Patents
Literature
37results about How to "Less available" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
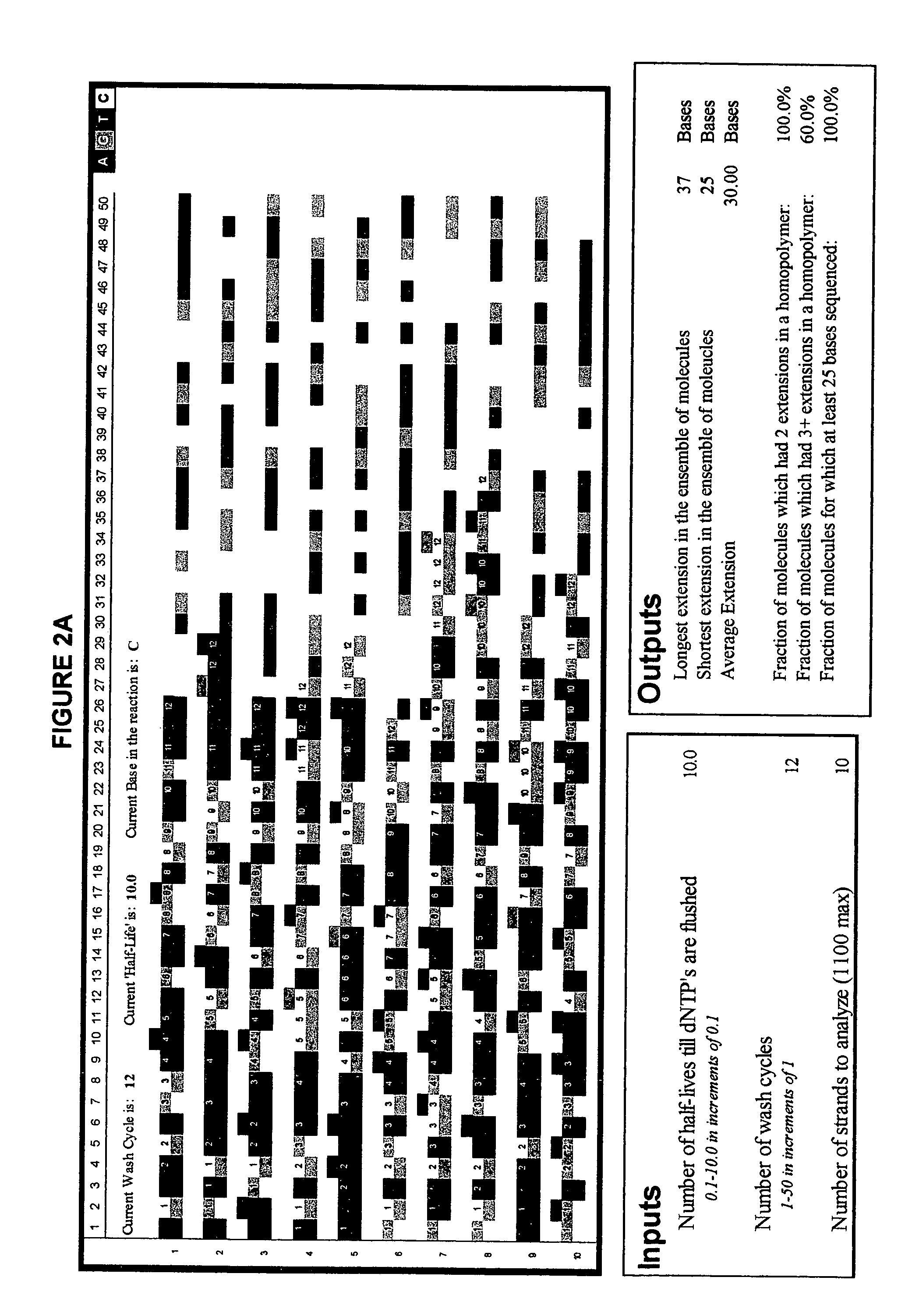
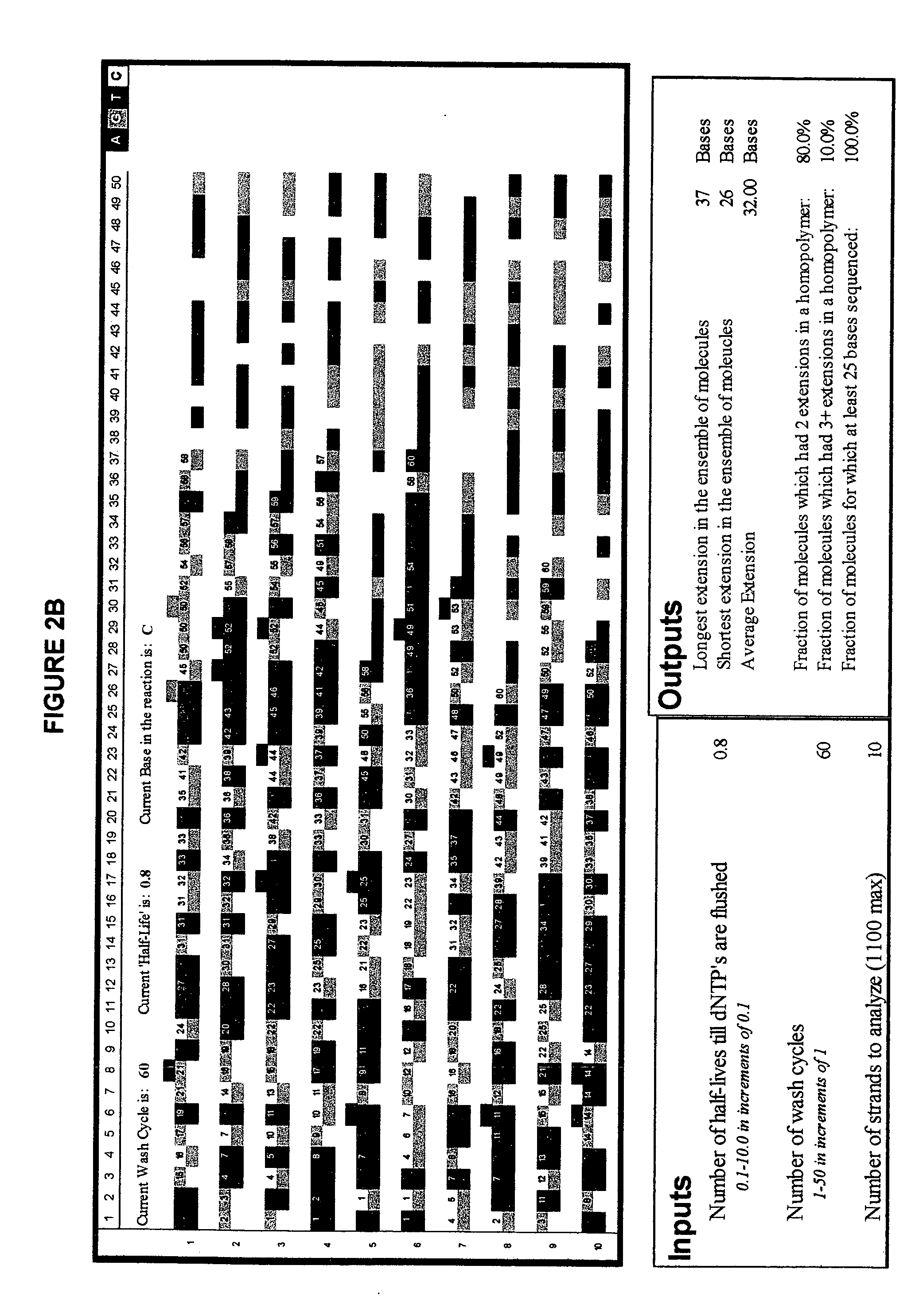
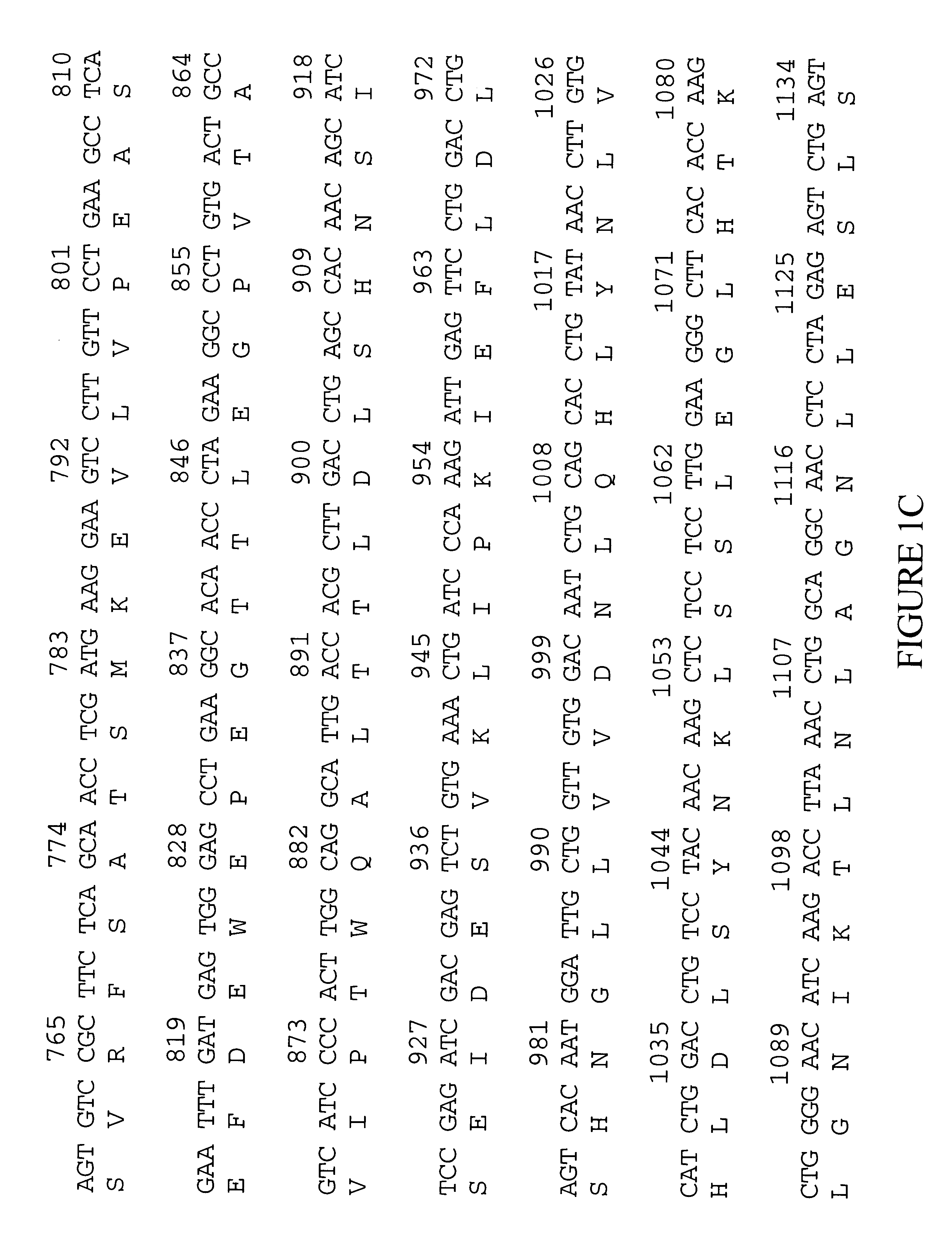
Short cycle methods for sequencing polynucleotides
InactiveUS7169560B2Increase resolution and reliabilityHigh throughput single molecule sequencingSugar derivativesMicrobiological testing/measurementPolynucleotideComputational biology
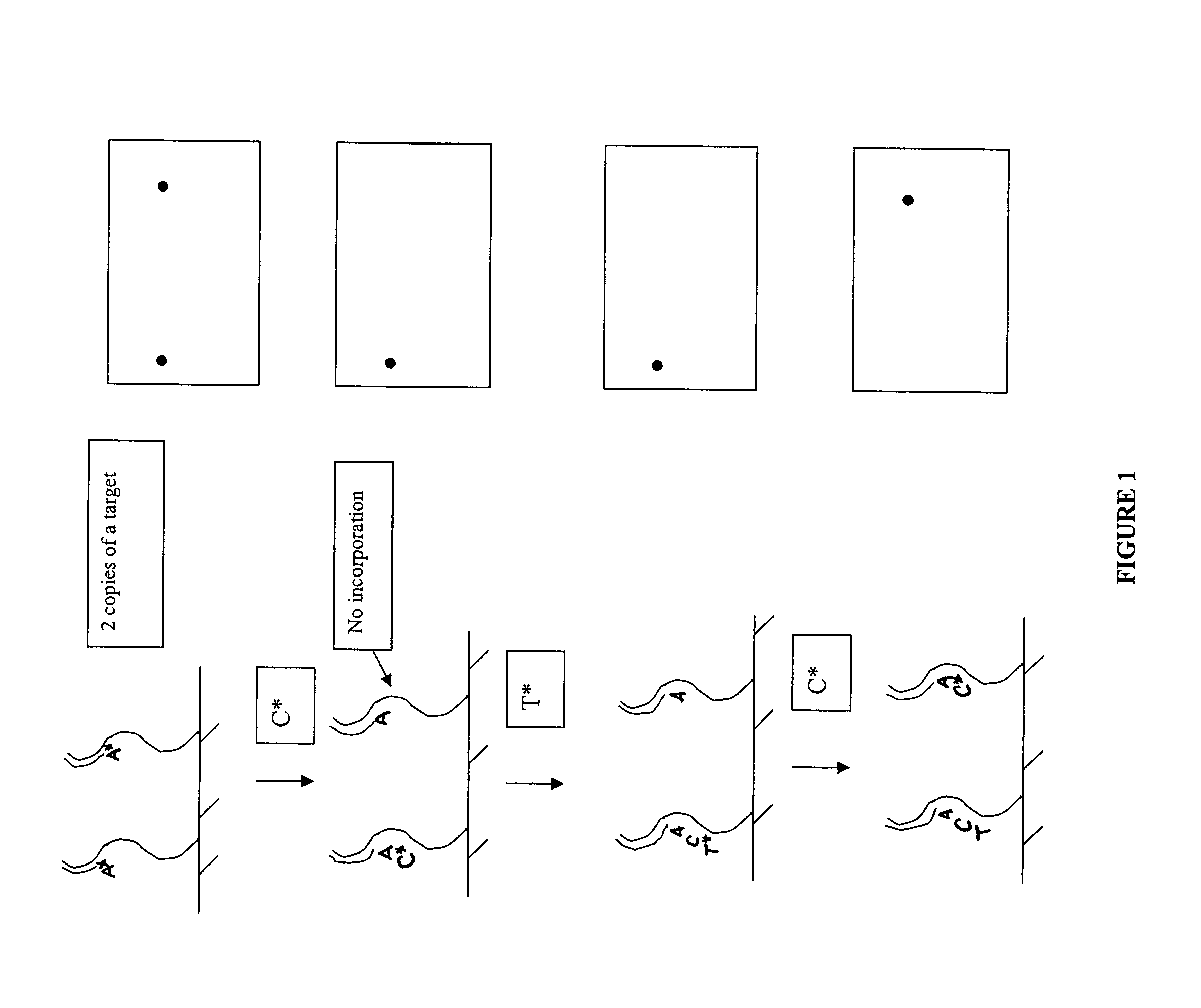
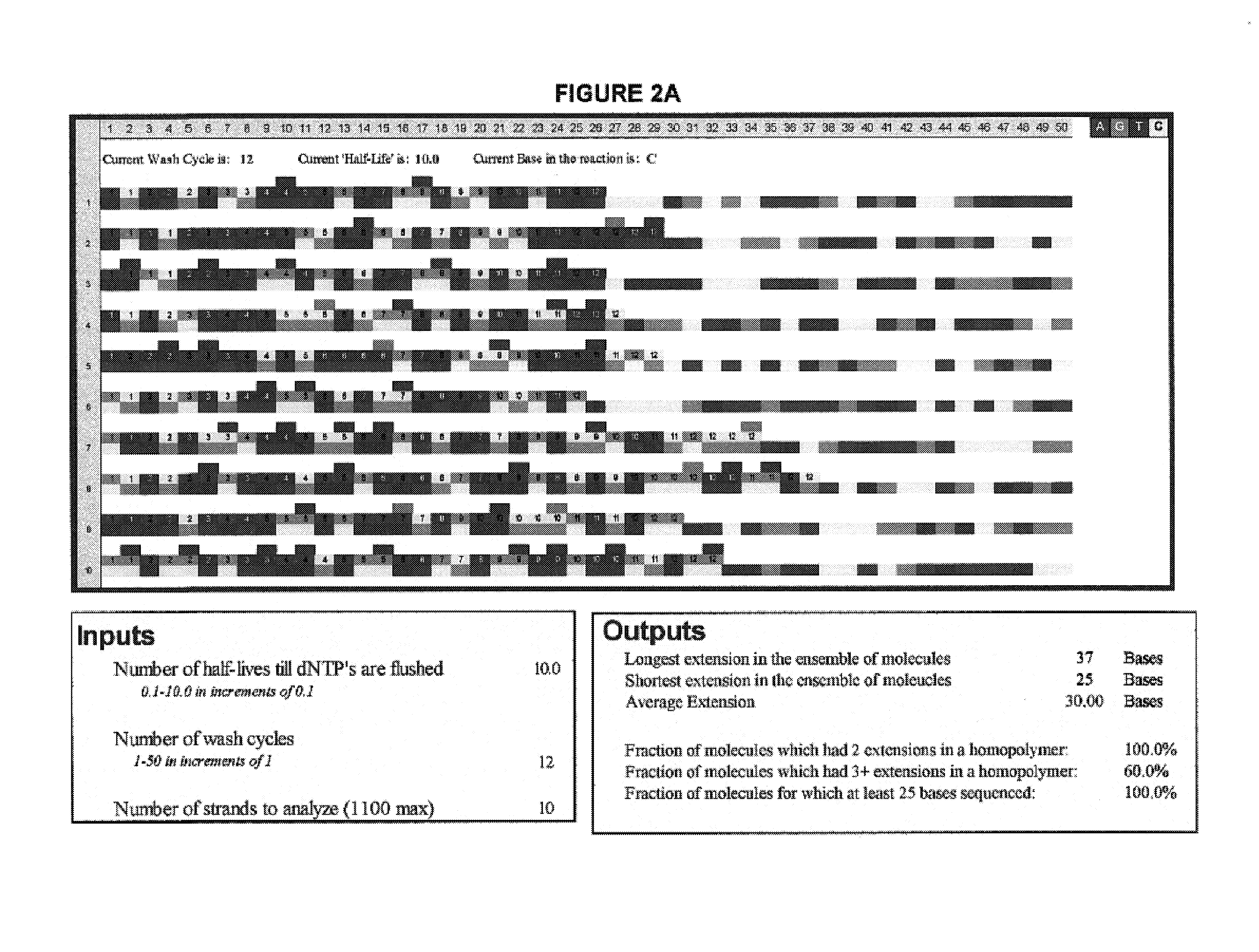
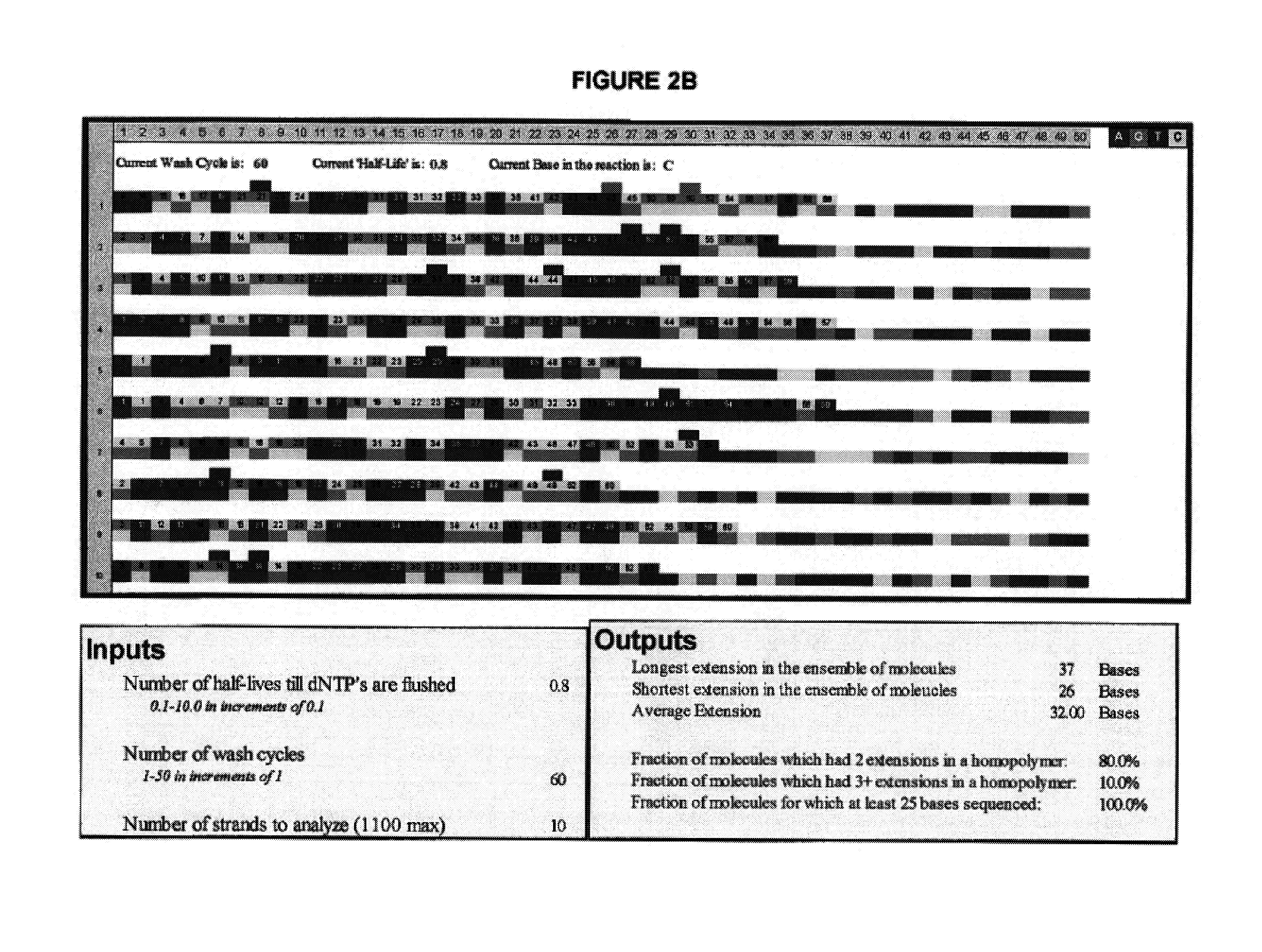
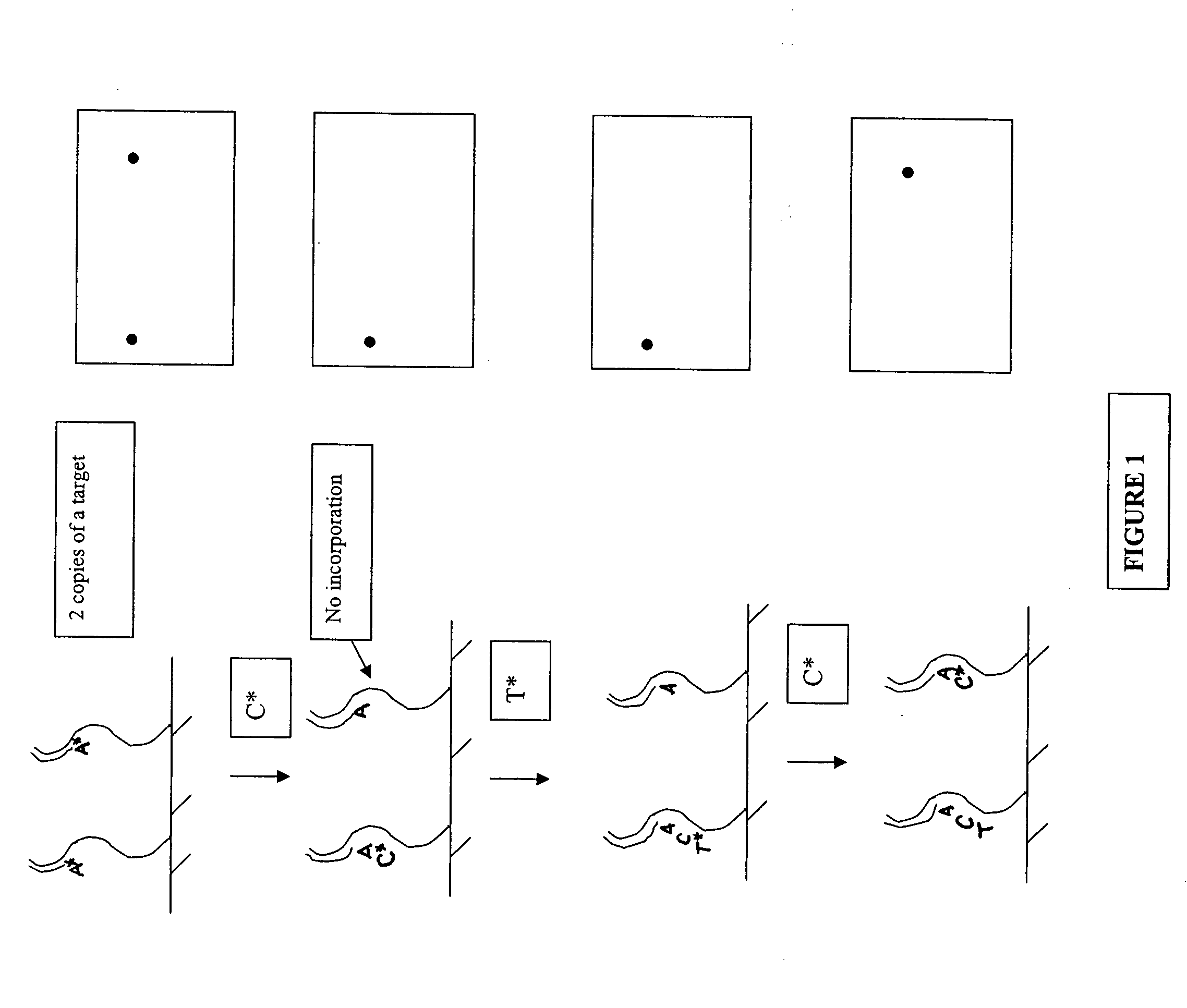
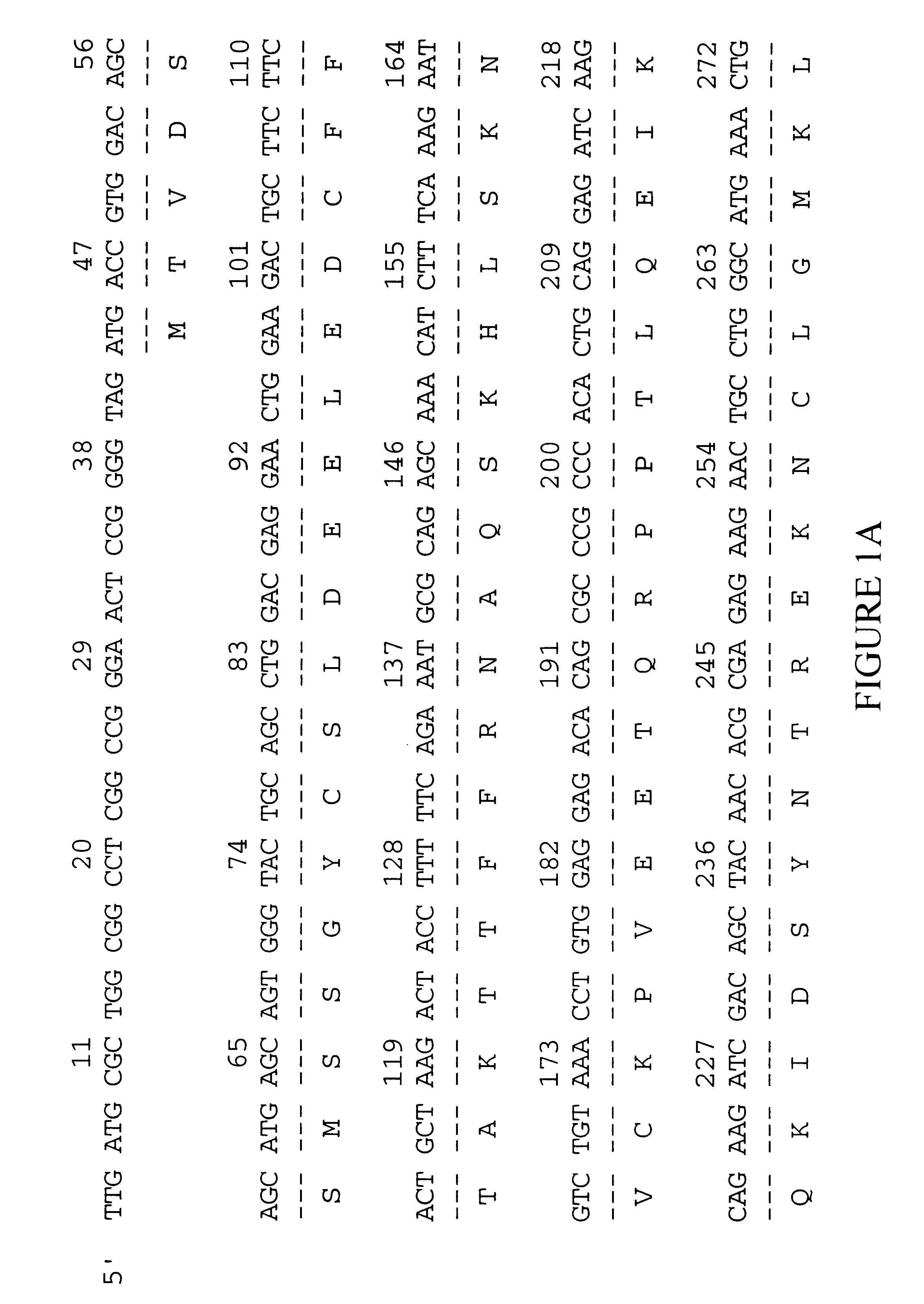
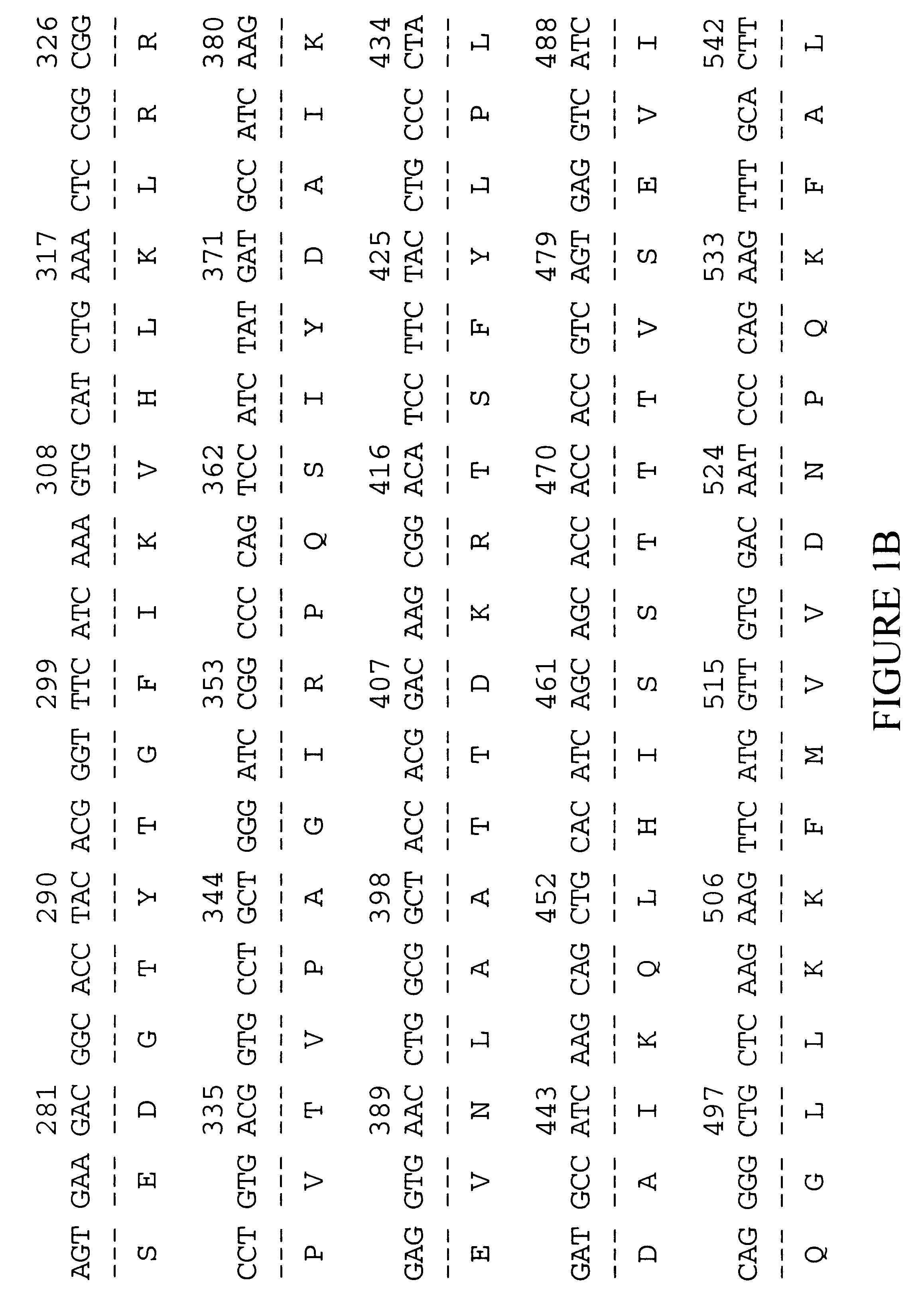
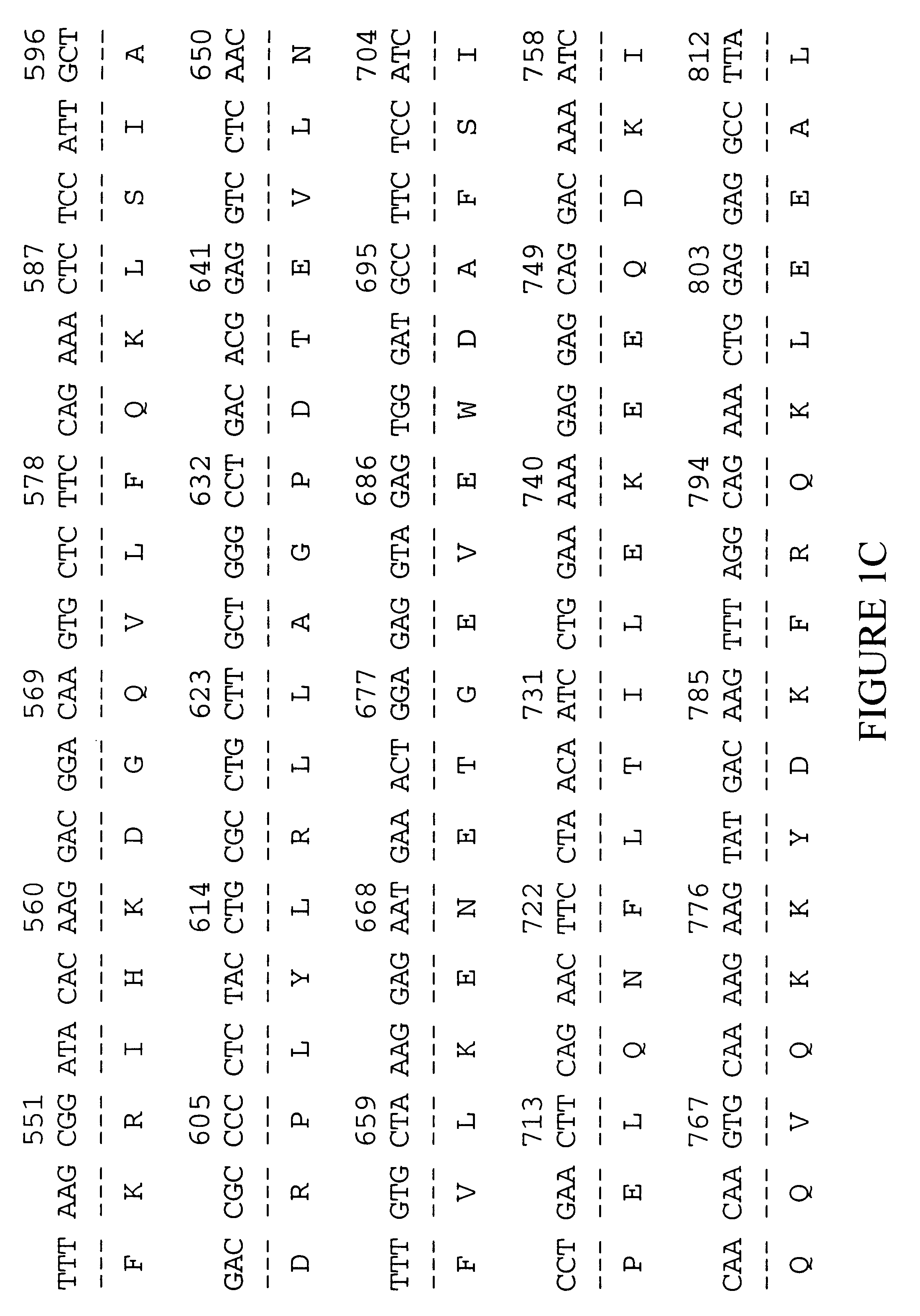
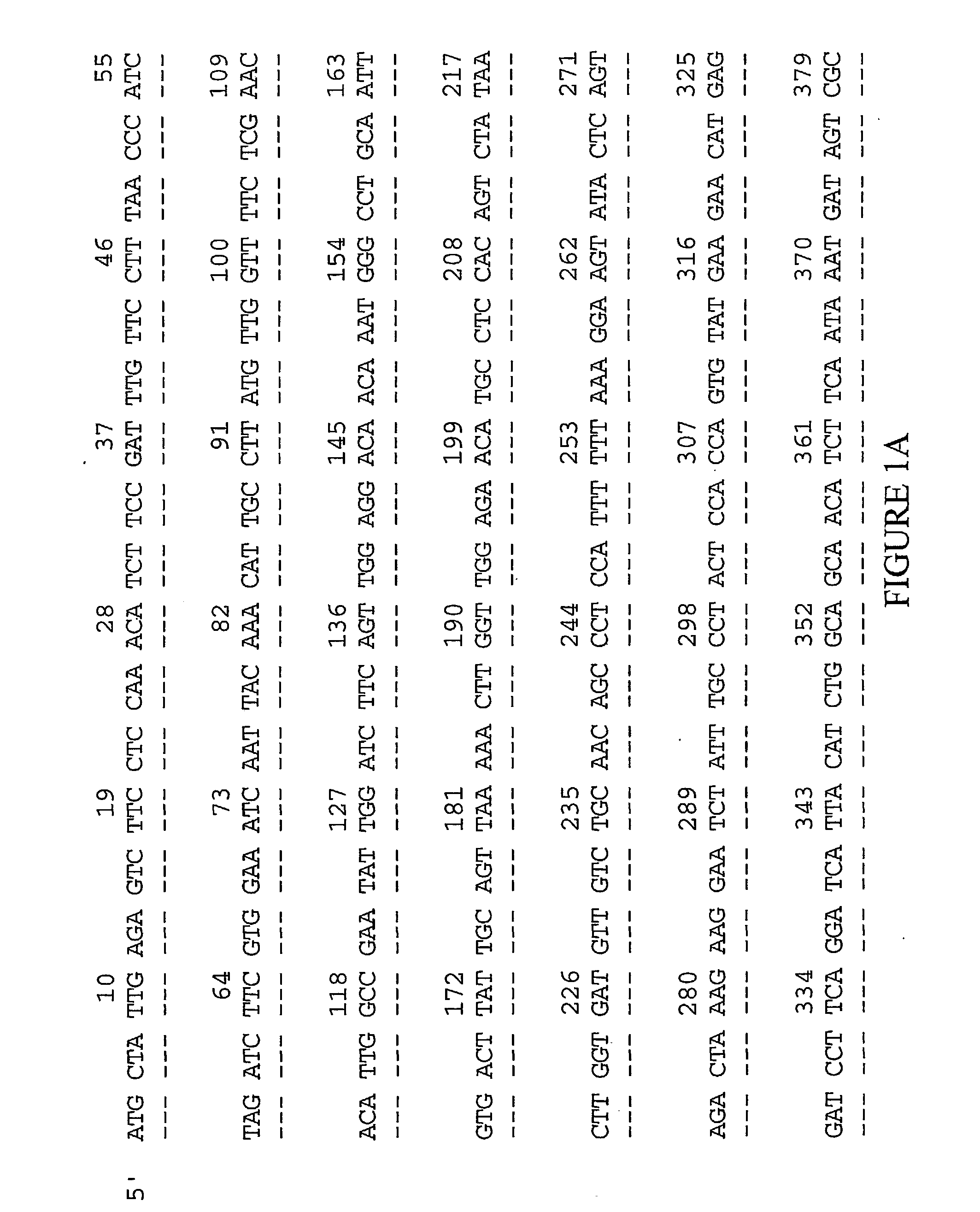
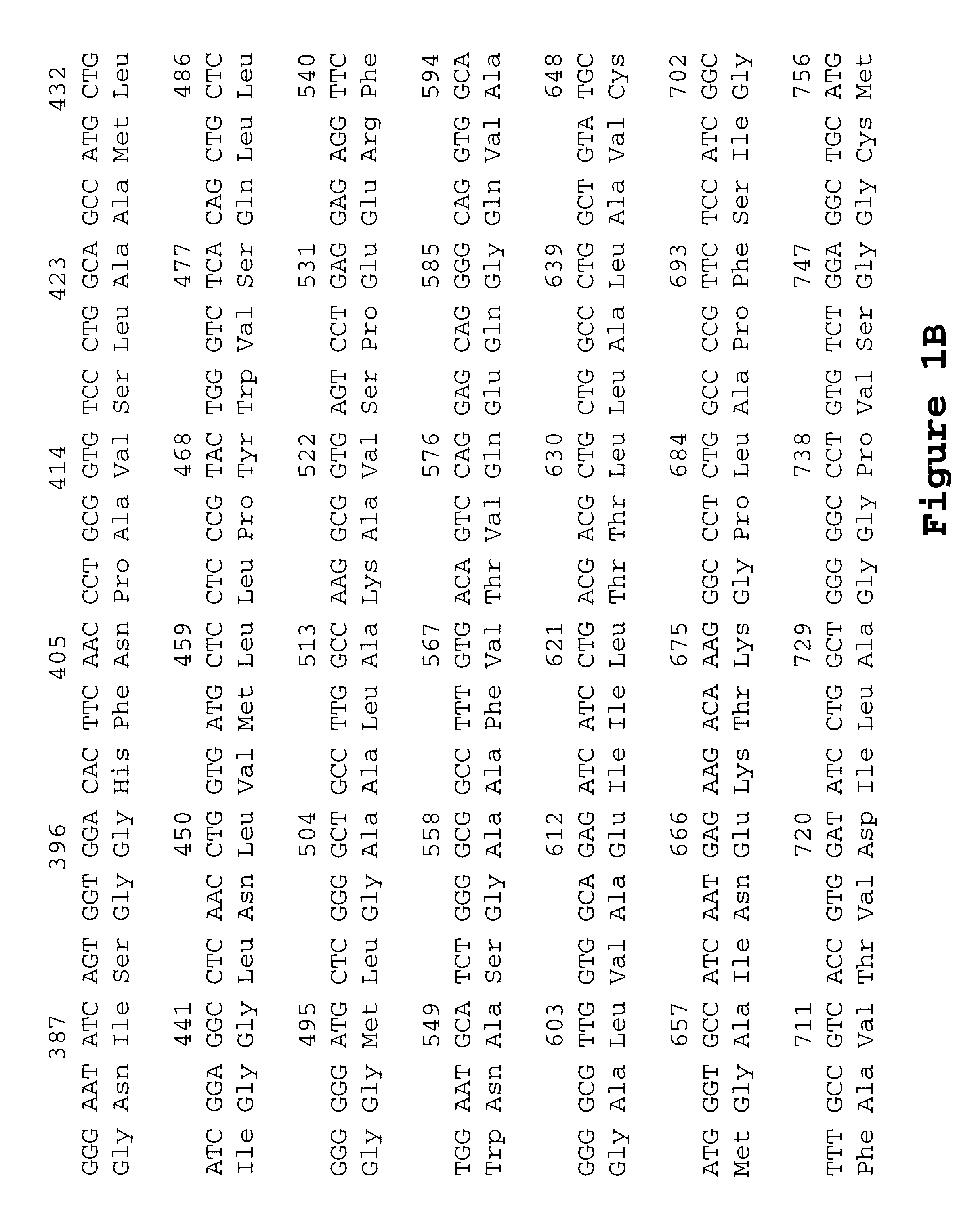
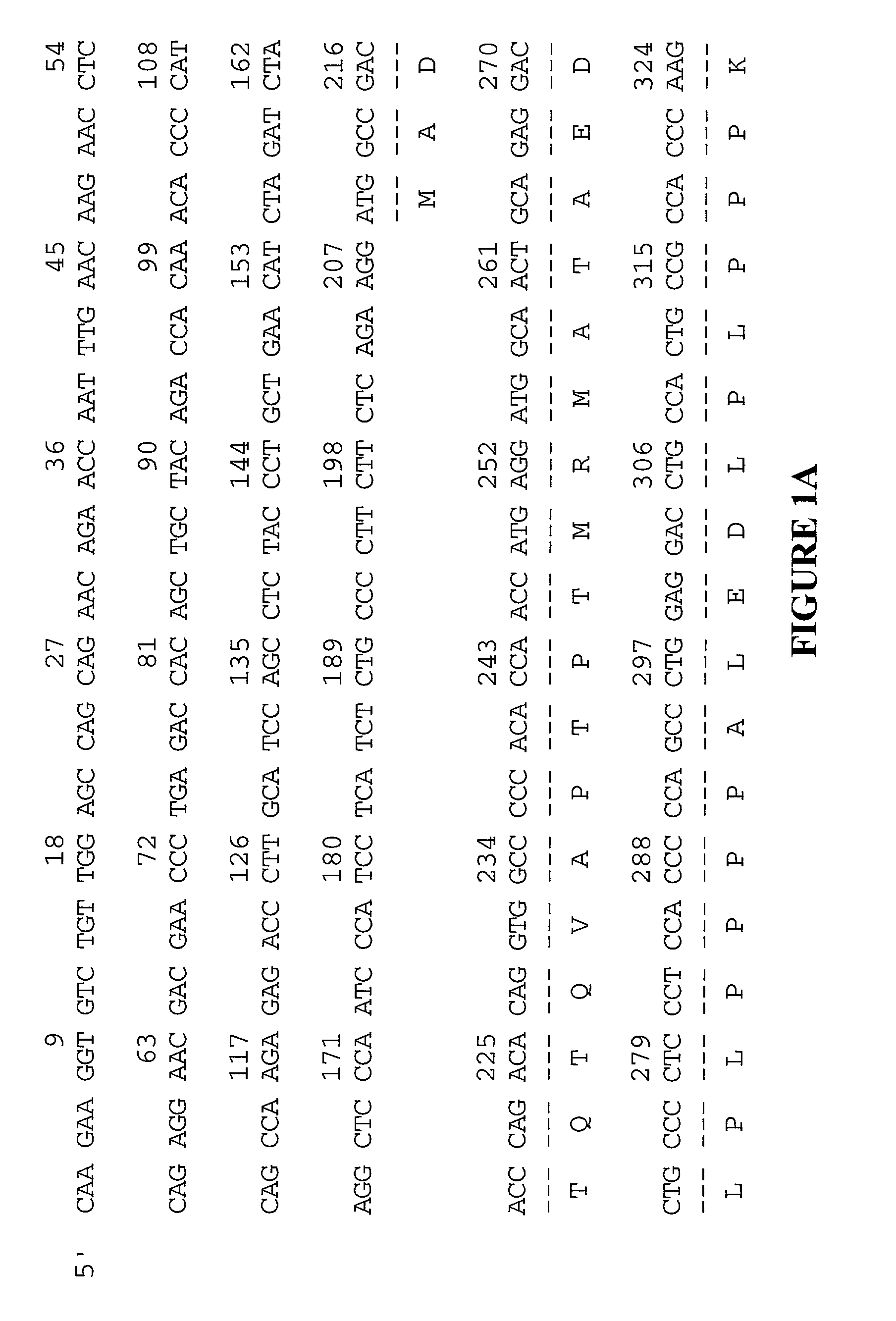
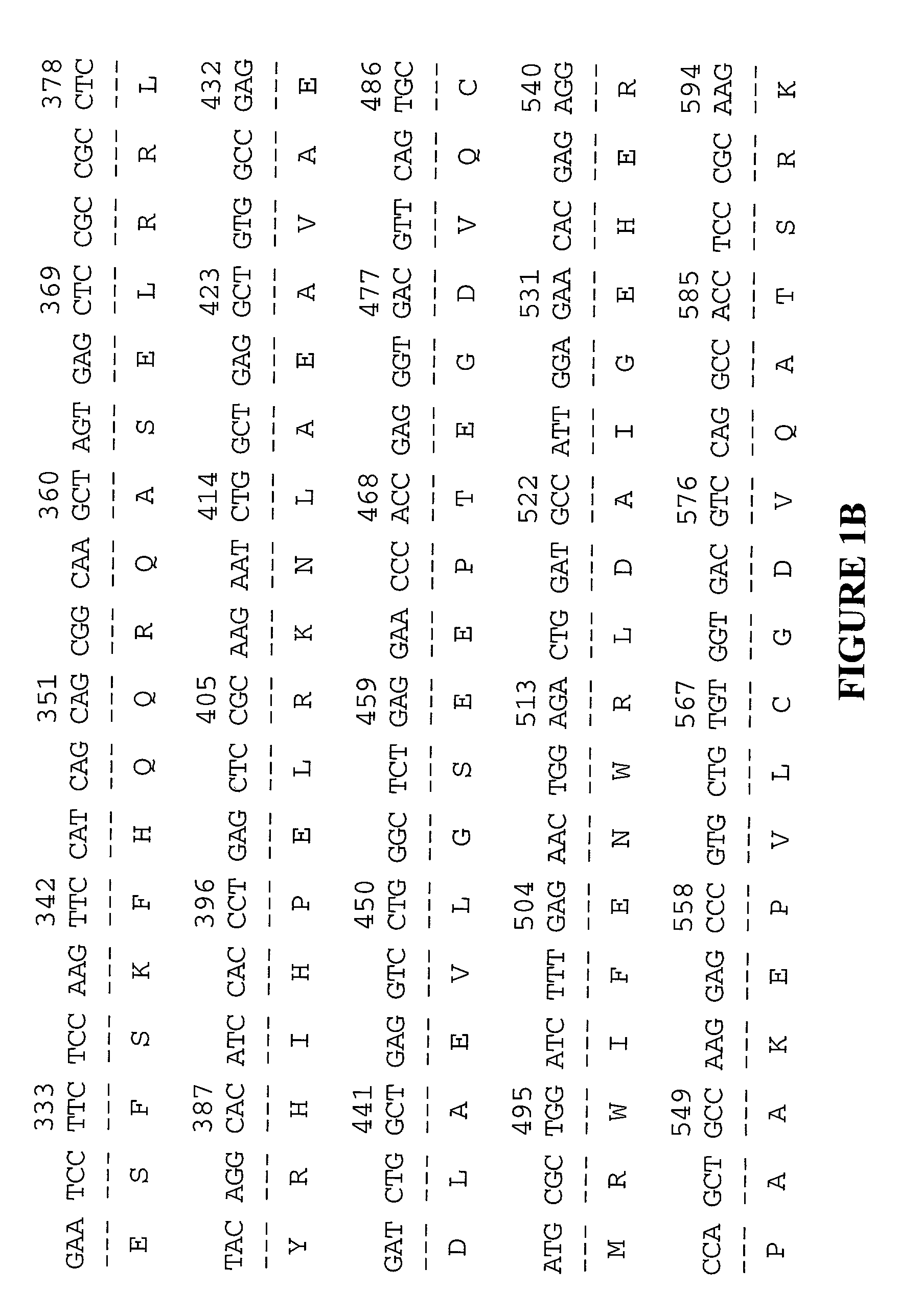
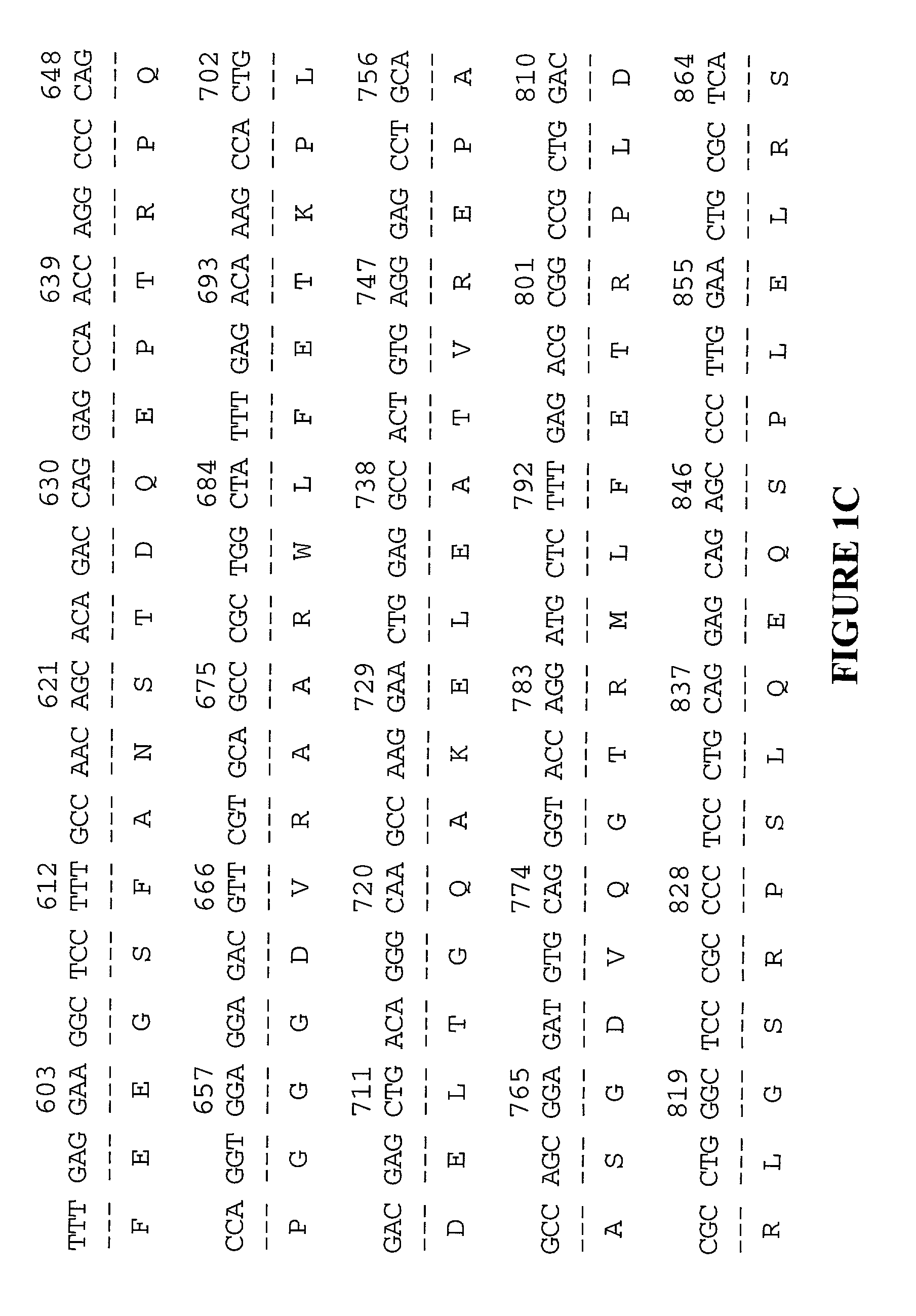
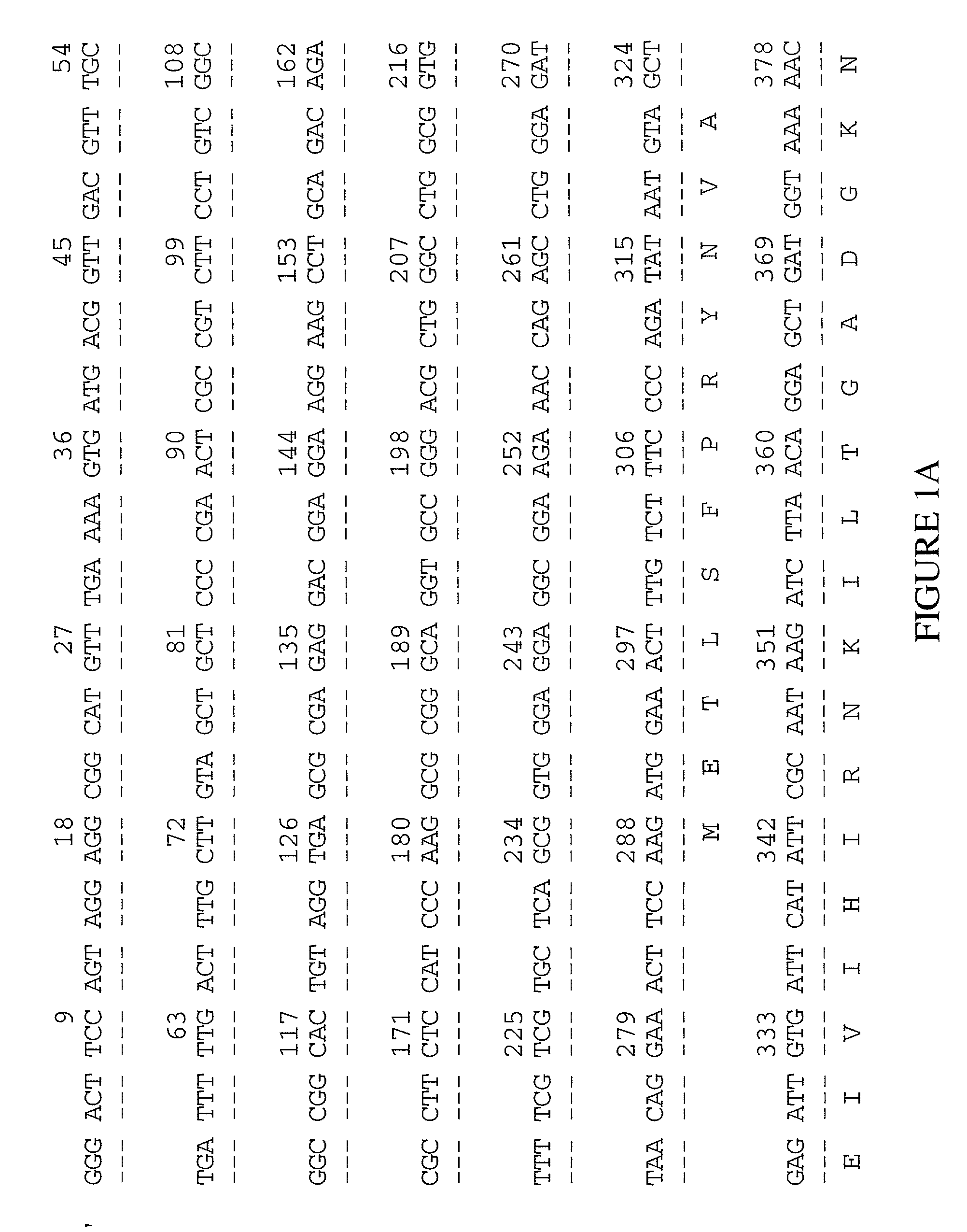
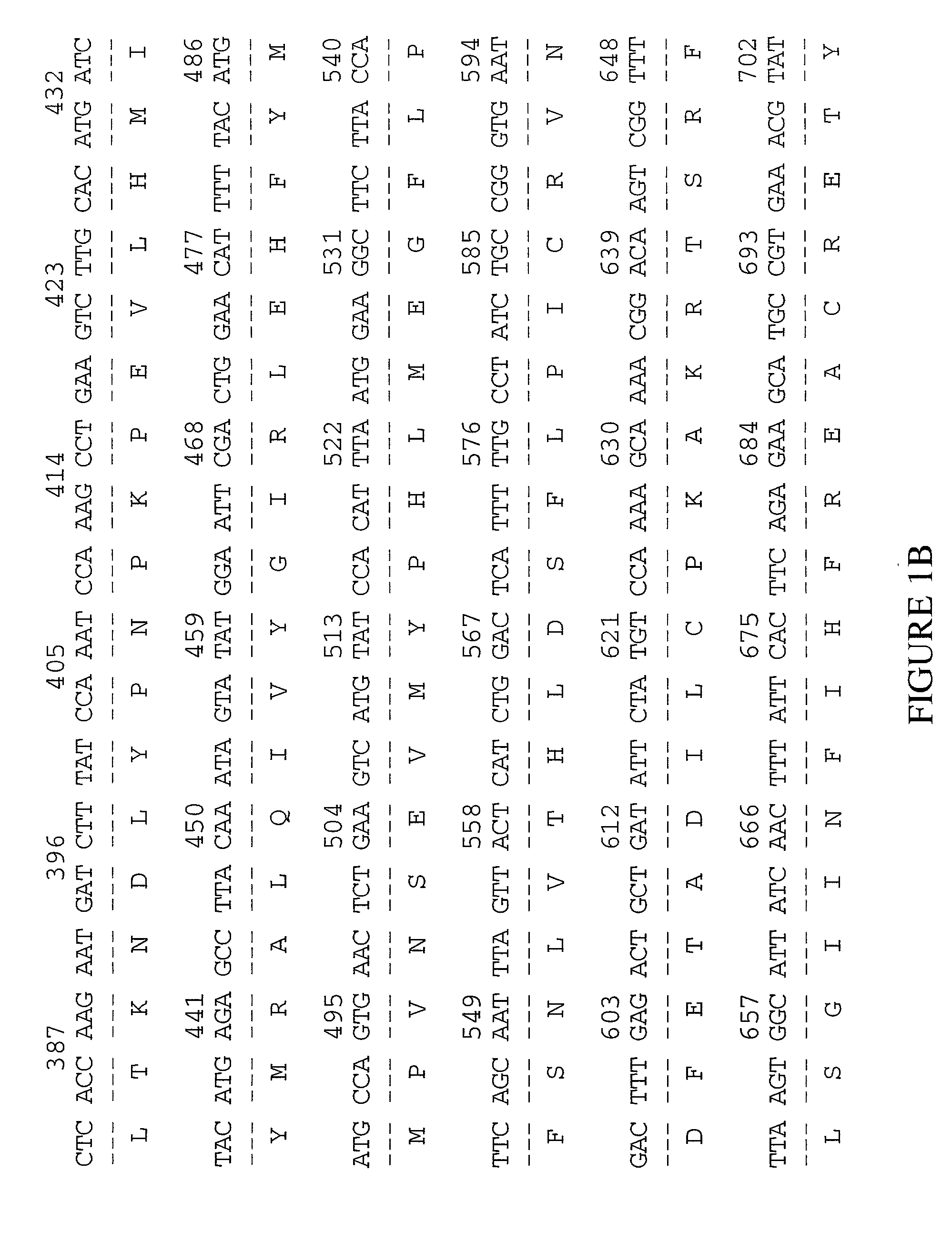
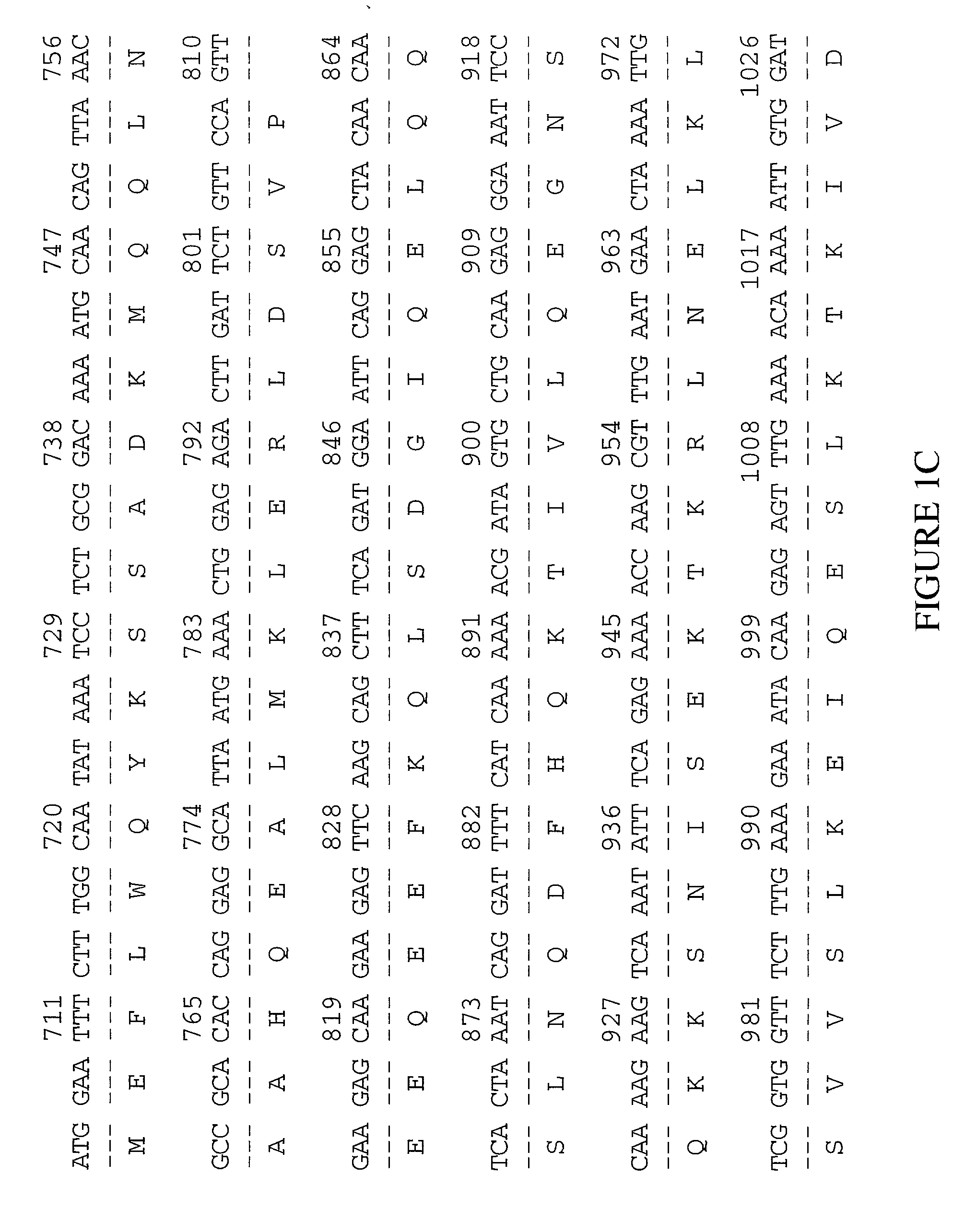
The invention provides methods for sequencing a polynucleotide comprising stopping an extension cycle in a sequence by synthesis reaction before the reaction has run to near or full completion.
Owner:FLUIDIGM CORP
Short cycle methods for sequencing polynucleotides
InactiveUS20050100932A1High throughput single molecule sequencingImprove resolutionSugar derivativesMicrobiological testing/measurementPolynucleotideComputational biology
The invention provides methods for sequencing a polynucleotide comprising stopping an extension cycle in a sequence by synthesis reaction before the reaction has run to near or full completion.
Owner:FLUIDIGM CORP
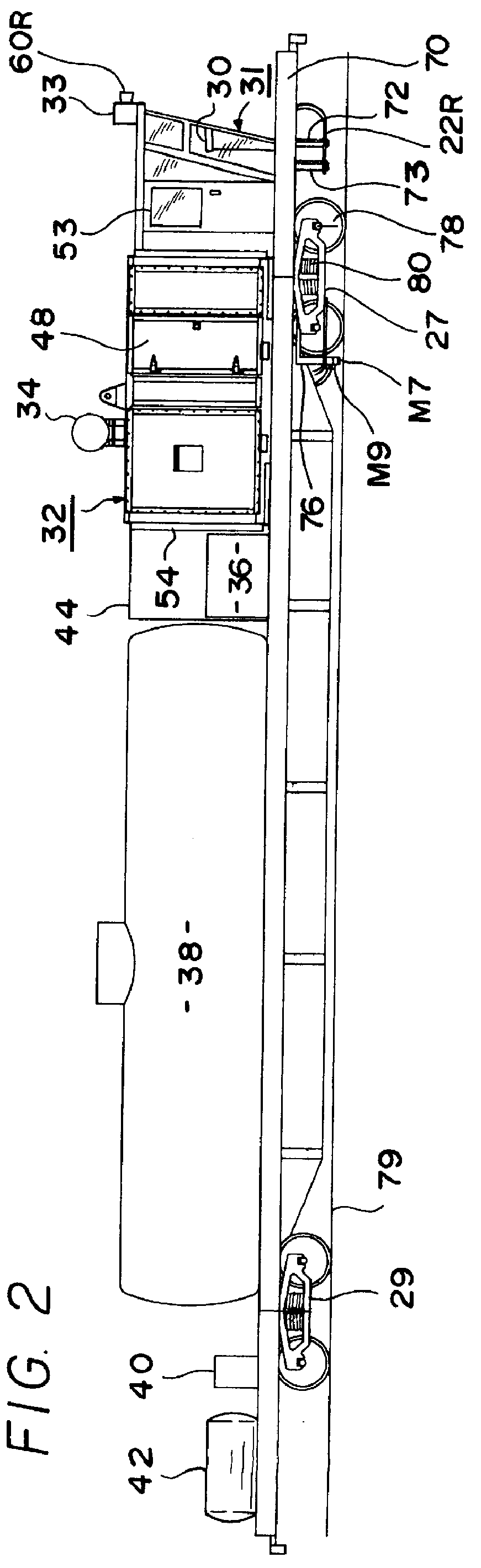
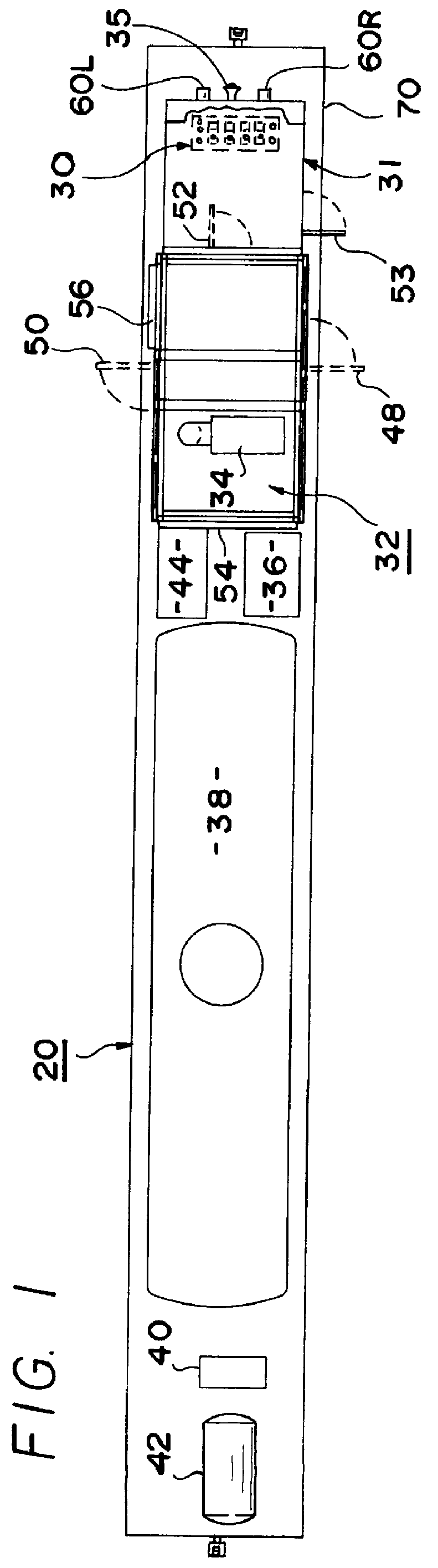
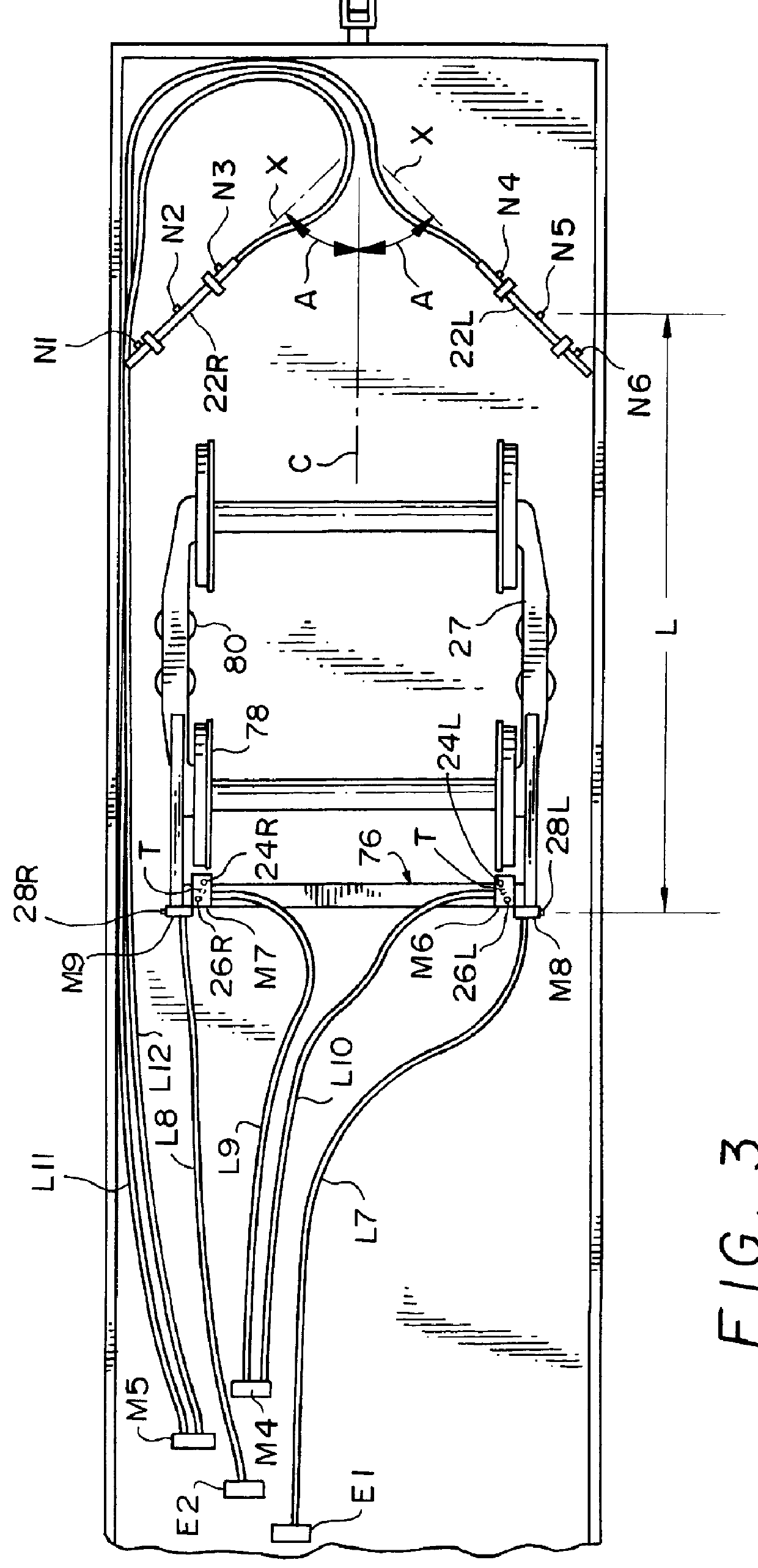
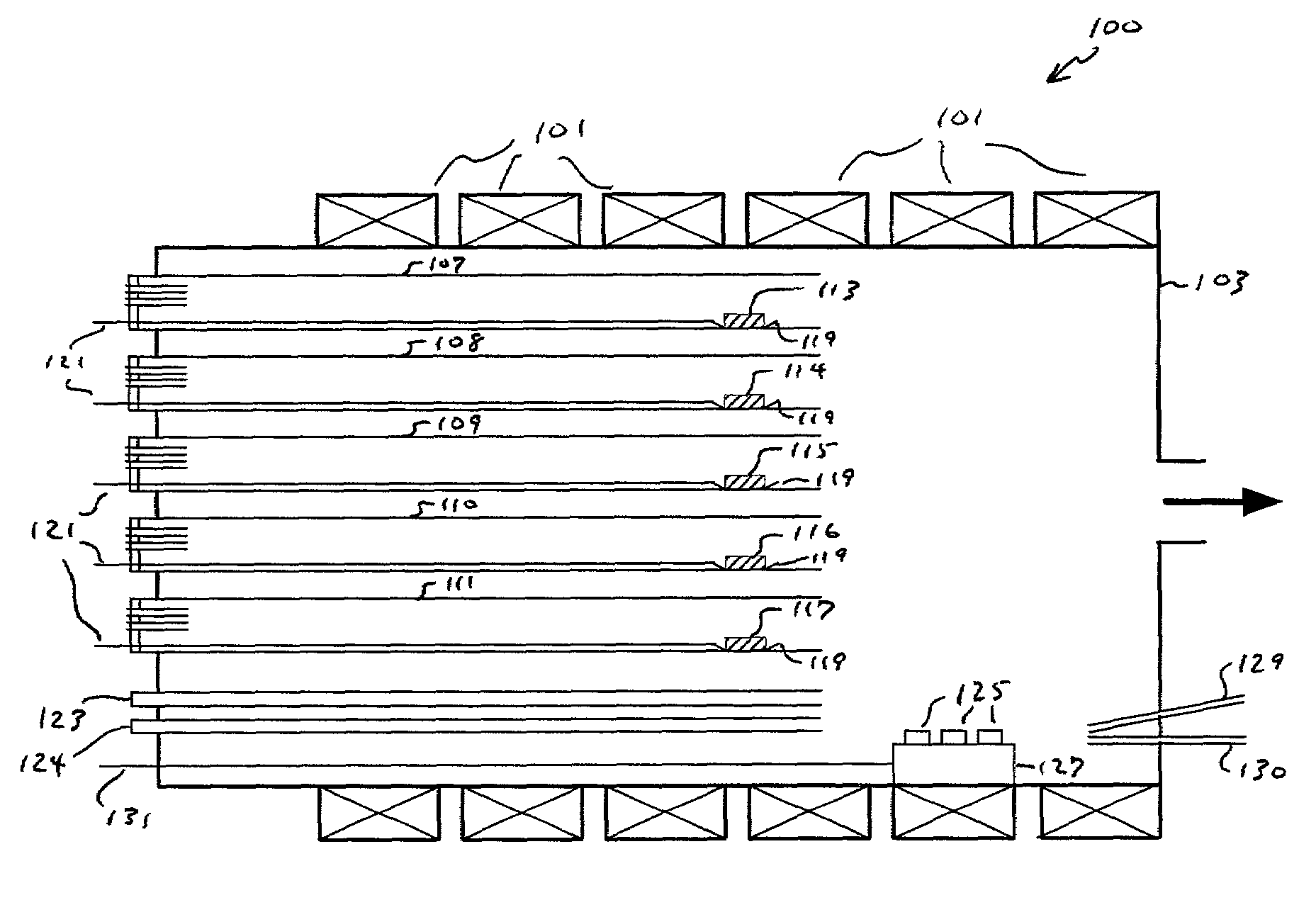
Railcar track cleaning system
InactiveUS6148732AWeaken energyEfficient and effectiveLiquid surface applicatorsSpray nozzlesLong axisSpray nozzle
A track cleaning system mounted on a railcar and comprising track rail cleaning nozzles, leaf removal nozzles and third rail cleaning nozzles. Each of the nozzles may provide a fan-shaped spray pattern diverging to either side of a central axis and having a major axis. For each track rail nozzle, the central axis may be perpendicular to a horizontal top rail surface and the major axis may be perpendicular to the rail surface centerline. For each leaf nozzle, the central axis may be directly downwardly from the horizontal and the major axis may be parallel to an elongated spray bar on which one or more leaf nozzles are mounted. For each third rail nozzle, the central axis may be directed downwardly from the horizontal and the major axis may be positioned vertically. The third rail nozzles may be mounted to the rear of the leaf nozzles to aid in leaf removal. Main water valves are remotely actuated by air to release high pressure water to corresponding sets of nozzles. A pressure control valve controls the pressure of water supplied to the main water valves from a positive displacement, high pressure water pump.
Owner:CAROLINA EQUIP & SUPPLY
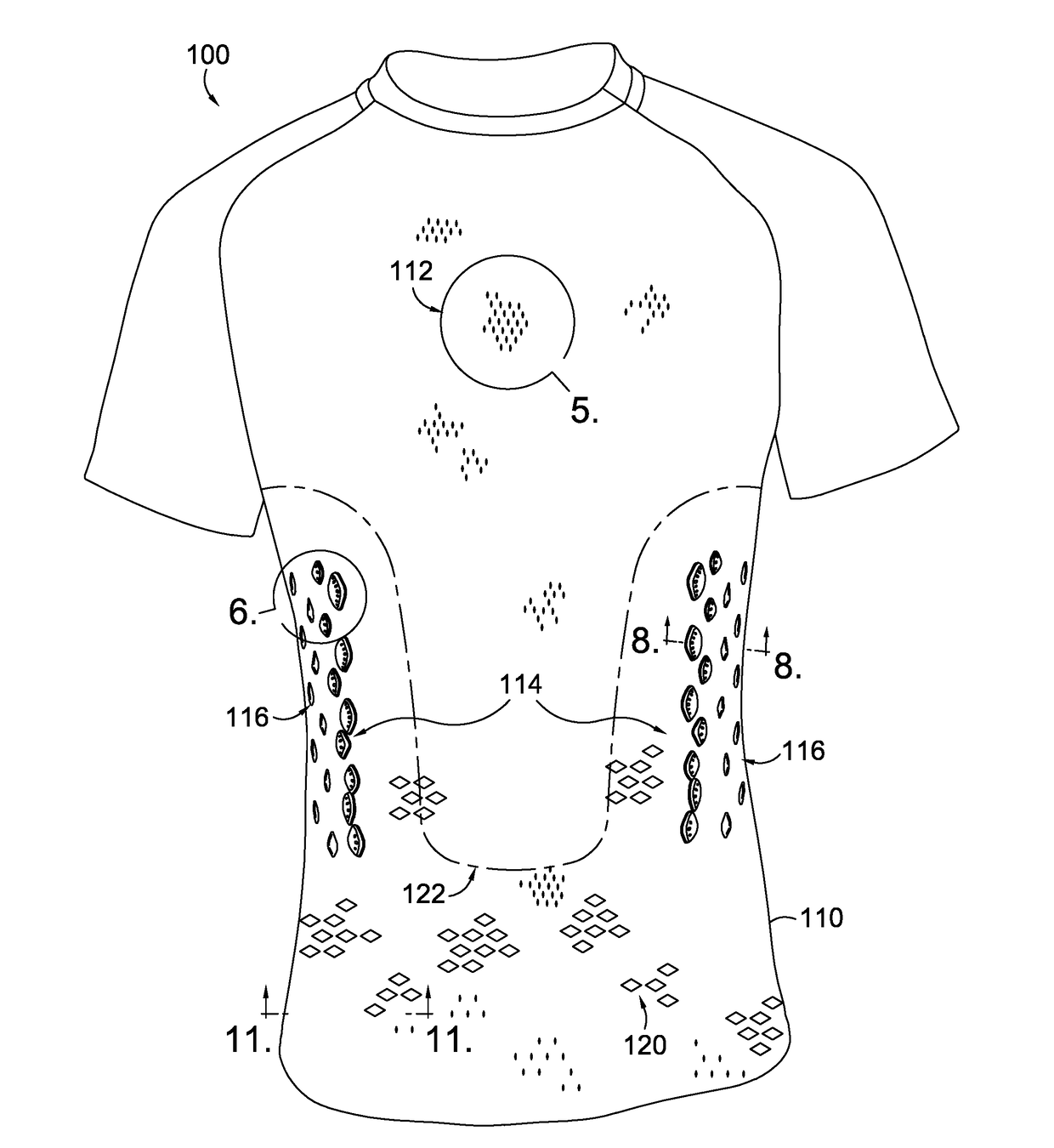
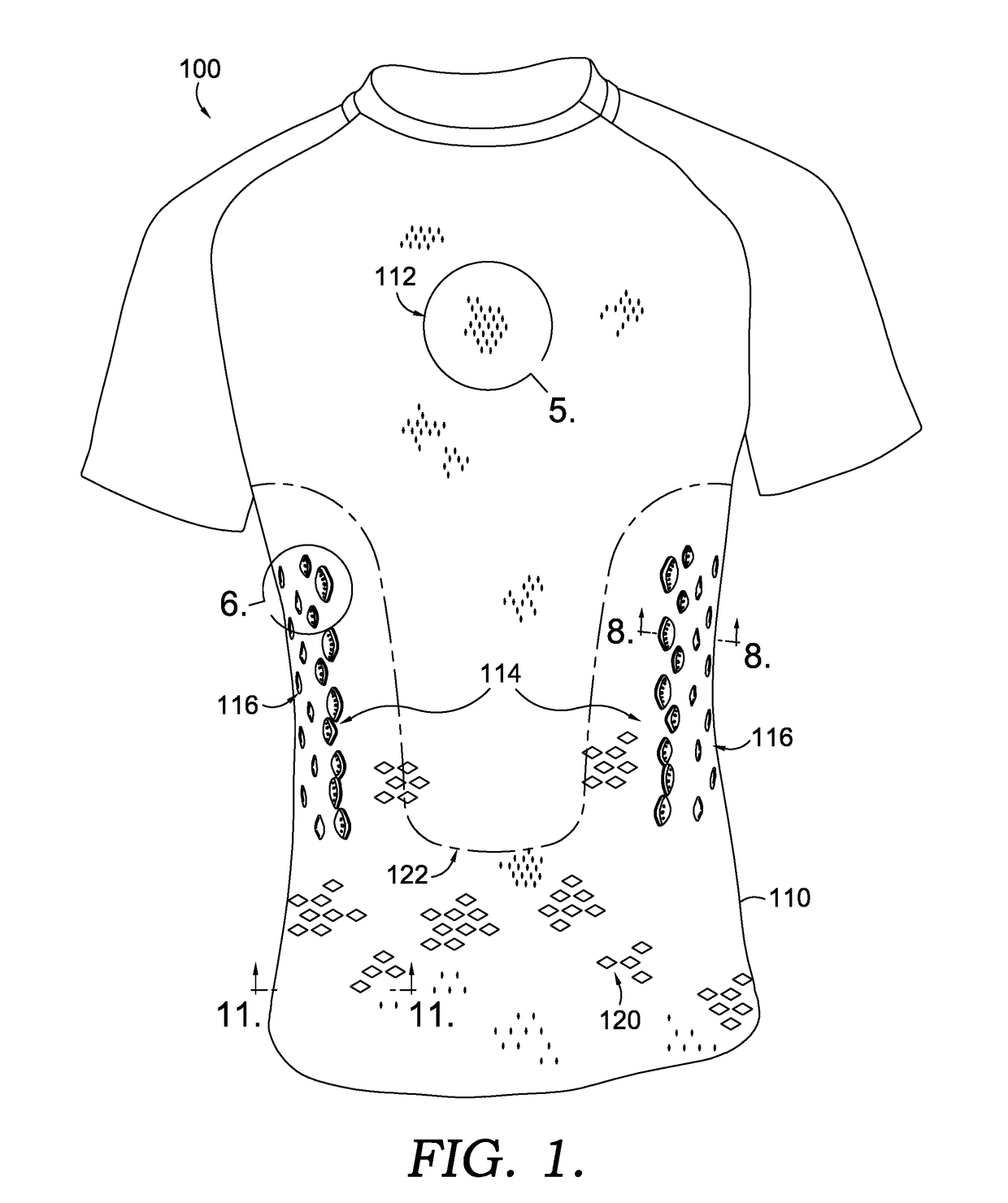
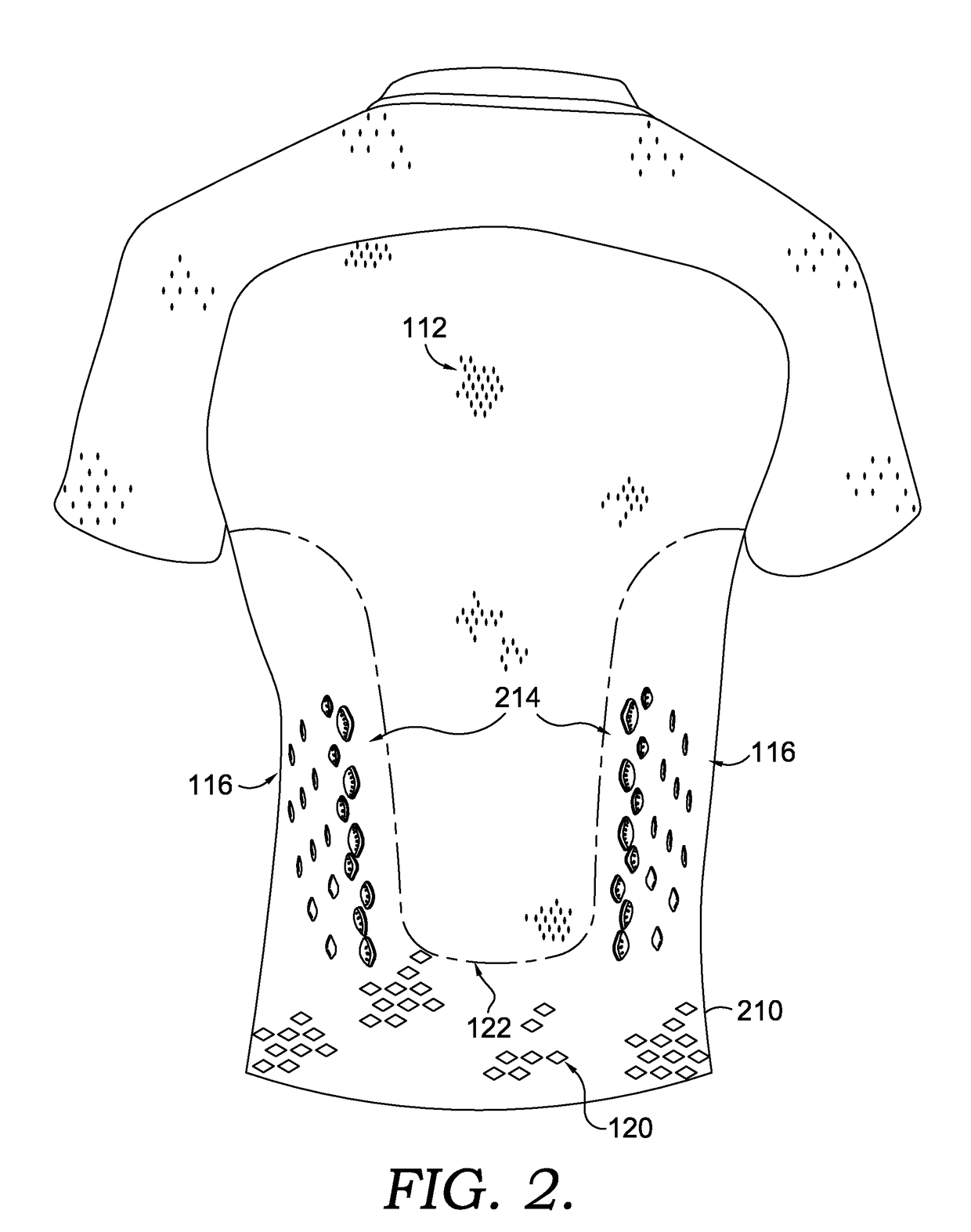
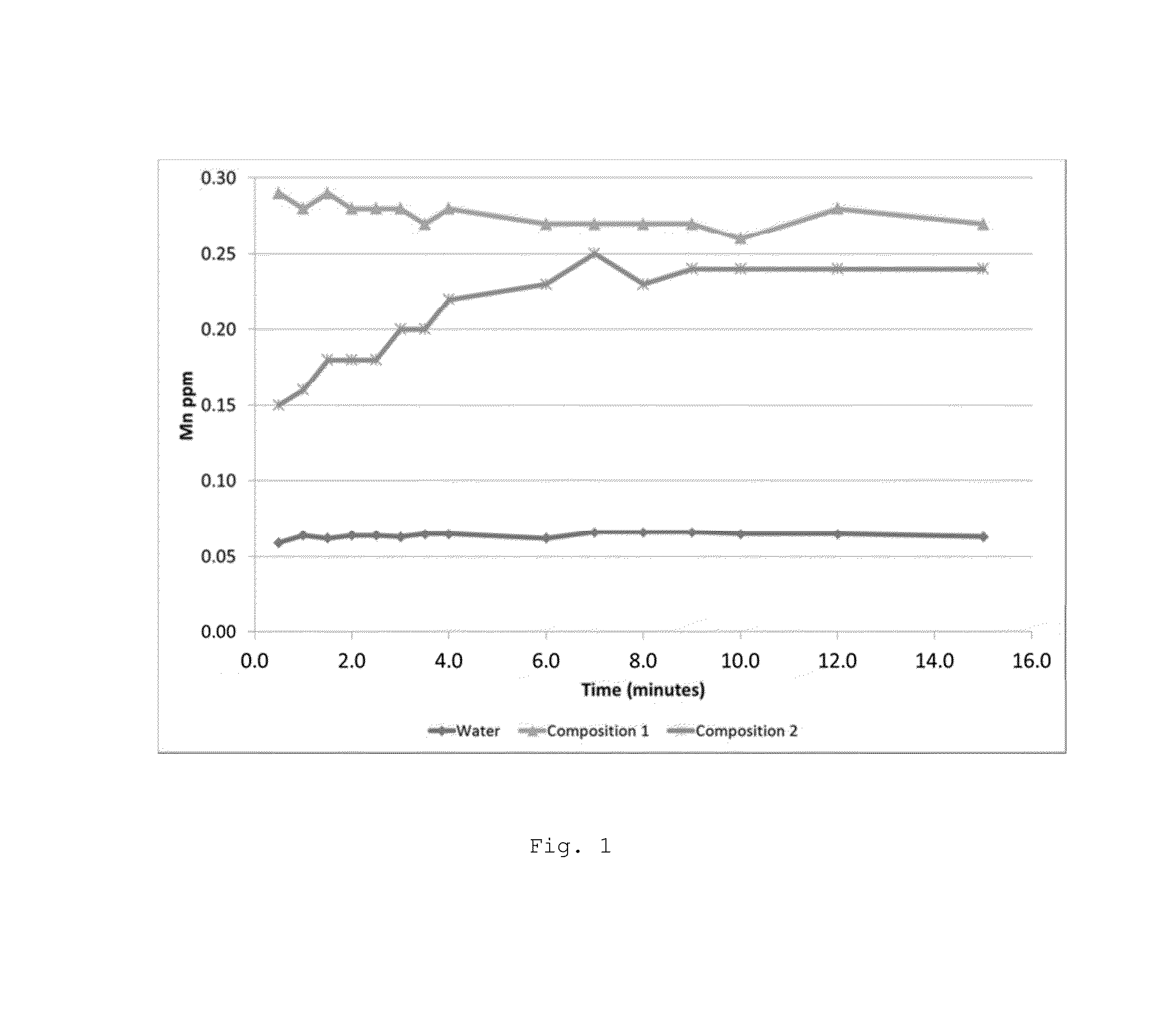
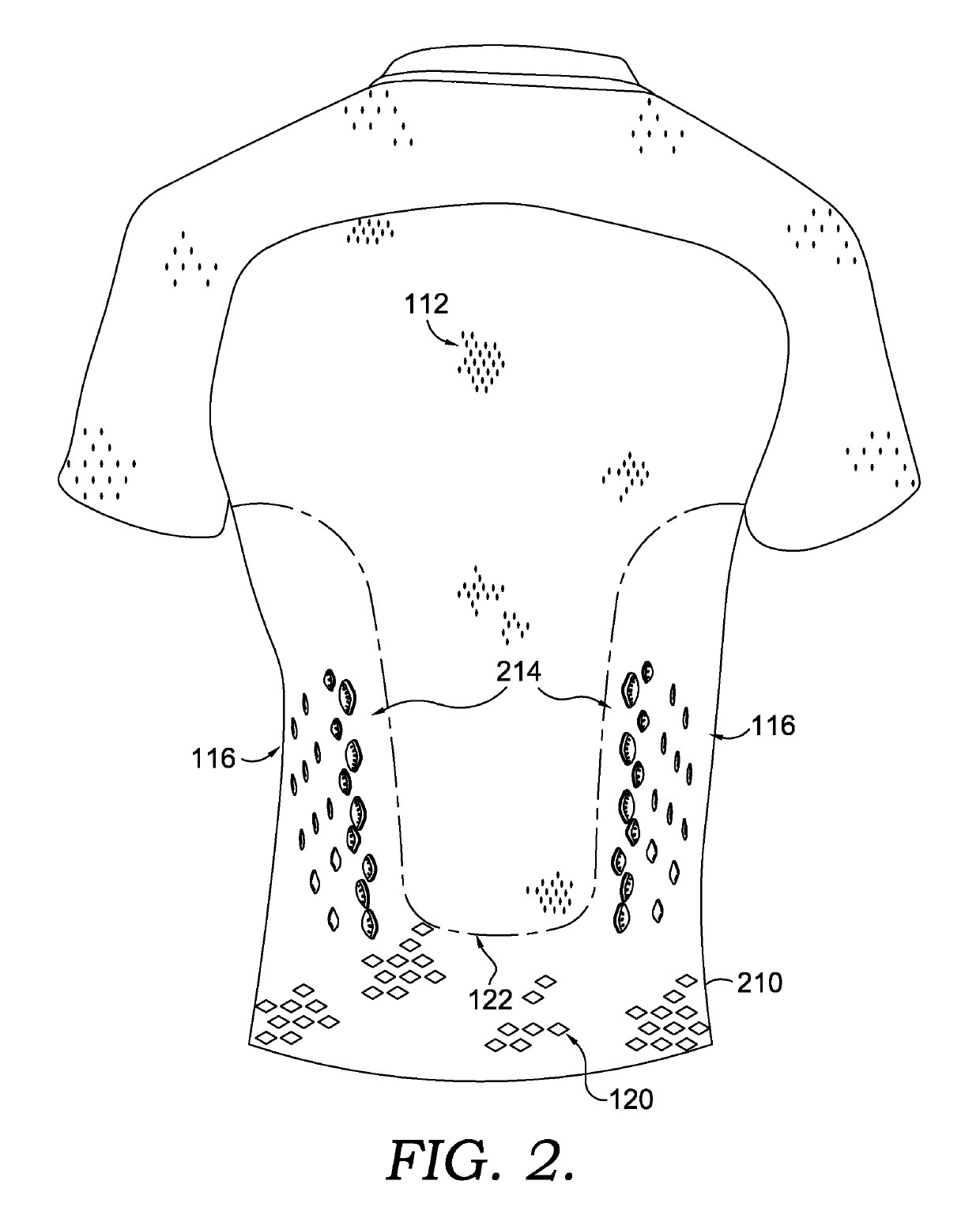
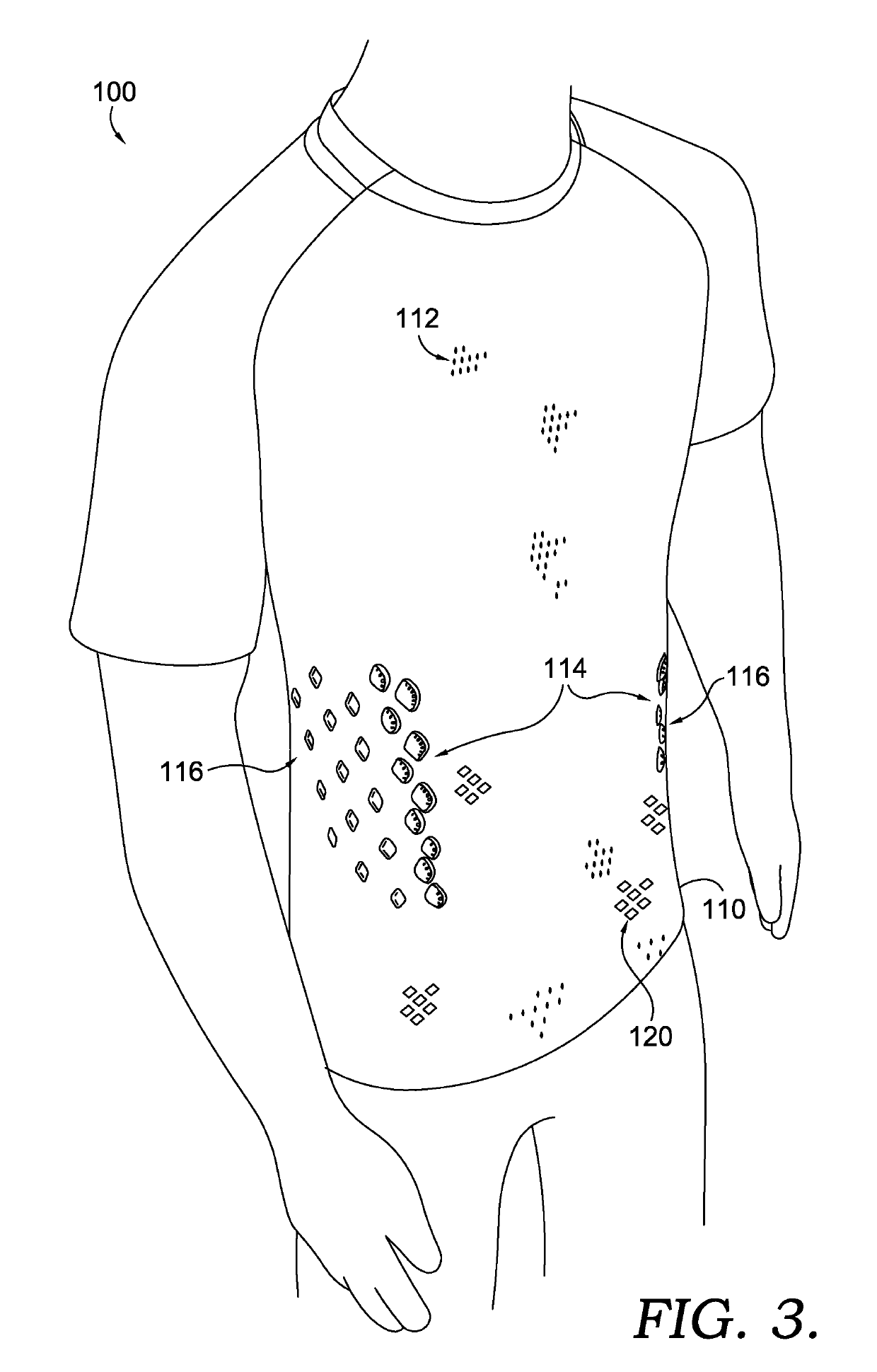
Apparel item configured for reduced cling perception
ActiveUS20170071275A1Reduce perceptionSmall surface areaGarment special featuresWeft knittingSkin surfacePattern perception
An apparel item configured to reduce the perception of cling is provided herein. The apparel item comprises a first set of outwardly-projecting nodes on a first portion of the apparel item, a second set of outwardly-projecting nodes on a second portion of the apparel item, and a third set of inwardly-projecting nodes on a third portion of the apparel item, where the third set of nodes is positioned between the first set of nodes and the second set of nodes. The first and second sets of outwardly-projecting nodes comprise apertures that provide a communication passage from an outer surface of the apparel item to an inner surface of the apparel item. Besides reducing the surface area of the apparel item that comes into contact with a wearer's skin surface, the nodes also facilitate cooling the wearer and speed up drying times of the apparel item when being worn.
Owner:NIKE INC
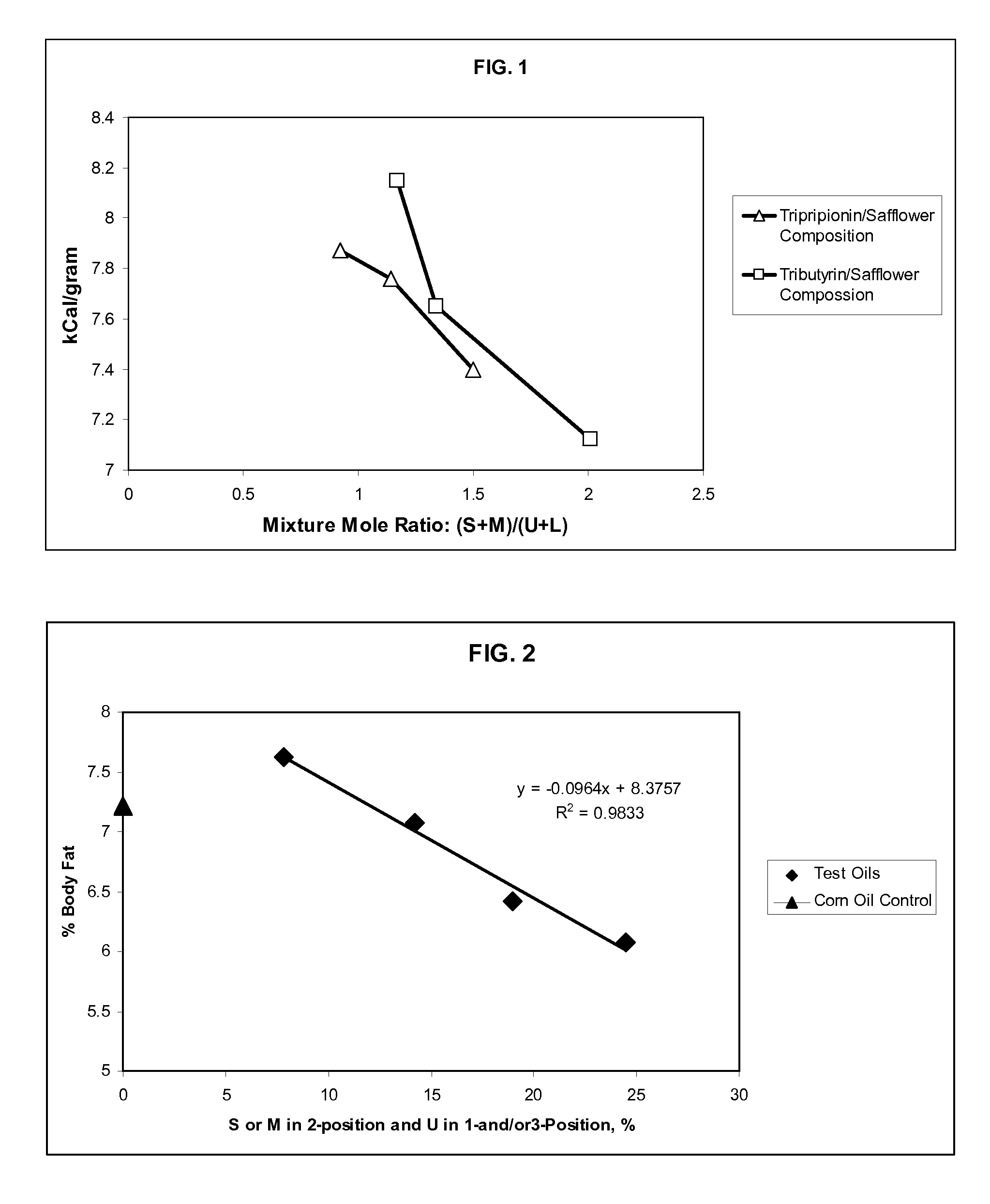
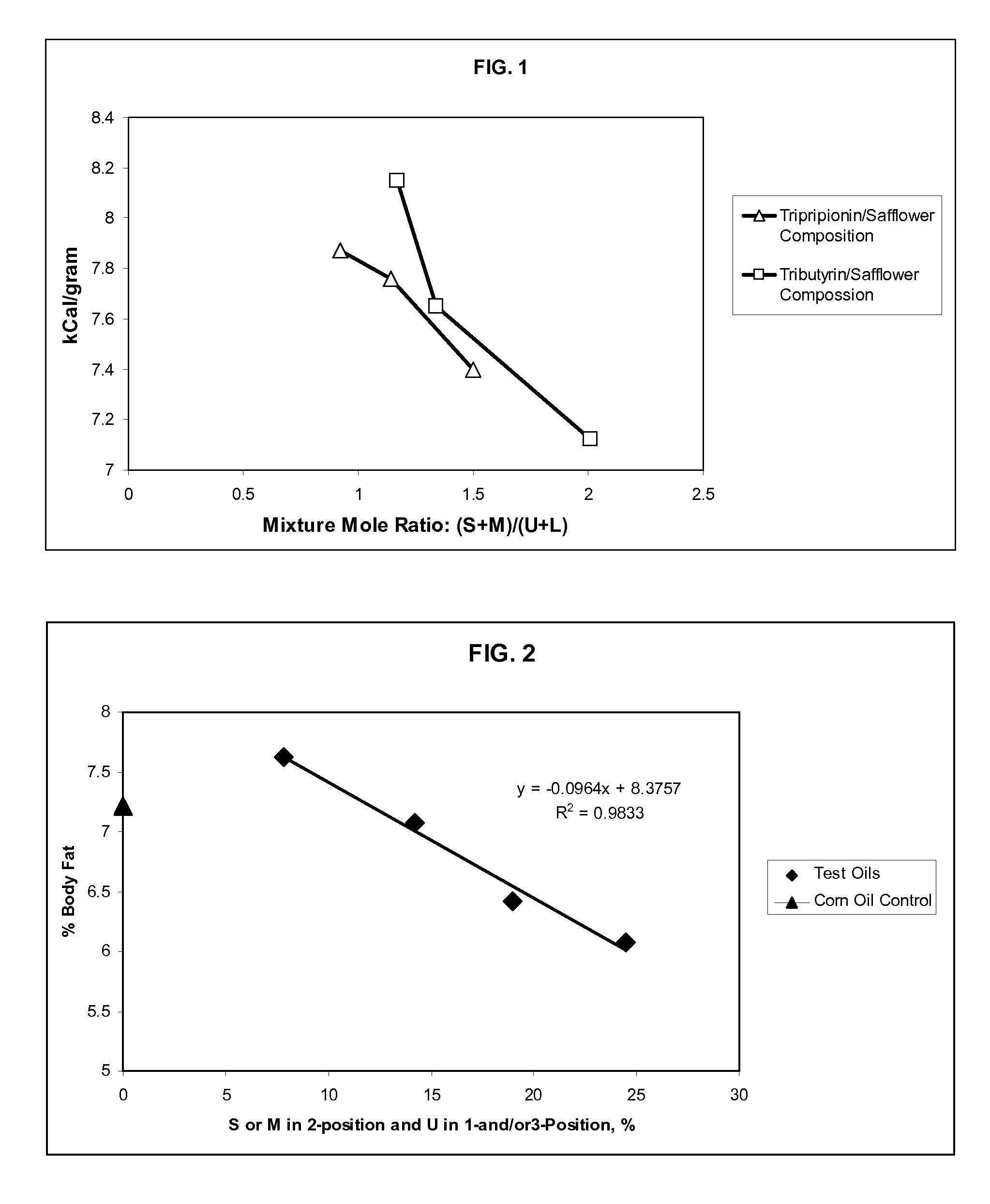
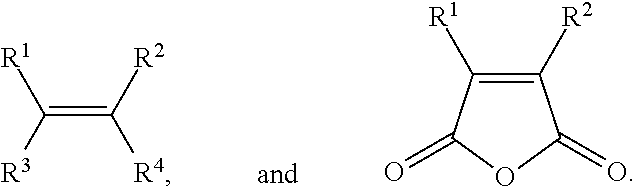
Structured Lipid Compositions And Methods Of Formulation Thereof
ActiveUS20090123634A1High energyIncrease valueFood preparationEdible oils/fats with aqeous phaseTriglycerideWeight management
Lipid compositions comprising specific mixtures of edible synthetic triglycerides are provided that are useful in formulating food products having highly desirable dietary benefits. The novel lipid compositions allow simultaneous access to highly desirable dietary benefits such as delivery of calorie reduction, weight management, health benefits, or any combination thereof, and they also may be formulated trans-fatty acid free.
Owner:INTERCONTINENTAL GREAT BRANDS LLC
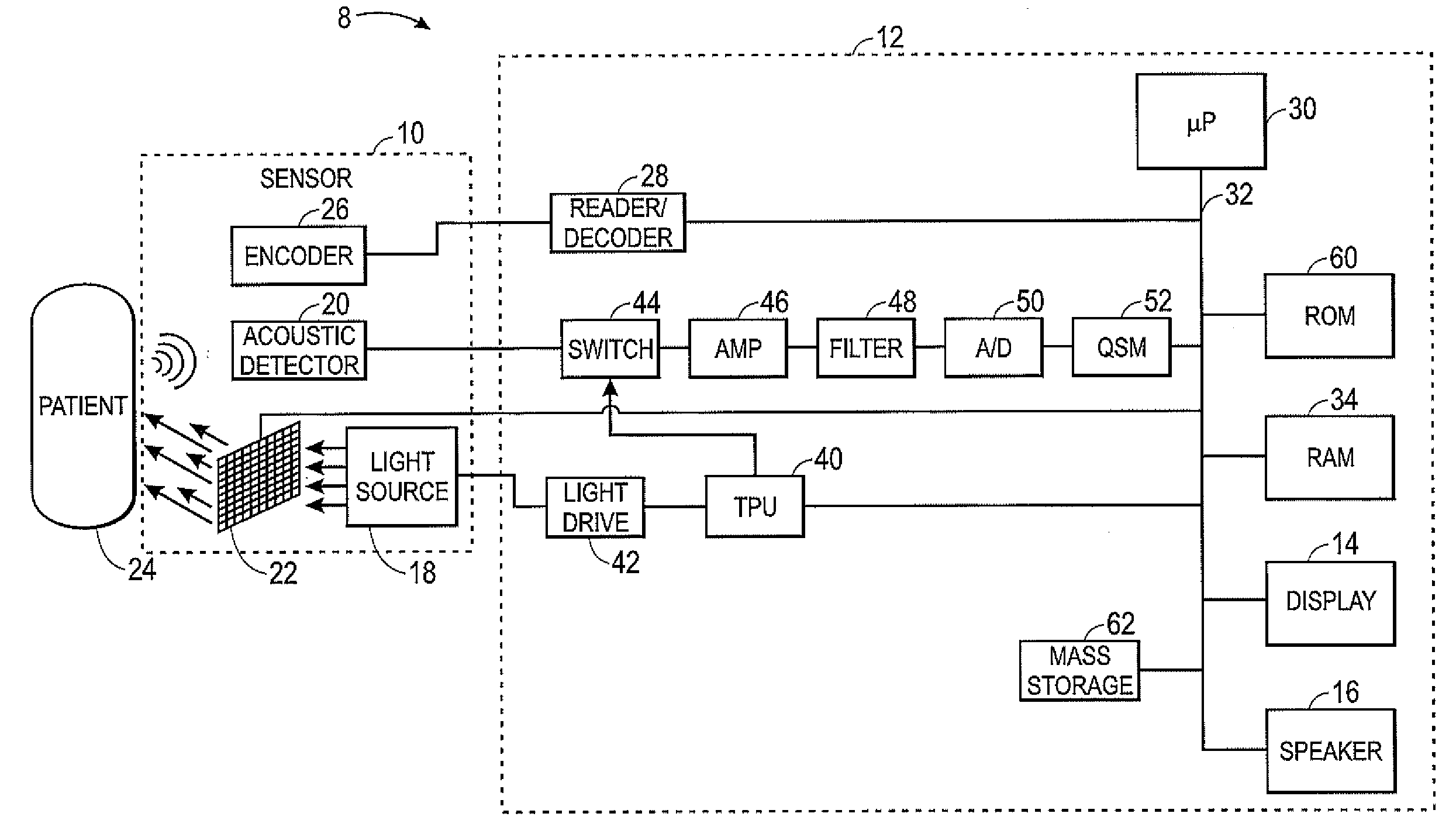
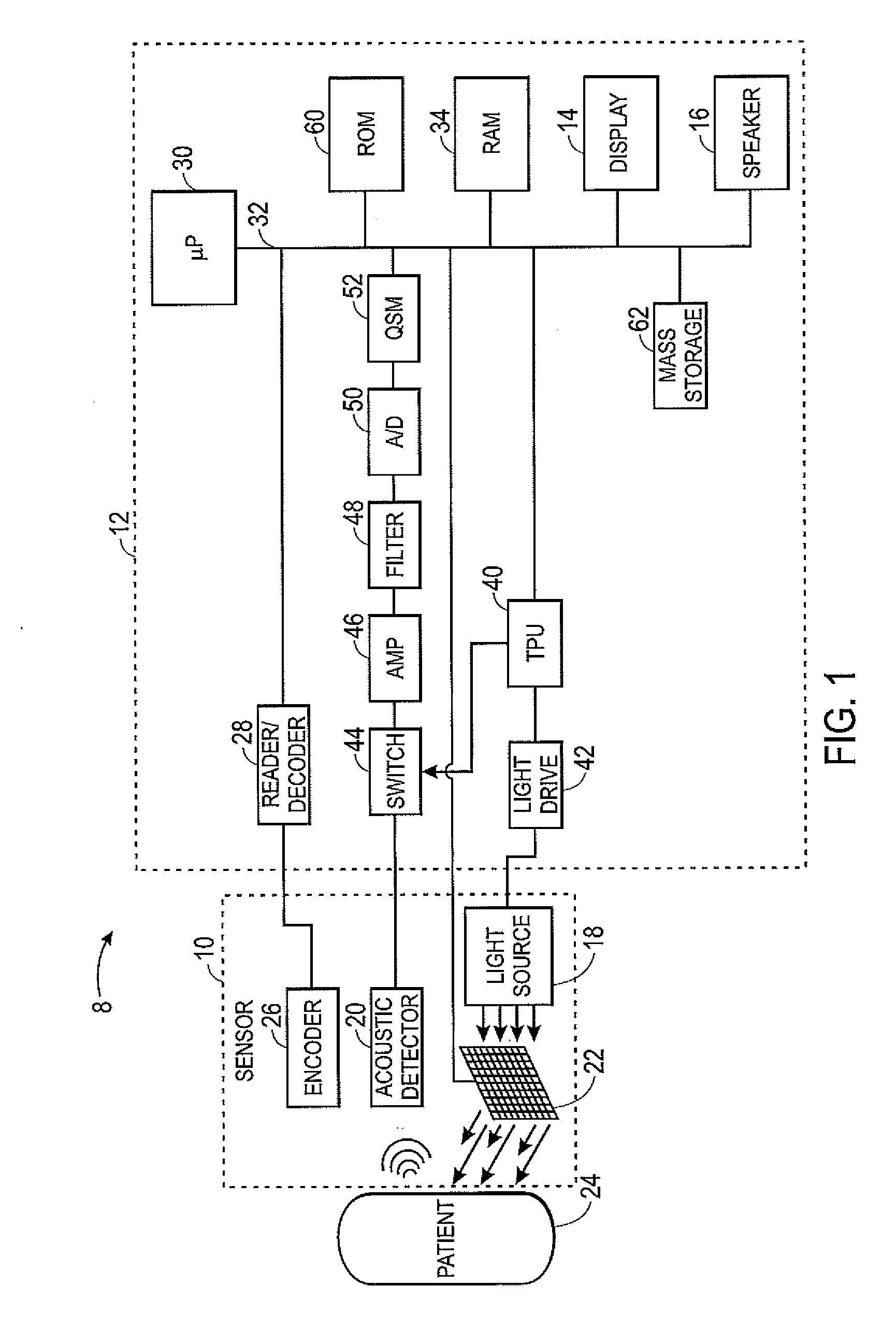
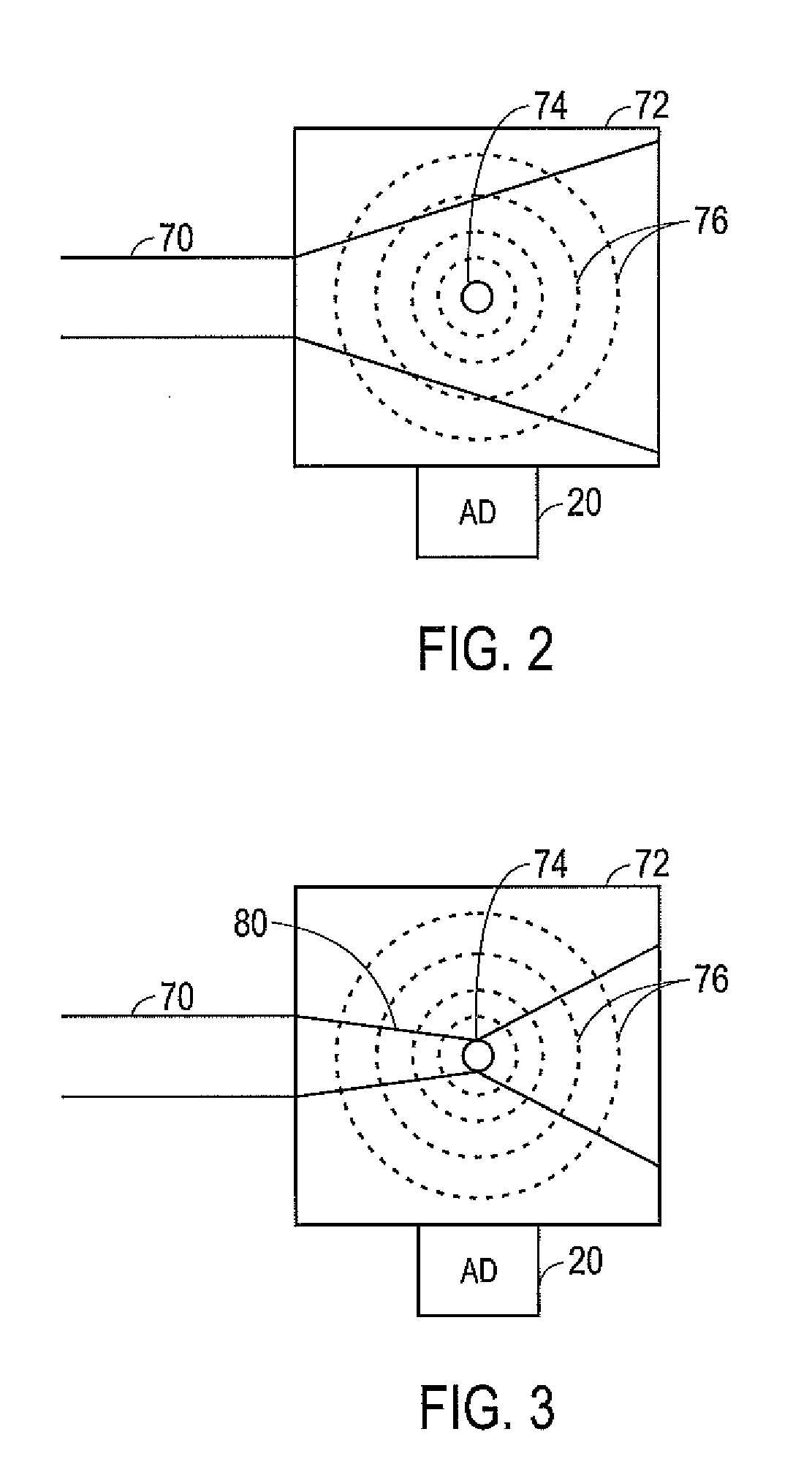
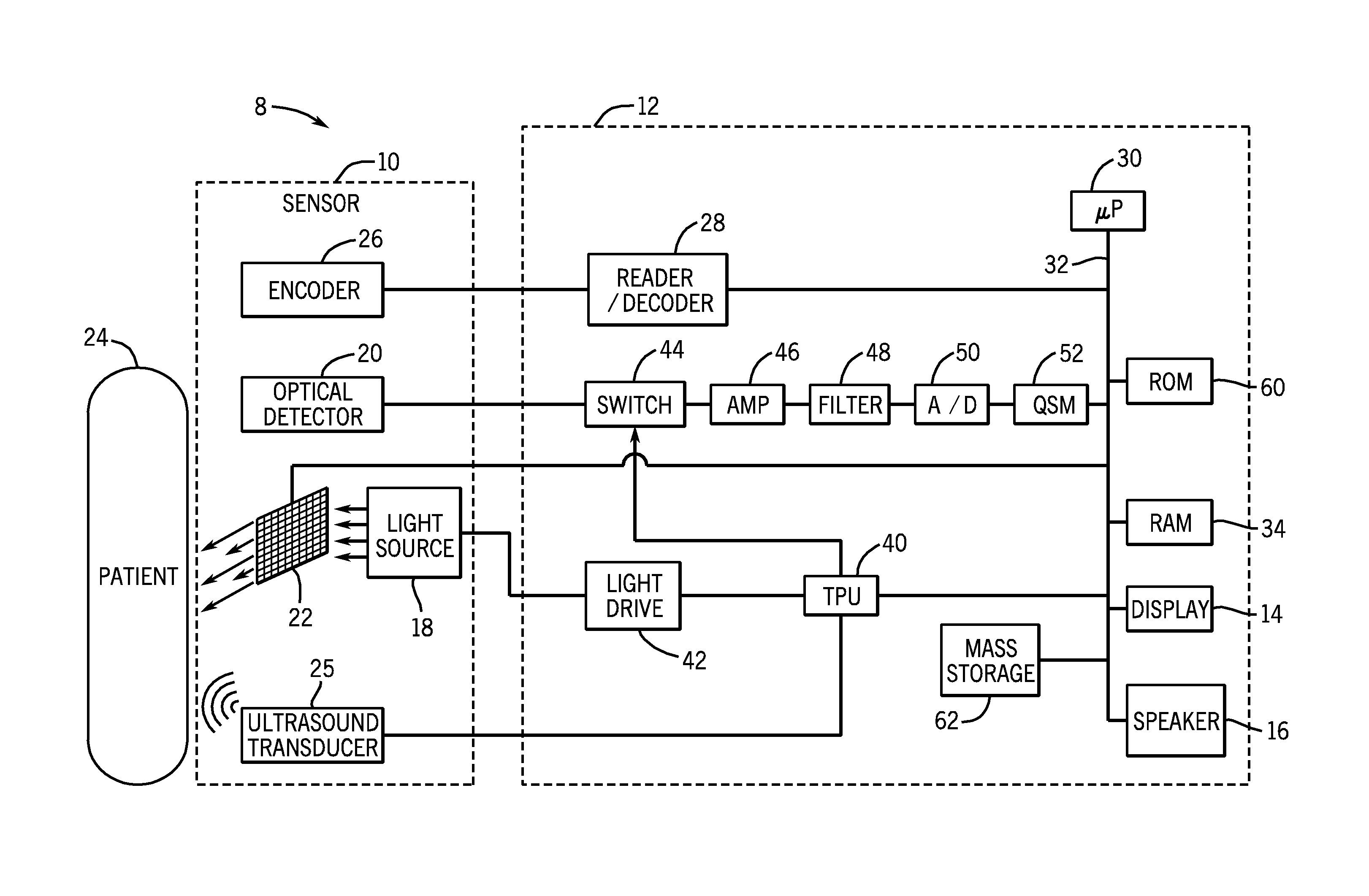
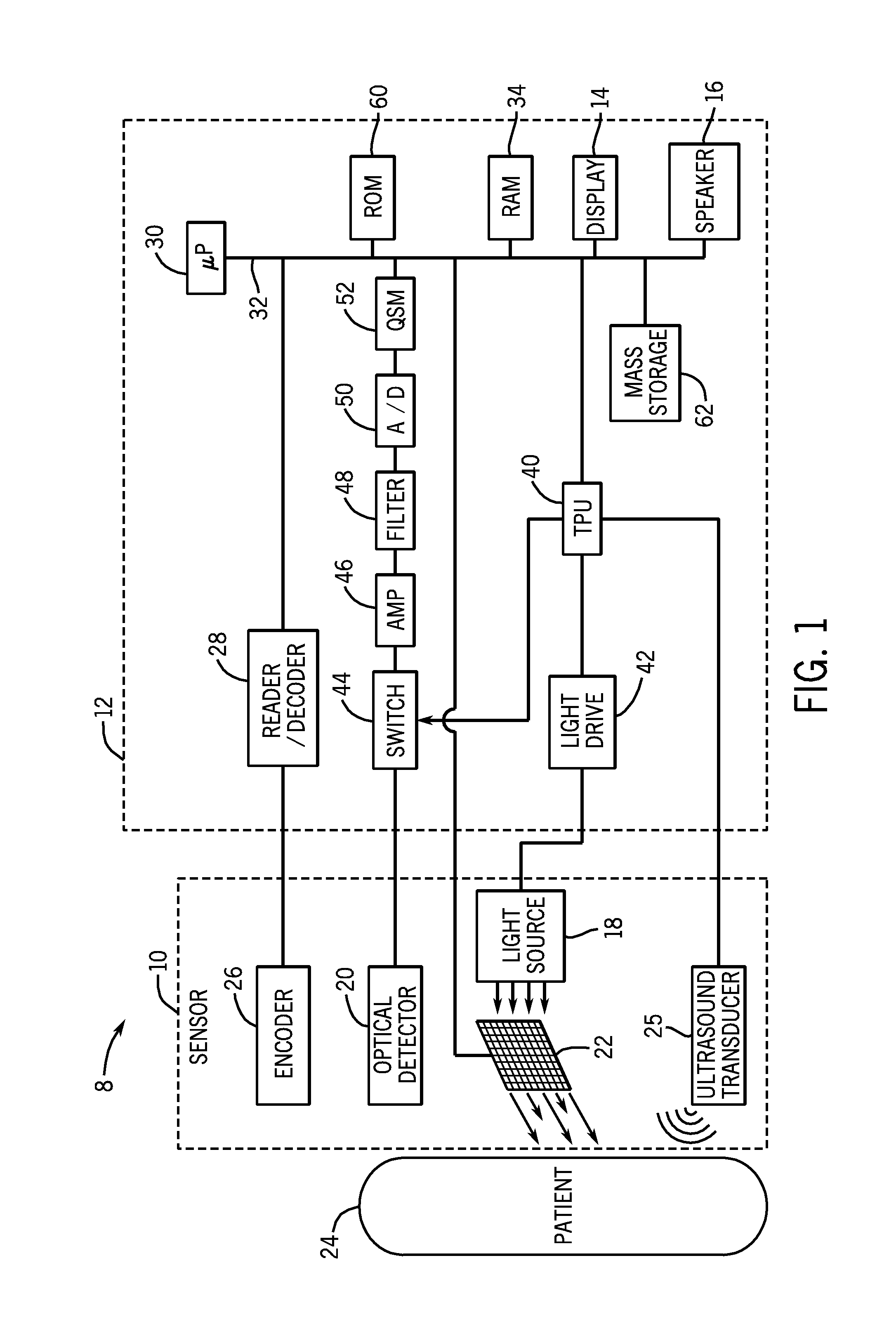
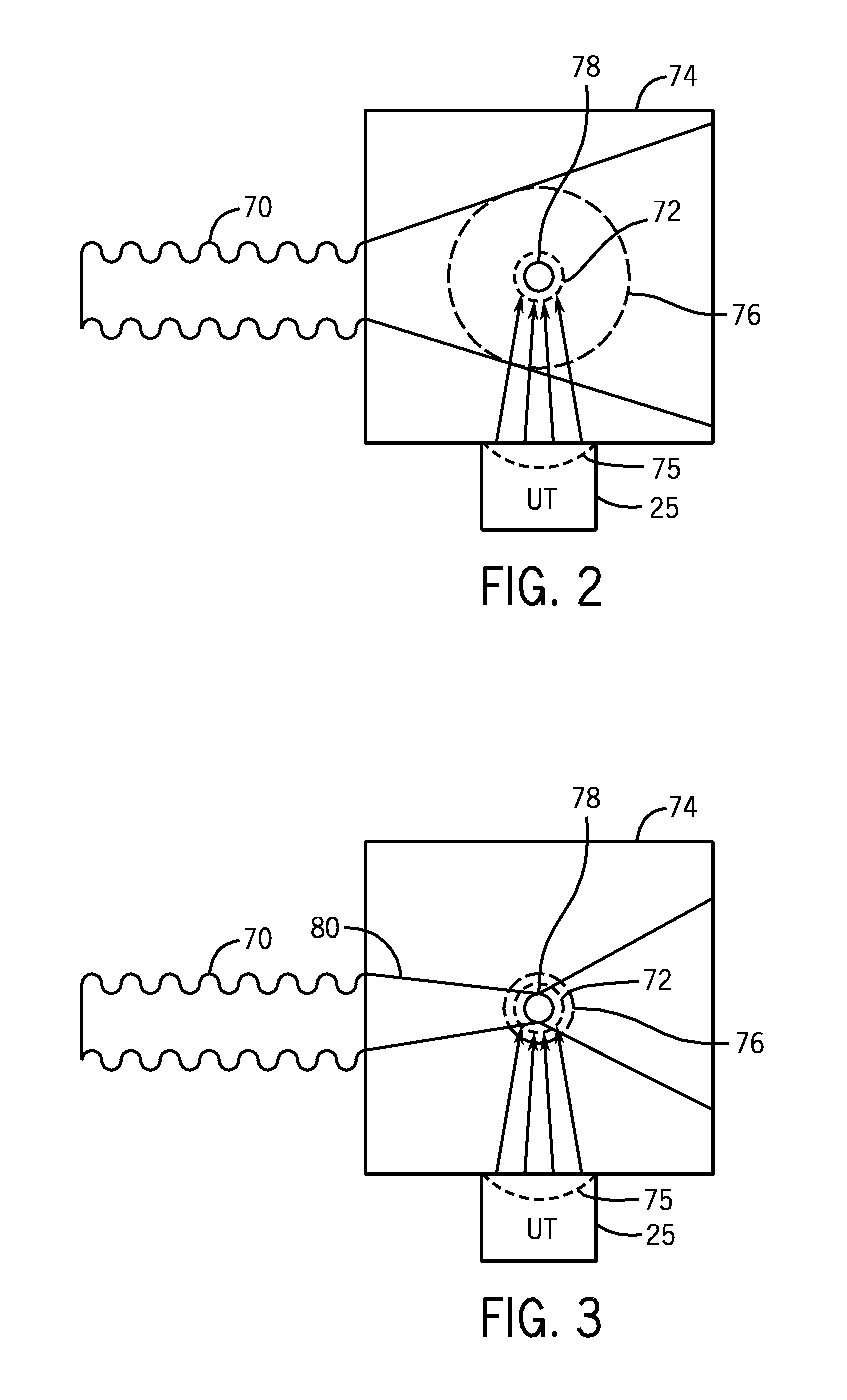
Photoacoustic Spectroscopy With Focused Light
InactiveUS20110083509A1Reduce and eliminate effect of light diffusionReducing the ultrasonic waves generatedUltrasonic/sonic/infrasonic diagnosticsVibration measurement in solidsPhotoacoustic microscopyPhotoacoustic spectroscopy
Photoacoustic measurements utilize emitted light to generate an acoustic response in tissue, with the acoustic response being proportional to the presence of an absorber of the light in the tissue. The present disclosure relates the use of focused light to acquire photoacoustic measurements. In one embodiment, the light is modulated, such as spatially modulated, such that the light may be focused within an otherwise scattering medium, such as tissue.
Owner:TYCO HEALTHCARE GRP LP
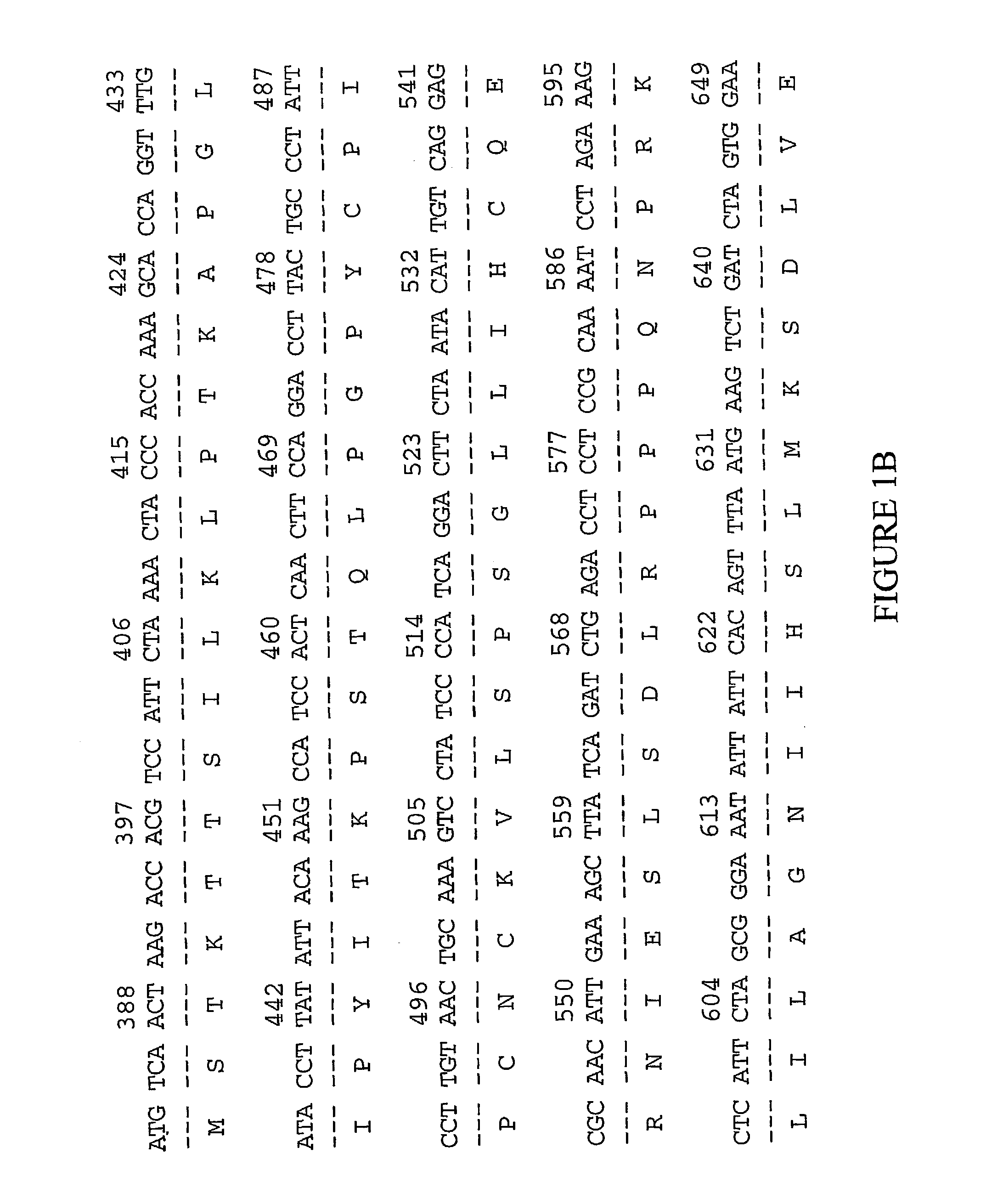
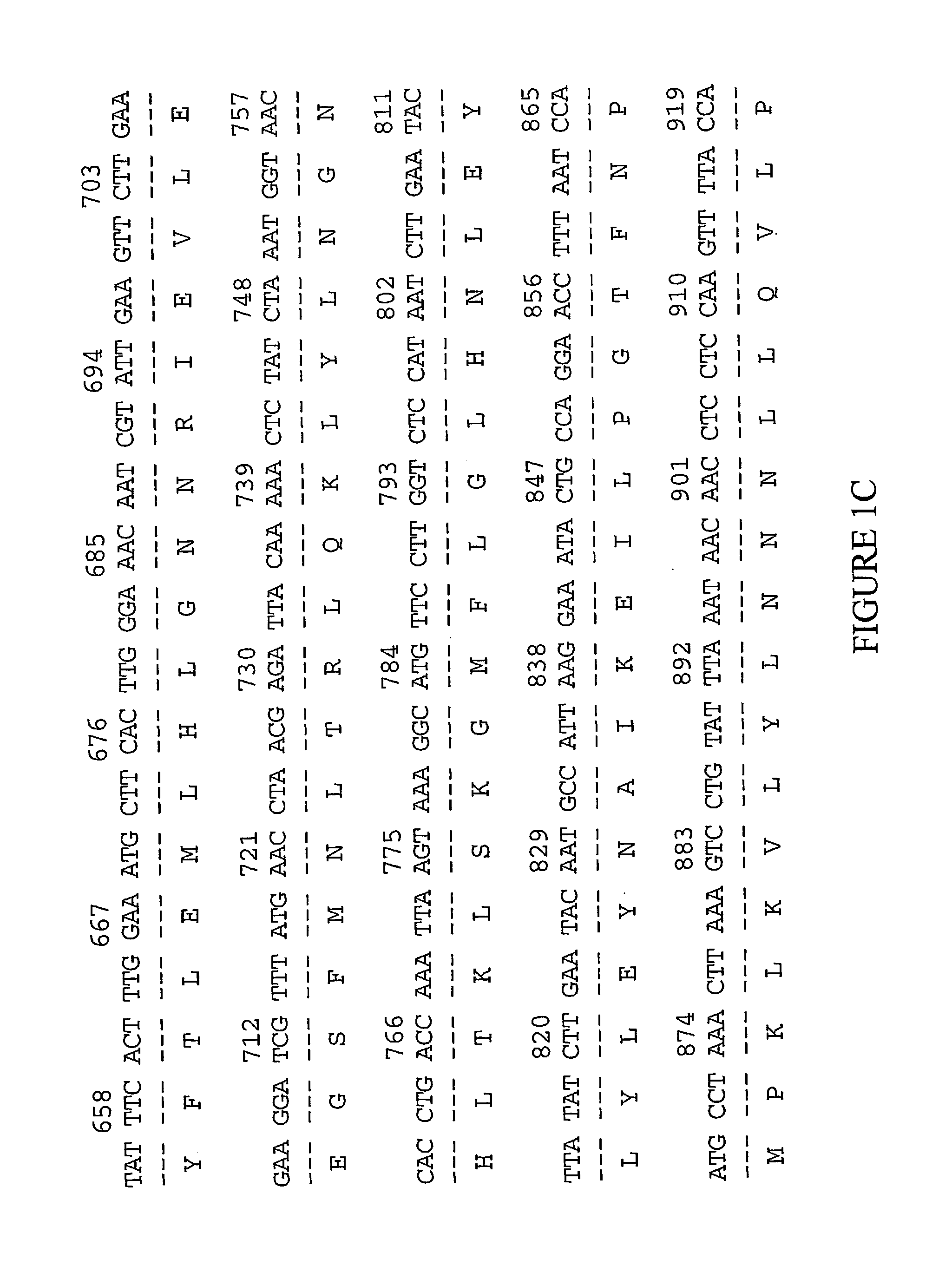
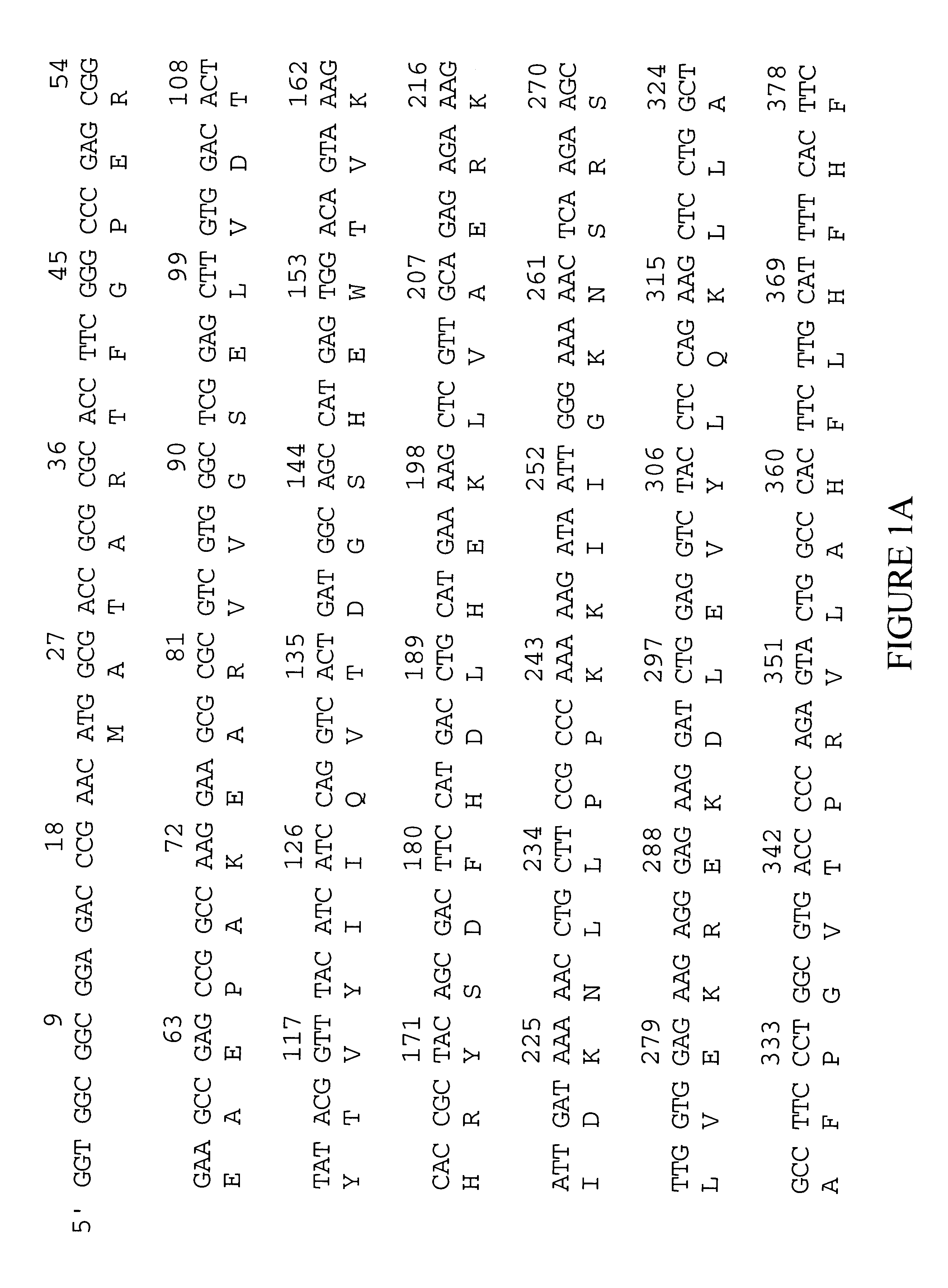
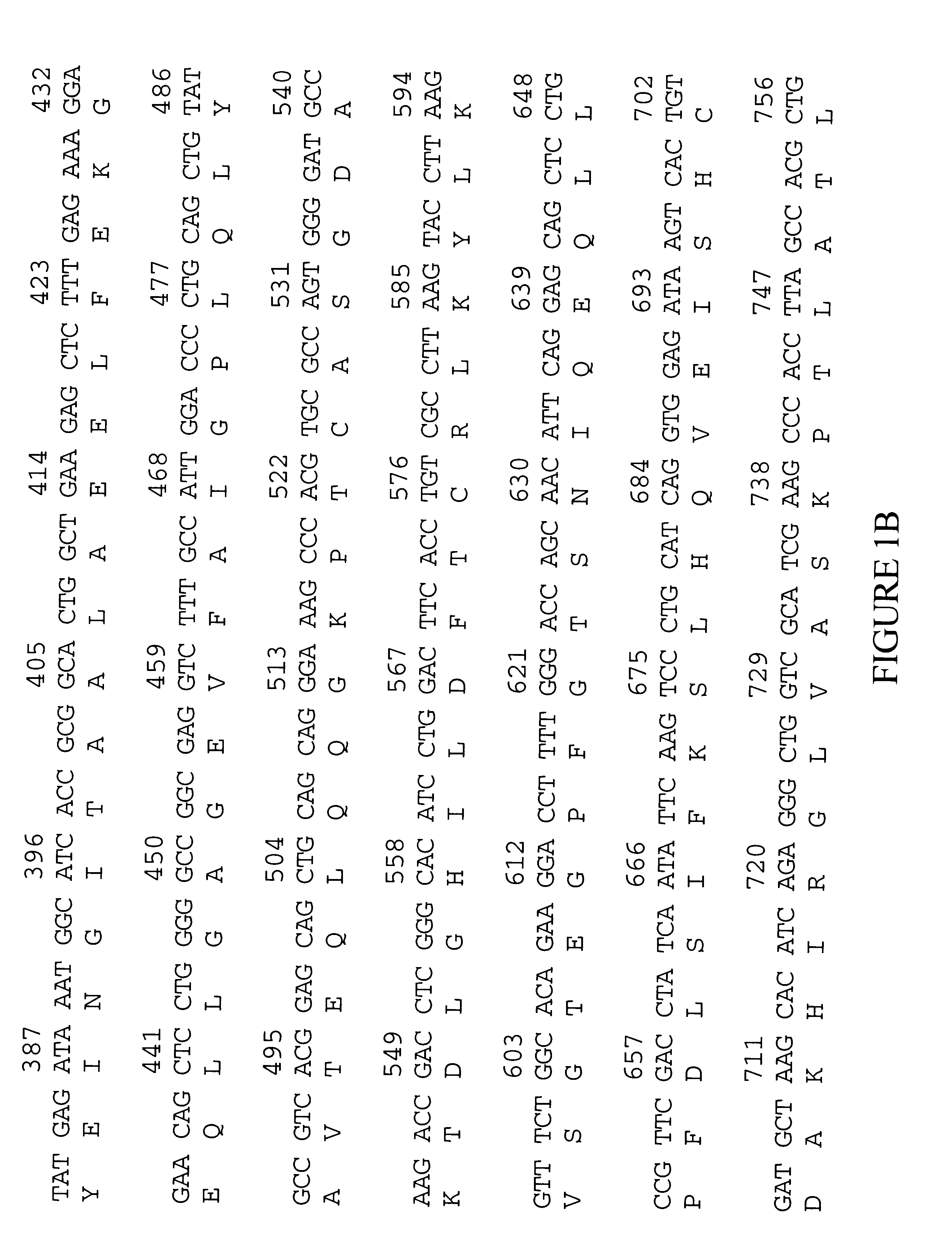
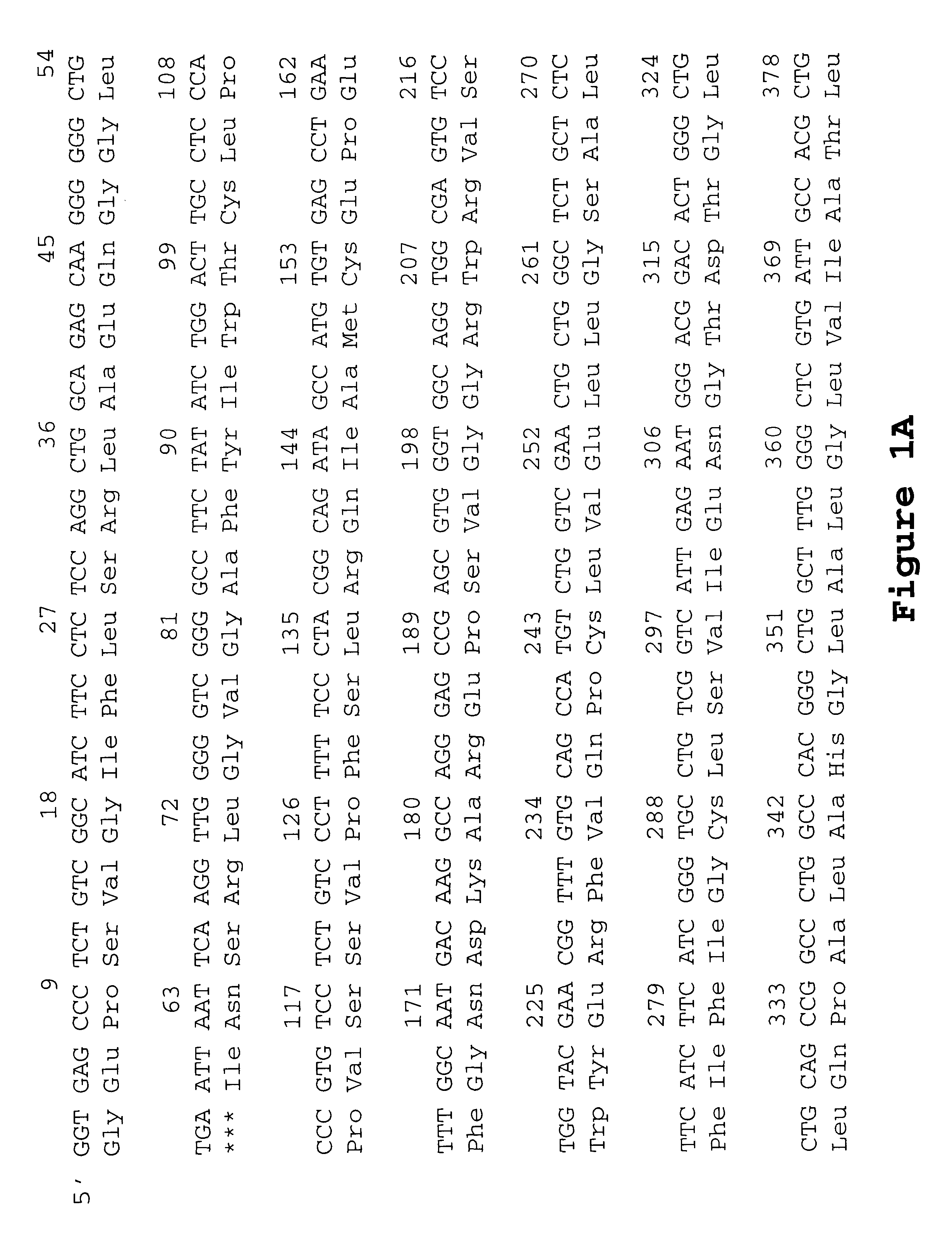
Ras association domain containing protein
InactiveUS6485910B1Enhanced interactionHigh frequencySugar derivativesPeptide/protein ingredientsAllergyADAMTS Proteins
The invention provides a mammalian cDNA which encodes a mammalian Ras association domain containing protein. It also provides for the use of the cDNA, fragments, complements, and variants thereof and of the encoded protein, portions thereof and antibodies thereto for diagnosis and treatment of cell proliferative and inflammatory disorders, particularly thymus hyperplasia, allergies, asthma, and hypereosinophilia. The invention additionally provides expression vectors and host cells for the production of the protein and a transgenic model system.
Owner:INCYTE
Novel compounds
InactiveUS20030211515A1Enhanced interactionHigh frequencyOrganic active ingredientsFungiNucleotidePolynucleotide
Owner:INCYTE
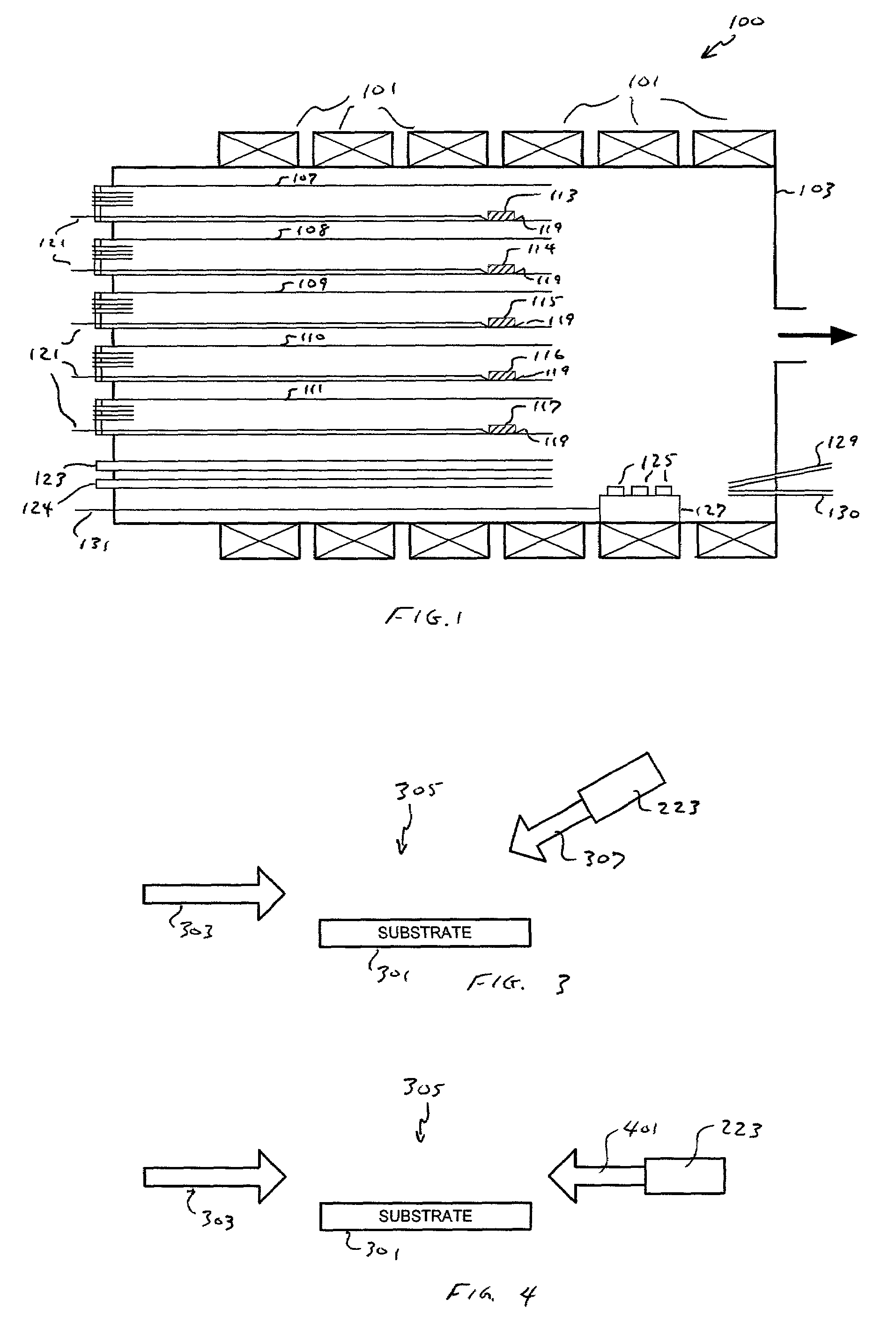
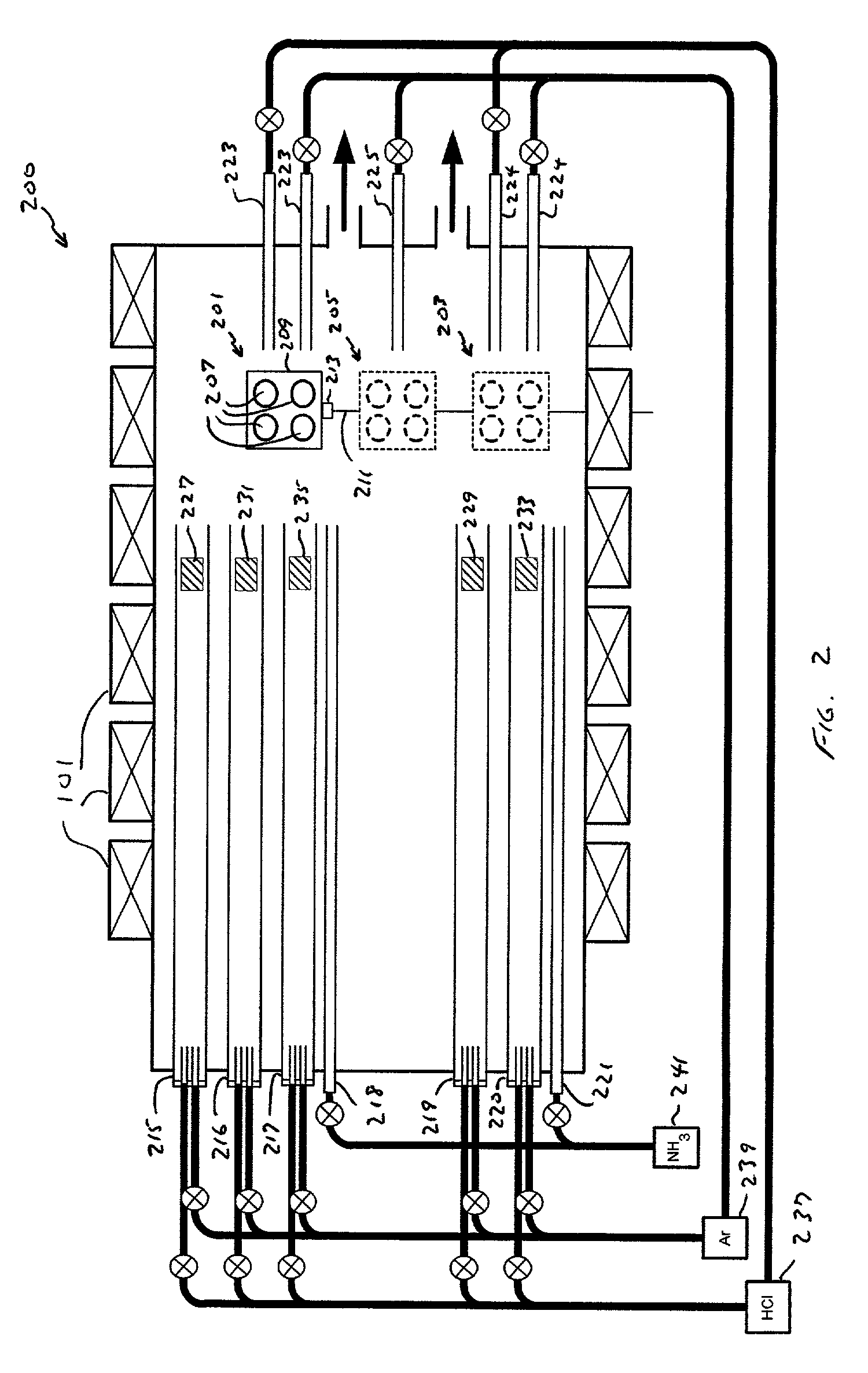
Apparatus for epitaxially growing semiconductor device structures with sharp layer interfaces utilizing HVPE
InactiveUS7670435B2Reduce conductivityPreventing thermal shockPolycrystalline material growthSemiconductor/solid-state device manufacturingLayer interfaceReactive gas
A method and apparatus for fabricating thin Group III nitride layers as well as Group III nitride layers that exhibit sharp layer-to-layer interfaces are provided. According to one aspect, an HVPE reactor includes one or more gas inlet tubes adjacent to the growth zone, thus allowing fine control of the delivery of reactive gases to the substrate surface. According to another aspect, an HVPE reactor includes both a growth zone and a growth interruption zone. According to another aspect, an HVPE reactor includes a slow growth rate gallium source, thus allowing thin layers to be grown. Using the slow growth rate gallium source in conjunction with a conventional gallium source allows a device structure to be fabricated during a single furnace run that includes both thick layers (i.e., utilizing the conventional gallium source) and thin layers (i.e., utilizing the slow growth rate gallium source).
Owner:OSTENDO TECH INC
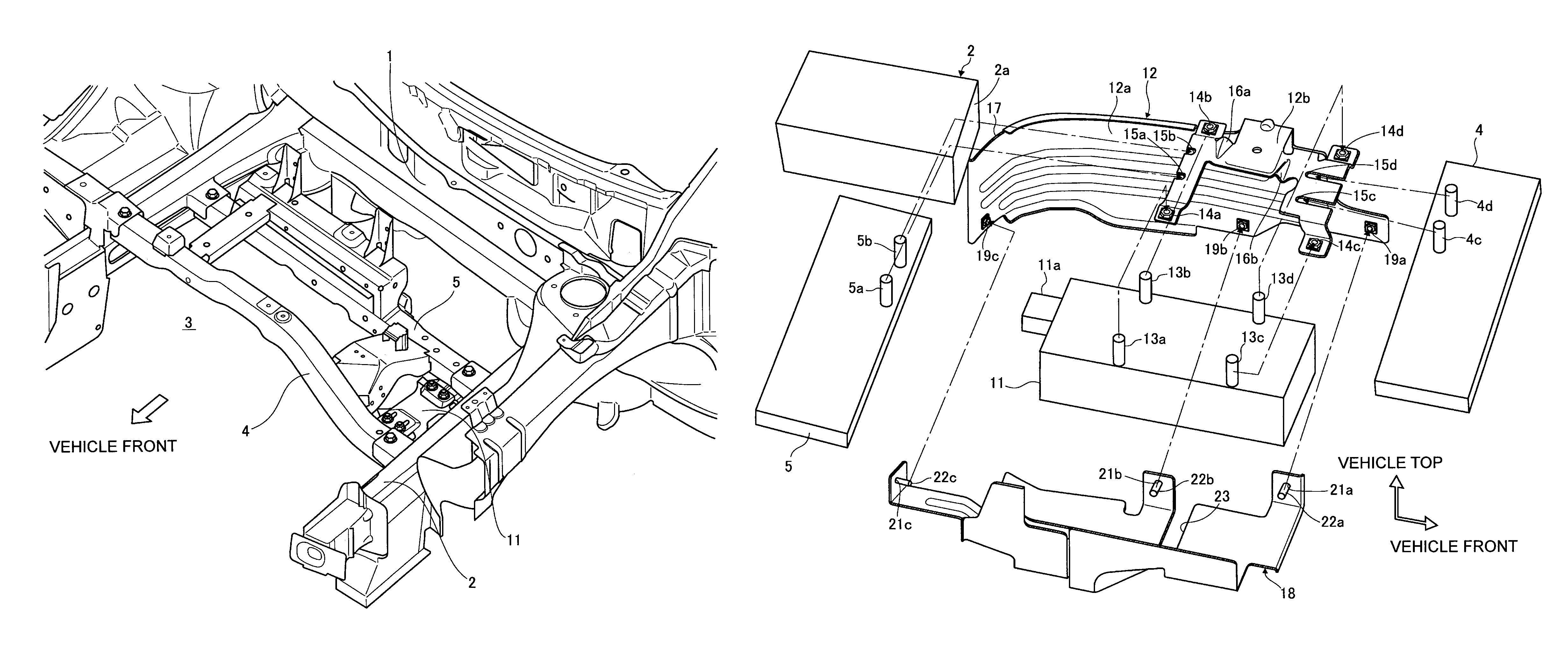
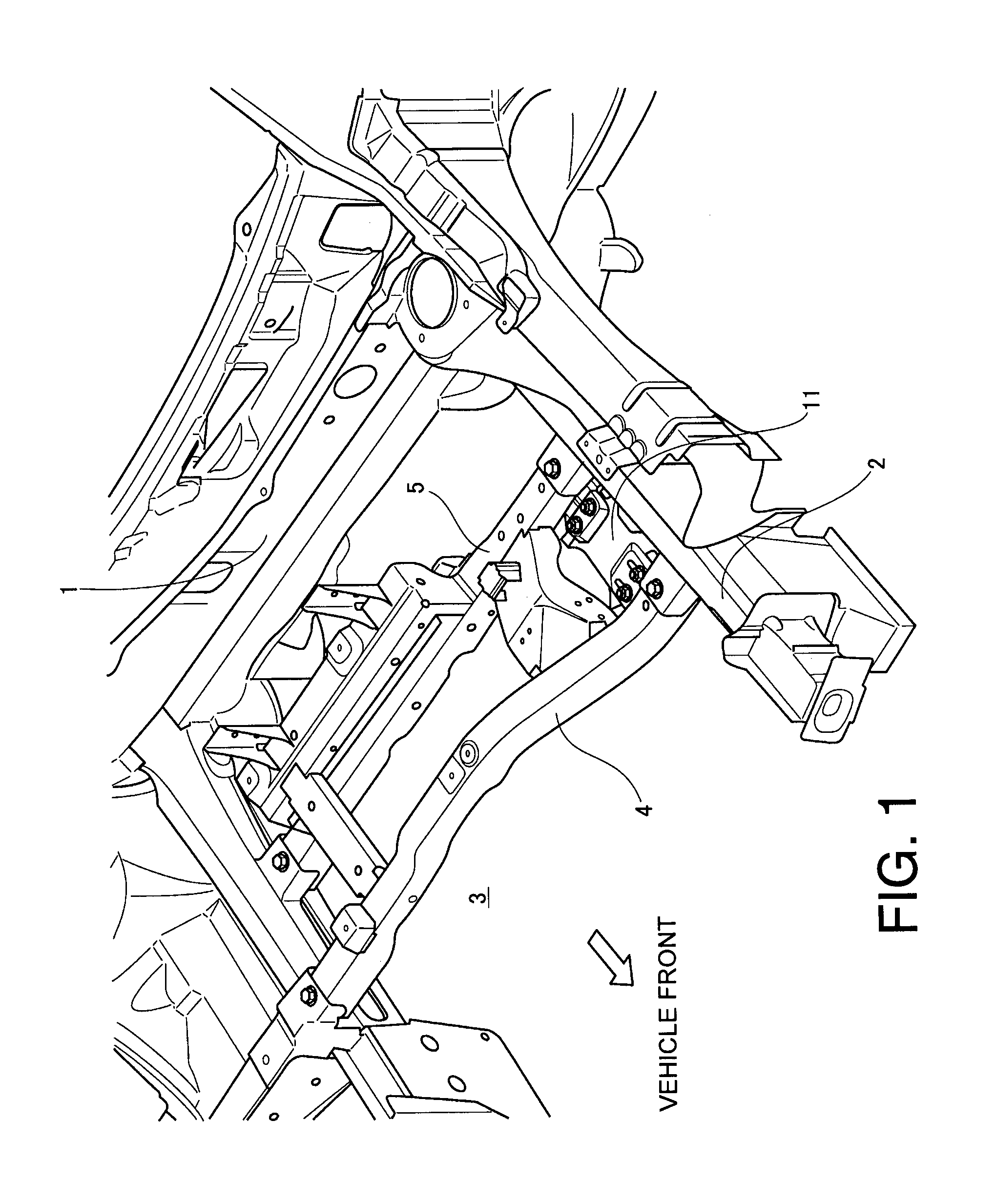
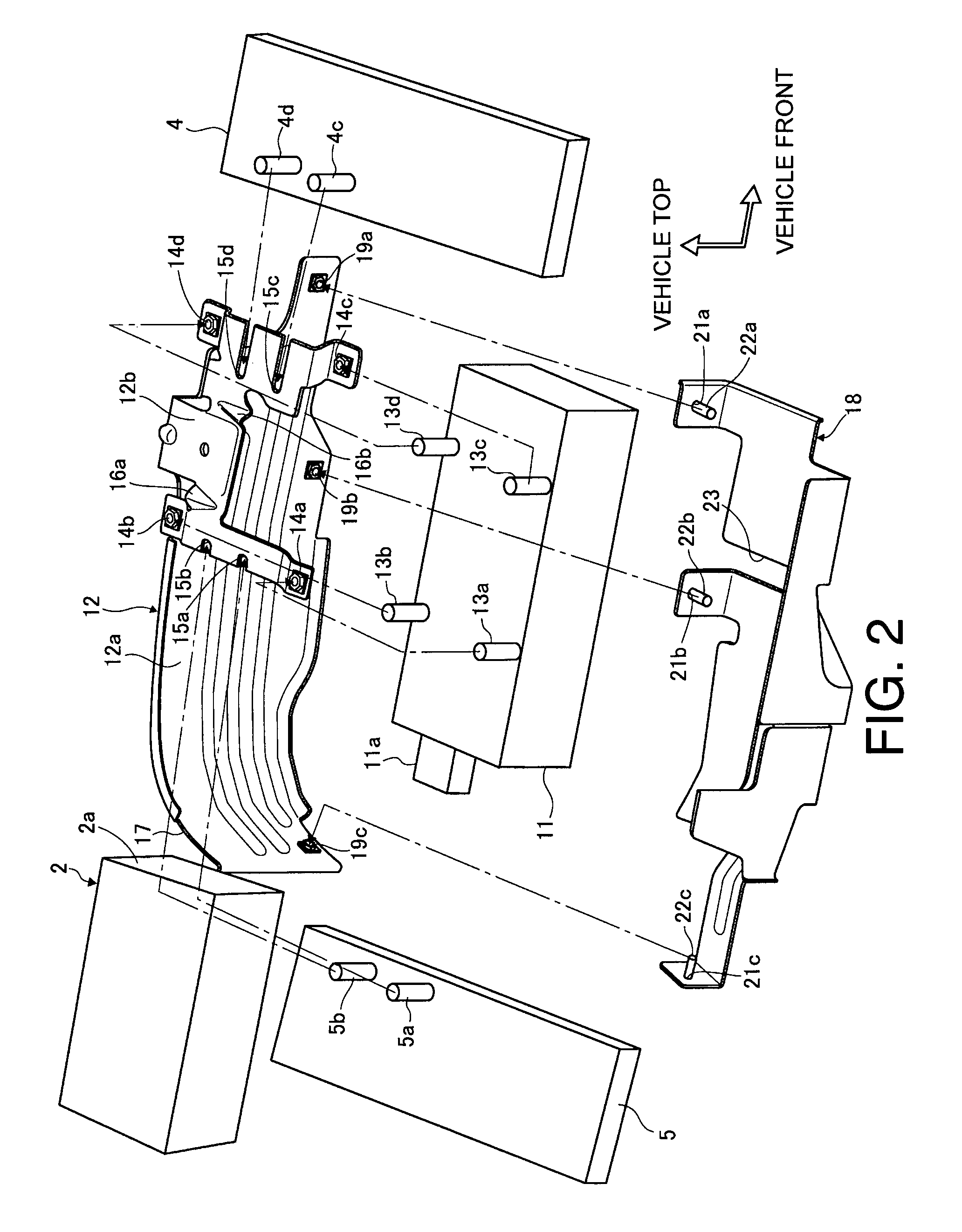
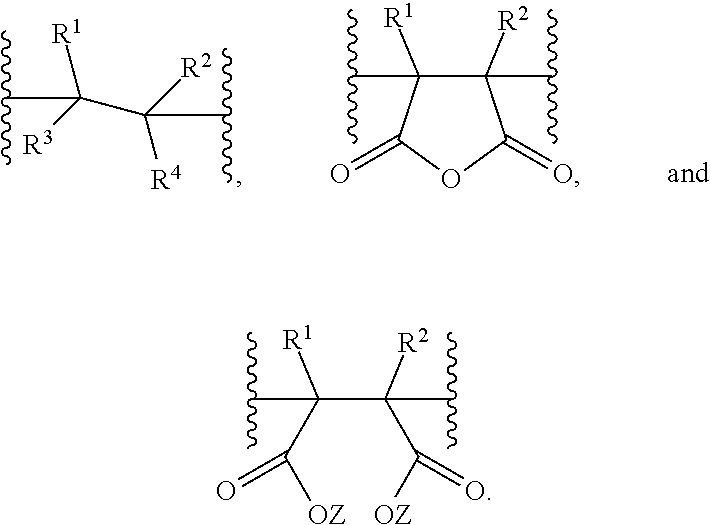
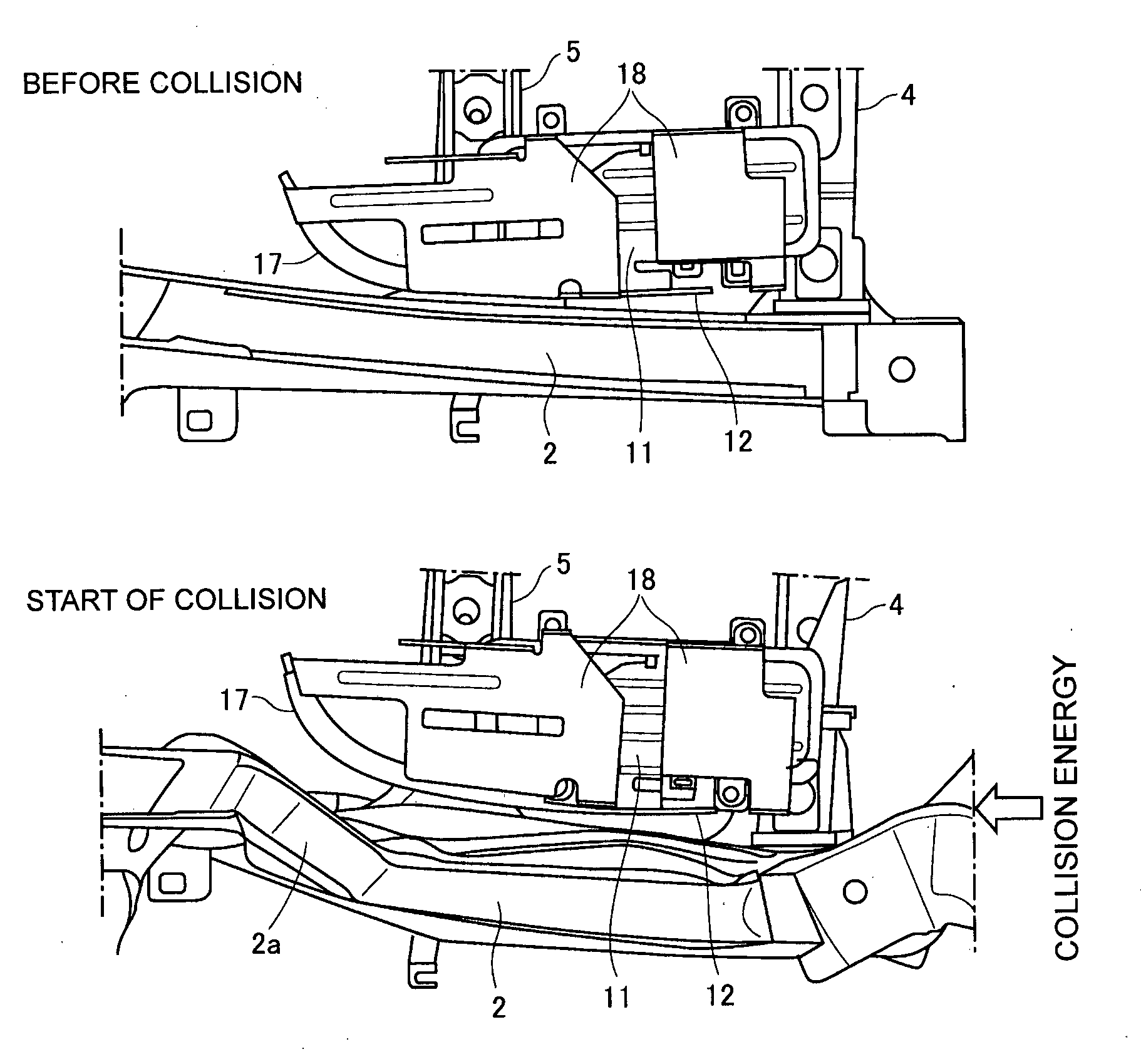
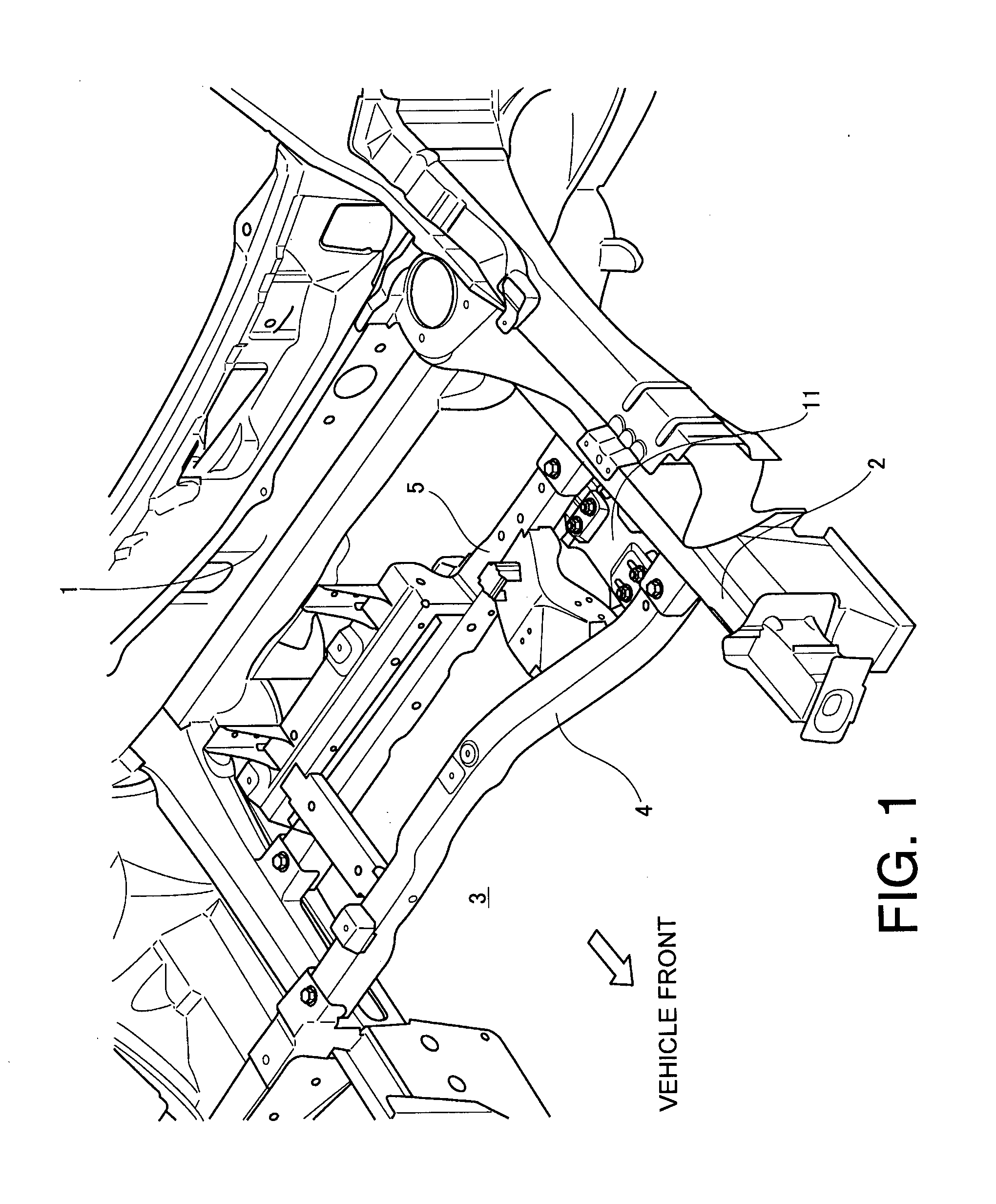
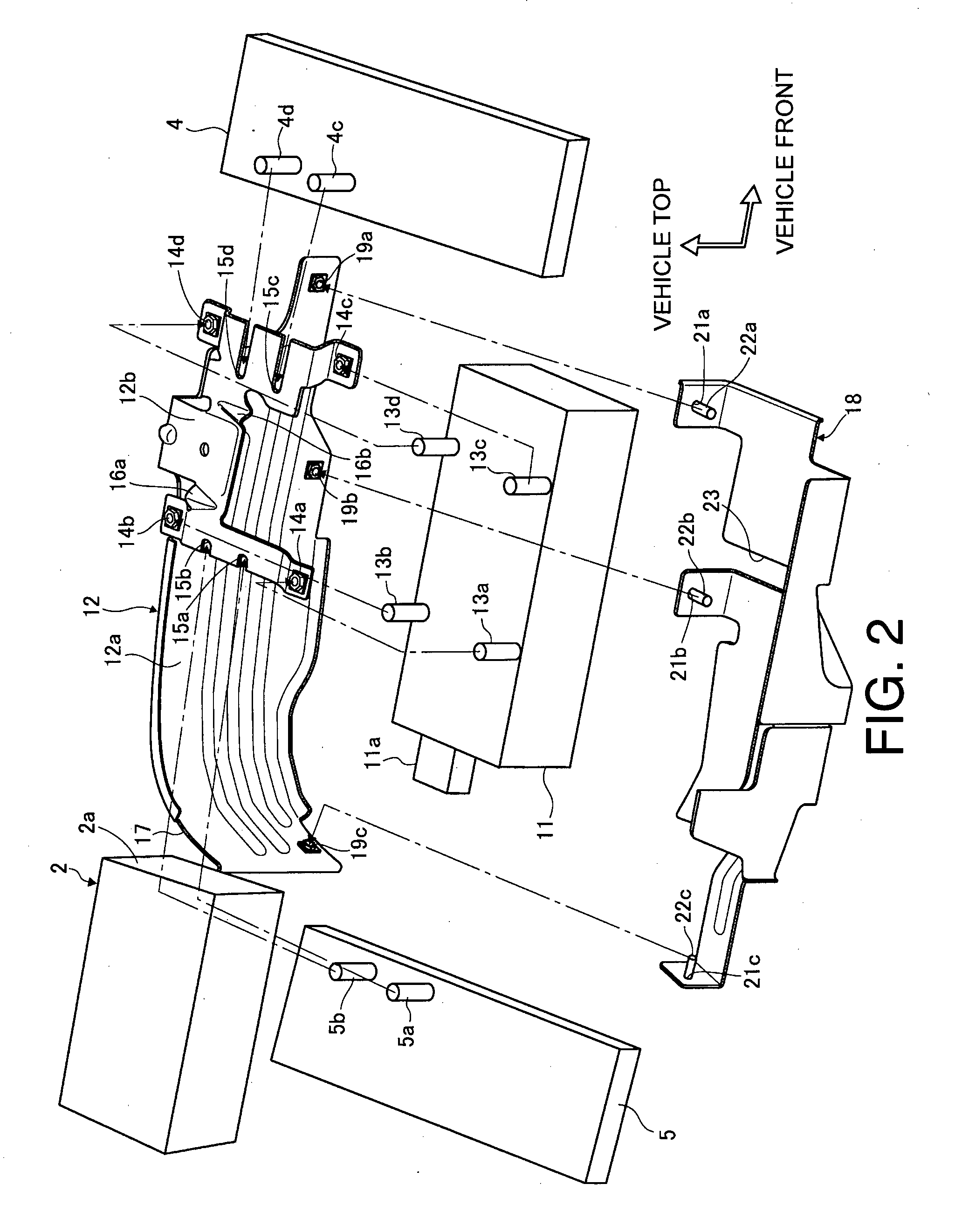
Vehicle collision protection apparatus
InactiveUS8720976B2Less availableImprove performanceVehicle seatsUnderstructuresEngineeringAutomotive engineering
Owner:NISSAN MOTOR CO LTD
Control Channel Transmitting, Receiving Method, Base Station and Terminal
ActiveUS20150078266A1Avoid problemsLess availableError preventionSignal allocationControl channelComputer terminal
A method for transmitting and receiving a control channel, a base station and a terminal relate to a long term evolution advanced system. The method for transmitting a control channel disclosed by the present document includes: a base station side configuring, for a terminal side, detection-limited subframe cluster information of a control channel, so as to notify the terminal side of the manner by which the base station side transmits the control channel. The present document also discloses a method for receiving a control channel, a base station and a terminal.
Owner:ADVANCED STANDARD COMM LLC
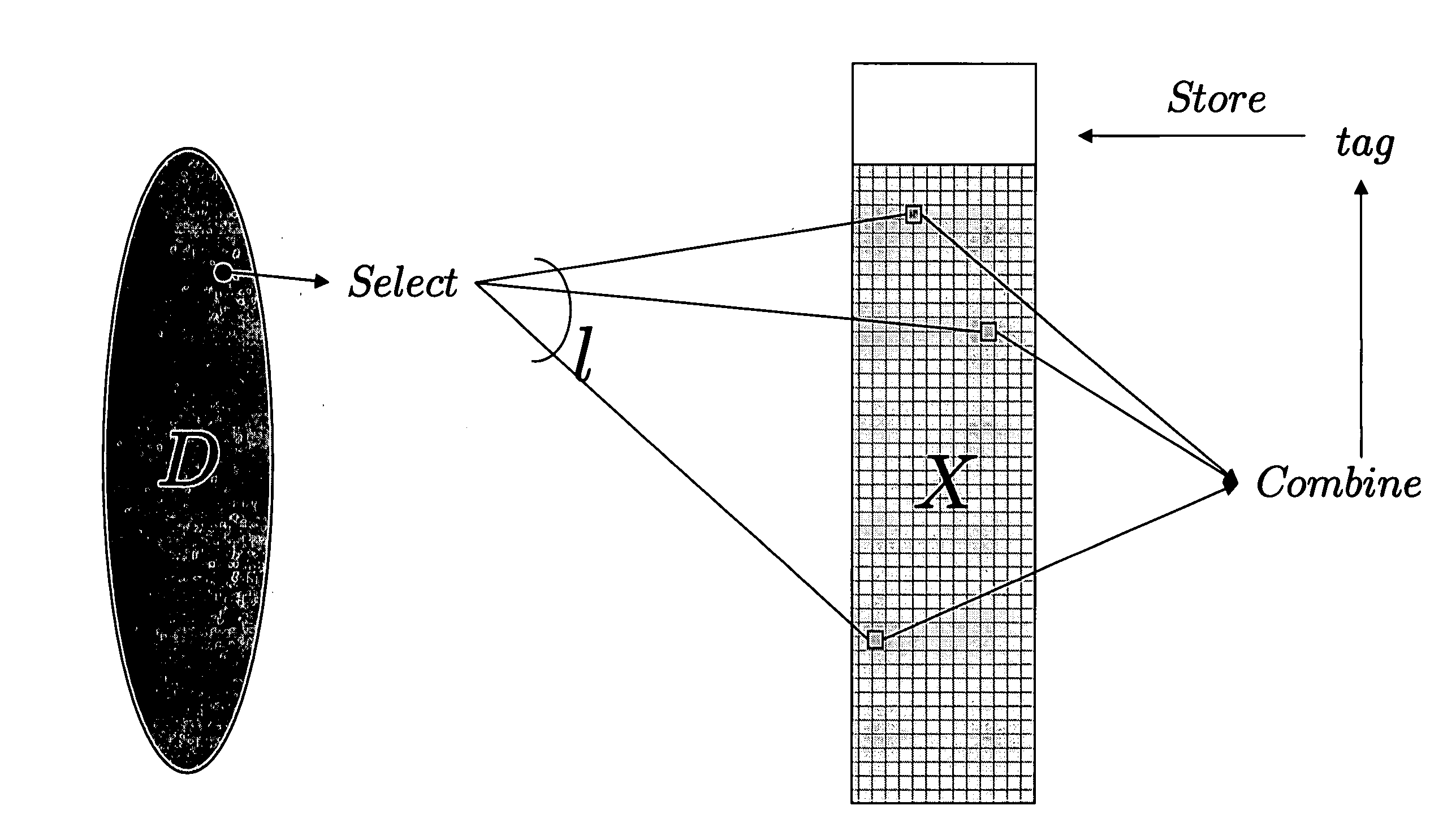
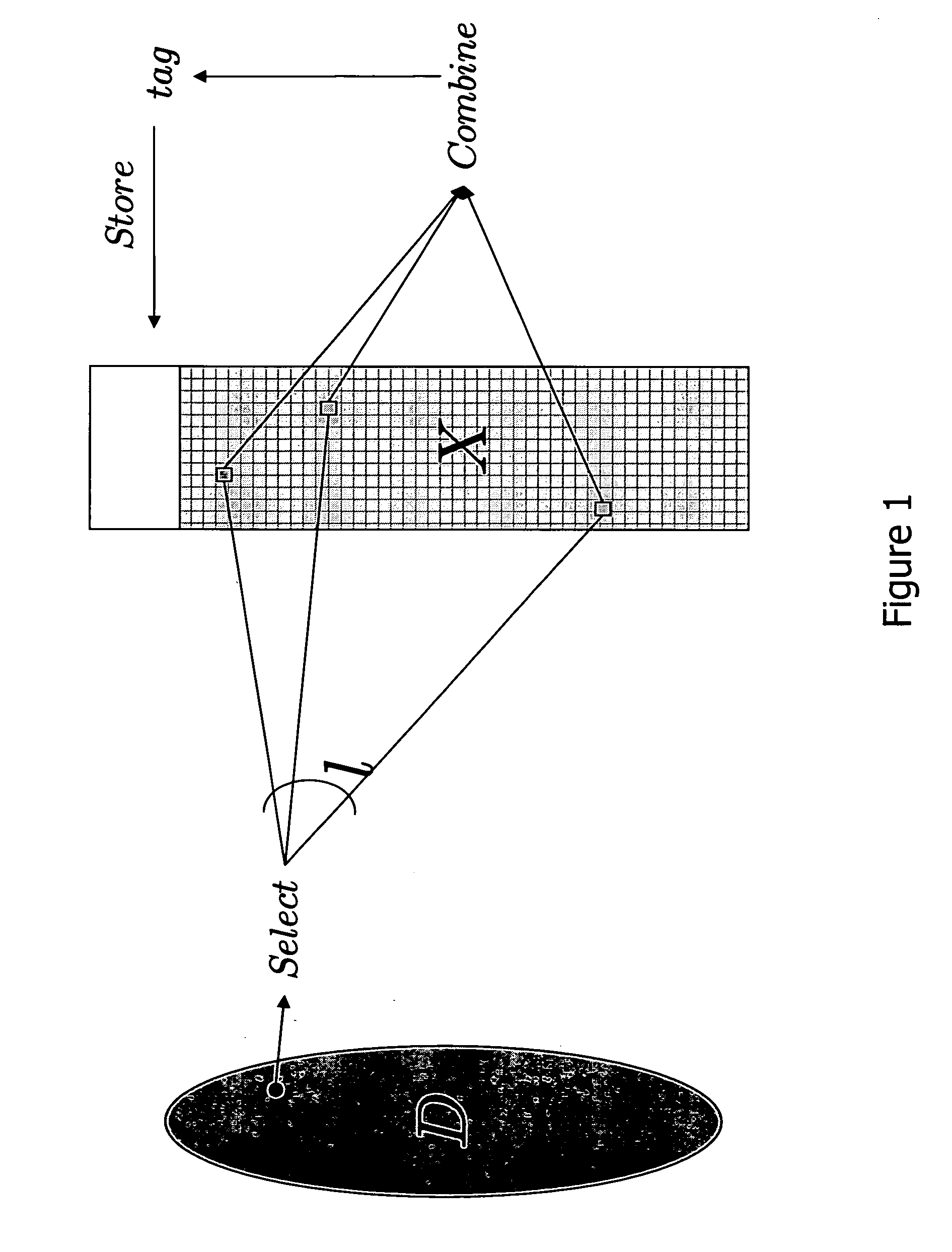
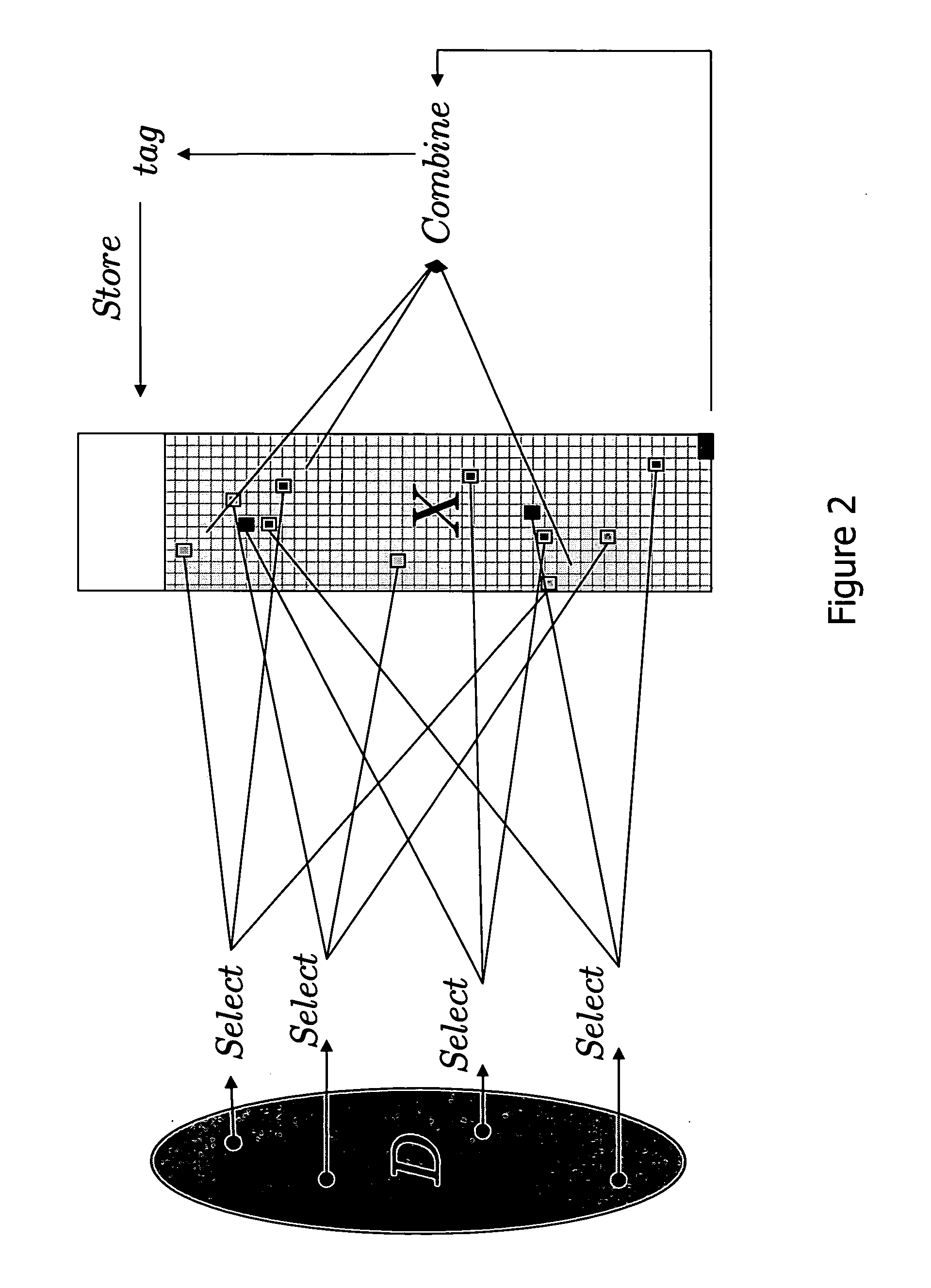
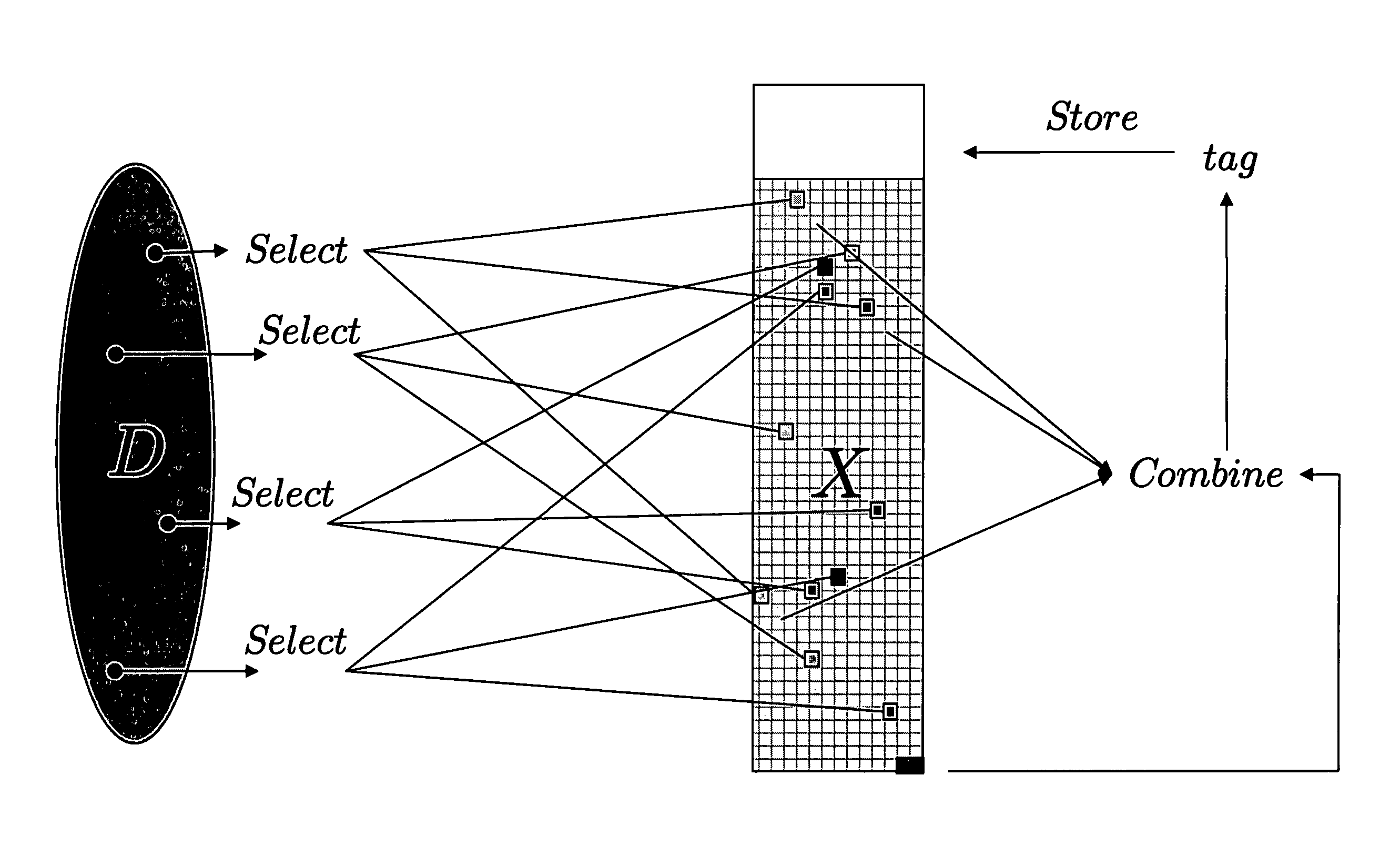
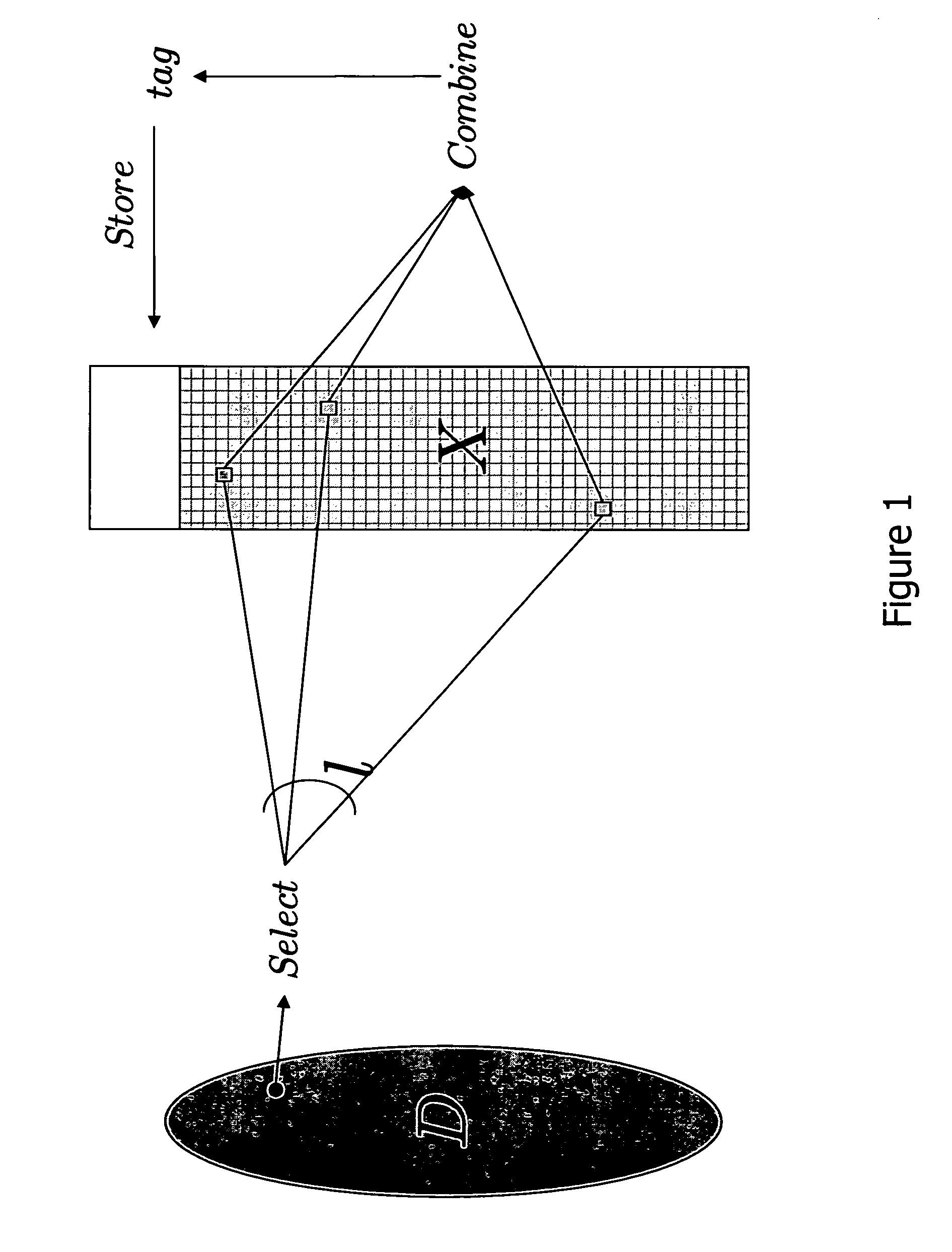
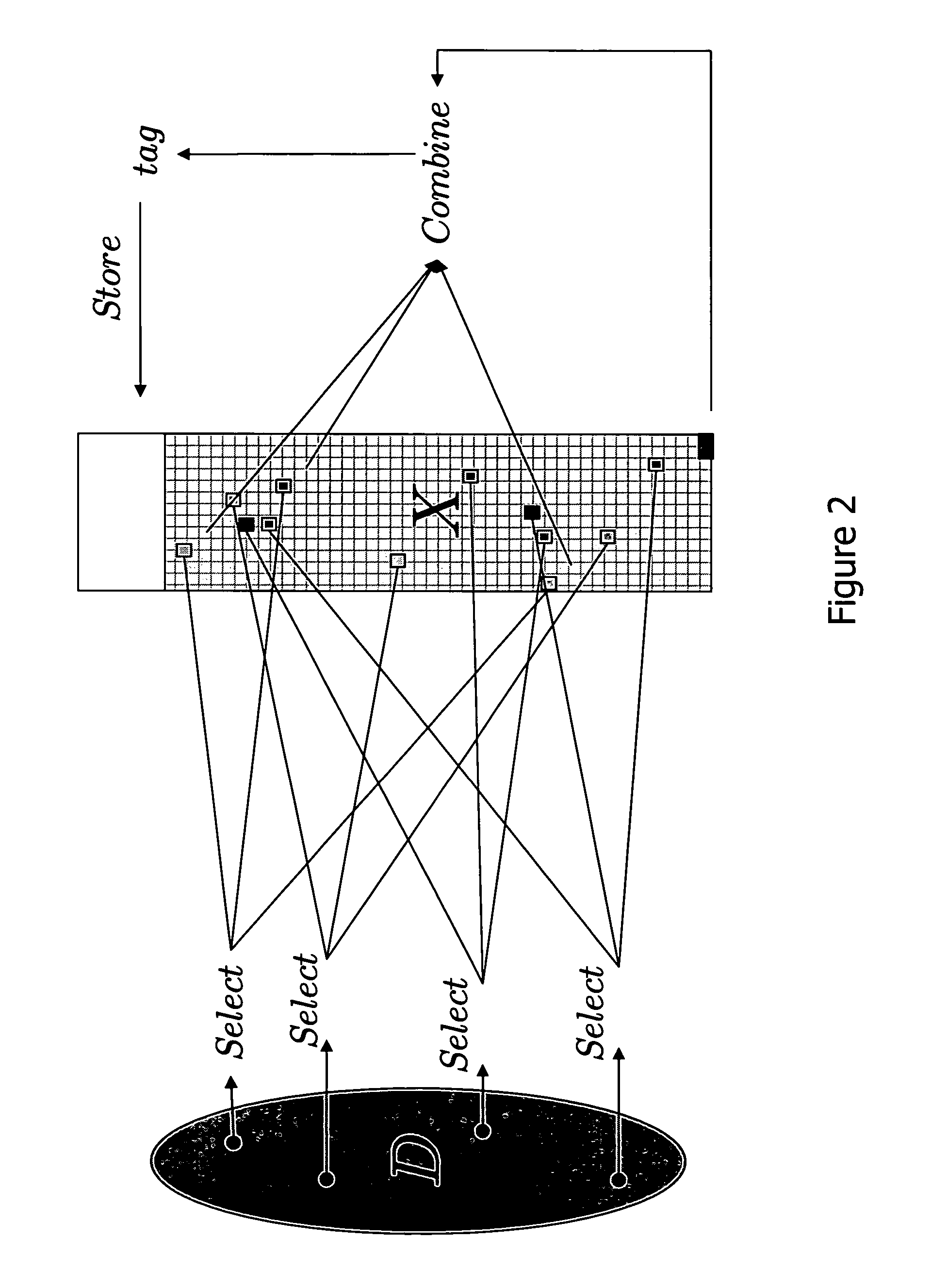
Method and system for password protocols in the bounded retrieval model with security against dictionary attacks and intrusions
ActiveUS20070180260A1Efficiently computableHard to invertDigital data processing detailsUser identity/authority verificationSelf adaptiveDictionary attack
Efficient secure password protocols are constructed that remain secure against offline dictionary attacks even when a large, but bounded, part of the storage of a server responsible for password verification is retrieved by an adversary through a remote or local connection. A registration algorithm and a verification algorithm accomplish the goal of defeating a dictionary attack. A password protocol where a server, on input of a login and a password, carefully selects several locations from the password files, properly combines their content according to some special function, and stores the result of this function as a tag that can be associated with this password and used in a verification phase to verify access by users. Two main instantiations of our method are given; in one, a combination of mathematical tools, called dispersers and pairwise-independent hash functions is used to achieve security against adaptive intrusions (dispersers make sure that the password of each user depends on randomly chosen locations in a large password file, and pairwise-independent hash functions help in making this dependency sufficiently random); in a second one, a combination of mathematical tools, called k-wise independent hash functions and locally-computable and strong extractors (k-wise independent hash functions make sure that the locations chosen in the large password file from each password are sufficiently random, and locally-computable and strong extractors are used to combine the contents of these locations to generate a single long random value, which makes verification harder for the adversary to foil).
Owner:TELCORDIA TECHNOLOGIES INC
Advanced Ultrasound Modulated Optical Spectroscopy And Its Application To Patient Monitoring
InactiveUS20120197133A1Reduce and eliminate effect of light diffusionAccurate measurementDiagnostics using spectroscopySensorsRegion of interestSpectroscopy
The present disclosure describes systems and methods that use spatial modulation to focus light into a localized region of interest such as an individual blood vessel. In certain embodiments, acoustic modulation techniques, such as ultrasound pulse modulation, are used in conjunction with spatial modulation to achieve more precise measurements through otherwise scattering medium. The focused beam of light is capable of penetrating several centimeters of tissue to deliver measurements and images associated with individual blood vessels and other discrete vascular components.
Owner:TYCO HEALTHCARE GRP LP
Mammalian imidazoline receptor
InactiveUS6475752B1Low costAbundant reference toxicologyCell receptors/surface-antigens/surface-determinantsSugar derivativesImidazoline receptorDisease
The invention provide a mammalian nucleic acid molecule and fragments thereof. It also provides for the use of the mammalian nucleic acid molecule for the characterization, diagnosis, evaluation, treatment, or prevention of conditions, diseases and disorders associated with its expression and for the production of a model system. The invention additionally provides expression vectors and host cells for the production of the protein encoded by the mammalian nucleic acid molecule. The invention further provides a mammalian protein or portions thereof. The invention still further provides for the use of the nucleic acid molecule and protein in assays to detect or purify ligands.
Owner:INCYTE PHARMA INC
Titanium article having improved corrosion resistance
InactiveUS6607846B1Low costLong delivery timeVacuum evaporation coatingSputtering coatingTitaniumAlloy
Owner:TITANIUM METALS CORP
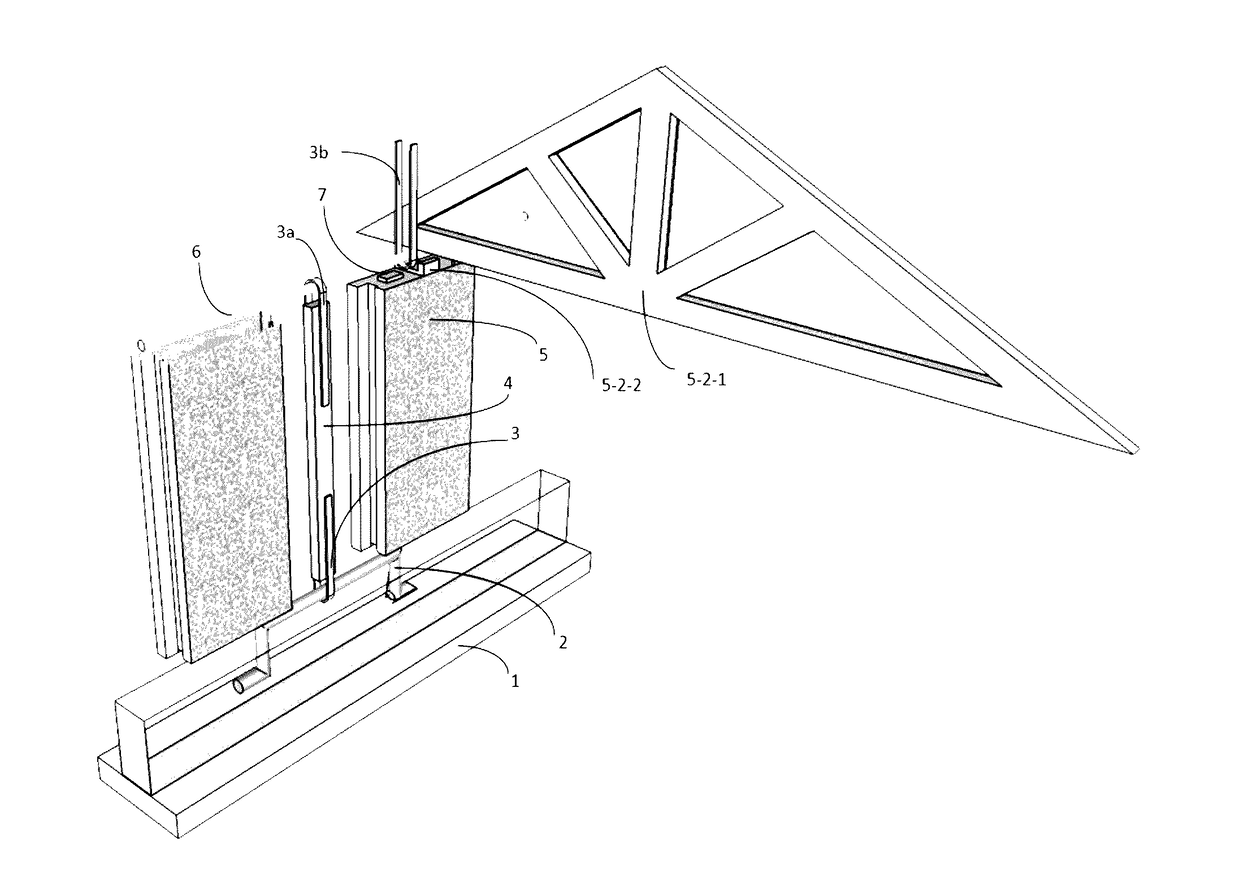
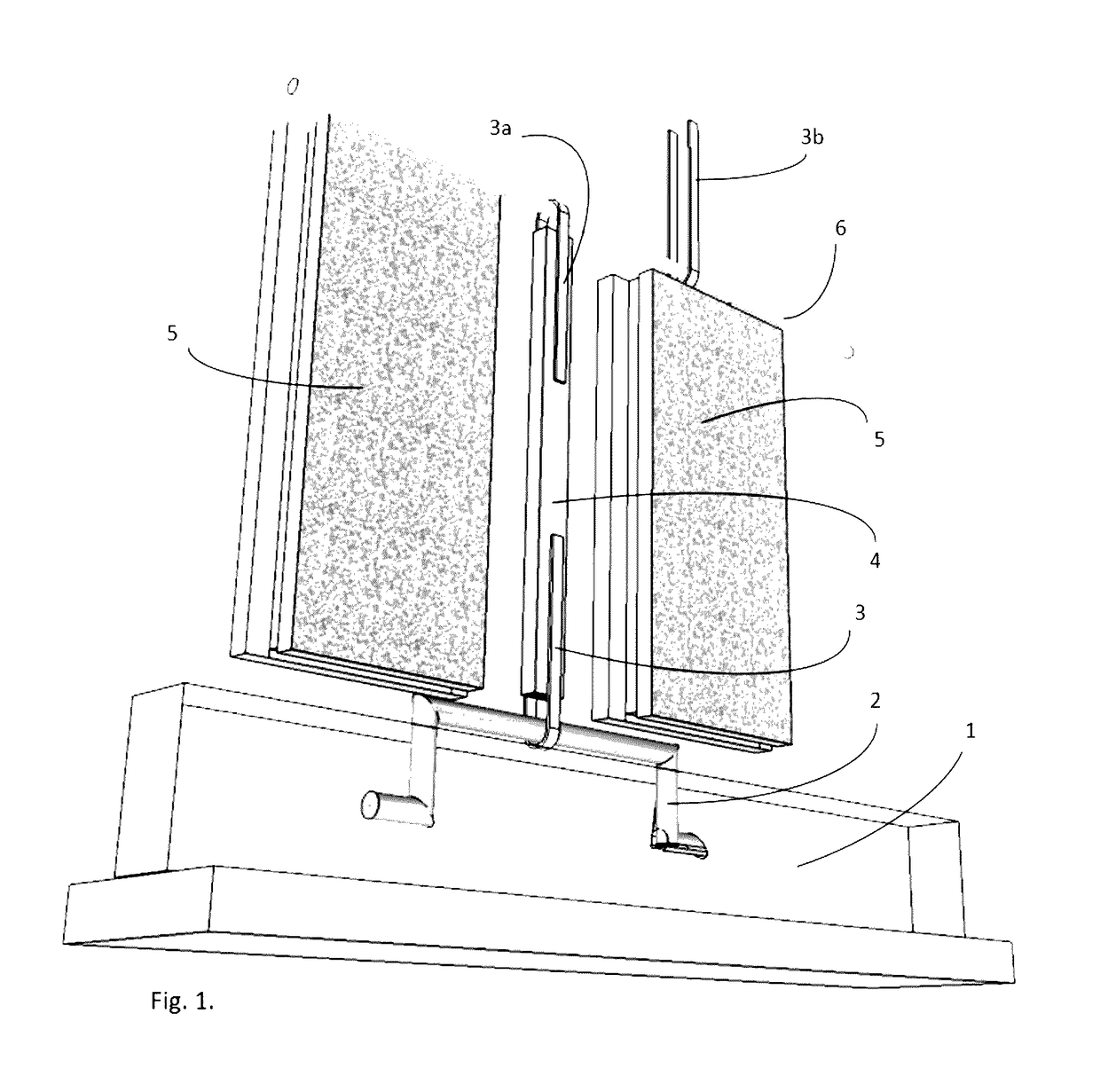
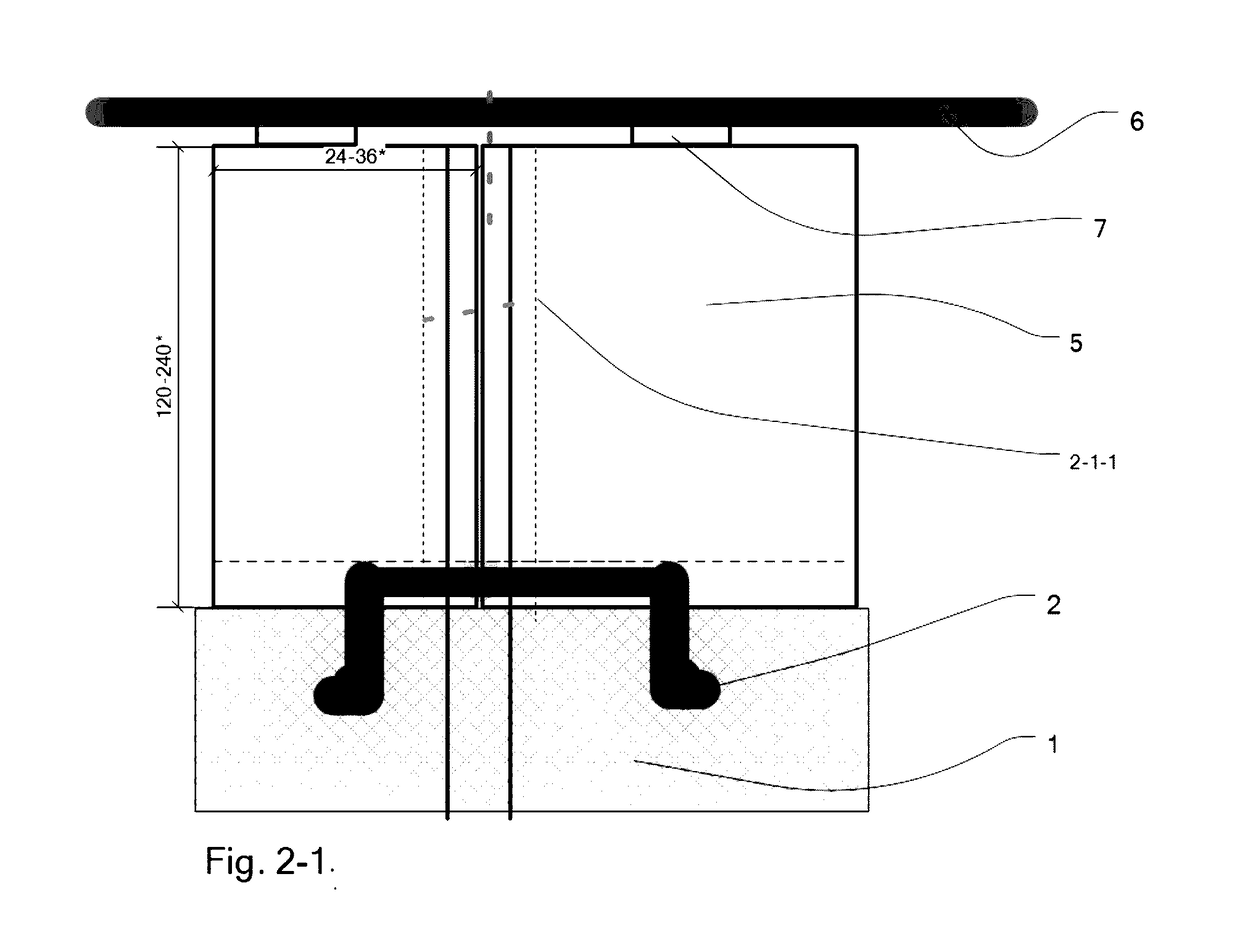
Construction Method to Reinforce Masonry Walls with Wood
InactiveUS20170121958A1Less availableLess on-site coordinationConstruction materialWallsBrickEngineering
This disclosure relates to masonry construction of residential houses using prefabricated masonry panels or blocks, such as Autoclaved Aerated Concrete (AAC) panels or Concrete Masonry Units (CMU). Unlike existing masonry construction methods, this masonry structure is reinforced by common wood studs as join keys. All wood studs are individually strap-tied directly to the foundation and horizontally bound together to form a network of cells enclosing masonry blocks throughout the entire building. Considerations are given to prevent wood studs absorbing moisture from masonry material.
Owner:JIN YOUXUAN
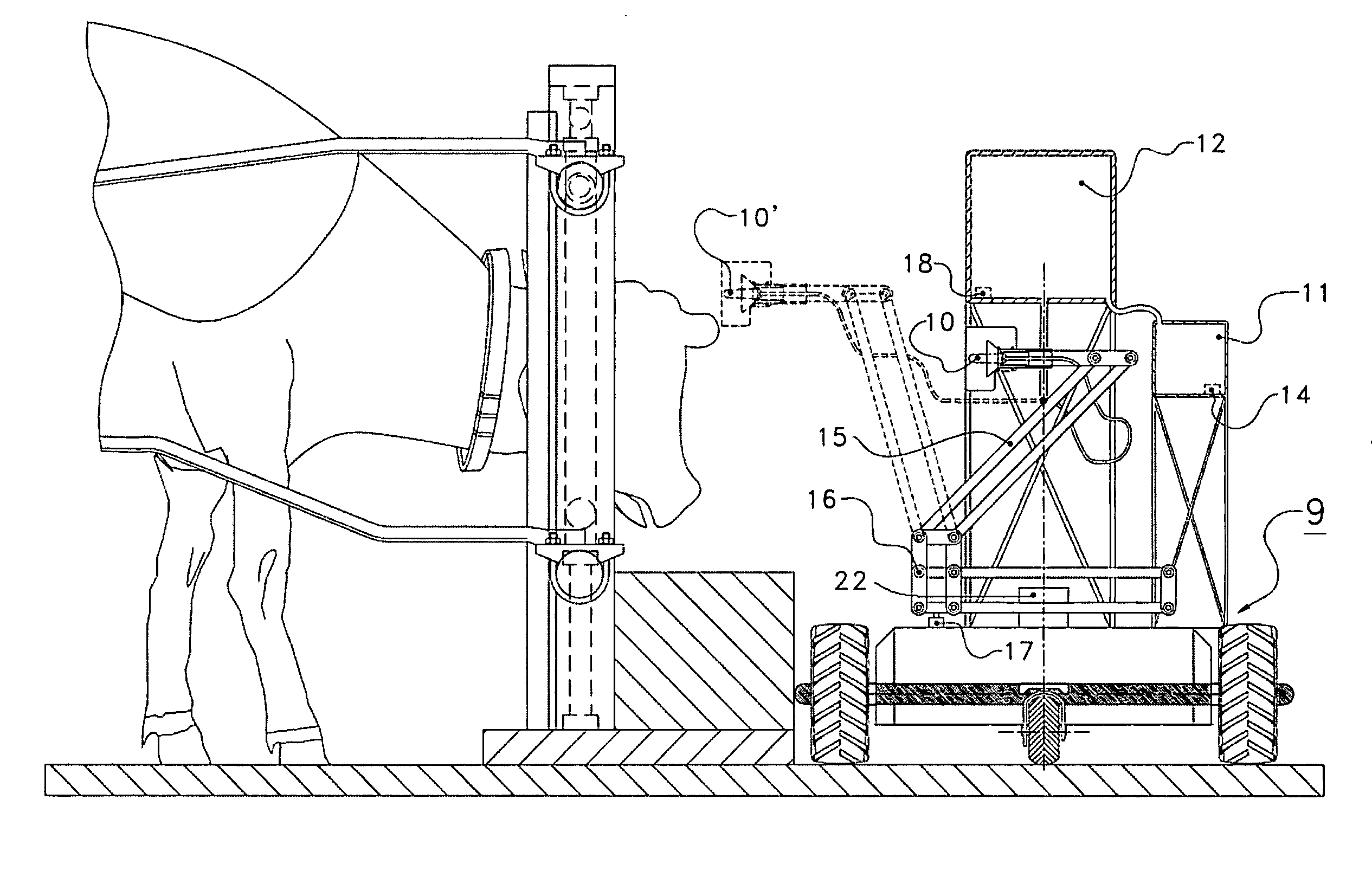
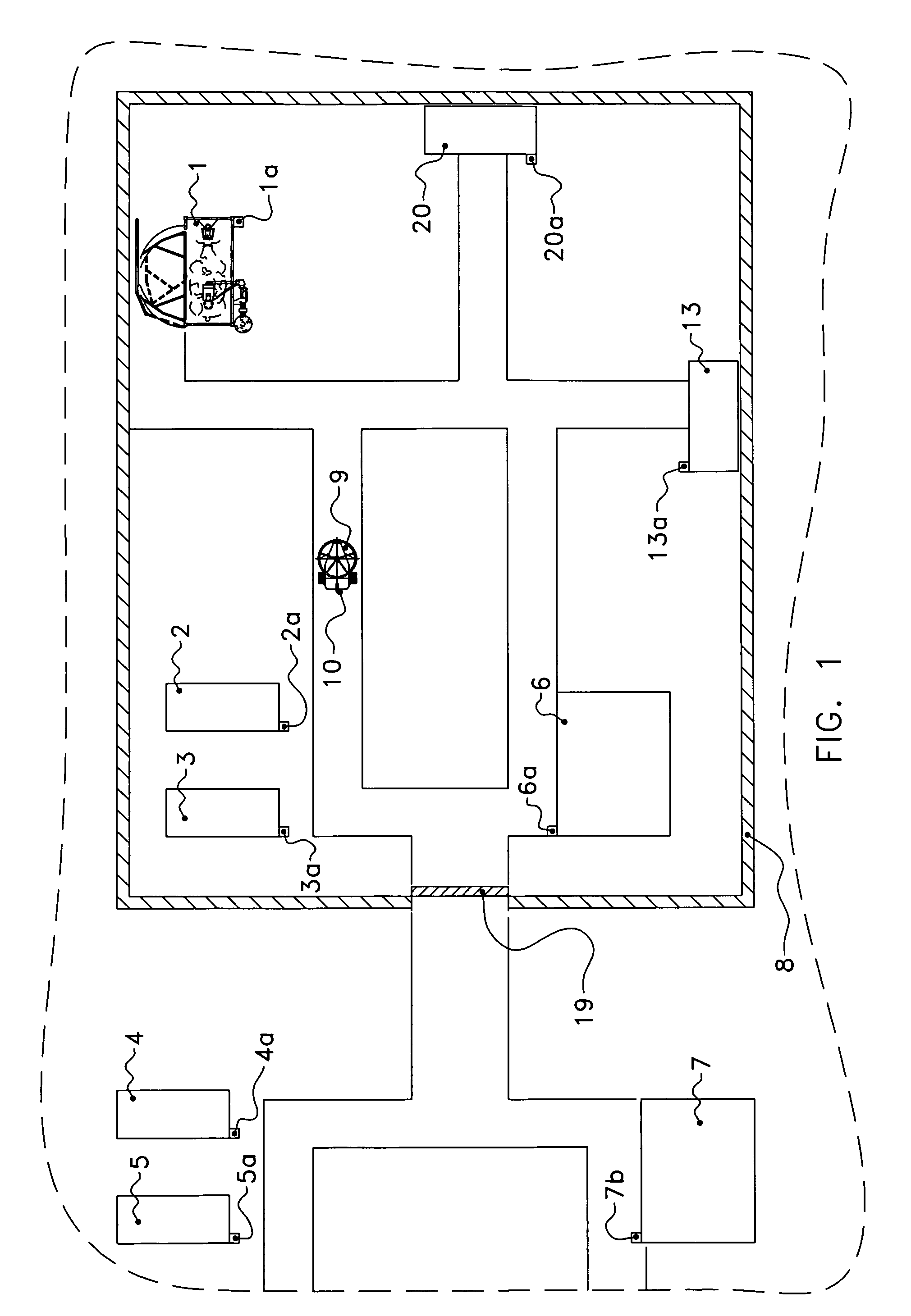
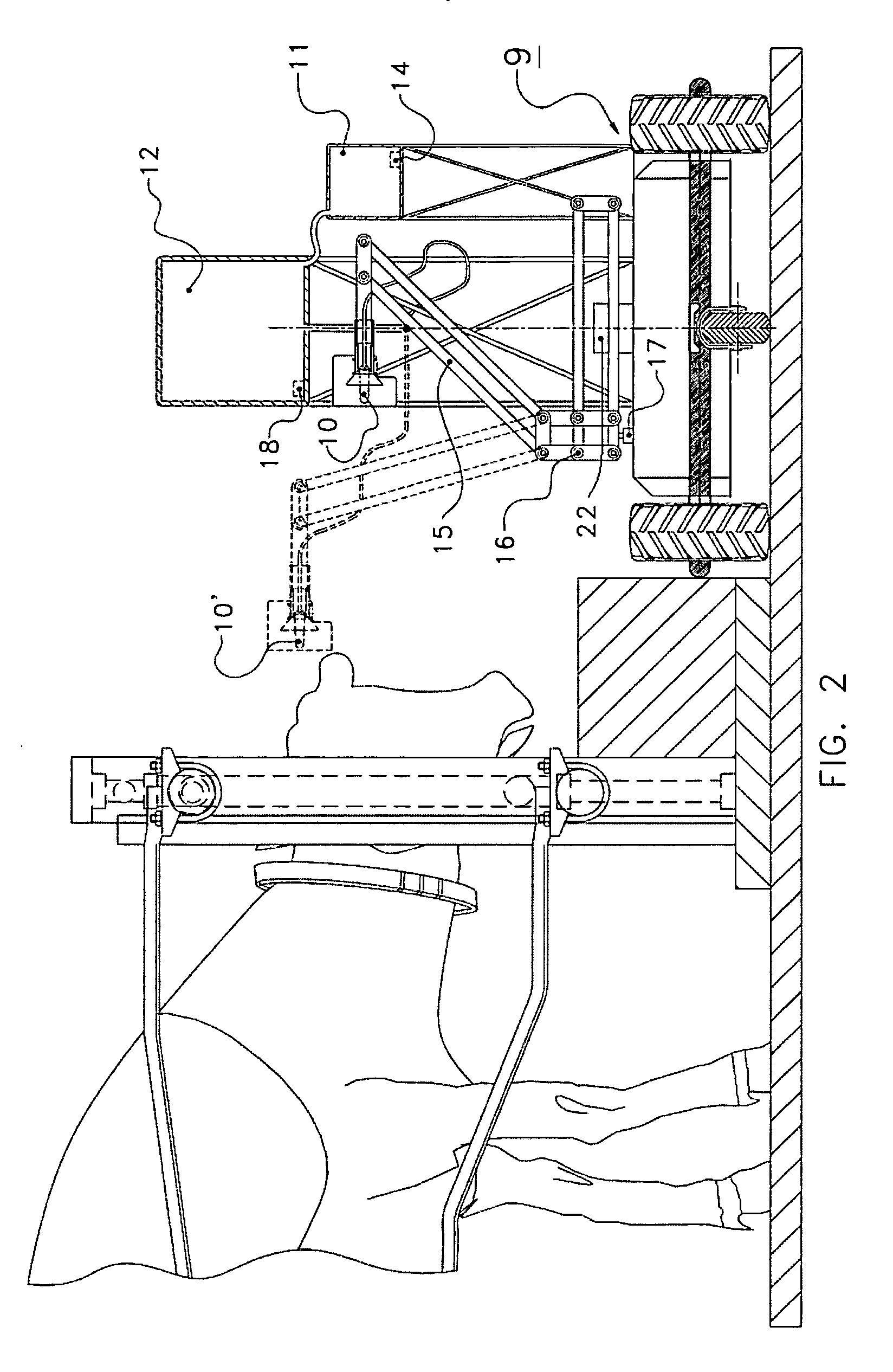
Installation for supplying liquid feed to an animal and an autonomously displaceable vehicle for use in such an installation
InactiveUS20080236509A1Easy constructionFlexible useAnimal watering devicesCathetersEngineeringProcess engineering
An installation for supplying liquid feed to an animal, such as a calf. The installation comprises one or more feed loading places (1) and one or more feed unloading places (2-5), and one or more vehicles (9) that are autonomously displaceable, controlled by a microprocessor or the like, between one or more feed loading places and one or more feed unloading places, each vehicle comprising a drinking nozzle (10), such as a flexible teat.
Owner:MAASLAND
Aquaporin-8 variant
The invention provides a mammalian cDNA which encodes a mammalian AQP8V. It also provides for the use of the cDNA, fragments, complements, and variants thereof and of the encoded protein, portions thereof and antibodies thereto for diagnosis and treatment of pancreatic disorders, particularly type I diabetes. The invention additionally provides expression vectors and host cells for the production of the protein and a transgenic model system.
Owner:INCYTE
Fabricated titanium article having improved corrosion resistance
InactiveUS20040058190A1Low costLong delivery timeVacuum evaporation coatingSputtering coatingAlloyTitanium
Owner:TITANIUM METALS CORP
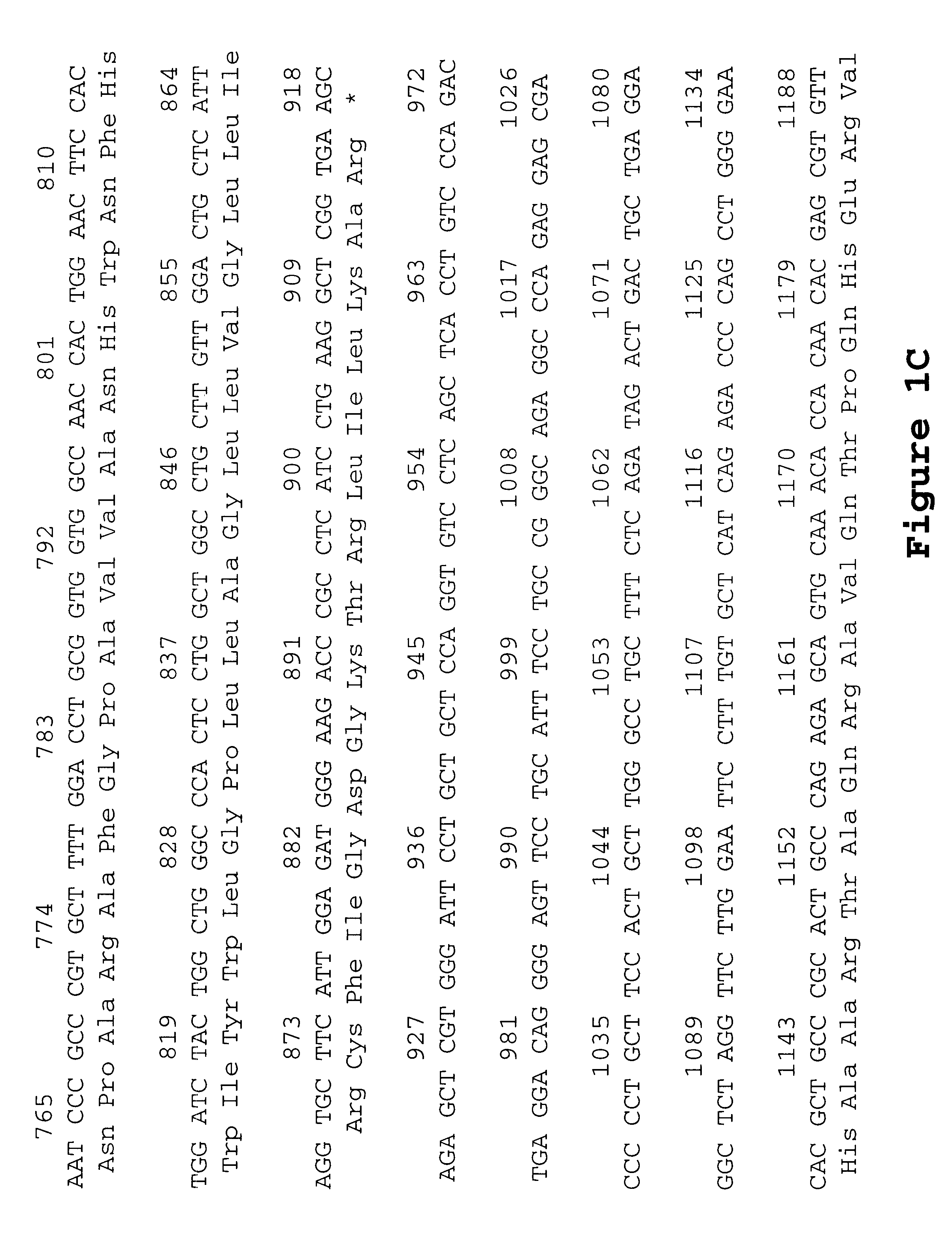
Method of dishwashing
InactiveUS20160222323A1Low efficacyReduce amountOrganic detergent compounding agentsOrganic/inorganic per-compounds compounding agentsParticulatesPhosphate
A method of automatic dishwashing comprising the step of delivering into a dishwasher a cleaning product comprising a particulate loose-powder composition comprising an organic complexing agent, bleach, manganese bleach catalyst and free of phosphate and wherein the manganese bleach catalyst is in the form of a delayed release particle.
Owner:THE PROCTER & GAMBLE COMPANY
Apparel item configured for reduced cling perception
ActiveUS10271580B2Reduce perceptionSmall surface areaGarment special featuresWeft knittingSkin surfacePattern perception
An apparel item configured to reduce the perception of cling is provided herein. The apparel item comprises a first set of outwardly-projecting nodes on a first portion of the apparel item, a second set of outwardly-projecting nodes on a second portion of the apparel item, and a third set of inwardly-projecting nodes on a third portion of the apparel item, where the third set of nodes is positioned between the first set of nodes and the second set of nodes. The first and second sets of outwardly-projecting nodes comprise apertures that provide a communication passage from an outer surface of the apparel item to an inner surface of the apparel item. Besides reducing the surface area of the apparel item that comes into contact with a wearer's skin surface, the nodes also facilitate cooling the wearer and speed up drying times of the apparel item when being worn.
Owner:NIKE INC
Structured lipid compositions and methods of formulation thereof
ActiveUS8206772B2Less availableTotal calories lowFermentationFood preparationTriglycerideWeight management
Lipid compositions comprising specific mixtures of edible synthetic triglycerides are provided that are useful in formulating food products having highly desirable dietary benefits. The novel lipid compositions allow simultaneous access to highly desirable dietary benefits such as delivery of calorie reduction, weight management, health benefits, or any combination thereof, and they also may be formulated trans-fatty acid free.
Owner:INTERCONTINENTAL GREAT BRANDS LLC
Control channel transmitting, receiving method, base station and terminal
A method for transmitting and receiving a control channel, a base station and a terminal relate to a long term evolution advanced system. The method for transmitting a control channel disclosed by the present document includes: a base station side configuring, for a terminal side, detection-limited subframe cluster information of a control channel, so as to notify the terminal side of the manner by which the base station side transmits the control channel. The present document also discloses a method for receiving a control channel, a base station and a terminal.
Owner:ADVANCED STANDARD COMM LLC
High-energy and protein-enriched nutritional composition
InactiveUS20180228196A1Low viscositySufficient fluidityFood scienceEnvironmental healthAdditive ingredient
This application relates to a high-protein and high-calorie, ready-to-use, heat-sterilized, oral enteral nutritional composition.
Owner:EVEN SANTE IND
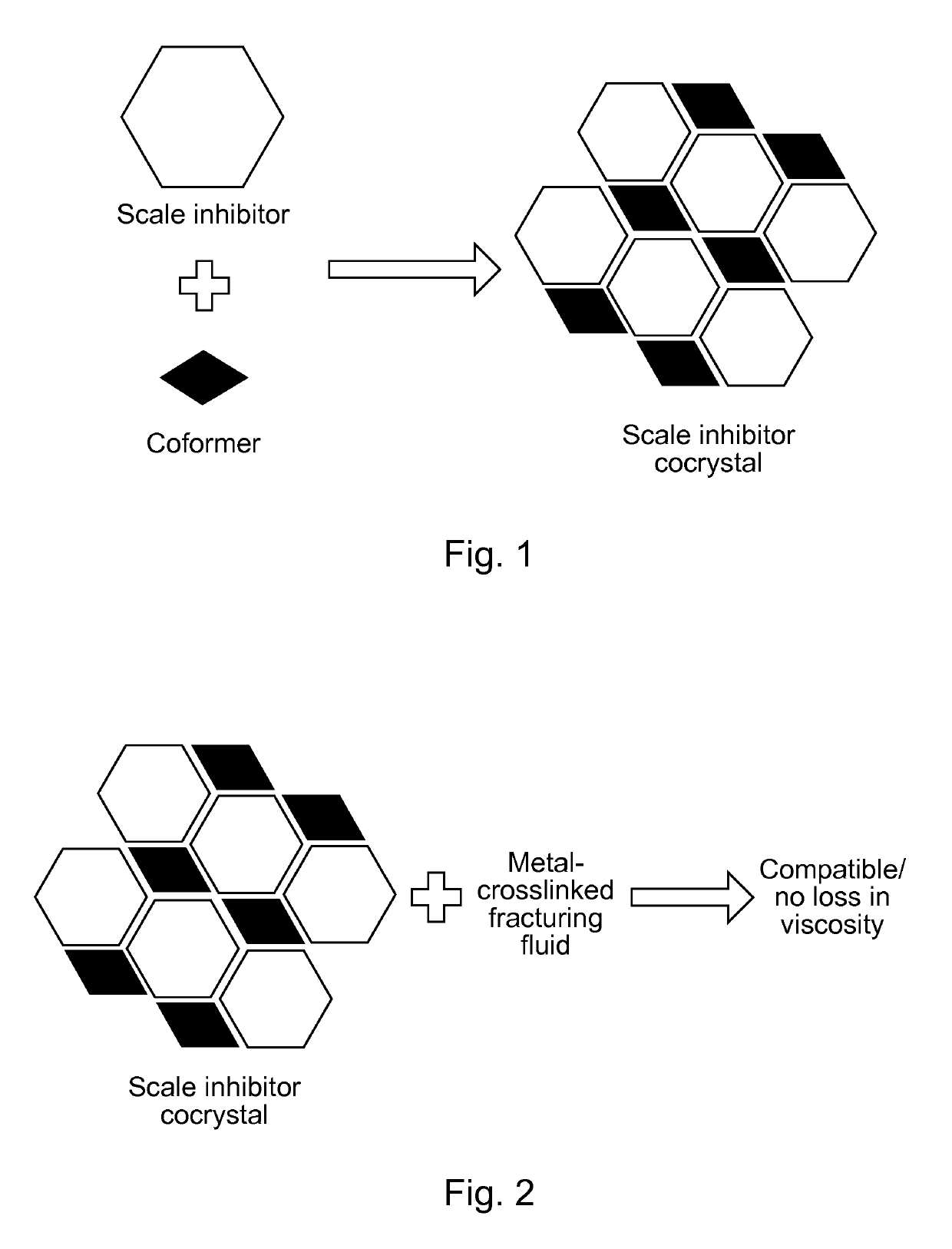
Scale-inhibiting cocrystals for treatment of a subterranean formation
InactiveUS10253244B2Improve the environmentImprove effectivenessSolid waste managementCleaning apparatusCrystalCocrystal
The present invention relates to cocrystals including a scale-inhibiting compound, and methods of using the cocrystals for treating a subterranean formation. In various embodiments, the present invention provides a method of treating a subterranean formation including obtaining or providing a composition including cocrystals. Each cocrystal independently includes a scale-inhibiting compound and a secondary material. The method also includes placing the composition in a subterranean formation.
Owner:HALLIBURTON ENERGY SERVICES INC
Vehicle collision protection apparatus
InactiveUS20130033048A1Less availableImprove performanceUnderstructuresVehicle heating/cooling devicesAutomotive engineeringEngineering
Owner:NISSAN MOTOR CO LTD
Method and system for password protocols in the bounded retrieval mode with security dictionary attacks and intrusions
ActiveUS8528060B2Efficiently computableDifficult to invertDigital data processing detailsUser identity/authority verificationHash functionRandom choice
Efficient secure password protocols are constructed that remain secure against offline dictionary attacks even when a large, but bounded, part of the storage of a server responsible for password verification is retrieved by an adversary through a remote or local connection. A registration algorithm and a verification algorithm accomplish the goal of defeating a dictionary attack. A password protocol where a server, on input of a login and a password, carefully selects several locations from the password files, properly combines their content according to some special function, and stores the result of this function as a tag that can be associated with this password and used in a verification phase to verify access by users. Two main instantiations of our method are given; in one, a combination of mathematical tools, called dispersers and pairwise-independent hash functions is used to achieve security against adaptive intrusions (dispersers make sure that the password of each user depends on randomly chosen locations in a large password file, and pairwise-independent hash functions help in making this dependency sufficiently random); in a second one, a combination of mathematical tools, called k-wise independent hash functions and locally-computable and strong extractors (k-wise independent hash functions make sure that the locations chosen in the large password file from each password are sufficiently random, and locally-computable and strong extractors are used to combine the contents of these locations to generate a single long random value, which makes verification harder for the adversary to foil).
Owner:TELCORDIA TECHNOLOGIES INC
Xin-related proteins
InactiveUS20040110937A1Enhanced interactionHigh frequencySugar derivativesMicrobiological testing/measurementAntibodySkeletal muscle disorder
The invention provides mammalian cDNAs which encode Xin-related proteins. It also provides for the use of the cDNAs, fragments, and complements thereof and of the encoded proteins, portions thereof and antibodies thereto for diagnosis and treatment of cardiac and skeletal muscle disorders, particularly hypertrophic cardiomyopathy, and for monitoring cardiac and skeletal muscle morphogenesis and development. The invention additionally provides expression vectors and host cells for the production of the proteins.
Owner:INCYTE
Growth-related inflammatory and immune response protein
InactiveUS20030166300A1Facilitate interactionIncreased frequencyFungiBacteriaImmunoreactive proteinAntibody
The invention provides a mammalian cDNA which encodes a mammalian GRIIP. It also provides for the use of the cDNA, fragments, complements, and variants thereof and of the encoded protein, portions thereof and antibodies thereto for diagnosis and treatment of disorders associated with inflammation and immune response, particularly cancers of the immune system. The invention additionally provides expression vectors and host cells for the production of the protein and a transgenic model system.
Owner:INCYTE
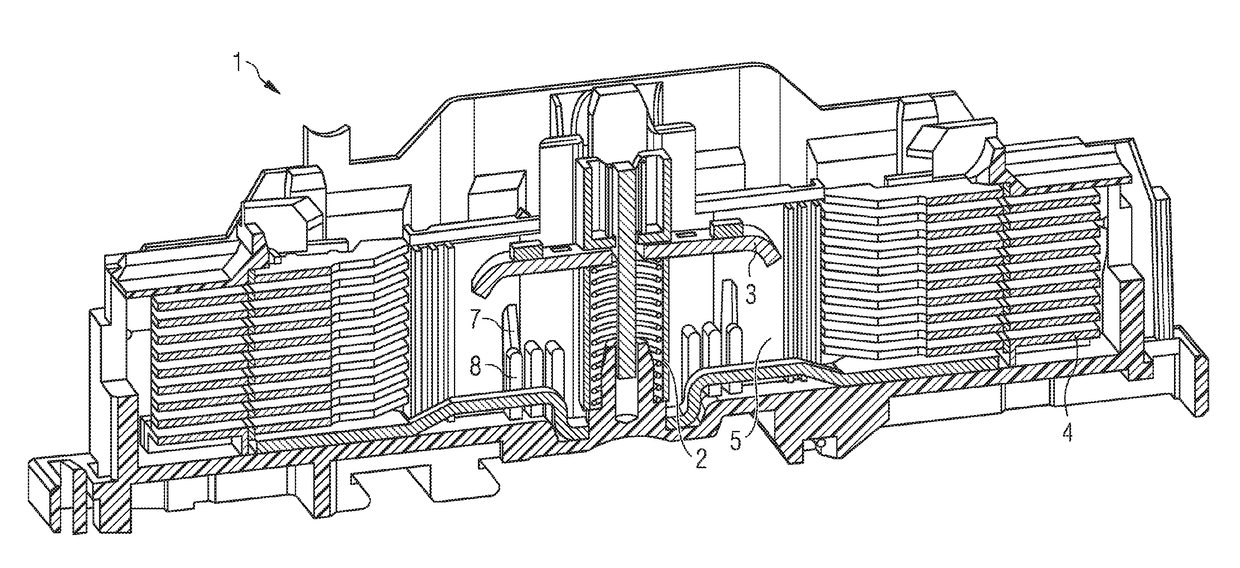
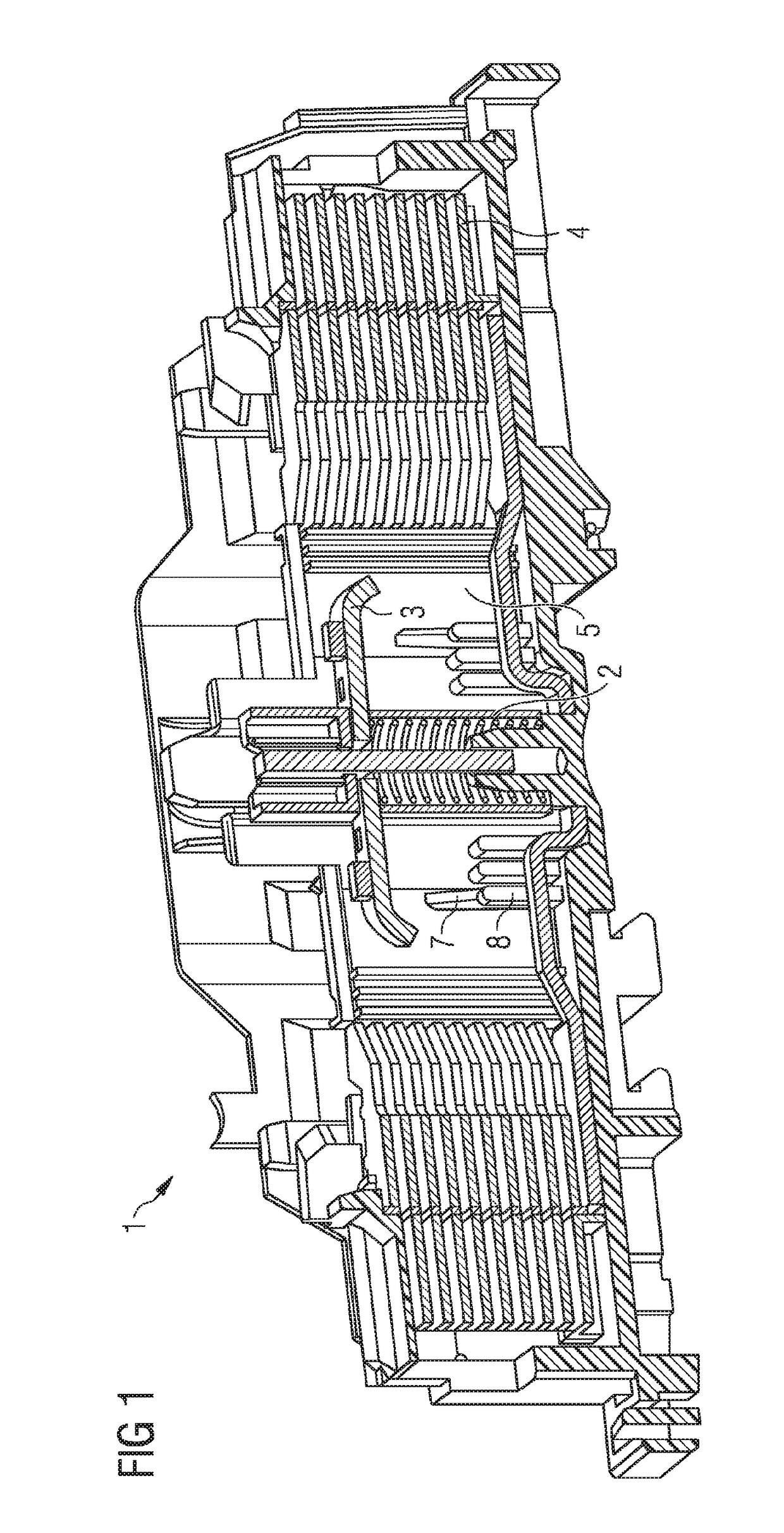
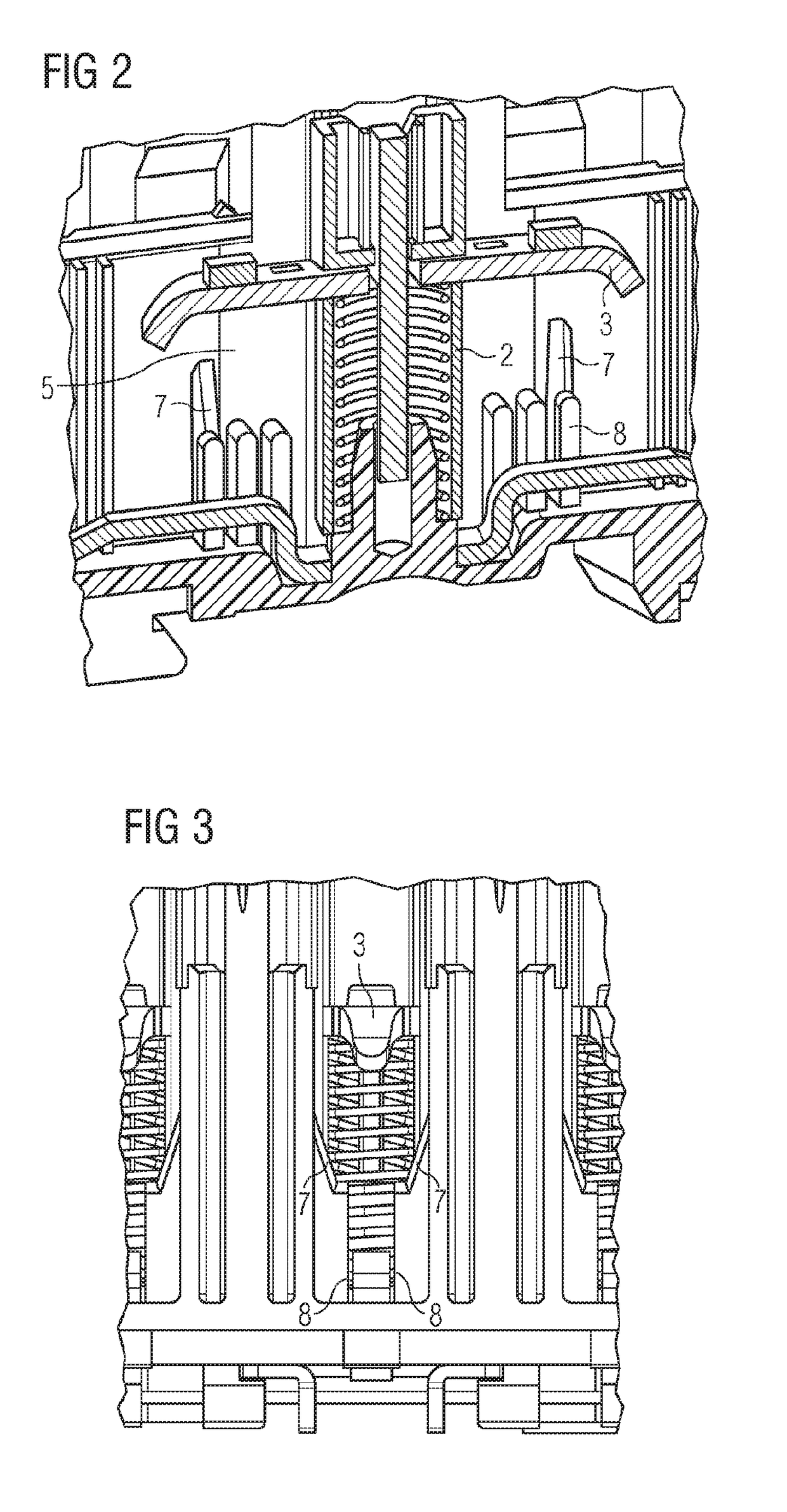
Switching device with improved tripping action in the event of a short circuit
ActiveUS9659726B2Increase switching capacityAvoid structureProtective switch detailsHigh-tension/heavy-dress switchesEngineeringContact element
A switching device having an arc quenching chamber, a fixed contact element and a movable contact element movable in a sliding contact between untripped and tripped positions within the chamber. A plurality of centering structures are arranged on the walls of the arc quenching chamber for centered guiding movement of the movable contact element as it moves from its untripped position to its tripped position. The centering structures may be fabricated unitarily with the chamber walls, as of plastic, and are arranged in parallel and spaced apart relation to one another.
Owner:SIEMENS AG