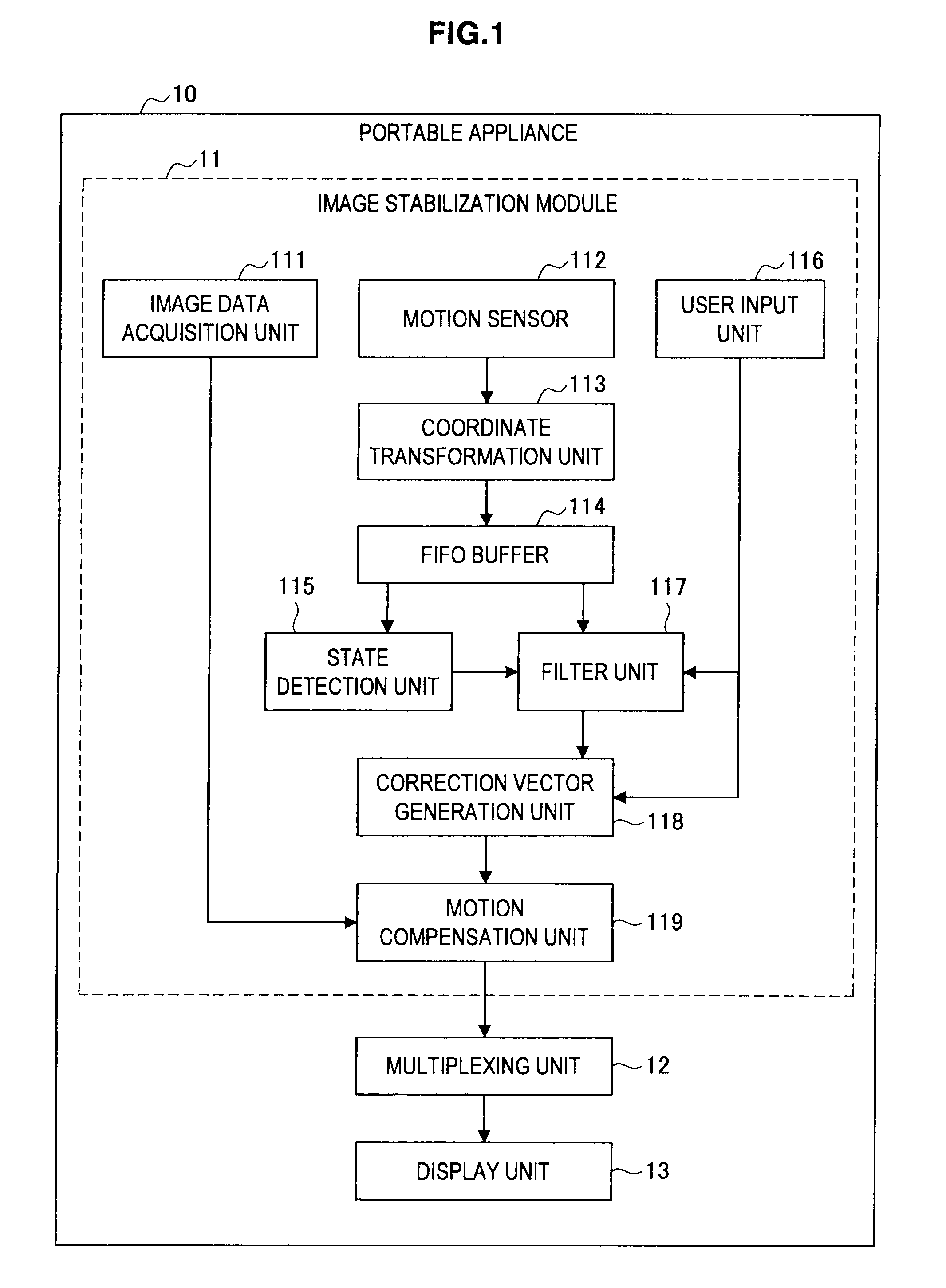
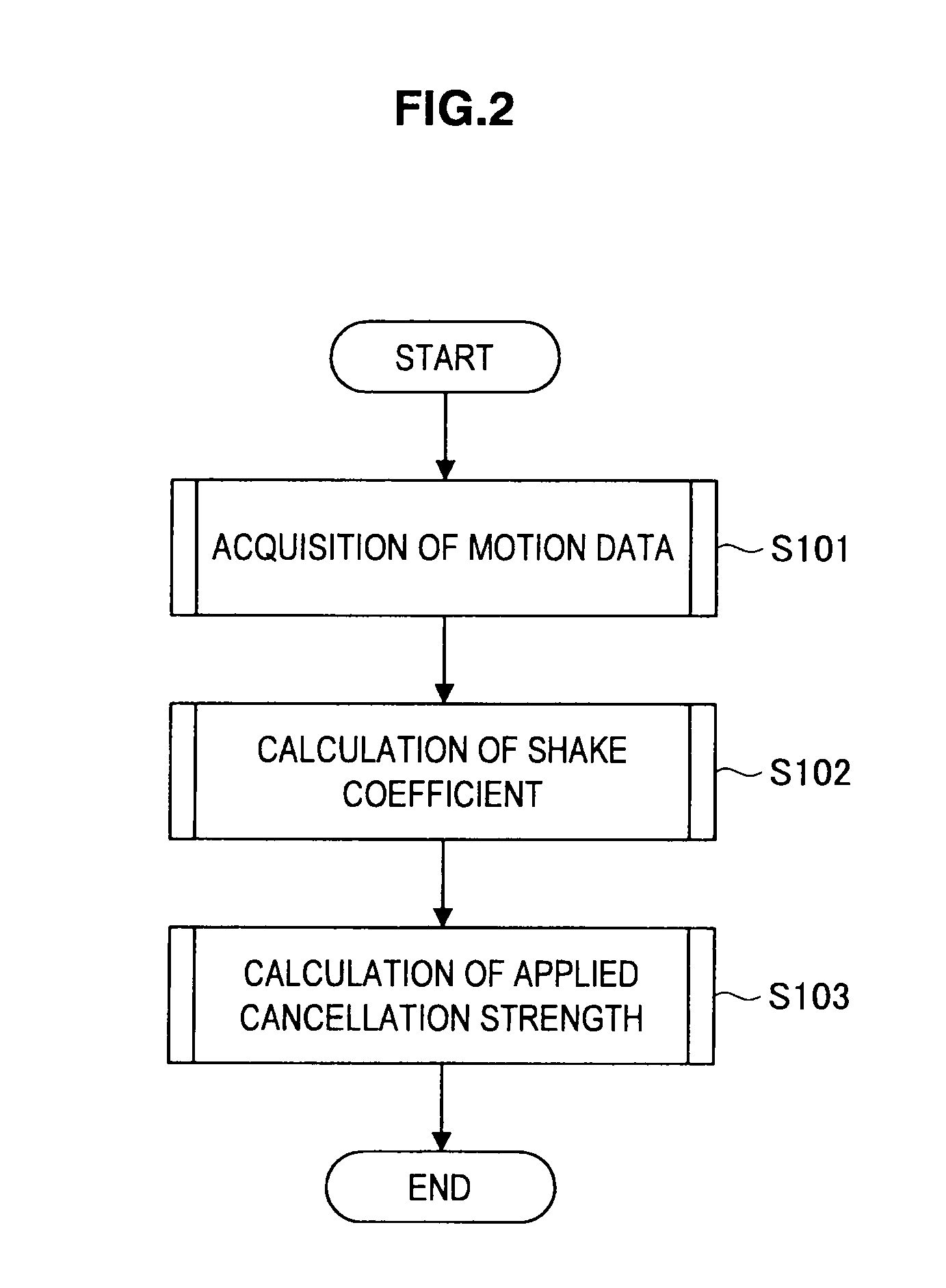
Image stabilization device, image stabilization method, and program
ActiveUS20110298937A1Reduce shakingReduce fatigueTelevision system detailsColor television detailsData displayExecution control
Provided is an image stabilization device including a motion sensor for detecting motion data, an image data display unit for displaying image data, a shake coefficient calculation unit for calculating a shake coefficient indicating intensity of shaking based on time-series motion data detected by the motion sensor, and a motion correction unit for performing control on the image data display unit to move the image data in a direction of cancelling the shaking in a case the shake coefficient calculated by the shake coefficient calculation unit becomes less than a predetermined first threshold.
Owner:SONY CORP
Device and method for minimally invasive spinal intervention
ActiveUS20110184234A1View accuratelyInternal osteosythesisCannulasBiomedical engineeringSpinal column
The invention proposes a device for minimally invasive intervention in the skeletal region, in particular on the spinal column, having at least the following two elements:a cannula with a distal end generally bevelled in shape (22) relative to a symmetrical axis of the cutting tool (2); andan optical probe (endoscope) for insertion through the cavity of the cannula.The device is further characterized in that the cannula takes the form of a hollow cutting tool (2), in which the most distal region of the distal end comprises a cutting edge (26), which is incorporated into the edge of the wall of the cutting tool (2).
Owner:JOIMAX GMBH
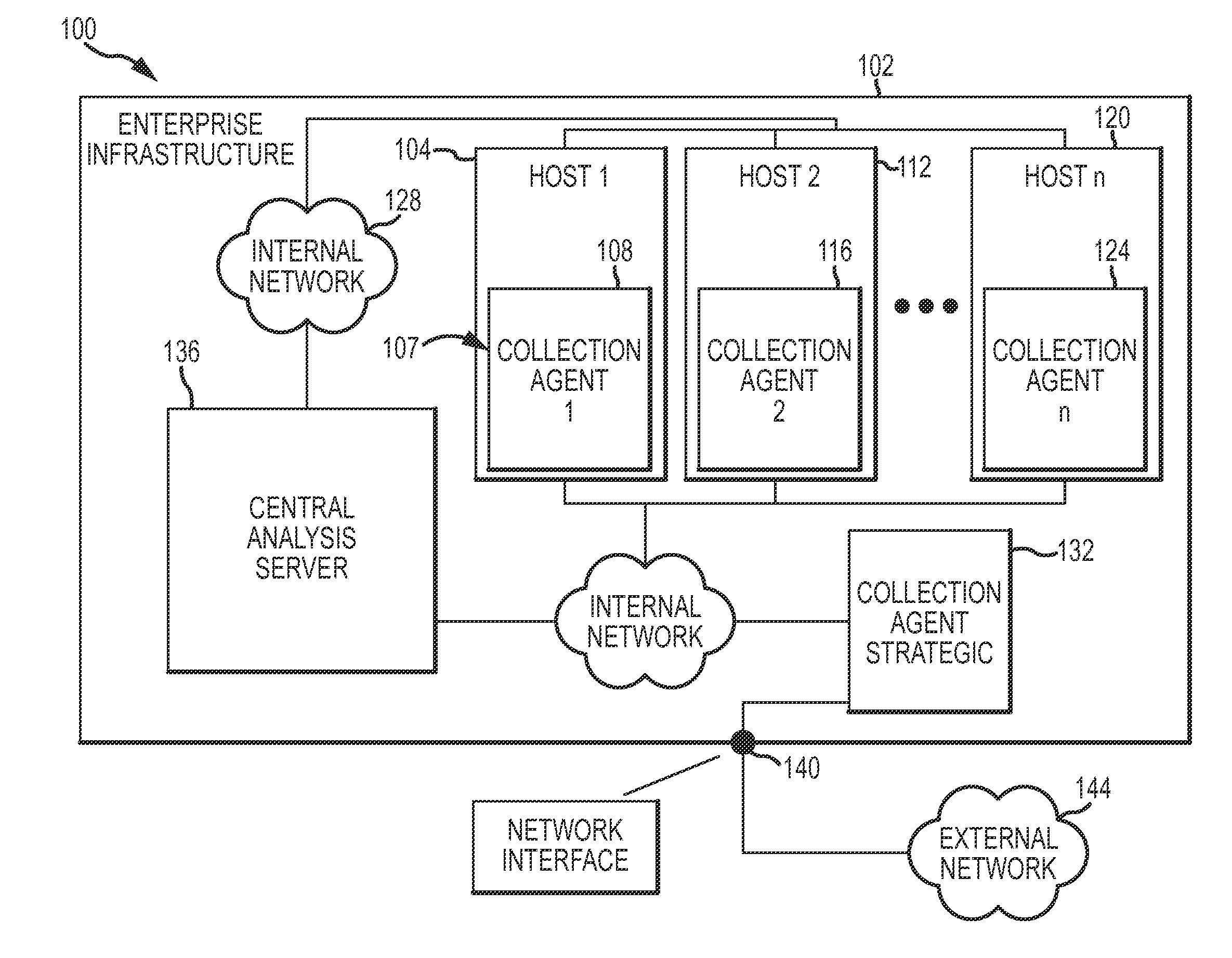
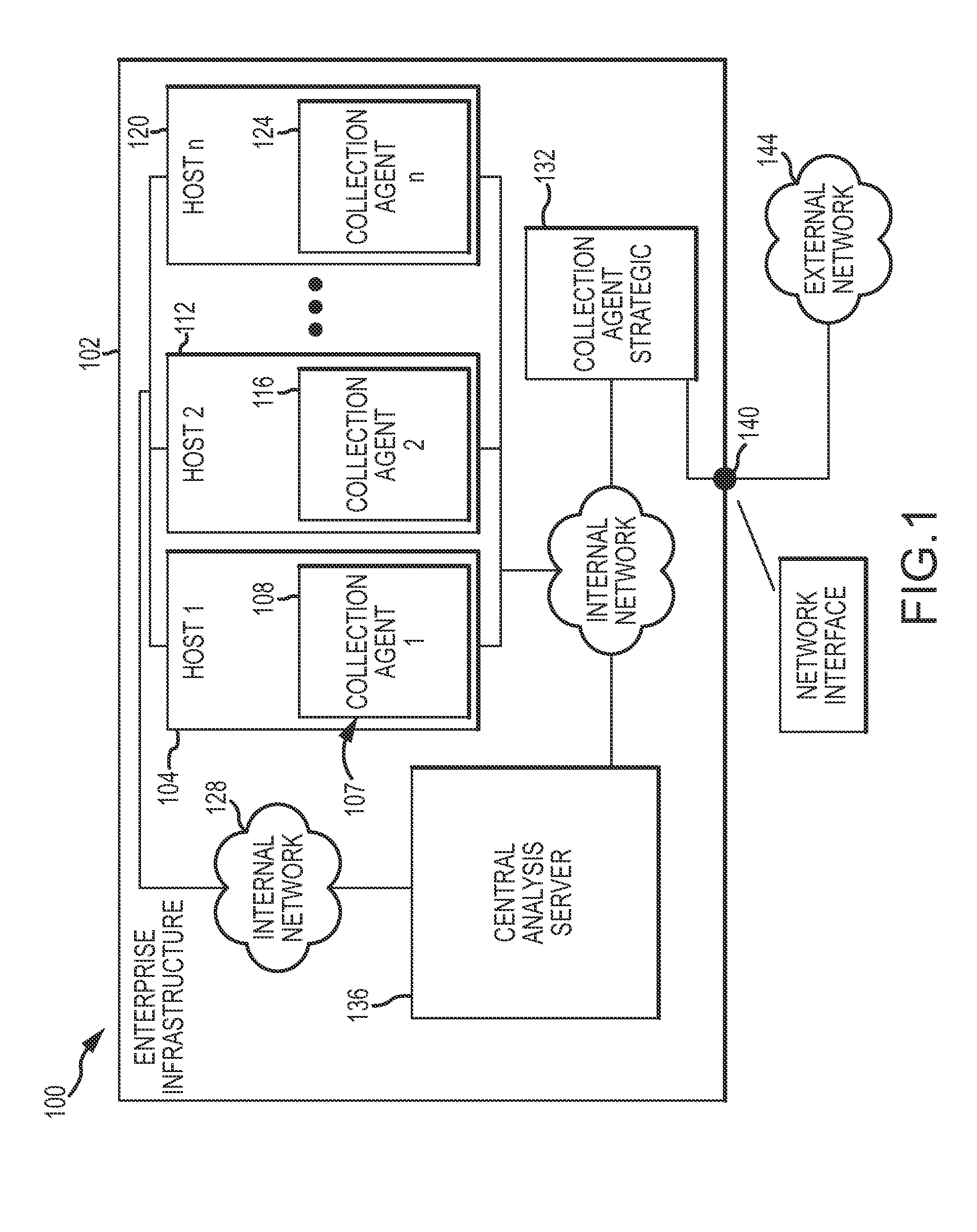
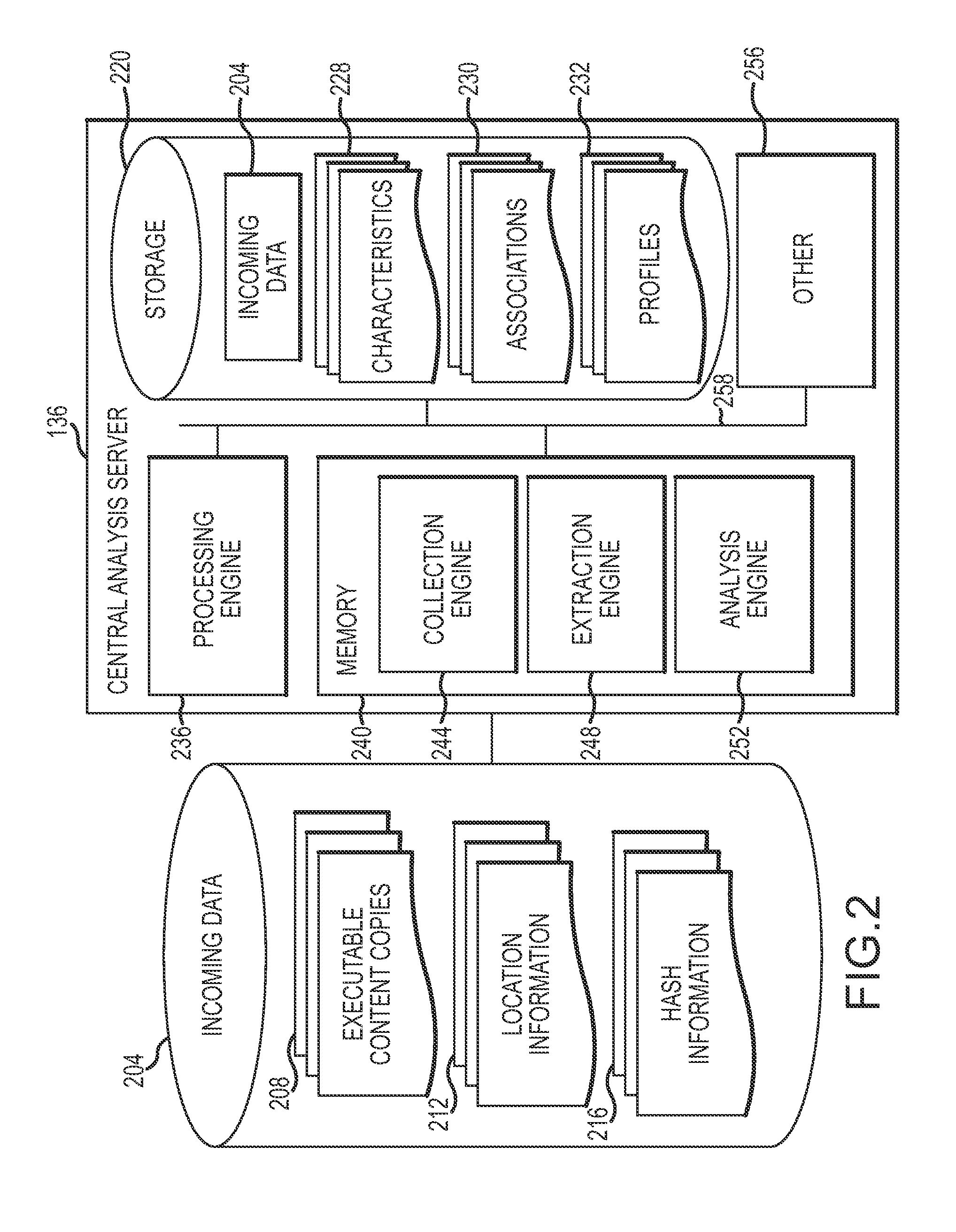
Composite analysis of executable content across enterprise network
ActiveUS20150047034A1Proactive defenseProactive responseMemory loss protectionError detection/correctionByteEnterprise networking
Identification, characterization and attribution of executable content within and across an enterprise infrastructure (e.g., hosts, subnets, routers, etc.) to provide situational awareness for cyber security for purposes of supporting proactive defense and response. Copies of executable content collected at one or more locations within an infrastructure (e.g., hosts, network edges, etc.) may be passed to a central analysis server whereby various characteristics of the executable content may be extracted or gleaned from the copies such as author marks (e.g., directory names), tool marks (e.g., compiler settings), behaviors (e.g., function extraction), patterns (e.g., byte sequences), text, and / or the like. The characteristics may be analyzed in various manners to build profiles of actors or organizations associated with (e.g., responsible for) executable content within the enterprise infrastructure.
Owner:LOCKHEED MARTIN CORP
System and method for using off-screen mask space to provide enhanced viewing
InactiveUS20080225059A1Enhance visual propertyView accuratelyCathode-ray tube indicatorsSteroscopic systemsComputer graphics (images)Display device
Methods and apparatuses for compensating for clipped portions of one or more objects in an image provide a boundary mask portion adjacent to one or more edges of an image display. The boundary mask portion is used to display information which will fill clipped portions of the objects in the image.
Owner:CONVERSION WORKS
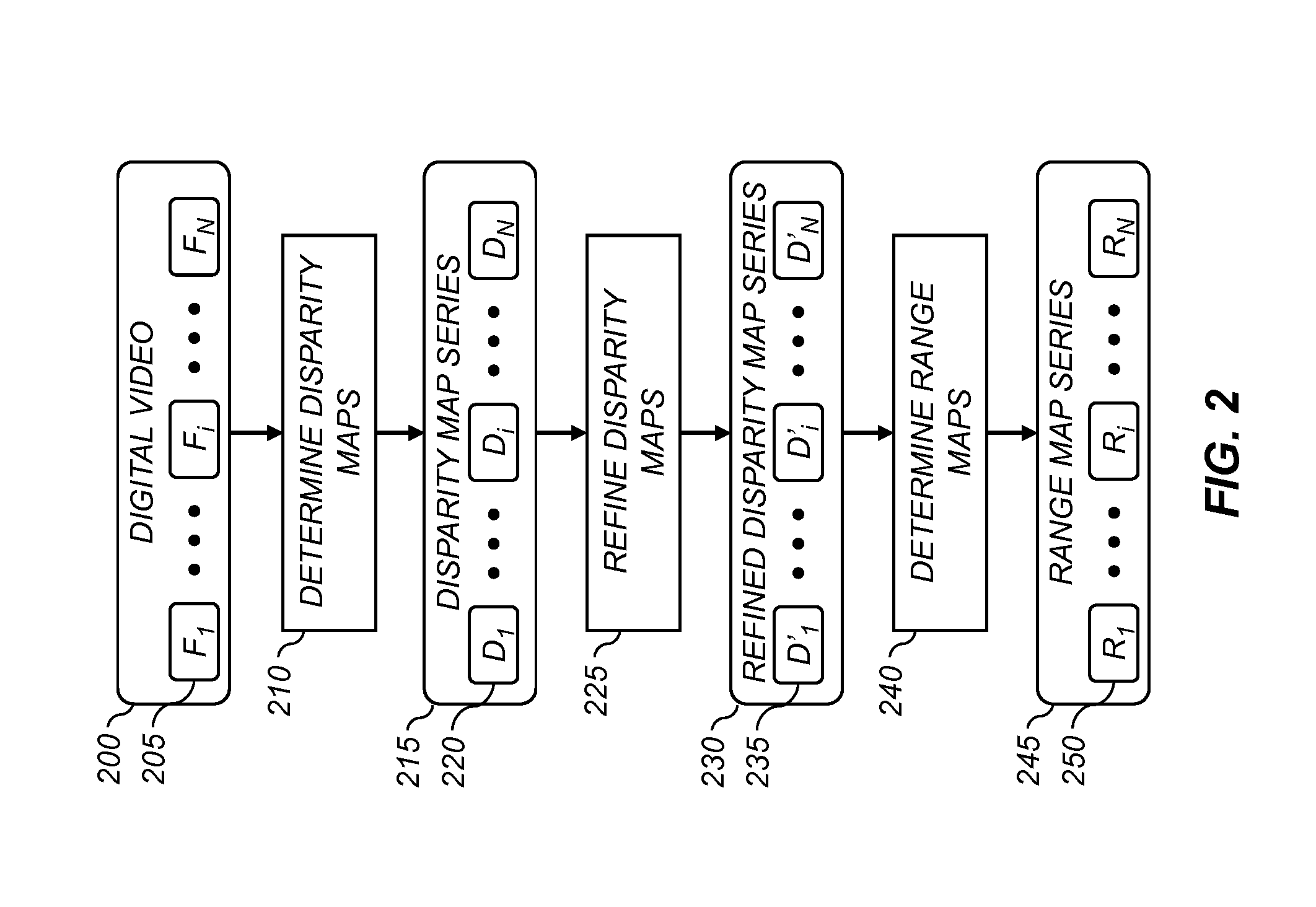
Method for stabilizing a digital video
A method for stabilizing an input digital video. Input camera positions are determined for each of the input video frames, and an input camera path is determined representing input camera position as a function of time. A smoothing operation is applied to the input camera path to determine a smoothed camera path, and a corresponding sequence of smoothed camera positions. A stabilized video frame is determined corresponding to each of the smoothed camera positions by: selecting an input video frame having a camera position near to the smoothed camera position; warping the selected input video frame responsive to the input camera position; warping a set of complementary video frames captured from different camera positions than the selected input video frame; and combining the warped input video frame and the warped complementary video frames to form the stabilized video frame.
Owner:APPLE INC
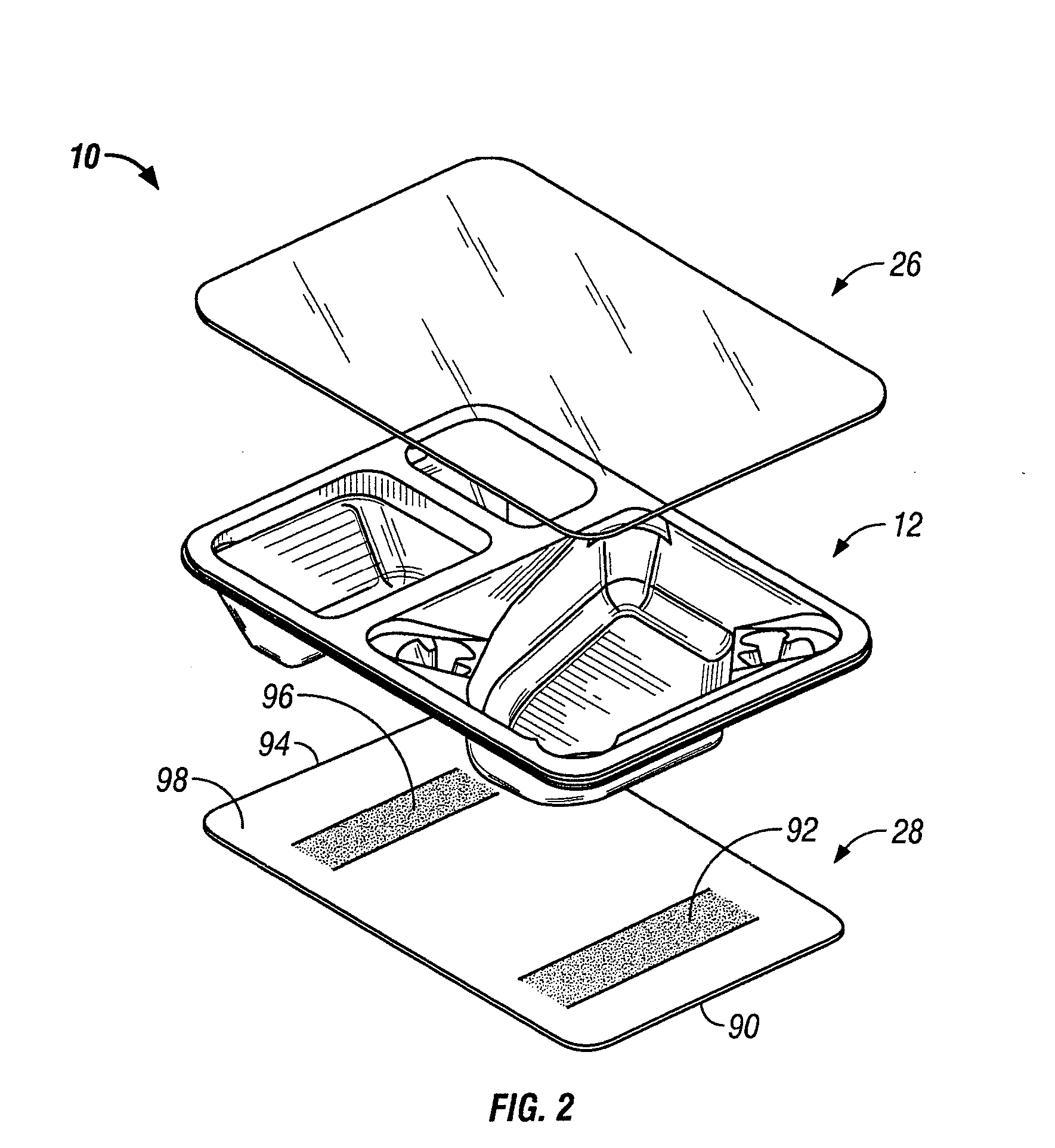
Food package
InactiveUS20060151339A1Optimize locationMinimizing any thinningTobacco devicesTray containersProcess engineeringFood packaging
Owner:INTERCONTINENTAL GREAT BRANDS LLC
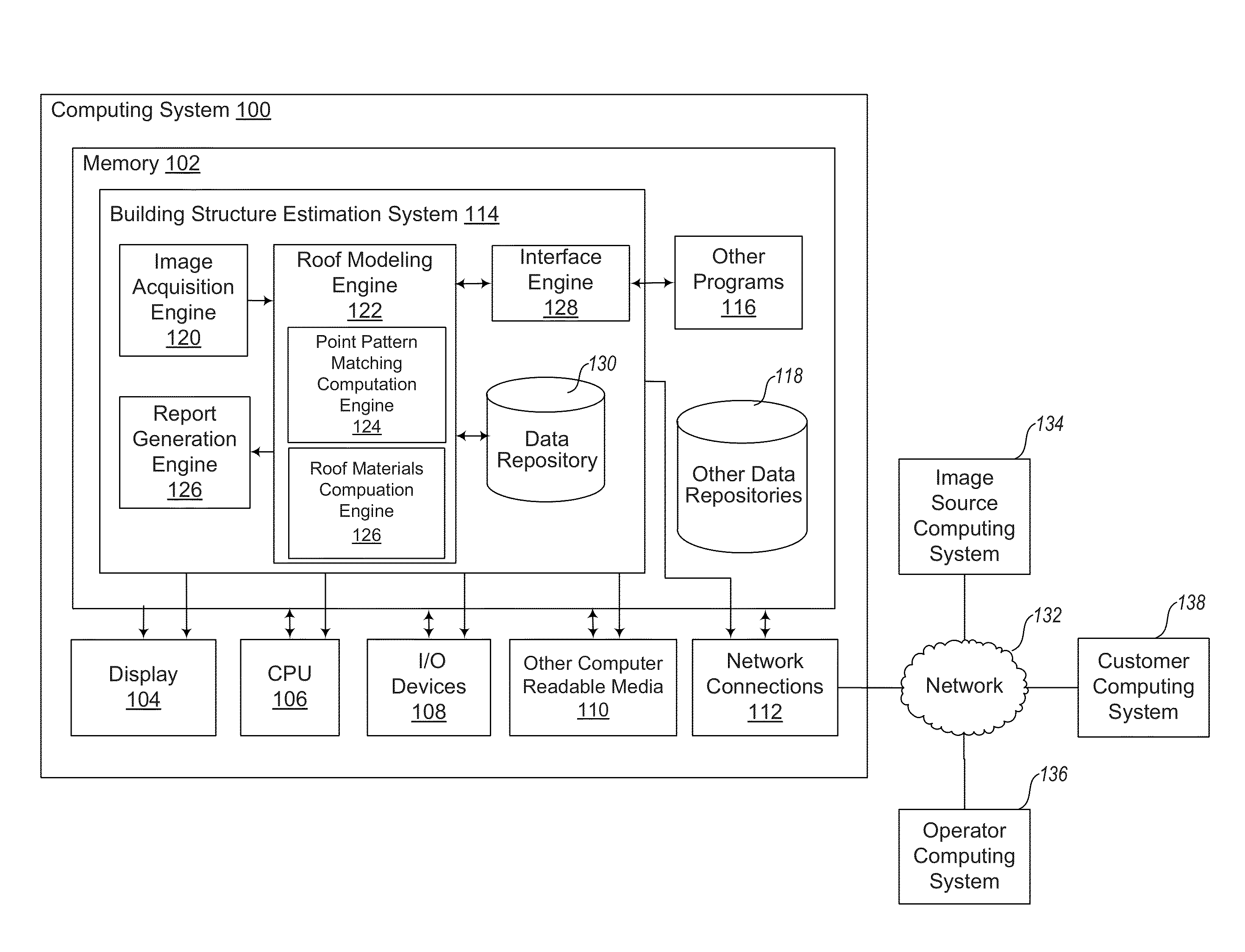
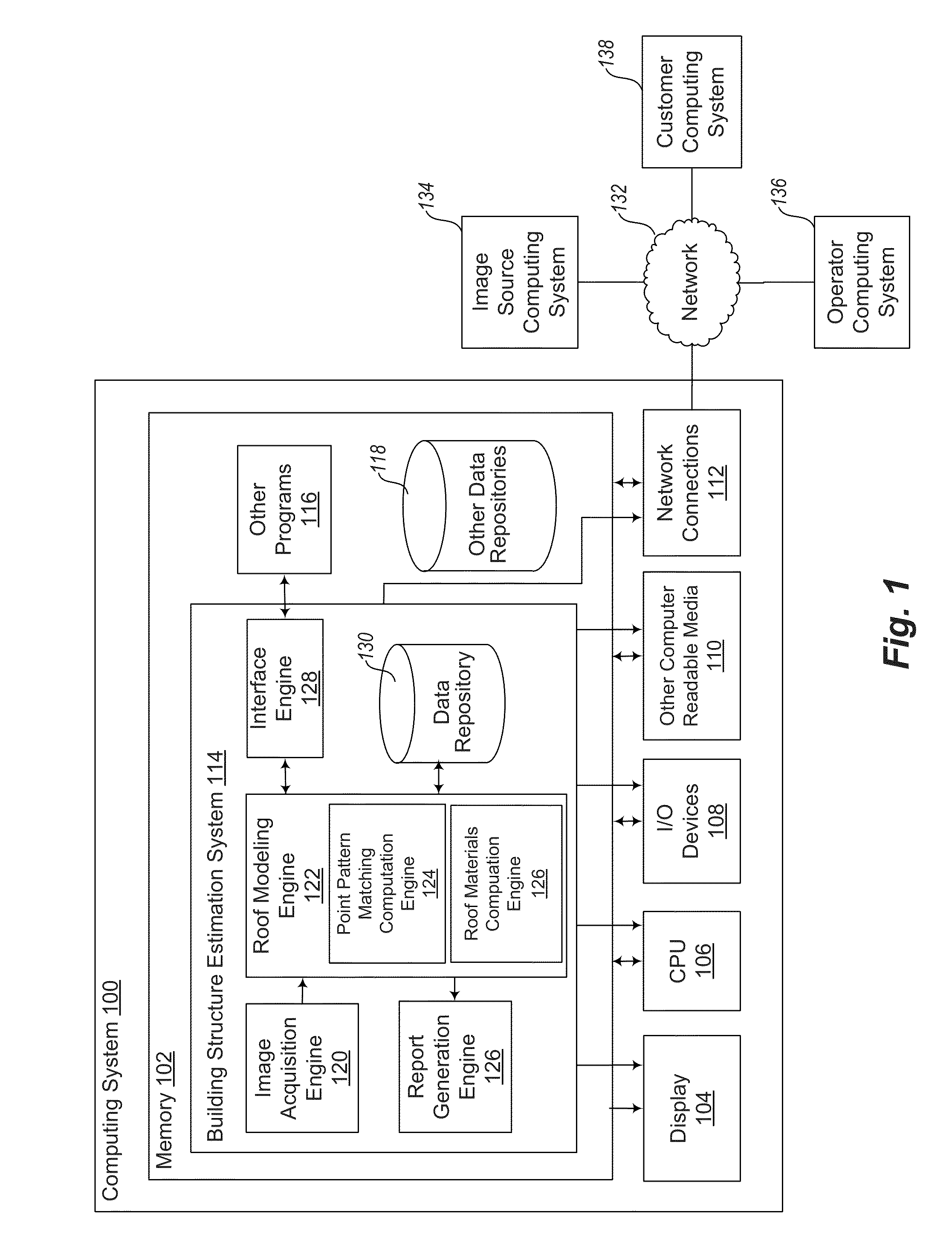
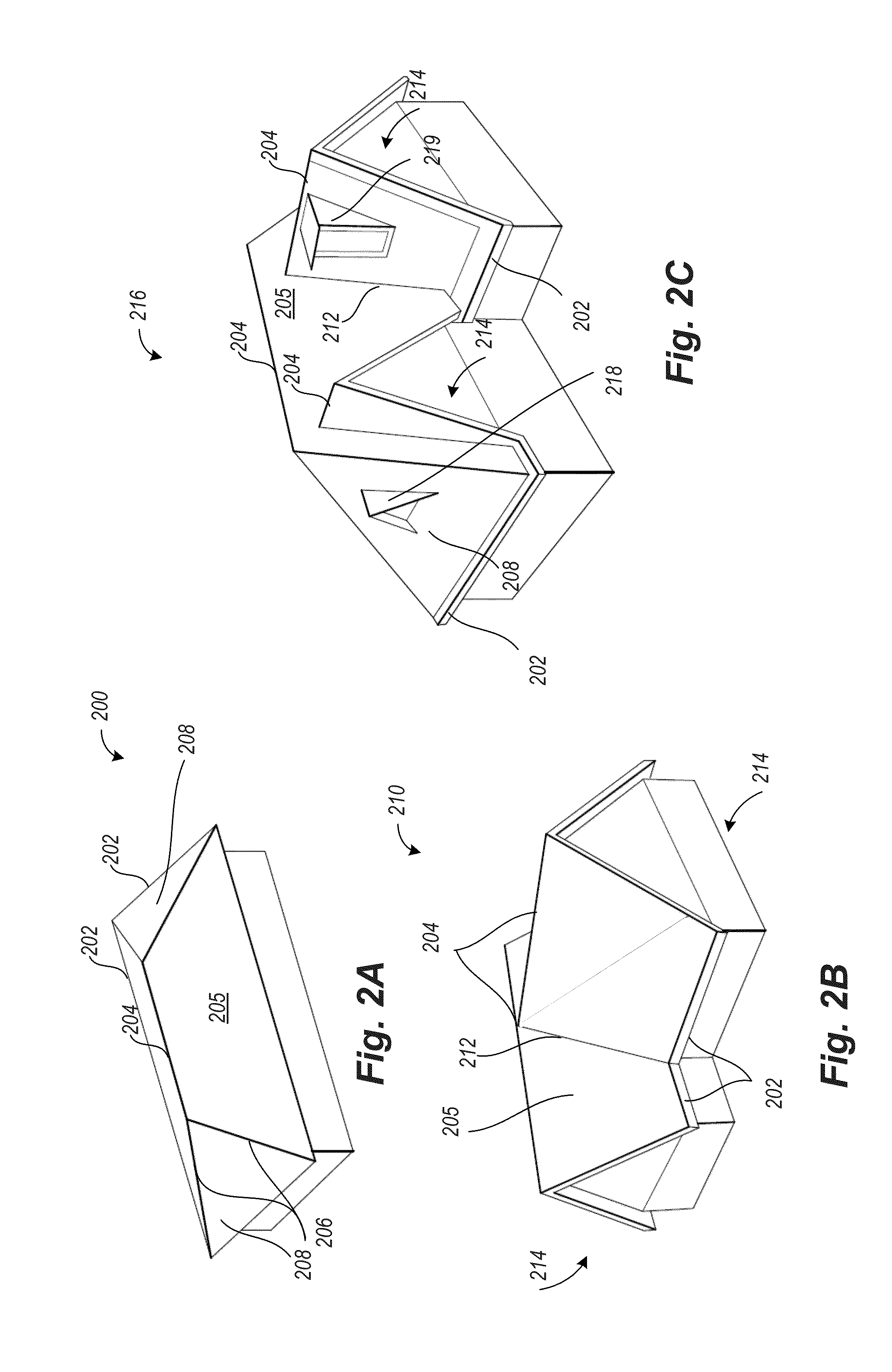
Building materials estimation
ActiveUS20140278697A1Improve accuracyAccurately calculate material costImage analysisCommerceImaging processingEngineering
Using remote image acquisition, image processing, and computational systems and methods, it has become possible to obtain actual building dimensions that can be used to generate construction estimates for repairing or maintaining buildings. For example, actual roof dimensions can be used to provide a computer-based estimate of materials and / or materials overage needed. Instead of simply applying a generic overage percentage based on roof shape, a computer-based approach can take into account cut lines as a percentage of total roof area. The resulting computer-generated estimate is shown to be more accurate, less expensive, and faster than using a human on-site estimator.
Owner:PICTOMETRY INTERNATIONAL CORPORATION
Method and system for processing transactions
A system and method are provided for processing transactions between at least one buying company and at least one selling company using a central datastore accessible to users from the buying company and selling company. Purchase order and invoice data are obtained and compared to identify a matched record having purchase order data and corresponding invoice data. A collaborative data set in the central datastore is created, based in part on the matched record and storing in the datastore detailed settlement data regarding settlement of the matched record of purchase order data and corresponding invoice data. A complete settlement transaction history is stored by providing for storage of additional settlement data in the central datastore, wherein credit memos, debit memos regarding the invoice, the purchase order of the matched record, and / or other documents related to the transaction are stored as part of the collaborative data set.
Owner:ORACLE INT CORP
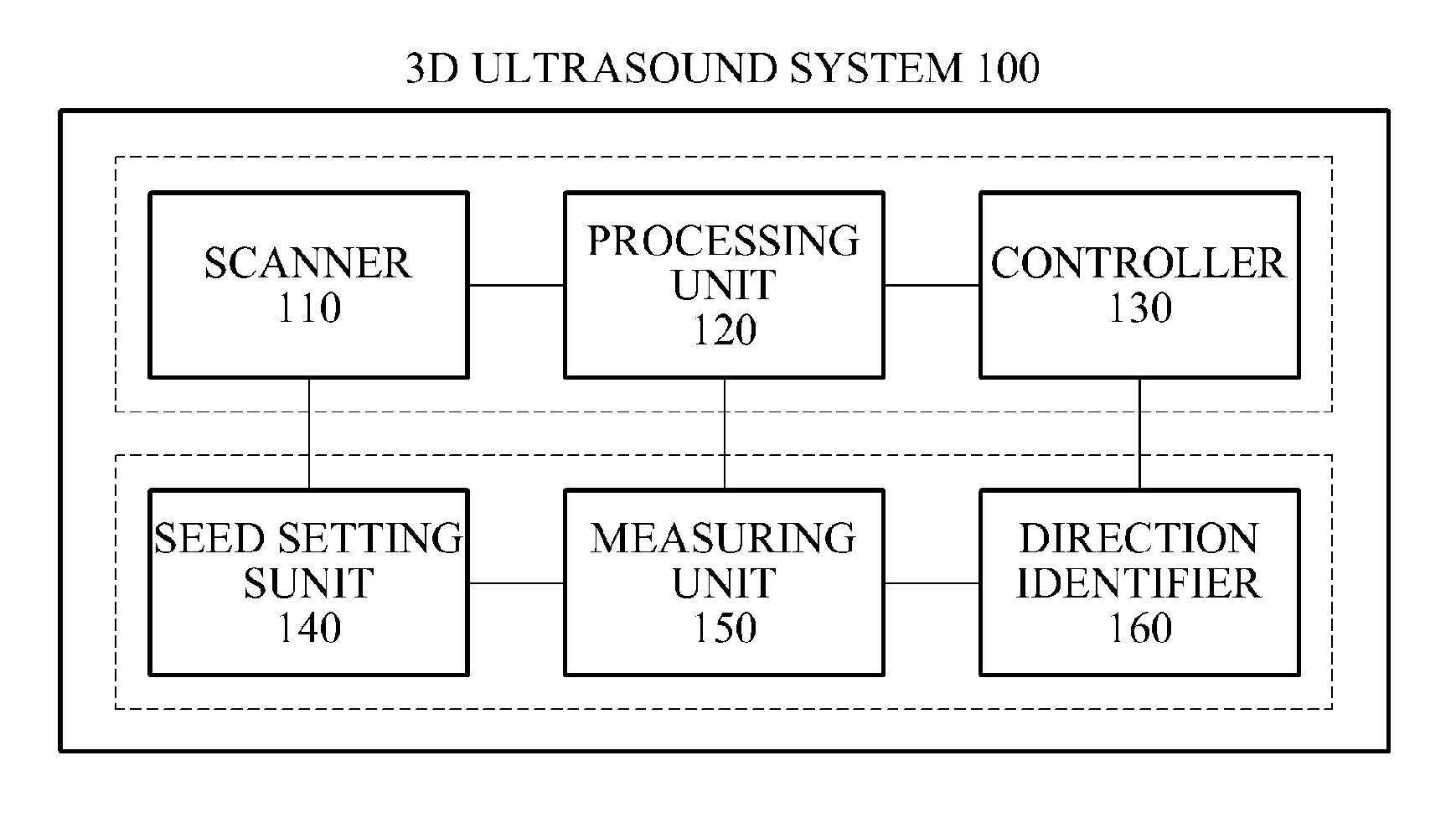
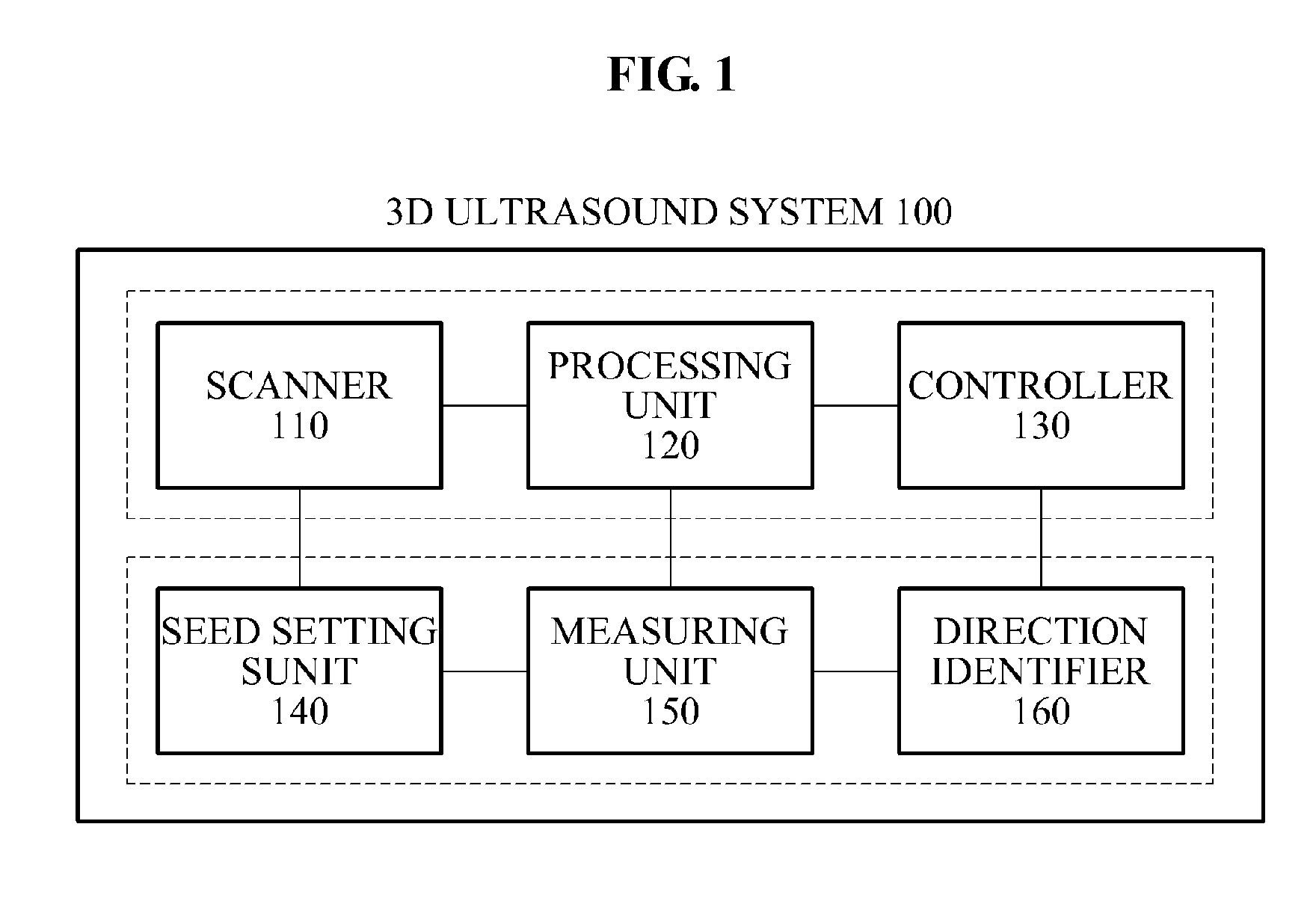
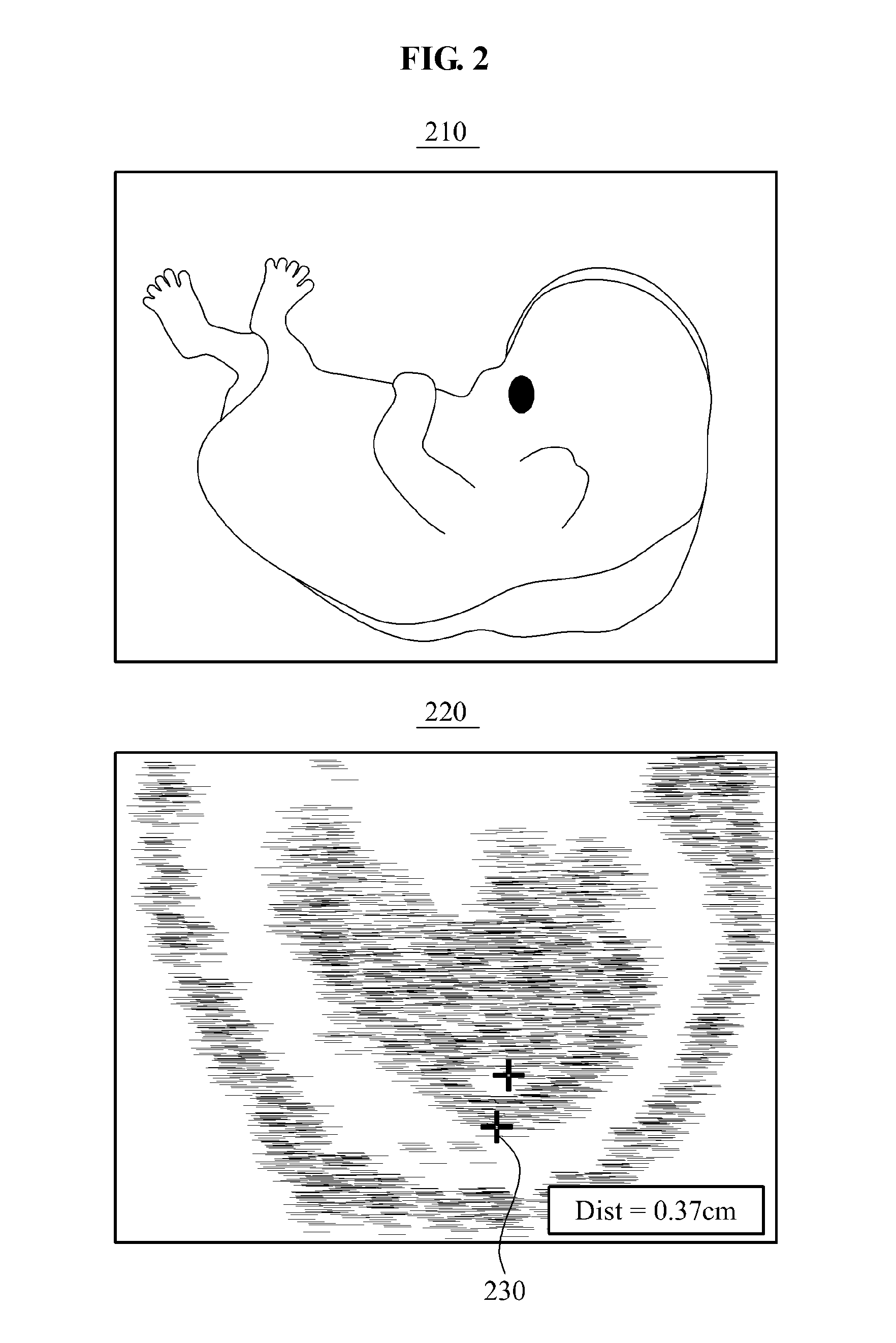
Three-dimensional (3D) ultrasound system for scanning object inside human body and method for operating 3D ultrasound system
ActiveUS20110224546A1View accuratelyAccurate diagnosisImage enhancementImage analysisSonificationImaging data
Provided is a three-dimensional (3D) ultrasound system and a 3D ultrasound system operating method that may obtain 3D ultrasound data with respect to an object inside a human body to determine an accurate sagittal view. The 3D ultrasound system may include a scanner to generate ultrasound data including image data generated by scanning an object inside a human body, a processing unit to detect a center point of the object from the generated ultrasound data, and to generate, on the ultrasound data, a virtual plane on which the detected center point is placed, and a controller to rotate the ultrasound data based on the image data included in the virtual plane and to determine a sagittal view with respect to the object.
Owner:SAMSUNG MEDISON
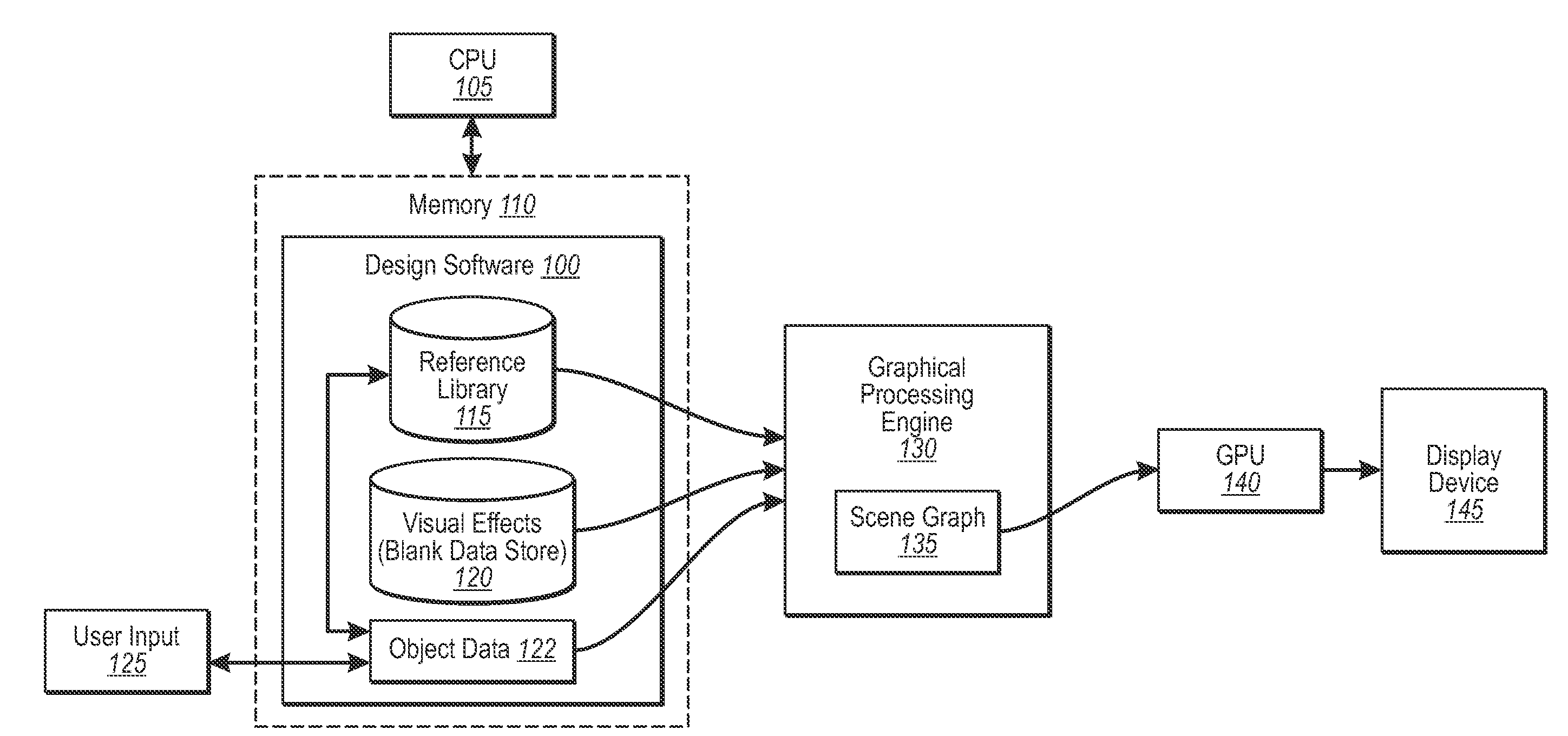
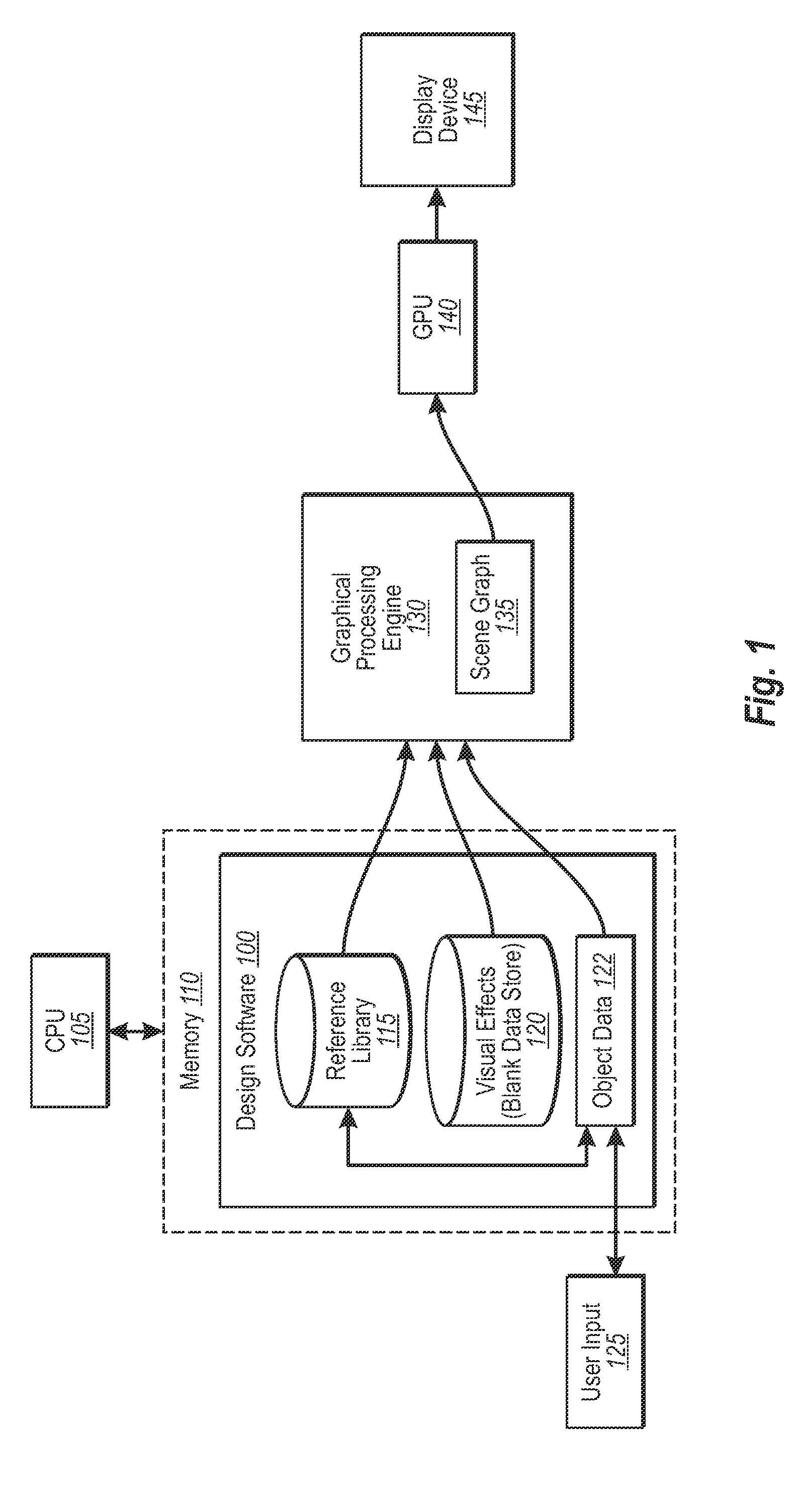
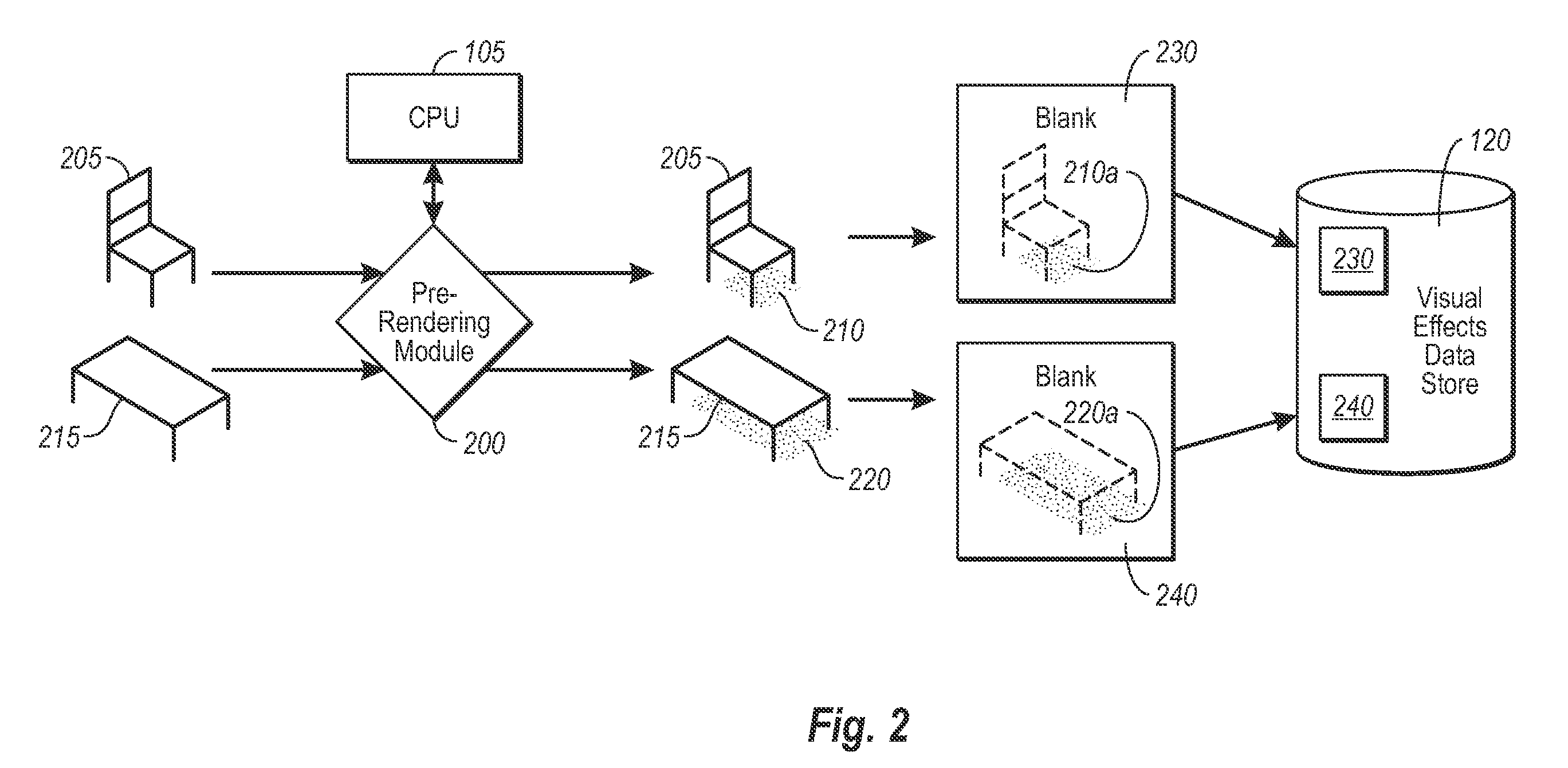
Design software incorporating efficient 3-D rendering
ActiveUS7249005B2Efficient and accurateAccurate visual effect dataCathode-ray tube indicatorsEducational modelsComputer graphics (images)Display device
Design software in accordance with an implementation of the present invention is configured to provide believable three-dimensional representations of user selections in real-time. Design elements that would otherwise be difficult to efficiently render three-dimensionally in real-time are prerendered for realistic visual effects, such as realistic shading, which correspond to various positions of the elements in a design space. Blanks of the visual effects for each position are then stored in a data store for visual effects. At run time, data associated with user design choices, as well as the blanks for any corresponding design elements are fed in one implementation to peripheral processing hardware, such as a GPU, which sends the processed data to a display device. The user is therefore able to view complex visual data of certain design choices efficiently with added realism.
Owner:ARMSTRONG WORLD INDUSTRIES +1
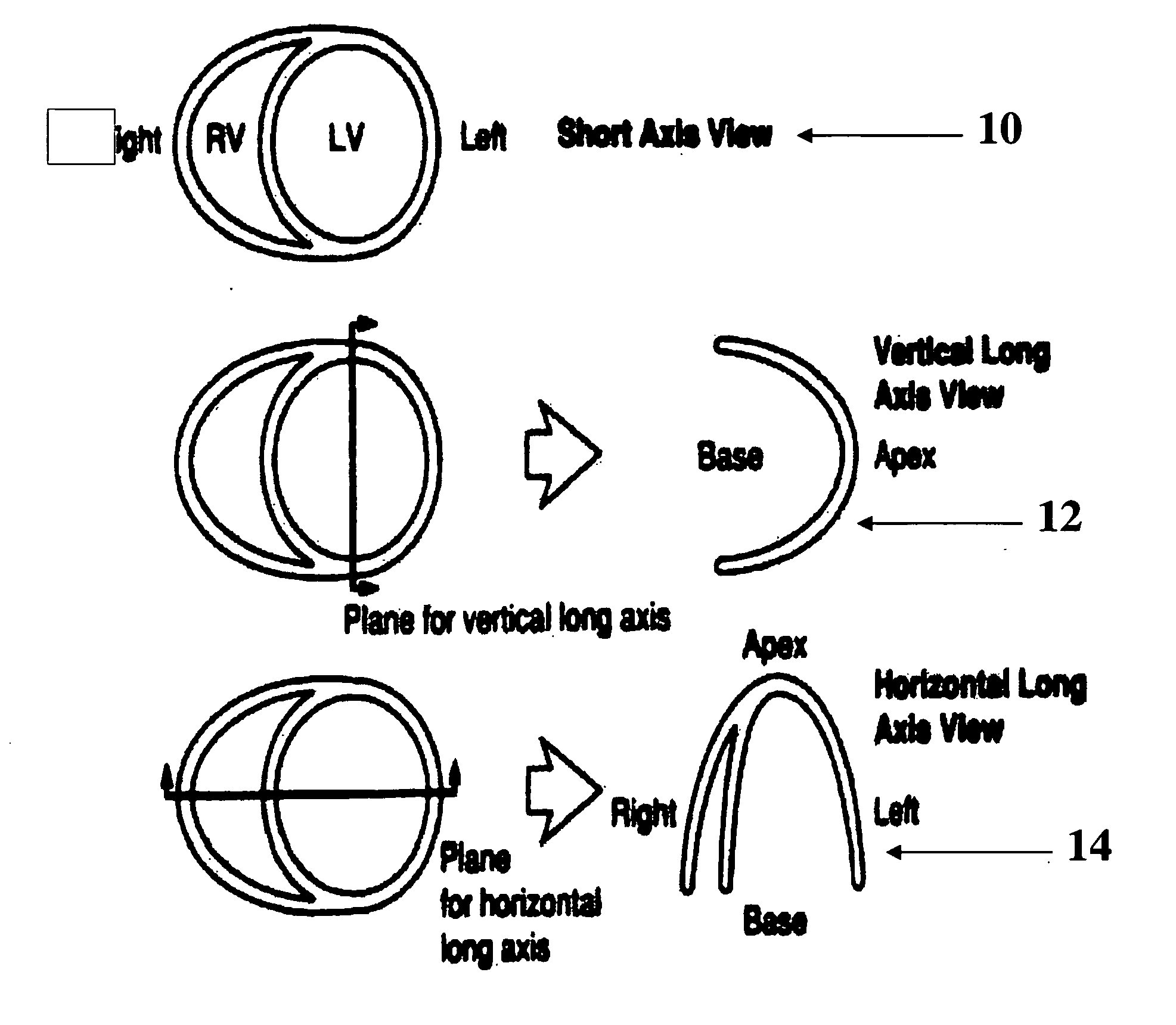
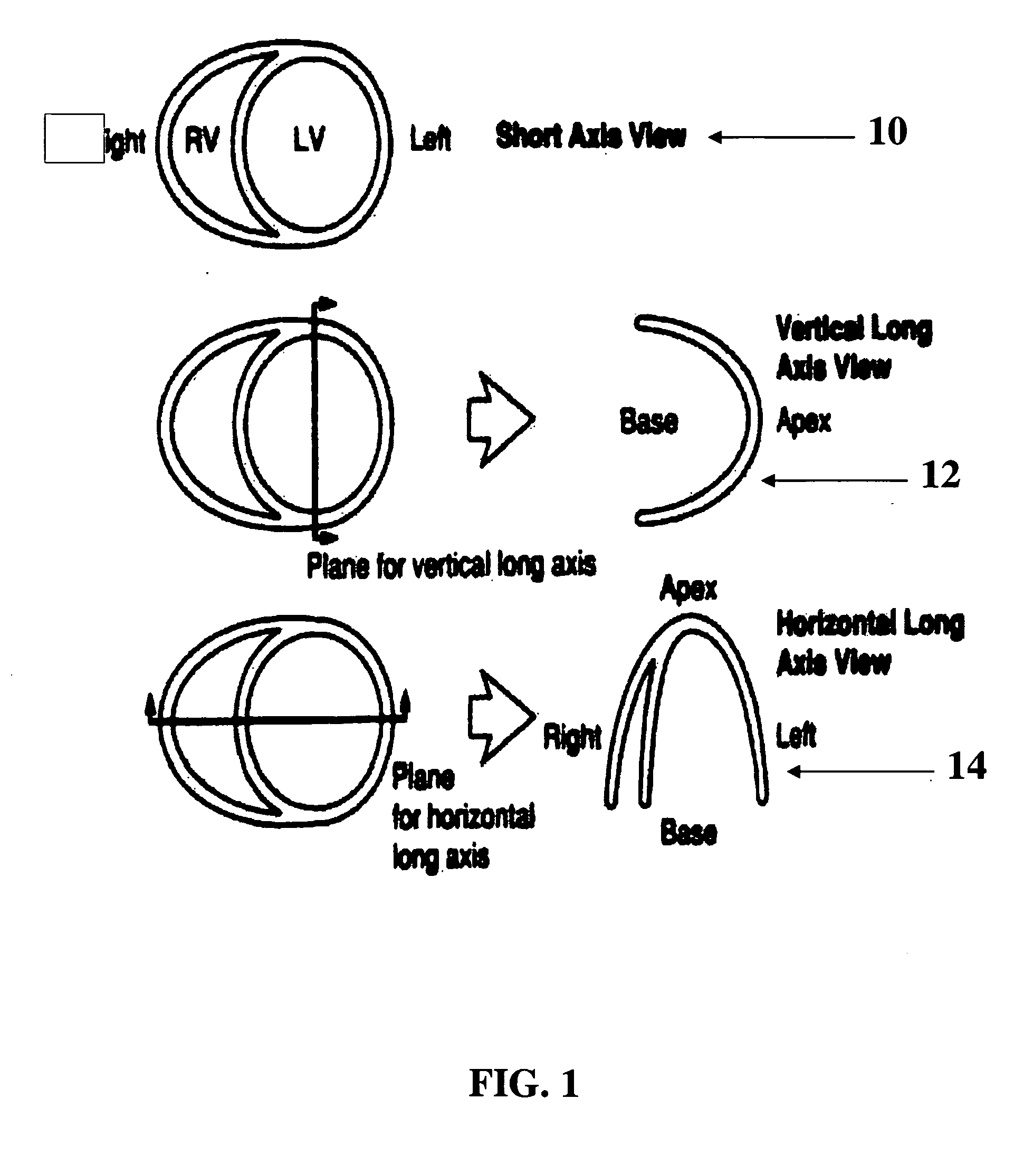
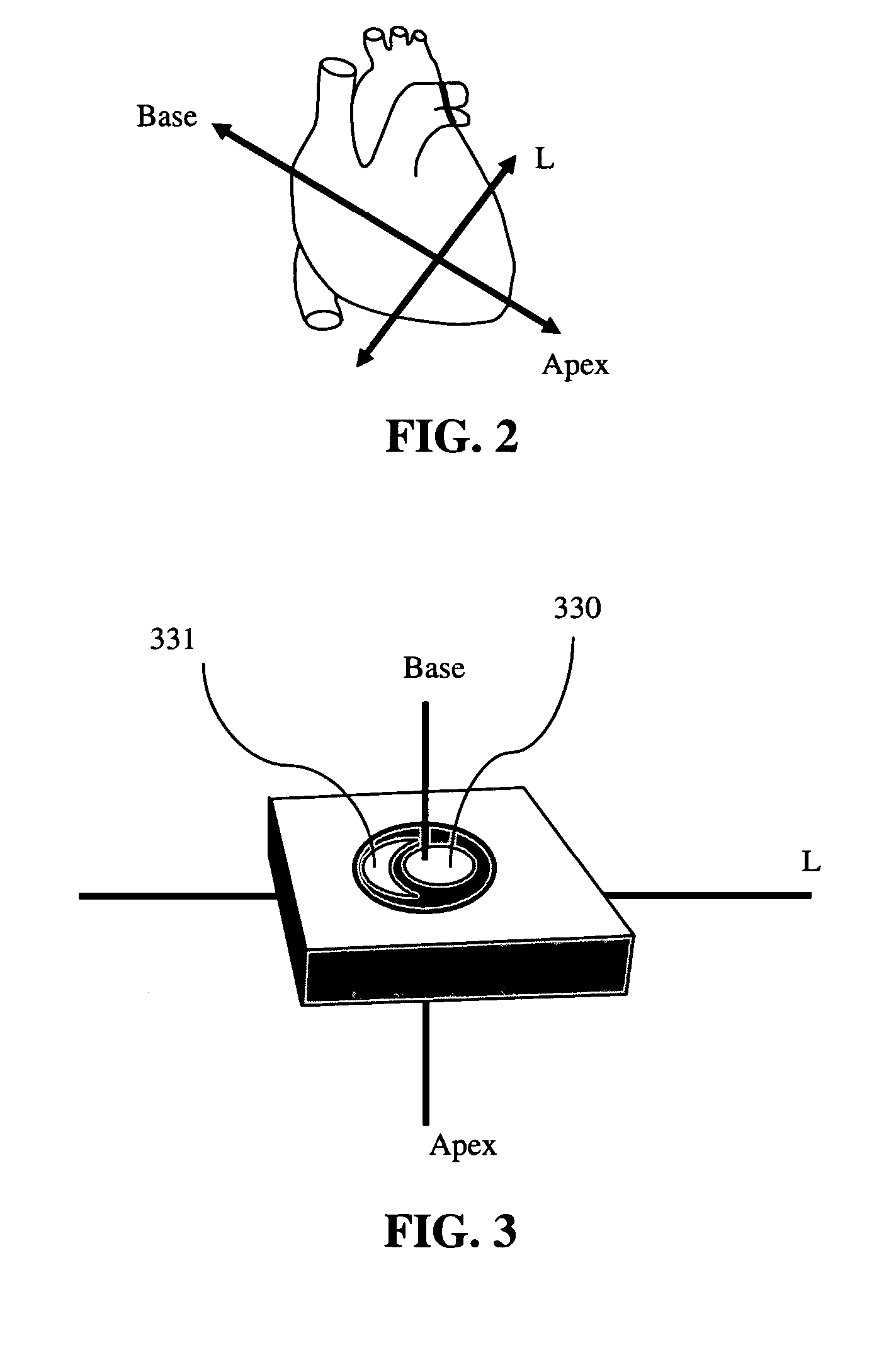
Automatic determination of the standard cardiac views from volumetric data acquisitions
InactiveUS20060239554A1Accurately estimate standard cardiac image viewView accuratelyImage enhancementImage analysisVolumetric dataData acquisition
A system and method for automatically determining the standard cardiac image views as defined by the American Heart Association from volumetric data of the chest including the heart. The system and method can be used by a health practitioner to quickly see the two dimensional views from which a diagnosis is generally made. The left ventricle is detected. Then the relative orientation of the right ventricle is determined and the standard cardiac views are determined.
Owner:SIEMENS MEDICAL SOLUTIONS USA INC
Method for the selection of physical objects in a robot system
ActiveUS9050719B2View accuratelyImprove operationProgramme controlProgramme-controlled manipulatorRobotic systemsEngineering
A method in which an apparatus receives first sensor data from first sensors and determines a target position from the data, the target position may be a position in space or an orientation of a gripper in a robot arm First instructions are issued to the robot arm or the gripper in order to move a gripper to the target position. Force feedback sensor data is received from force feedback sensors associated with either the robot arm or the gripper or from the first sensors. A failure in carrying out the first instructions is determined. Second sensor data is received from the at least one first sensor. Successful gripping of an object is determined from the second sensor data.
Owner:MP ZENROBOTICS OY
System and method for using off-screen mask space to provide enhanced viewing
InactiveUS20110227917A1Enhance visual propertyView accuratelyCathode-ray tube indicatorsSteroscopic systemsComputer graphics (images)Display device
Methods and apparatuses for compensating for clipped portions of one or more objects in an image provide a boundary mask portion adjacent to one or more edges of an image display. The boundary mask portion is used to display information which will fill clipped portions of the objects in the image.
Owner:CONVERSION WORKS