Patents
Literature
10883 results about "Data treatment" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
Statistical treatment of data also involves describing the data. The best way to do this is through the measures of central tendencies like mean, median and mode. These help the researcher explain in short how the data are concentrated.
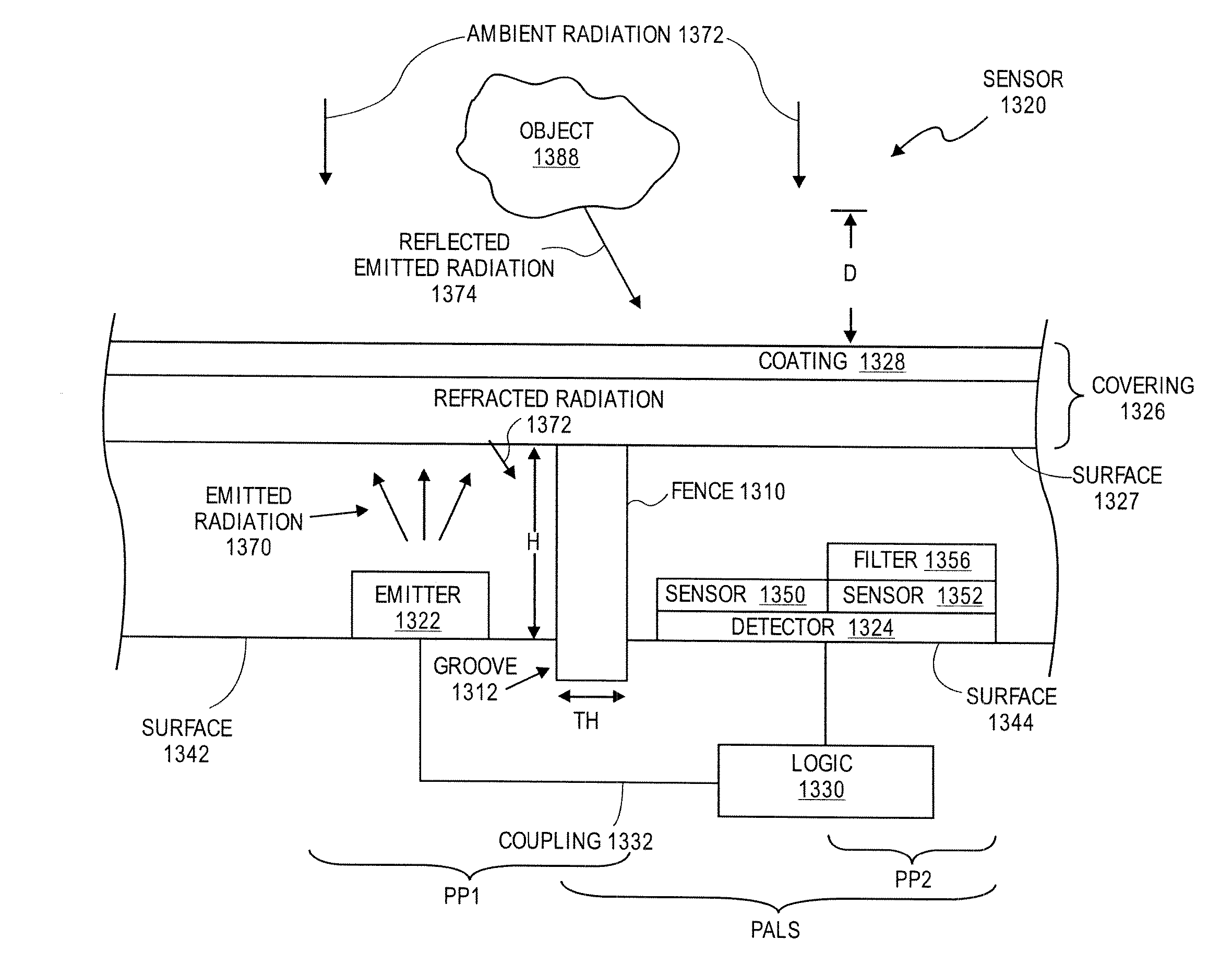
Integrated proximity sensor and light sensor
Apparatuses and methods to sense proximity and to detect light. In one embodiment, an apparatus includes an emitter of electromagnetic radiation and a detector of electromagnetic radiation; the detector has a sensor to detect electromagnetic radiation from the emitter when sensing proximity, and to detect electromagnetic radiation from a source other than the emitter when sensing visible light. The emitter may be disabled at least temporarily to allow the detector to detect electromagnetic radiation from a source other than the emitter, such as ambient light. In one implementation, the ambient light is measured by measuring infrared wavelengths. Also, a fence having a non-IR transmissive material disposed between the emitter and the detector to remove electromagnetic radiation emitted by the emitter. Other apparatuses and methods and data processing systems and machine readable media are also described.
Owner:APPLE INC
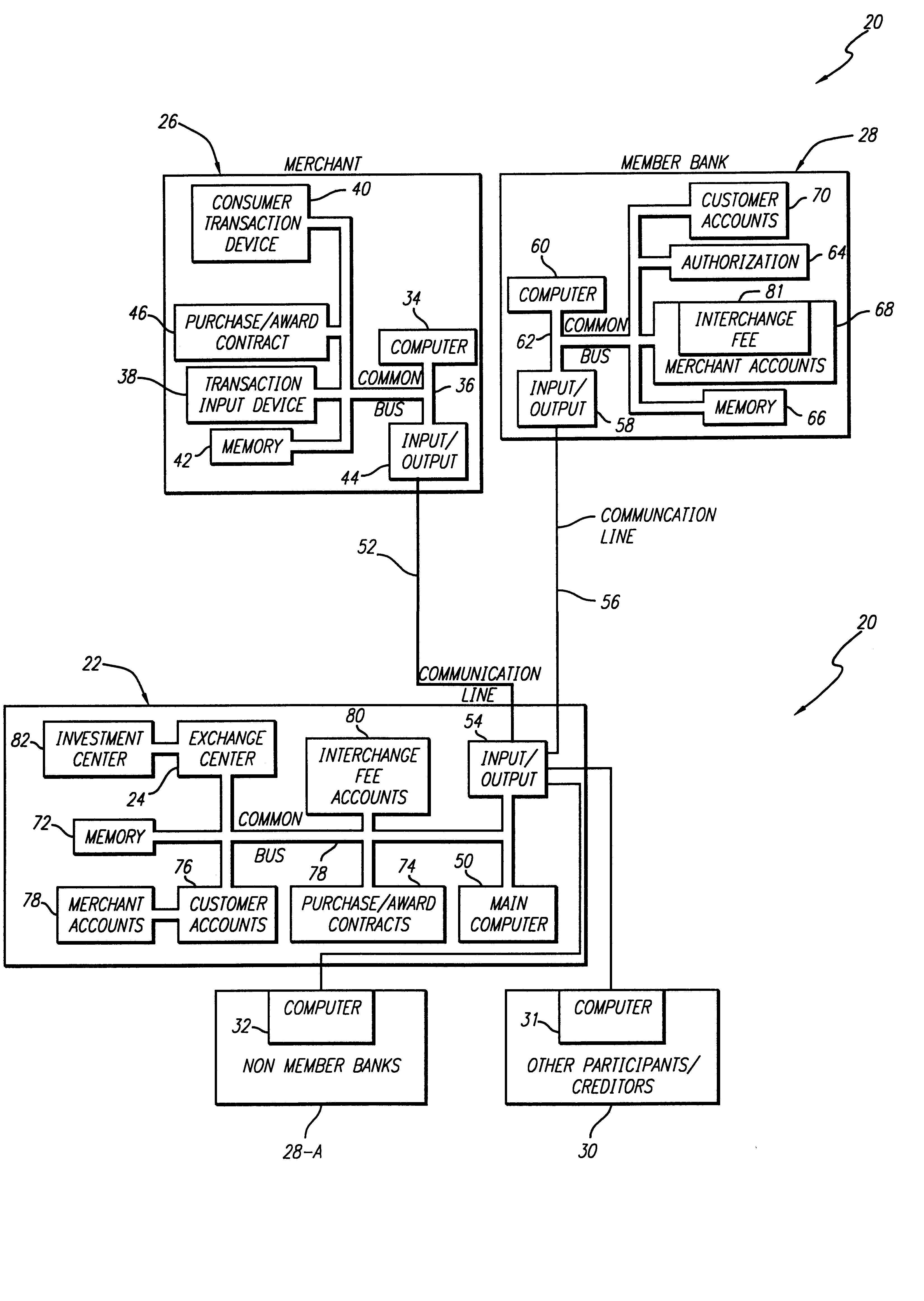
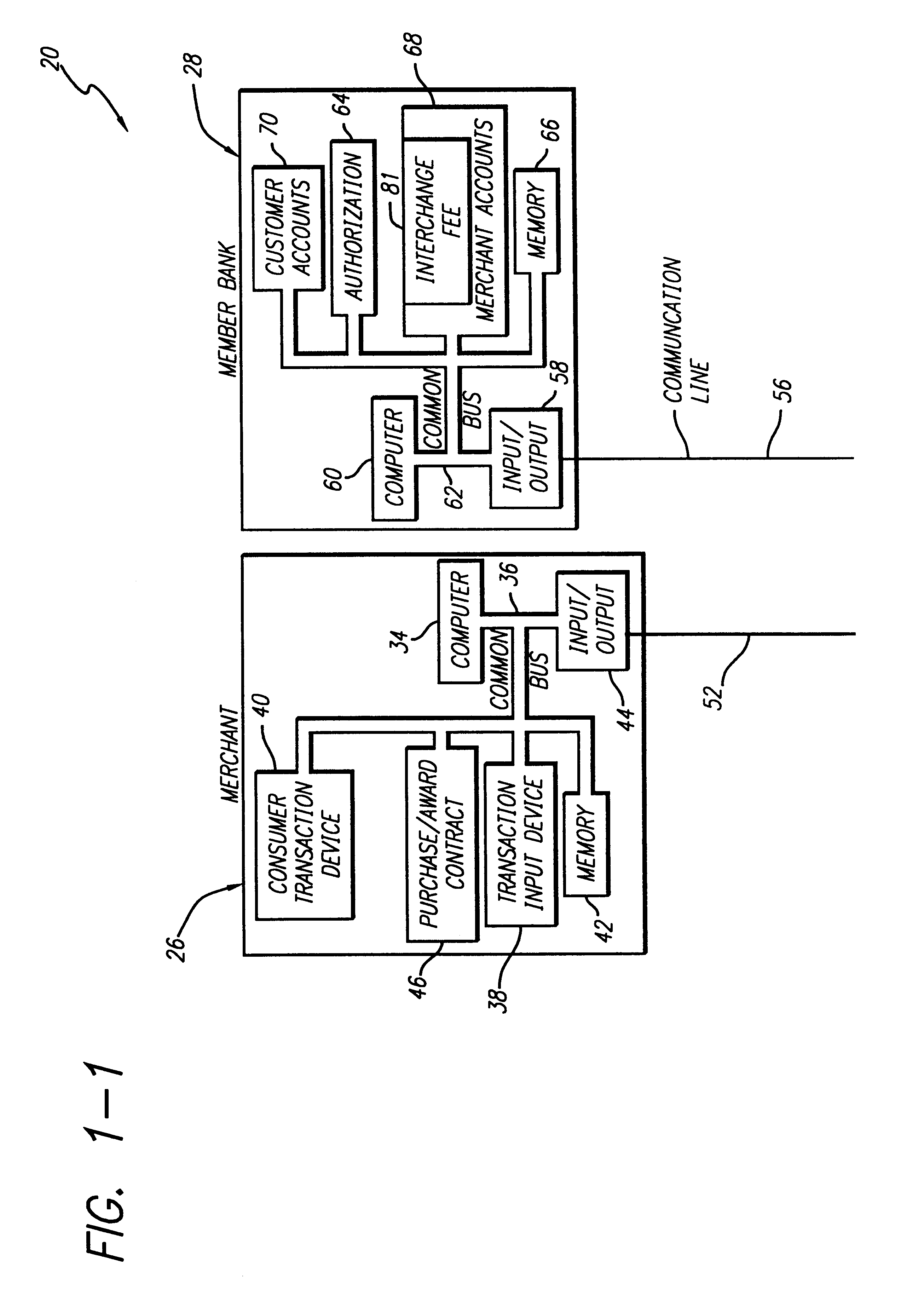
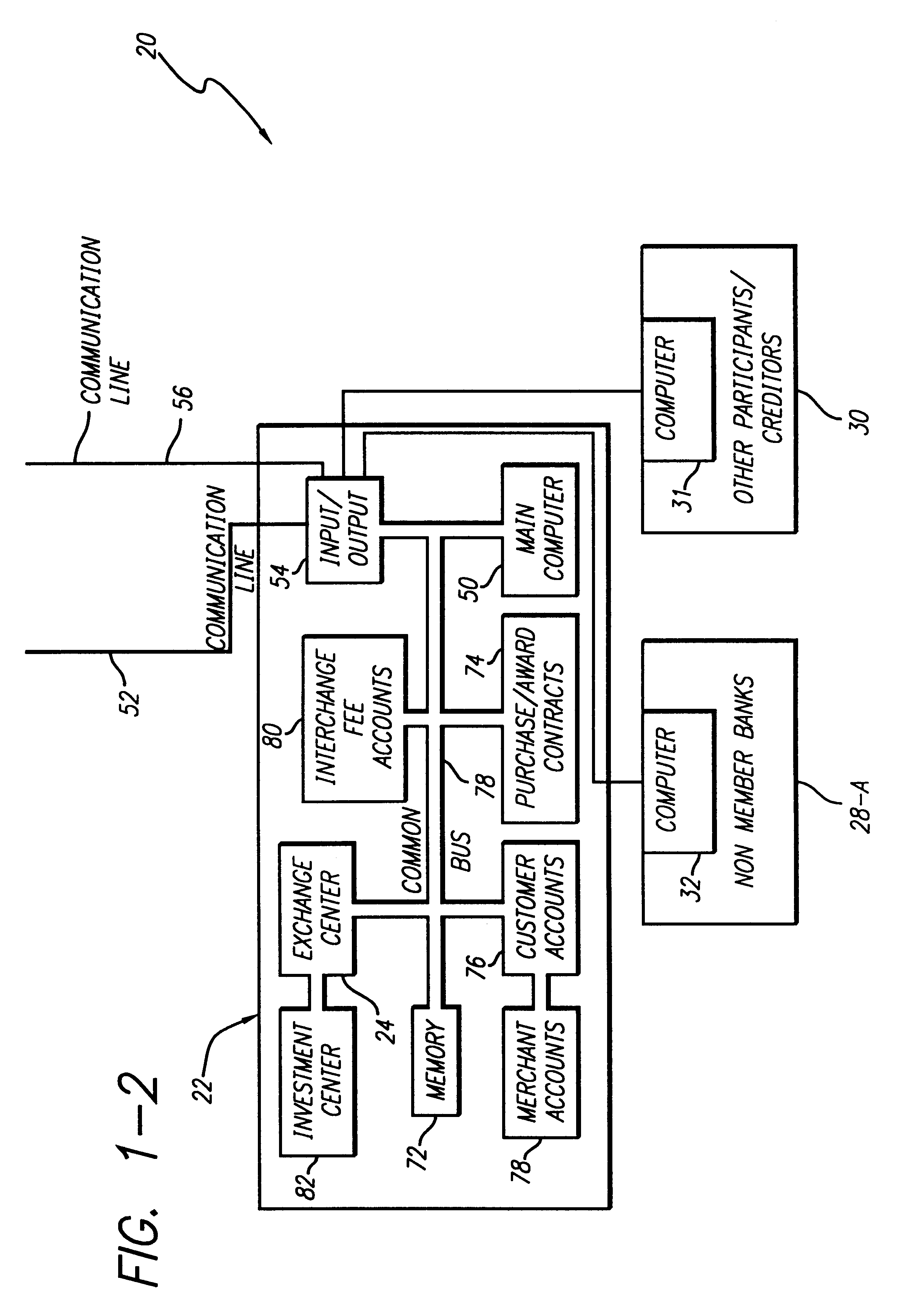
Internet-based credit interchange system of converting purchase credit awards through credit exchange system for purchase of investment vehicle
An Internet-based purchase credit award interchange center is described which interfaces with a credit award exchange center for conversion of any form of merchant or purchase credit award resulting from customer purchase of goods or services to investment in a mutual fund and / or investment vehicle utilizing computer data processing methods. Preassigned purchase credit accumulations earned by a consumer are exchanged from a merchant or creditor through or combination of credit cards, co-branded credit cards, PIN cards, debit and smart cards, coupons, stamps, proof of purchase, rebates, or any form of purchase award of merchant or creditors choice for an investment in a mutual fund or other investment vehicle. A specific implementation is described wherein a credit card account having investment credit awards is issued through the Internet to a customer. While inputting information through the Internet necessary for establishing the credit card account, the customer also provides any information needed to authorize the purchase of investment vehicles on his or her behalf. Any forms that need to be signed by the customer to authorize purchase of the investment vehicles may be printed out by the customer. The customer may also select, via the Internet, particular investment vehicles out of a group of possible investment vehicles. Subsequent use of the credit card by the customer automatically results in accrual of credit award accumulations in the selected investment vehicle.
Owner:KALINA DYAN T
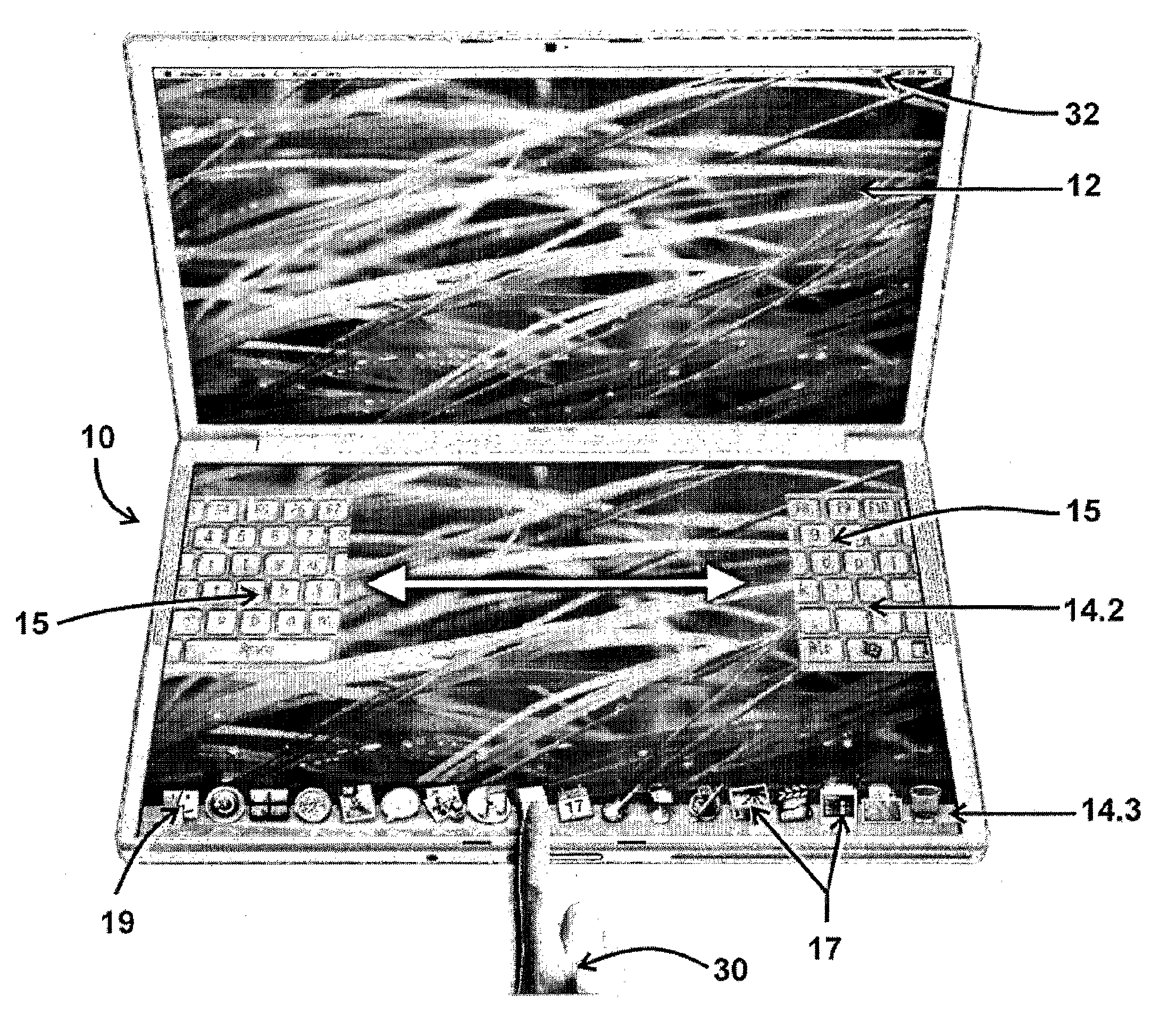
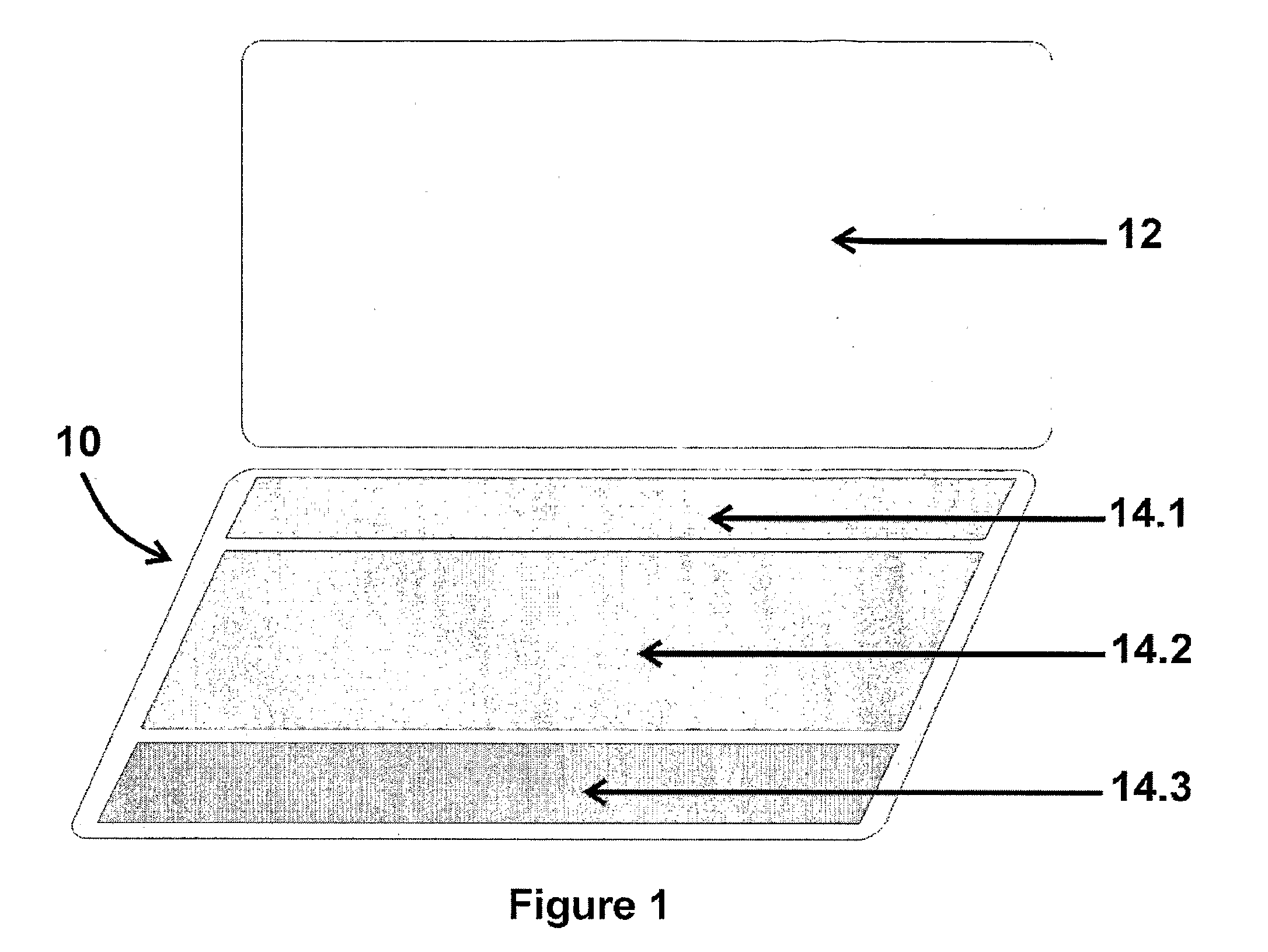
User interface
InactiveUS20110047459A1Avoid constructionImprove experienceInput/output for user-computer interactionDigital data processing detailsGraphicsDisplay device
The invention provides a user interface for a data processing machine which user interface is combined with a primary display screen for the machine or which is configured to be used with a machine which usually includes a primary display screen, which user interface comprises a secondary touch-sensitive display screen which is configured to be an input device for the machine and configured such that the graphic display of the input device is configured to complement and operatively cooperate with the graphic display of the primary display screen.
Owner:VAN DER WESTHUIZEN WILLEM MORKEL
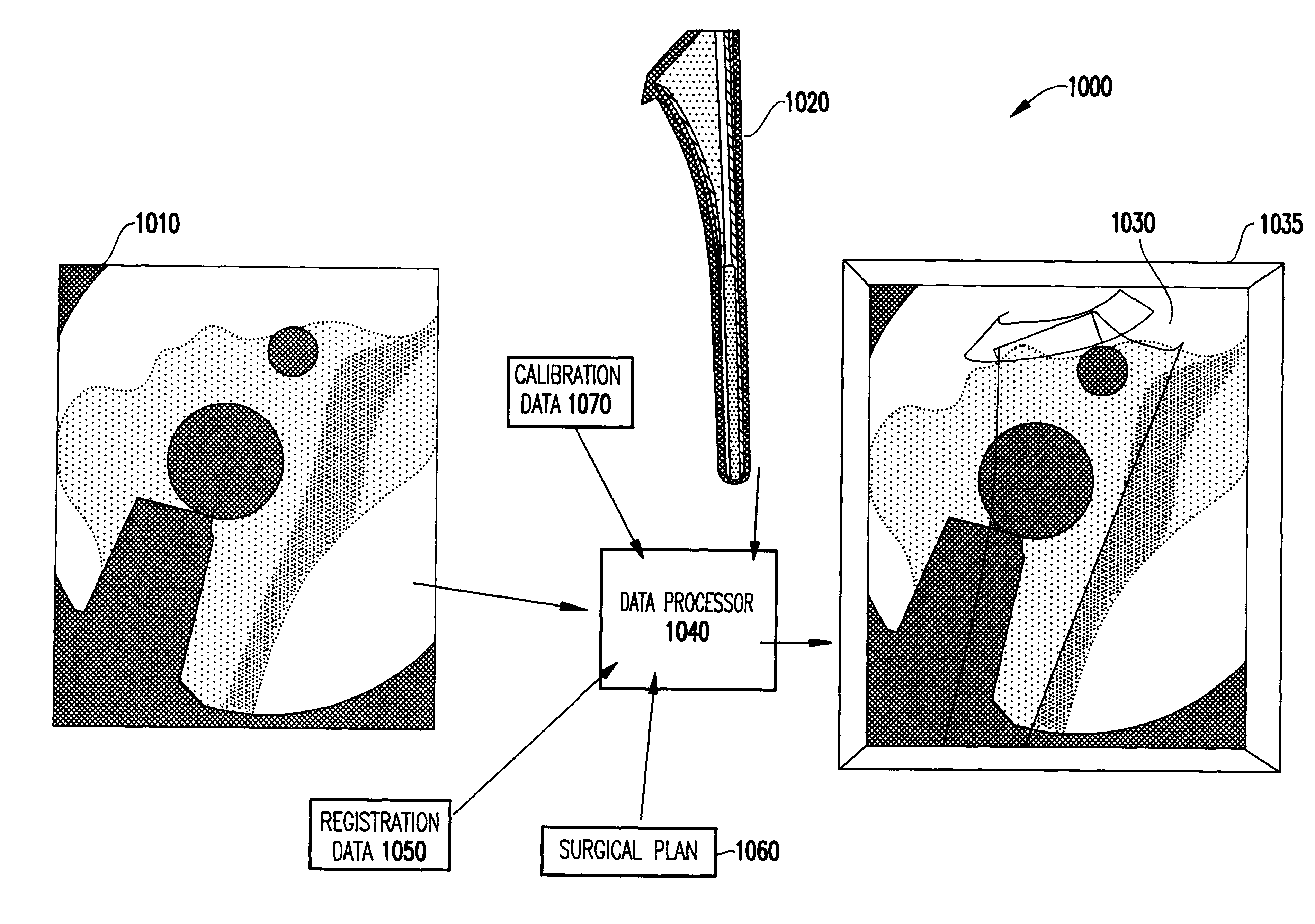
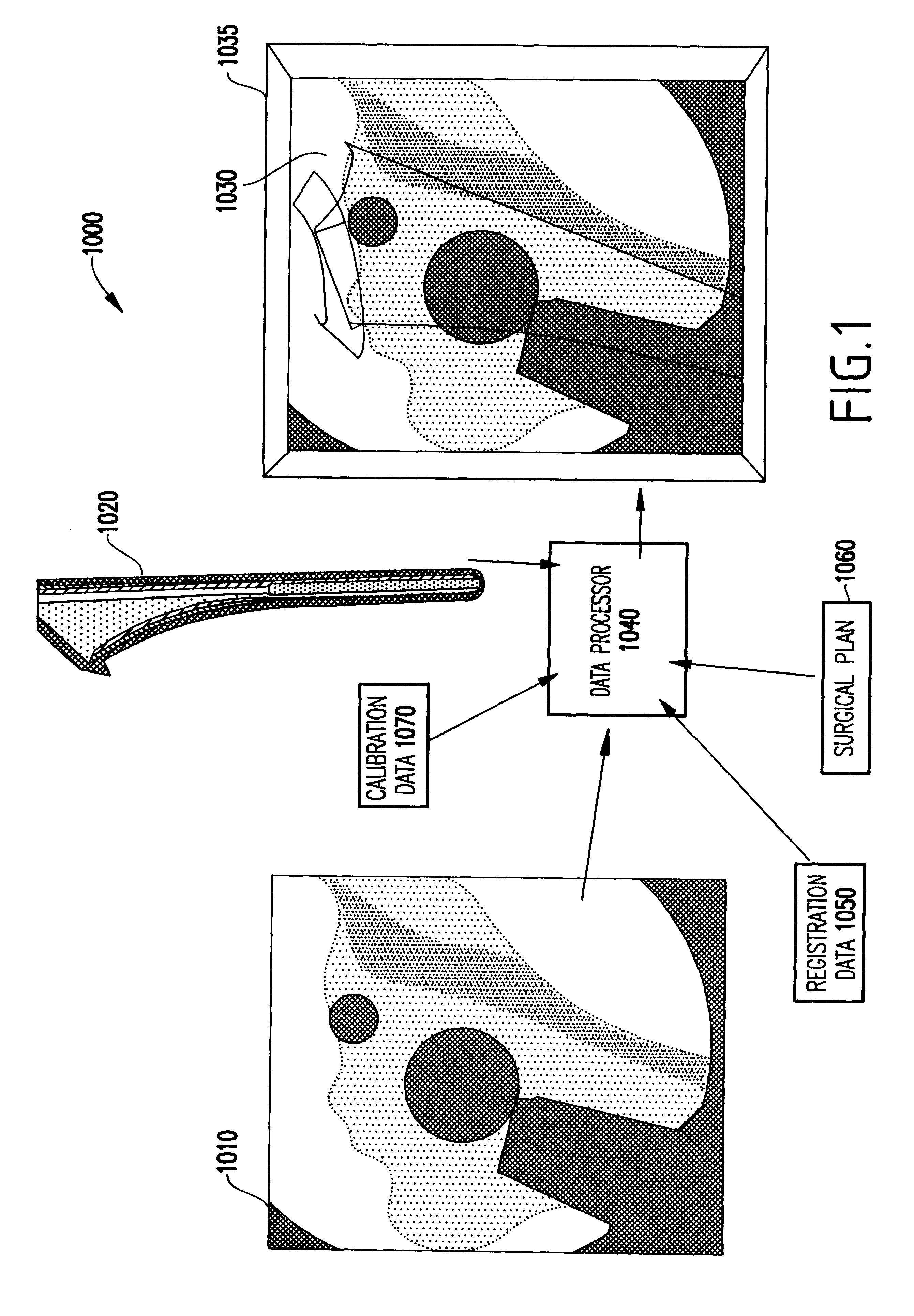
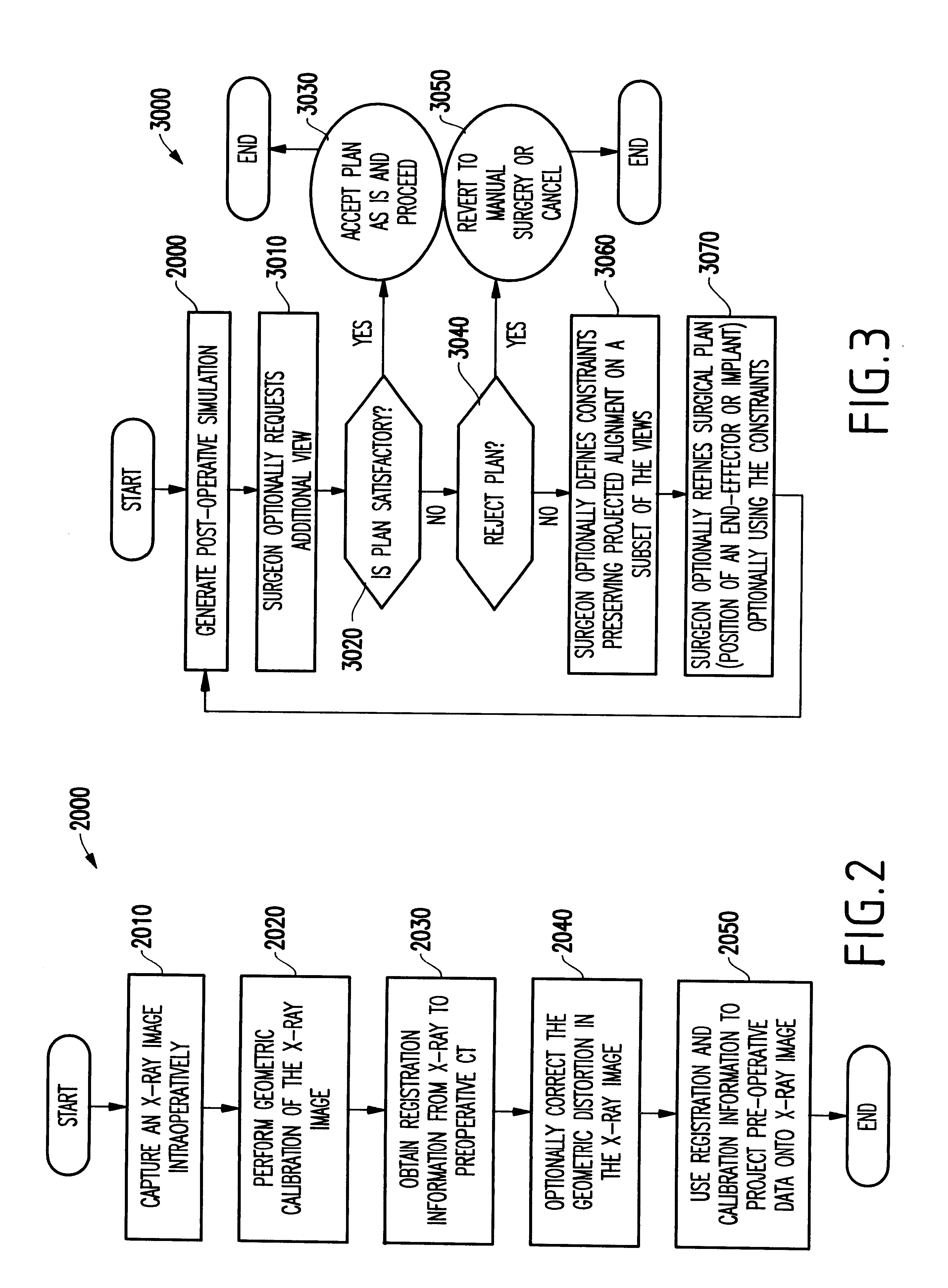
System and method for intra-operative, image-based, interactive verification of a pre-operative surgical plan
InactiveUS6301495B1Registration errorAvoid mistakesGeometric image transformationDiagnostic markersFusion mechanismPhysical space
A system and method for intra-operatively providing a surgeon with visual evaluations of possible surgical outcomes ahead of time, and generating simulated data, includes a medical imaging camera, a registration device for registering data to a physical space, and to the medical imaging camera, and a fusion mechanism for fusing the data and the images to generate simulated data. The simulated data (e.g., such as augmented X-ray images) is natural and easy for a surgeon to interpret. In an exemplary implementation, the system preferably includes a data processor which receives a three-dimensional surgical plan or three-dimensional plan of therapy delivery, one or a plurality of two-dimensional intra-operative images, a three-dimensional model of pre-operative data, registration data, and image calibration data. The data processor produces one or a plurality of simulated post-operative images, by integrating a projection of a three-dimensional model of pre-operative data onto one or a plurality of two-dimensional intra-operative images.
Owner:IBM CORP
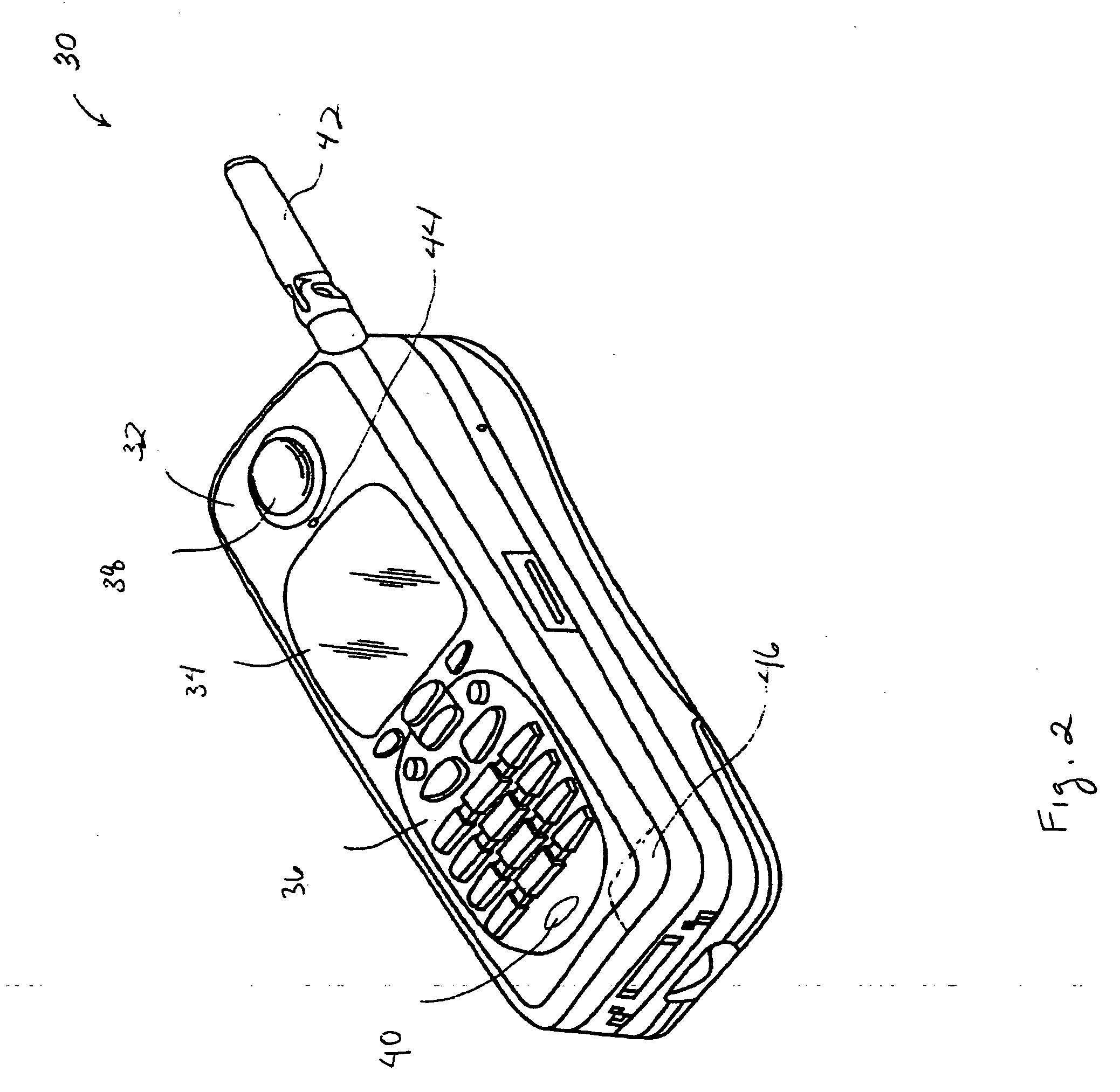
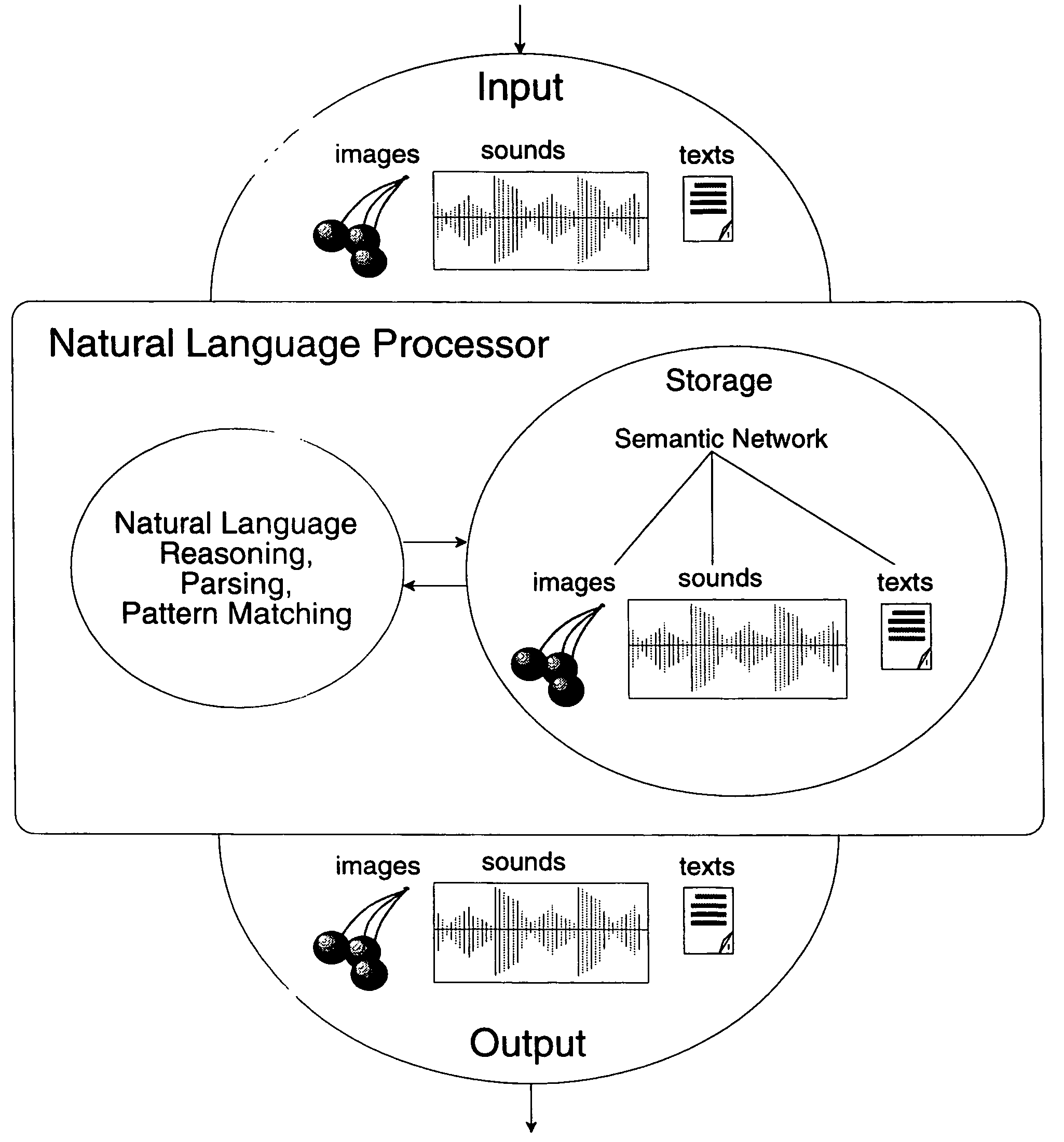
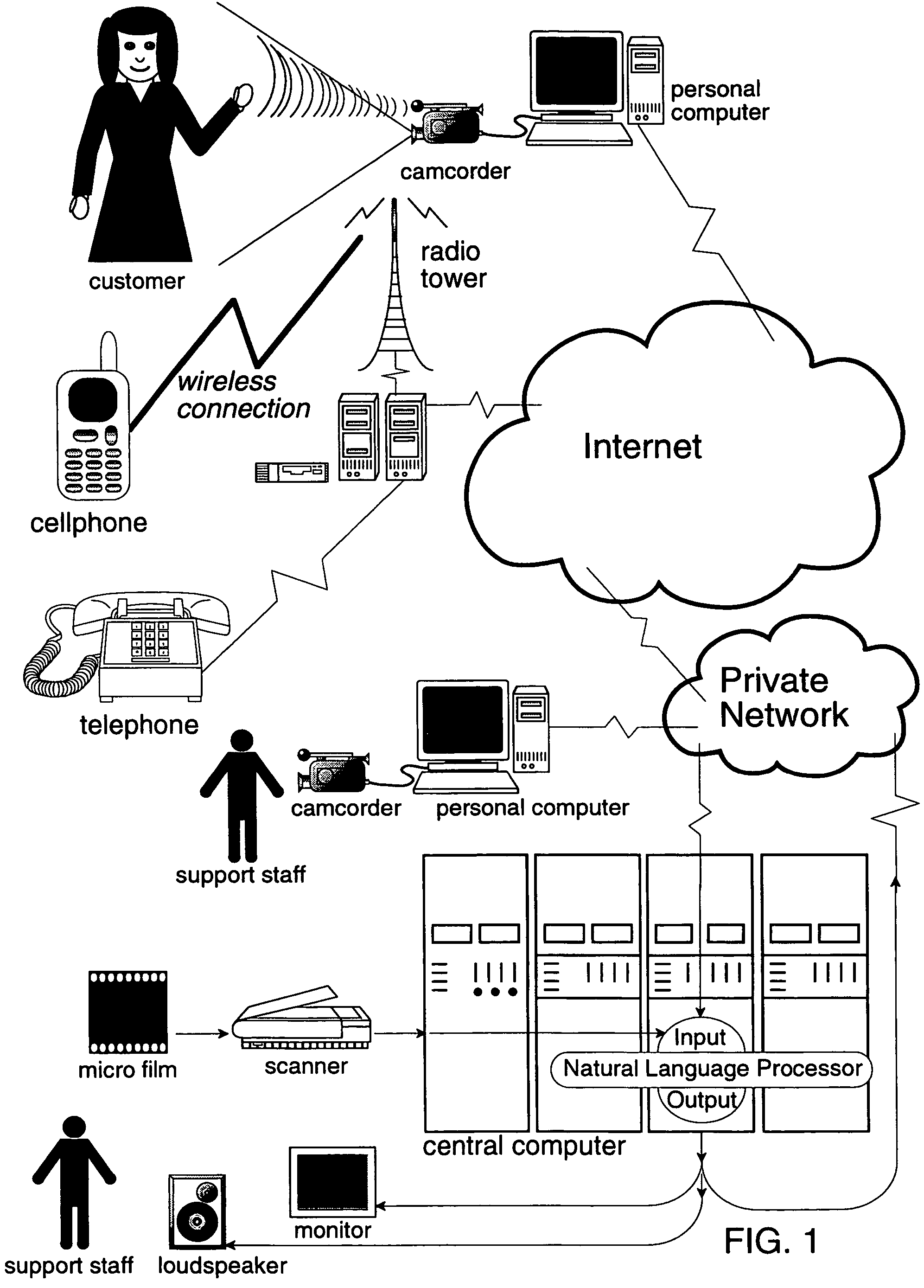
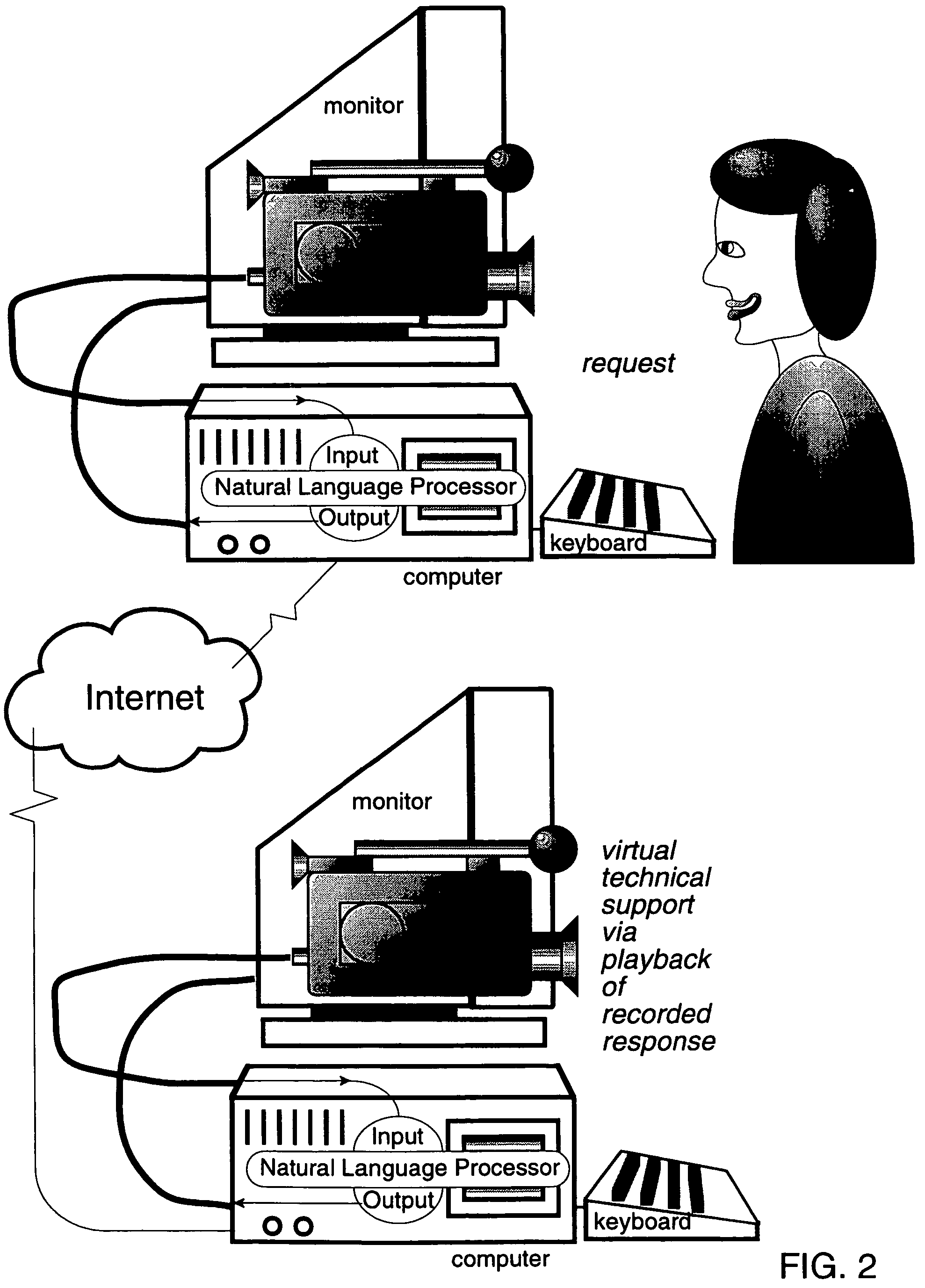
Method and system for analysis of intended meaning of natural language
InactiveUS7526466B2Flexible and efficient natural language interfaceAccurate measurementSemantic analysisChaos modelsData treatmentHand held devices
A computer implemented data processor system automatically disambiguates a contextual meaning of natural language symbols to enable precise meanings to be stored for later retrieval from a natural language database, so that natural language database design is automatic, to enable flexible and efficient natural language interfaces to computers, household appliances and hand-held devices.
Owner:DATACLOUD TECH LLC
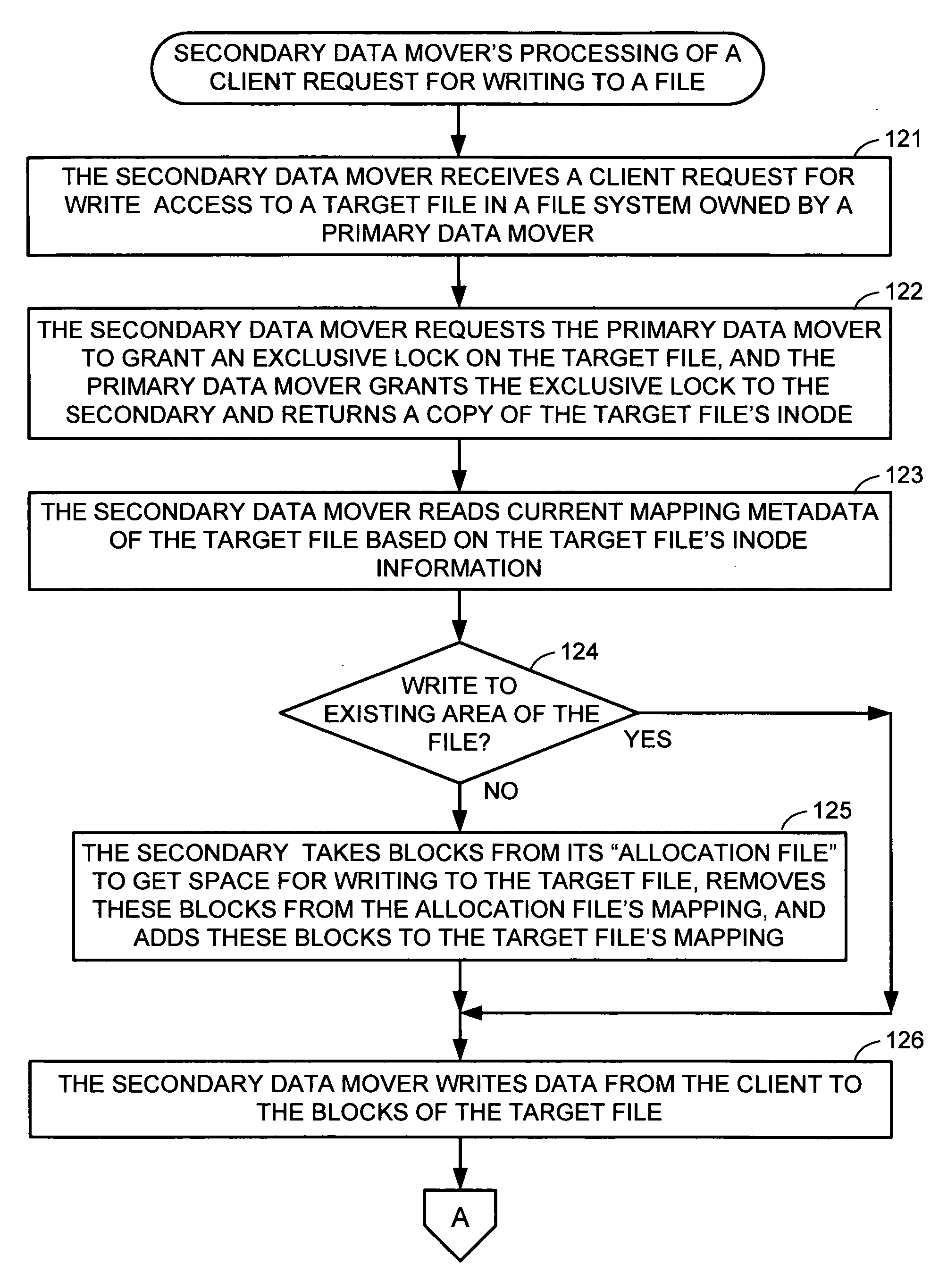
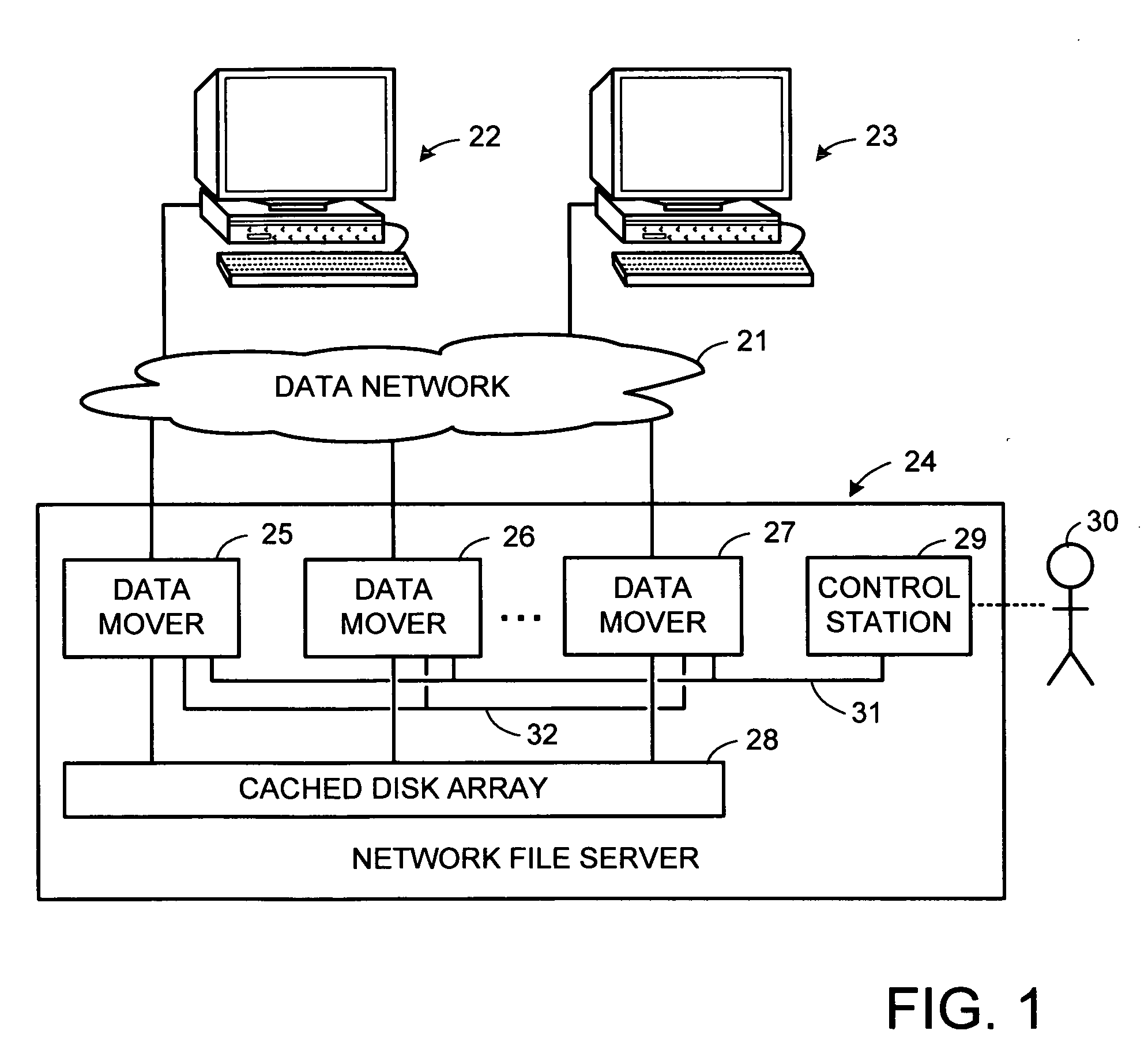
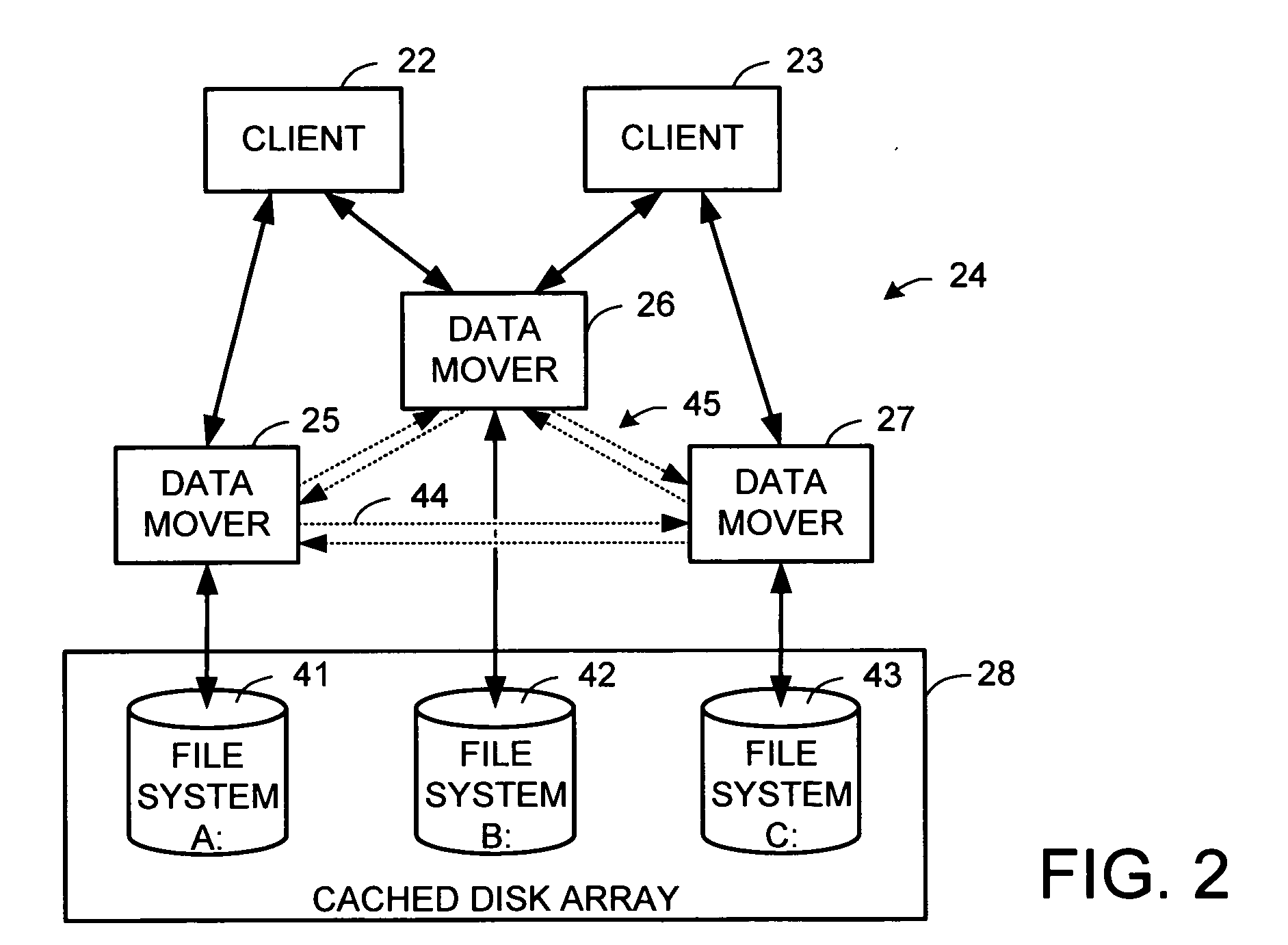
Metadata offload for a file server cluster
ActiveUS20070055702A1Promote recoveryReduce processDigital data information retrievalSpecial data processing applicationsFile systemData treatment
A file server system has a cluster of server computers that share access to a file system in shared storage. One of the server computers has primary responsibility for management of access to the file system. In order to reduce the possibility of primary server overload when a large number of the clients happen to concurrently access the same file system, most metadata processing operations are offloaded to secondary server computers. This also facilitates recovery from failure of a primary server computer since only a fraction of the ongoing metadata operations of a primary server computer is interrupted by a failure of the primary server computer. For example, a secondary data mover may truncate, delete, create, or rename a file in response to a client request.
Owner:EMC IP HLDG CO LLC
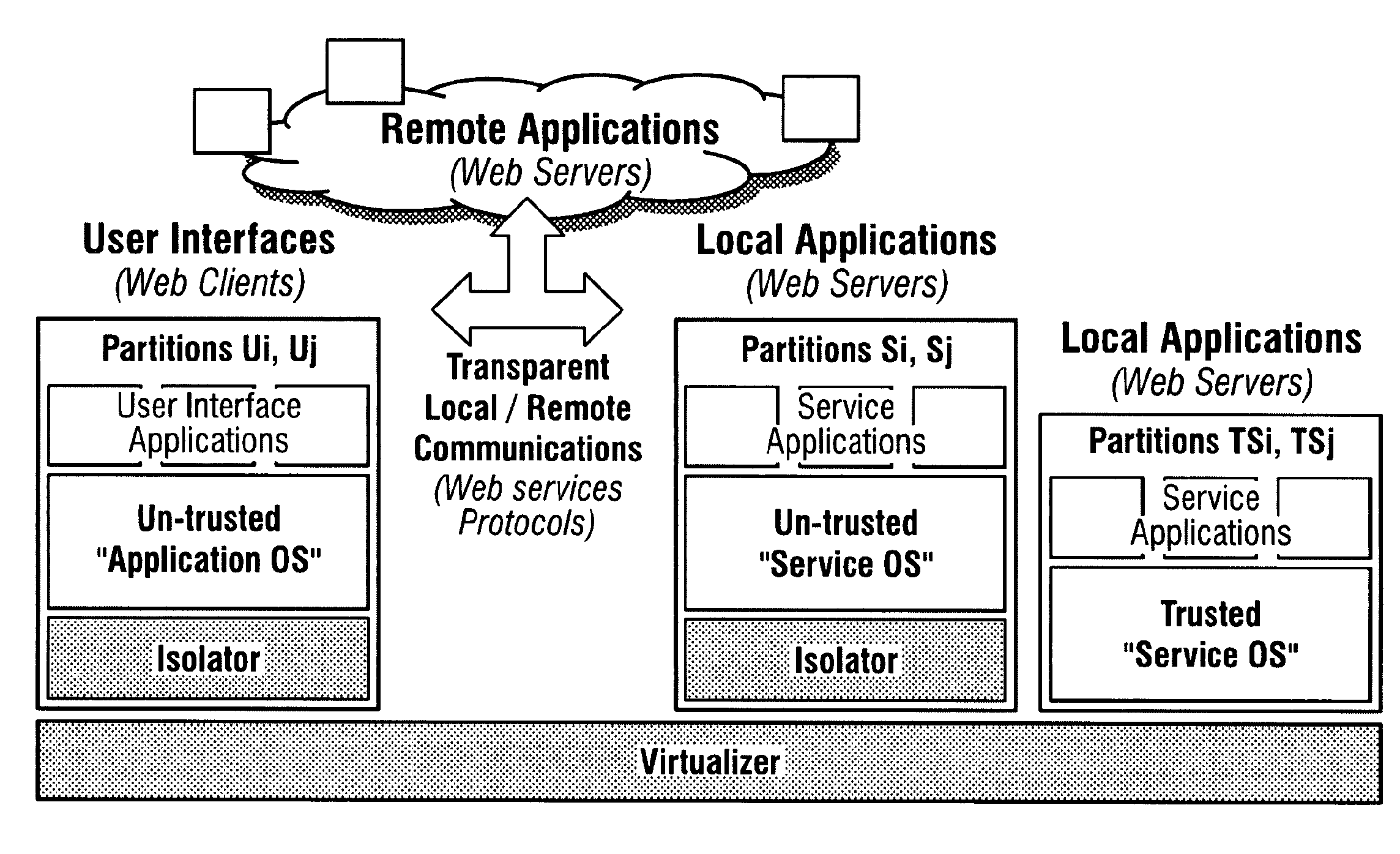
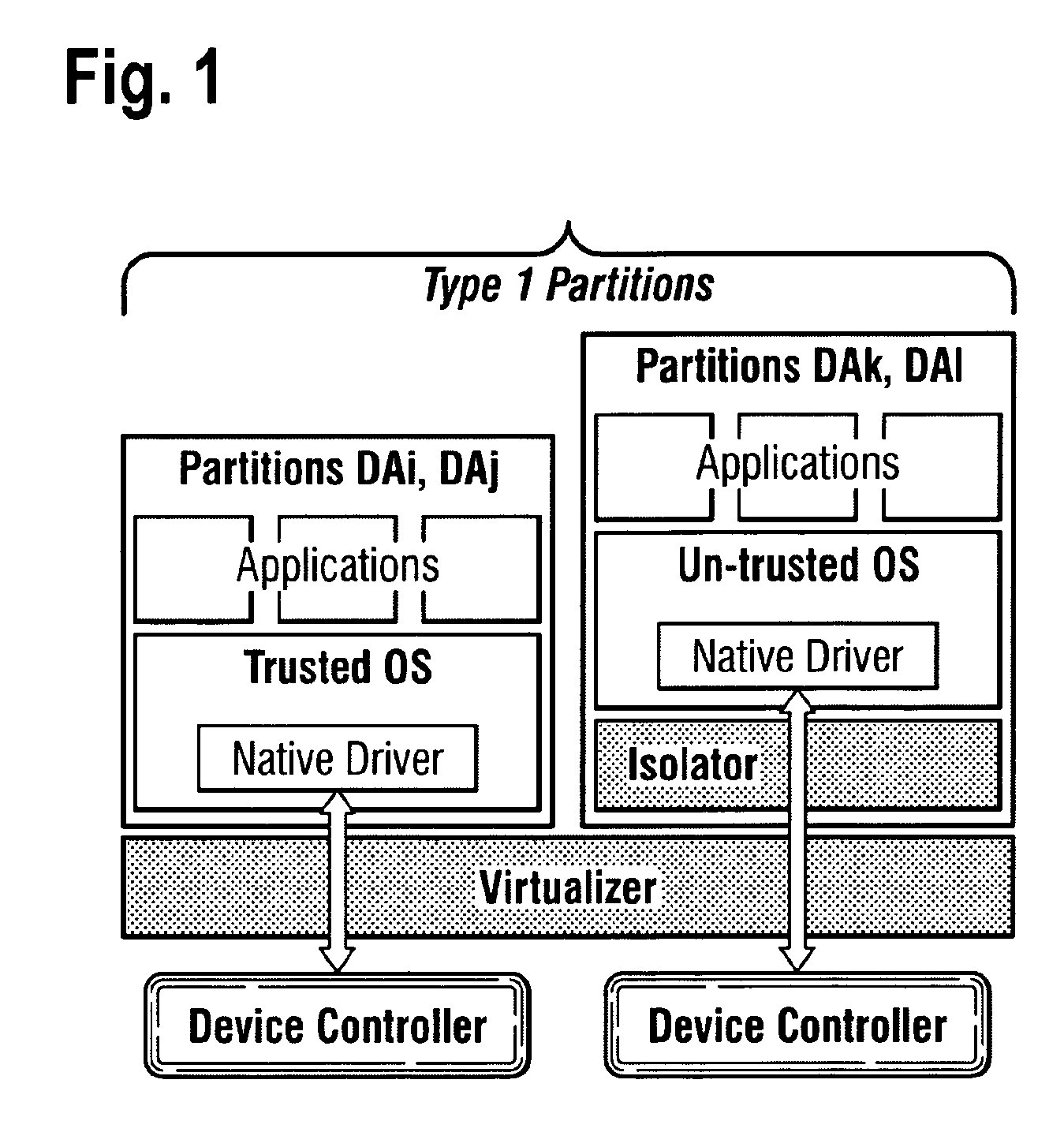
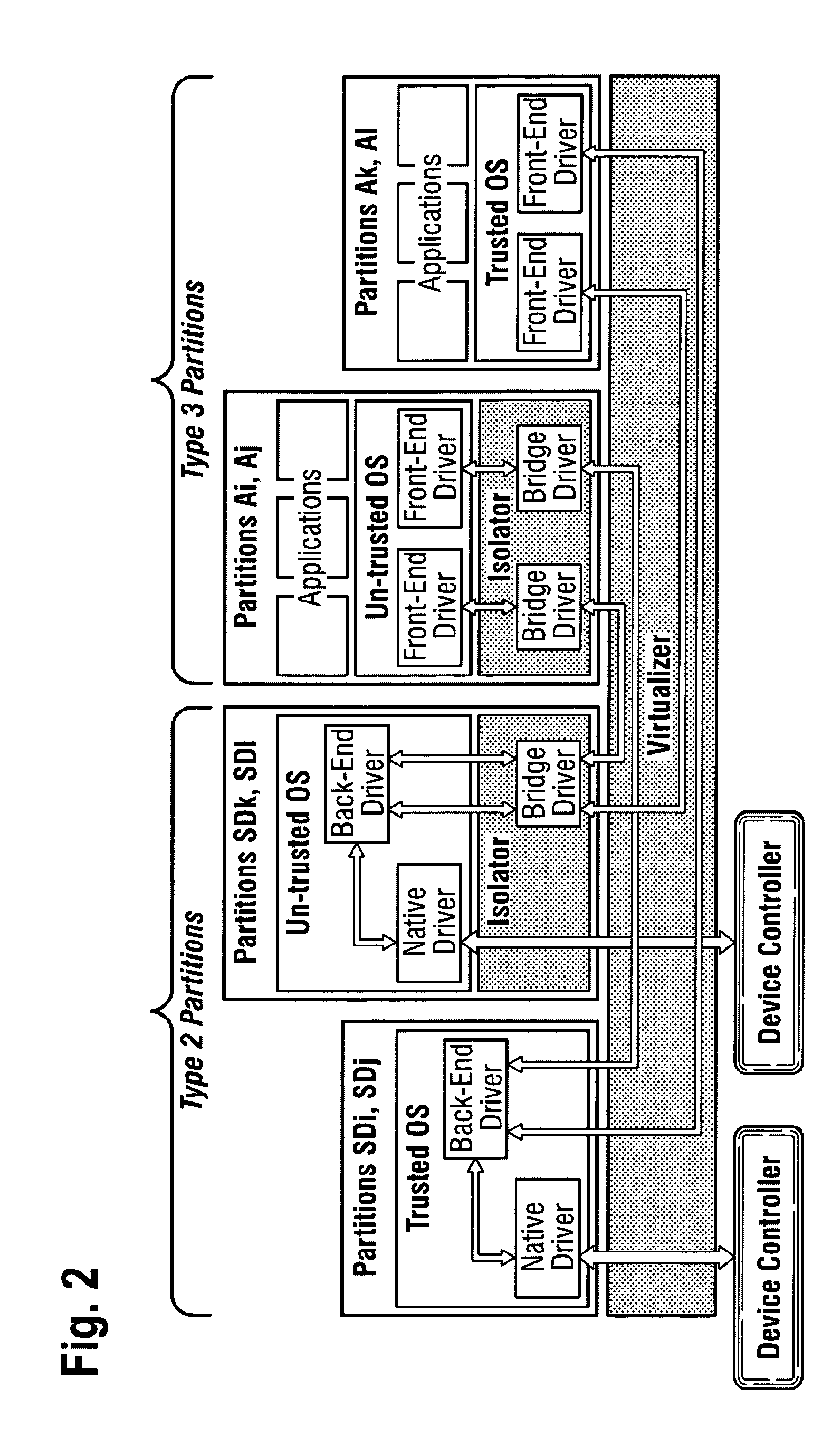
System for enabling multiple execution environments to share a device
ActiveUS20100031325A1Digital data processing detailsAnalogue secracy/subscription systemsData processing systemData treatment
According to the present invention, there is provided a data processing system comprising: a dedicated physical device for access by a single client only; a shared physical device for shared access by multiple clients; a partition of a first type associated with the dedicated physical device, the first type partition comprising said single client and a first device driver for accessing the dedicated physical device; a partition of a second type associated with the shared physical device, the second type partition comprising a second device driver for accessing the shared physical device, and a back end driver for accessing the second device driver; and multiple partitions of the third type each comprising a respective one of said multiple clients and a front end driver for accessing the shared physical device via the second type partition. There is also provided a method of operating the data processing system comprising: executing a user application in the standard domain; and executing in the trusted domain, one or more predetermined operations, services and / or functions relating to the user application.
Owner:VIRTUALLOGIX
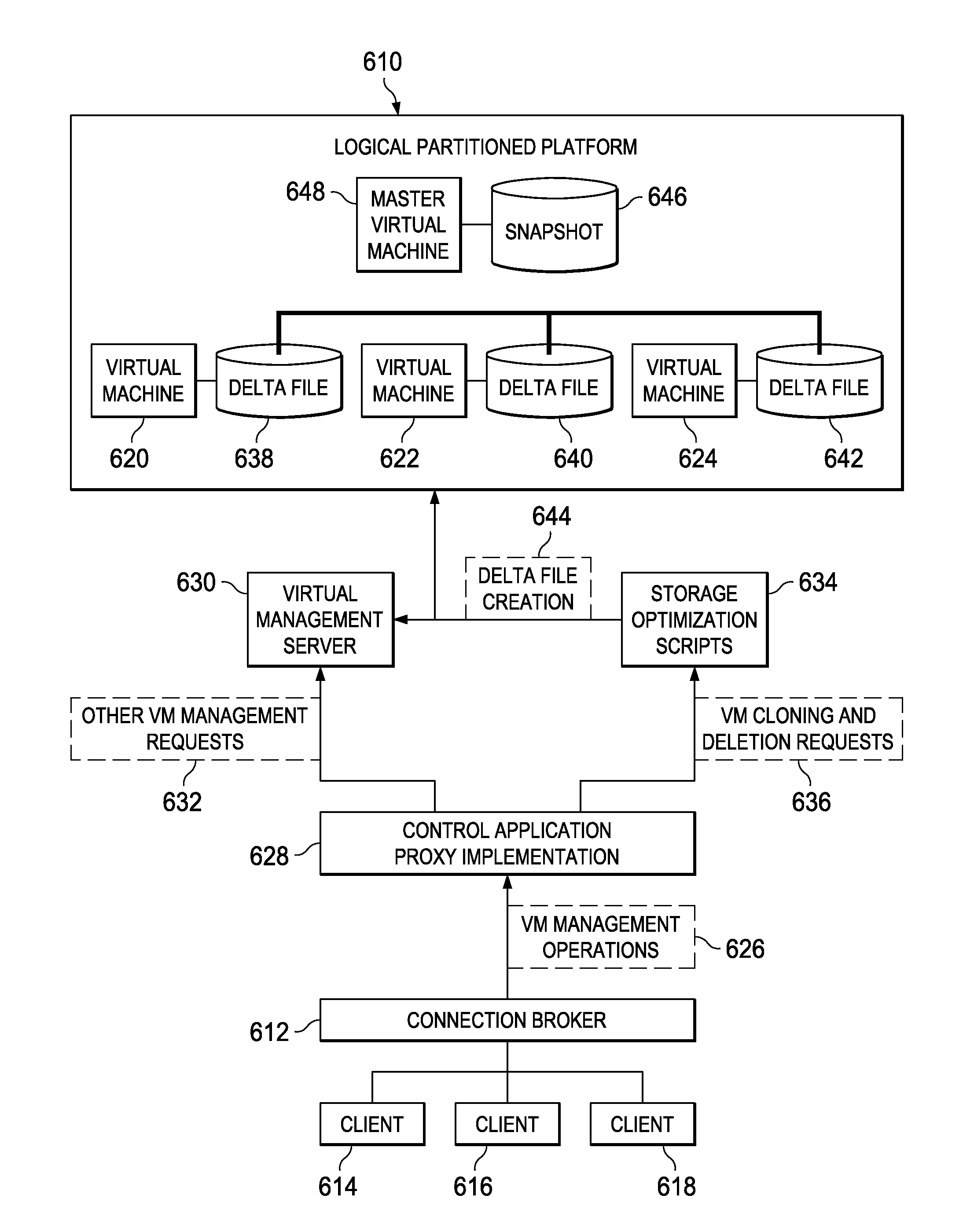
Provisioning Storage-Optimized Virtual Machines Within a Virtual Desktop Environment
ActiveUS20090260007A1Software simulation/interpretation/emulationMemory systemsData processing systemData treatment
A computer implemented method, a computer program product, and data processing system clone virtual machines in a virtual desktop environment. A request to clone a new virtual machine is intercepted, wherein the request was initially sent to a virtual management server. Responsive to intercepting the request, the new virtual machine is cloned from a snapshot of a master virtual machine. A delta file is created for the new virtual machine, wherein the delta file includes a base disk reference and a copied delta file. The new virtual machine is configured to read a base disk image from a snapshot of the master virtual machine. The new virtual machine is configured to write data to the copied delta file in the delta file.
Owner:IBM CORP
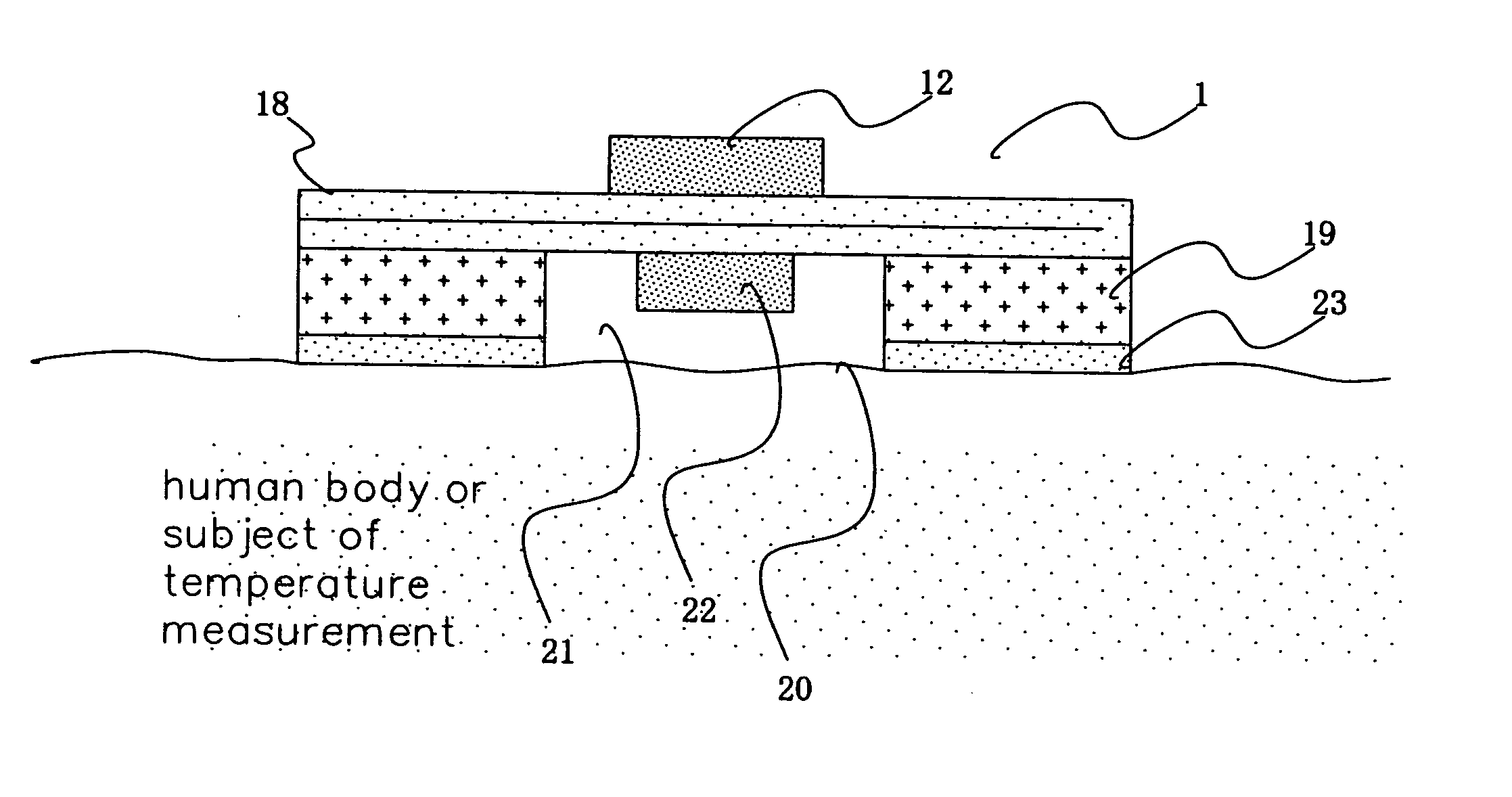
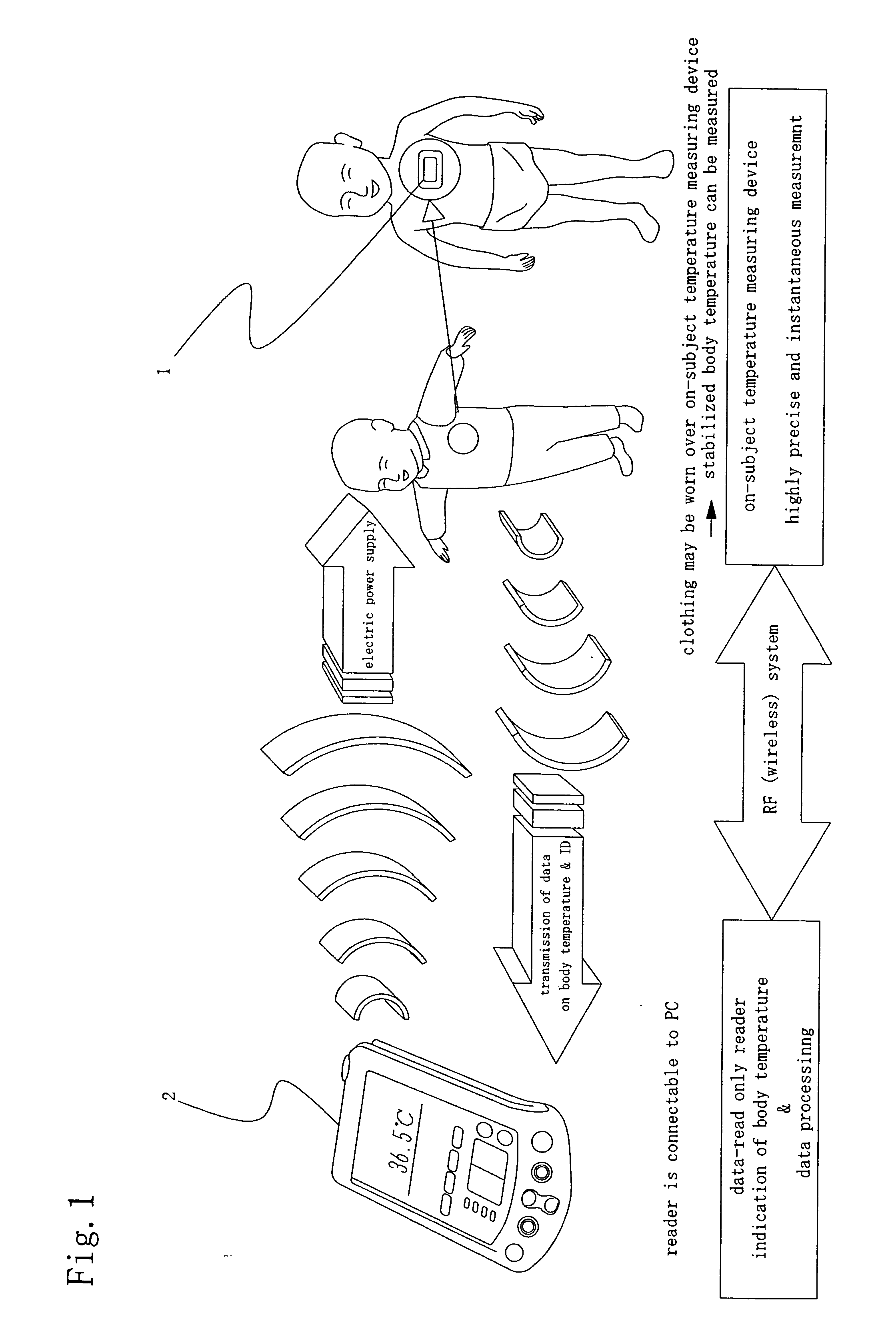
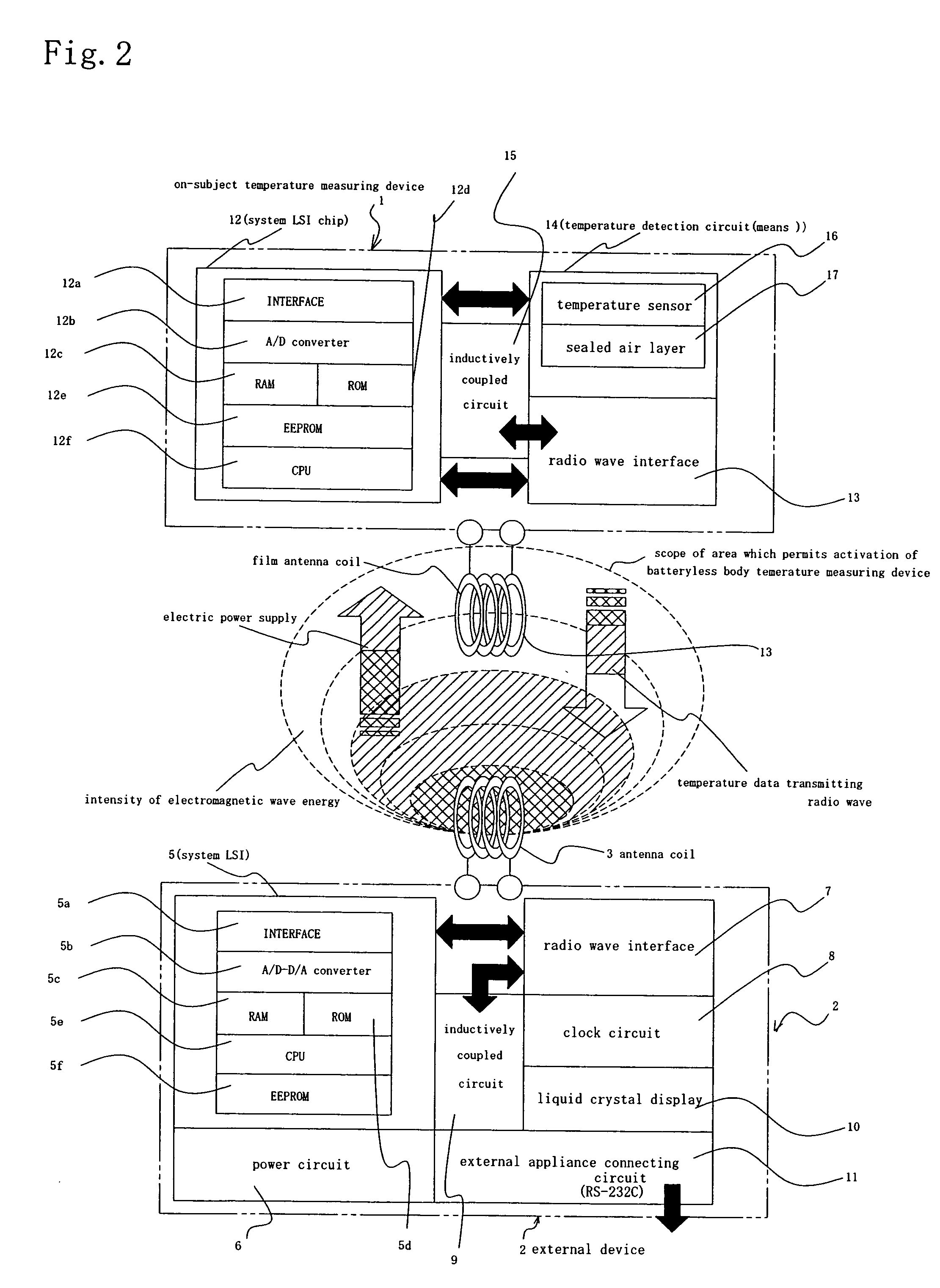
Temperature measuring device and temperature measuring method
InactiveUS20050141591A1Low production costFree replacementThermometer detailsElectric signal transmission systemsSingle-Use DeviceMeasurement device
A temperature measuring device and a temperature measuring method are provided which are capable of obtaining precise measured temperature values with respect even to old persons, sucklings or infants, which device may be formed into a disposable type according to need, which method may be carried out using such a disposable type device according to need, and which enable precise temperature measurement in real time. An on-subject temperature measuring device 1, which is attached to a subject when a temperature of the subject is measured, receives a radio wave from a reader 2 as an external device and is thereby electrically powered. Using the electric power, temperature measurement is performed in the on-subject temperature measuring device 1. The results of the measurement are transmitted through radio waves to the reader 2 in the form of a temperature of the subject and ID data. The reader 2 is so constructed as to be connectable to a personal computer (not shown), and data processing by the personal computer is performed according to need.
Owner:SAKANO KAZUHITO +2
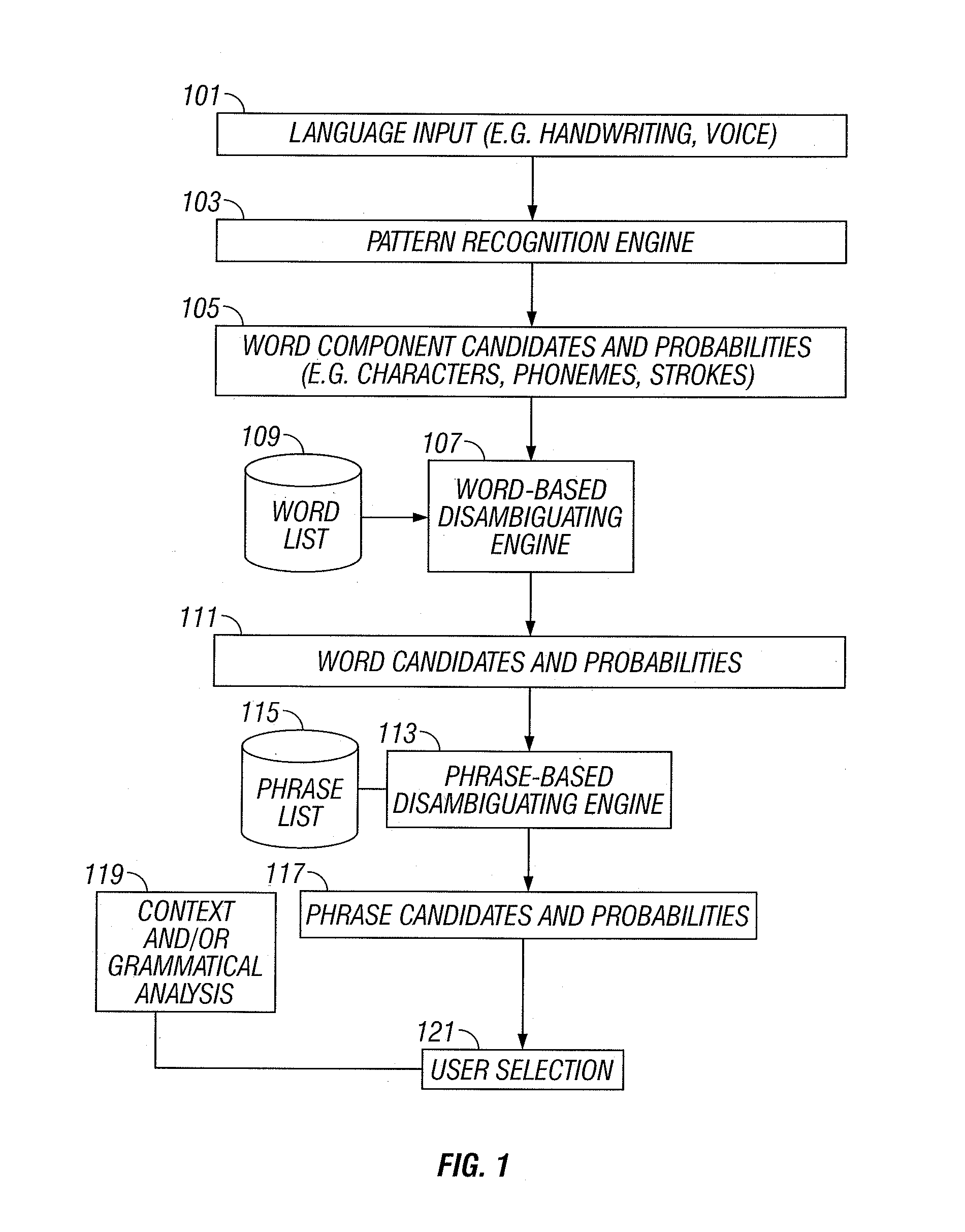
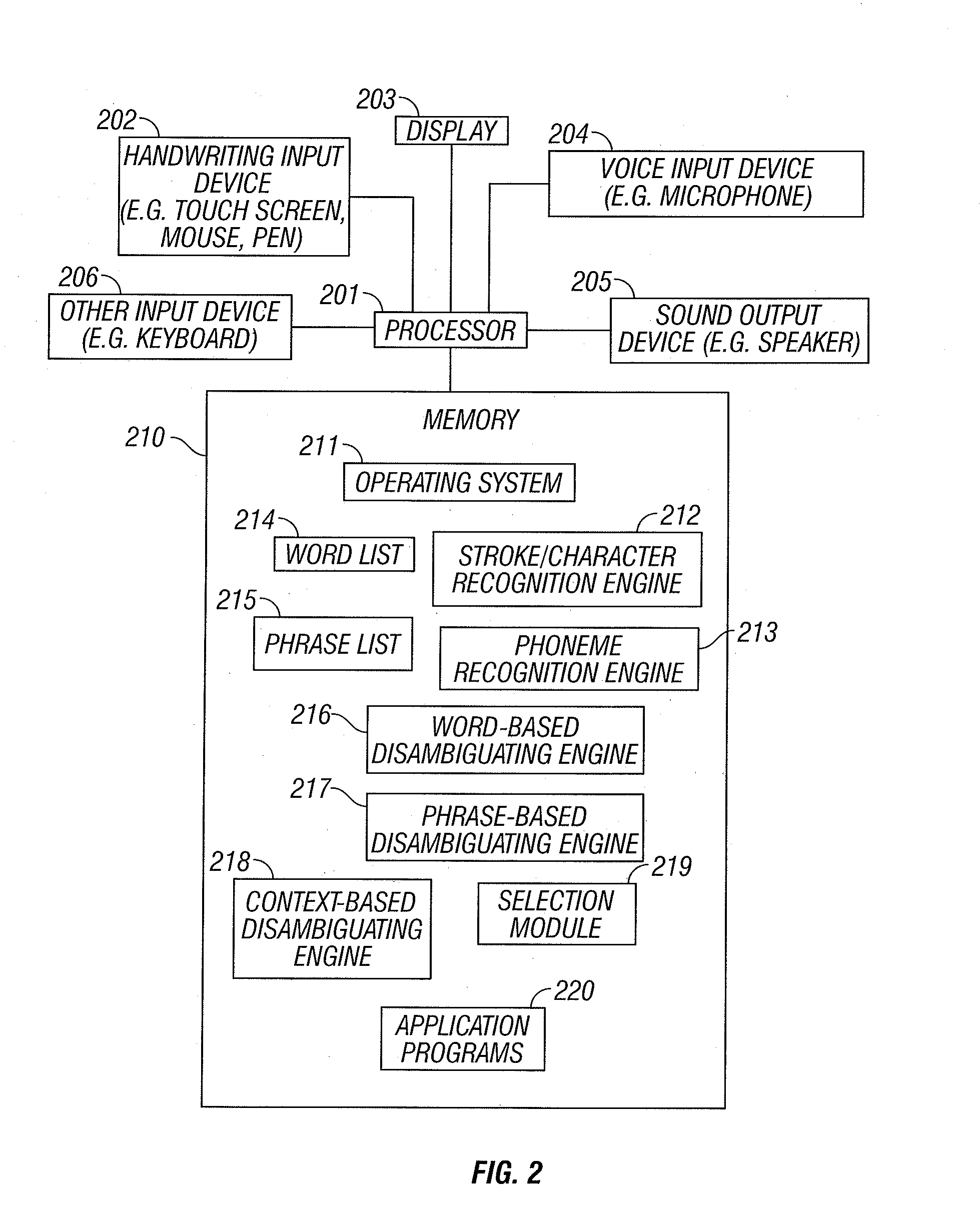
Handwriting and voice input with automatic correction
A hybrid approach to improve handwriting recognition and voice recognition in data process systems is disclosed. In one embodiment, a front end is used to recognize strokes, characters and / or phonemes. The front end returns candidates with relative or absolute probabilities of matching to the input. Based on linguistic characteristics of the language, e.g. alphabetical or ideographic language for the words being entered, e.g. frequency of words and phrases being used, likely part of speech of the word entered, the morphology of the language, or the context in which the word is entered), a back end combines the candidates determined by the front end from inputs for words to match with known words and the probabilities of the use of such words in the current context.
Owner:TEGIC COMM
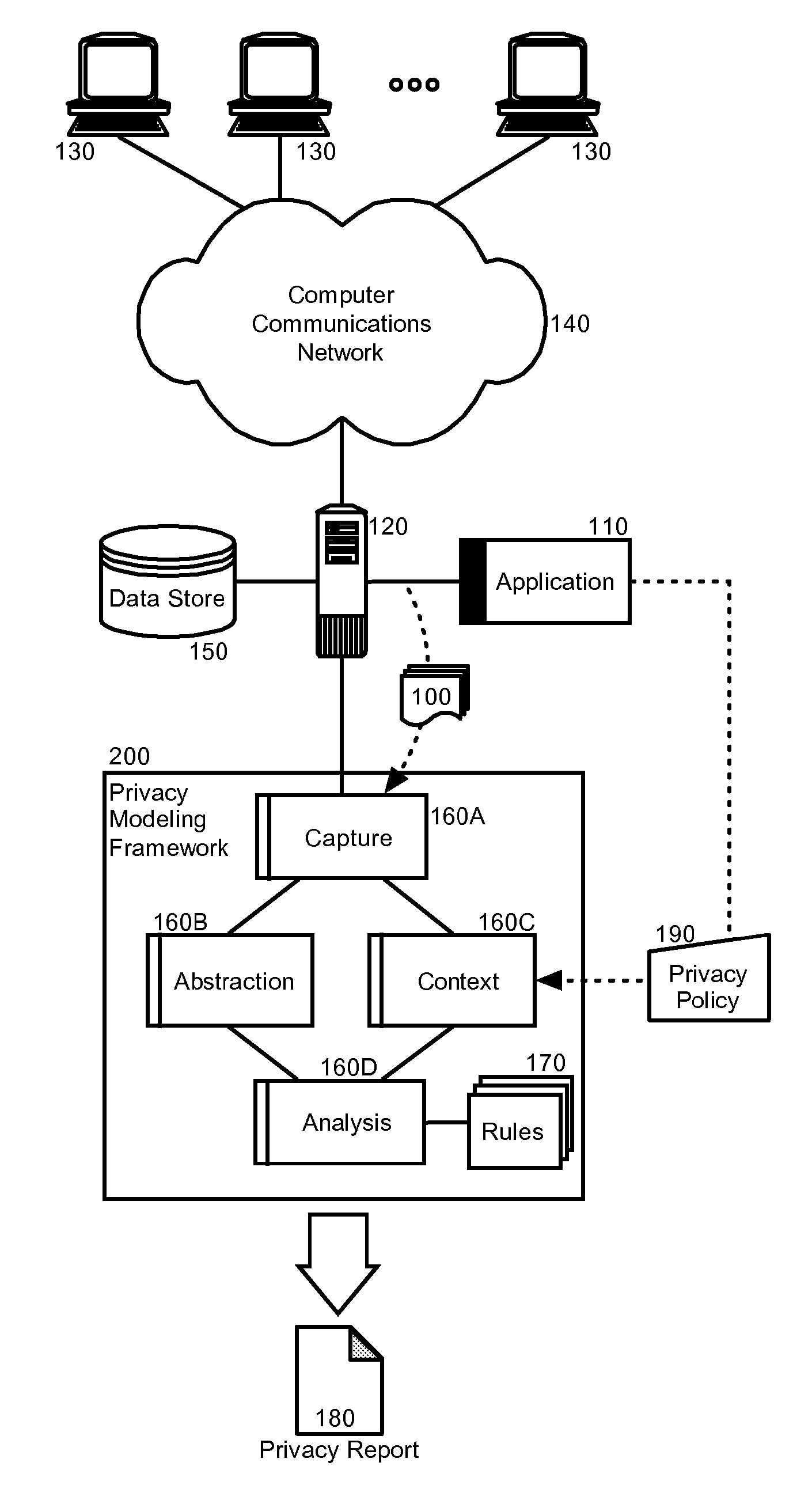
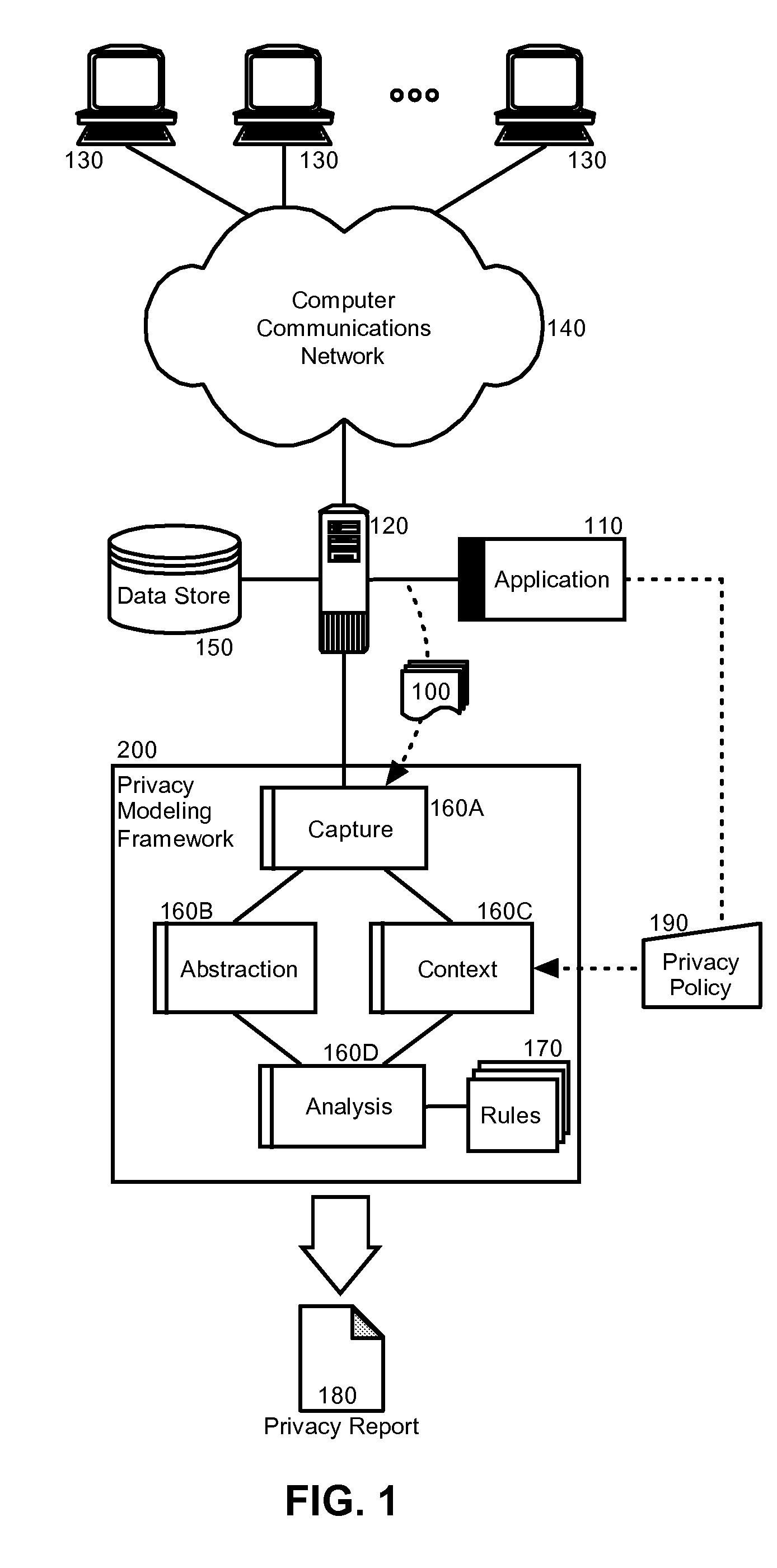
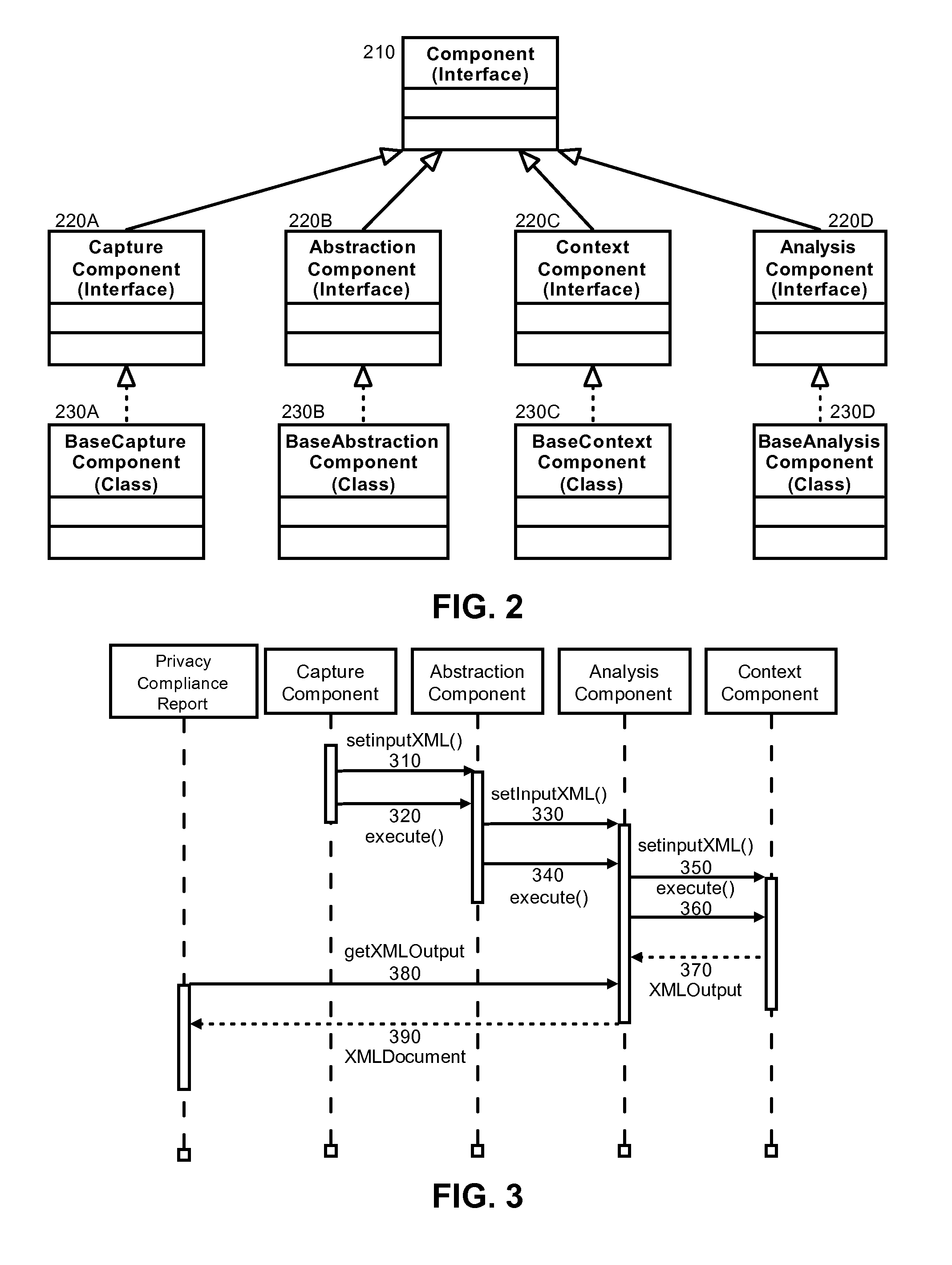
Privacy modeling framework for software applications
InactiveUS20070266420A1Computer security arrangementsOffice automationData processing systemCoupling
Embodiments of the present invention address deficiencies of the art in respect to privacy compliance assessment for computer software and provide a method, system and computer program product for a privacy model framework for software applications. In one embodiment, a privacy modeling data processing system can be provided. The privacy modeling data processing system can include a modeling framework configured for communicative coupling to a software application. The modeling framework can capture information flows from requests to and responses from a coupled software application, and can rules-based process the captured information flows for privacy rules to generate a privacy compliance report for the software application.
Owner:IBM CORP
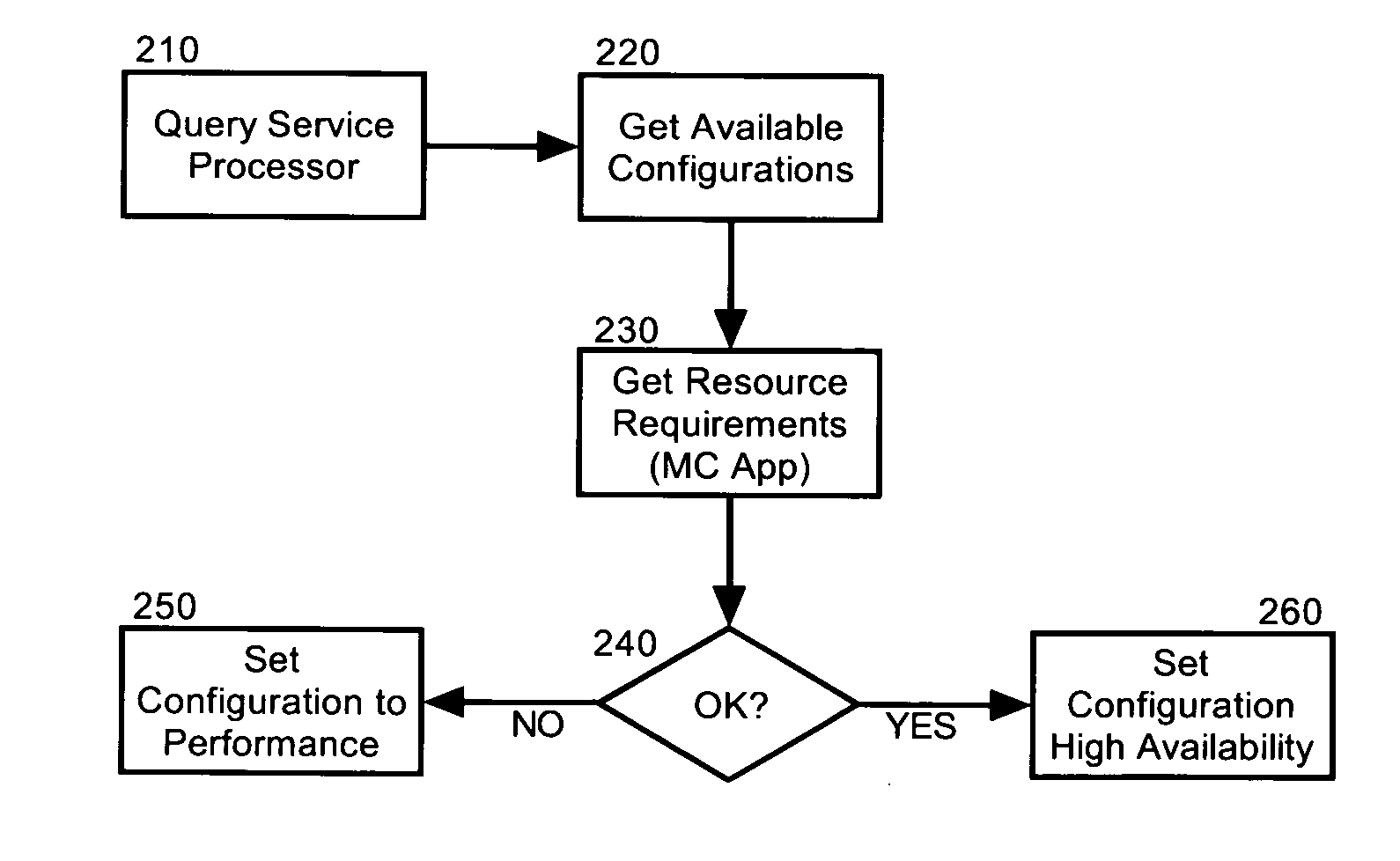
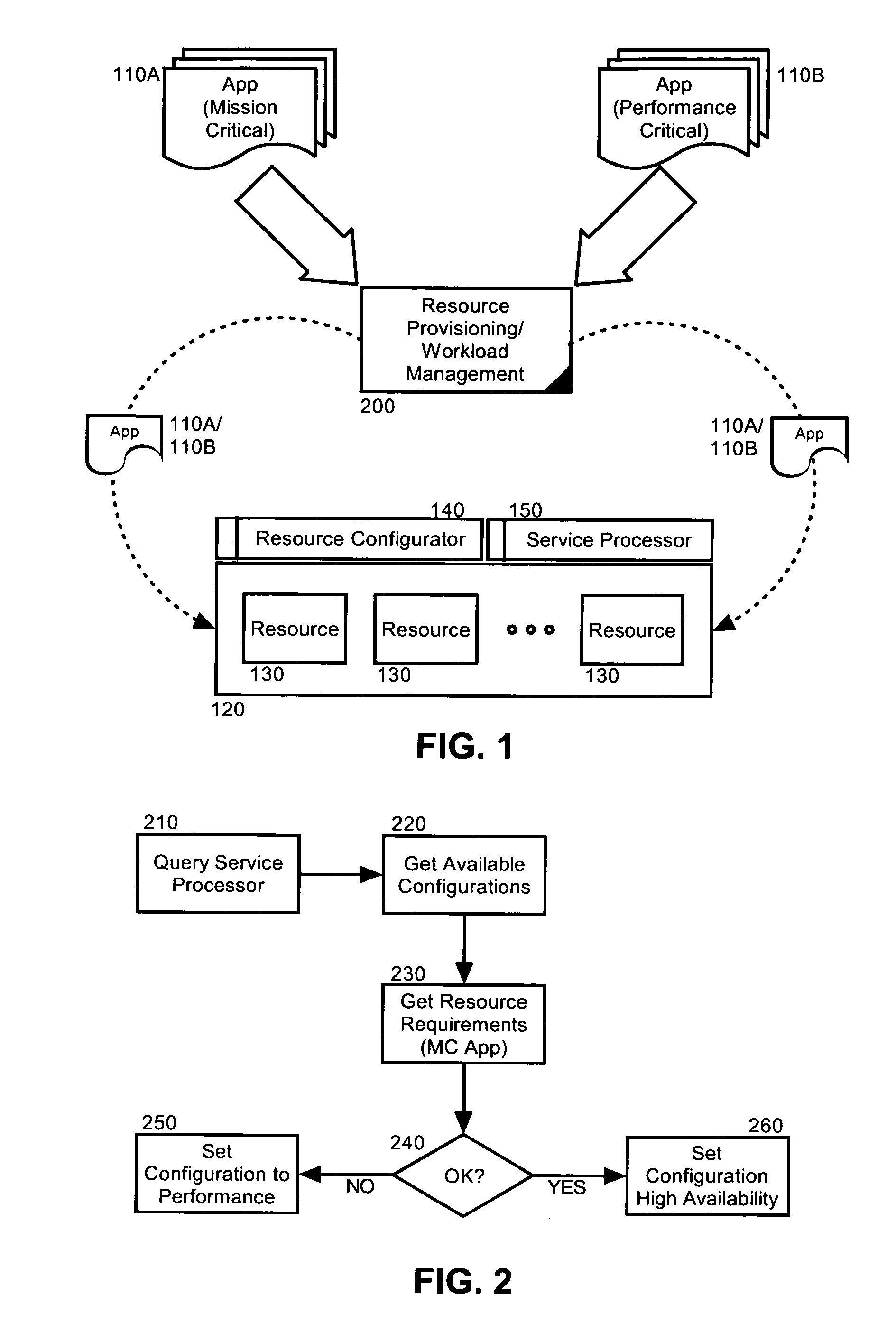
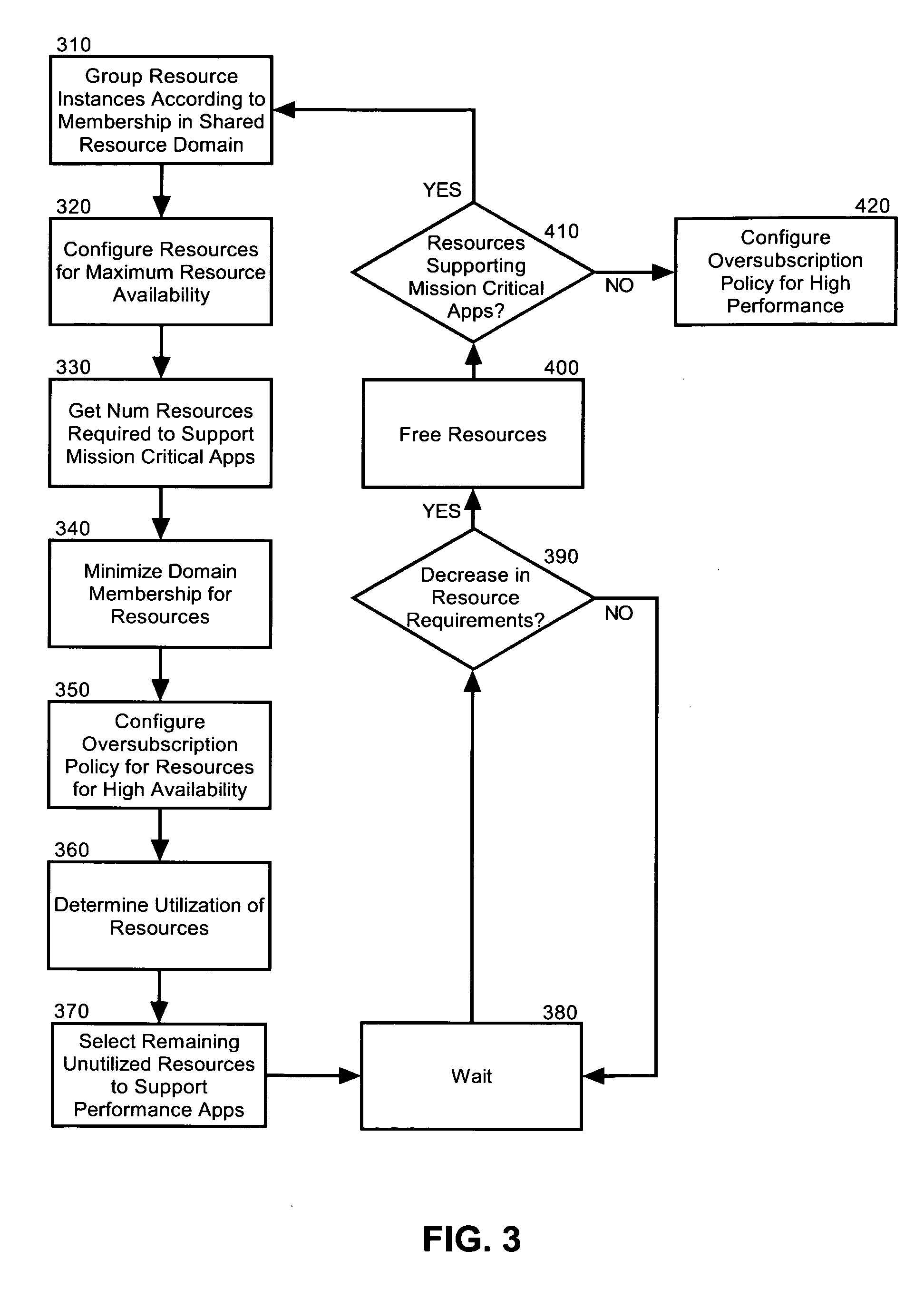
Dynamic resource allocation for disparate application performance requirements
InactiveUS20070198982A1Multiprogramming arrangementsMemory systemsResource poolData processing system
Embodiments of the invention address deficiencies of the art in respect to dynamic computing resource allocation, and provide a method, system and computer program product for dynamic resource allocation for disparate application performance requirements. In one embodiment of the invention, a resource allocation data processing system can include a shared resource pool including resources and a resource configurator coupled to the shared resource pool. The system further can include a service processor coupled to the resource configurator, wherein the service processor can include an application programming interface (API) exposing methods for commanding the resource configurator to configure the resources in the shared resource pool.
Owner:LENOVO ENTERPRISE SOLUTIONS SINGAPORE
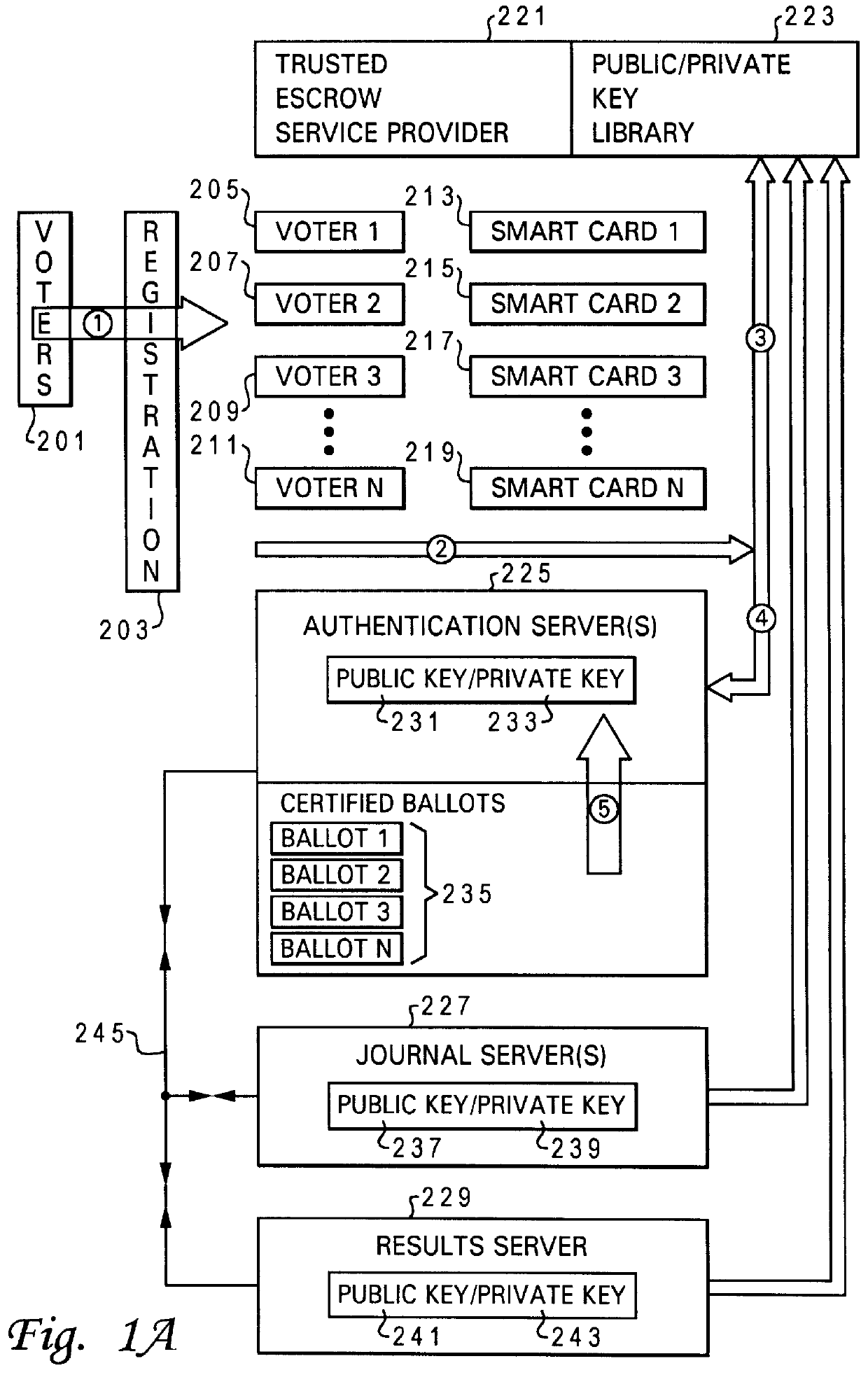
Method and system for secure computer moderated voting
InactiveUS6081793AVoting apparatusMultiple keys/algorithms usageData processing systemAuthentication server
A method and system is provided for improved electronic voting. The system optionally allows paper type ballots to be utilized. A plurality of cryptographic routines are utilized in a distributed data processing system to maximize the privacy of both the voter's identity and the content of completed ballots. An authentication server is utilized to interact with a voter to issue electronic ballots and receive completed electronic ballots in a manner which determines the authenticity of the identification of the voter, while maintaining the content of the completed ballot confidential. The distributed data processing system further includes a results server which tabulates the content of completed ballots in a manner which maintains the identity of the voters associated with the particular ballots confidential. The distributed data processing system may further include a journal server which records completed ballots, in a manner which facilitates the challenge of ineligible votes and the correction of erroneous votes.
Owner:LENOVO PC INT
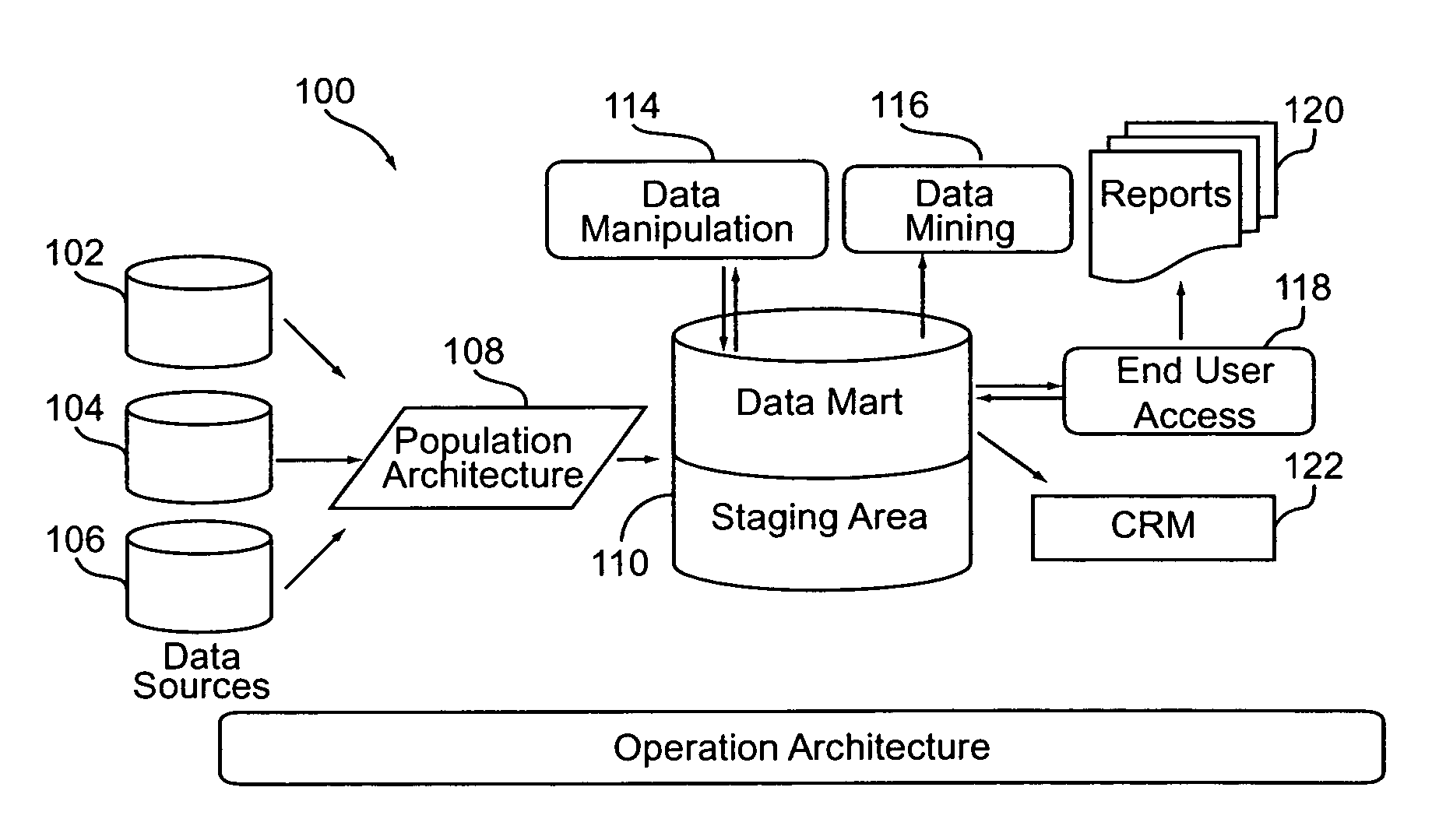
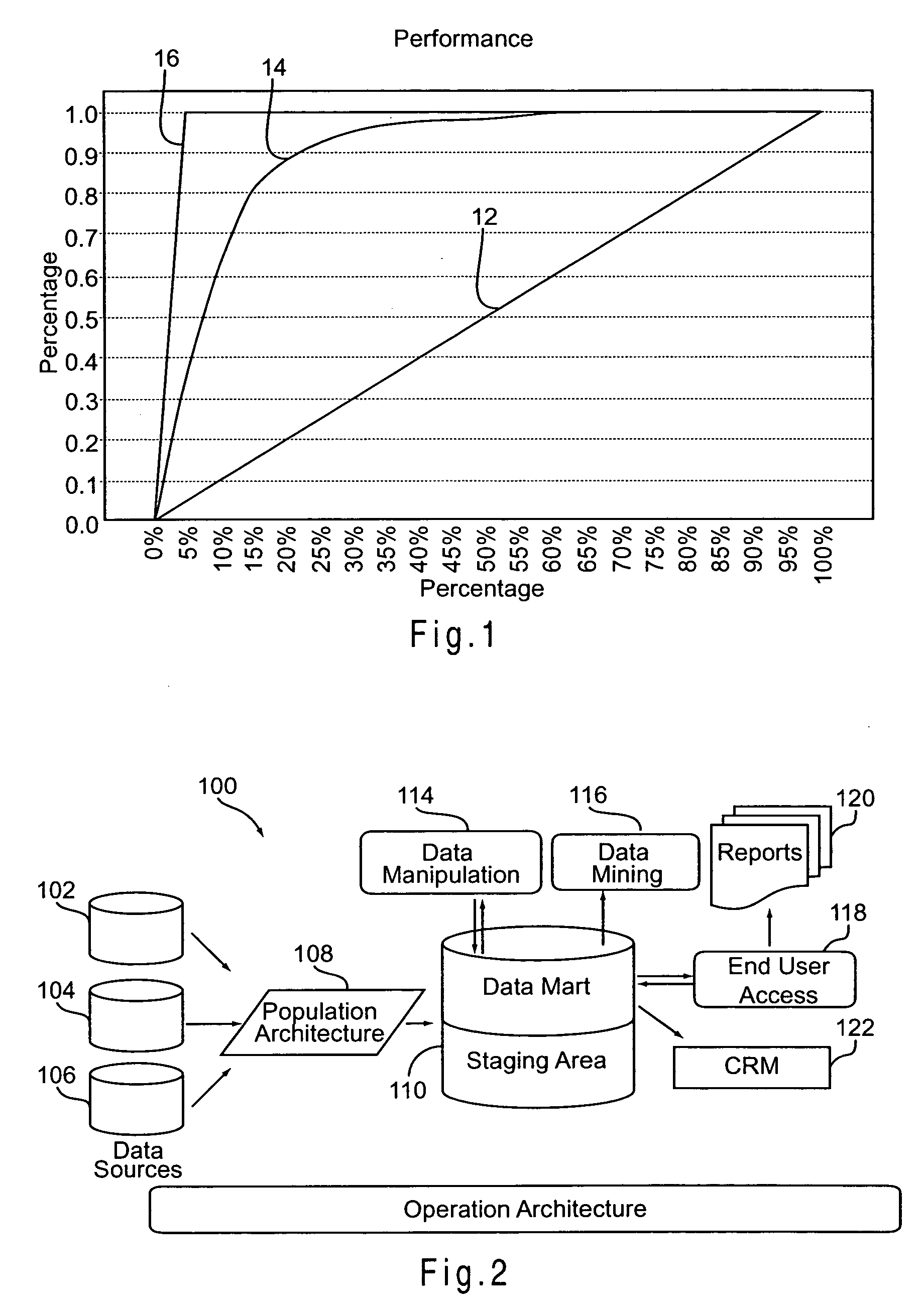
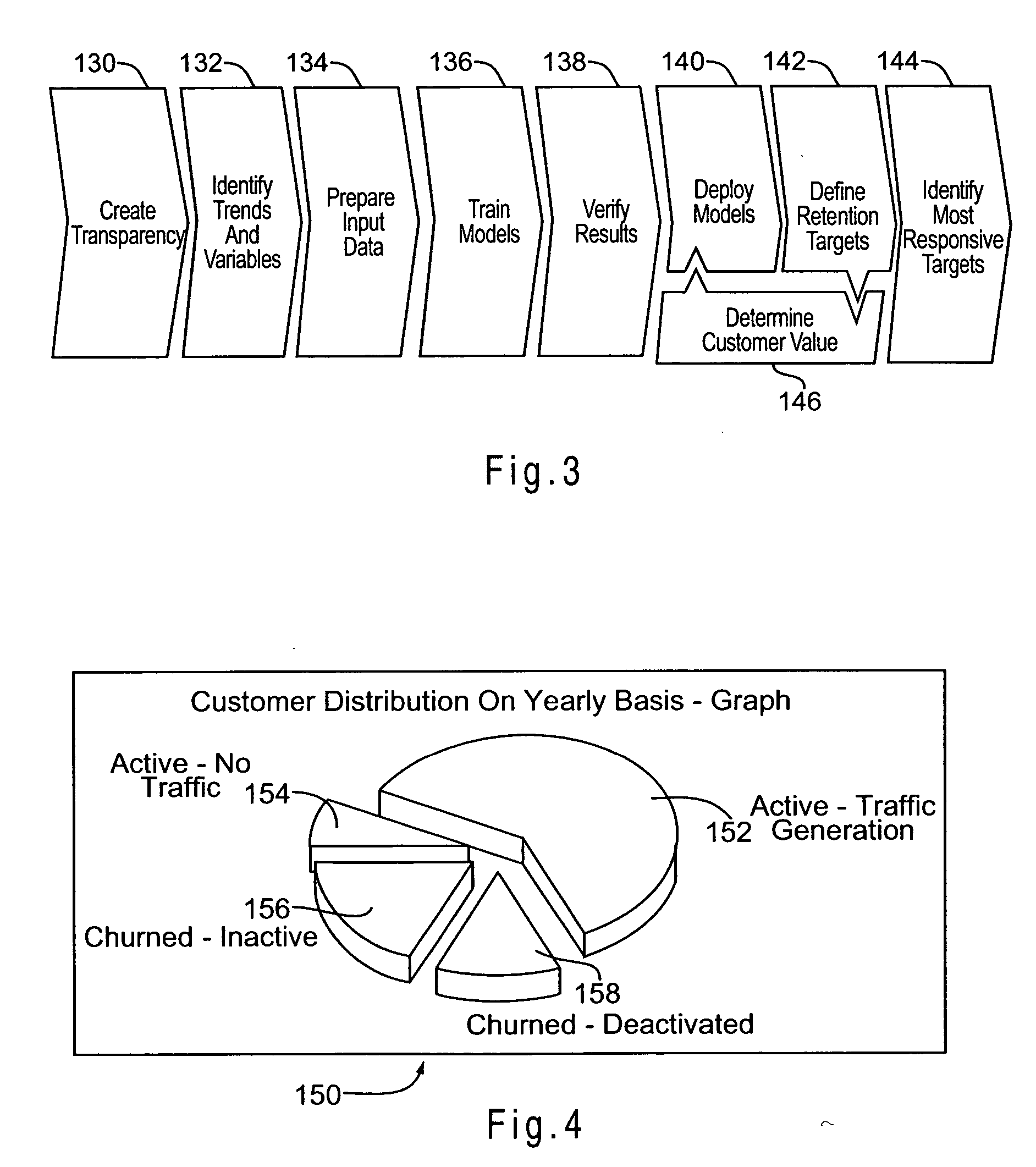
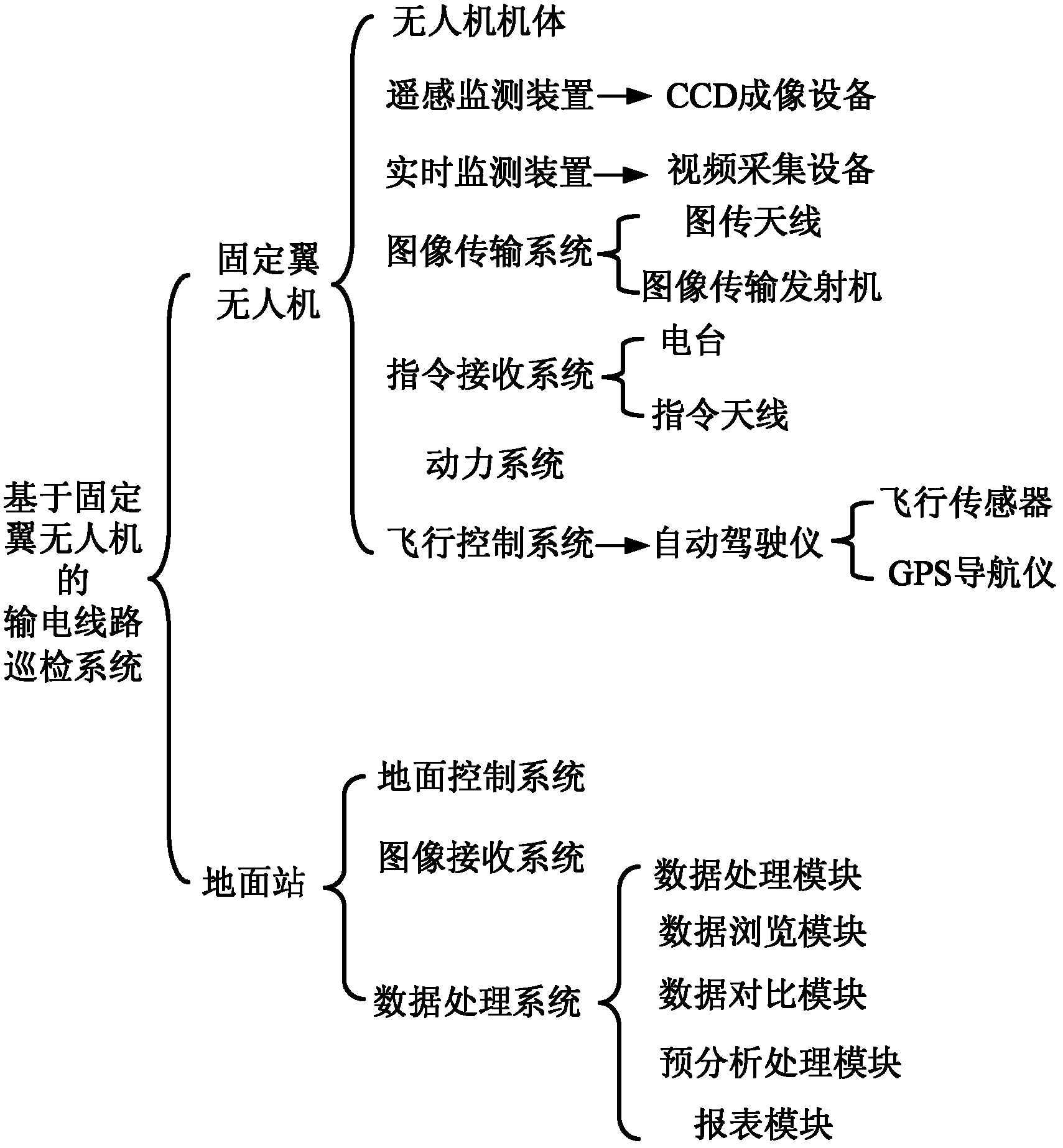
Statistical modeling methods for determining customer distribution by churn probability within a customer population
InactiveUS20070185867A1Avoid erosionFacilitates efforts to retain high profitability customersDatabase queryingMarketingData dredgingCustomer attrition
A system and method for managing churn among the customers of a business is provided. The system and method provide for an analysis of the causes of customer churn and identifies customers who are most likely to churn in the future. Identifying likely churners allows appropriate steps to be taken to prevent customers who are likely to chum from actually churning. The system included a dedicated data mart, a population architecture, a data manipulation module, a data mining tool and an end user access module for accessing results and preparing preconfigured reports. The method includes adopting an appropriate definition of churn, analyzing historical customer to identify significant trends and variables, preparing data for data mining, training a prediction model, verifying the results, deploying the model, defining retention targets, and identifying the most responsive targets.
Owner:ACCENTURE GLOBAL SERVICES LTD
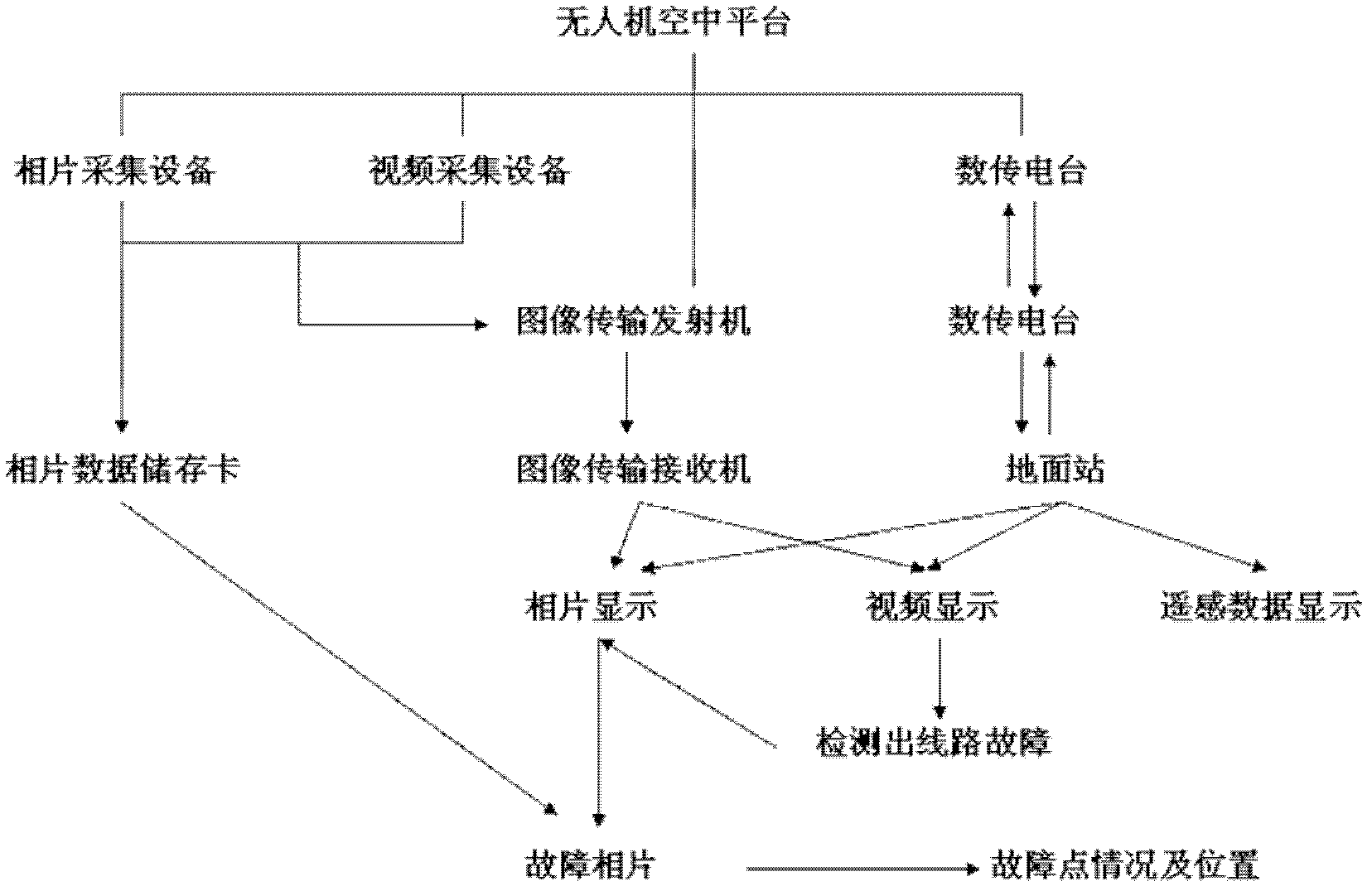
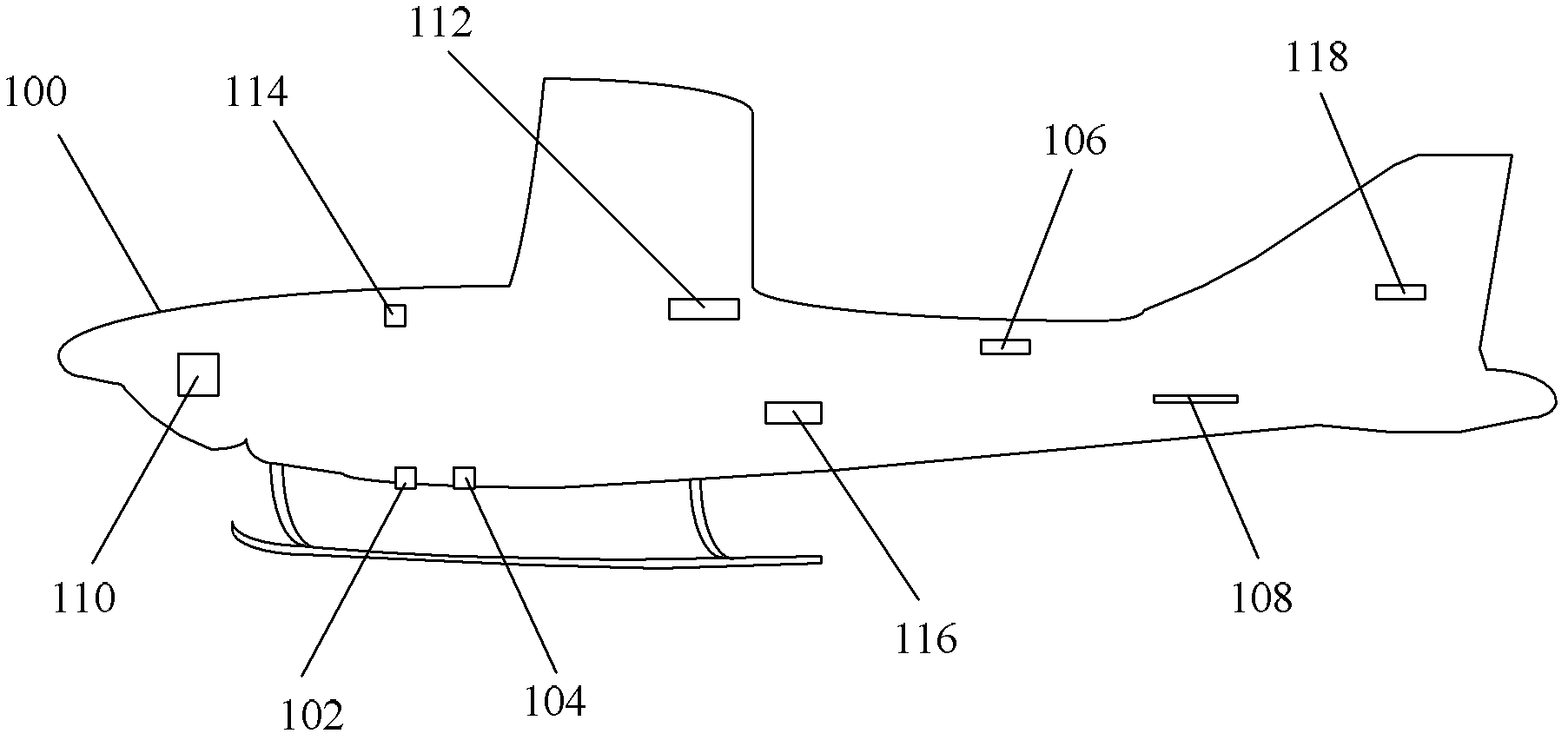
Power transmission line inspection system based on fixed-wing unmanned aerial vehicle
InactiveCN103163881AImprove the effectiveness of inspection workSolve the problem of difficult macro inspectionVehicle position/course/altitude controlPosition/direction controlFly controlEngineering
The invention discloses a power transmission line inspection system based on a fixed-wing unmanned aerial vehicle. The power transmission line inspection system based on the fixed-wing unmanned aerial vehicle comprises a ground station and a fixed-wing unmanned aerial vehicle, wherein the ground station comprises a ground control system, an image receiving system, and a data processing system, the fixed-wing unmanned aerial vehicle comprises an unmanned aerial vehicle body, a remote sensing monitoring device, a real-time detection device, an image transmission system, an instruction receiving system, a power system, and a flying control system. The remote sensing monitoring device is used for collecting image information in an area of a power transmission line at a fixed time or a fixed distance or a fixed spot, the real-time detection device is used for collecting information in the area of the power transmission line in real time, and the remote sensing monitoring device and the real-time detection device are arranged on the unmanned aerial vehicle body in a front-and-back adjacent and direct-to-ground mode. The power transmission line inspection system based on the fixed-wing unmanned aerial vehicle is capable of conducting periodical or emergent macroscopic inspections on the power transmission line and accessory equipment of the power transmission line, so that labor intensity of manual power transmission line inspection work is greatly reduced, and power transmission line inspection efficiency is improved.
Owner:STATE GRID CORP OF CHINA +2
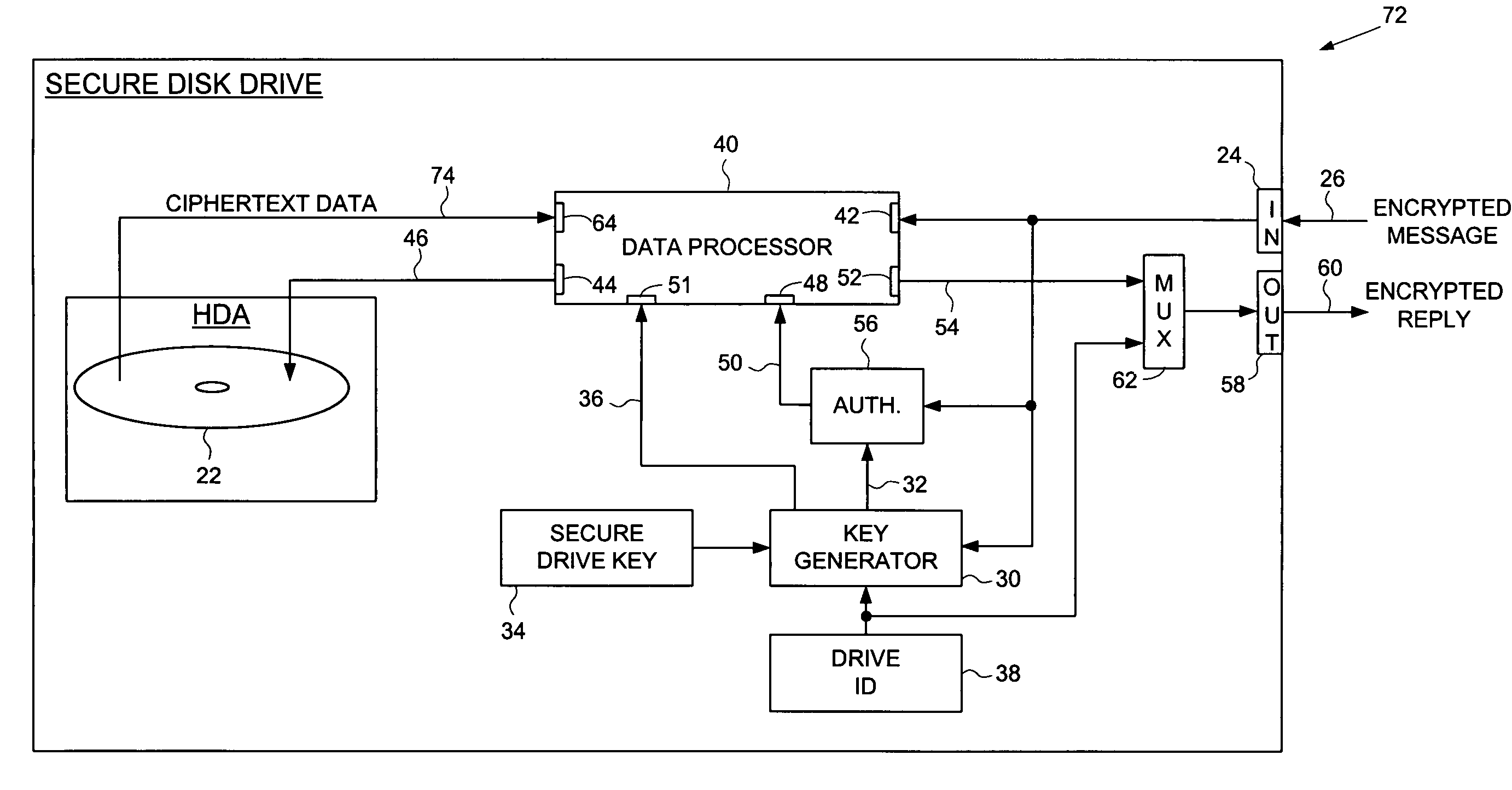
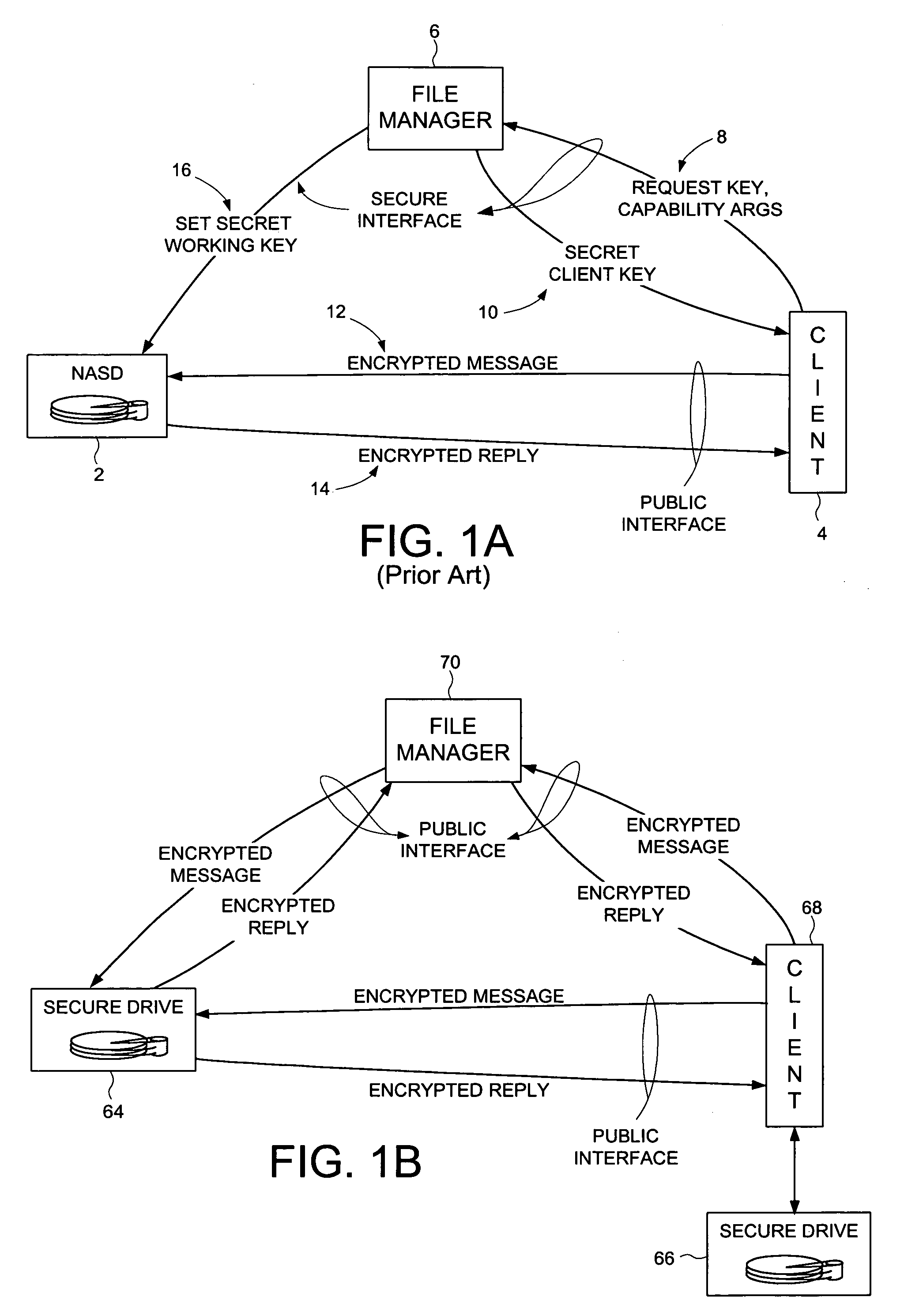
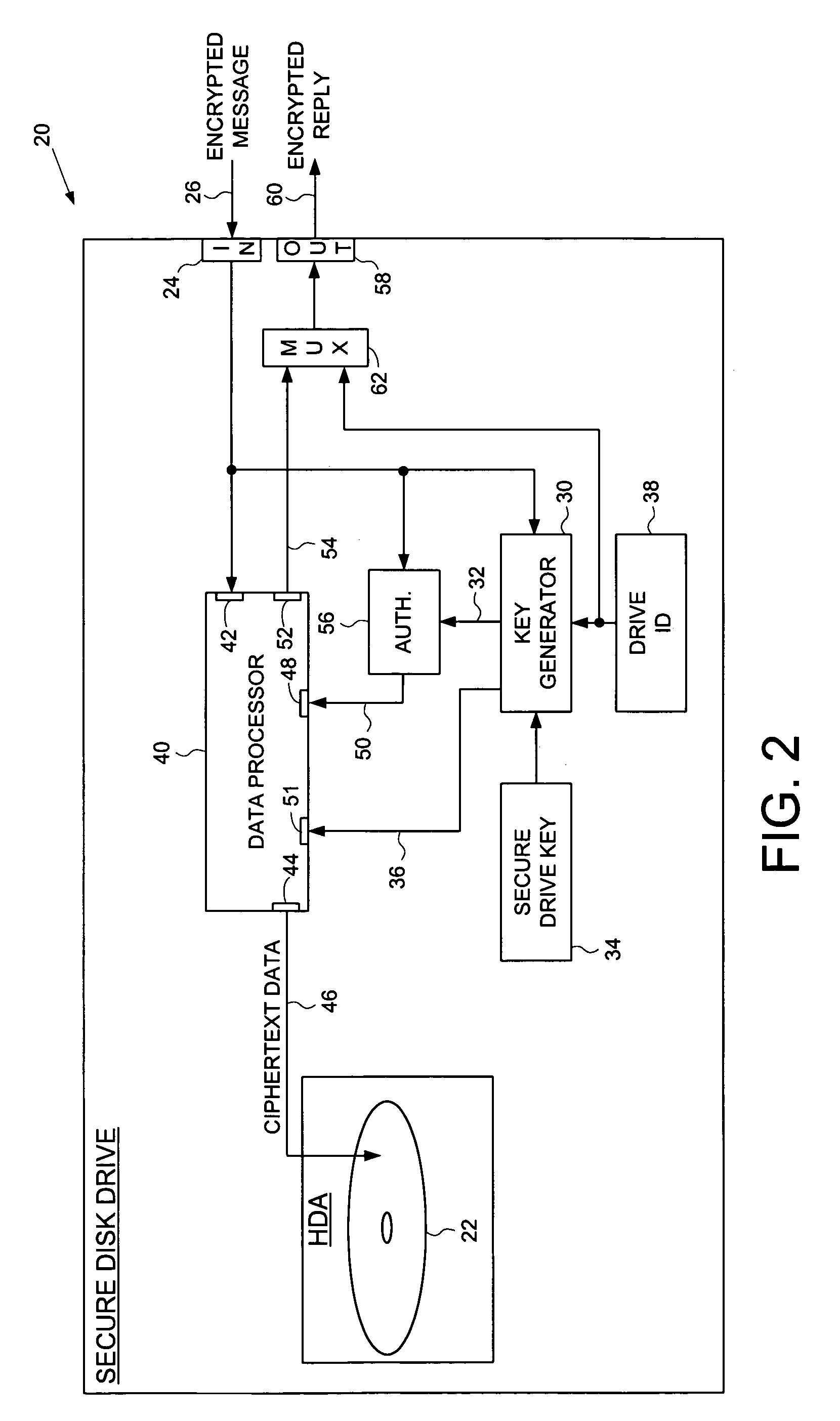
Secure disk drive comprising a secure drive key and a drive ID for implementing secure communication over a public network
InactiveUS7215771B1Volume/mass flow measurementUser identity/authority verificationSecure communicationCiphertext
A secure disk drive is disclosed comprising a disk for storing data, and an input for receiving an encrypted message from a client disk drive, the encrypted message comprising ciphertext data and a client drive ID identifying the client disk drive. The secure disk drive comprises a secure drive key and an internal drive ID. A key generator within the secure disk drive generates a client drive key based on the client drive ID and the secure drive key, and an internal drive key based on the internal drive ID and the secure drive key. The secure disk drive further comprises an authenticator for verifying the authenticity of the encrypted message and generating an enable signal, the authenticator is responsive to the encrypted message and the client drive key. The secure disk drive further comprises a data processor comprising a message input for receiving the encrypted message from the client disk drive, and a data output for outputting the ciphertext data to be written to the disk. The data processor further comprises an enable input for receiving the enable signal for enabling the data processor, and a key input for receiving the internal drive key, the internal drive key for use in generating a message authentication code. The data processor outputs reply data comprising the message authentication code. The secure disk drive outputs a reply to the client disk drive, the reply comprising the reply data and the internal drive ID.
Owner:WESTERN DIGITAL TECH INC
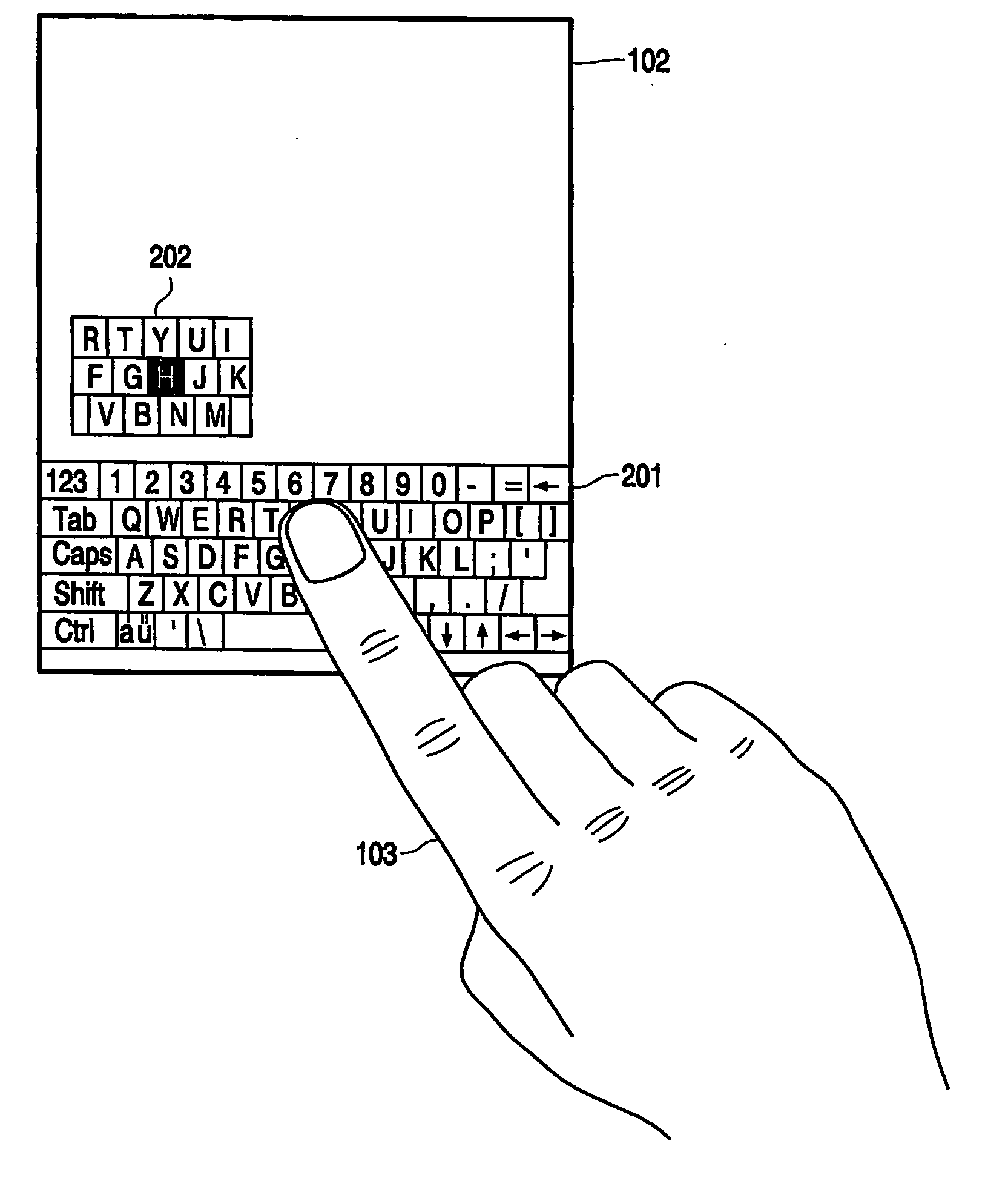
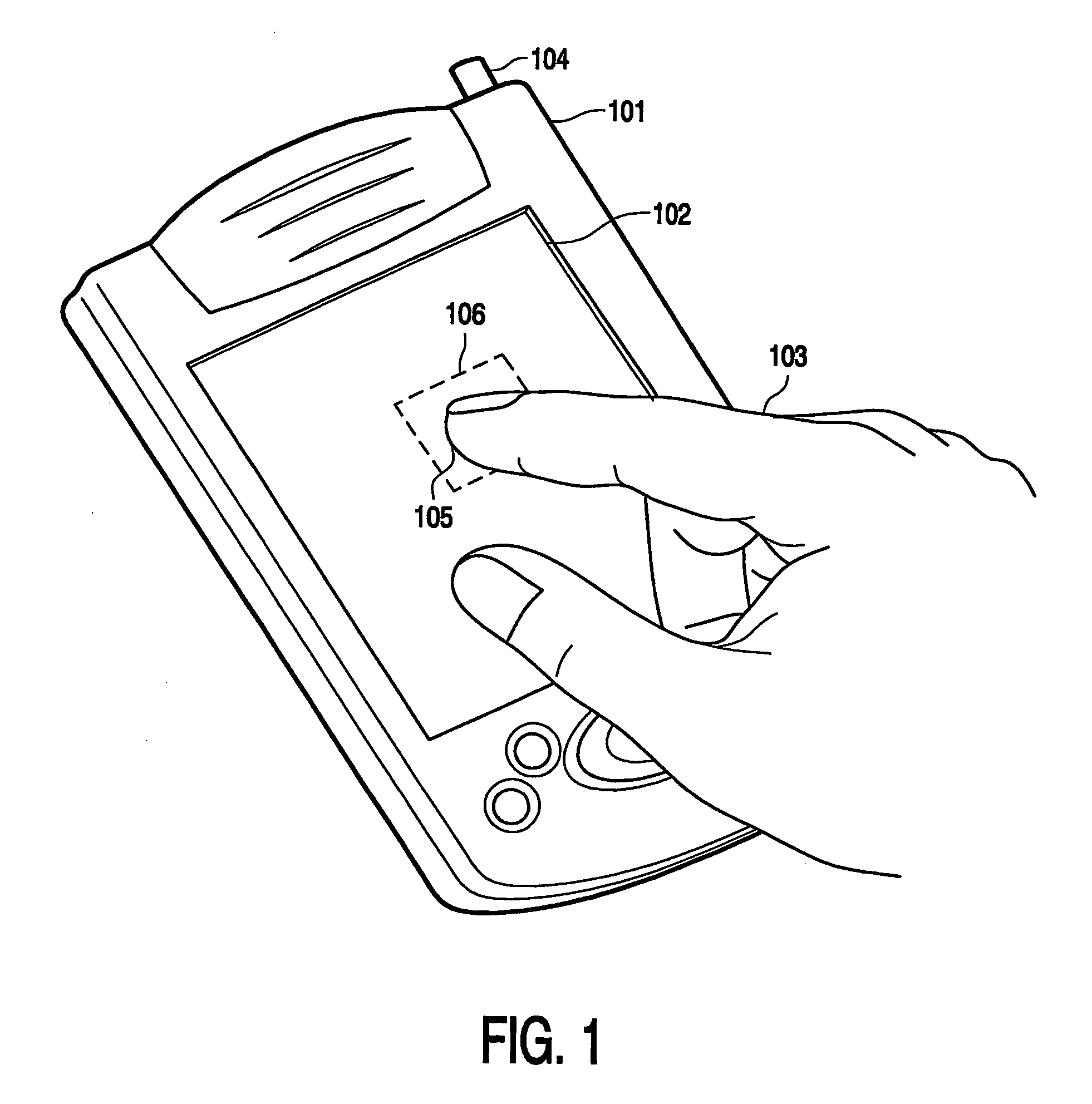
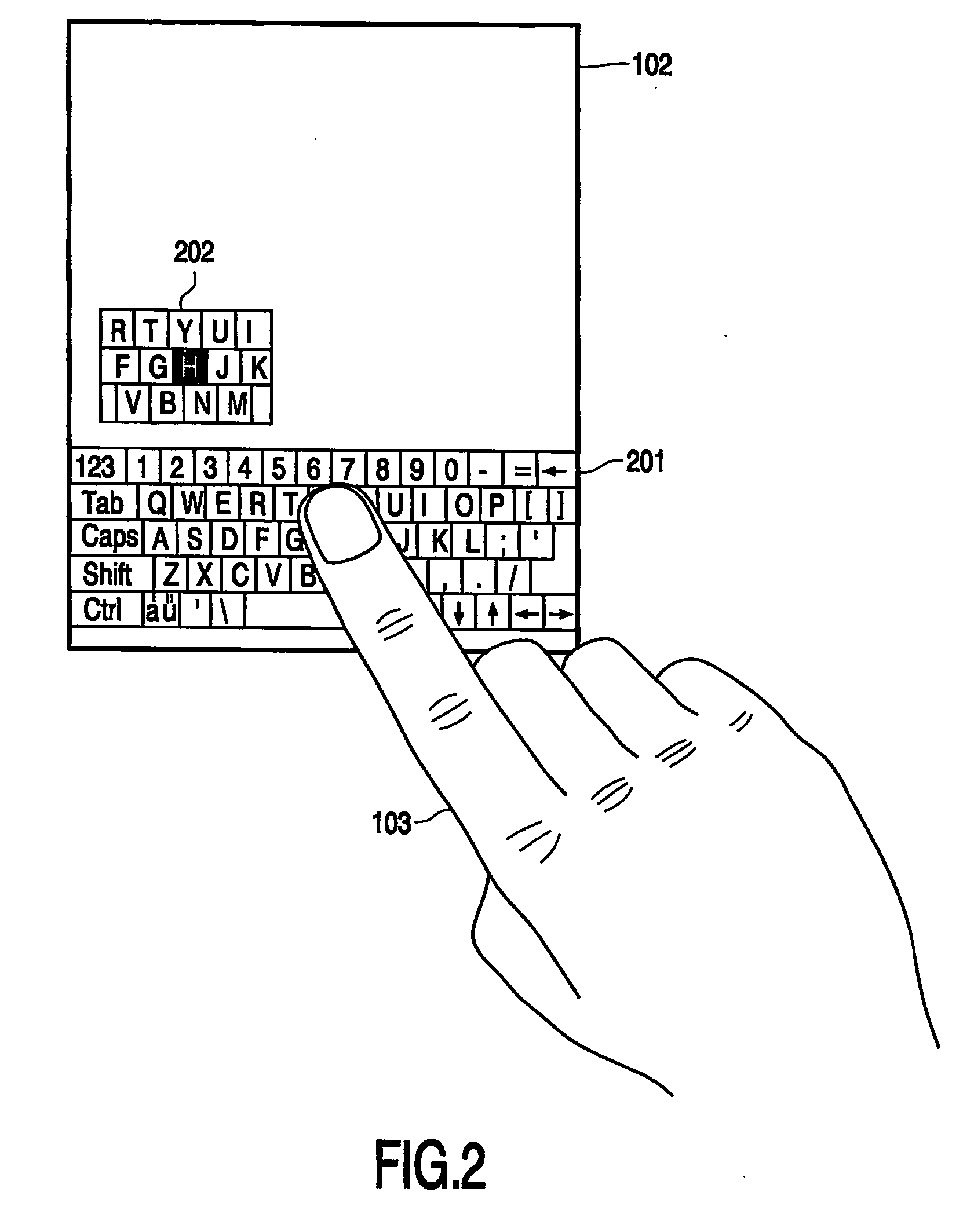
User interface with displaced representation of touch area
ActiveUS20060161846A1Clear overviewAvoid positioningInput/output for user-computer interactionDigital data processing detailsData processing systemGraphics
The invention relates to a data processing system comprising a display screen (102), a graphical user interface for displaying objects on the display screen, and detection means (102) for detecting a touch position of a pointing object (103) on the display screen. The detection means (102) is capable of measuring a distance between the pointing object and the display screen. A property of the displayed objects is dependent on the measured distance between the pointing object and the display screen.
Owner:KONINKLIJKE PHILIPS ELECTRONICS NV
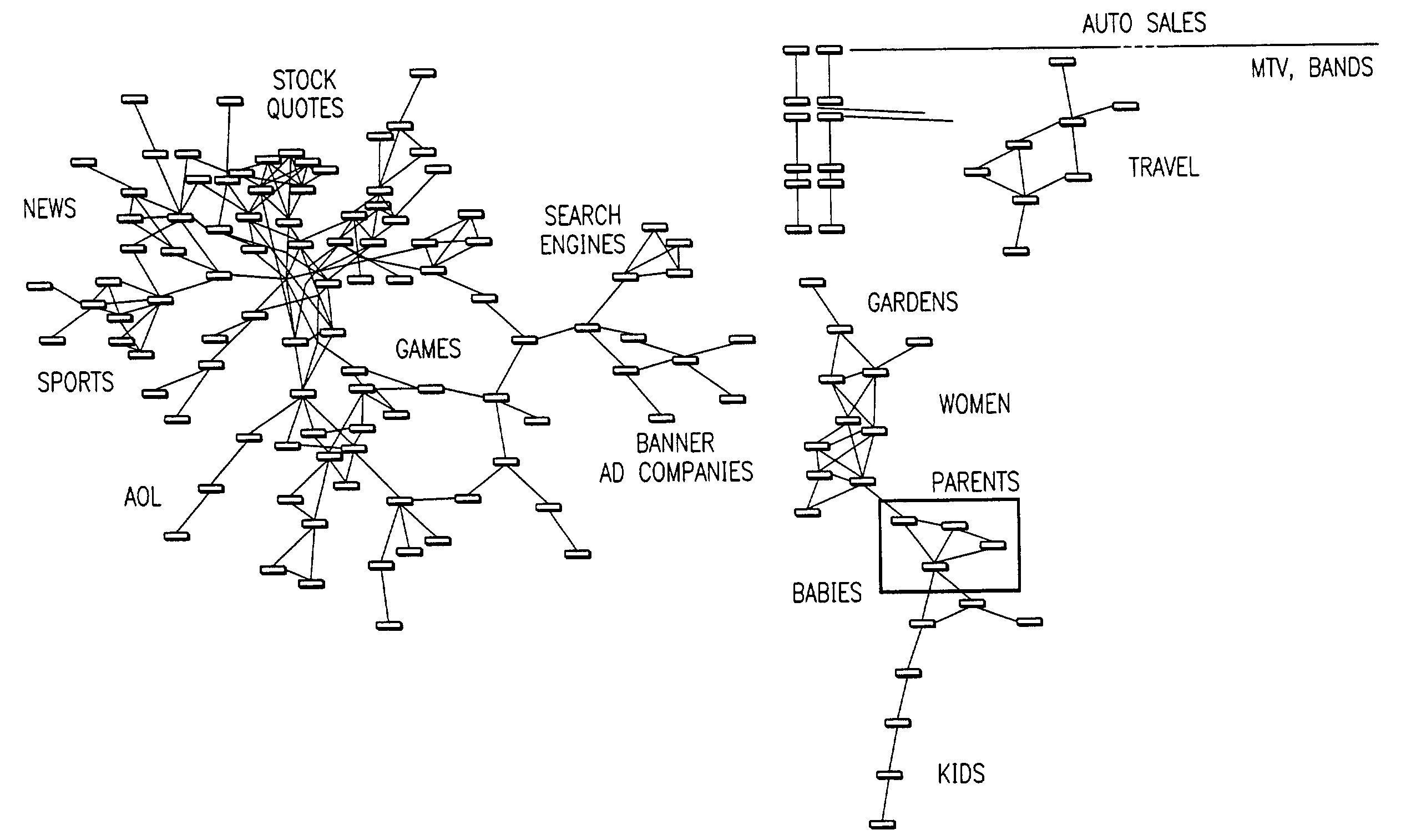
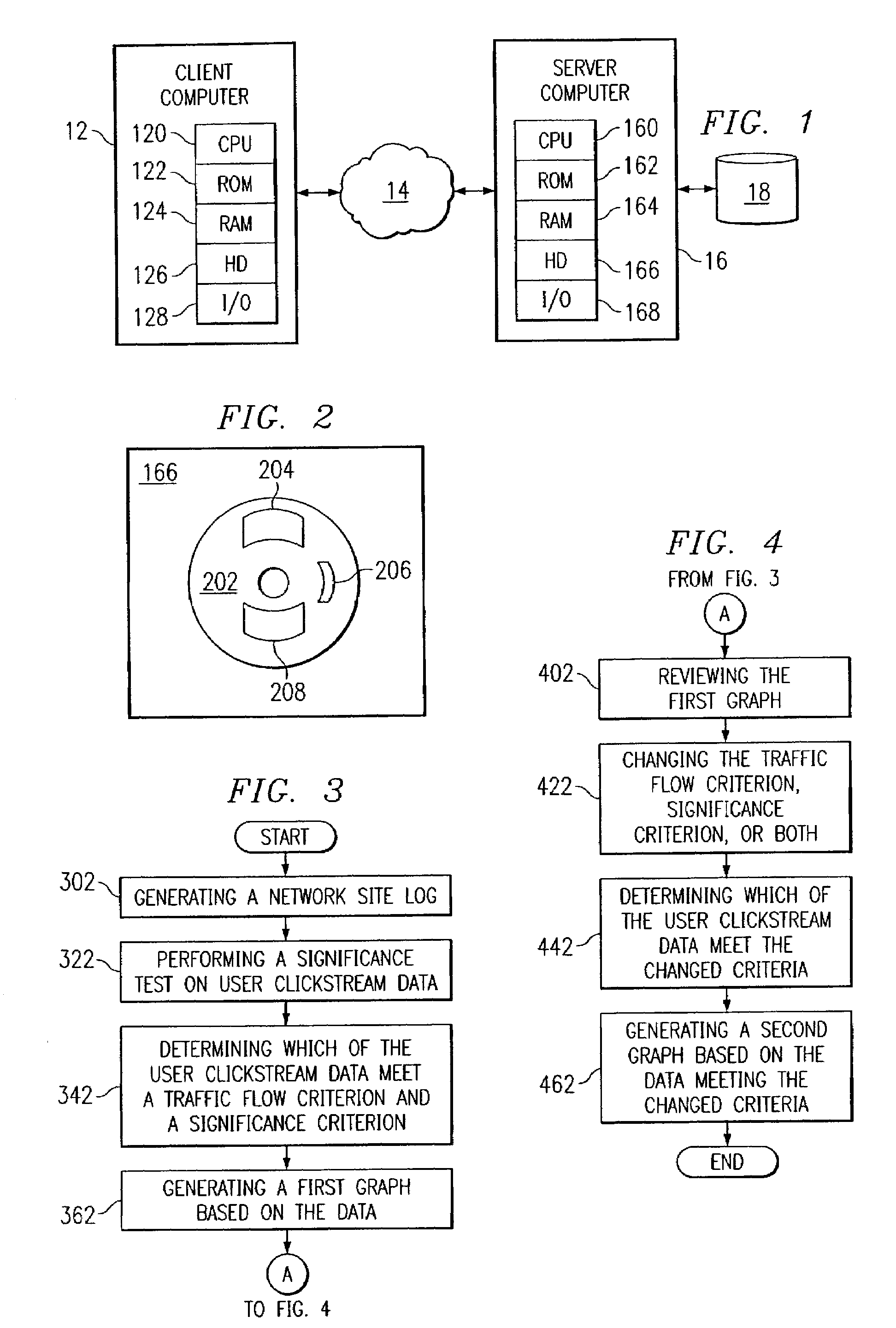
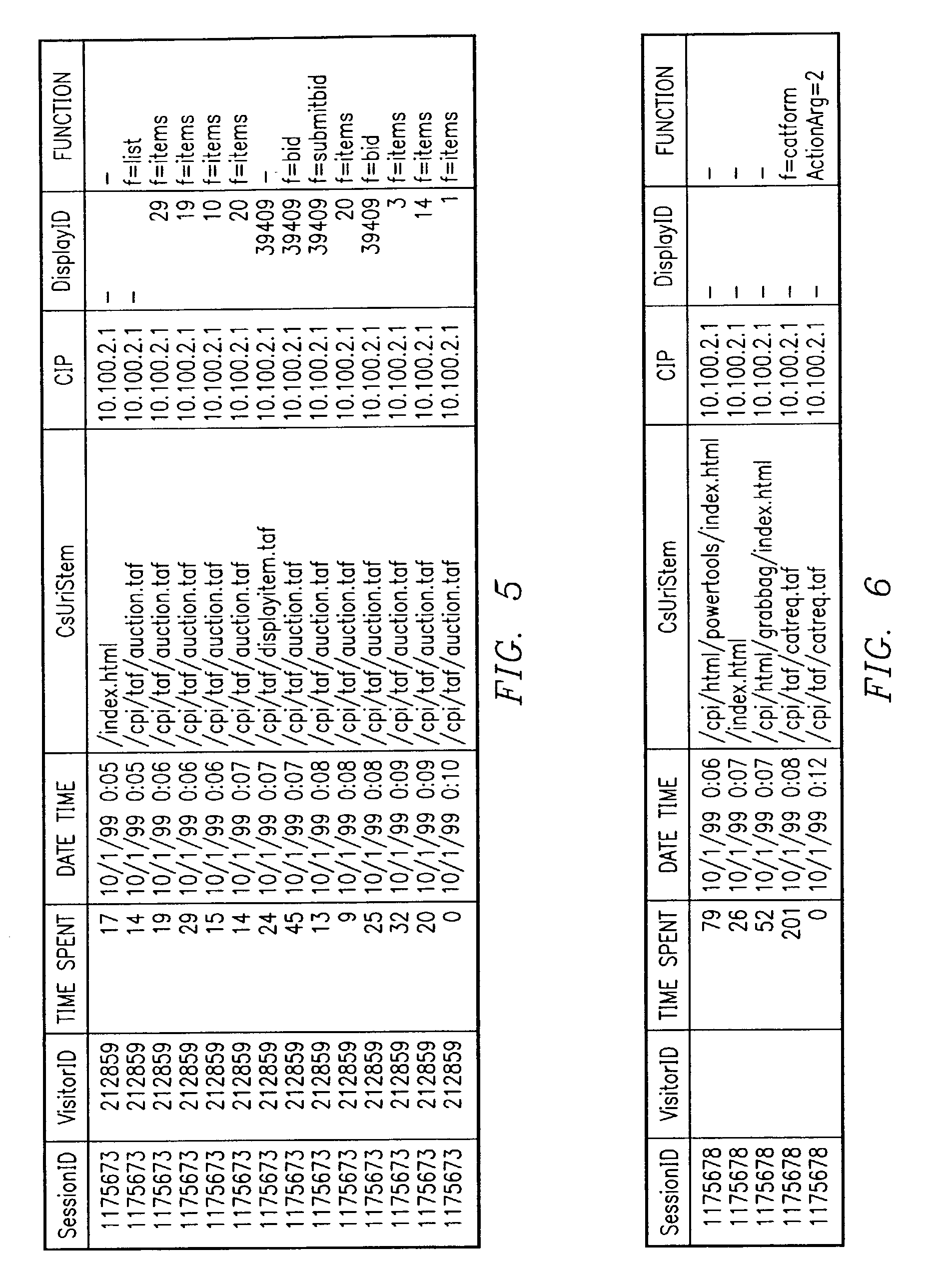
Visualization and analysis of user clickpaths
Methods and data processing system readable media have been created to graph user clickstream data over a network or at a network site to yield meaningful and visually esthetic information. In one set of embodiments, the method can comprise (i) performing a significance test on data from a network log and generating significance results. The method can also comprise (ii) determining which of network addresses and clicktrails between network addresses meet a traffic flow criterion. The data that meet a significance criterion, traffic criterion, or both can form (iii) graphable addresses and relationships. The method can further comprise (iv) generating statistics about the graphable addresses and relationships. The method can still further comprise (v) generating a graph based on the statistics about the graphable addresses and relationships, and (vi) changing any or all of the traffic flow, significance criterion, and statistics being computed, and regenerating the graph.
Owner:OPEN TEXT SA ULC
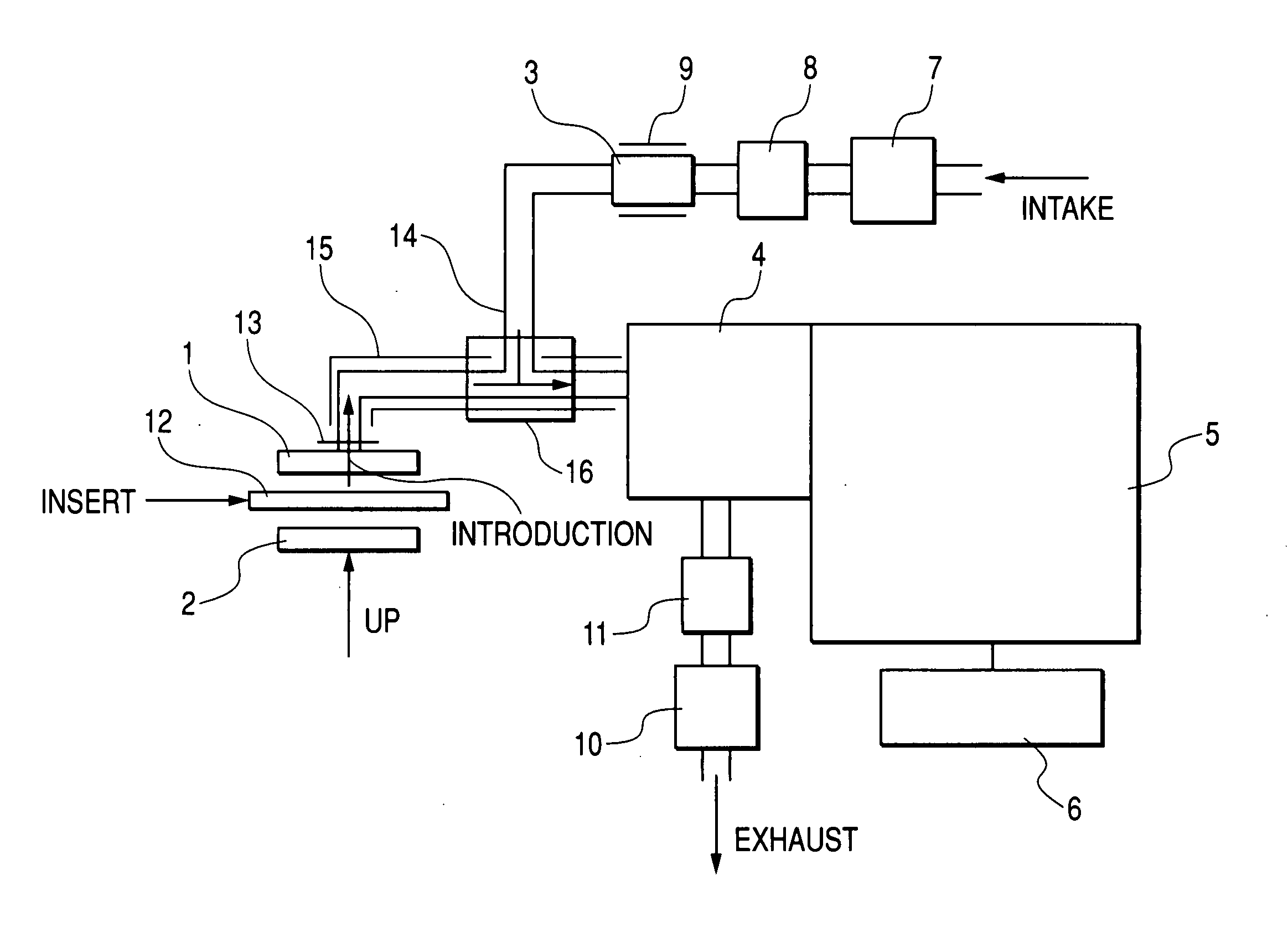
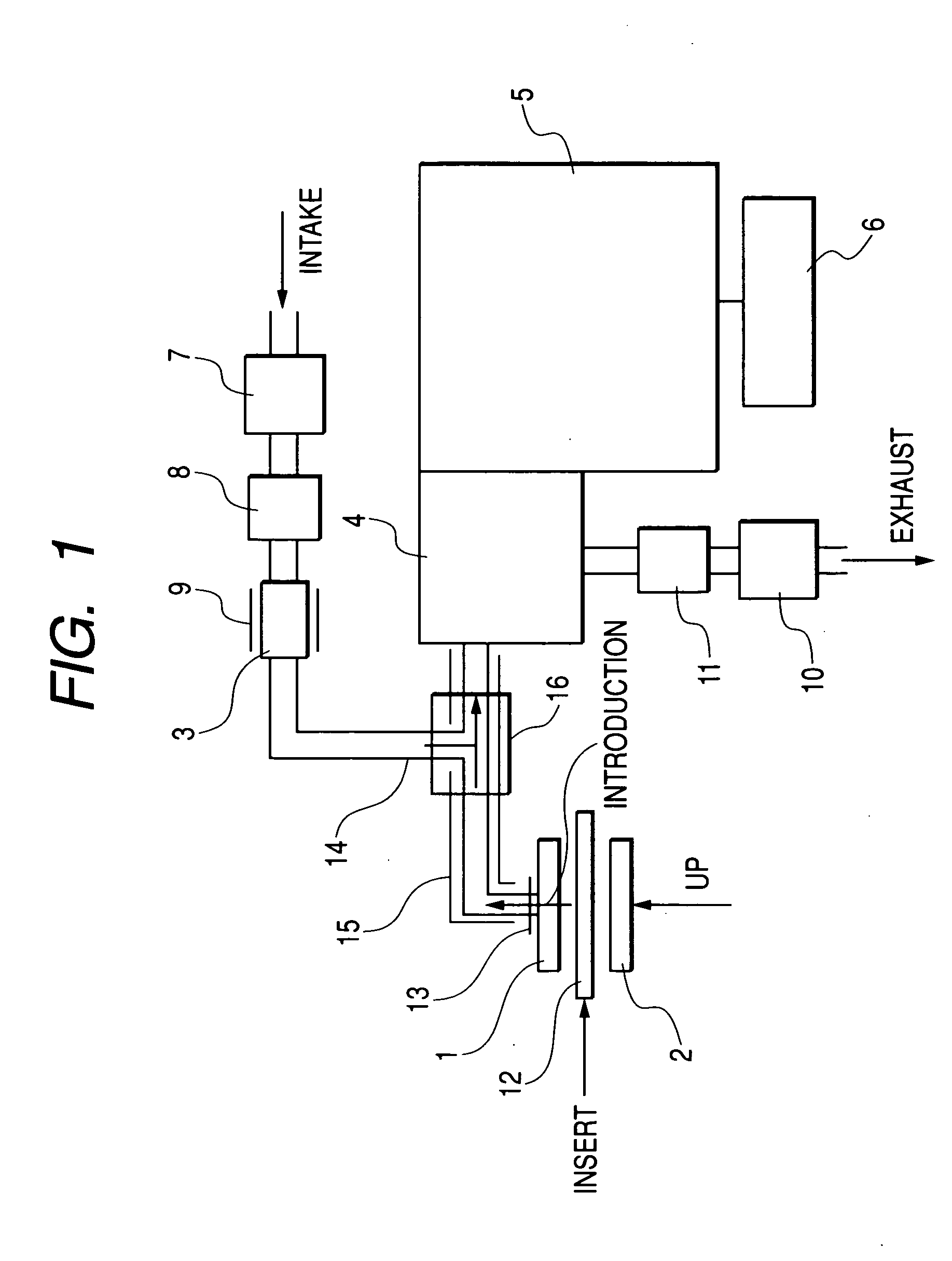
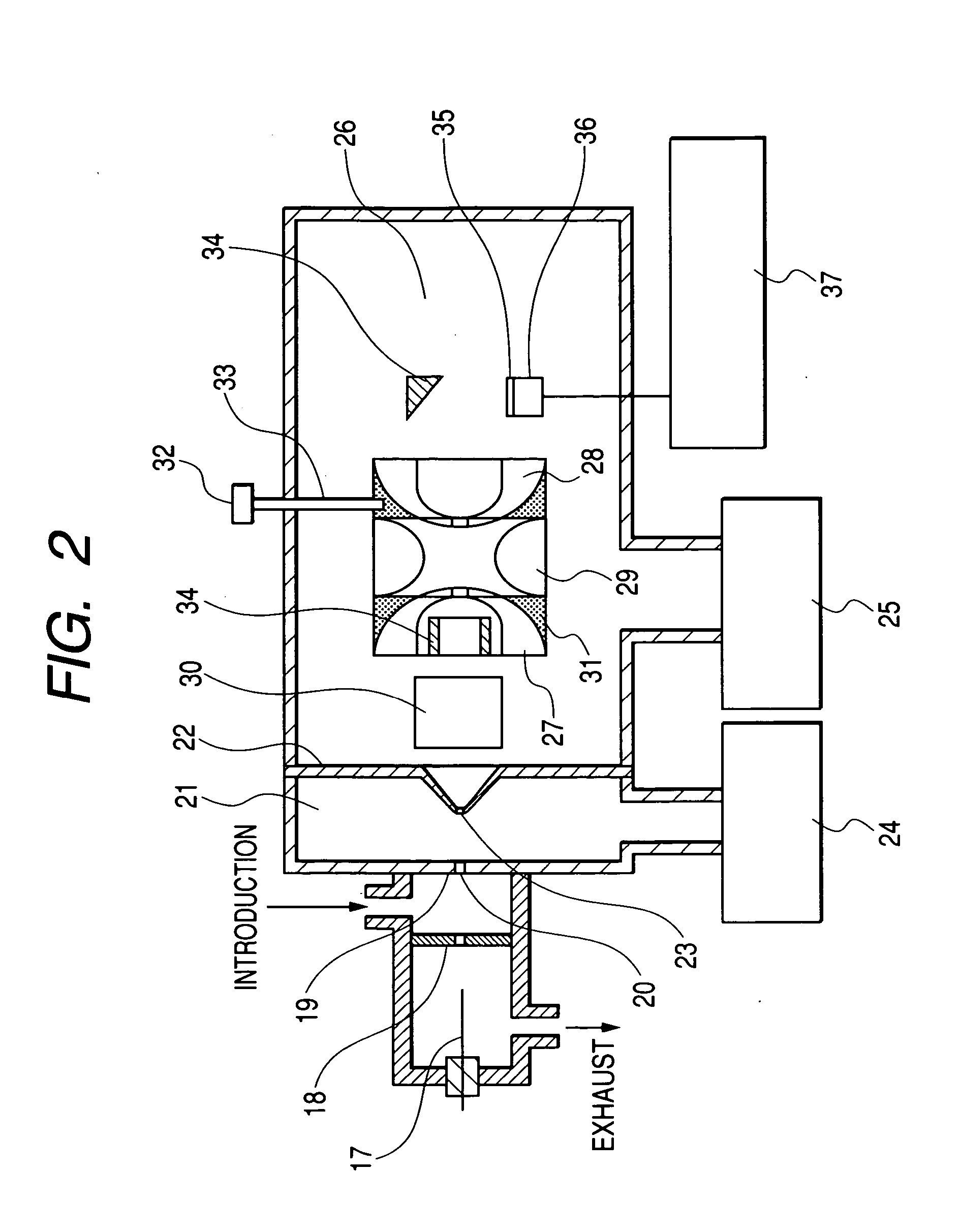
Apparatus for detecting chemical substances and method therefor
ActiveUS20050061964A1High detection sensitivityPrevent false detectionStability-of-path spectrometersAnalysis using chemical indicatorsNon detectionData treatment
An apparatus for detecting chemical substances which is high in sensitivity and selectivity is provided. An organic acid or an organic acid salt is used to generate an organic acid gas from an organic acid gas generator 3 to be mixed with a sample gas for introduction into an ion source 4 for ionization, thereby obtaining a mass spectrum by a mass analysis region 5. A data processor 6 determines the detection or non-detection of a specific m / z of an organic acid adduct ion obtained by adding a molecule generated from the organic acid to a molecule with specific m / z generated from a target chemical substance to be detected based on the obtained mass spectrum. When there is an ion peak with the m / z of the organic acid adduct ion, the presence of the target chemical substance to be detected is determined, and an alarm is sounded. False detection can be prevented.
Owner:HITACHI LTD
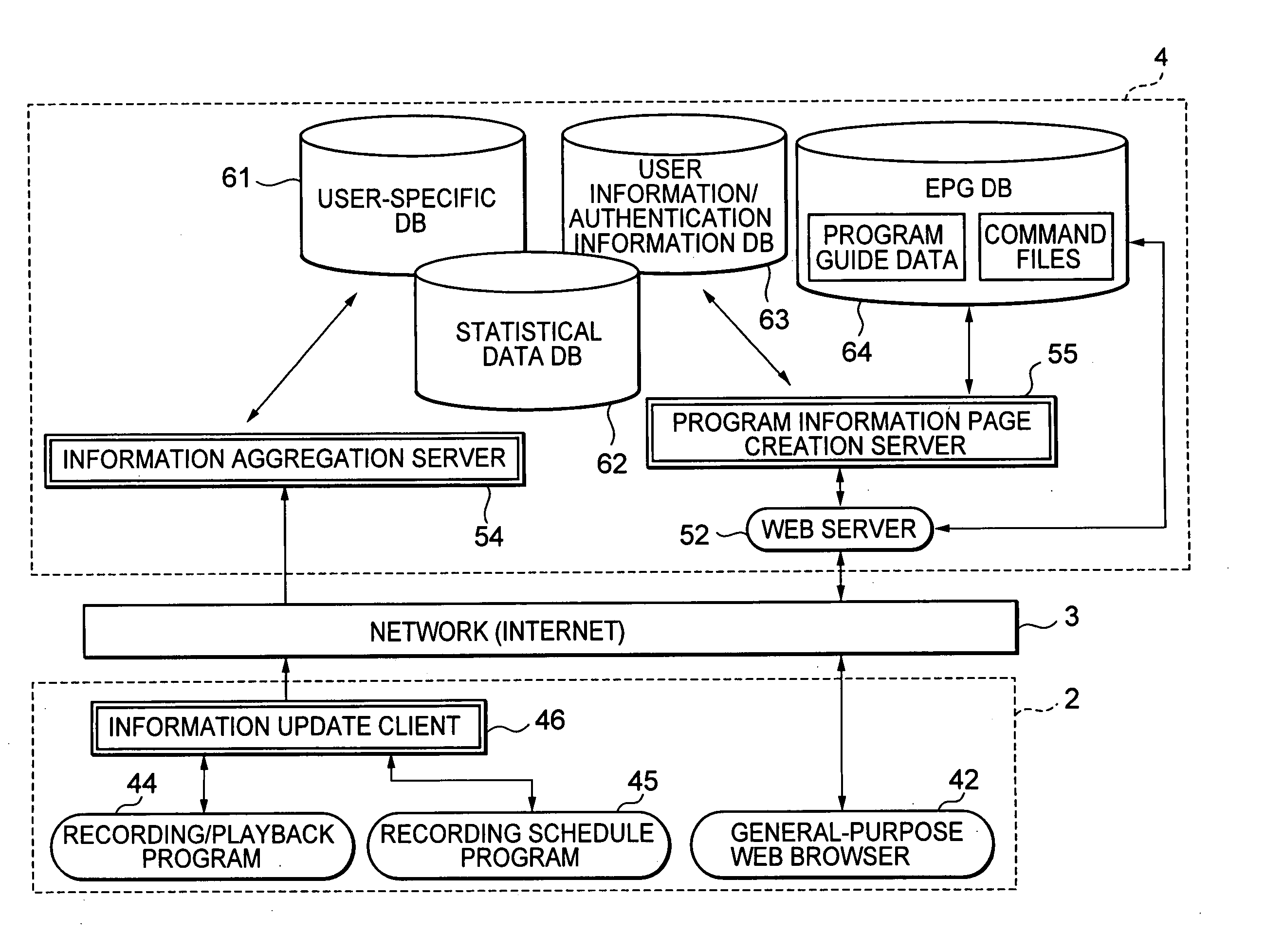
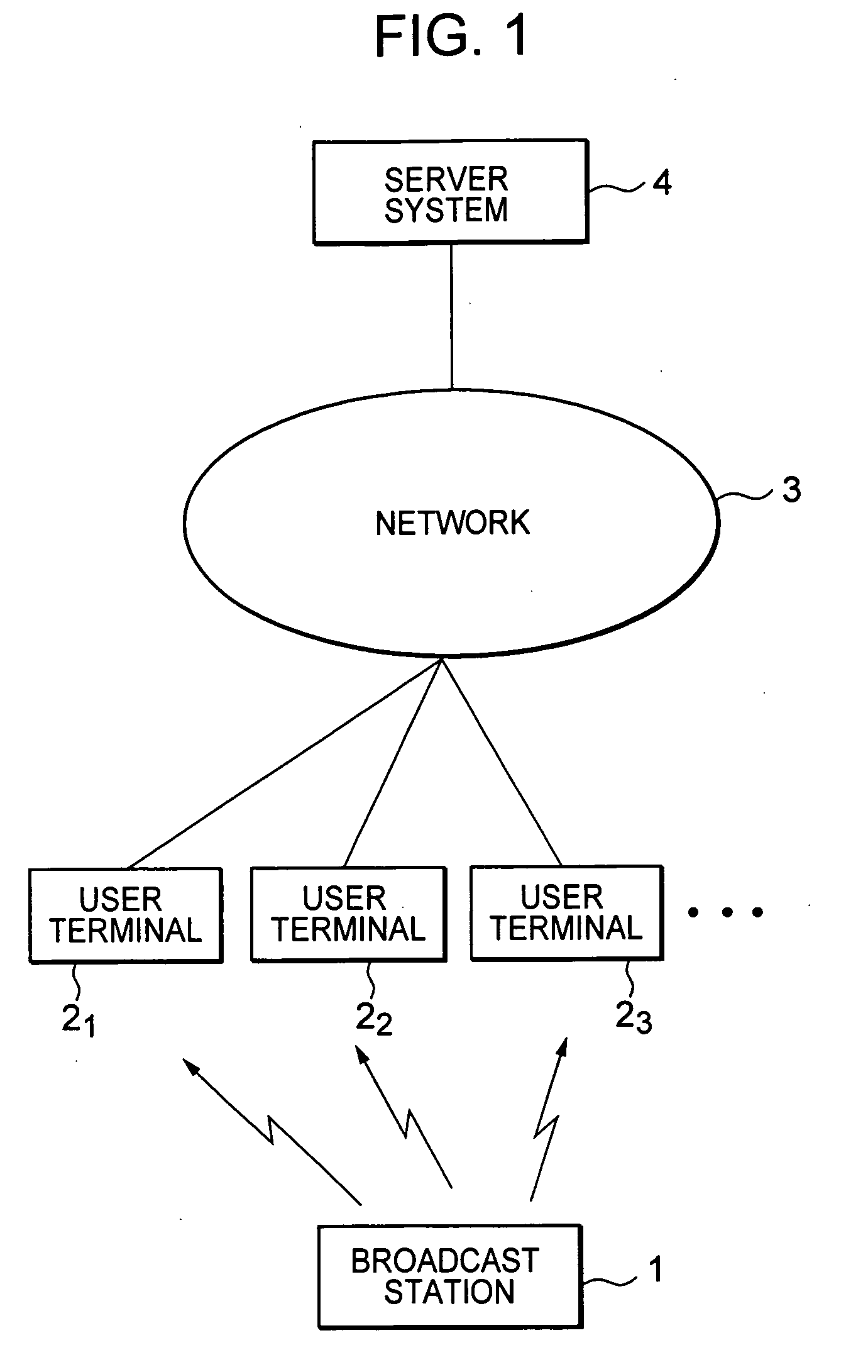
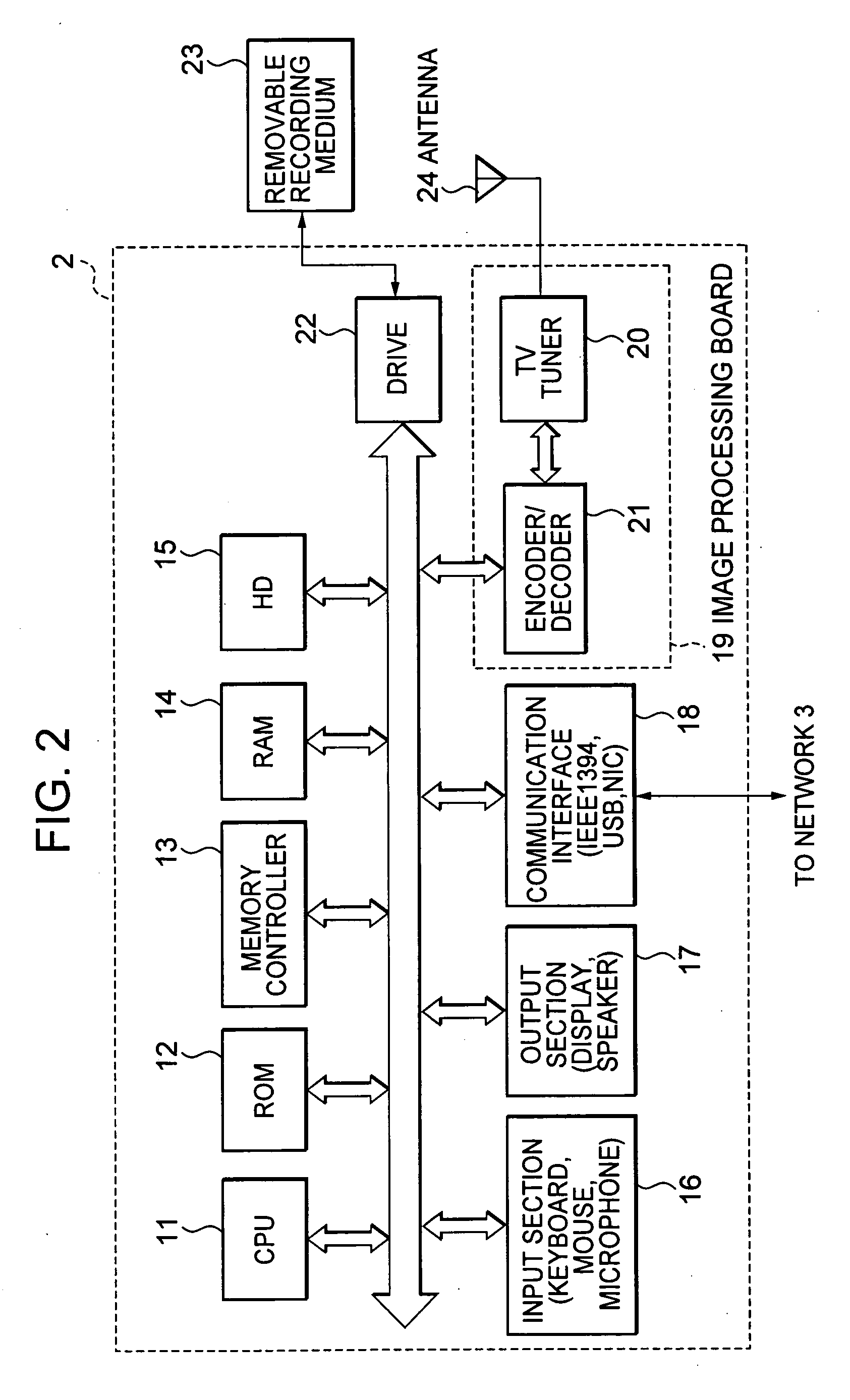
Data processing apparatus, data processing method and program, and data processing system
InactiveUS20060010470A1Facilitate decision-makingTelevision system detailsSpecific information broadcast systemsData processing systemHandling system
The present invention relates to a data processing apparatus, a data processing method and a program, and a data processing system which are configured to provide an EPG as a user interface that further facilitates decision on whether to view or record a program. By aggregating information uploaded from a user side, statistical data, such as the number of persons who viewed a program during its broadcast time, an audience rating of a program during its broadcast time, or a good impression level representing how the user feels about a program, are calculated, whereby an EPG page is automatically generated in which the statistical data and program guide data that gives guidance on programs are superimposed. The present invention is applicable to, e.g., a broadcasting system that broadcast television broadcasting programs.
Owner:SONY CORP
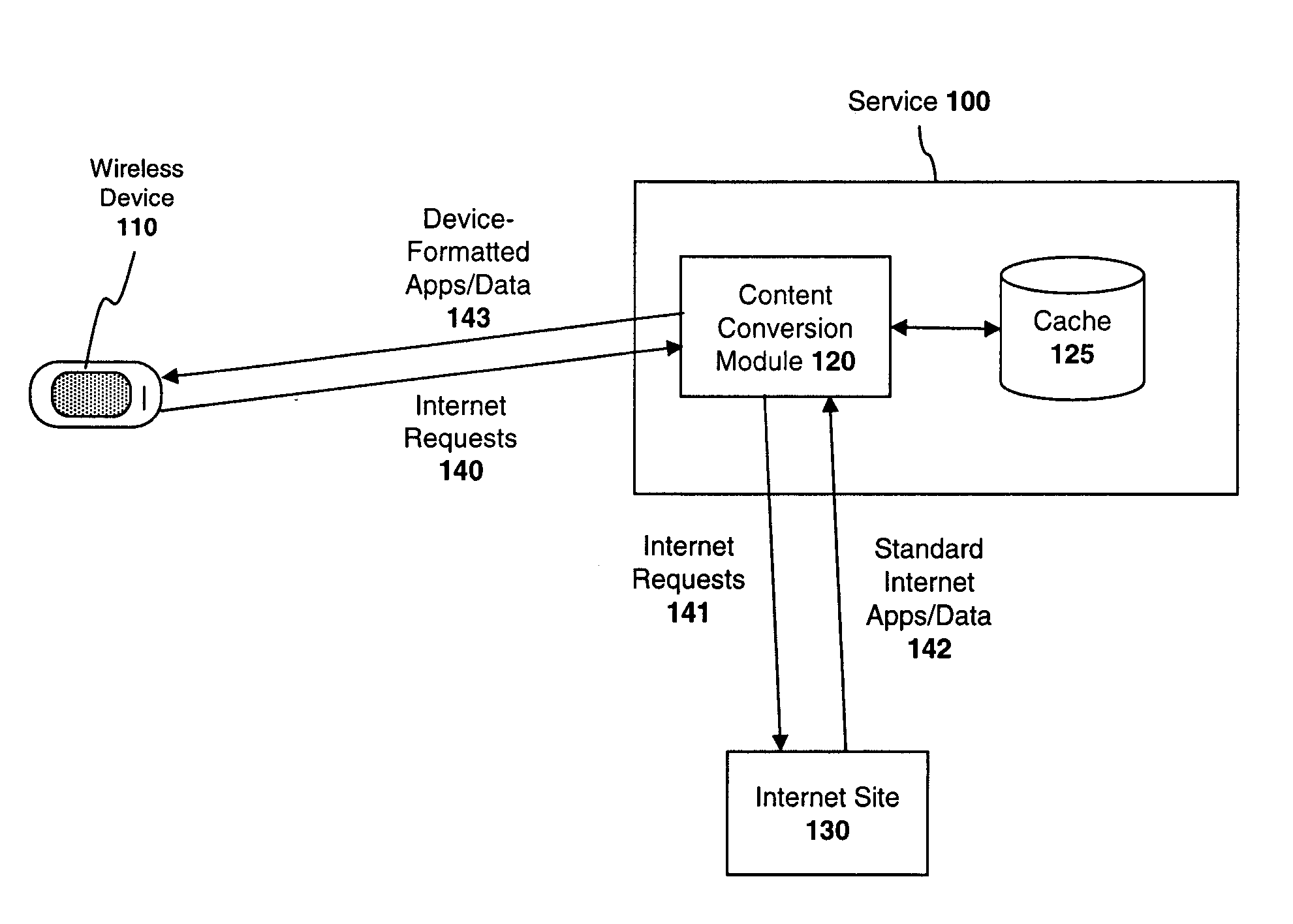
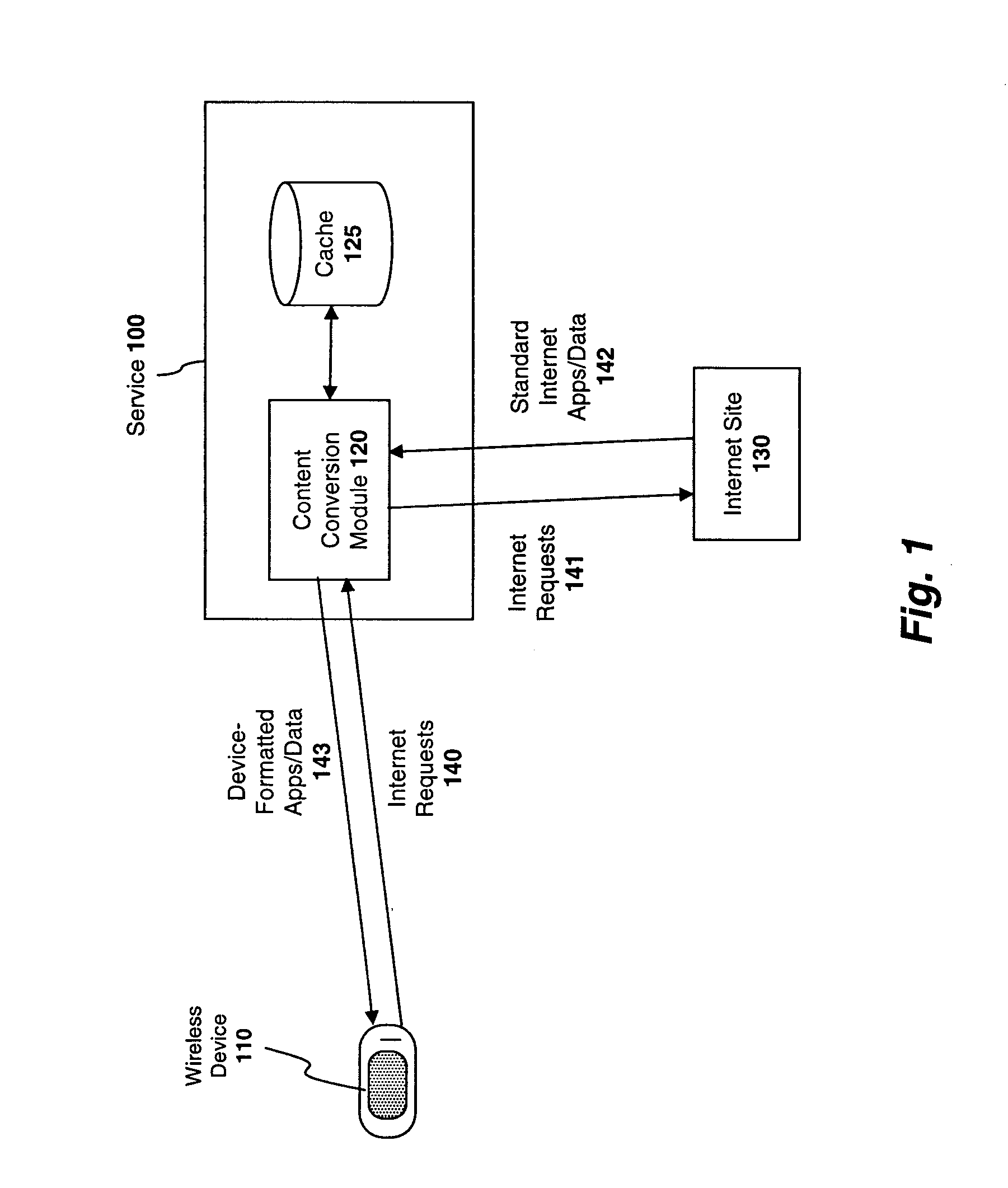
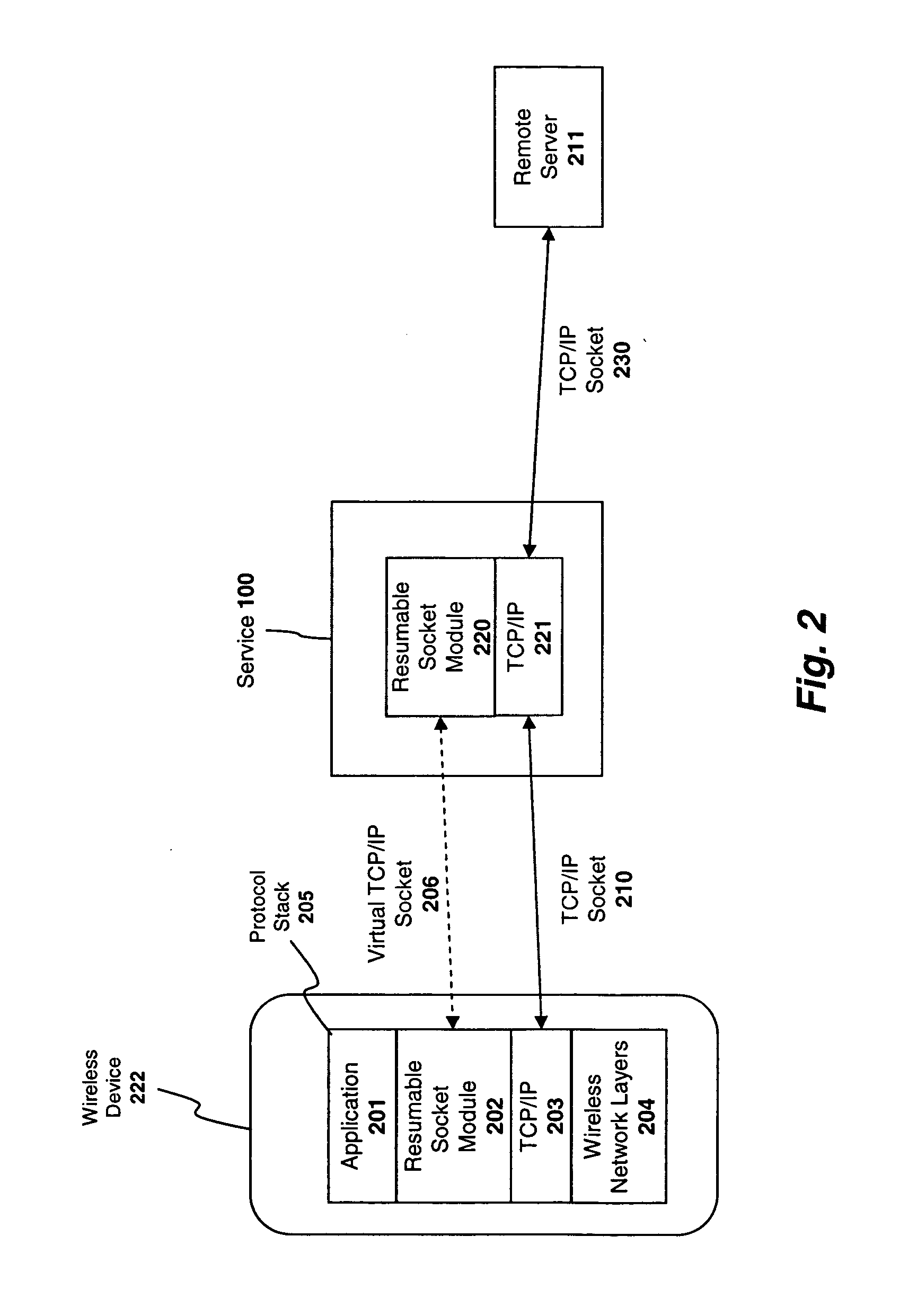
System and method for preserving socket connections over a wireless network
InactiveUS20090103515A1Time-division multiplexWireless commuication servicesNetworking protocolService provision
A system, apparatus, and method for maintaining a socket connection over a wireless network. For example, one embodiment of the invention is a wireless data processing device for emulating a socket connection comprising: a wireless radio for establishing a wireless communication channel with a wireless service provider over a wireless network; a network protocol stack including at least one layer configured to establish a socket connection with a remote server over the wireless network, the network protocol stack further including an application layer for executing applications capable of transmitting and receiving data over the socket connection; and a resumable socket module configured to emulate an open socket connection transparently to applications within the application layer, even when the wireless communication channel is temporarily lost, the resumable socket module counting a number of bytes transmitted or to be transmitted to the remote server and maintaining a buffer containing the bytes transmitted or to be transmitted.
Owner:MICROSOFT TECH LICENSING LLC
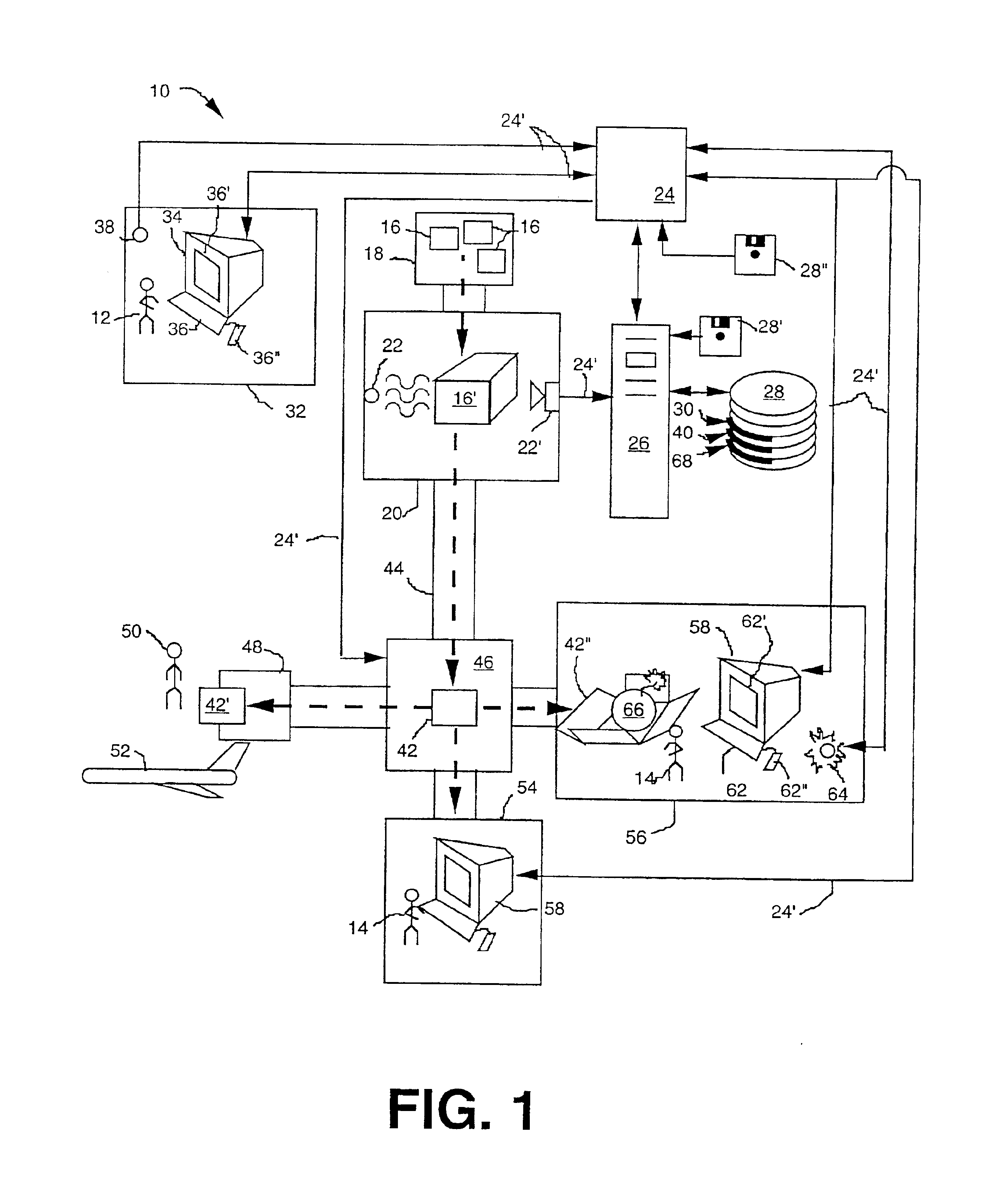
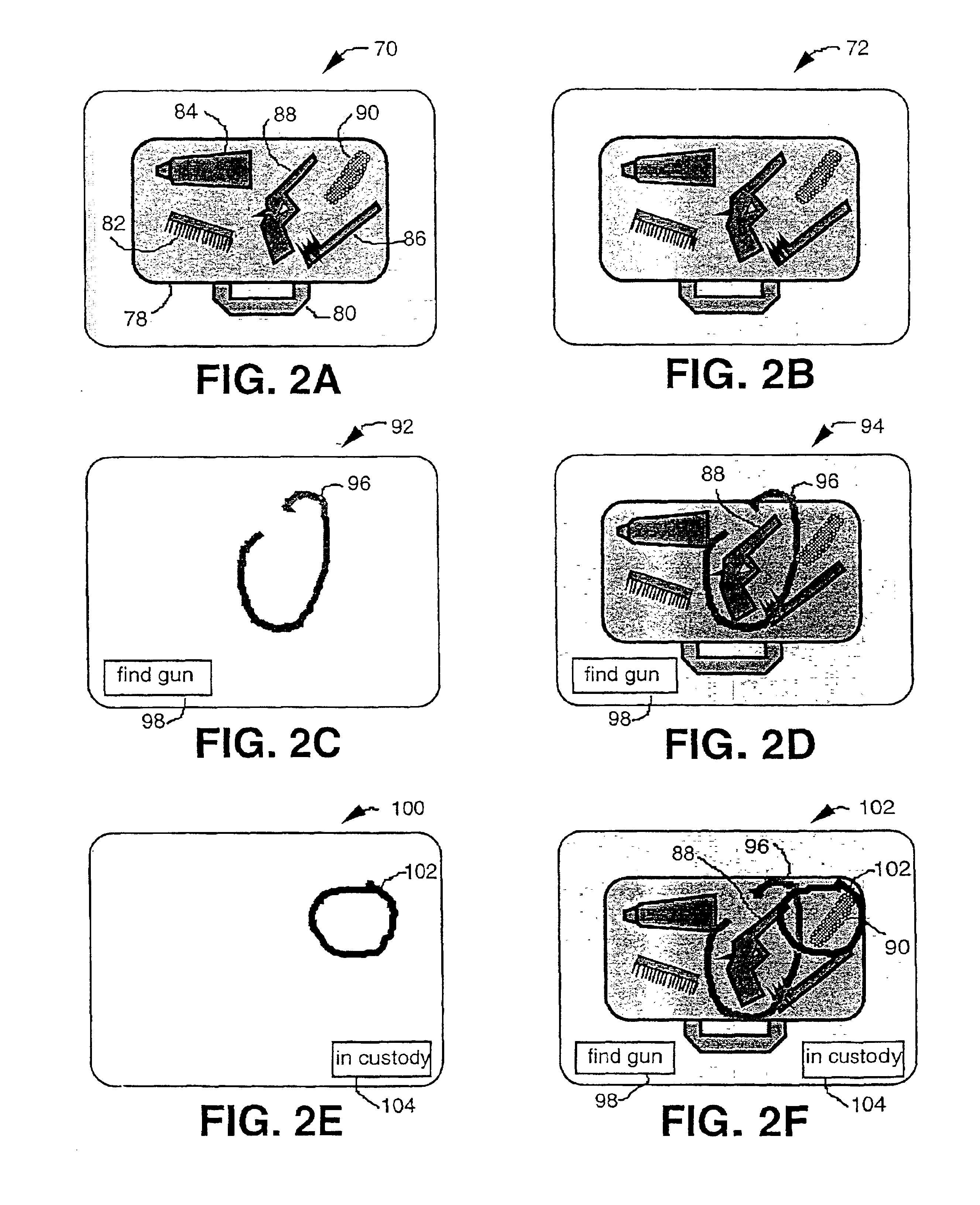
Generation and distribution of annotation overlays of digital X-ray images for security systems
InactiveUS6839403B1Material analysis by transmitting radiationNuclear radiation detectionX-rayData treatment
An image display storage and retrieval system provides a mechanism to transmit x-ray images of parcels to one or more remote workstations. The images may be annotated at these workstations to specifically identify articles to be targeted for more thorough investigation. The image display storage and retrieval system comprises an x-ray image source to illuminate a parcel with x-rays, scan the received x-ray pattern produced from the x-rays passing through the parcel, and digitize the x-ray image of the parcel, an initial screening station where images are initially received and may be annotated, an inspection station where the images (with or without annotation) and parcels to be inspected are received, an optional parcel path switch to direct parcels to either a clearance station or an inspection station, a data storage and retrieval device to record and retrieve images, a data processor to receive the images and a data network connecting the initial screening station, the inspection station, the optional path switch, the data storage and retrieval device and the data processor so as to enable the exchange of data.
Owner:RAPISCAN SYST INC (US)
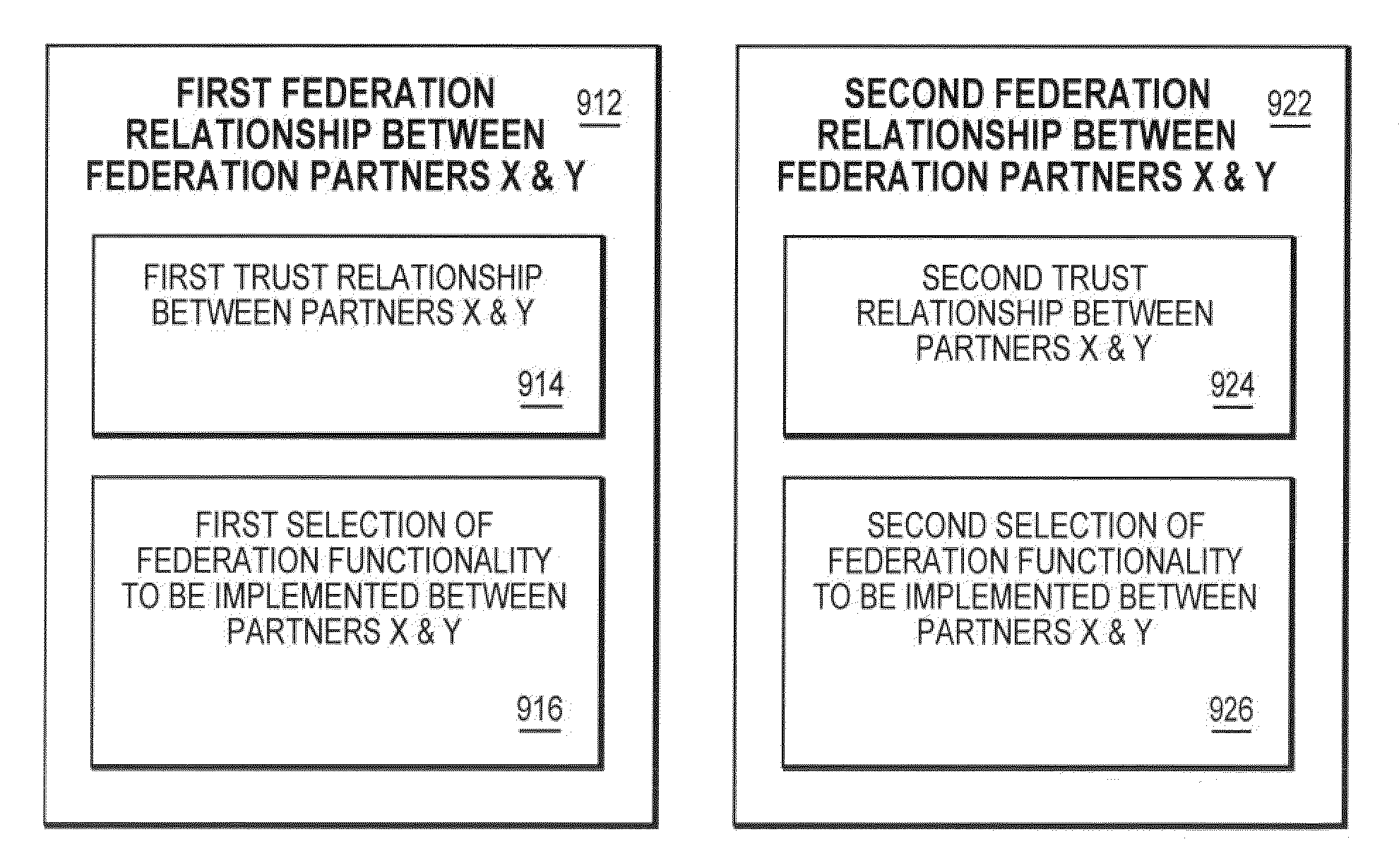
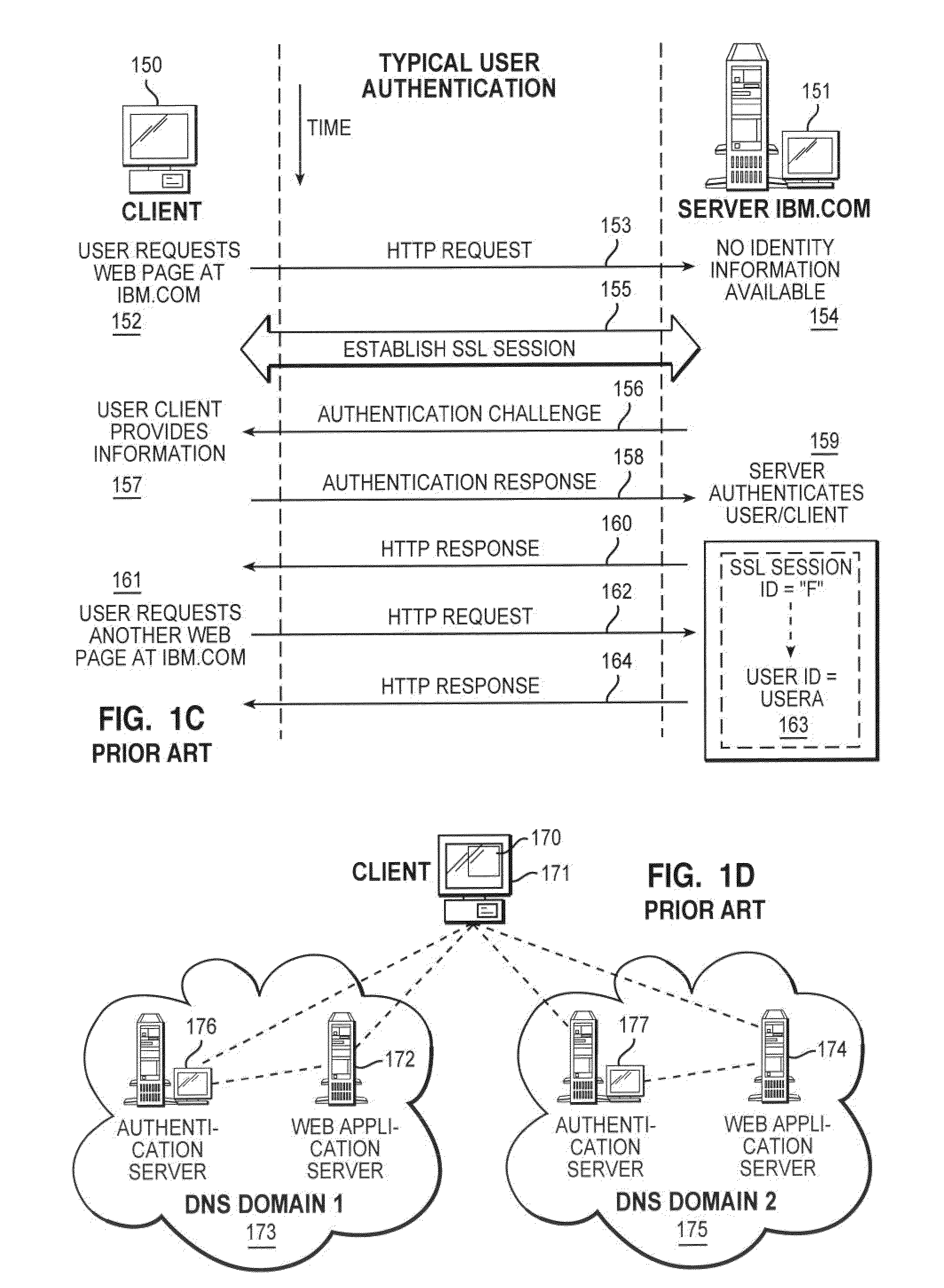
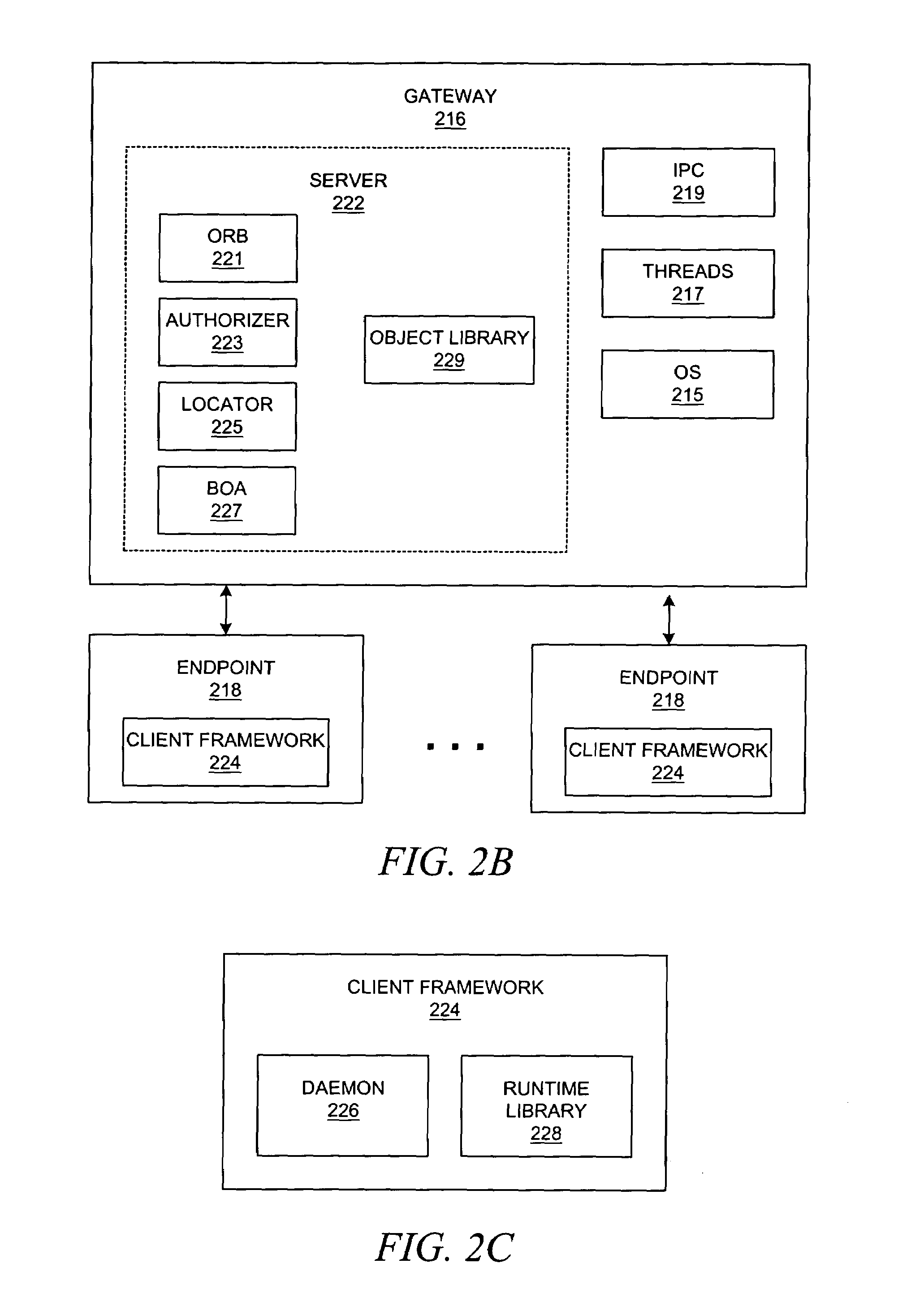
Specializing support for a federation relationship
ActiveUS7562382B2Change is minimalDigital data processing detailsUser identity/authority verificationData processing systemIdentity provider
The invention provides federated functionality within a data processing system by means of a set of specialized runtimes. Each of the plurality of specialized runtimes provides requested federation services for selected ones of the requestors according to configuration data of respective federation relationships of the requestors with the identity provider. The configuration data is dynamically retrieved during initialization of the runtimes which allows the respective runtime to be specialized for a given federation relationship. Requests are routed to the appropriate specialized runtime using the first requestor identity and the given federation relationship. The data which describes each federation relationship between the identity provider and each of the plurality of requesters is configured prior to initialization of the runtimes. Configuration data is structured into global specified data, federation relationship data and requestor specific data to minimize data change, making the addition or deletion of requestors very scalable.
Owner:IBM CORP
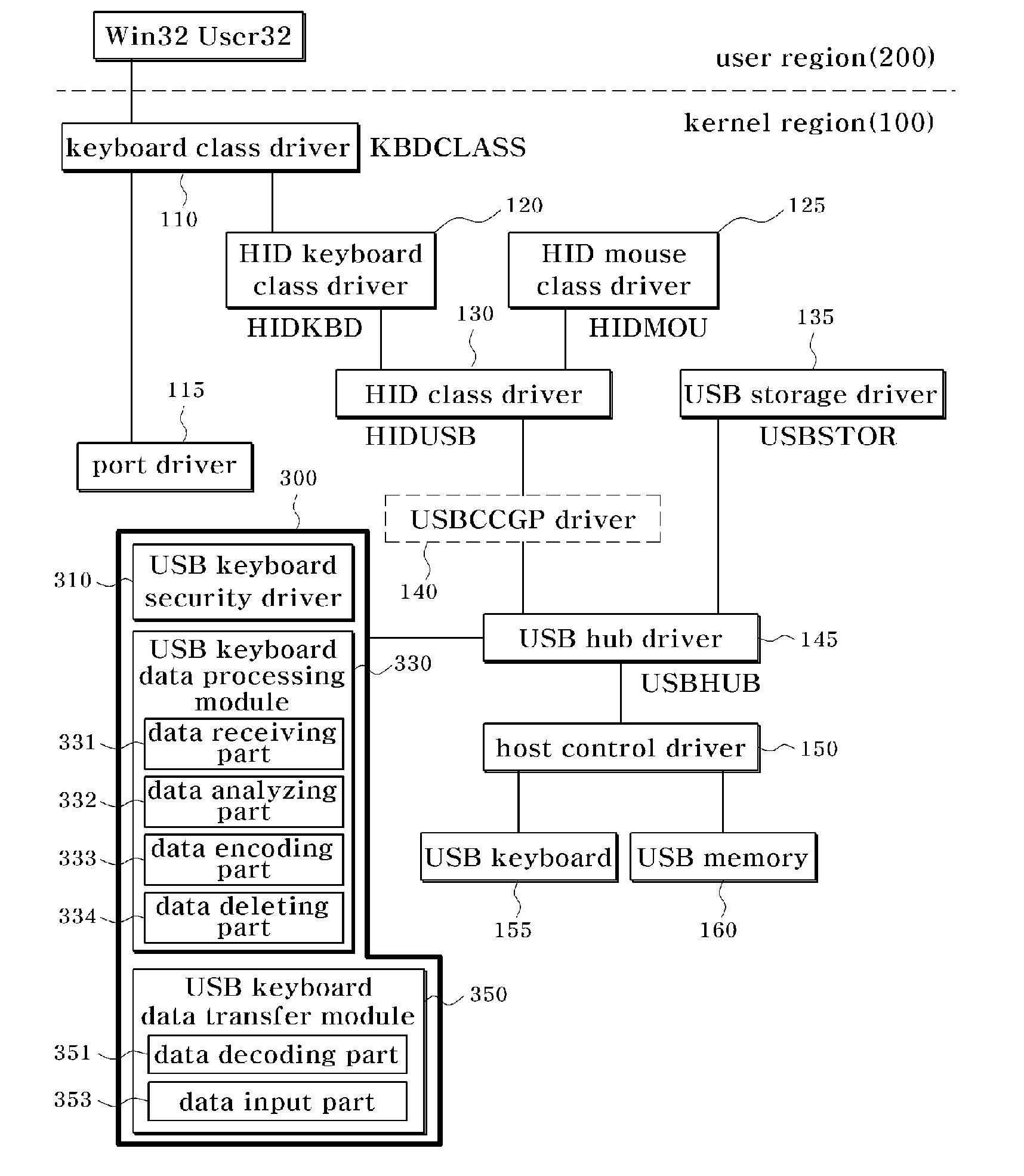
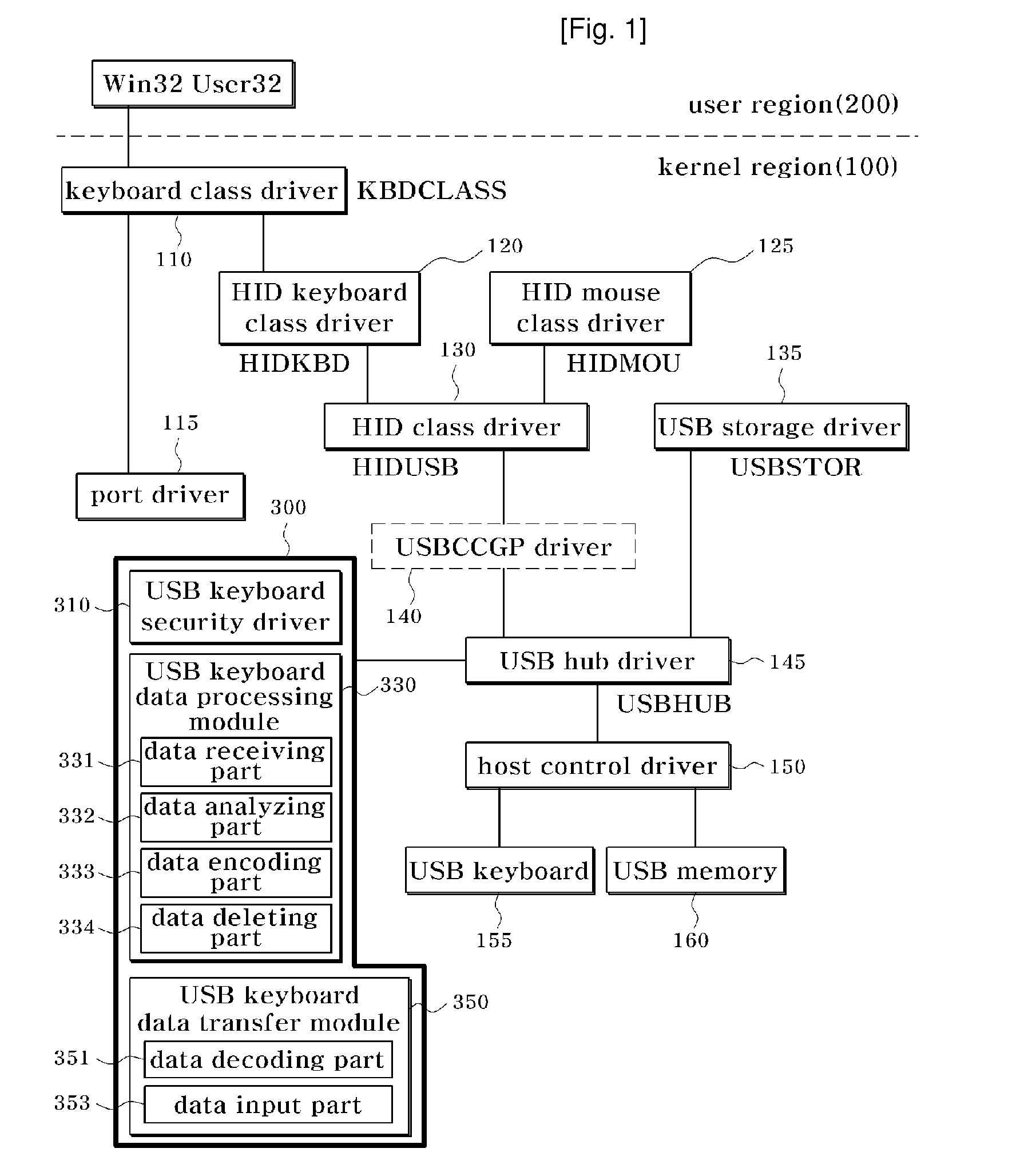
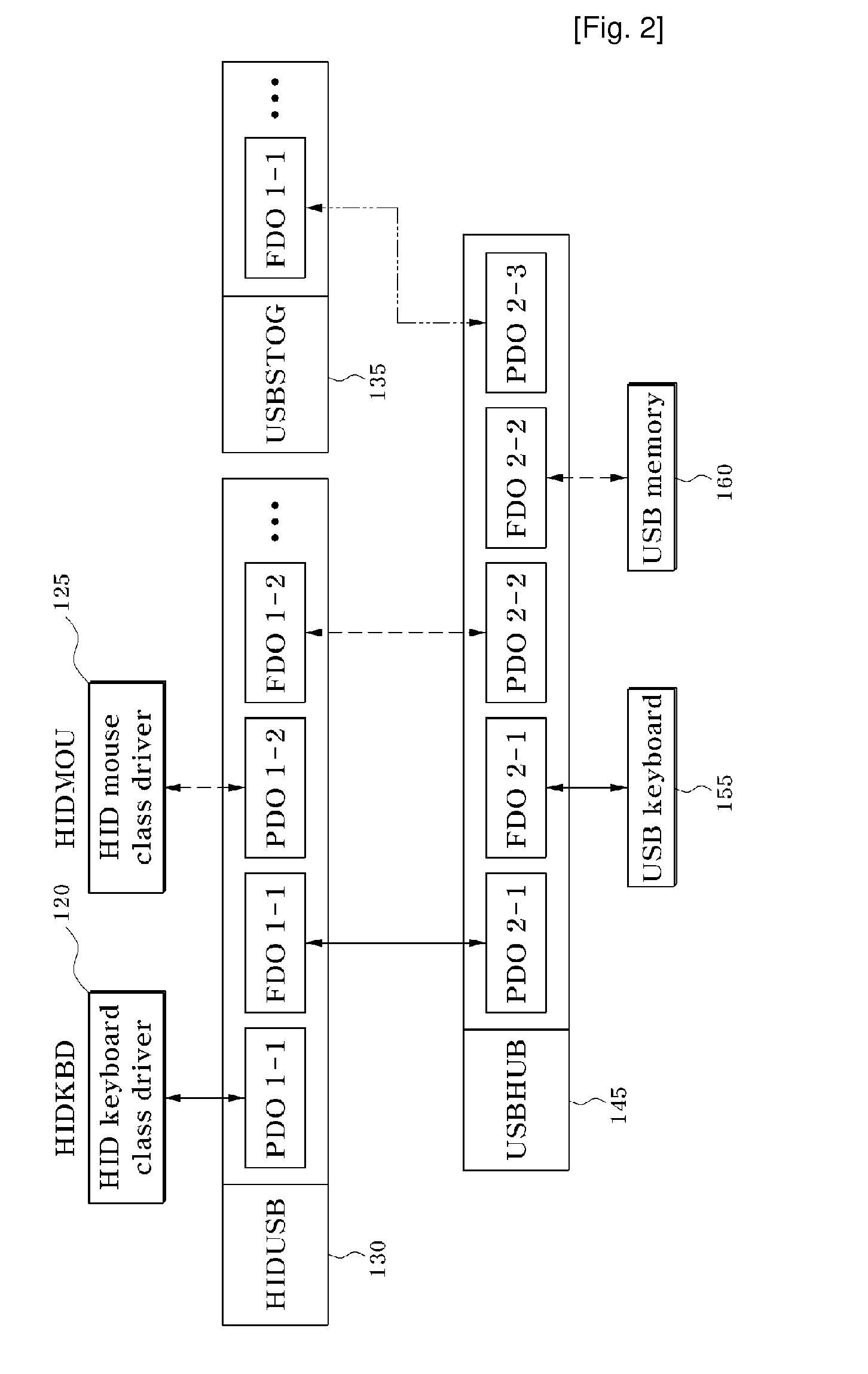
Apparatus and Method for Preservation of USB Keyboard
InactiveUS20090172705A1Inhibit inputInput/output for user-computer interactionProgram control using stored programsUSB hubPersonal computer
Provided are a data security apparatus and method for a USB keyboard. The data security apparatus includes: a USB keyboard security driver for selecting a driver for a USB keyboard from USB devices connected to a personal computer, and replacing a data processing function address in a USB hub driver with a function address of the selected USB keyboard driver to acquire input data input by the USB keyboard; a USB keyboard data processing module for preferentially receiving the input data acquired from the USB keyboard security driver, and processing the input data through analysis, encoding and deletion processes; and a USB keyboard data transfer module for decoding the input data processed by the USB keyboard USB keyboard data processing module and outputting the decoded input data to a user's desired location. Thus, data input by a malicious program from a keyboard in communication with a main body of a personal computer (PC) through USB to transmit data can be protected from being transmitted to the external.
Owner:KING INFORMATION & NETWORK
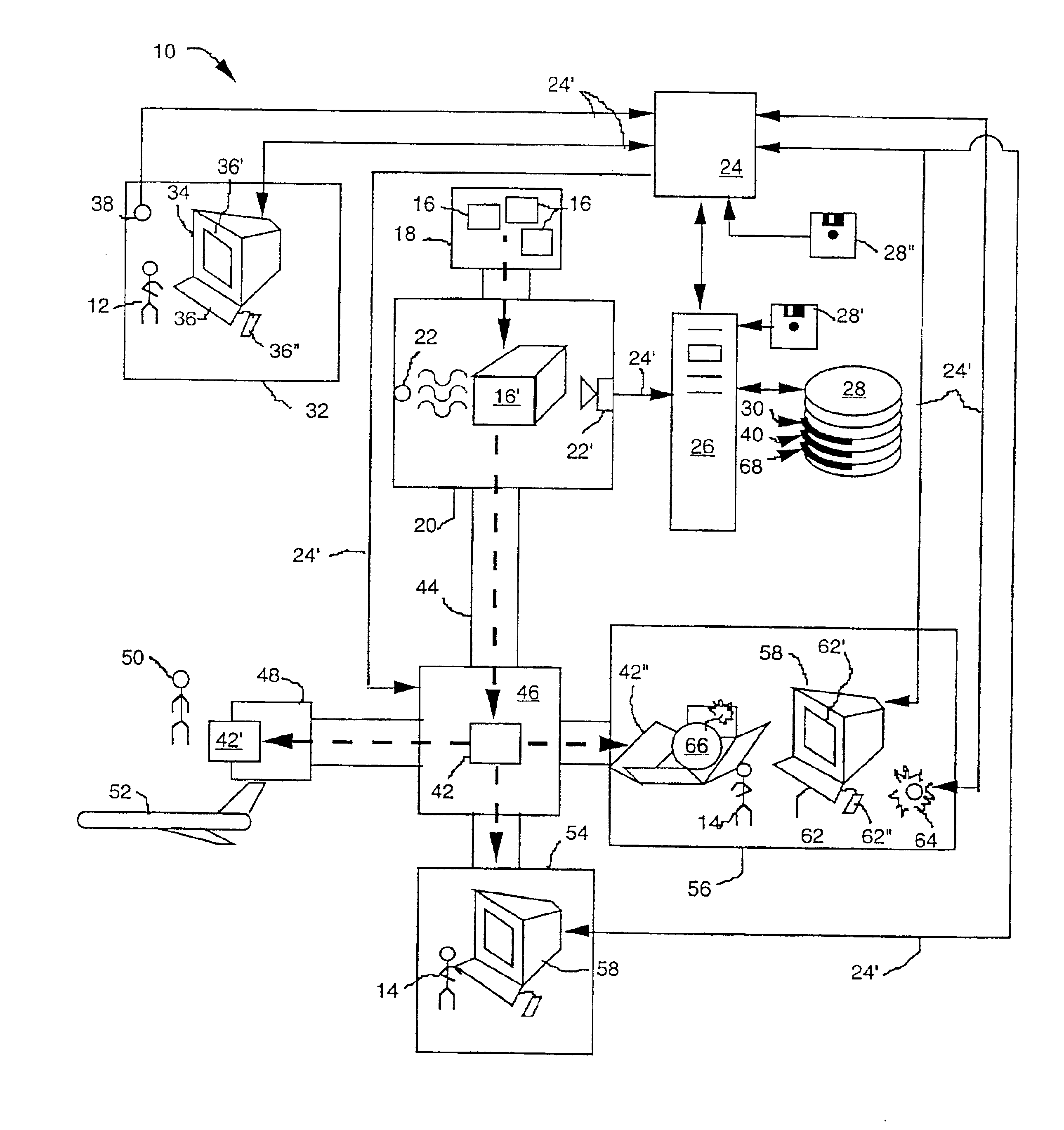
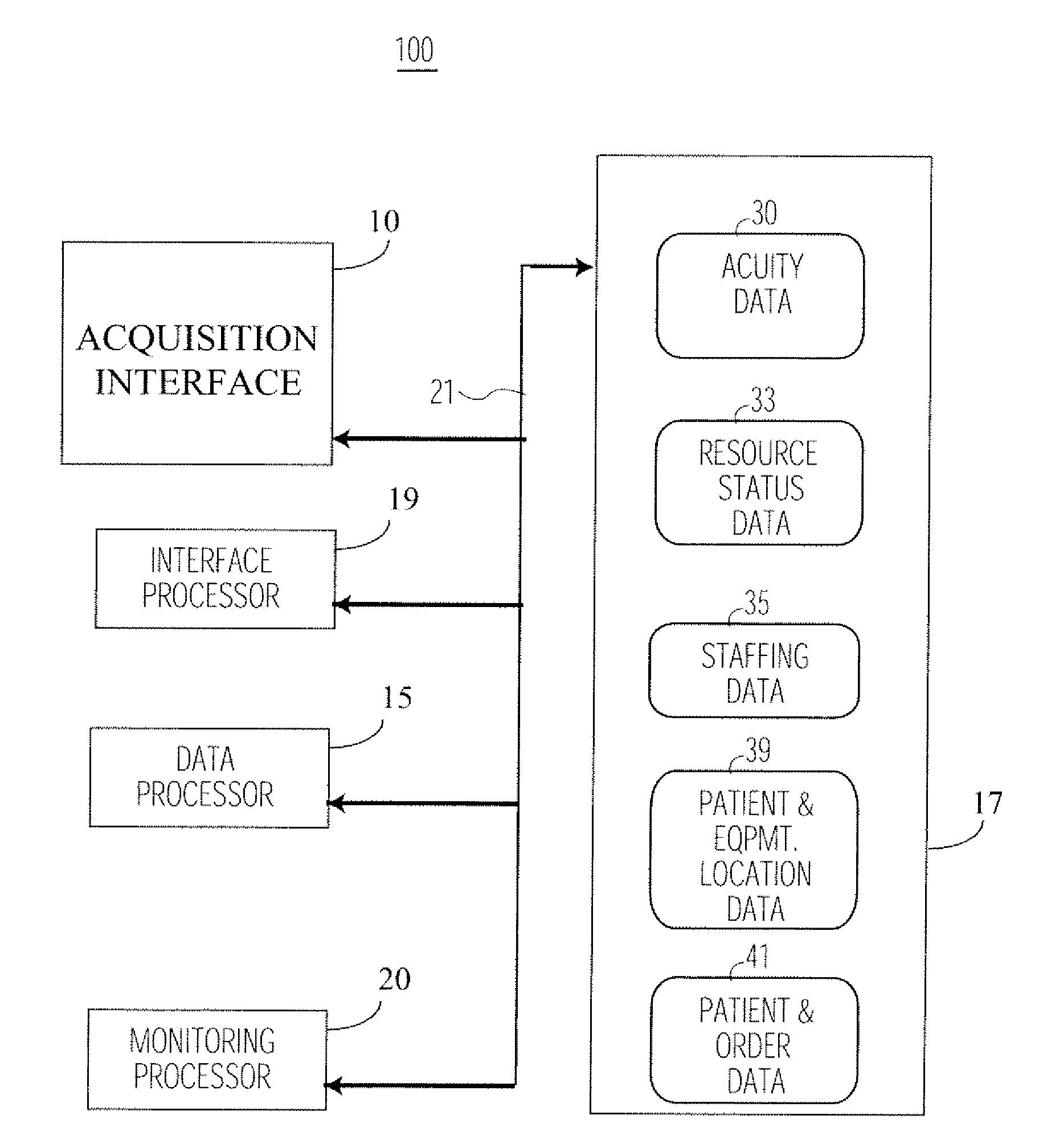
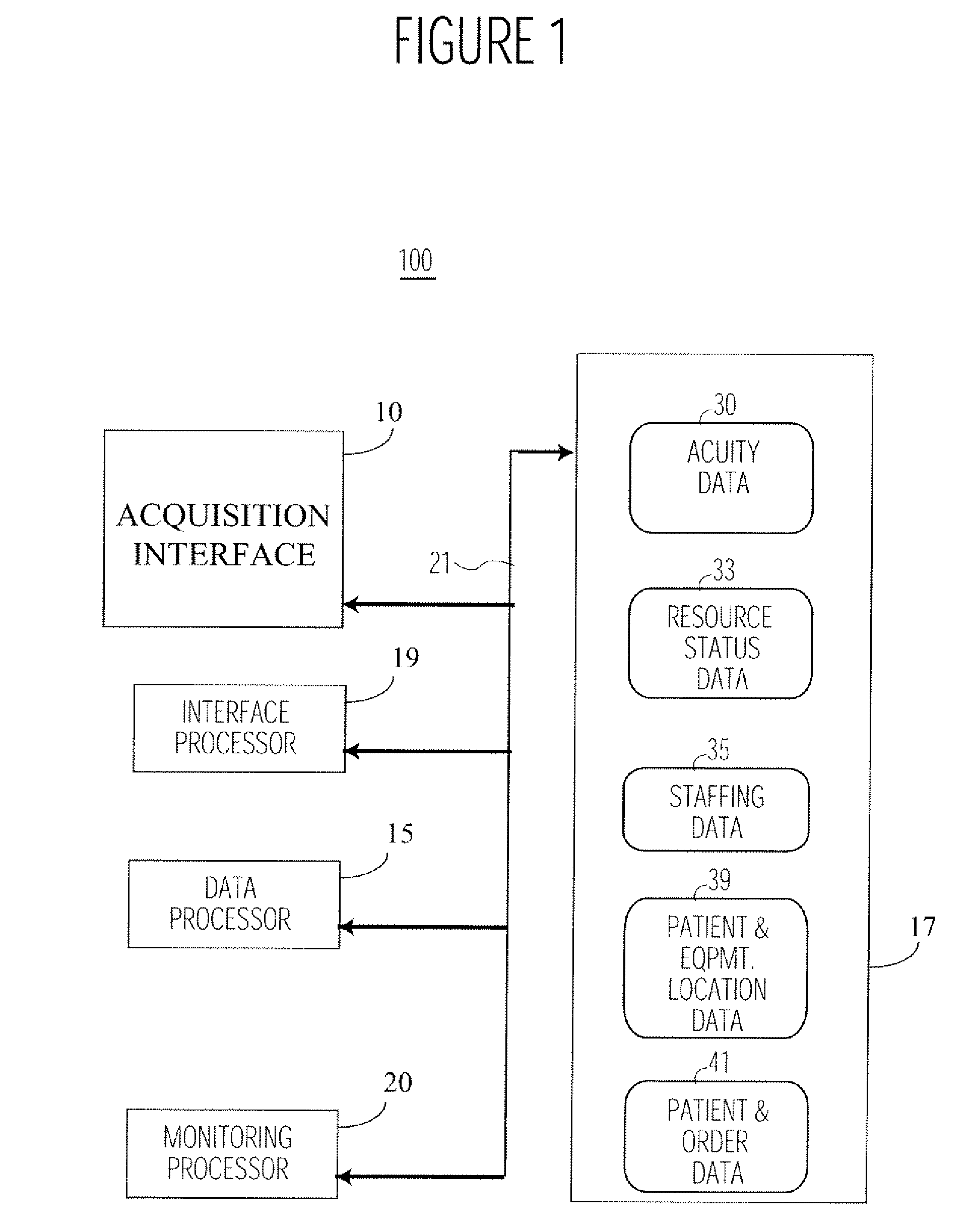
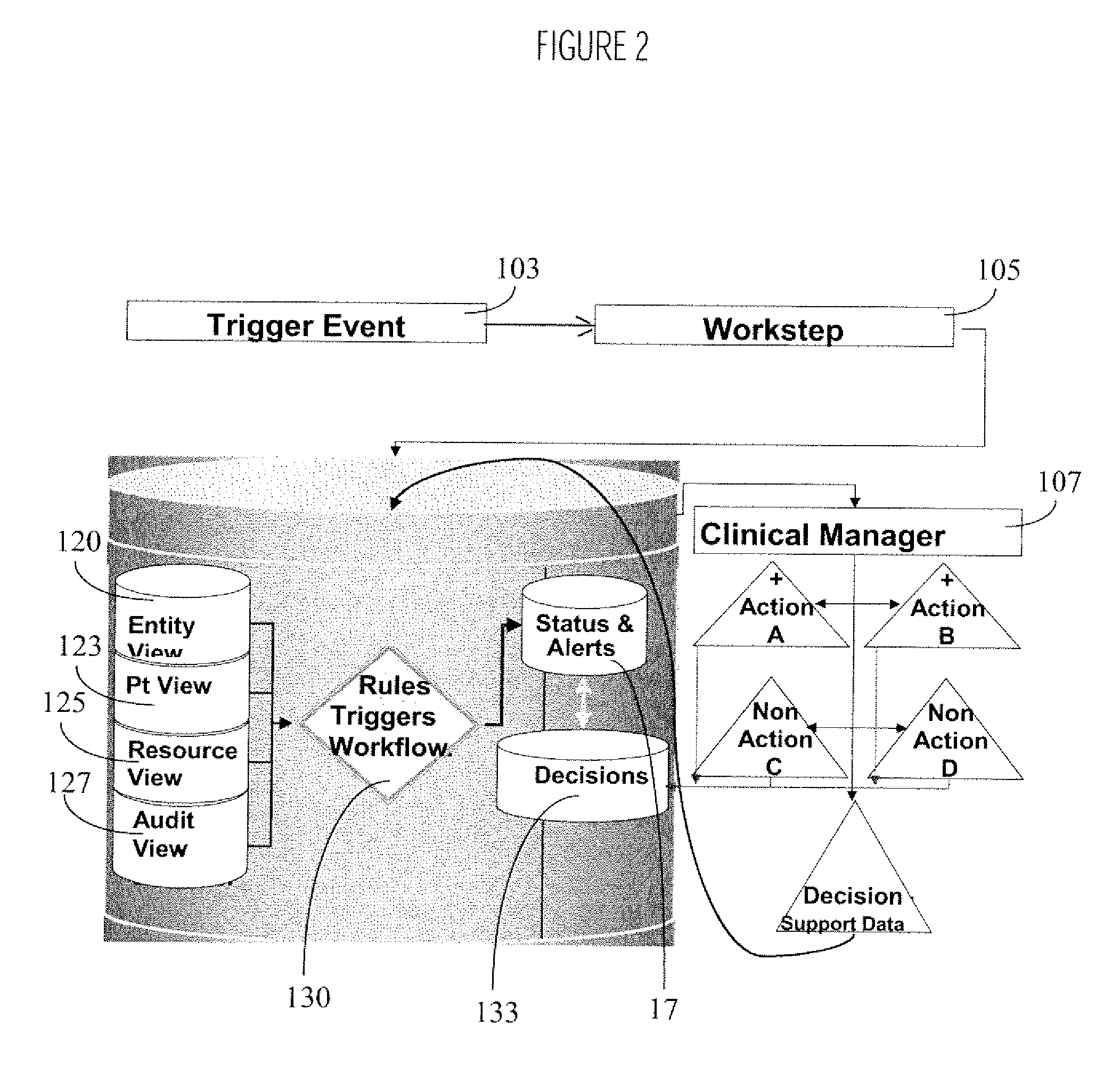
System for Monitoring Healthcare Related Activity In A Healthcare Enterprise
A system provides comprehensive patient and resource status information (manpower and equipment required to maintain optimal patient care) in an organization (e.g., a hospital) for use in adjusting resources to meet existing and future conditions. A system for monitoring activity in a healthcare enterprise includes an acquisition interface for acquiring acuity data representative of severity of medical condition of an individual patient, for multiple different patients. A monitoring processor monitors data identifying orders initiated for treatment to be provided to an individual patient and data identifying laboratory test results received for an individual patient, for multiple different patients. A data processor generates data representing status of healthcare activity for multiple patients in response to the data identifying orders and laboratory test results and the acuity data, for multiple different patients. An interface processor provides the data representing status of healthcare activity to a healthcare worker.
Owner:SIEMENS MEDICAL SOLUTIONS HEALTH SERVICES CORPORAT
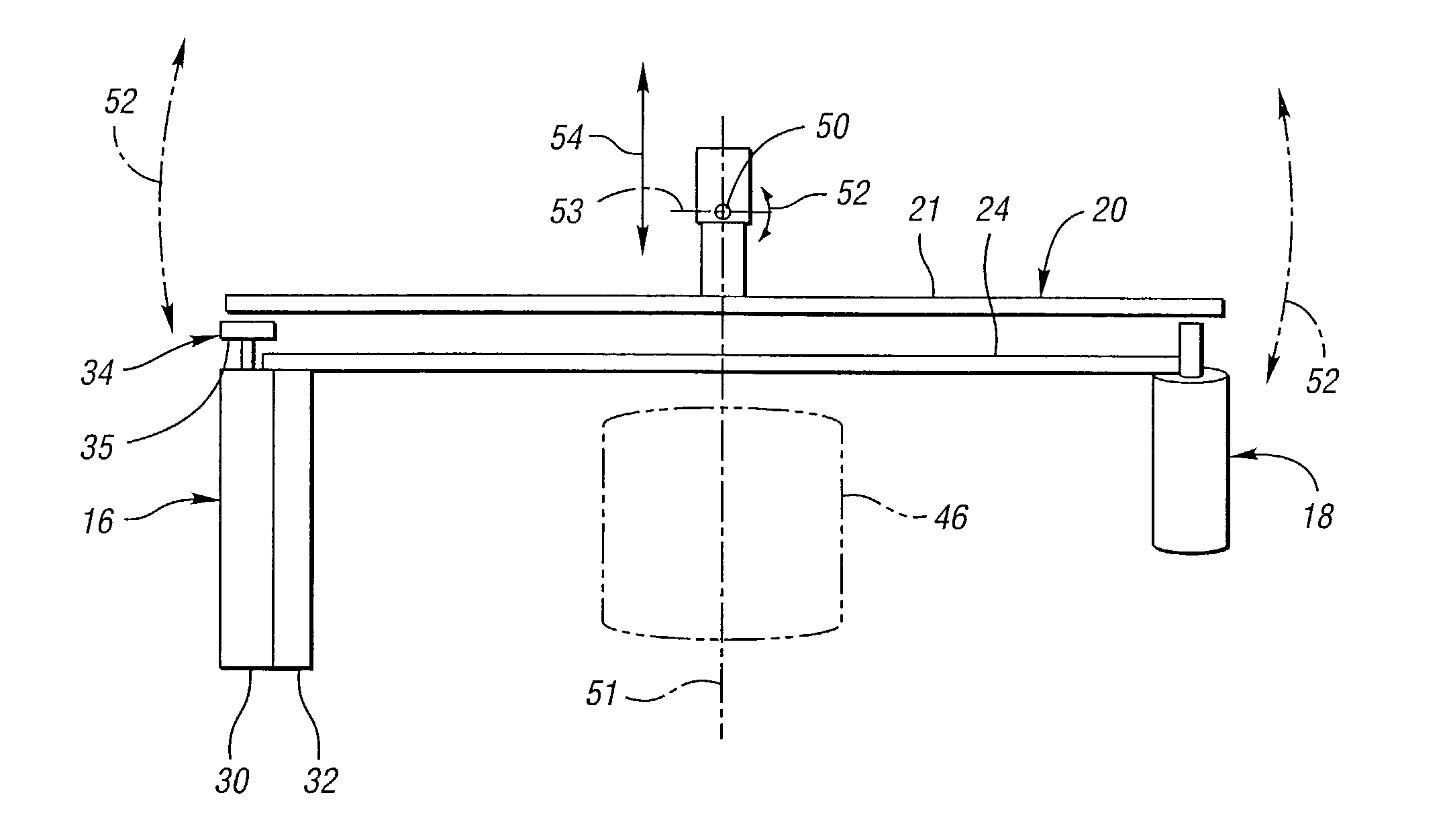
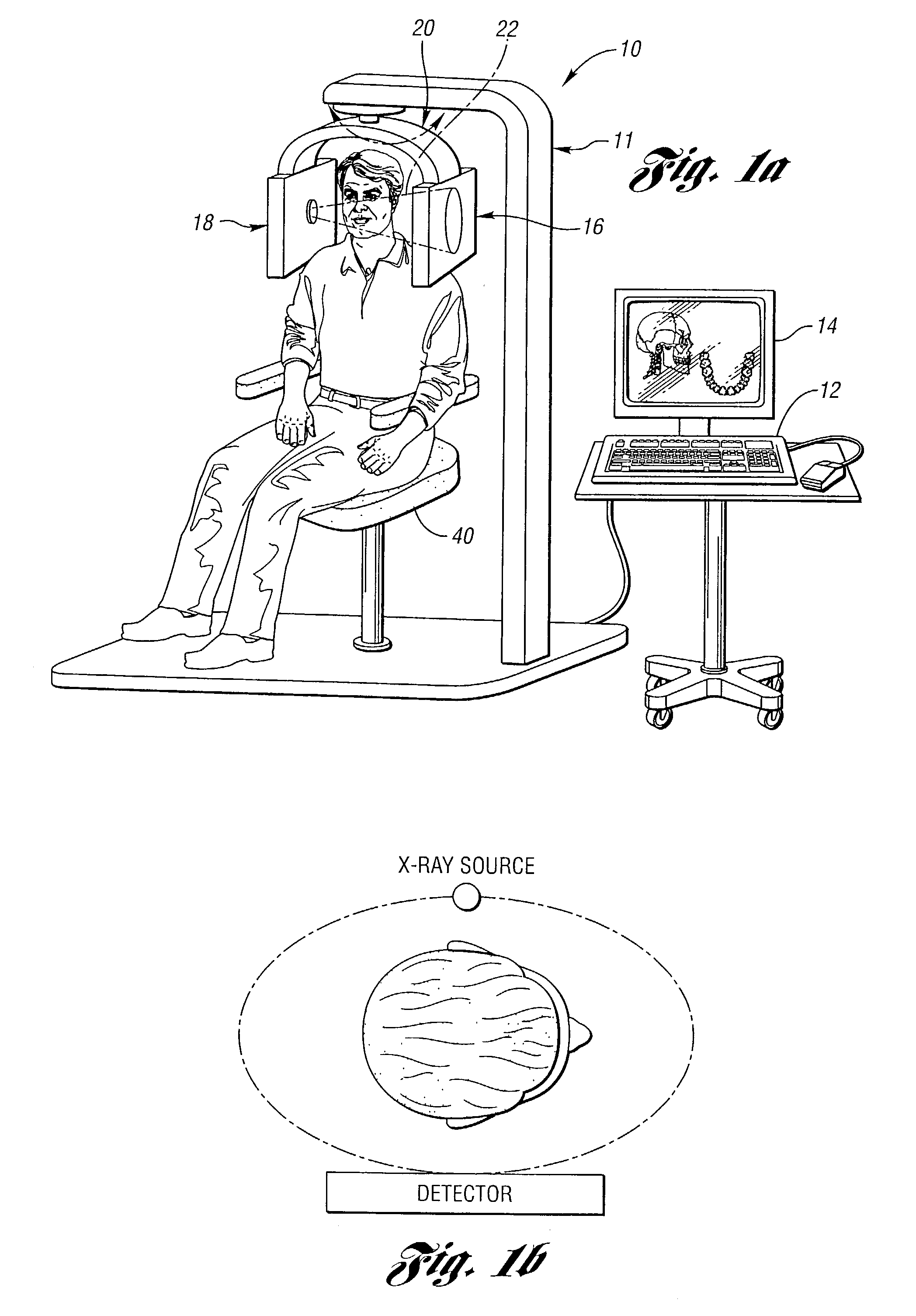
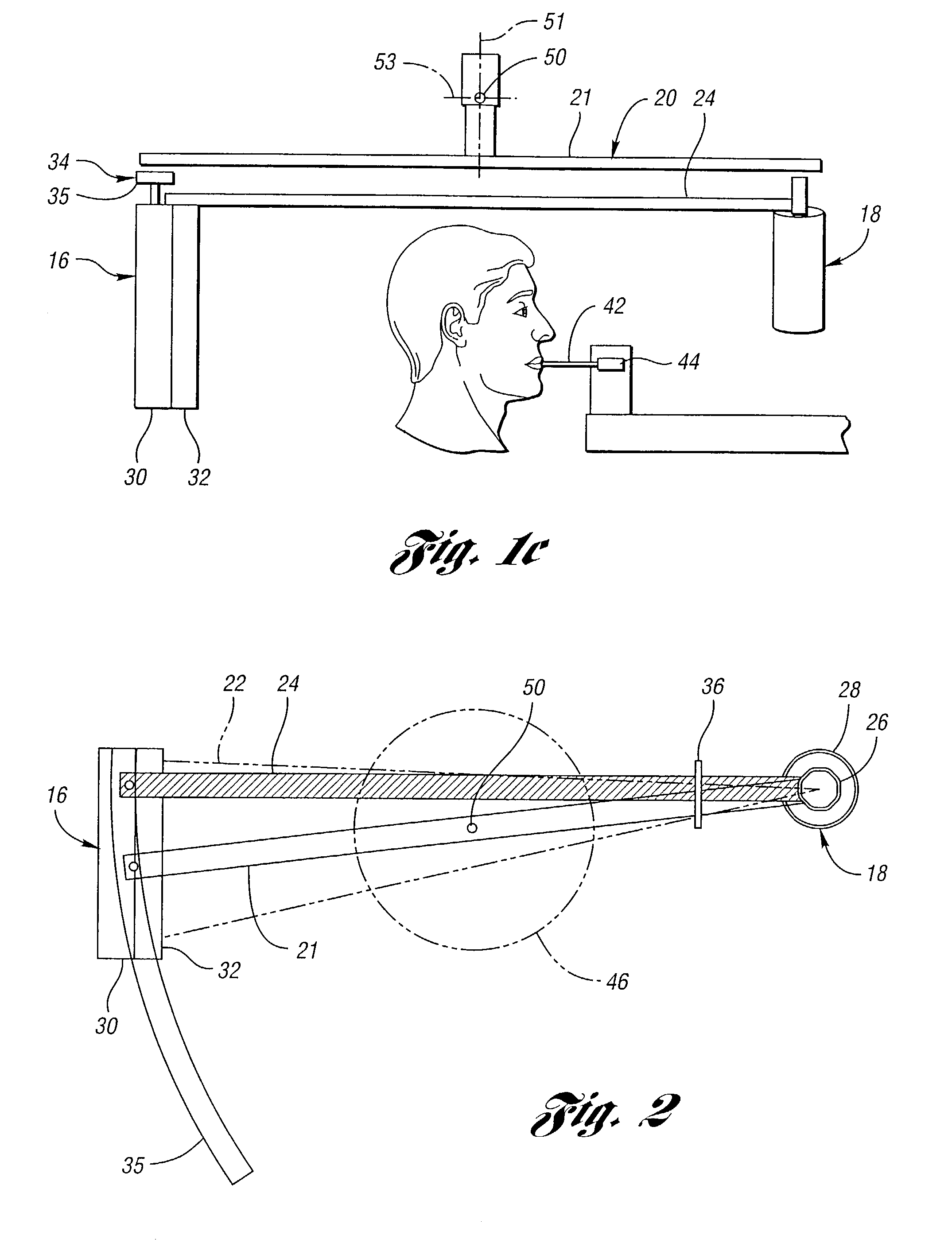
High spatial resolution X-ray computed tomography (CT) system
InactiveUS7099428B2Reduce dispersionMaterial analysis using wave/particle radiationRadiation/particle handlingComputed tomographyHigh spatial resolution
A high spatial resolution X-ray computed tomography (CT) system is provided. The system includes a support structure including a gantry mounted to rotate about a vertical axis of rotation. The system further includes a first assembly including an X-ray source mounted on the gantry to rotate therewith for generating a cone X-ray beam and a second assembly including a planar X-ray detector mounted on the gantry to rotate therewith. The detector is spaced from the source on the gantry for enabling a human or other animal body part to be interposed therebetween so as to be scanned by the X-ray beam to obtain a complete CT scan and generating output data representative thereof. The output data is a two-dimensional electronic representation of an area of the detector on which an X-ray beam impinges. A data processor processes the output data to obtain an image of the body part.
Owner:RGT UNIV OF MICHIGAN
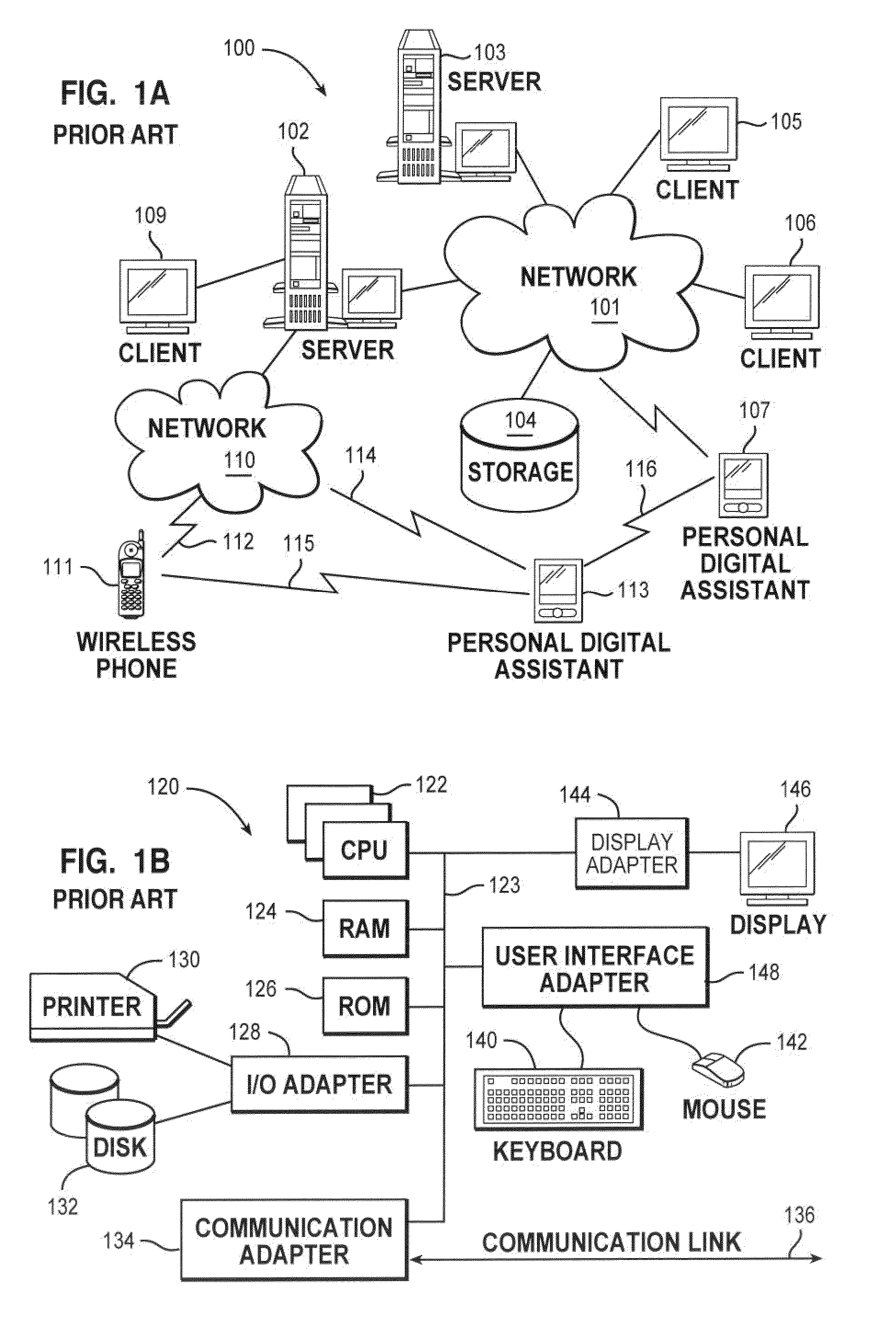
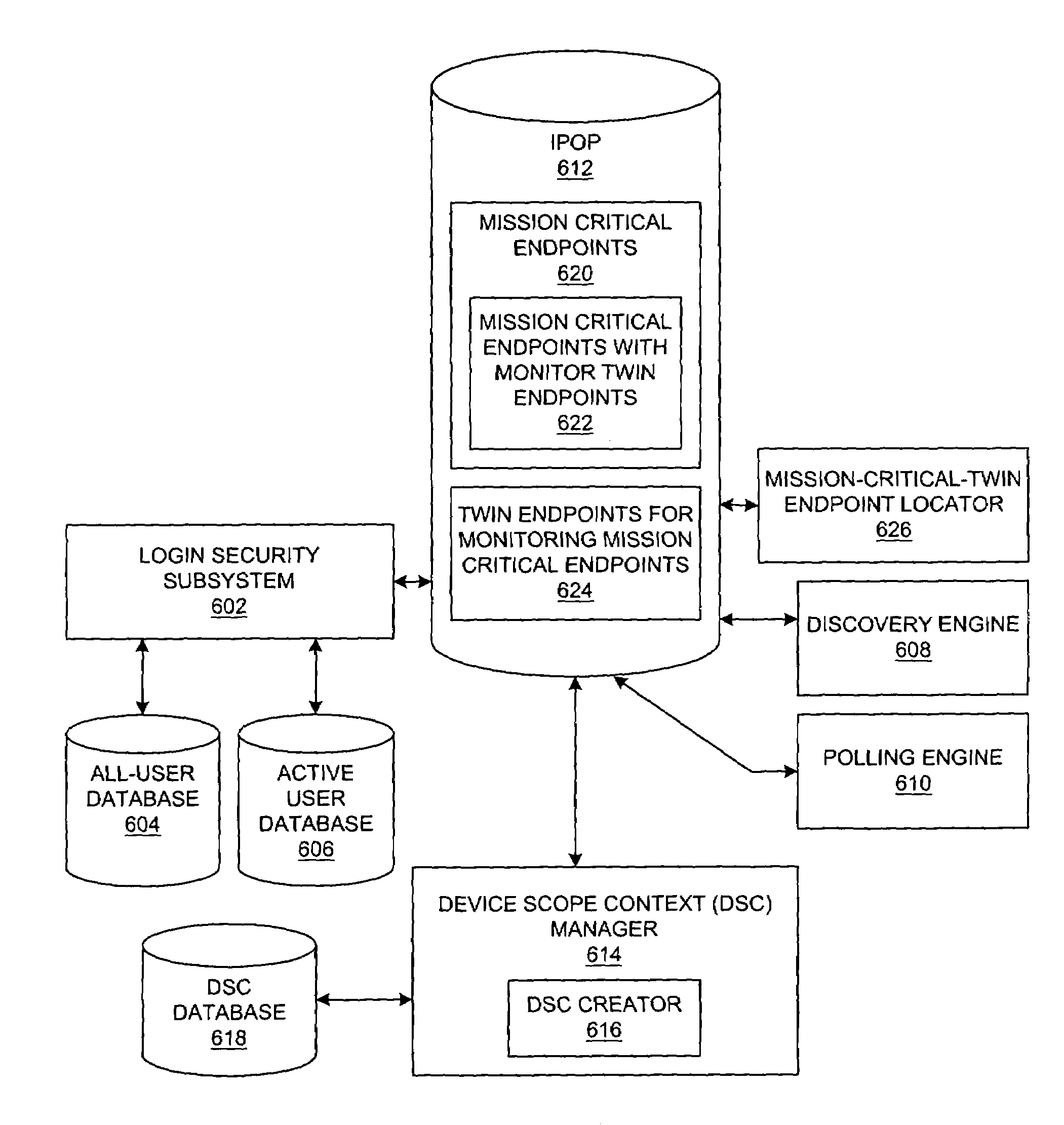
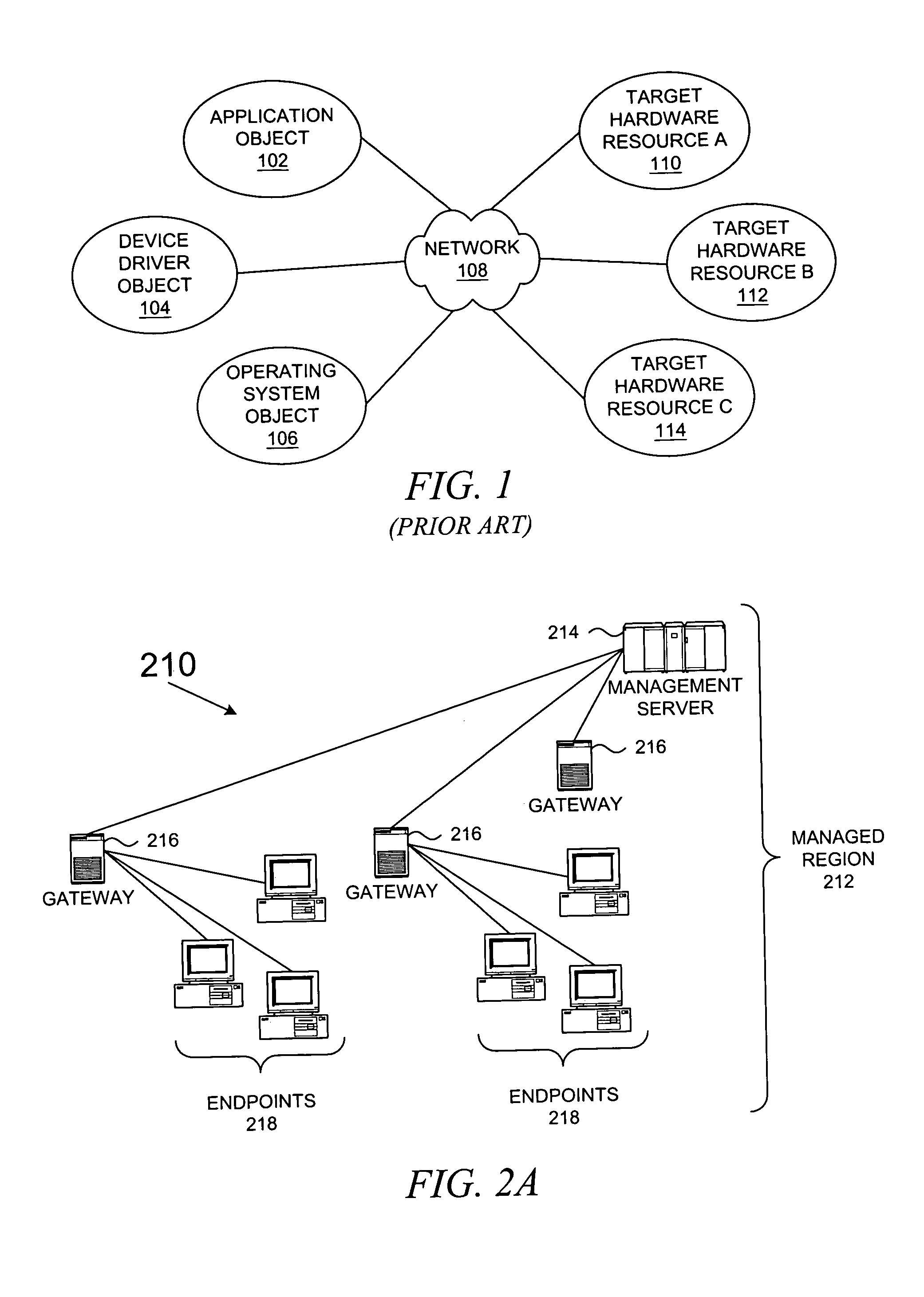
Method and system for network management with backup status gathering
A method, system, apparatus, and computer program product are presented for management of a distributed data processing system. Resources within the distributed data processing system are dynamically discovered, and the discovered resources are adaptively monitored using the network management framework. A network or system administrator configures some mission critical endpoints with multiple network interface cards (NICs) and specifies mission critical endpoints, non-mission critical actions, etc. During status collection activities associated with network or system management activities, the categorization of an endpoint as a mission-critical or non-mission critical endpoint affects the manner in which the status collection activity is performed. Applications can request the performance of actions at endpoints without regard to the categorization of the endpoint or without regard to the categorization of the requested action, and the network management system routes the action based on whether or not the specified endpoint is a mission critical endpoint. A non-mission-critical endpoint is associated with a mission-critical endpoint based on the non-mission-critical endpoint's communication history with the mission critical endpoint. The management system may use the status of a non-mission-critical endpoint as a reflection of the status of a mission-critical endpoint.
Owner:GOOGLE LLC
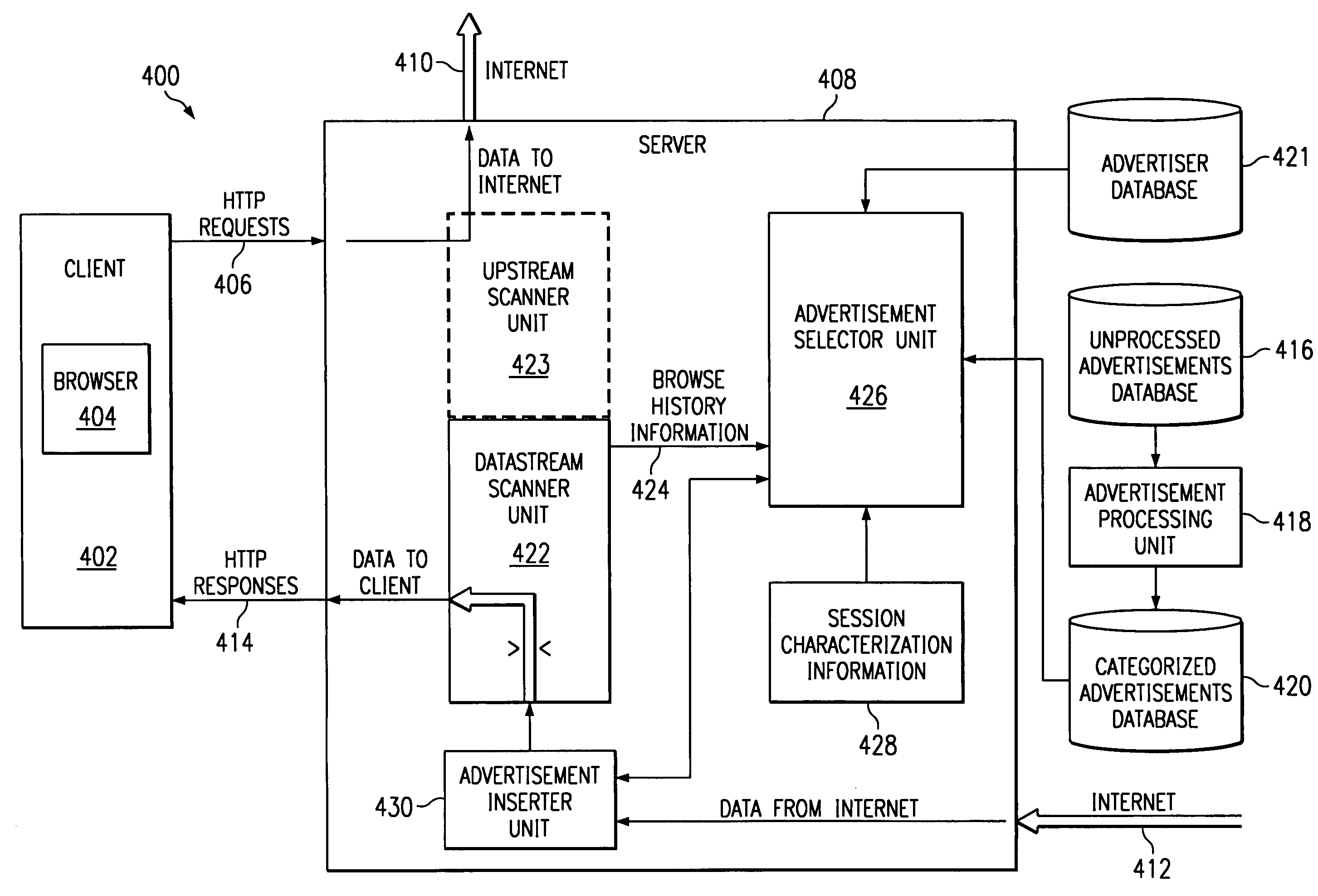
Method and apparatus for providing reduced cost online service and adaptive targeting of advertisements
InactiveUS7089194B1Low costAdvertisementsDigital computer detailsData processing systemAnalysis data
A method and apparatus for adaptively targeting advertisements to a specific client computer from a server within a distributed data processing system is provided. As a user of the client browses the World Wide Web, the material that is downloaded to the client constitutes a datastream. At some location during the routing of the datastream, either on the server or at the client, the datastream is scanned to generate a list of keywords that are present within the datastream. The datastream may be analyzed in real-time or cached and analyzed on a delayed basis. The generated list of keywords represents a summary of the content that appears to be the focus of interest of the user. The keywords are compared against a database of advertisements, and the server selects an advertisement that matches the user's area of interest in comparison to the analysis of the user's browsing history. The selected advertisement is then inserted into the datastream to be routed to the client. In consideration for viewing targeted advertisements and to entice a Web viewer to allow the monitoring of a datastream so that targeted advertisements may be placed into the datastream, a Web viewer may receive online connection service for free, for a reduced cost, at a premium level of service, or for other some other value, such as frequent viewer credits that may be exchanged for goods and services.
Owner:IBM CORP
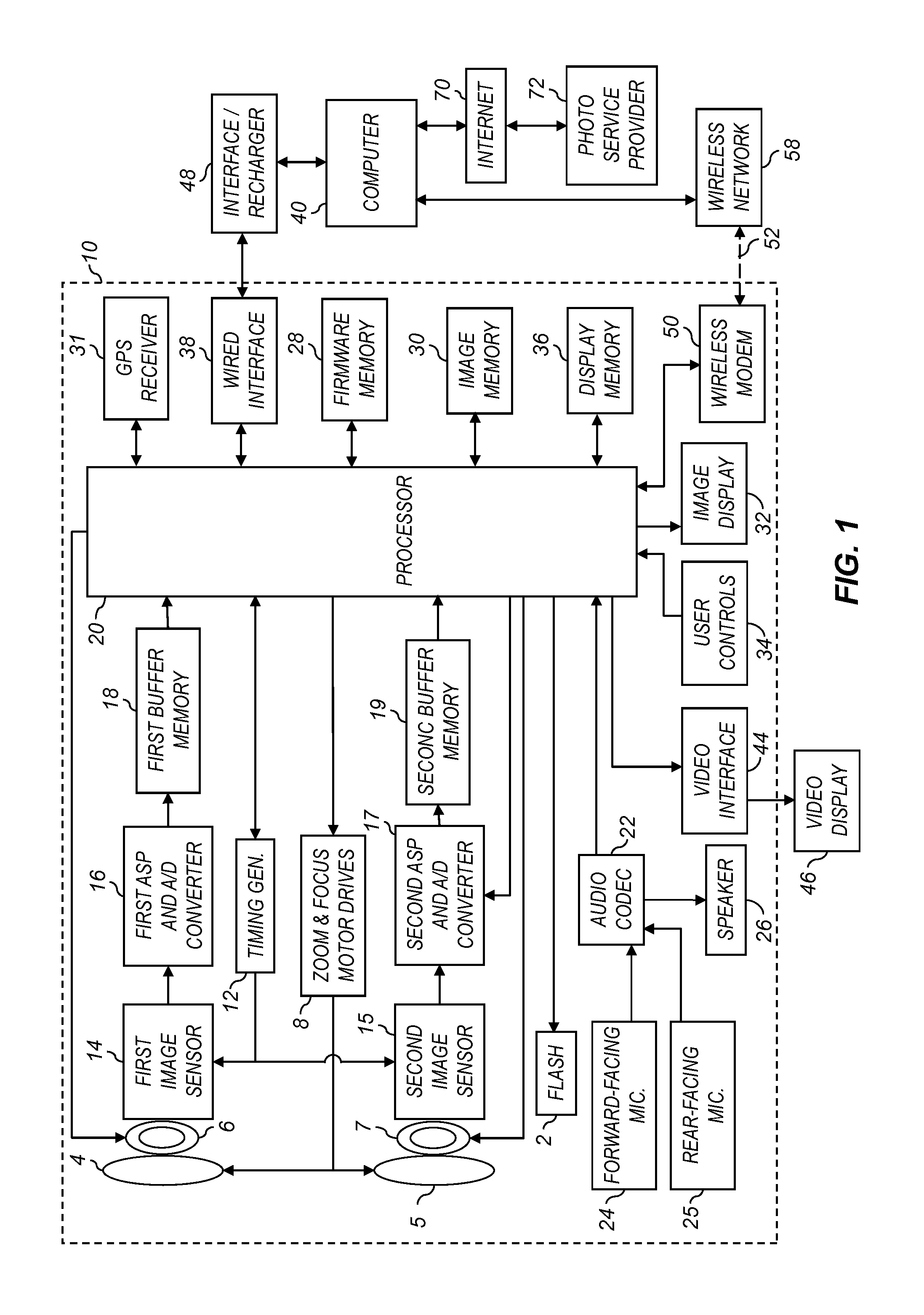
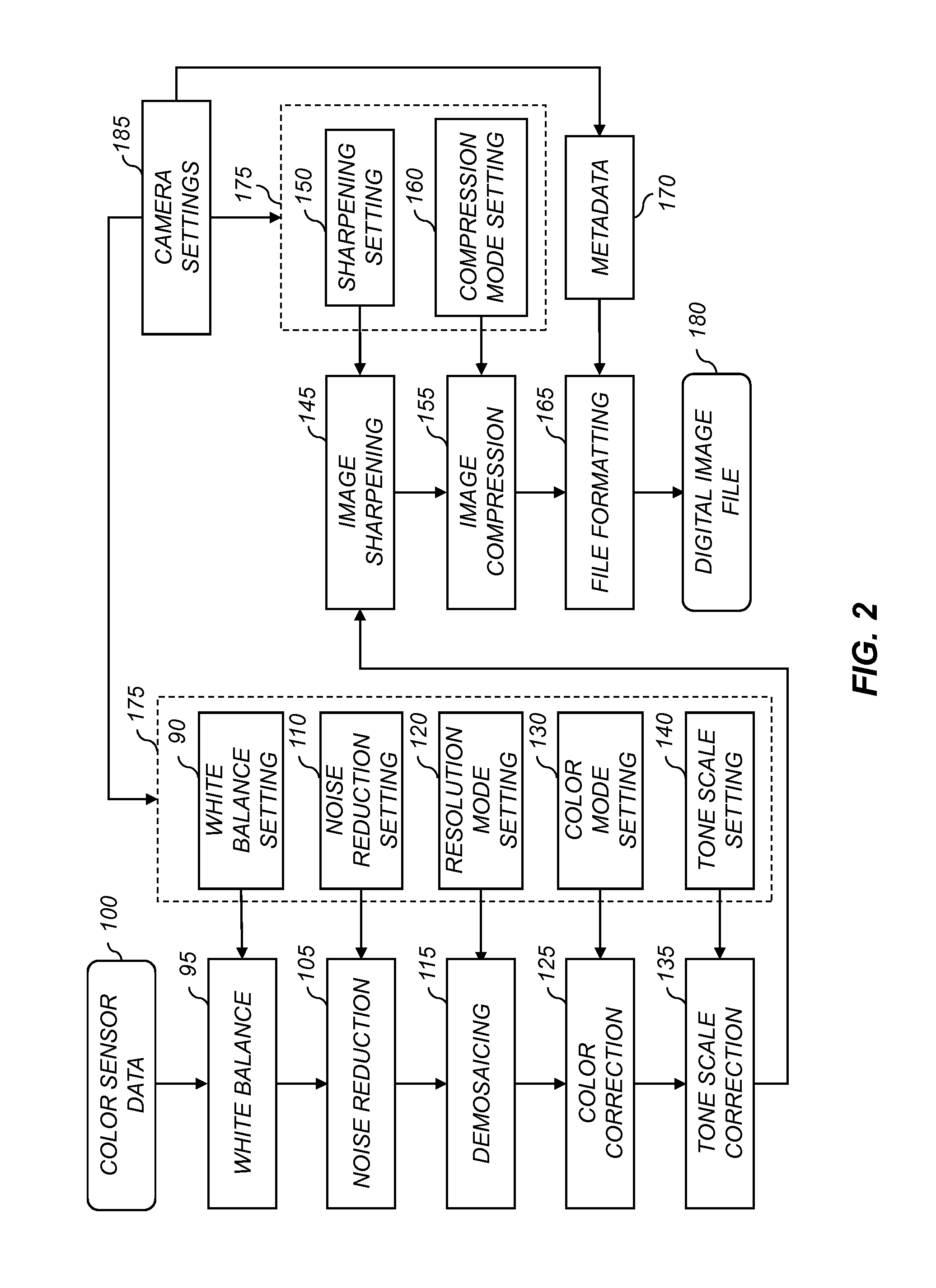
Video camera providing a composite video sequence
ActiveUS20130235224A1Inhibitory contentTelevision system detailsColor television detailsDigital videoComputer graphics (images)
A digital camera system including a first video capture unit for capturing a first digital video sequence of a scene and a second video capture unit that simultaneously captures a second digital video sequence that includes the photographer. A data processor automatically analyzes first digital video sequence to determine a low-interest spatial image region. A facial video sequence including the photographer's face is extracted from the second digital video sequence, and inserted into the low-interest spatial image region in the first digital video sequence to form the composite video sequence.
Owner:APPLE INC
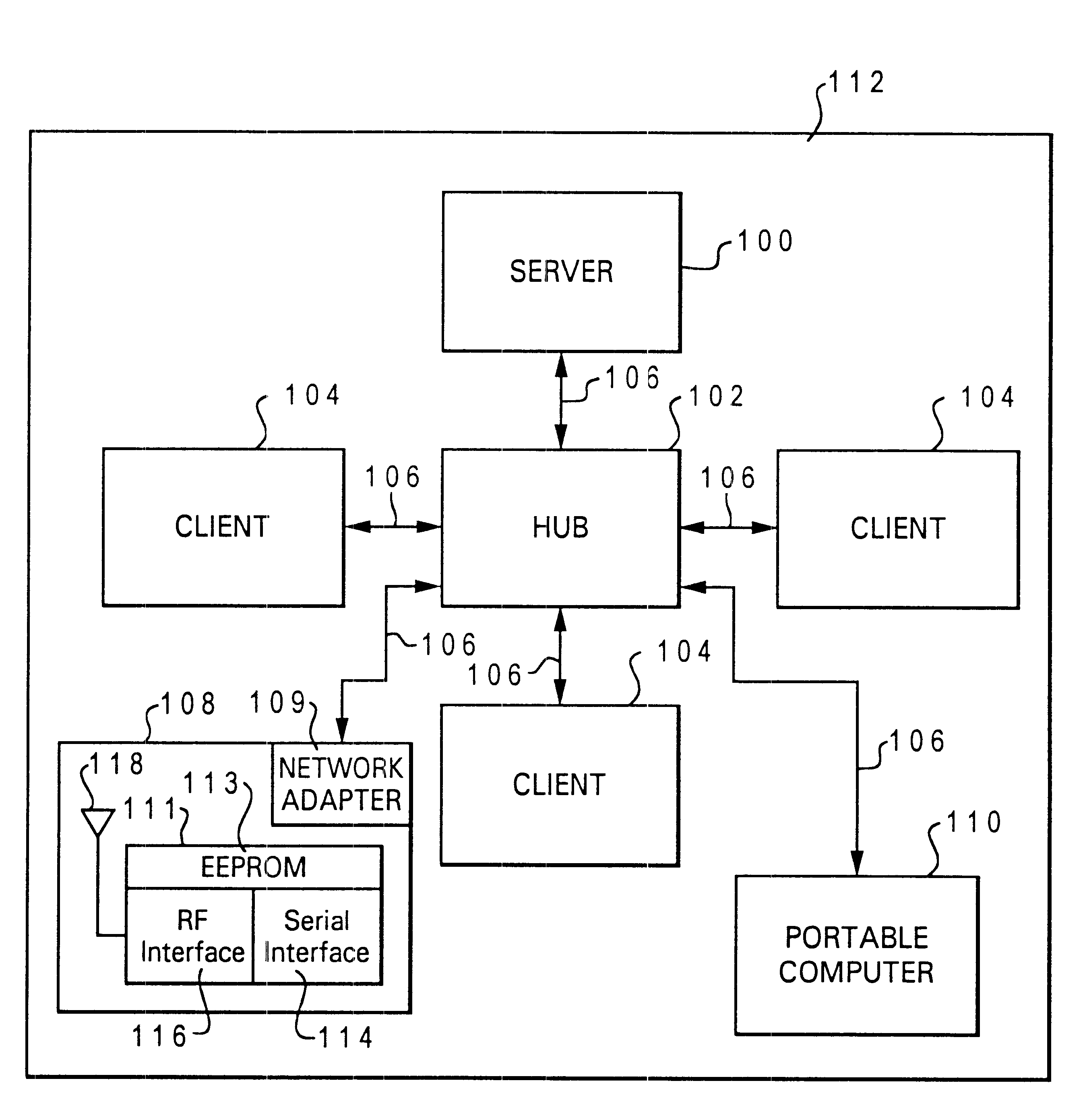
Data processing system and method for permitting a computer to automatically detect a presence of and establish a communications link with a printer
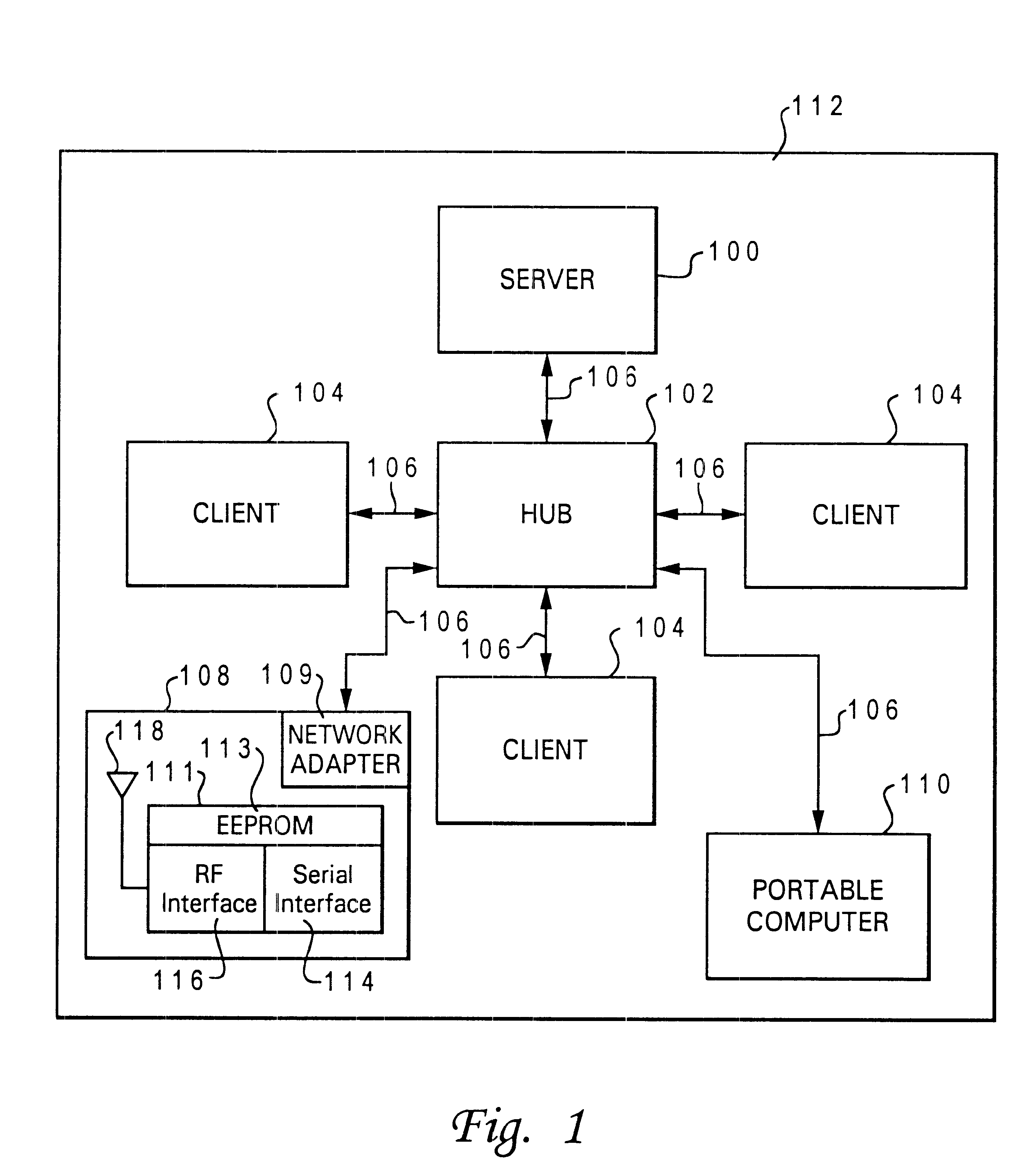
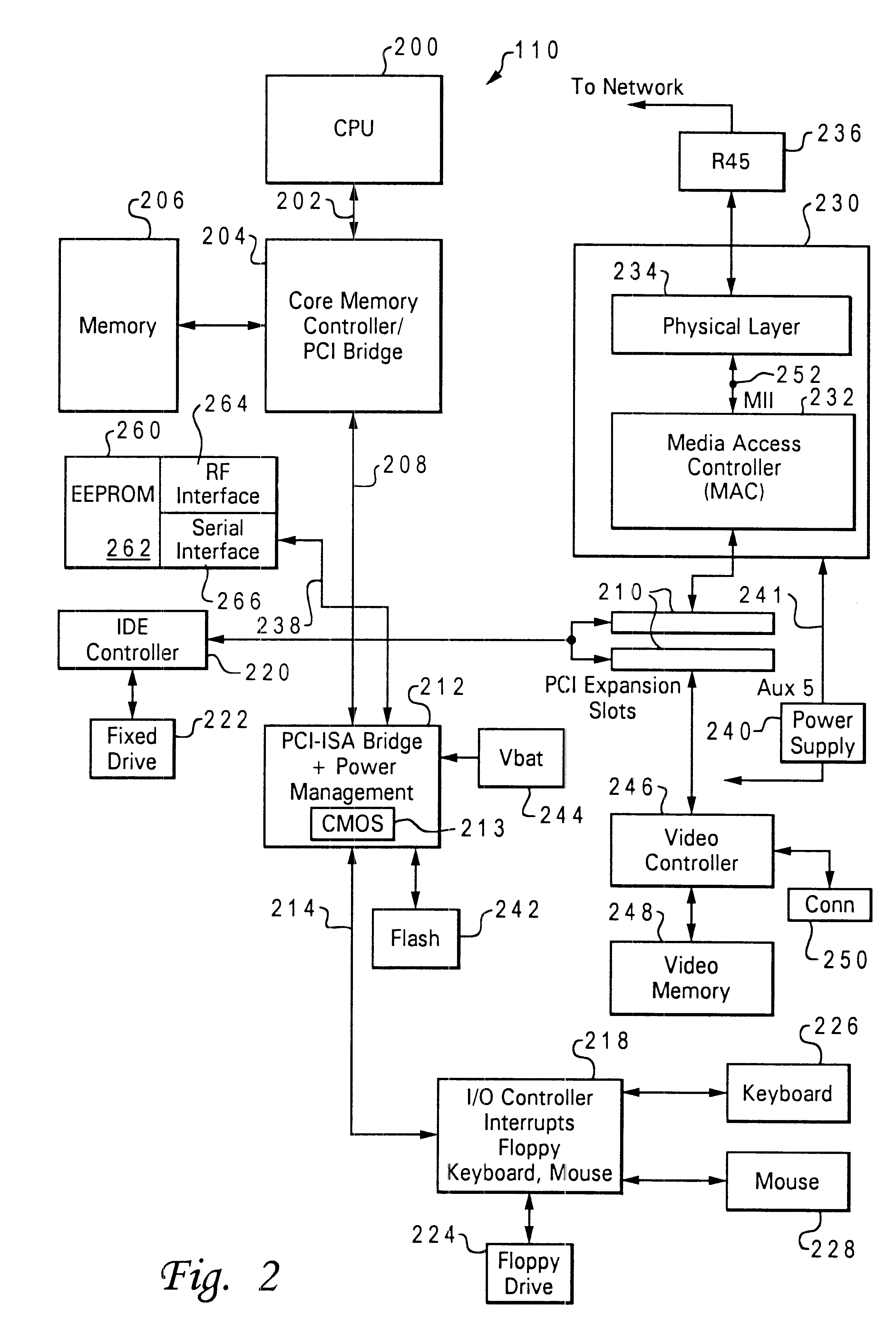
InactiveUS6493104B1Digital computer detailsRadio transmissionData processing systemTelecommunications link
A data processing system and method are described for permitting a portable computer to automatically detect the presence of a printer within a remote area, and responsive to the detection, automatically establishing a communications link with the printer. The portable computer is physically disconnected from the printer. The portable computer transmits a wireless query signal to the remote area. In response to a printer physically located within the remote area receiving the wireless query signal, the printer transmits a wireless reply signal to the remote area. In response to the portable computer receiving the wireless reply signal, the computer automatically establishes a communications link with the printer so that the computer may utilize the printer to print information. The communications link may be established with a printer for which the computer does not include a printer driver necessary for communicating with the printer.
Owner:LENOVO PC INT