Patents
Literature
537 results about "Selection rule" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
In physics and chemistry, a selection rule, or transition rule, formally constrains the possible transitions of a system from one quantum state to another. Selection rules have been derived for electromagnetic transitions in molecules, in atoms, in atomic nuclei, and so on. The selection rules may differ according to the technique used to observe the transition. The selection rule also plays a role in chemical reactions, where some are formally spin forbidden reactions, that is, reactions where the spin state changes at least once from reactants to products.
Apparatus and method for controlling distributed memory cluster
ActiveUS20120209943A1Valid choiceMemory adressing/allocation/relocationDigital computer detailsNode clusteringDistributed memory
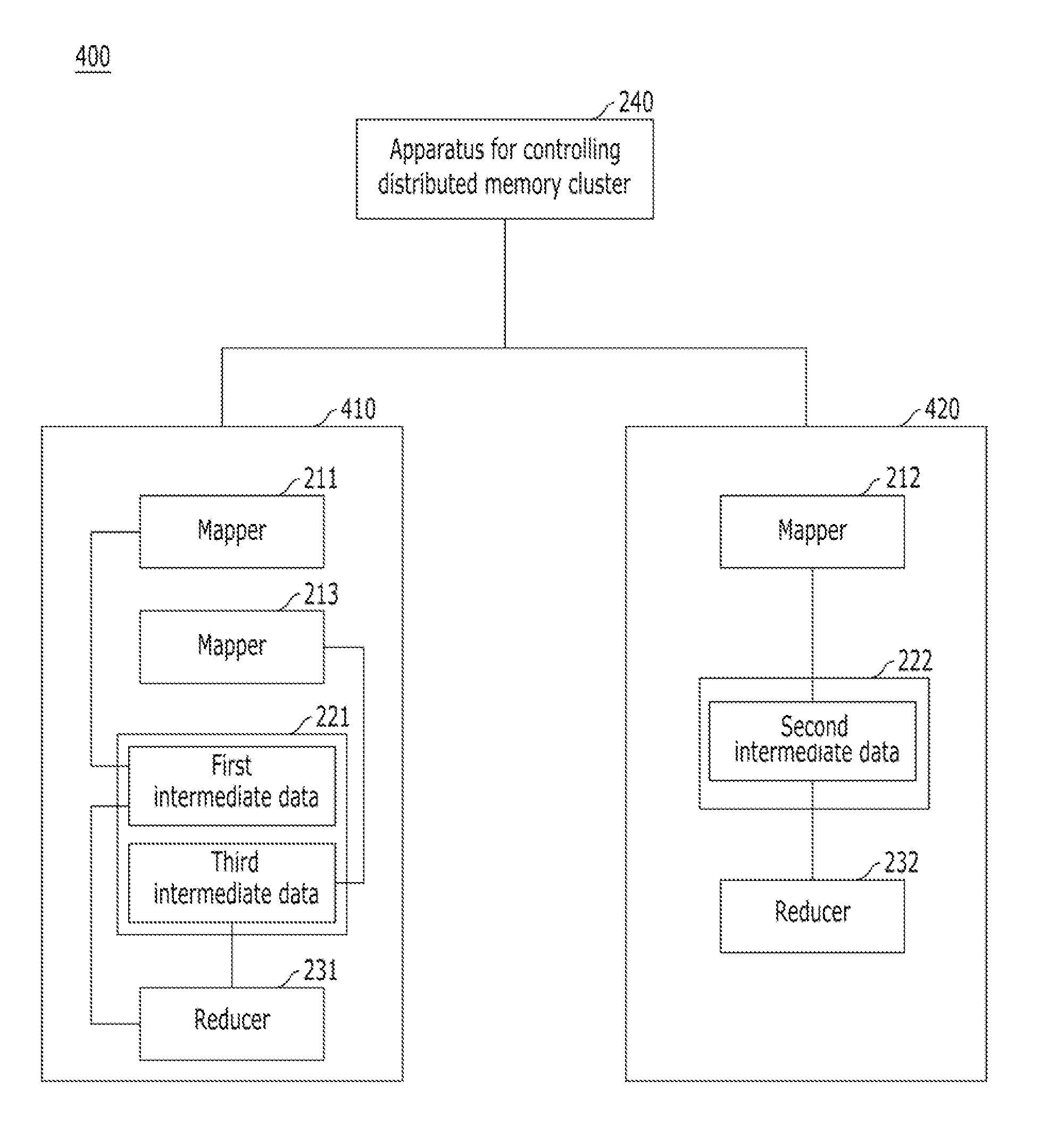
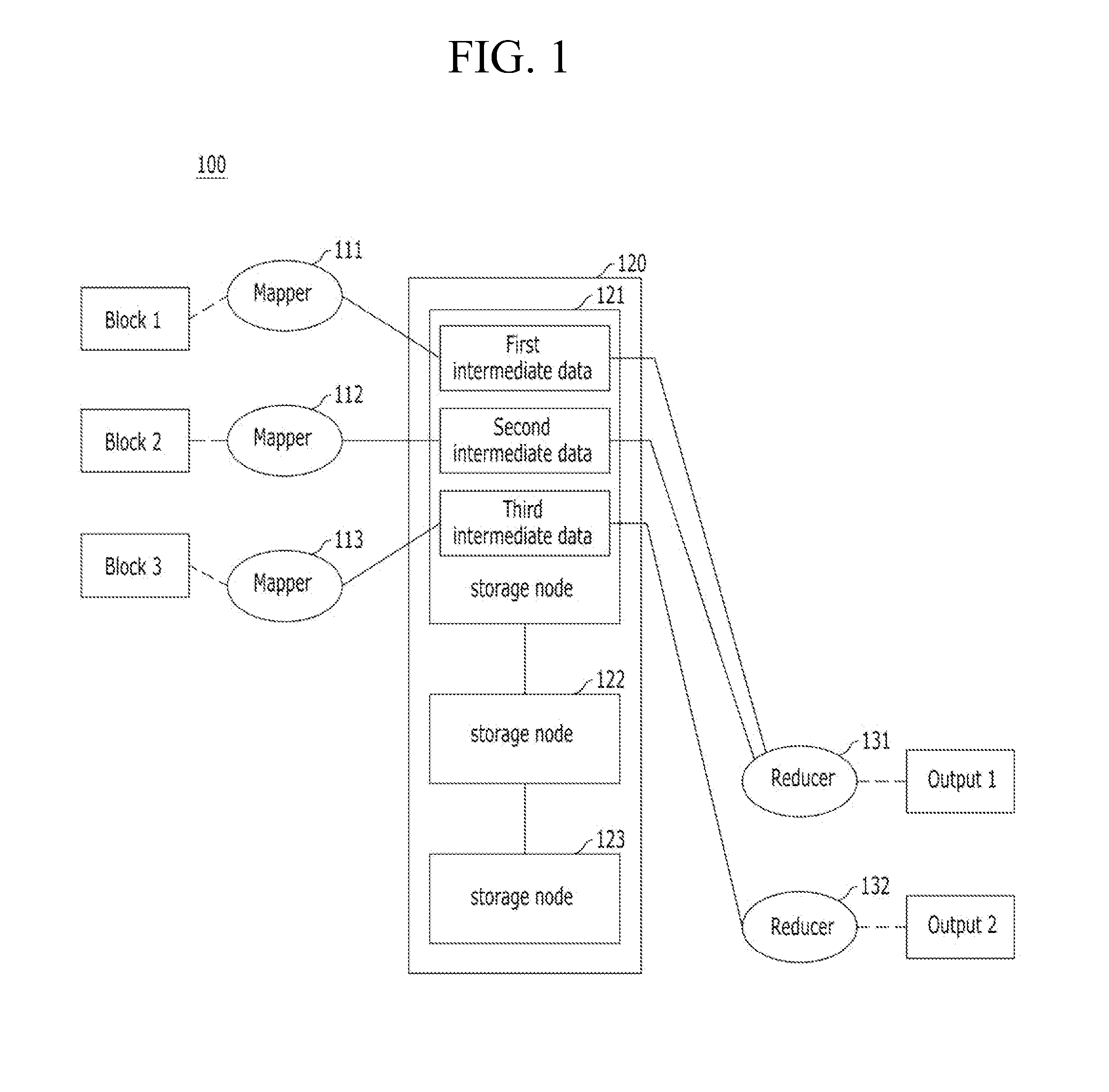
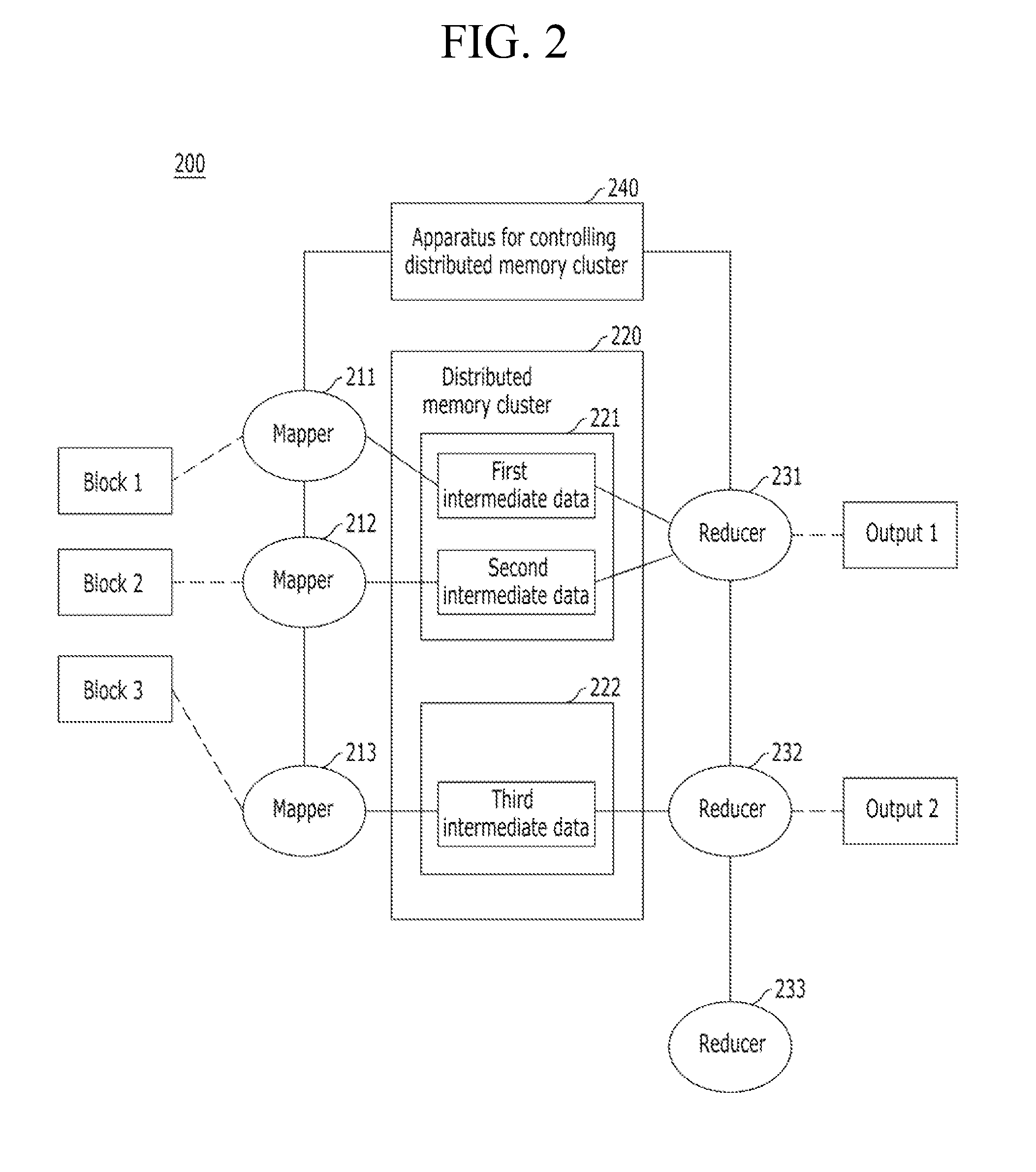
Provided are an apparatus and method for controlling a distributed memory cluster. A distributed computing system may include a computing node cluster, a distributed memory cluster, and a controlling node. The computing node cluster may include a plurality of computing nodes including first computing nodes that each generates associated data. The distributed memory cluster may be configured to store the associated data of the first computing nodes. The controlling node may be configured to select memory blocks of the associated data for distribution on the distributed memory cluster based on a node selection rule and memory cluster structure information, and to select second computing nodes from the computing node cluster based on a location selection rule and the memory cluster structure information.
Owner:KT CORP
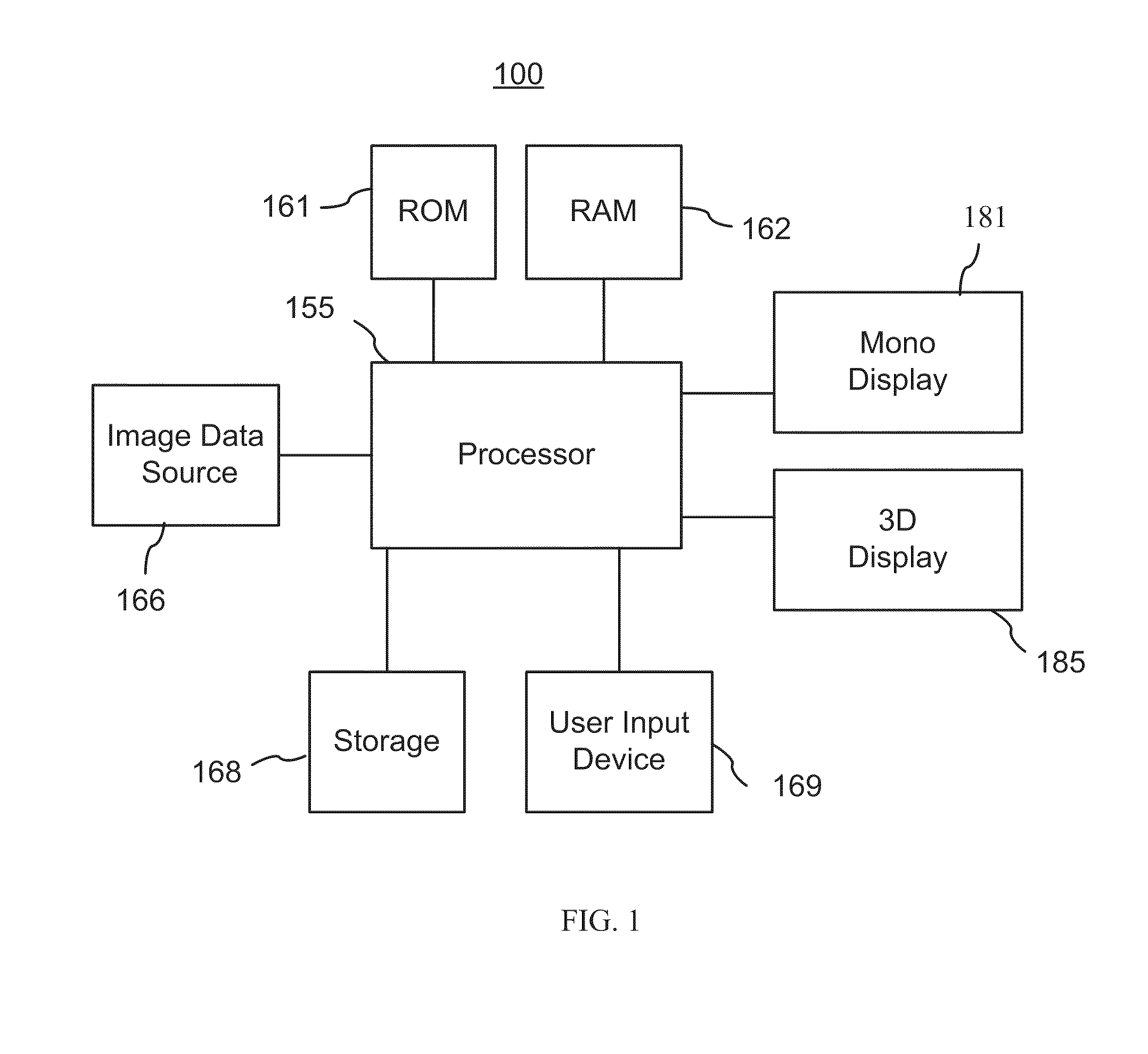
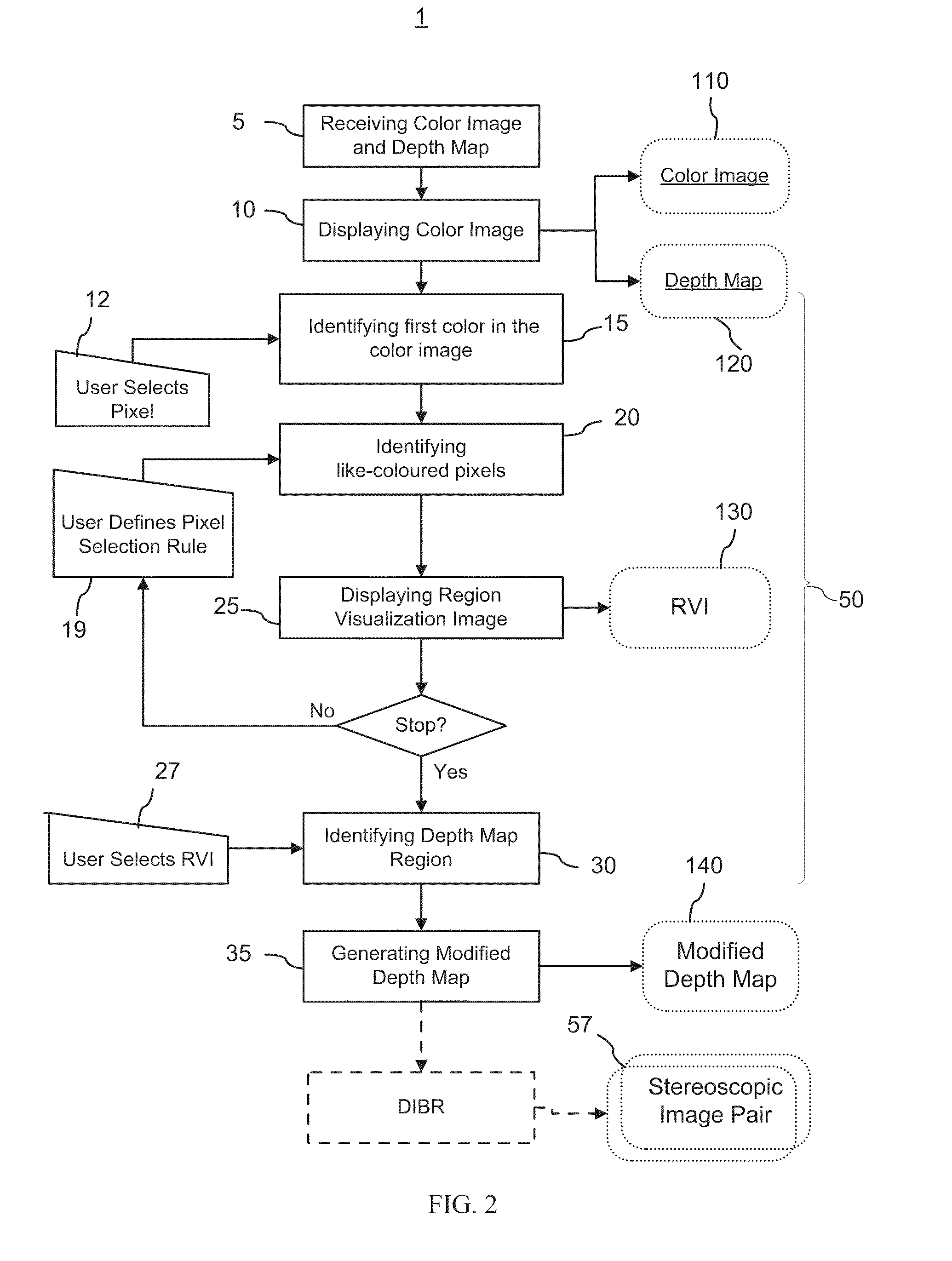
Method and graphical user interface for modifying depth maps
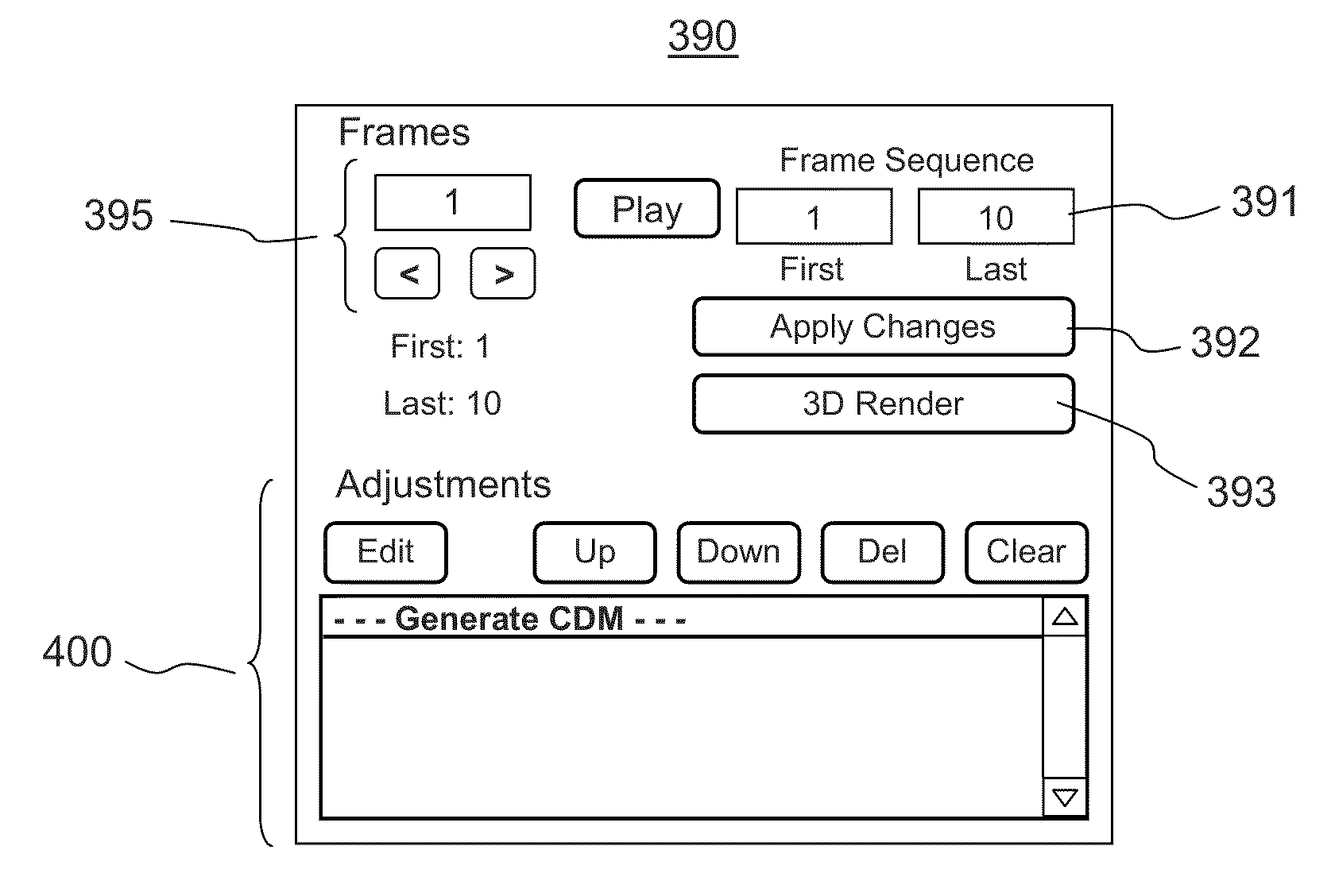
The invention relates to a method and a graphical user interface for modifying a depth map for a digital monoscopic color image. The method includes interactively selecting a region of the depth map based on color of a target region in the color image, and modifying depth values in the thereby selected region of the depth map using a depth modification rule. The color-based pixel selection rules for the depth map and the depth modification rule selected based on one color image from a video sequence may be saved and applied to automatically modify depths maps of other color images from the same sequence.
Owner:HER MAJESTY THE QUEEN & RIGHT OF CANADA REPRESENTED BY THE MIN OF IND THROUGH THE COMM RES CENT
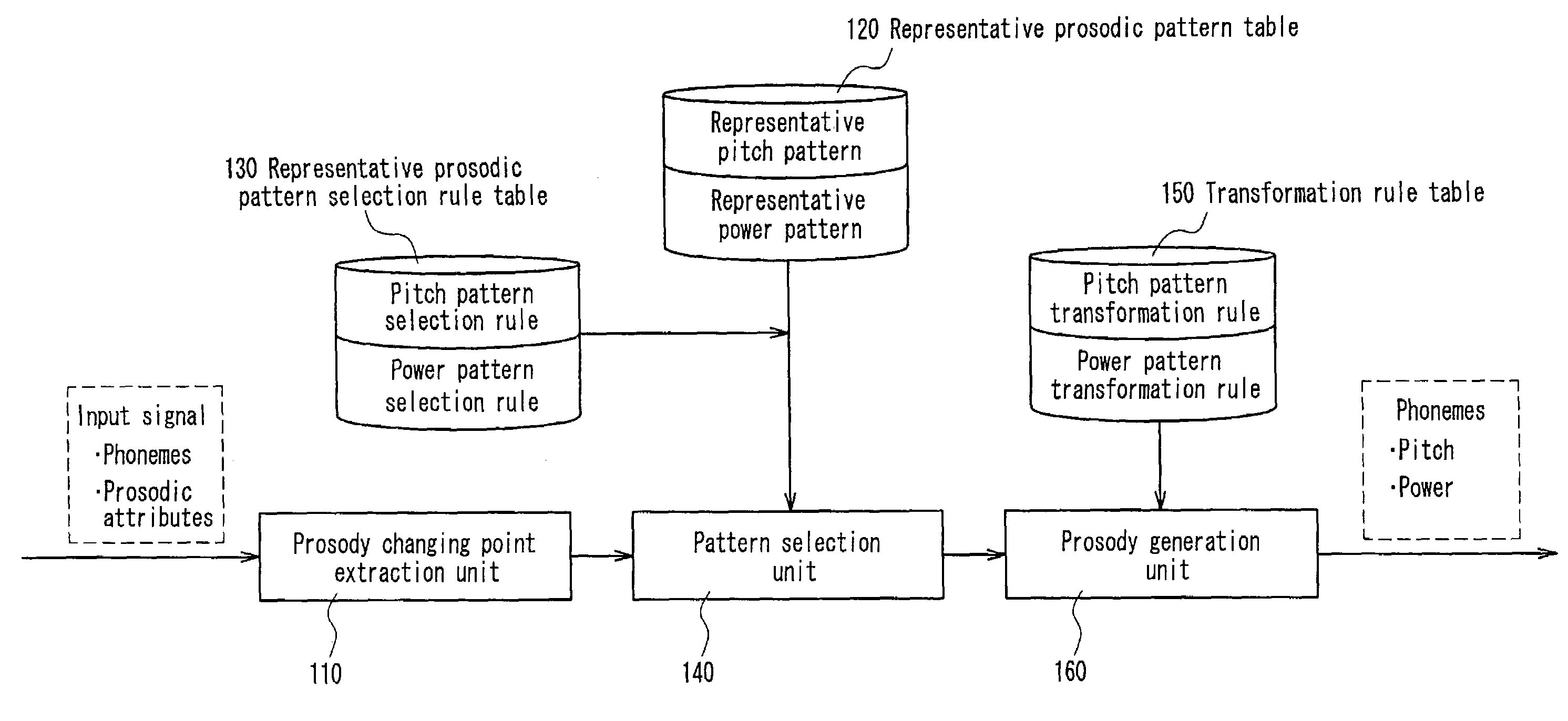
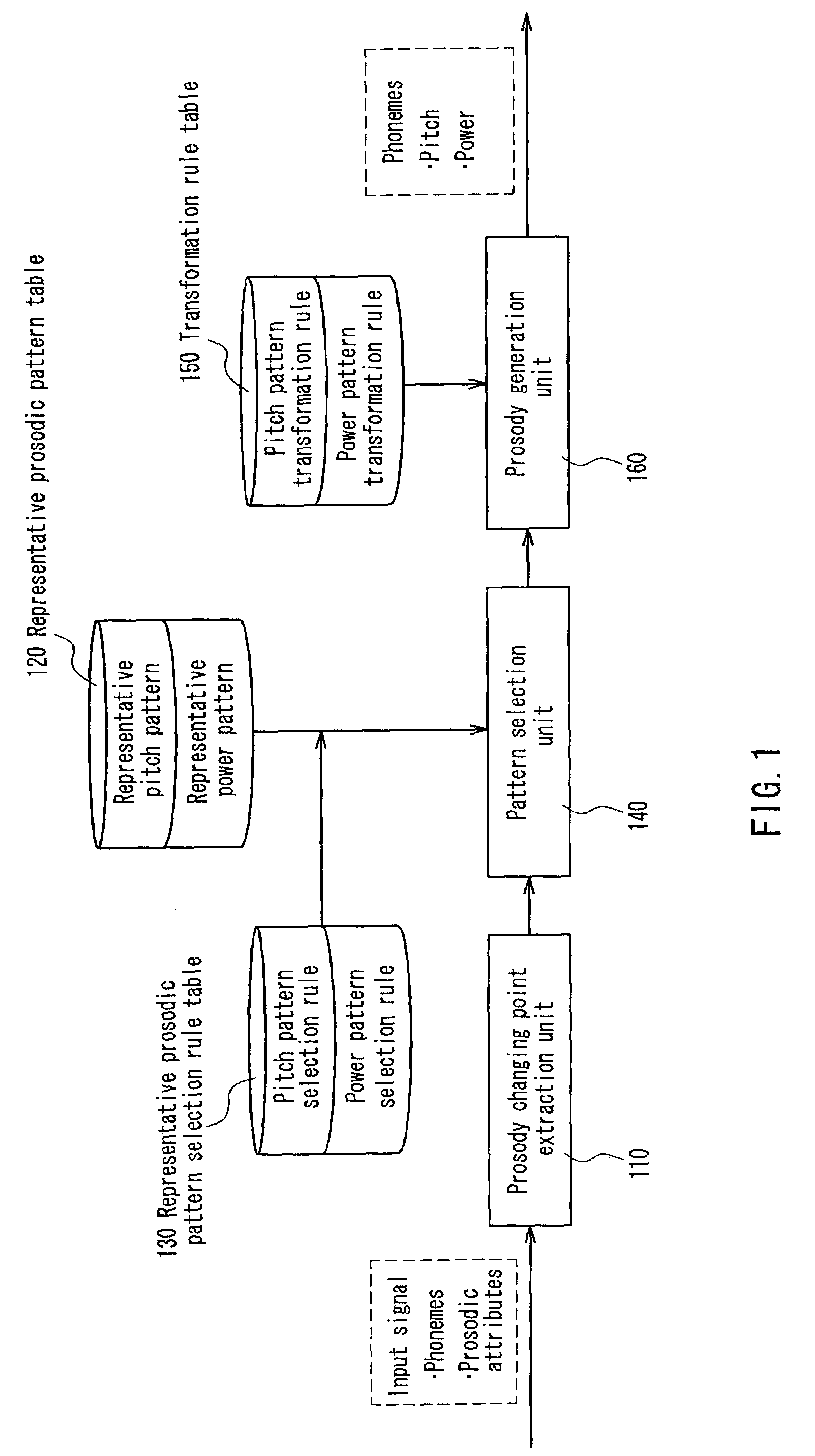
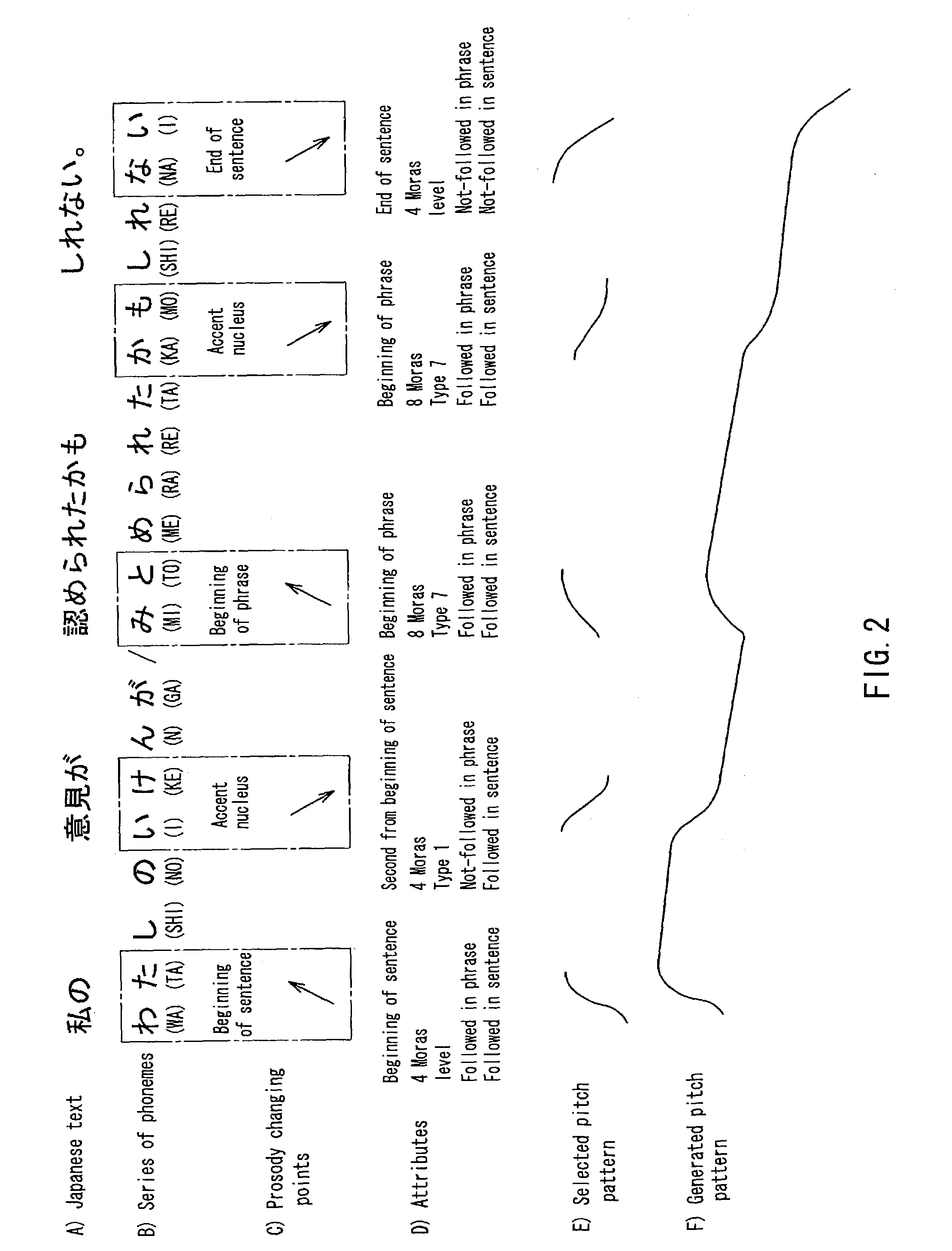
Prosody generating device, prosody generating method, and program
ActiveUS7200558B2Suppression of distortionSpeech recognitionSpecial data processing applicationsStatistical learningPattern selection
A prosody generation apparatus capable of suppressing distortion that occurs when generating prosodic patterns and therefore generating a natural prosody is provided. A prosody changing point extraction unit in this apparatus extracts a prosody changing point located at the beginning and the ending of a sentence, the beginning and the ending of a breath group, an accent position and the like. A selection rule and a transformation rule of a prosodic pattern including the prosody changing point is generated by means of a statistical or learning technique and the thus generate rules are stored in a representative prosodic pattern selection rule table and a transformation rule table beforehand. A pattern selection unit selects a representative prosodic pattern from the representative prosodic pattern selection rule table according to the selection rule. A prosody generation unit transforms the selected pattern according to the transformation rule and carries out interpolation with respect to portions other than the prosody changing points so as to generate prosody as a whole.
Owner:SOVEREIGN PEAK VENTURES LLC
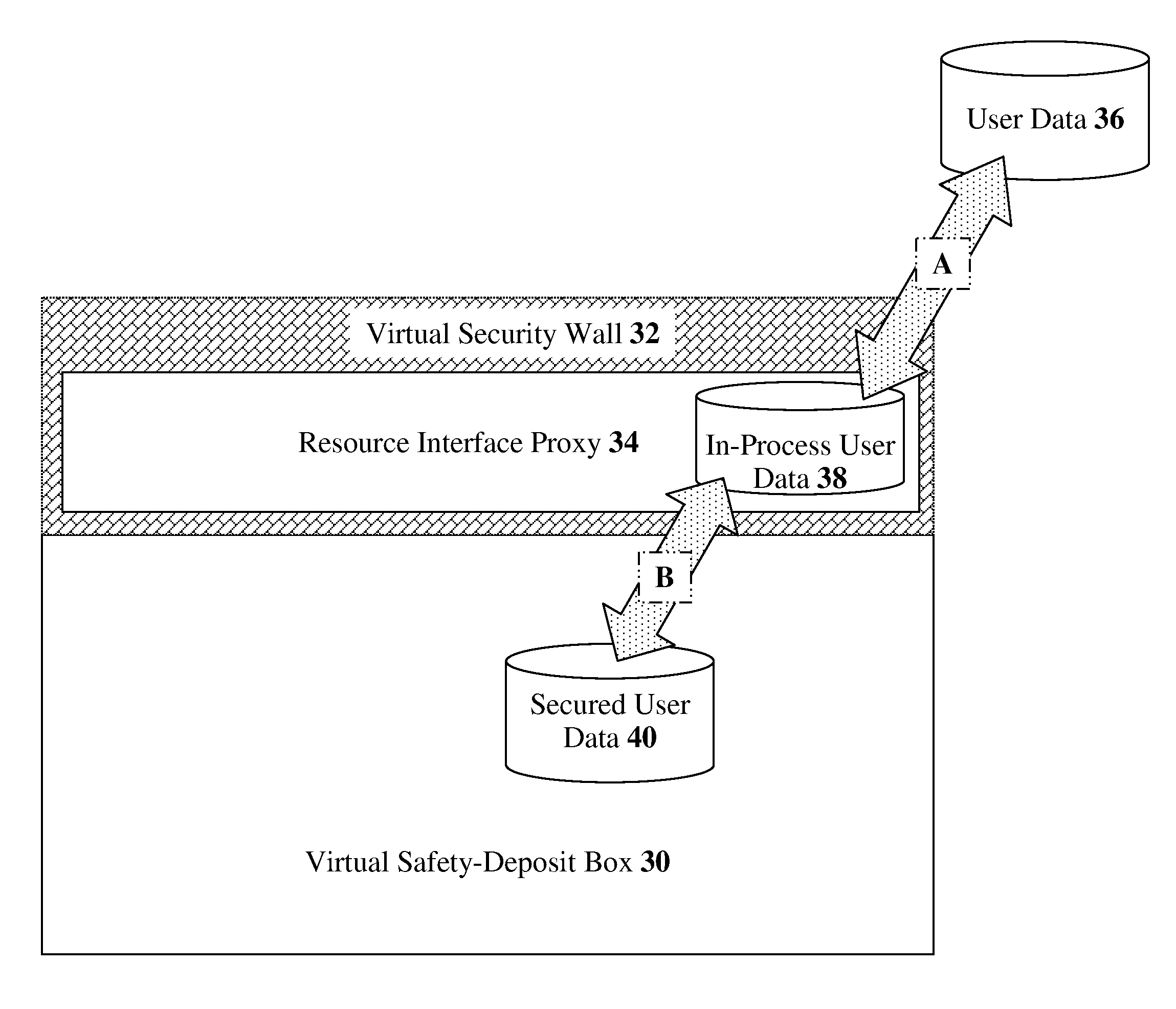
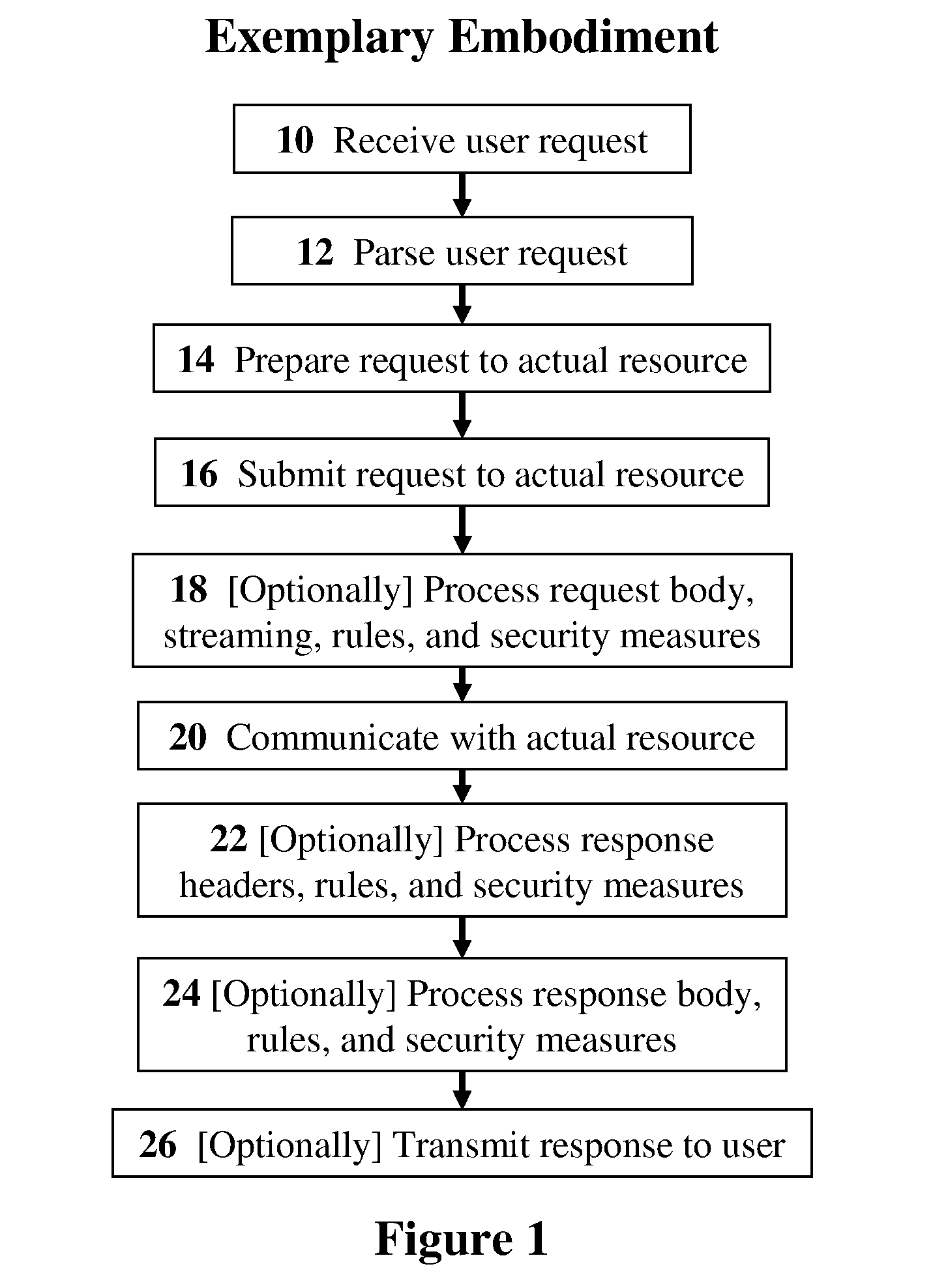
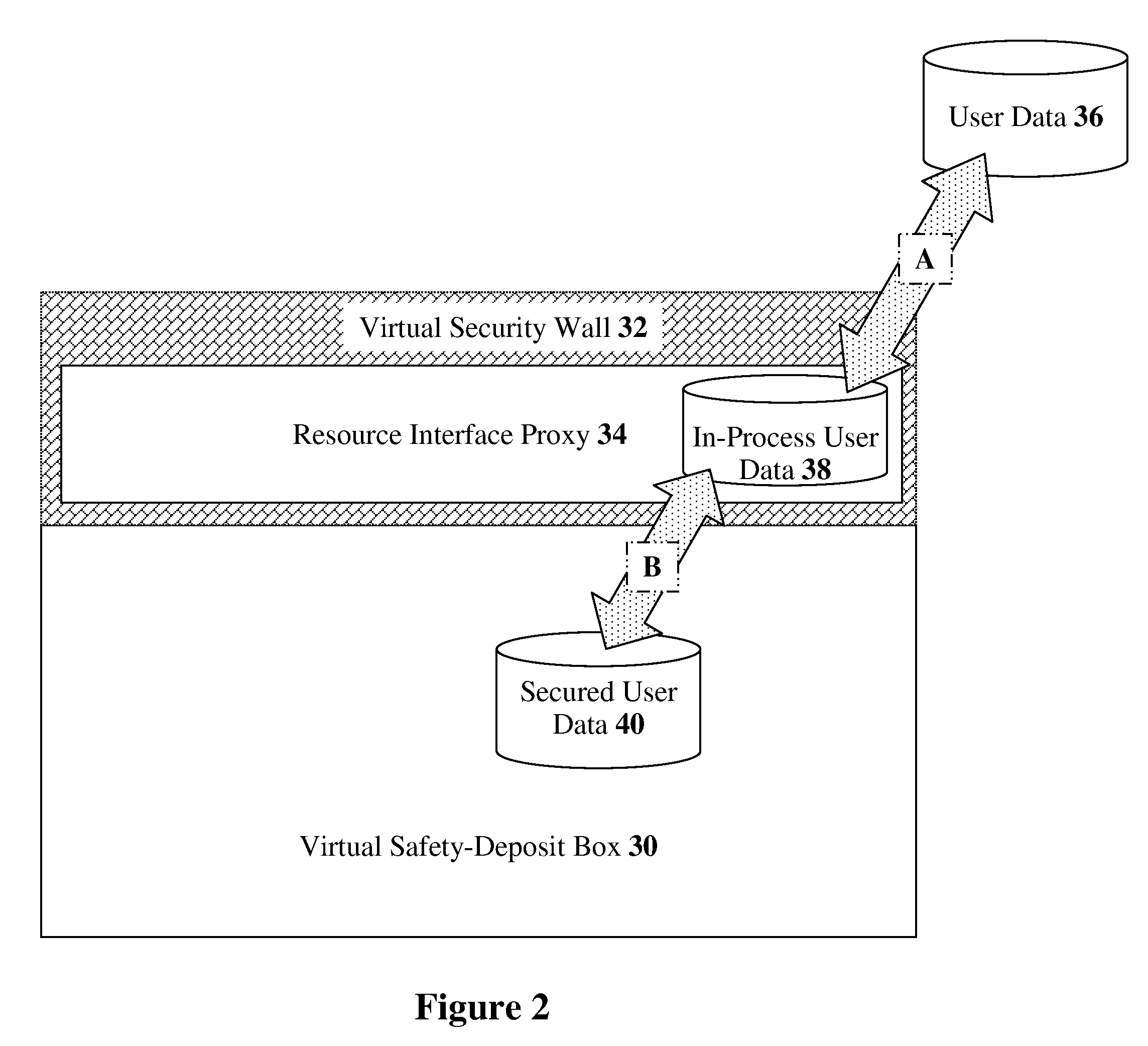
Methods, devices, and media for securely utilizing a non-secured, distributed, virtualized network resource with applications to cloud-computing security and management
InactiveUS20110072489A1Full securityFull controlDigital data protectionMultiple digital computer combinationsVirtualizationData stream
The present invention discloses methods, devices, and media for securely utilizing a non-secured, distributed, virtualized network resource with applications to cloud-computing security and management. Methods including the steps of: receiving, by a deployed security mechanism, a user request over a network; parsing the user request by the deployed security mechanism; preparing, including applying security measures, the user request to transmit to a computing-service resource; and submitting, by the deployed security mechanism, the user request to the computing-service resource. Methods further including the steps of: dividing an original data stream into a set of split data streams; applying a first invertible transformation function to the split data streams, which produces an intermediate set of data streams; and extracting a final set of data streams from the intermediate set by applying a selection rule which produces the final set, thereby transforming the original data stream into individually-unintelligible parts.
Owner:PORTICOR
Method for allocating shared computing infrastructure for application server-based deployments
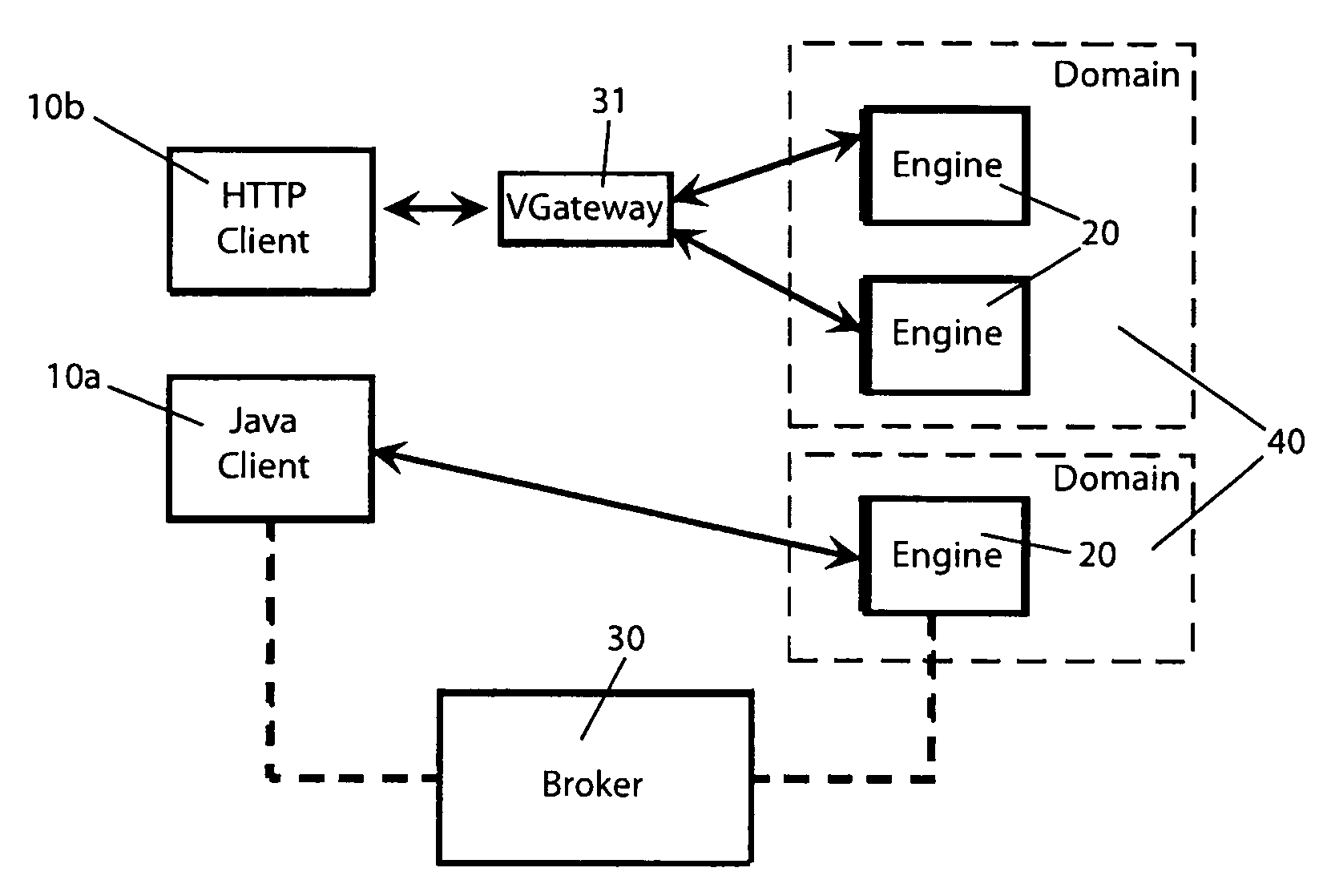
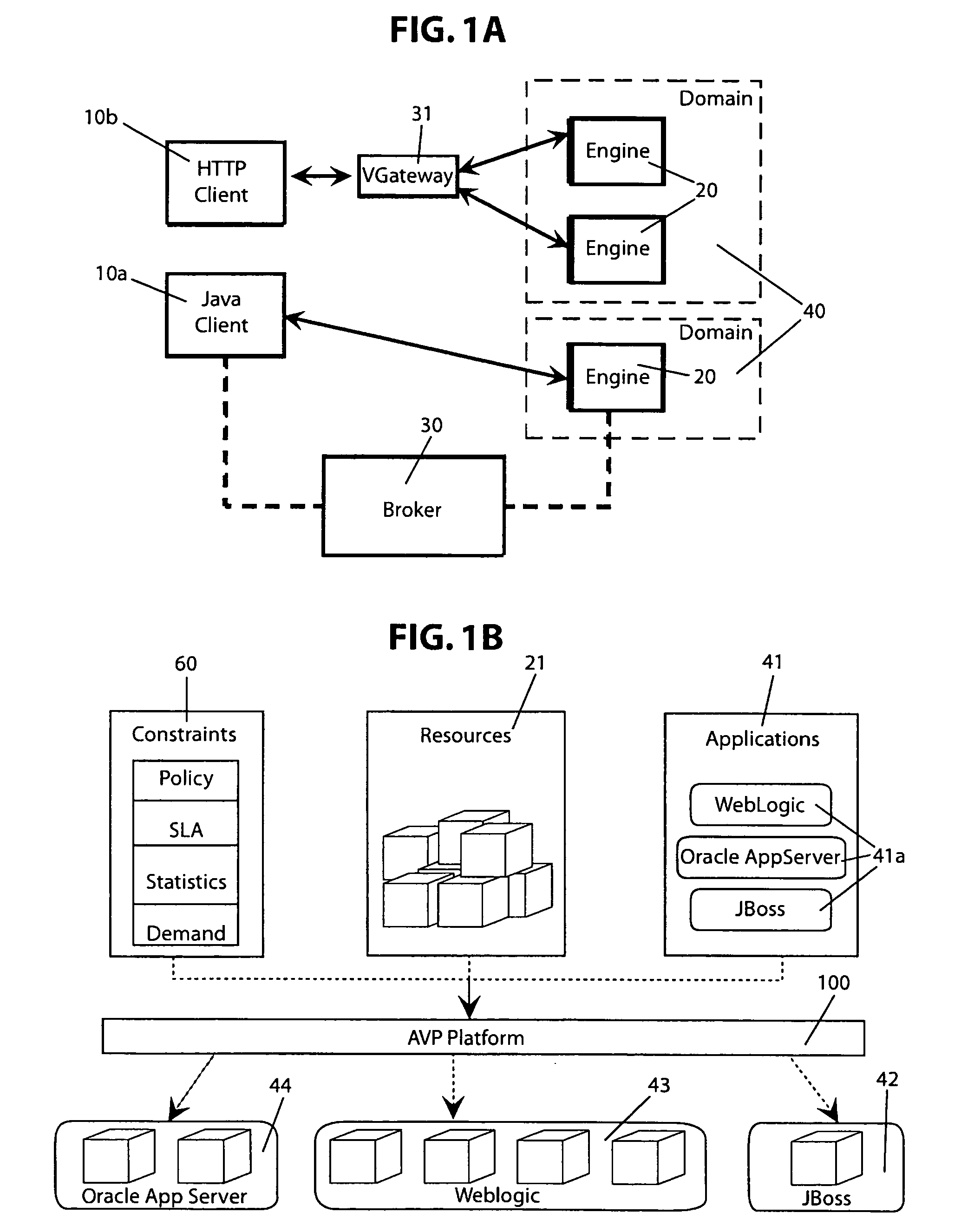
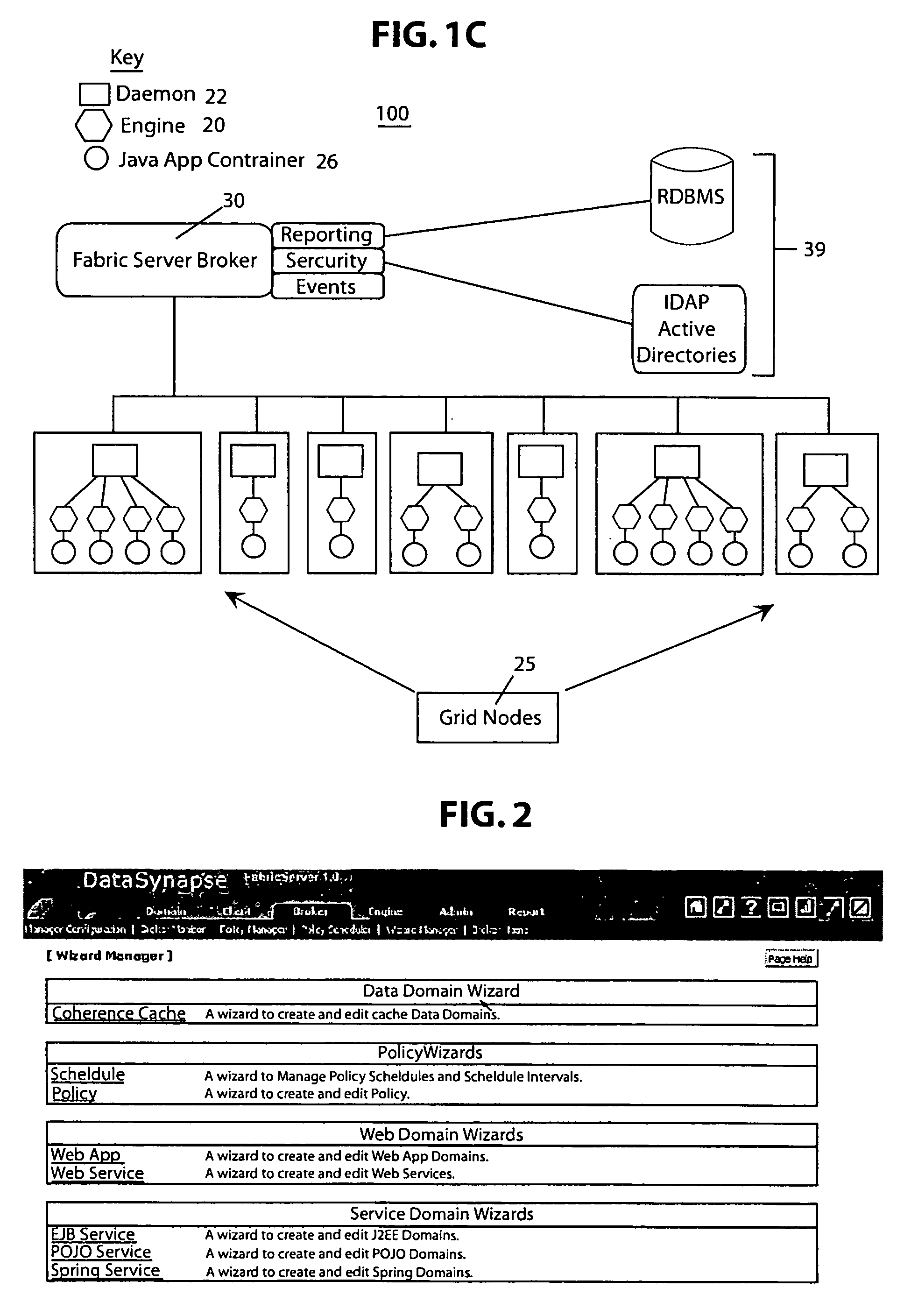
A shared computing infrastructure includes a plurality of computing engines, applications servers, and computing domains. A broker component executes a method for dynamically allocating the computing engines among the computing domains. The allocation method begins with the step of determining an expected number of computing engines to be allocated to each of the computing domains as a function of a predetermined service policy and a predicted demand for the domain While fewer than the expected number of computing engines has been allocated to each domain, the computing domains are sequentially selecting as a function of predetermined domain priorities. Unallocated computing engines are identified, and the unallocated computing engines are allocated to each selected computing domain according to predetermined selection rules for the domain. During an allocation improvement step, allocations among the computing domains are further adjusted to maximize a fitness statistic computed for the allocations.
Owner:CLOUD SOFTWARE GRP INC
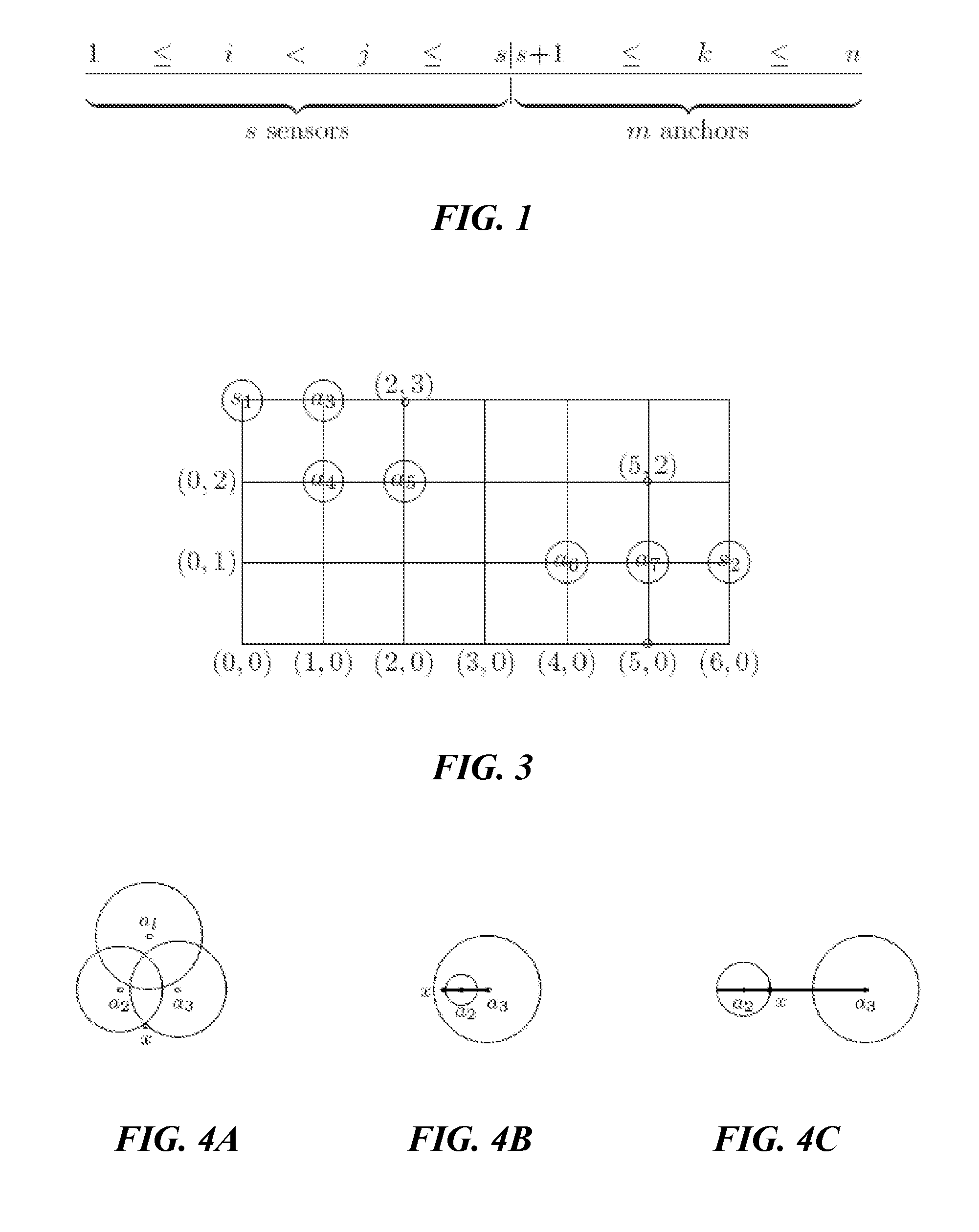
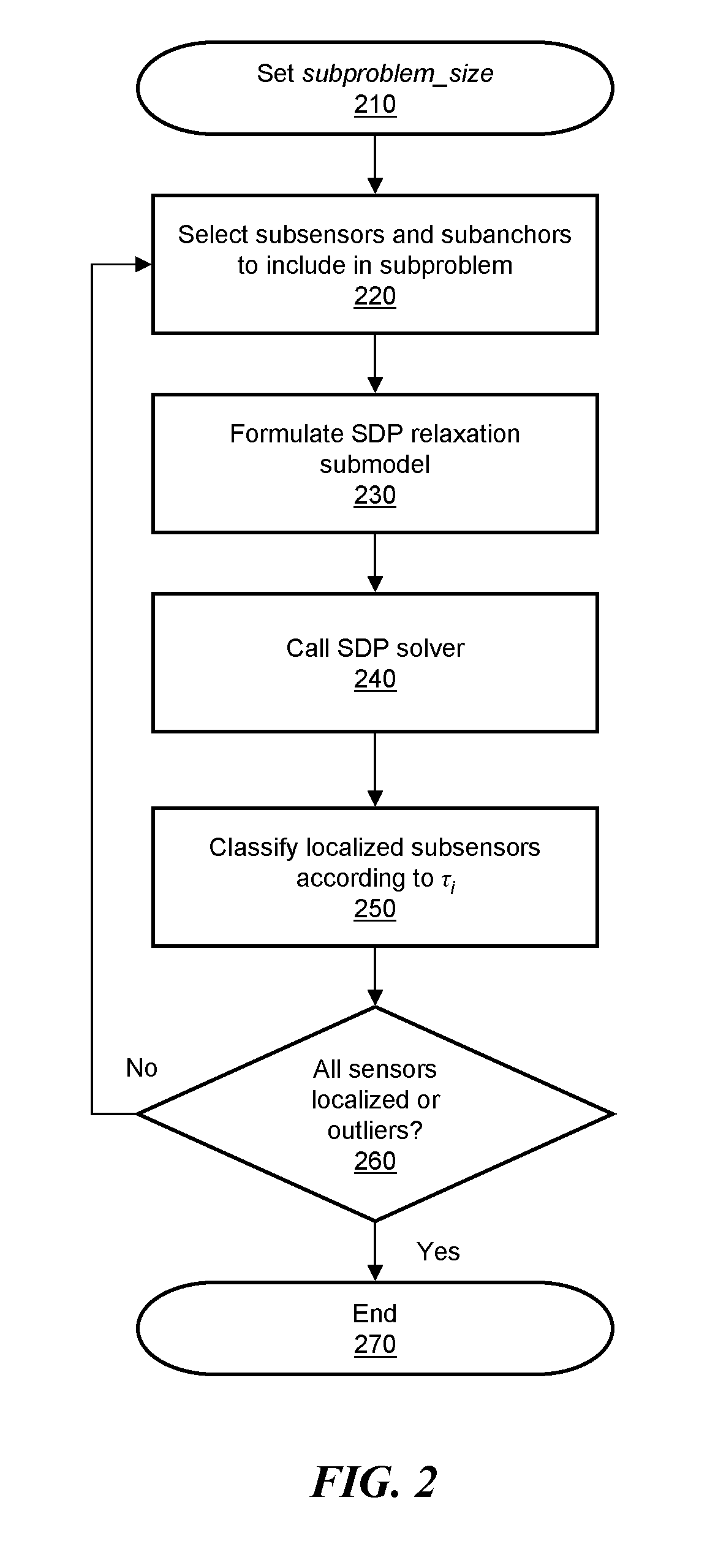
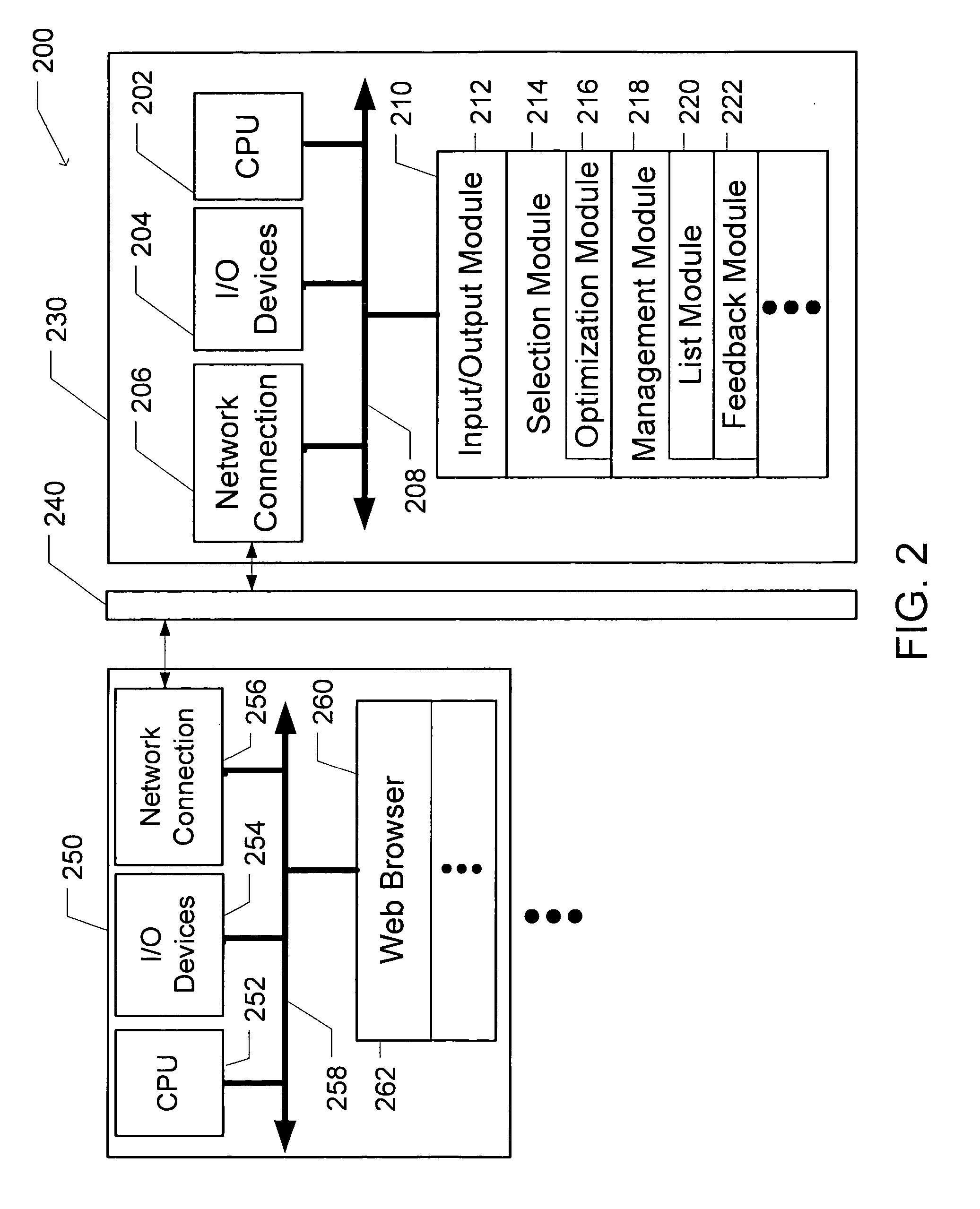
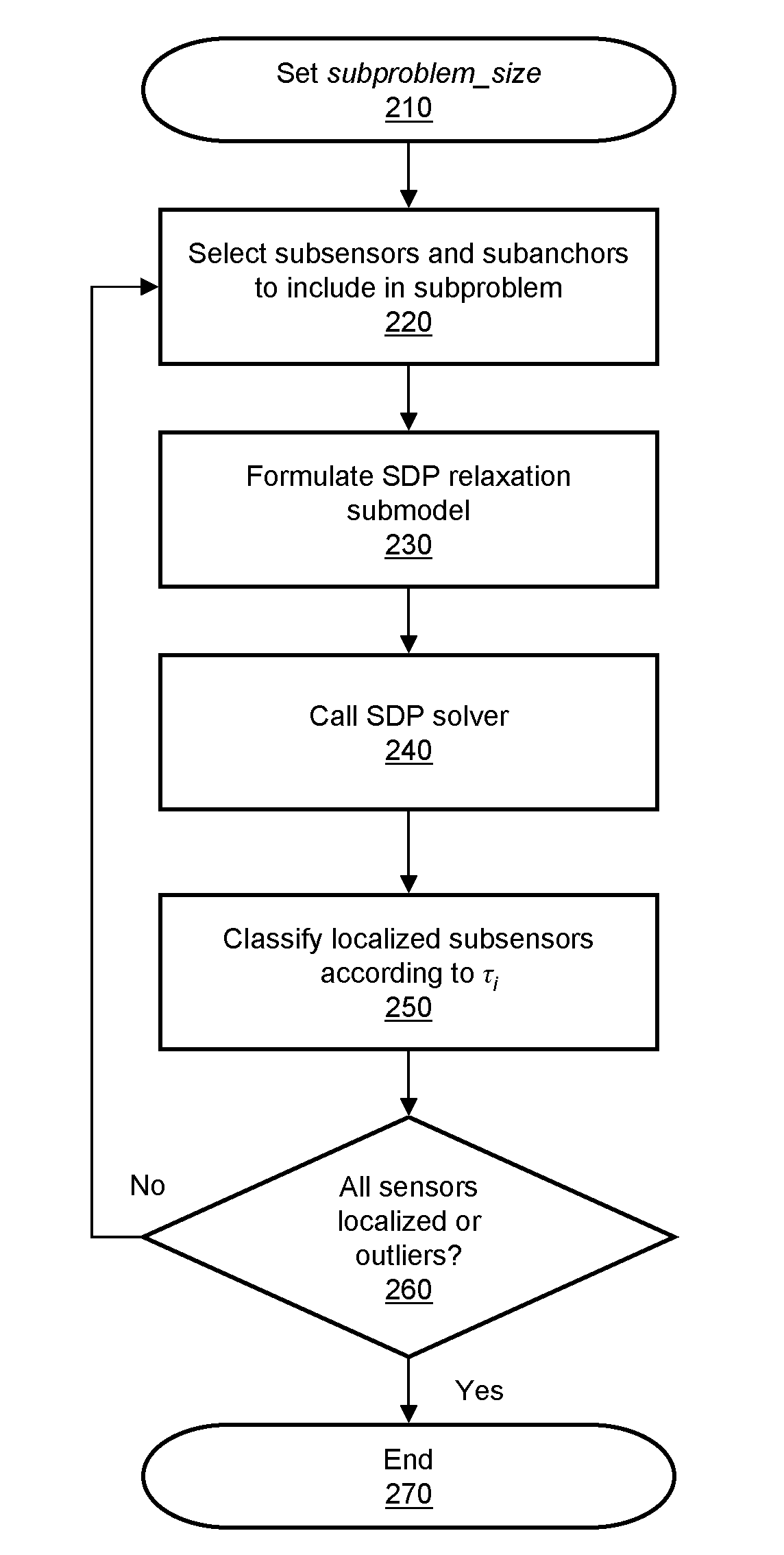
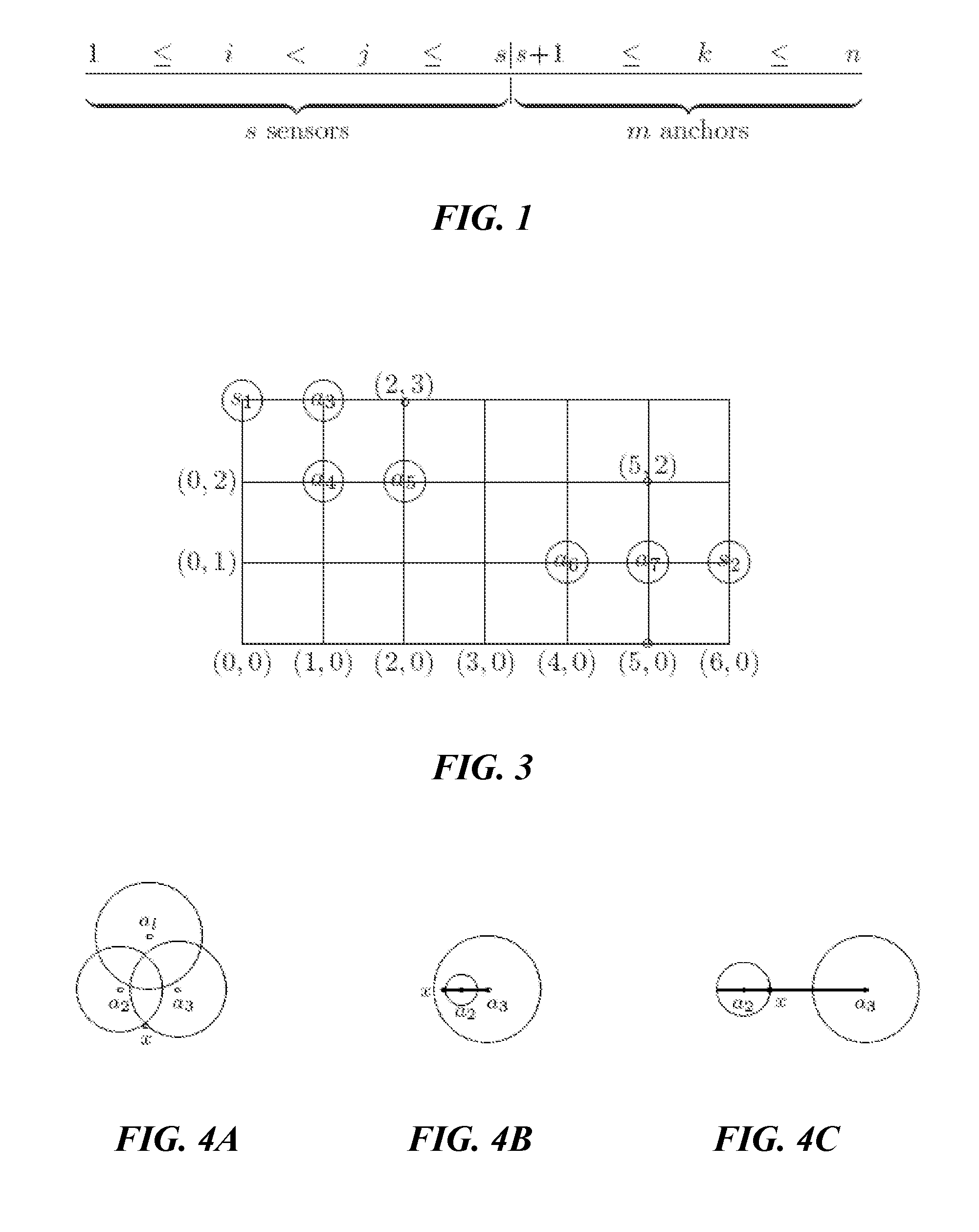
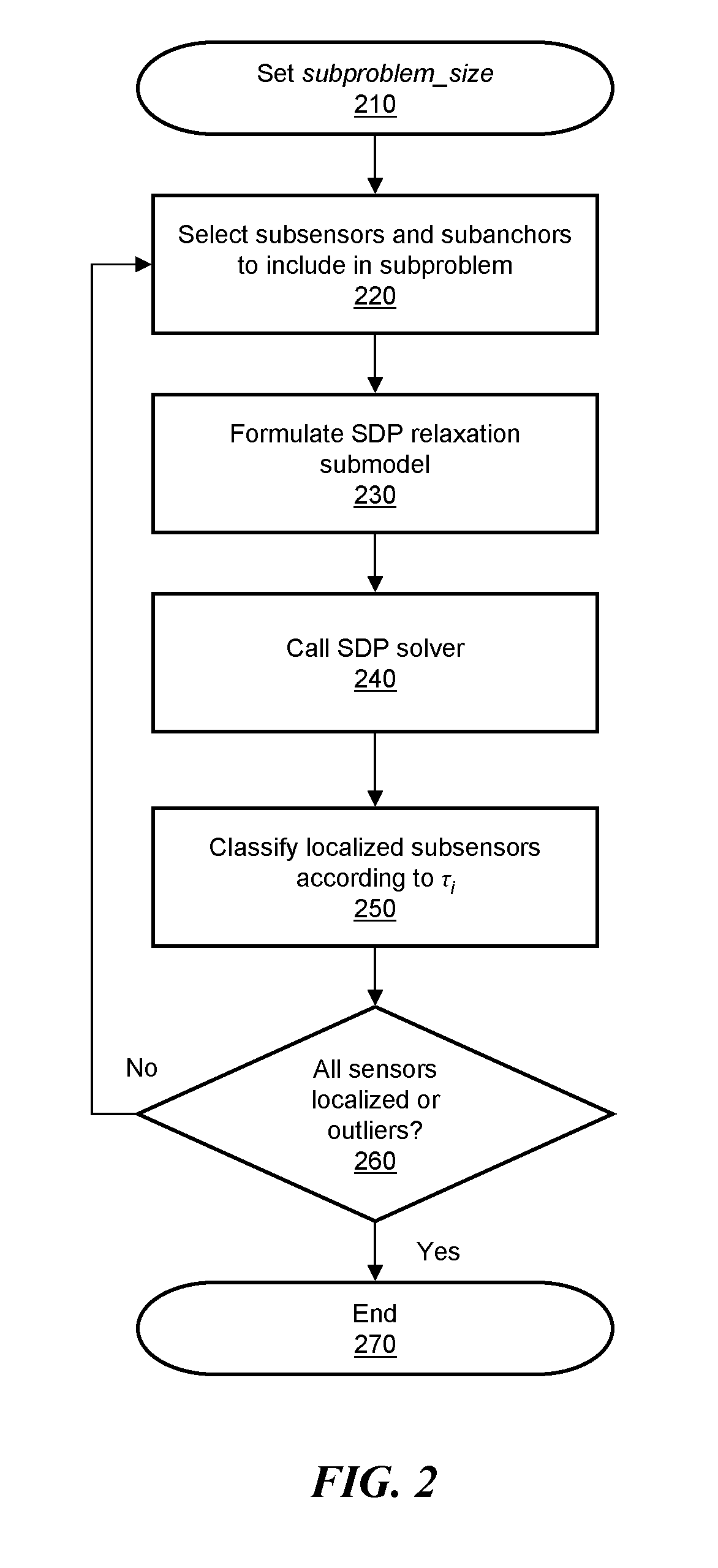
Scalable sensor localization for wireless sensor networks
ActiveUS20070005292A1Error minimizationSolve small or large problems more accuratelyNetwork traffic/resource managementNetwork topologiesWireless sensor networkingComputer science
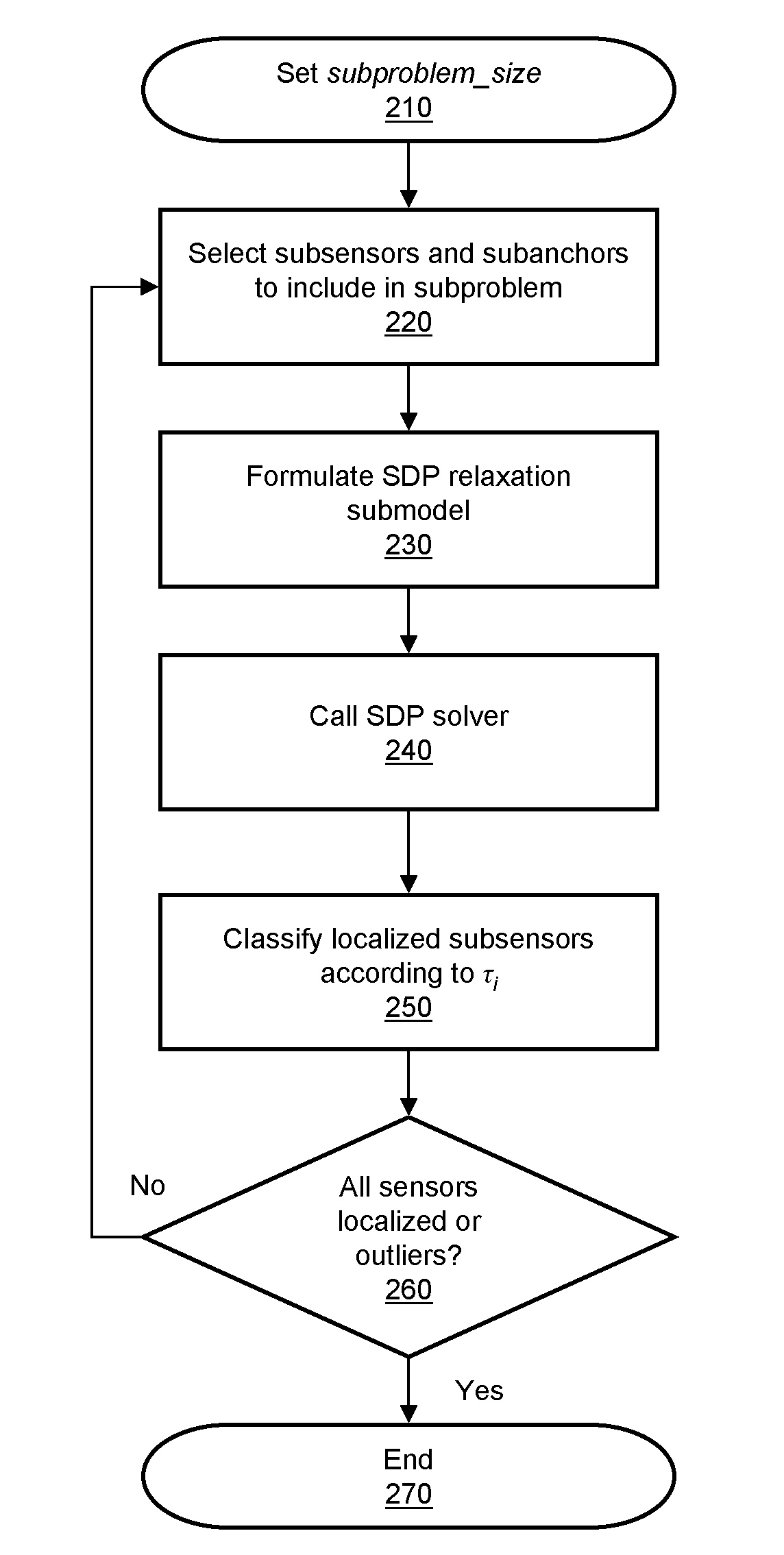
Adaptive rule-based methods to solve localization problems for ad hoc wireless sensor networks are disclosed. A large problem may be solved as a sequence of very small subproblems, each of which is solved by semidefinite programming relaxation of a geometric optimization model. The subproblems may be generated according to a set of sensor / anchor selection rules and a priority list. The methods scale well and provide improved positioning accuracy. A dynamic version may be used for estimating moving sensors locations in a real-time environment. The method may use dynamic distance measurement updates among sensors, and utilizes subproblem solving for static sensor localization. Methods to deploy sensor localization algorithms in clustered distributed environments are also provided, permitting application to arbitrarily large networks. In addition, the methods may be used to solve sensor localizations in 2D or 3D space. A preprocessor may be used for localization of networks without absolute position information.
Owner:THE BOARD OF TRUSTEES OF THE LELAND STANFORD JUNIOR UNIV
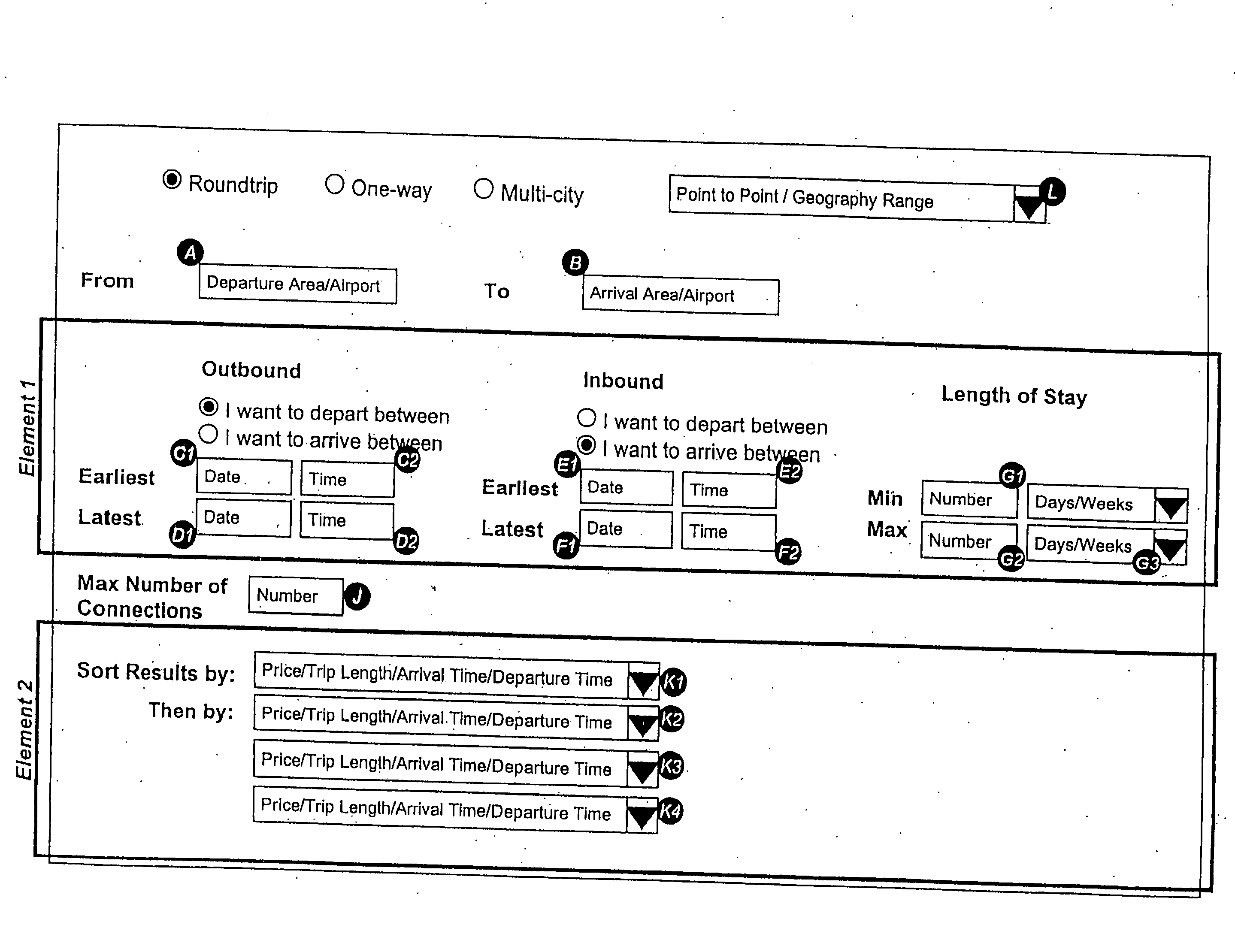
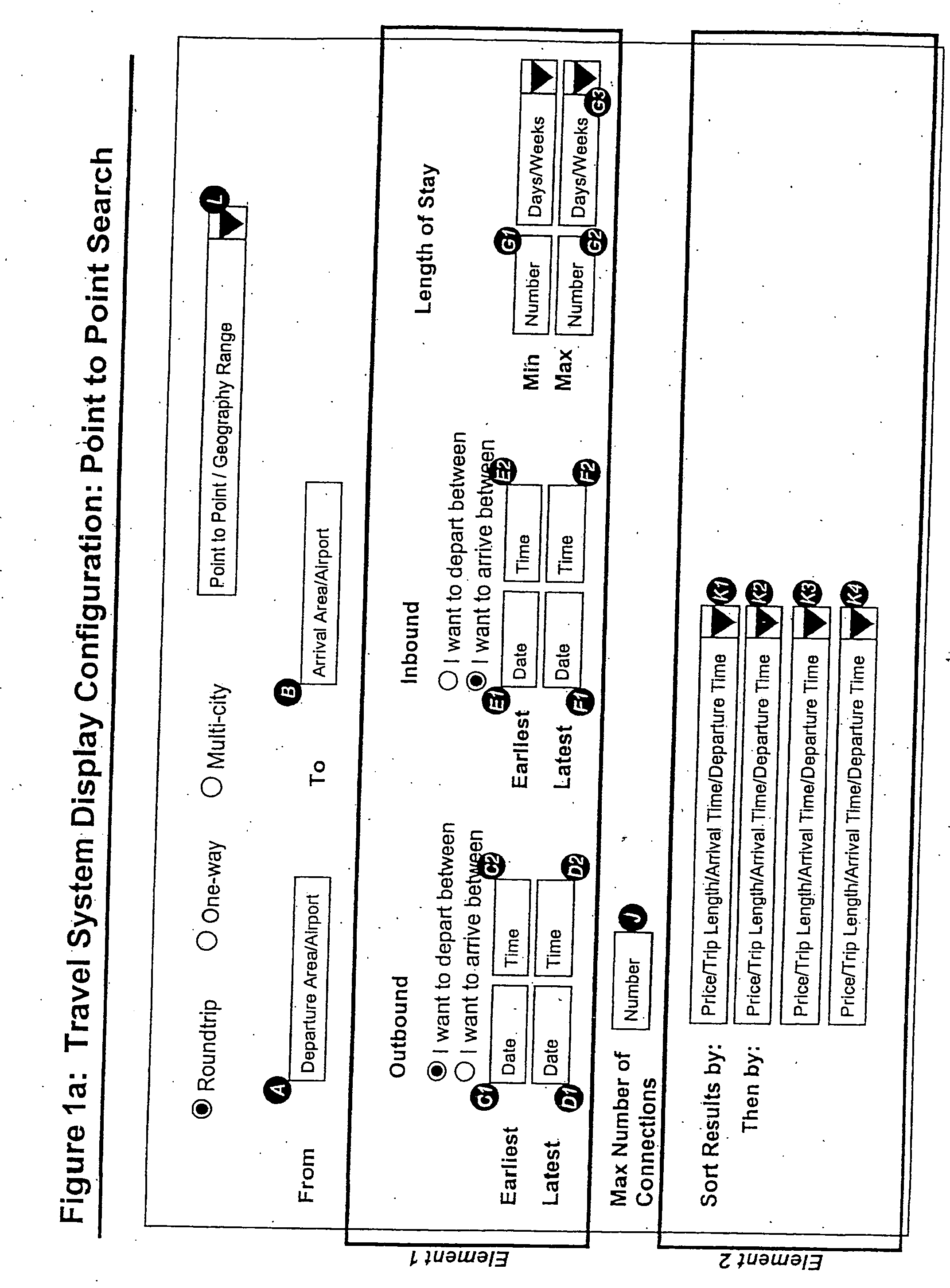
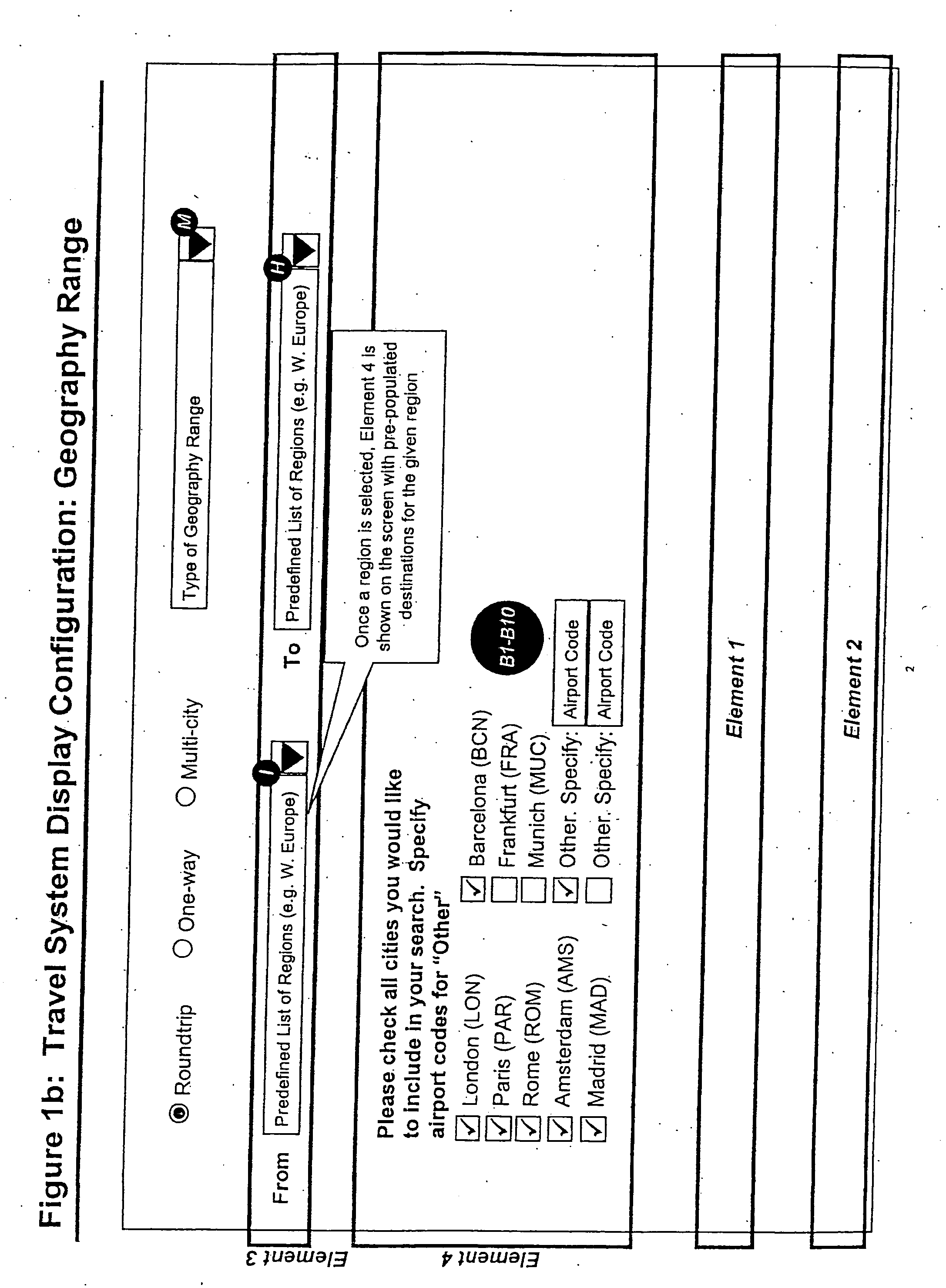
Bounded flexibility search and interface for travel reservations
InactiveUS20050043974A1Less time-consumingReservationsSpecial data processing applicationsSystem usageComputer science
Owner:VASSILEV ASSEN +1
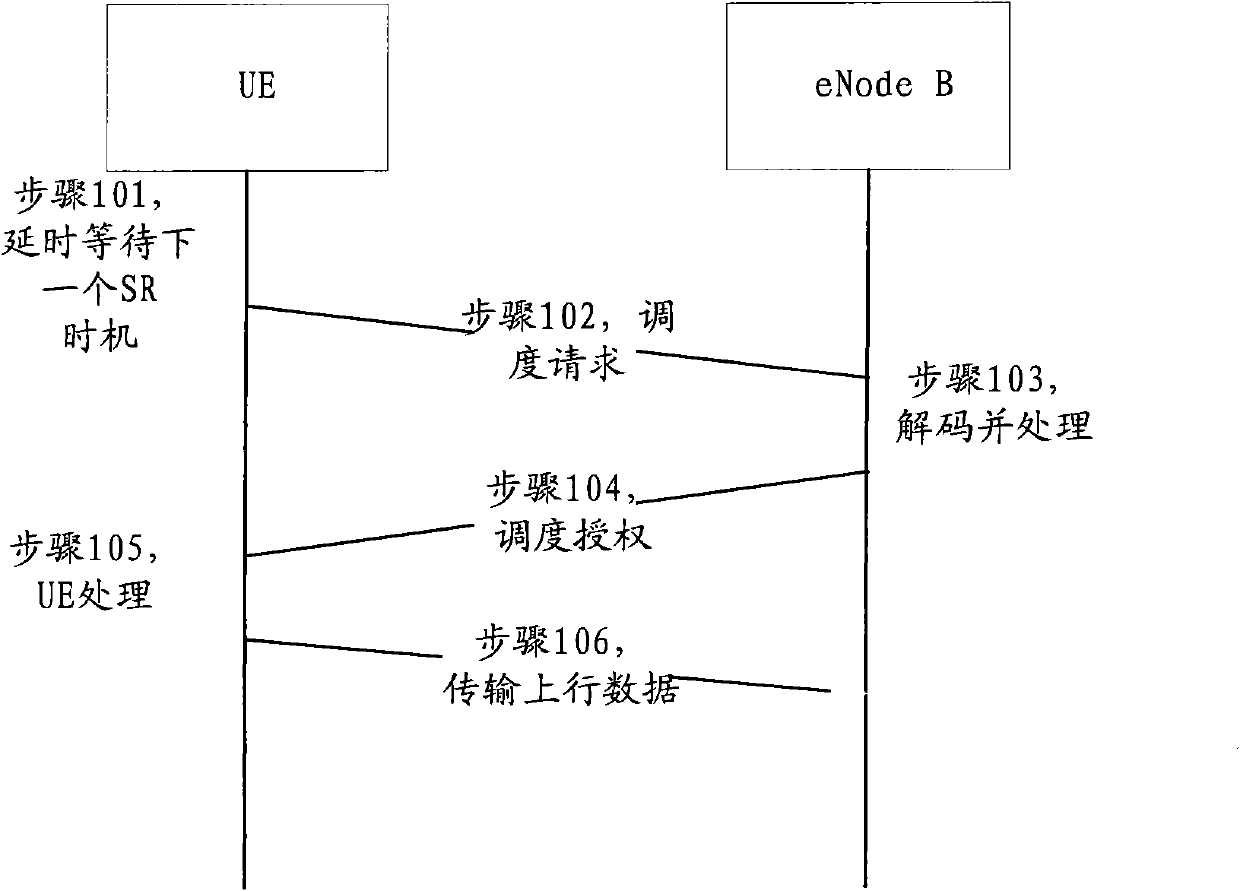
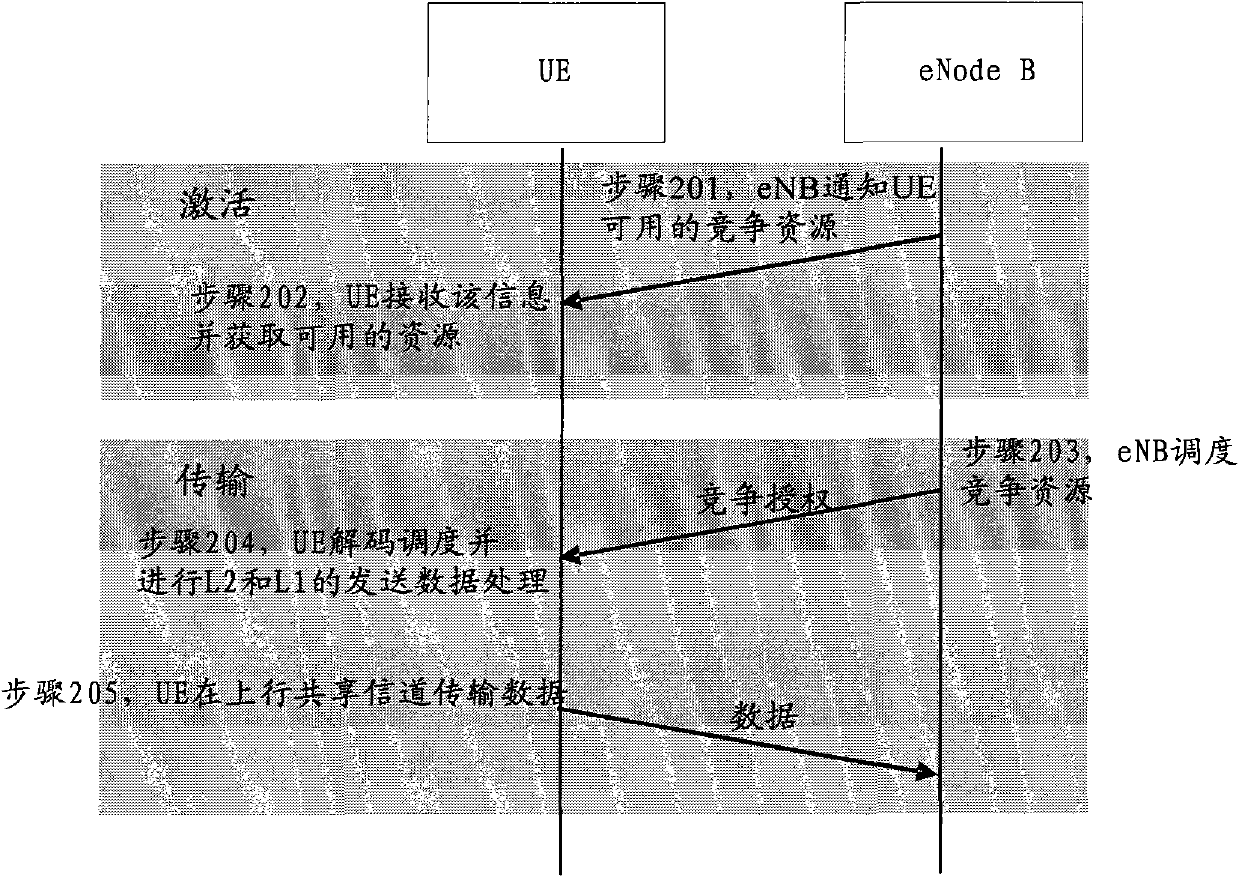
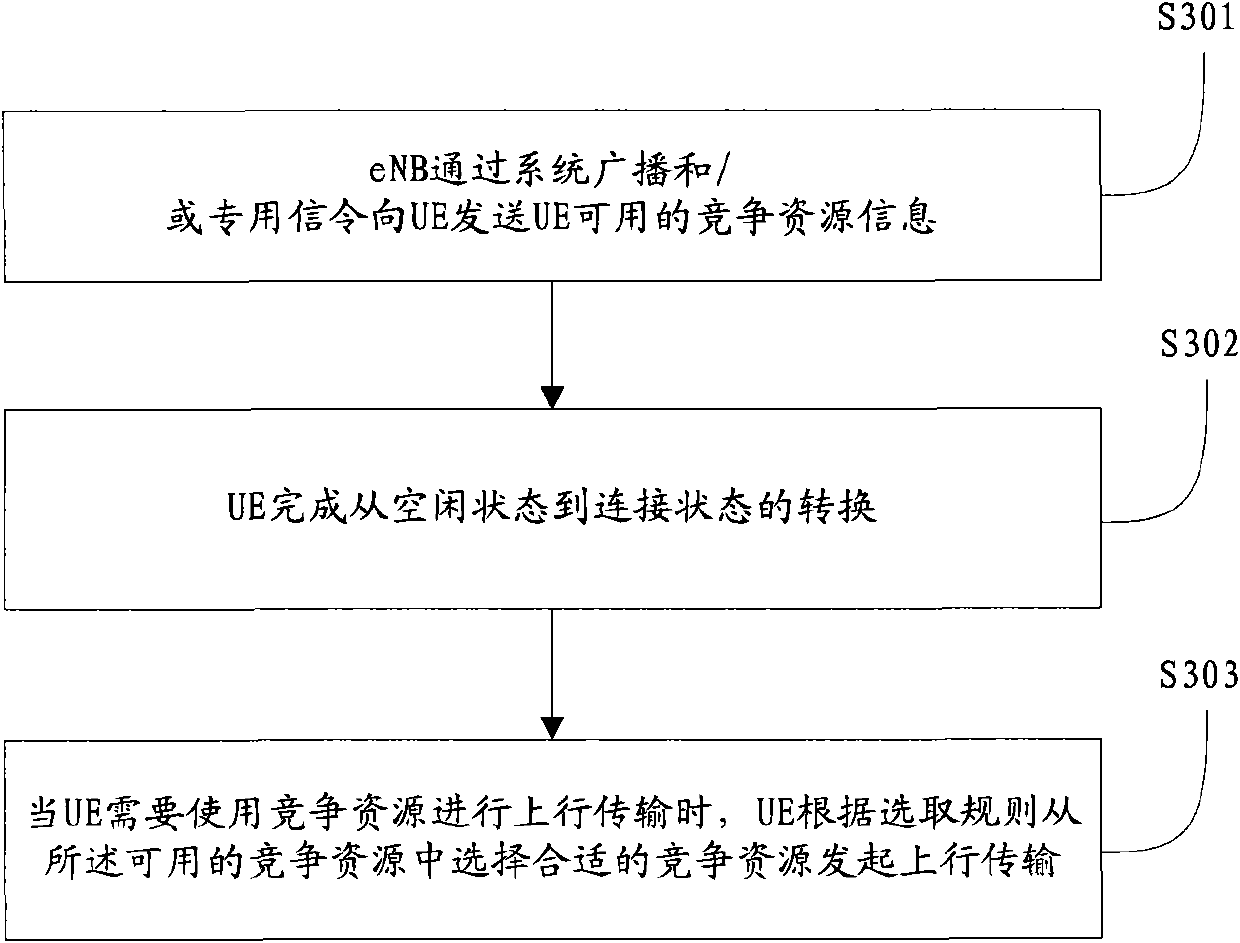
Method, system and device for distributing contention resources
ActiveCN102088775ASatisfy State Transition LatencyWireless communicationResource informationUplink transmission
The invention provides a method for distributing contention resources. The method comprises the following steps that: user equipment (UE) receives contention resource information which is available for the UE and sent by an evolution node base (eNB) through a system broadcast and / or special signaling; and when needing to perform uplink transmission by using the contention resources, the UE selects a proper contention resource from the available contention resources according to a selection rule to perform the uplink transmission. By the embodiment, the eNB can send the contention resource information of the contention resources to the UE through the system broadcast and / or special signaling, so the UE can select the proper one from the contention resource information to perform the uplink transmission; and finally, the contention-resource-based transmission can be realized, and an aim of state switchover time delay of a long term evolution-access system is achieved.
Owner:DATANG MOBILE COMM EQUIP CO LTD
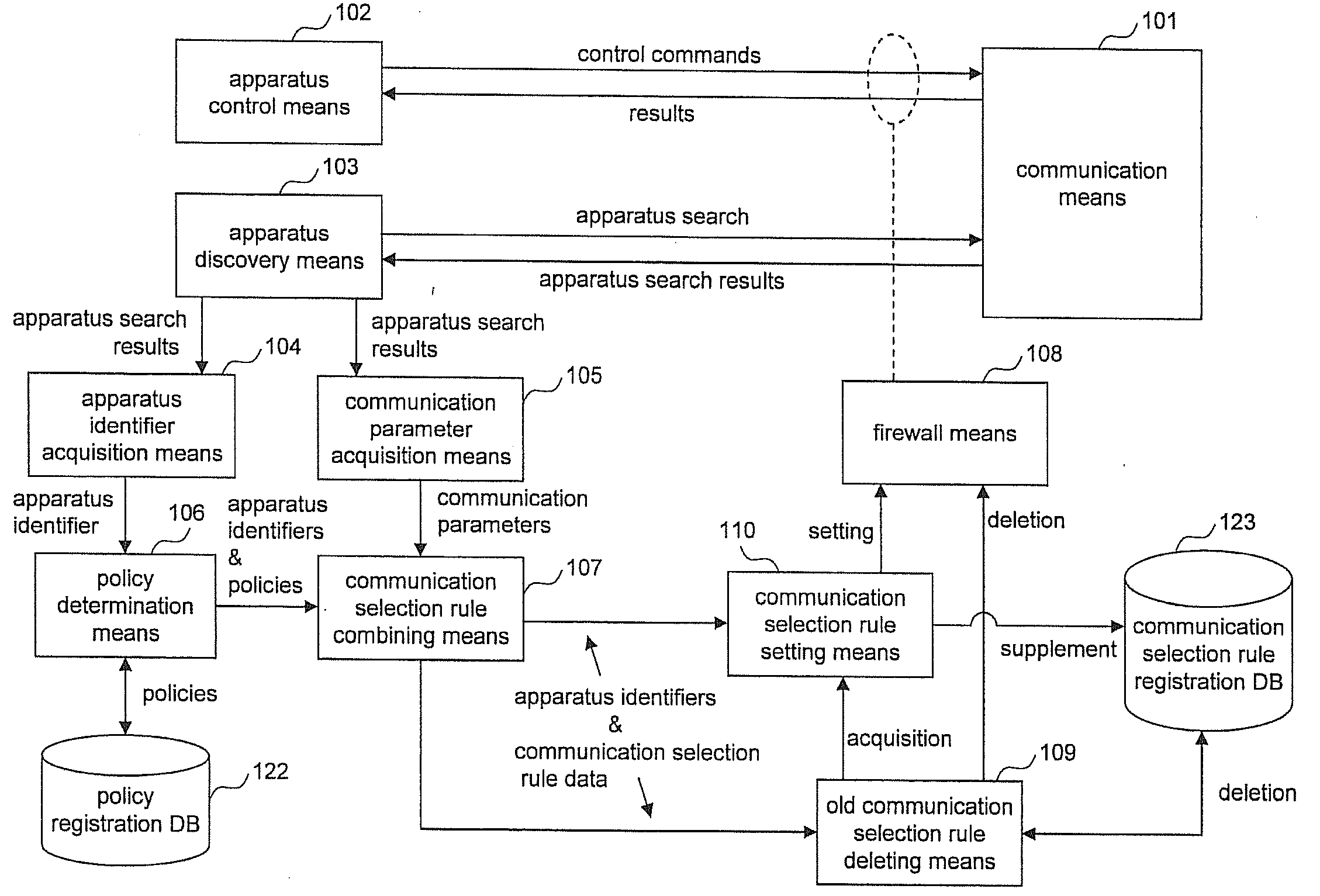
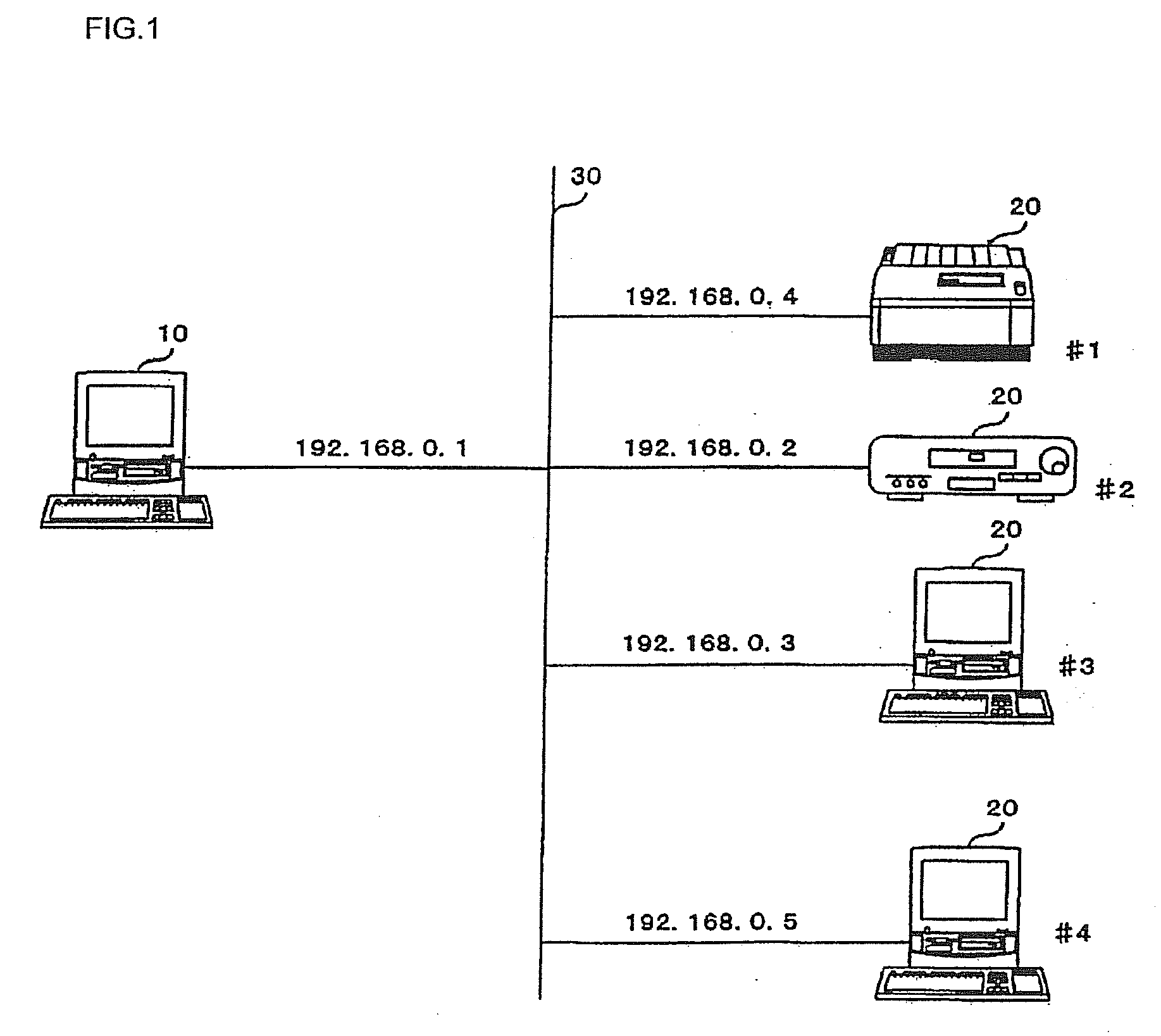
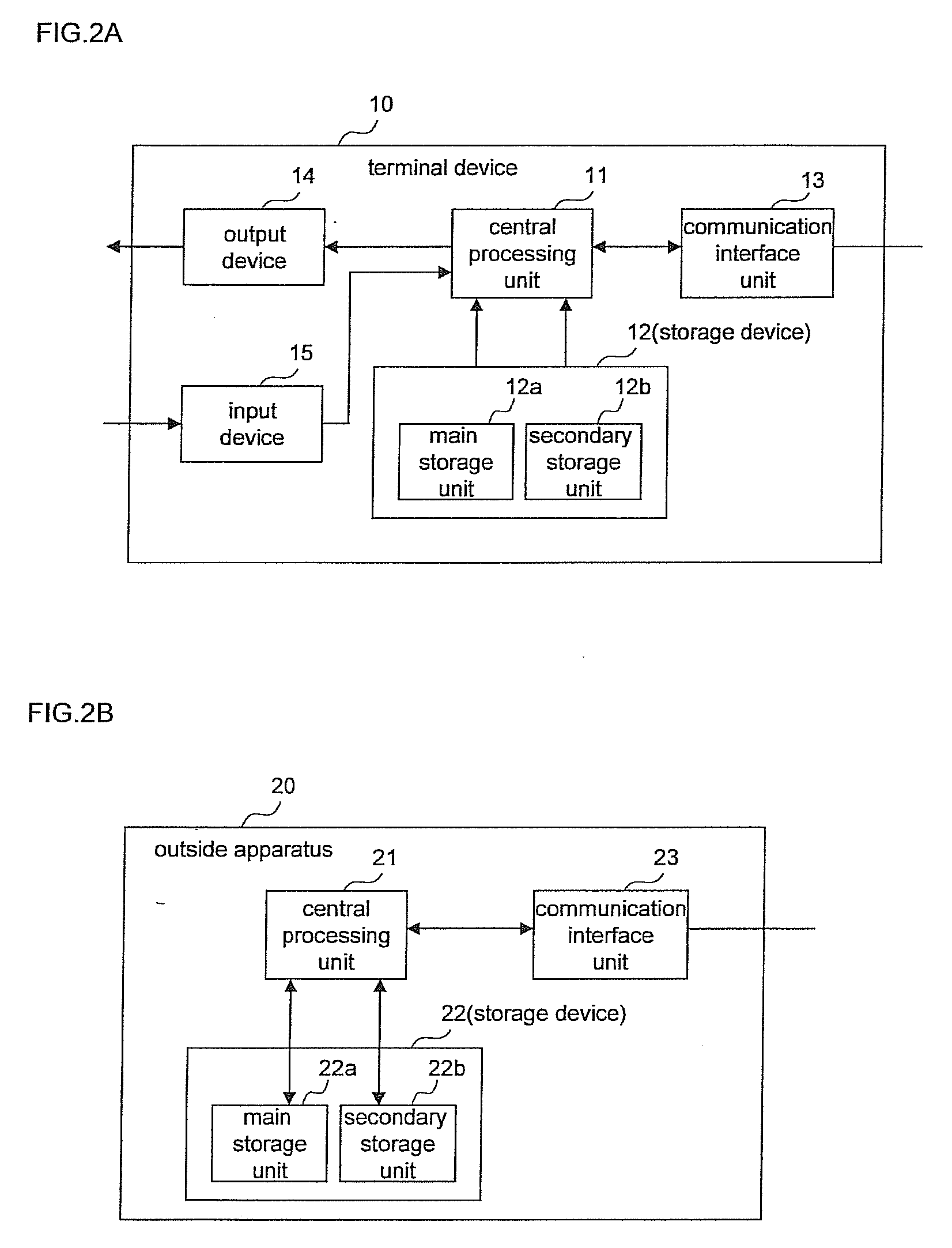
Communication Control Device, Communication Control System, Communication Control Method, and Communication Control Program
InactiveUS20090178110A1Increase speedImprove versatilityComputer security arrangementsMultiple digital computer combinationsControl systemCommunication control
The communication control device of the present invention includes: a communication parameter acquisition means (105) for acquiring communication parameters that specify the transmission origin of an outside apparatus based on existence information of the outside apparatus that is received from a communication network, an apparatus identifier acquisition means (104) for acquiring from the outside apparatus an apparatus identifier that is an identifier for the outside apparatus, a policy determination means (106) for determining a communication policy for permitting or prohibiting communication with the outside apparatus that is specified by the apparatus identifier, a communication selection rule combining means (107) for combining communication selection rules based on the communication policy and communication parameters, and a communication pass control means (108) for passing or blocking communication with the outside apparatus based on the communication selection rules that have been combined by the communication selection rule combining means.
Owner:NEC CORP
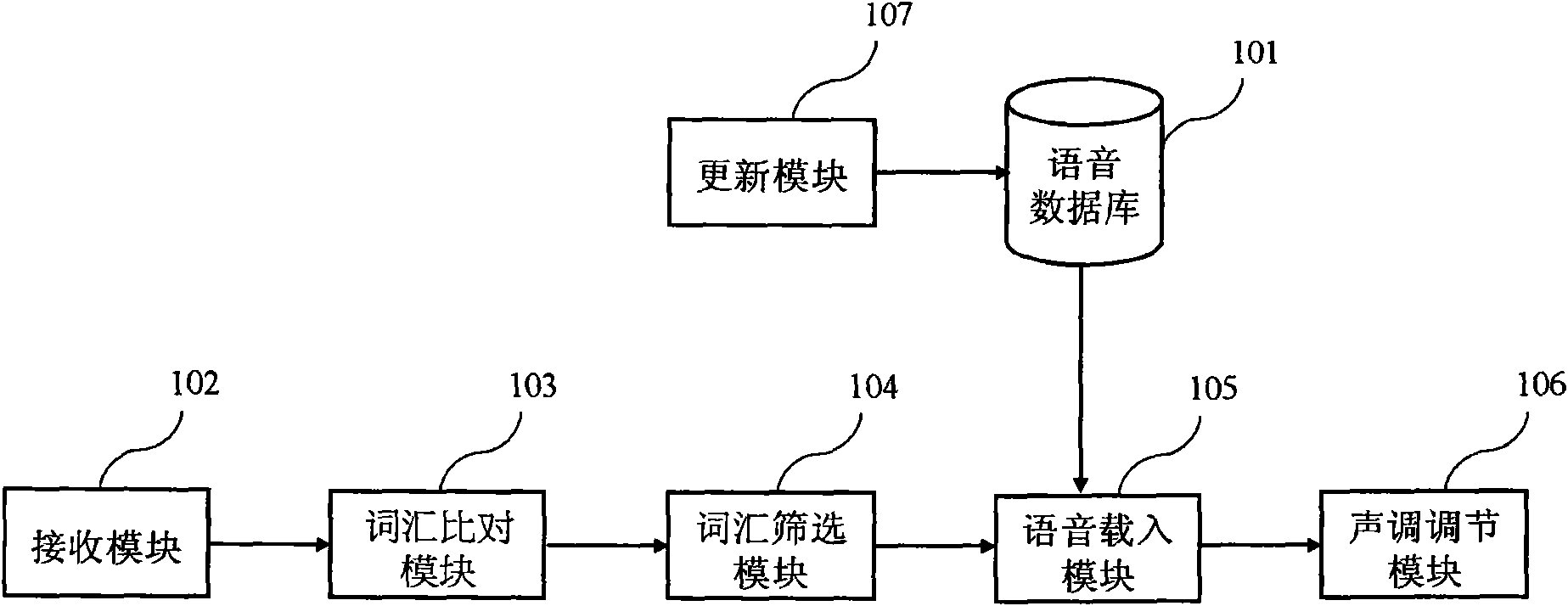
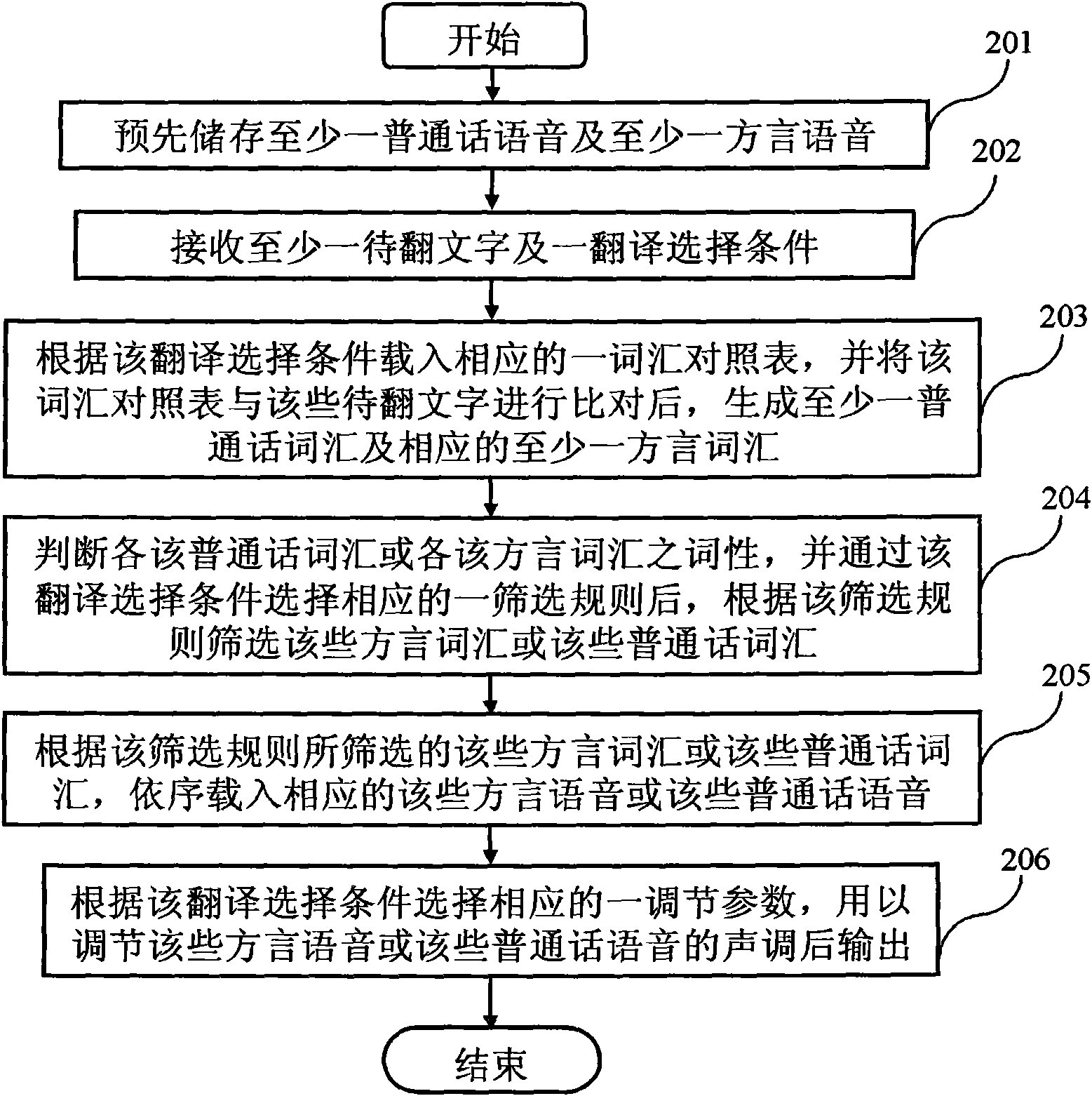
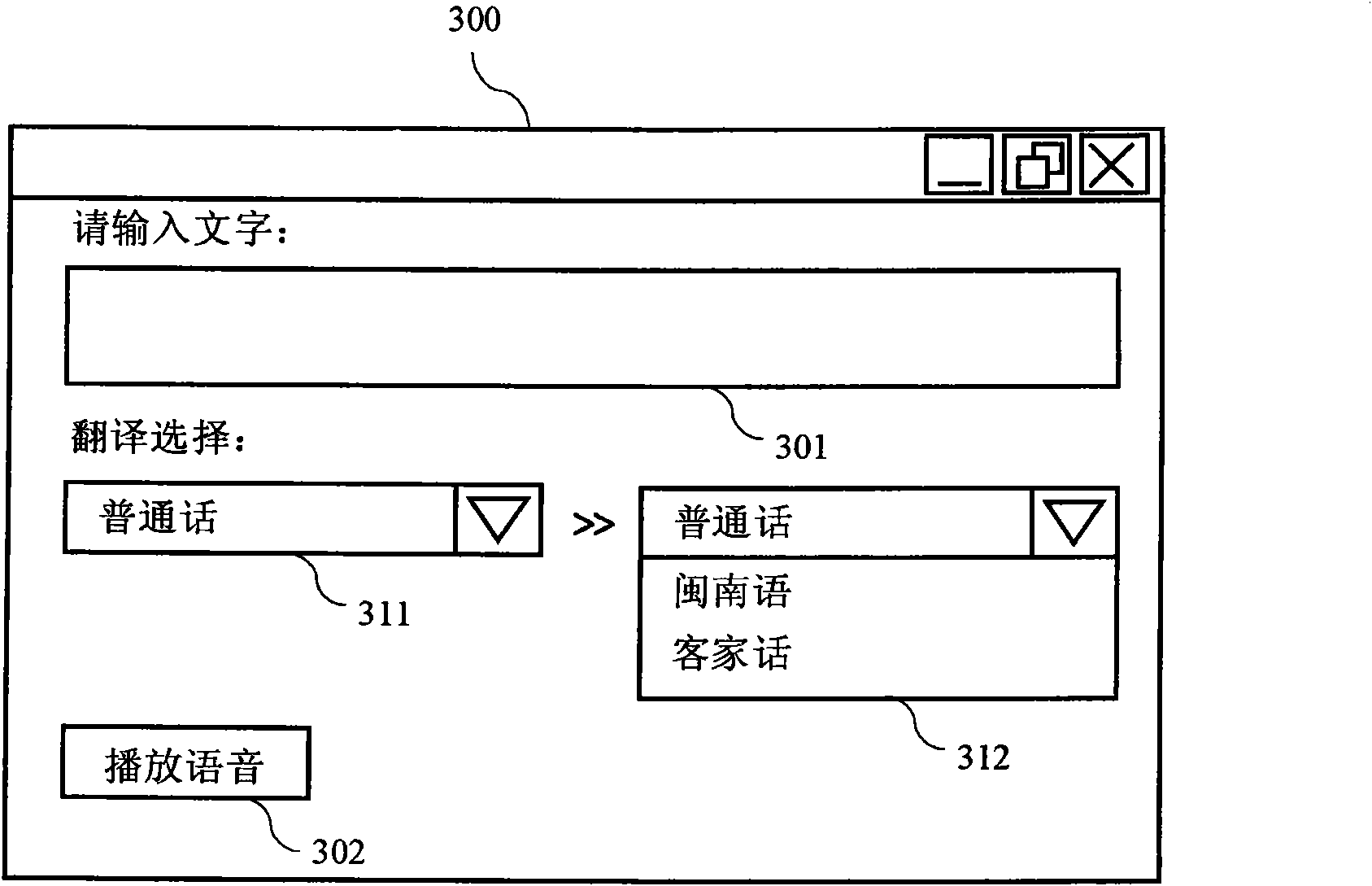
Speech translation system between Mandarin and various dialects and method thereof
InactiveCN101667424AImprove accuracyImprove completenessSpecial data processing applicationsSpeech synthesisSpeech translationSpeech sound
The invention relates to a speech translation system between the Mandarin and various dialects and a method thereof for solving the problems of poor correctness, tedium and stiffness of translated dialects. By selecting correct dialect speeches and carrying out tone regulation through a selection rule, the invention achieves the technical effect of improving the accuracy and the simulation degreeof the dialect speeches.
Owner:INVENTEC CORP
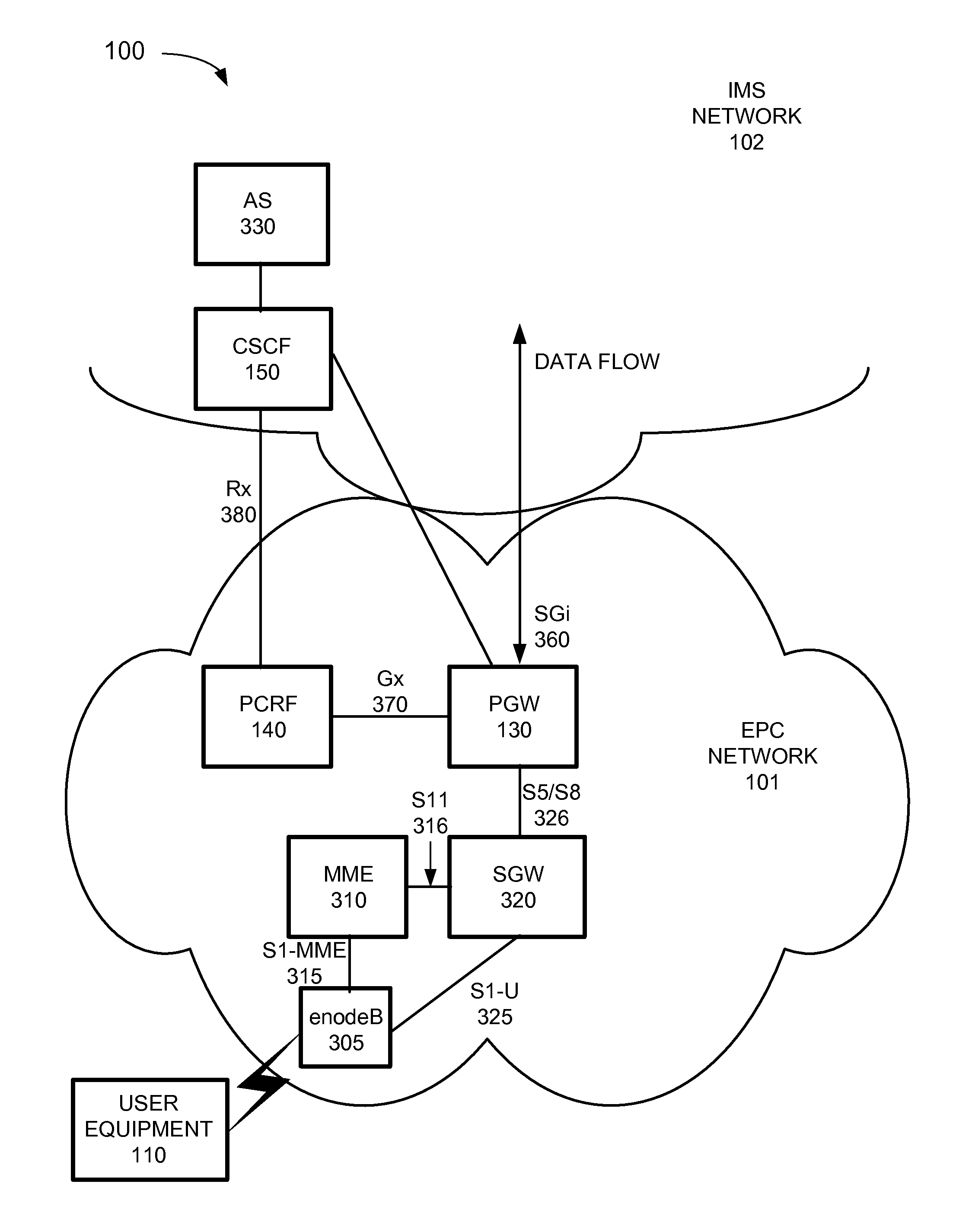
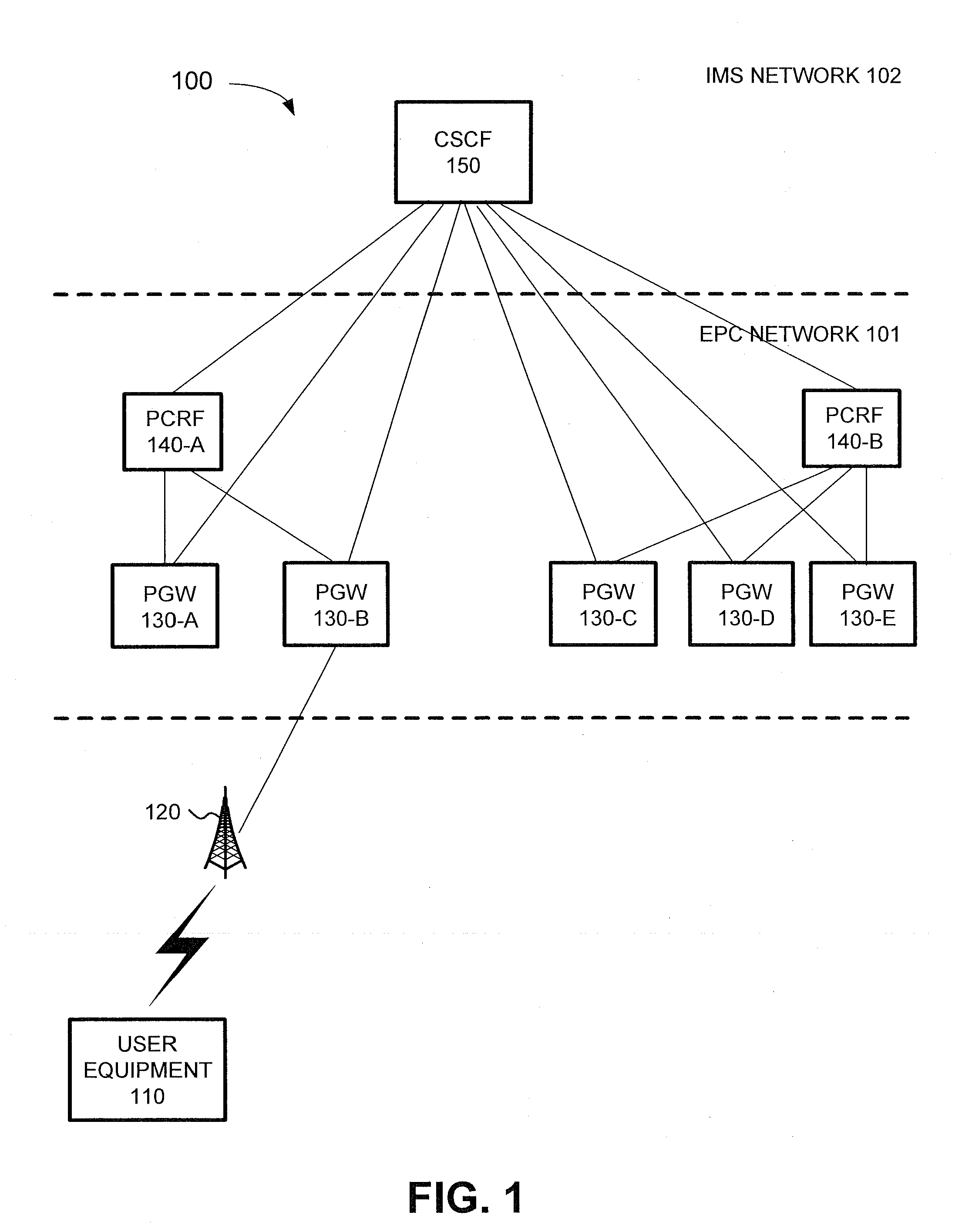
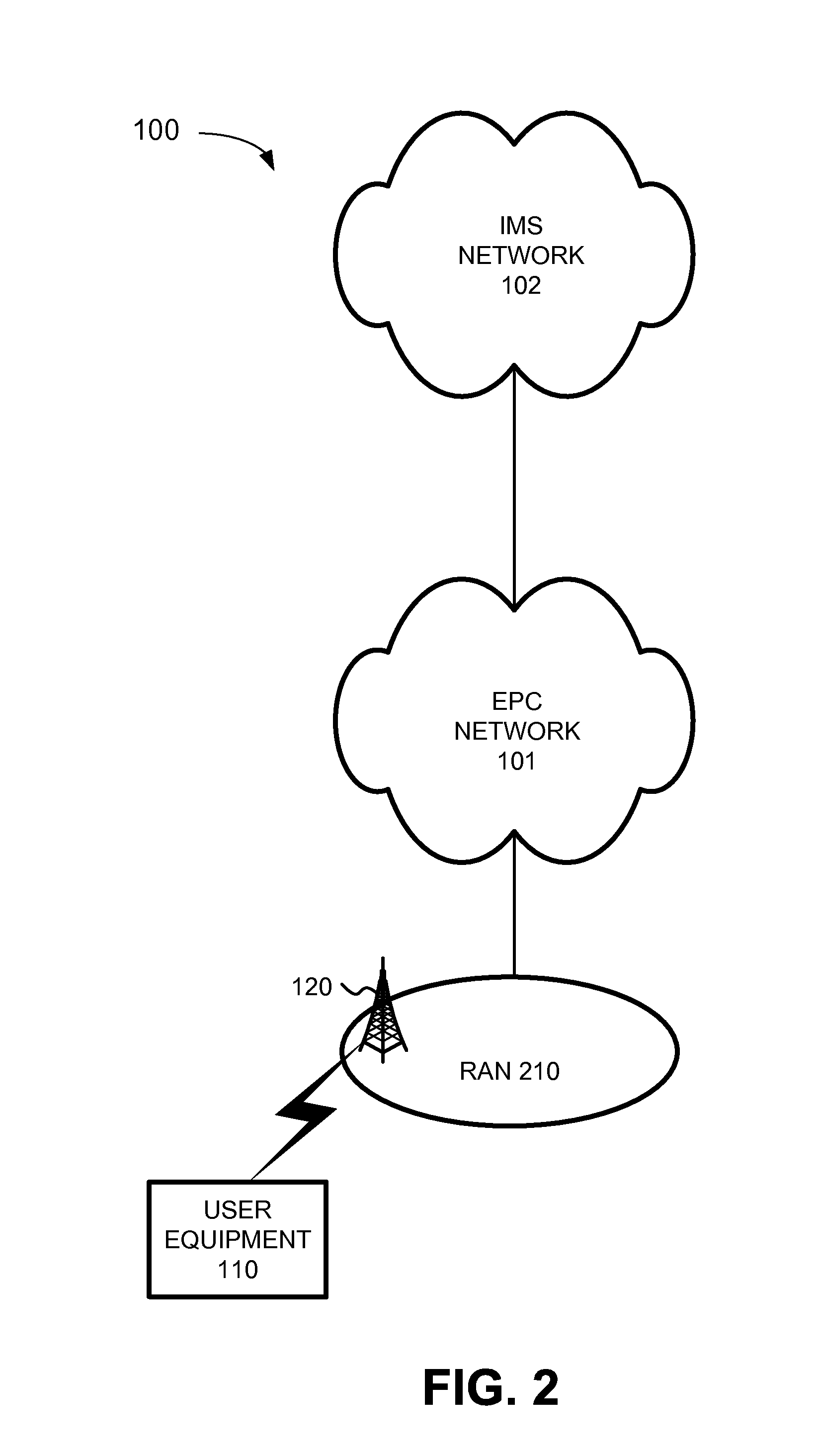
Selection of a policy and charging rules function device
ActiveUS20110302289A1Telephonic communicationMultiple digital computer combinationsIp addressUser equipment
A system includes a first device, in a first network; a second device, in a second network; and a policy rules and charging function (PCRF) database that associates Internet Protocol (IP) addresses assigned to user equipment (UE) devices with PCRF devices; where the first device is to identify a plurality of policy rules and charging function (PCRF) devices in the first network, select a PCRF device from the plurality of PCRF devices based on a selection rule, and provide information about the selected PCRF device to the second device; and where the second device is to receive a request to set up a communication session associated with a UE device; determine an IP address associated with the UE device; identify a PCRF device, based on the determined IP address, by accessing the PCRF database, and send session information associated with the communication session to the identified PCRF device.
Owner:VERIZON PATENT & LICENSING INC
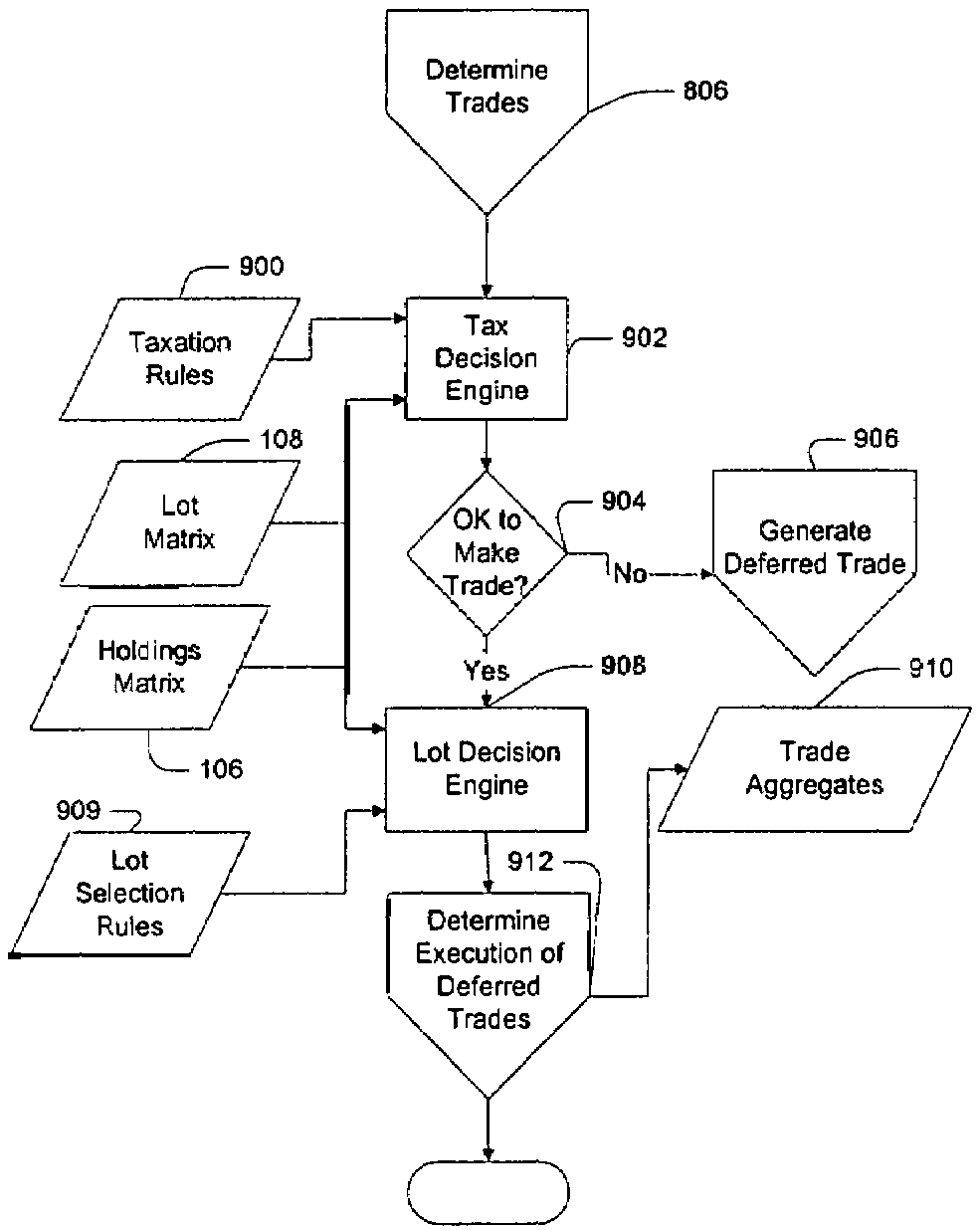
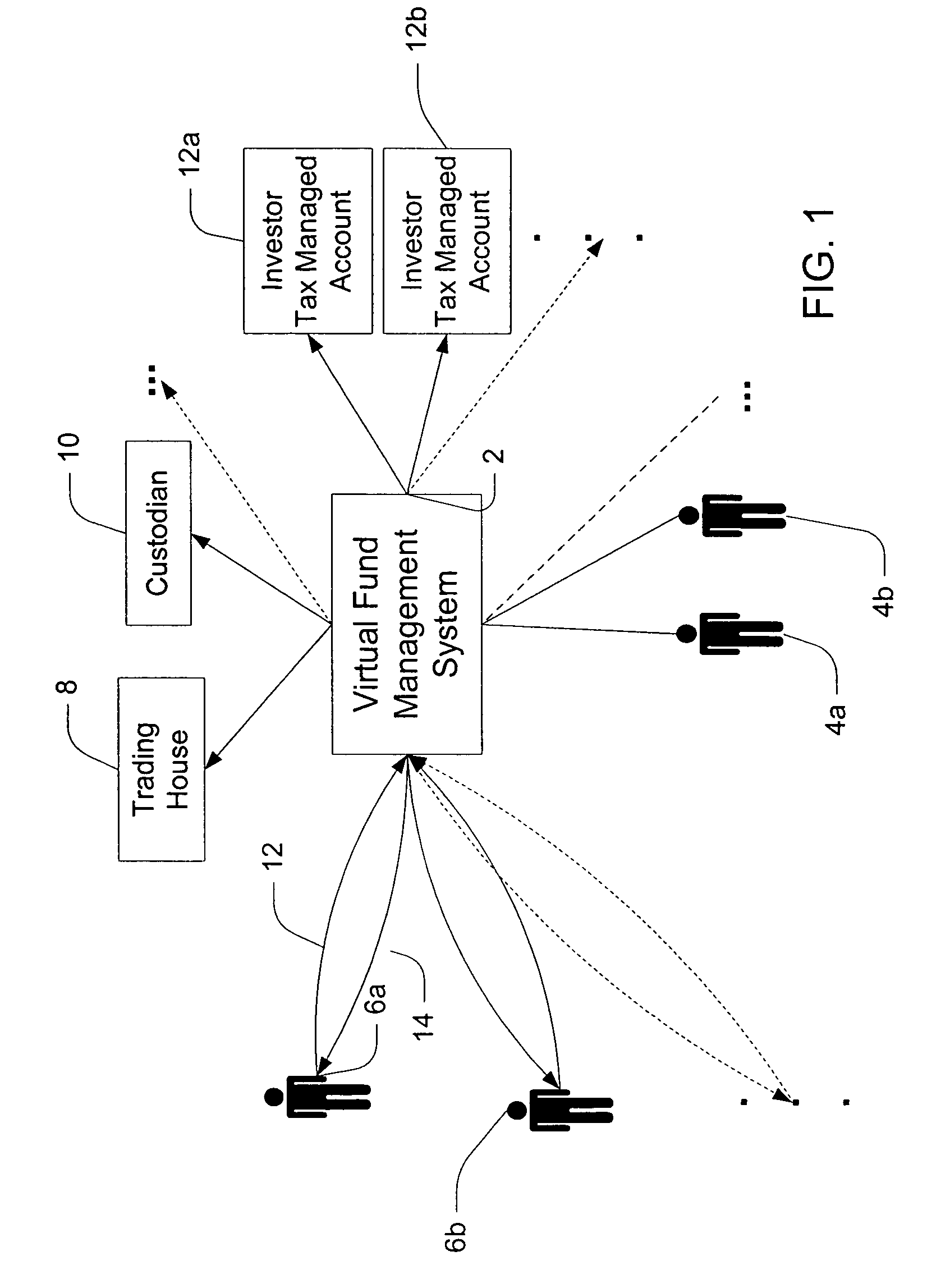
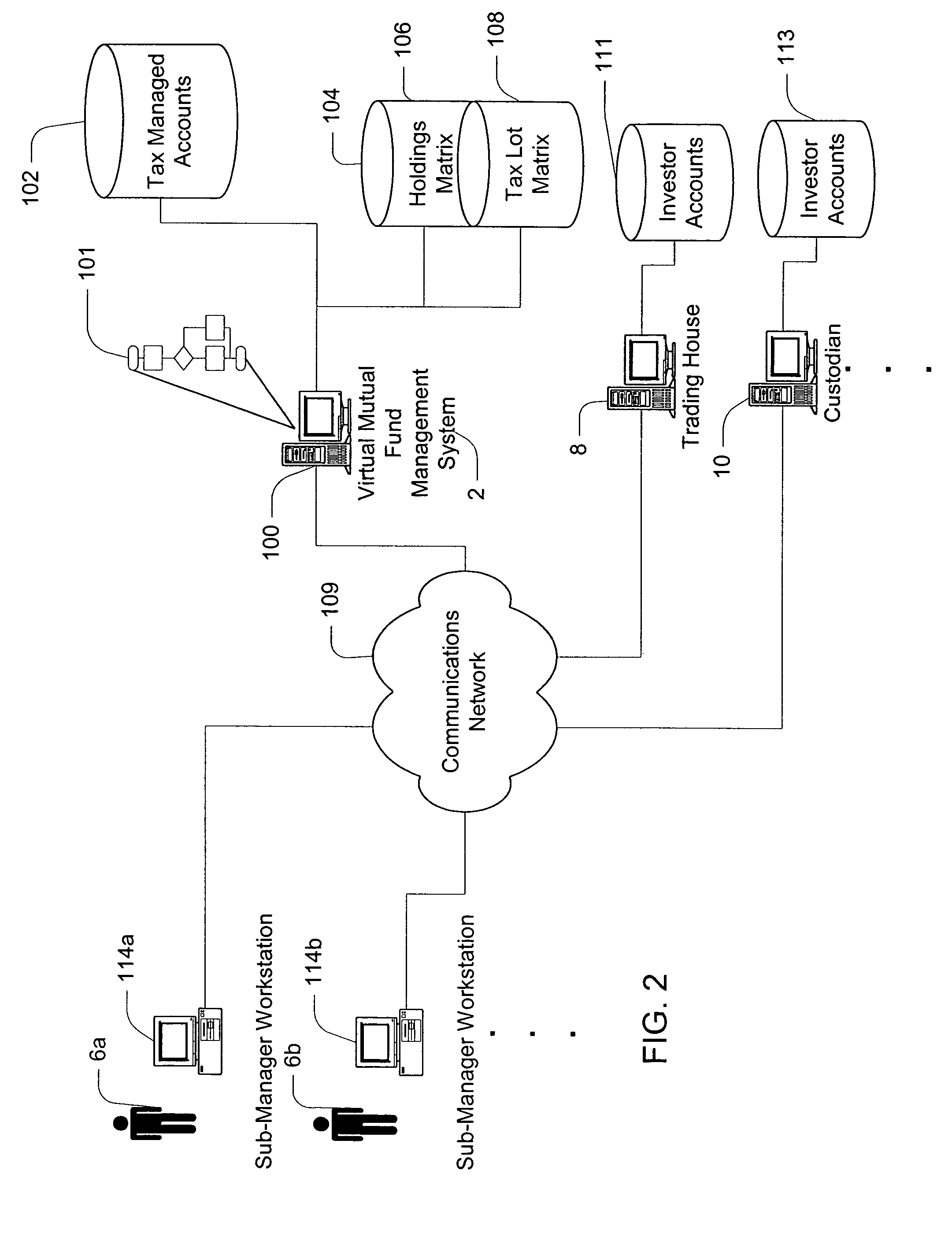
Method and apparatus for managing a virtual portfolio of investment objects
A method of managing financial object(s), on a computer, including but not limited to managing a virtual portfolio of the objects where the portfolio may include a collection of objects managed collectively but tracked separately with separately owned lots on behalf of investor(s); providing a database associating lot(s) owned by each of the investors and associating the lots as tradable regardless of initiator of the purchase; providing lot selection rules; receiving a requested trade; selecting a lot for trading using the database, the lot selection rules, and the requested trade; providing taxation rules; determining if a trade using the selected lot should be deferred; generating a deferred trade in a tax-managed sub-account if it is determined that the requested trade should be deferred; and selecting the deferred trade in the sub-account for execution if the deferred trade should no longer be deferred using the database and the taxation rules.
Owner:RES AFFILIATES LLC
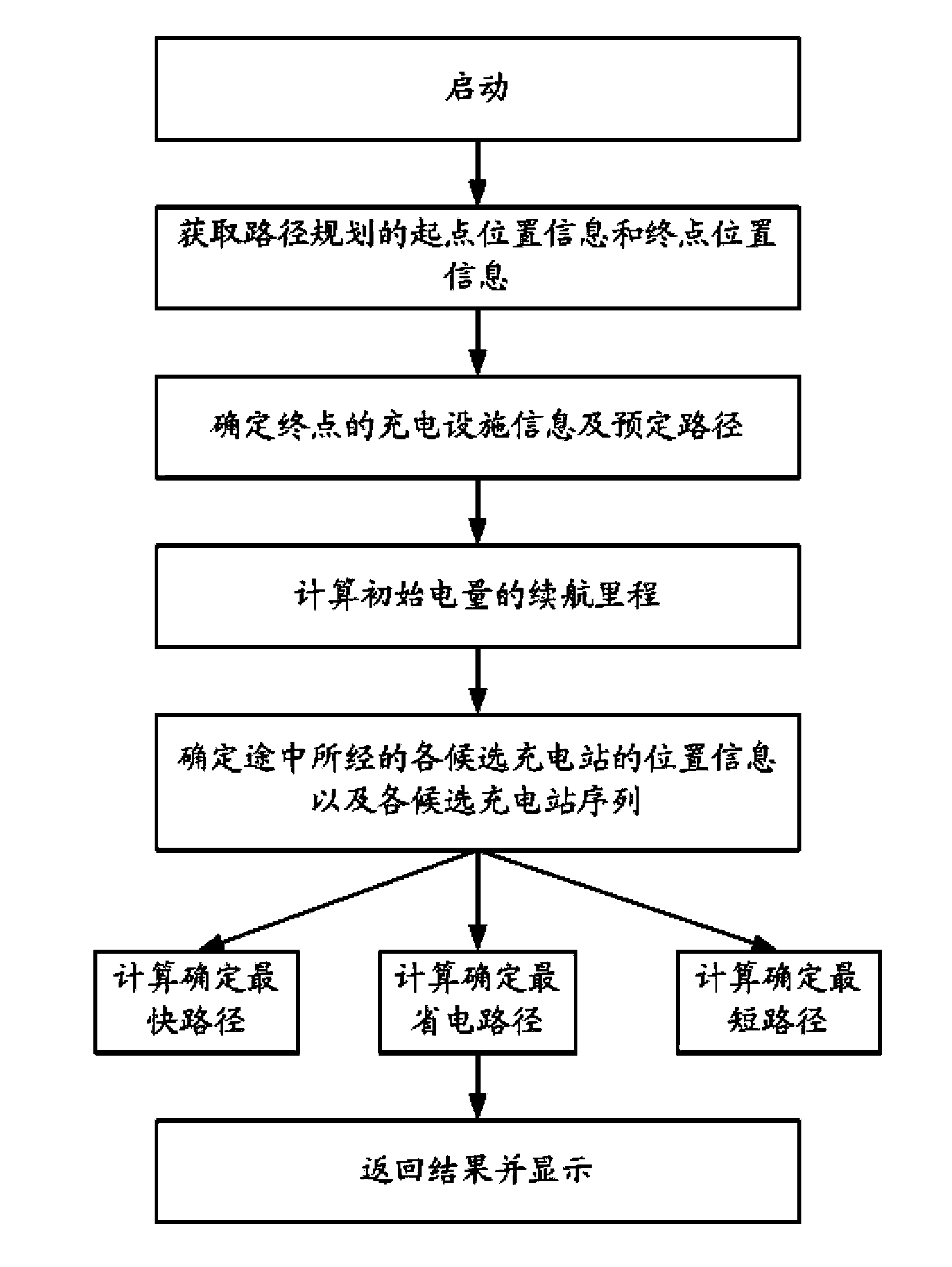
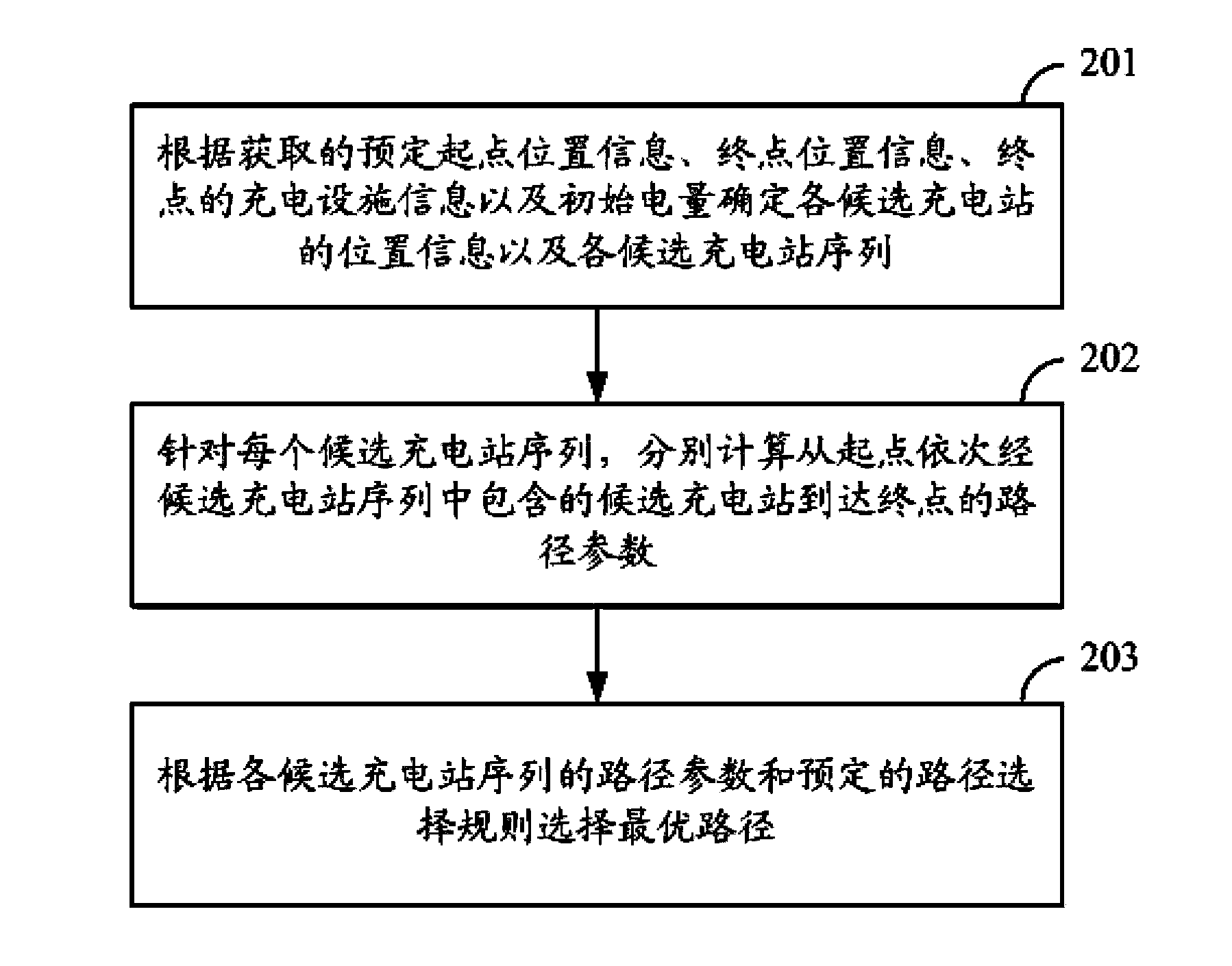
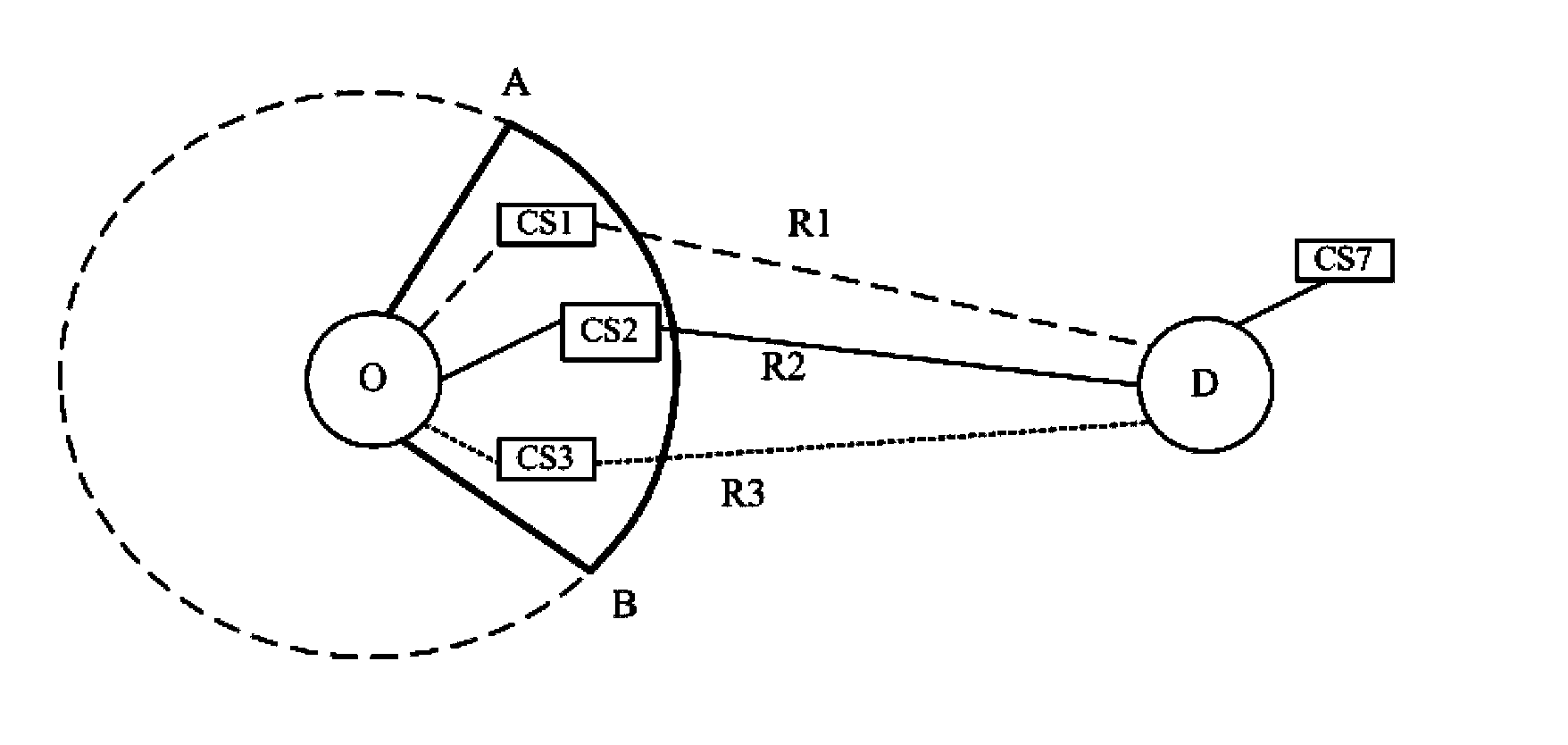
Method and device for planning route of electric car
The invention provides a method and a device for planning a route of an electric car, which are used for providing a global optimum route to the running of the electric card, and can get ready for the next travelling after the electric car arrives at the destination. The method comprises the following steps: determining the position information of each candidate charging station and each candidate charging station sequence according to acquired predetermined starting position information, destination position information, charging facility information of the destination and initial electric quantity; aiming at each candidate charging station sequence, respectively calculating the route parameters from the starting point, through the candidate charging stations included in the candidate charging station sequence in sequence and to the destination point, and selecting the optimal route according to the route parameter of each candidate charging station sequence and a predetermined route selection rule.
Owner:NEC (CHINA) CO LTD
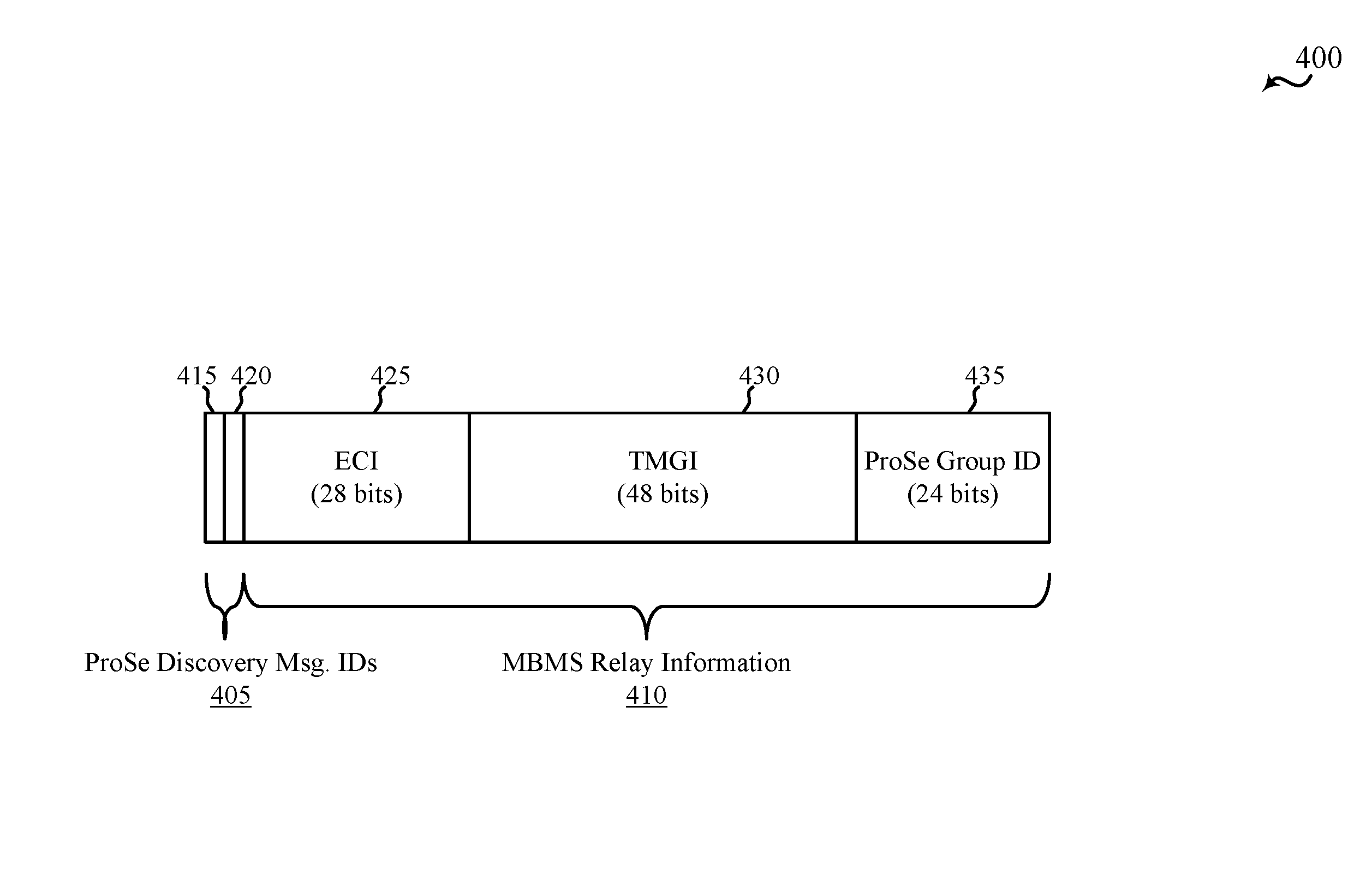
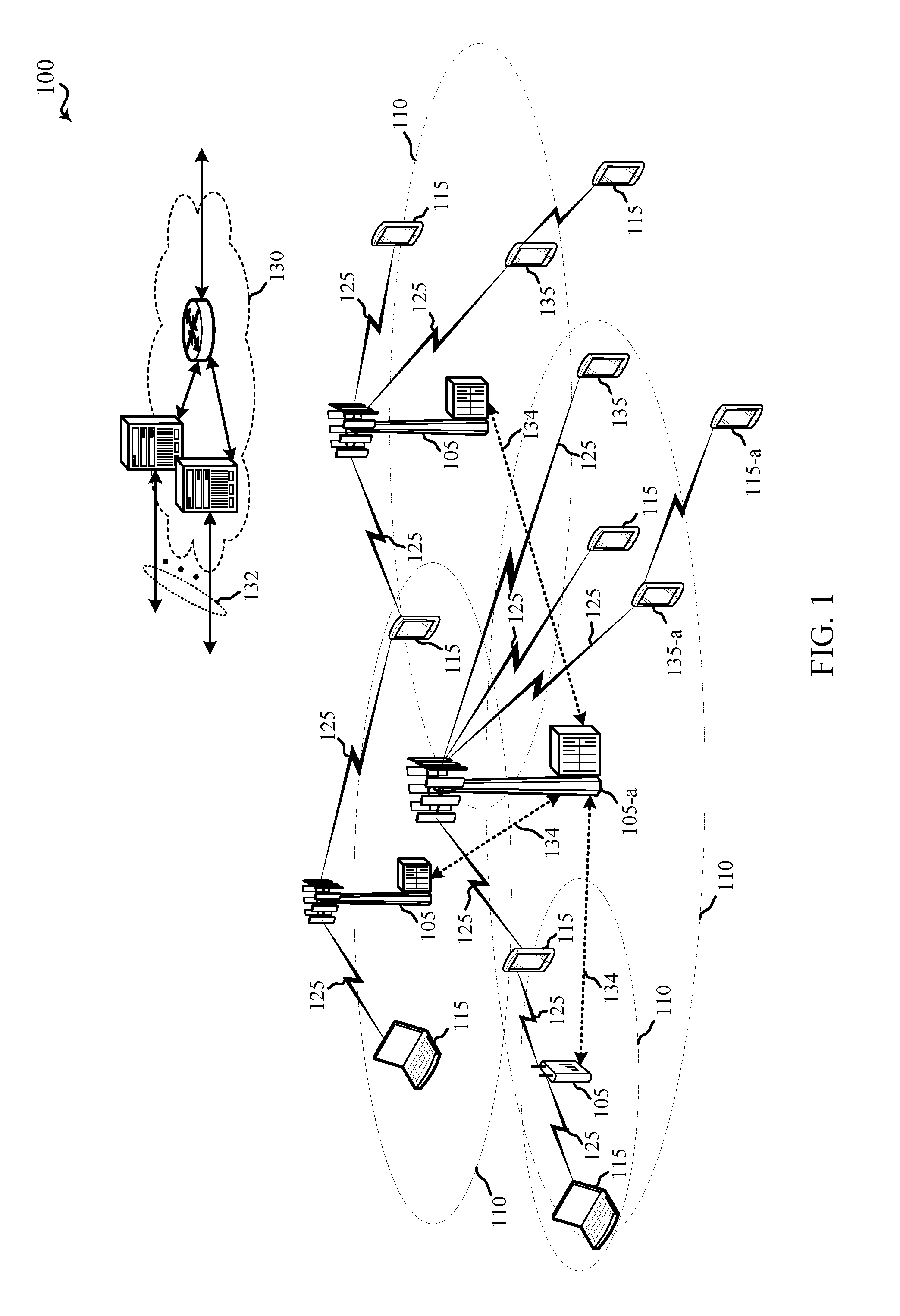
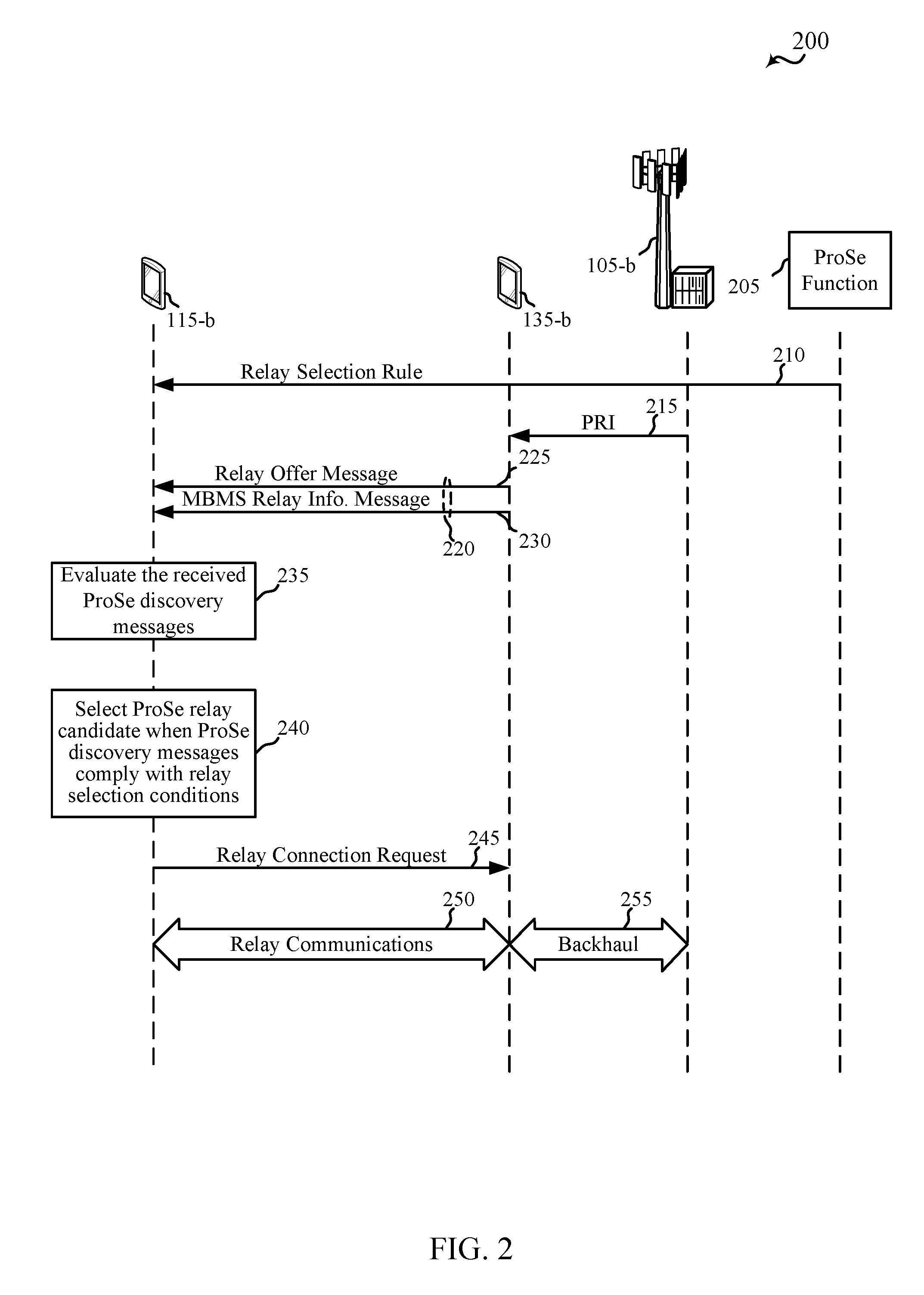
Selection of proximity services relay
ActiveUS20160286471A1Special service provision for substationAssess restrictionBroadcastingUser equipment
Techniques are described for wireless communication. A method for wireless communication at a user equipment (UE) includes configuring a relay selection rule; receiving at least one discovery message from each of a plurality of proximity services (ProSe) relay candidates providing access to a network; evaluating the received discovery messages with respect to the relay selection rule; selecting a first ProSe relay candidate from the plurality of ProSe relay candidates based at least in part on the evaluating; and connecting to the network via the first ProSe relay candidate. A method for wireless communication at a ProSe relay candidate includes receiving, from a network, a ProSe Relay Indication (PRI); broadcasting at least one discovery message that includes the PRI; and receiving a relay connection request from a UE based at least in part on a compliance of the at least one discovery message with a relay selection rule of the UE.
Owner:QUALCOMM INC
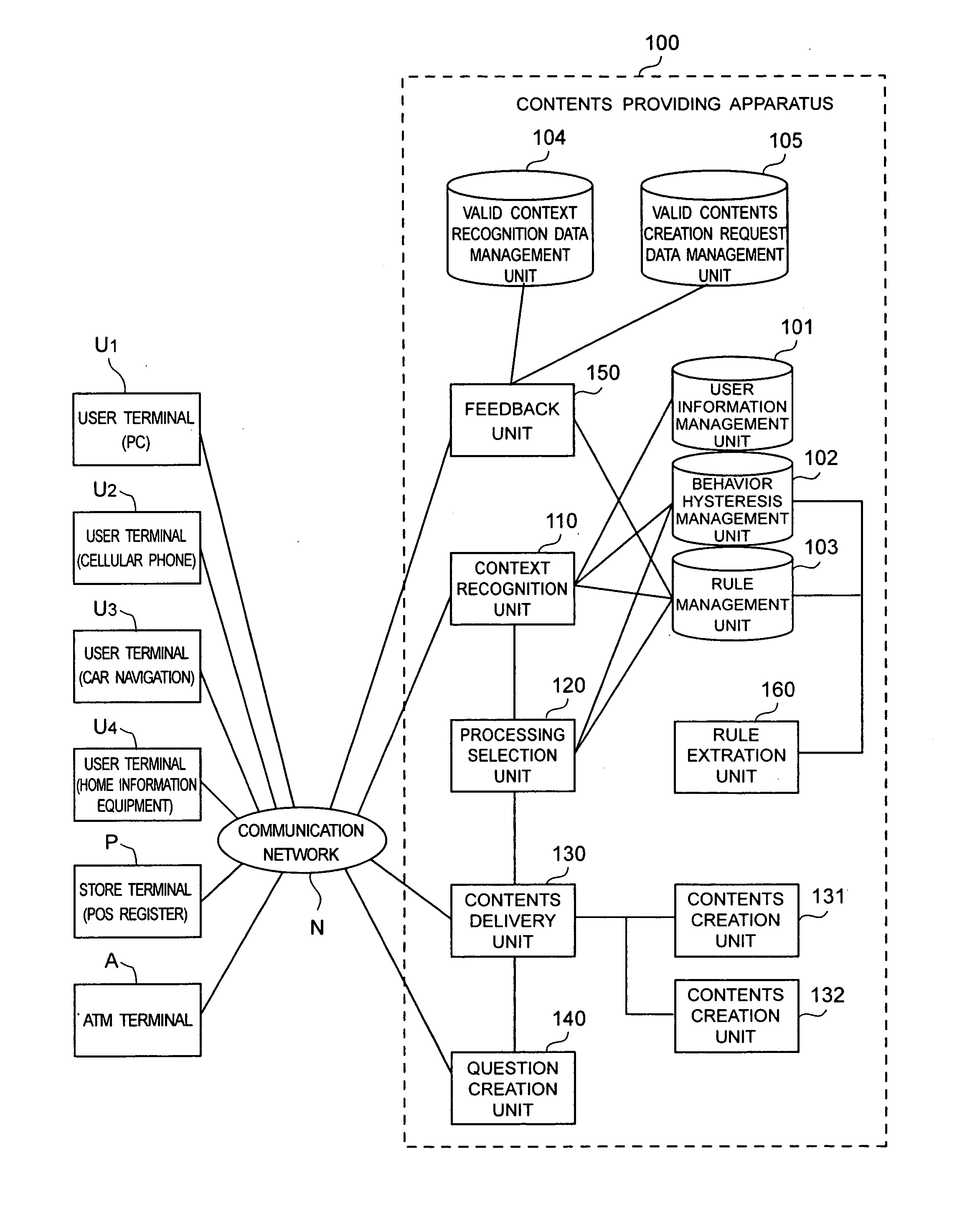
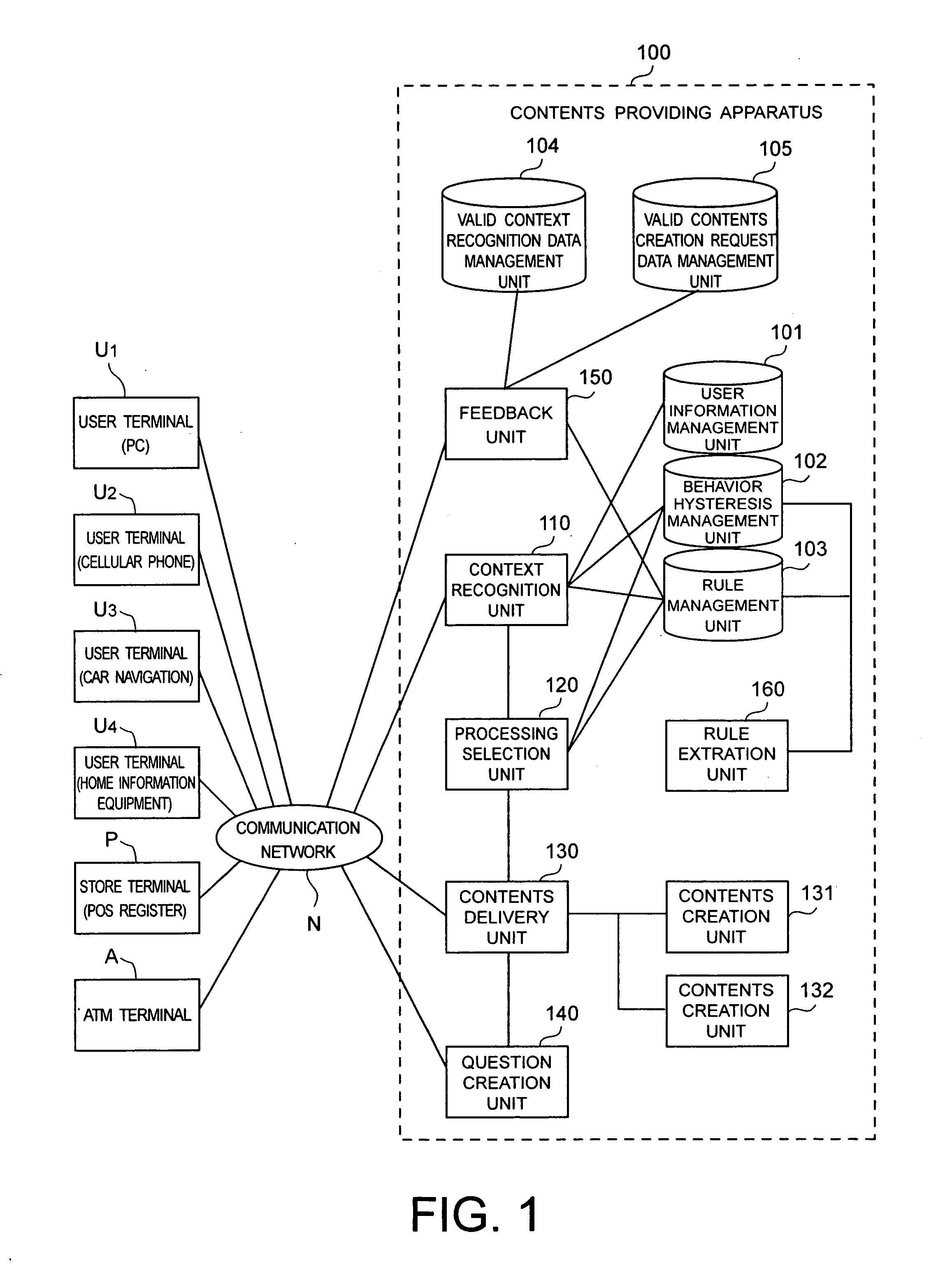
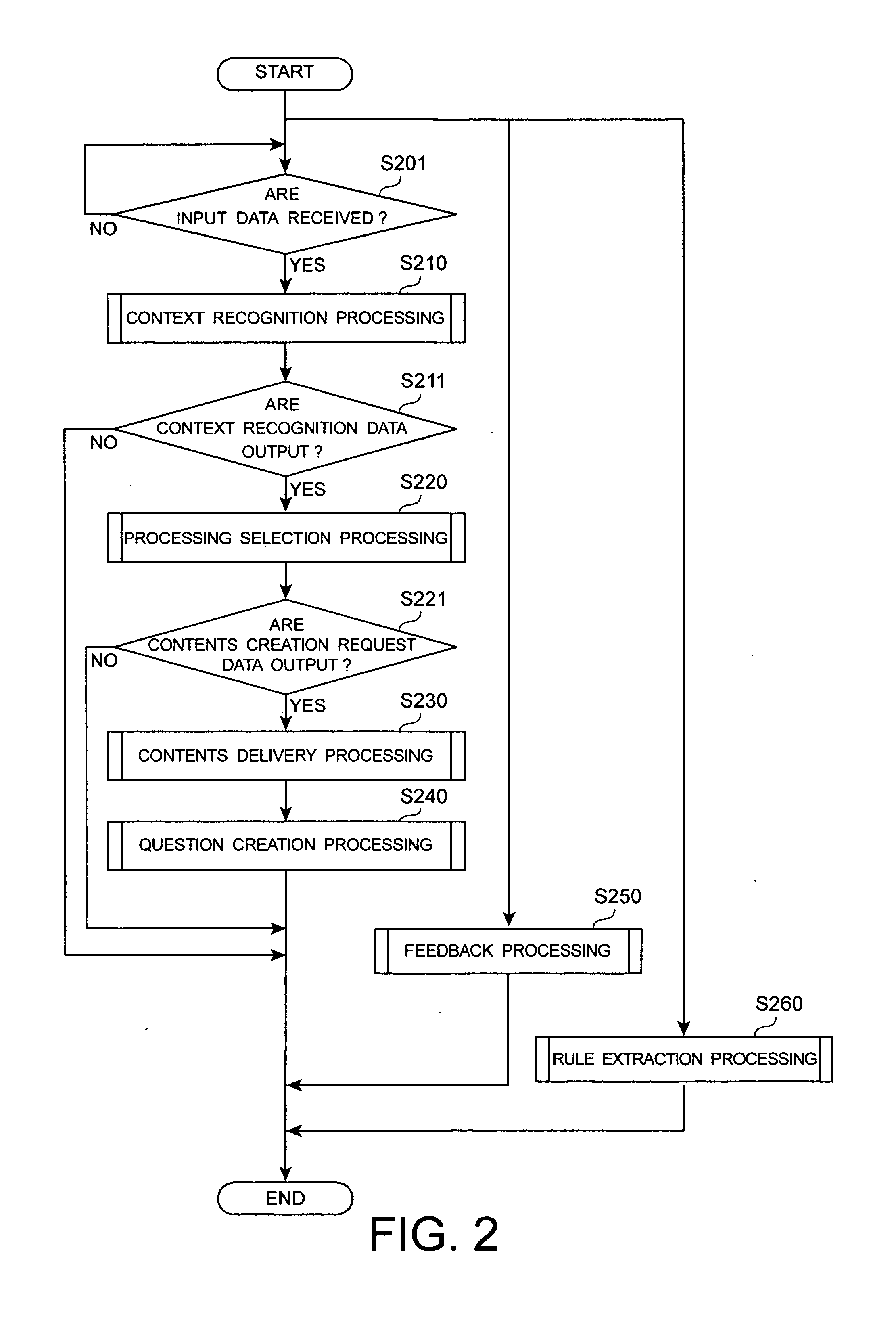
Contents providing apparatus and method
InactiveUS20050144000A1Other databases retrievalBuying/selling/leasing transactionsContent creationContext recognition
A context recognition unit decides a user's context by comparing context recognition rules to the user's information, and outputs context recognition data based on the user's context. A processing selection unit decides a contents type by comparing processing selection rules to the context recognition data, and outputs contents creation request data based on the contents type. A contents delivery unit obtains contents based on the contents creation request data, and delivers the contents to the user's terminal. A question creation unit creates a question about the contents delivery for the user. Each context recognition rule and each processing selection rule includes a priority degree. The question creation unit specifies the context recognition rule or the processing selection rule based on the user's answer to the question, and changes the priority degree of the specified rule.
Owner:KK TOSHIBA
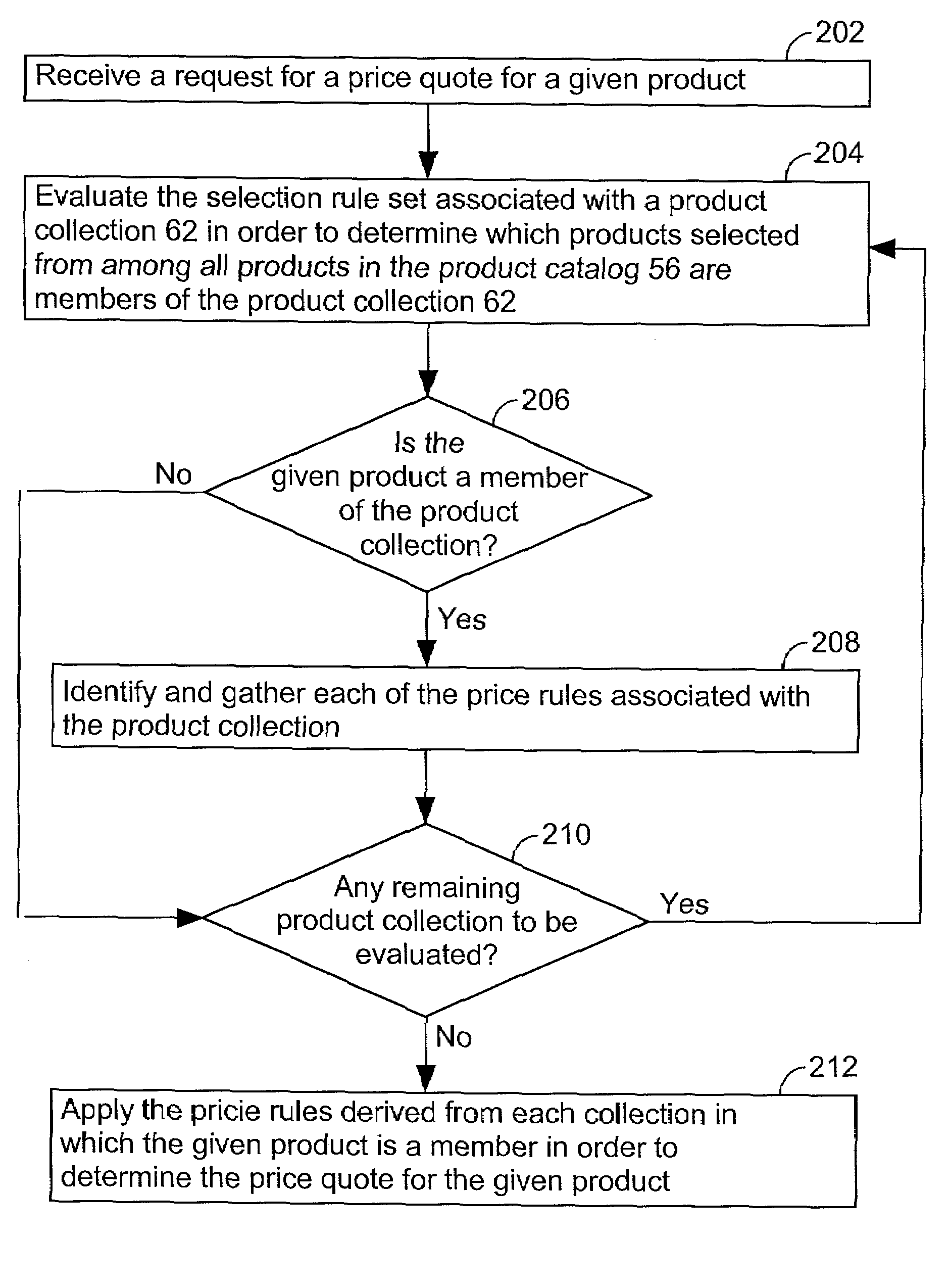
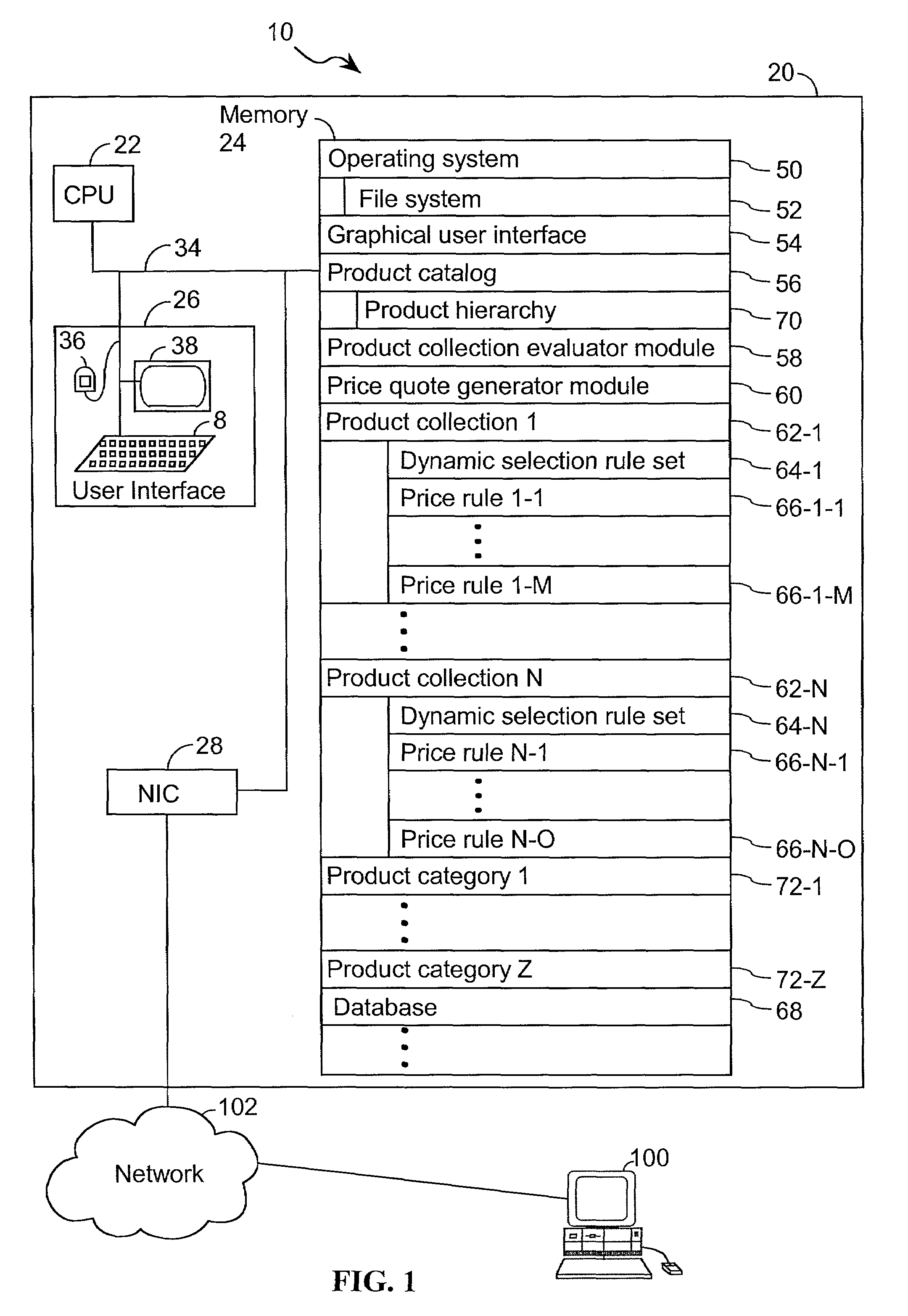
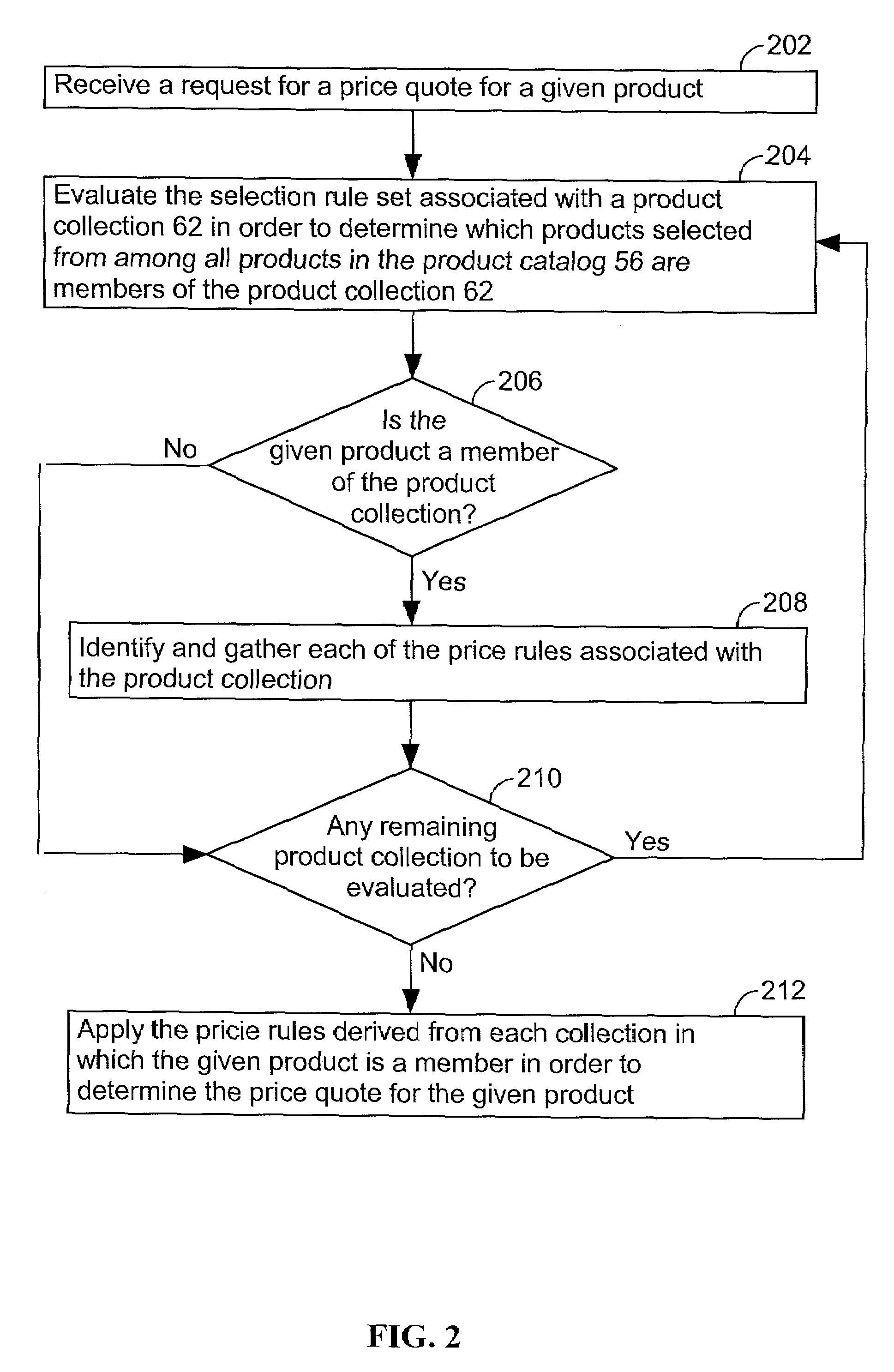
System and method for grouping products in a catalog
An apparatus and method for preparing a price quote for a product. The product is selected from among a plurality of products. A determination is made as to whether the product is a member of a particular product collection. This determination includes evaluating a dynamic selection rule set associated with the particular product collection. When the product is determined to be a member of the particular product collection, the method includes the additional steps of (i) identifying one or more price rules associated with the particular product collection and (ii) applying these price rules to the product in order to determine the price quote for the product.
Owner:VENDAVO
Ternary and multi-nary iron-based bulk glassy alloys and nanocrystalline alloys
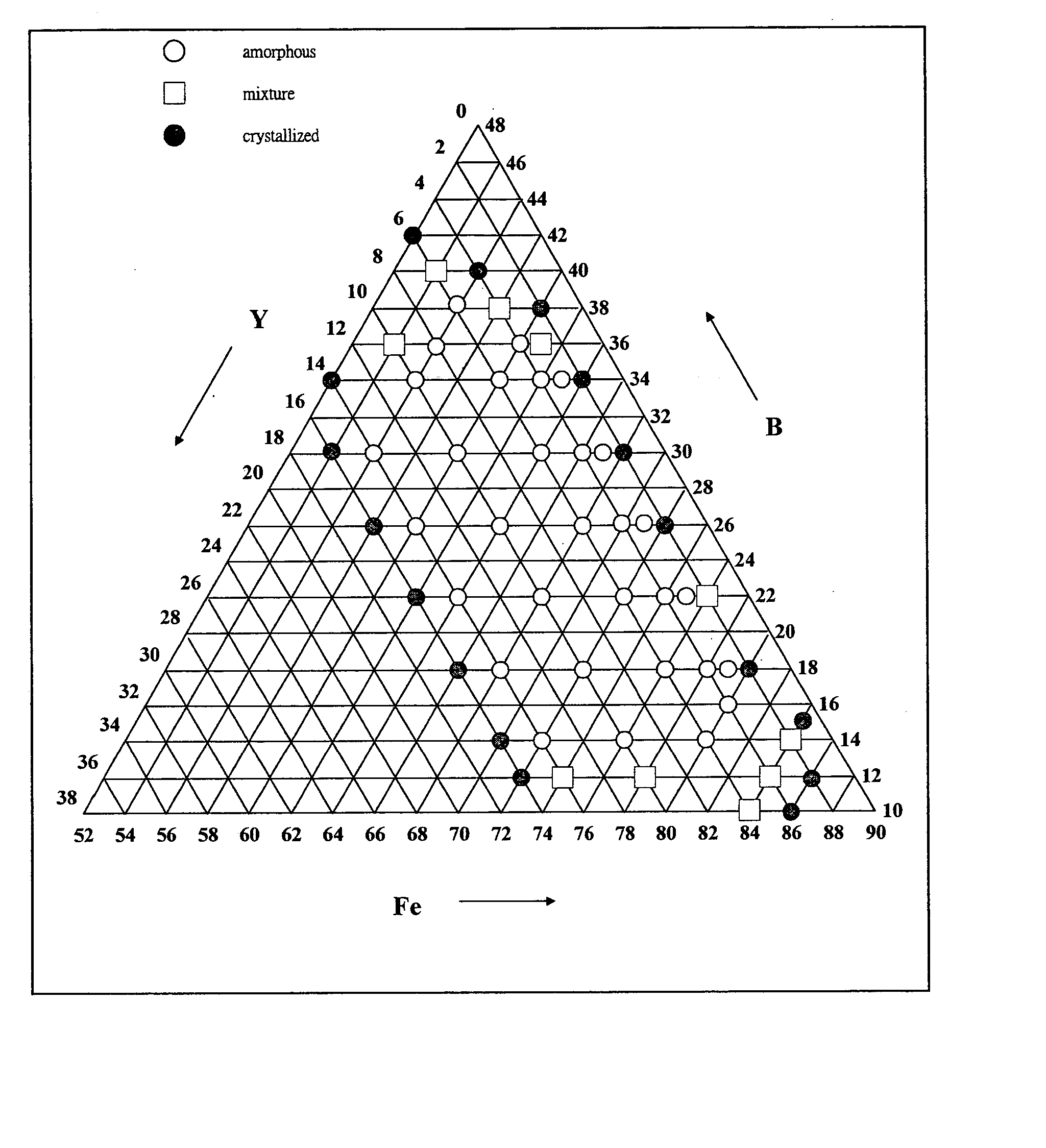
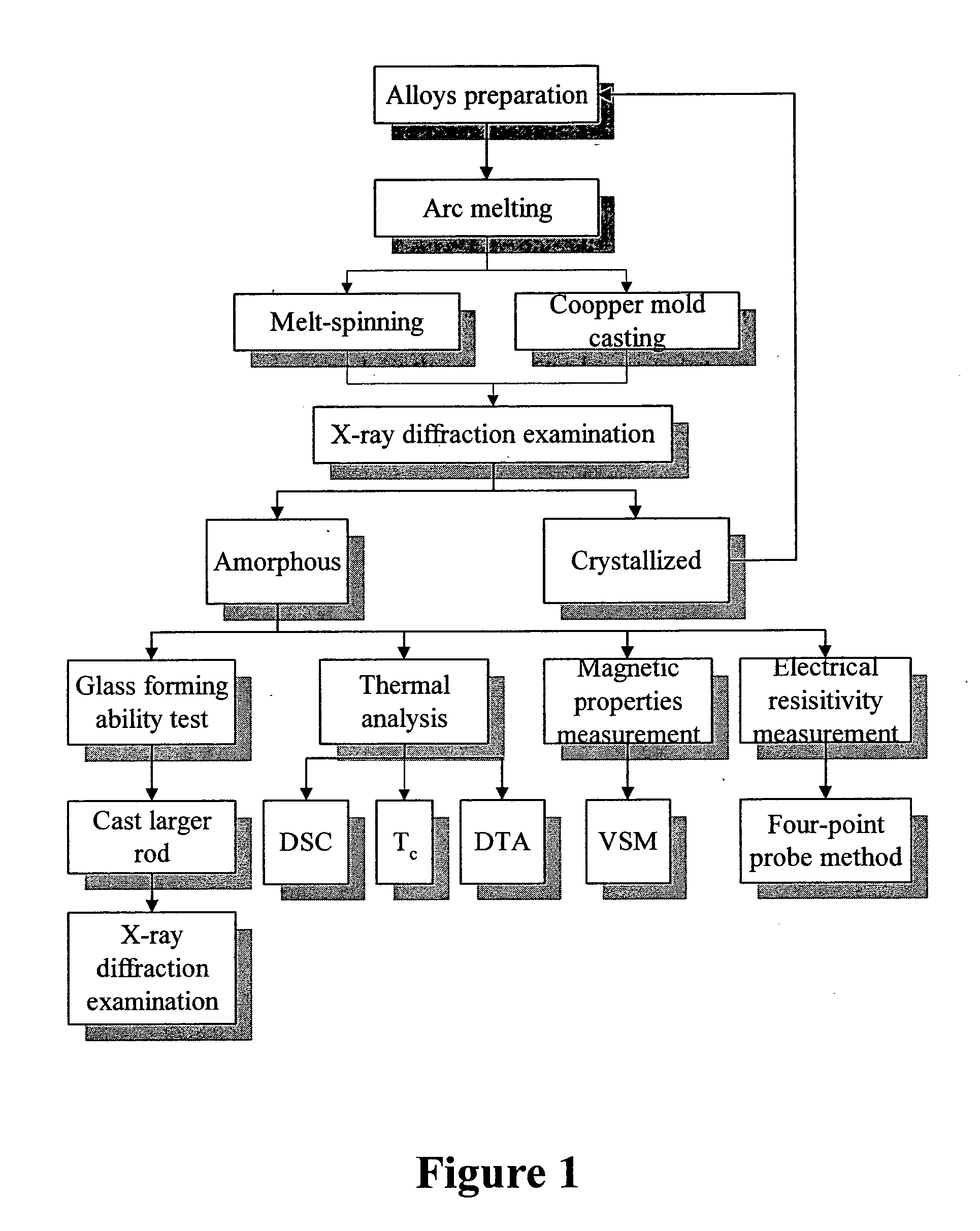
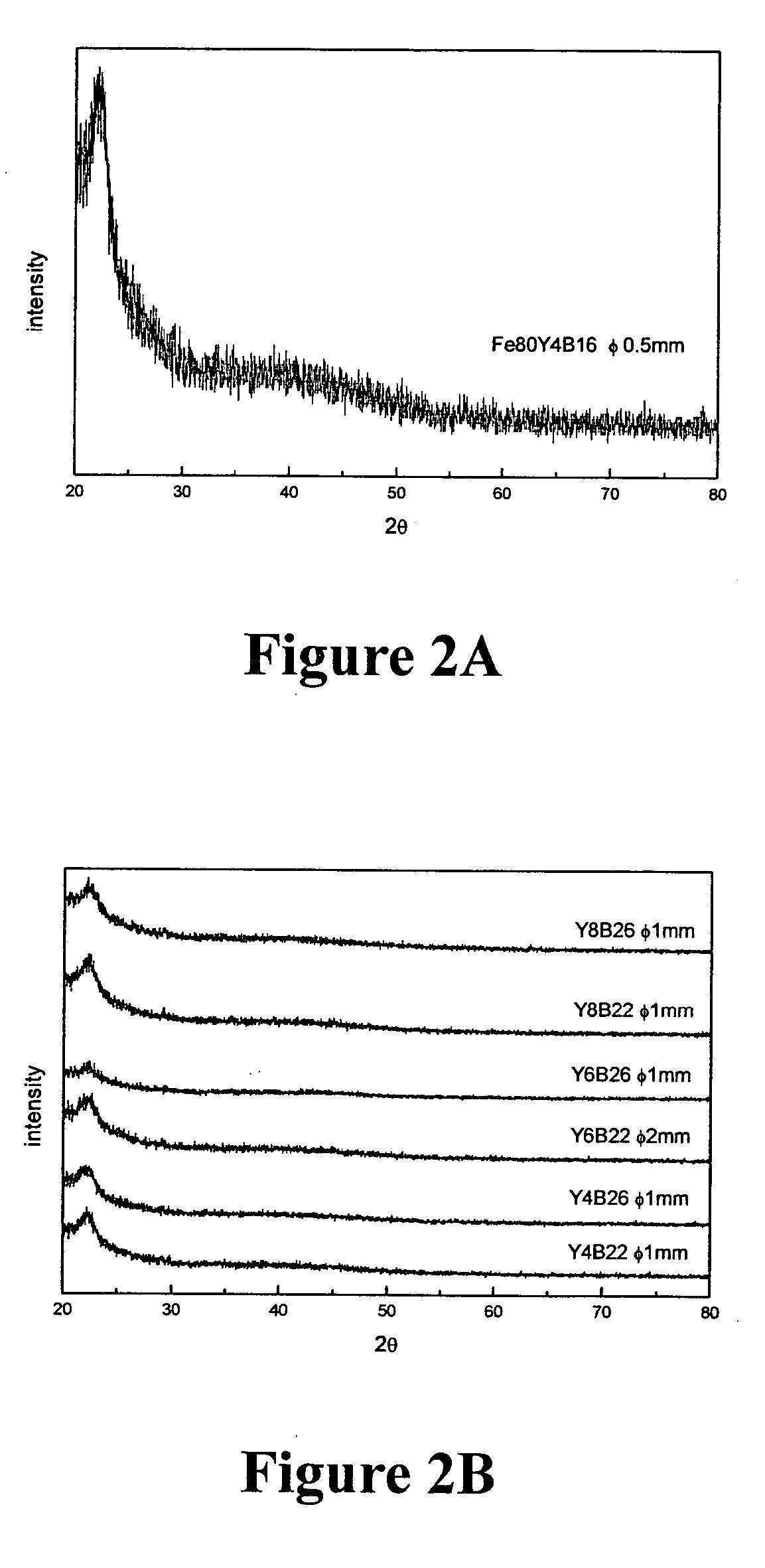
InactiveUS20050263216A1High glass forming abilityIncreased electrical resistivityMagnetic materialsAmorphous phaseAtomic radius
Disclosed in this invention is a family of ternary and multi-nary iron-based new compositions of bulk metallic glasses which possess promising soft magnetic properties, and the composition selection rules that lead to the design of such new compositions. The embodiment alloys are represented by the formula MaXbZc, where M represents at least one of ferromagnetic elements such as iron and may partly be replaced by some other substitute elements; X is an element or combinations of elements selected from those with atomic radius at least 130% that of iron and in the mean time is able to form an M-rich eutectic; and Z is an element or combinations of elements selected from semi-metallic or non-metallic elements with atomic radius smaller than 86% that of iron and in the meantime is able to form an M-Z eutectic; a, b, c are the atomic percentage of M, X, Z, respectively, and a+b+c=100%. When 1%<b<15% and 10%<c<39%, the alloys show a bulk glass forming ability to cast amorphous ribbons / sheets at least 0.1 mm in thickness. When 3%<b<10% and 18%<c<30%, the alloys show a bulk glass forming ability to cast amorphous rods at least 1 mm in diameter. The amorphous phase of these as-cast sheets / rods is at least 95% by volume. This invention also discloses the existence of nano-crystalline phase outside of the outer regime of the bulk glass forming region mentioned above.
Owner:NATIONAL TSING HUA UNIVERSITY
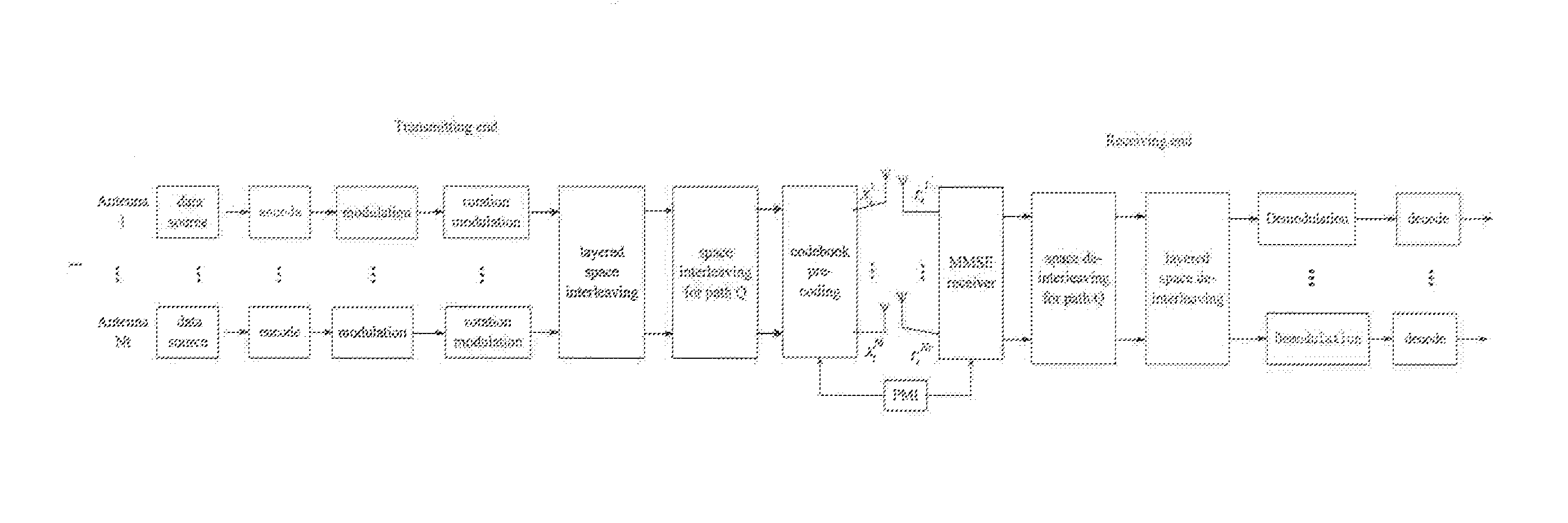
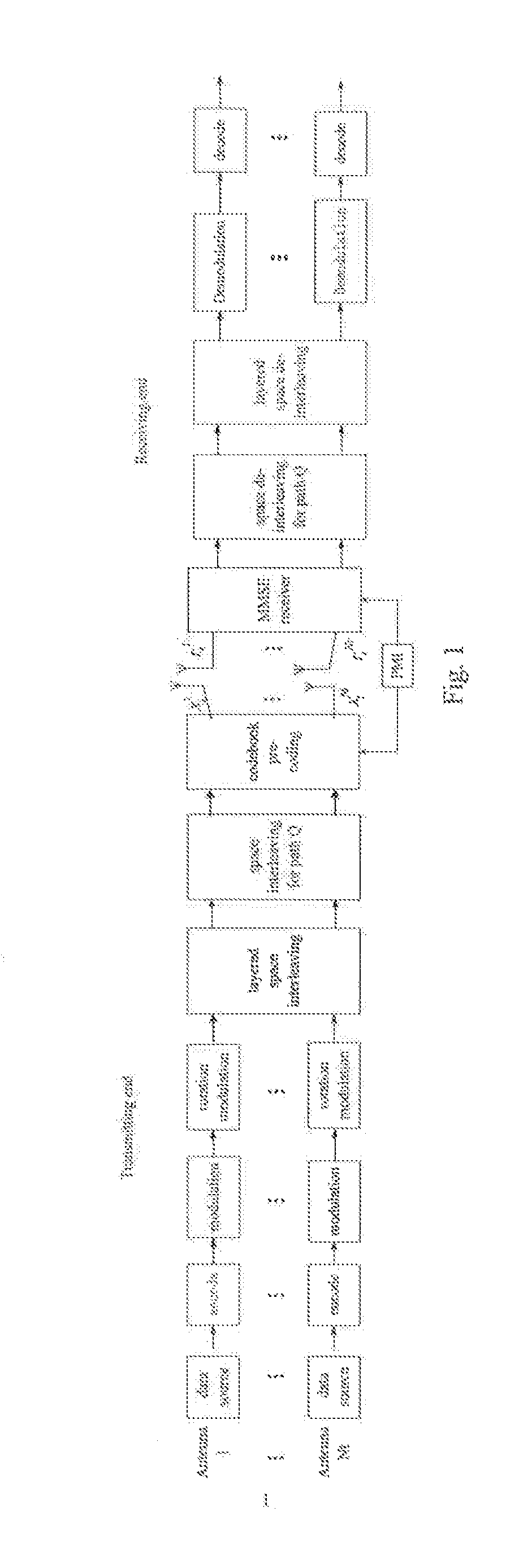
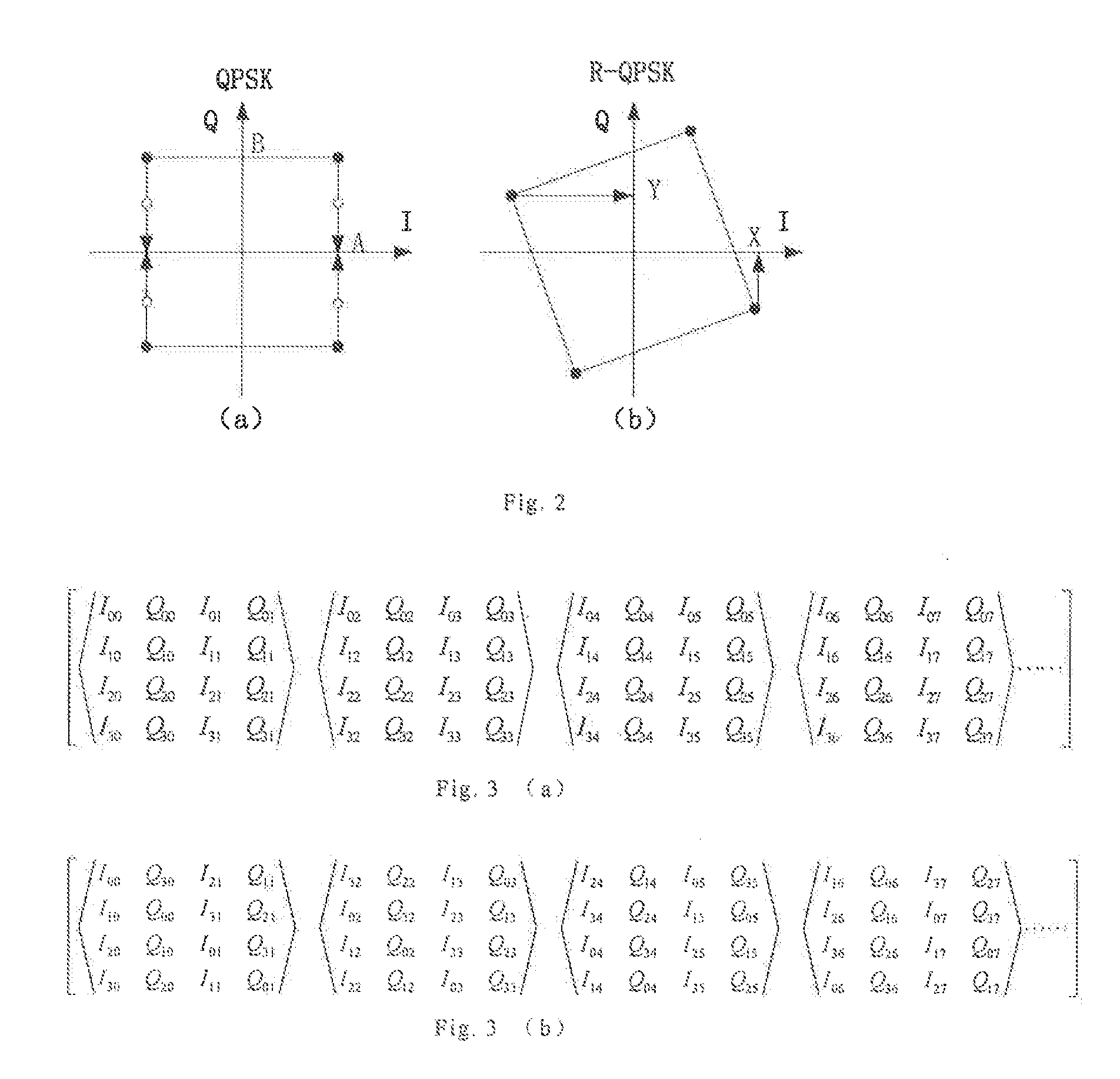
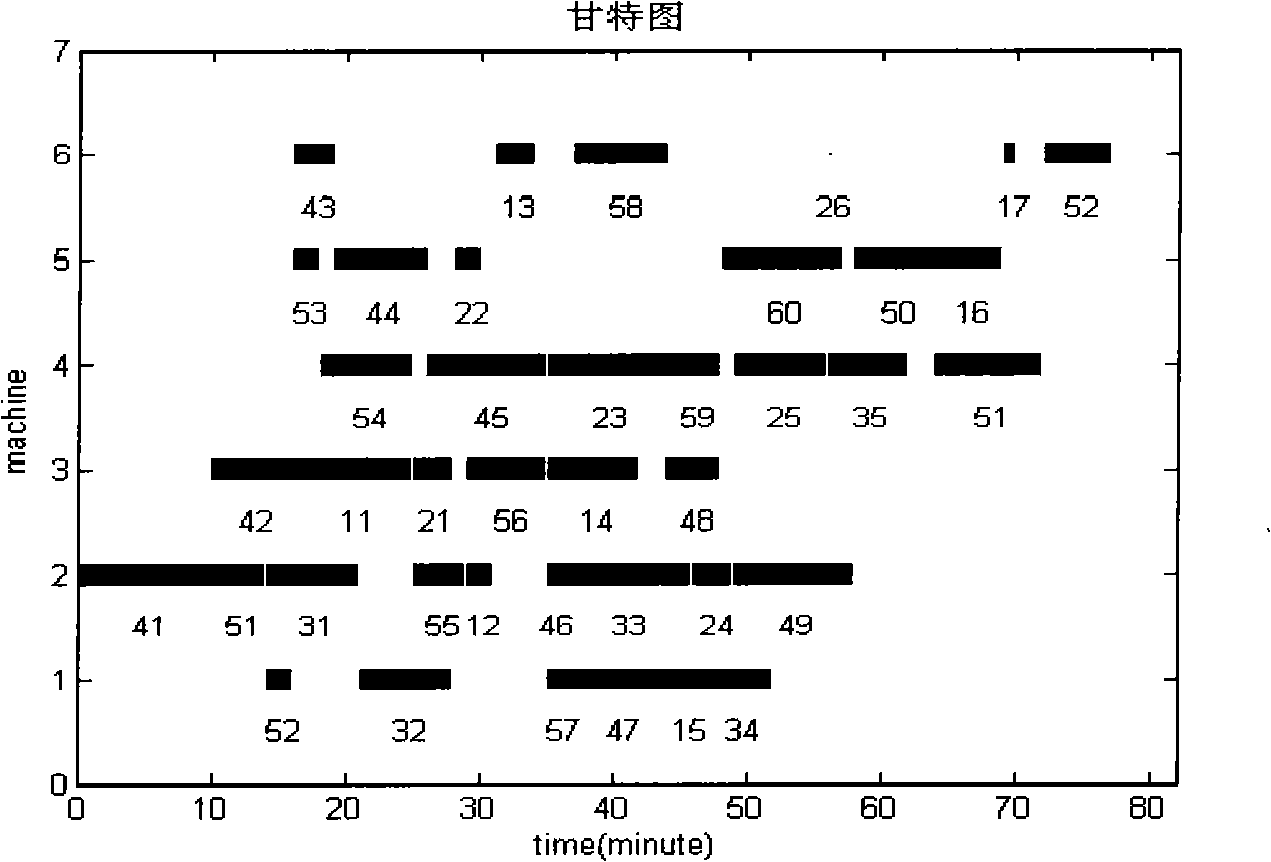
Multi-antenna codebook selection modulation method for solving weak scattering
InactiveUS20130251058A1Increase diversityReduce error rateSpatial transmit diversityChannel estimationDiversity schemeHigher-order modulation
A multi-antenna codebook selection modulation method for solving weak scattering is provided by the present invention. The method obtains higher diversity gain from a combination of multi-antenna codebook pre-coding and a rotation modulation solution by designing a new codebook selection rule. The present invention employs a design solution of designing a higher-order modulation diversity and space interleaver to obtain the higher diversity gain. In addition, the number of transmission antennas and the number of rotation modulation dimension can be set arbitrarily. However, the present invention takes the number Nt of transmission antennas to be equal to the number D of rotation modulation dimension in order to obtain higher diversity gain. In this way, the method evenly disperses signals of each dimension after D-dimensional rotation to each antenna through space interleaving technique, so that the signals of each dimension suffer different fading, thus enabling space diversity gain. With the present invention, the data of a transmitting end are pre-coded by using a channel value estimated for an ideal channel.
Owner:BEIJING UNIV OF POSTS & TELECOMM
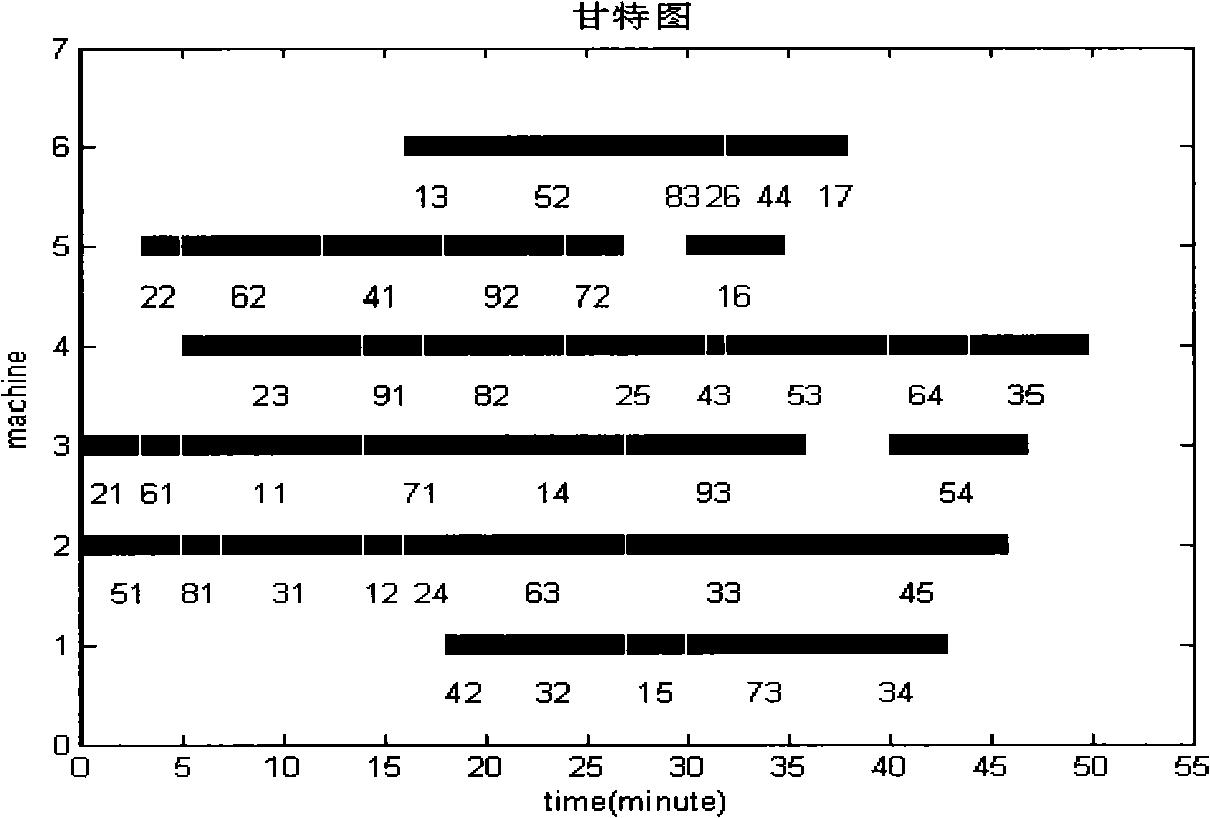
Right changing type accidental scheduling method based on real time condition
InactiveCN101303597AEasy to handleAvoid getting stuck in local optimumTotal factory controlAdaptive controlTime conditionStrong coupling
The invention discloses a variable weight type random scheduling method based on real-time working conditions; the scheduling method optimizes the problem of the dynamic random rescheduling in terms of classification of various perturbation, rescheduling driving mechanism, the construction of rescheduling majorized set, the selection rule of the workpieces to be processed and rescheduling optimization algorithm, classifies various perturbation in the production process into two classes of invisible perturbation and dominant perturbation, adopts corresponding rescheduling driving mechanisms according to different types of perturbation, thus quickly and effectively dealing with various uncertain problems which randomly occur in the production process; the scheduling method is suitable for the mode with a plurality of varieties and single-piece small lot production, can rapidly and effectively handle the various uncertain problems which randomly occur in the production scheduling process and has strong coupling capacity with the real-time working conditions, thus being capable of improving the self-adaptability of a workshop production system to the uncertain working conditions and the agility of production scheduling, reducing unnecessary rescheduling, enhancing reaction capacity to the working conditions and lowering the loss of the production system brought by the various uncertain problems.
Owner:HEFEI UNIV OF TECH
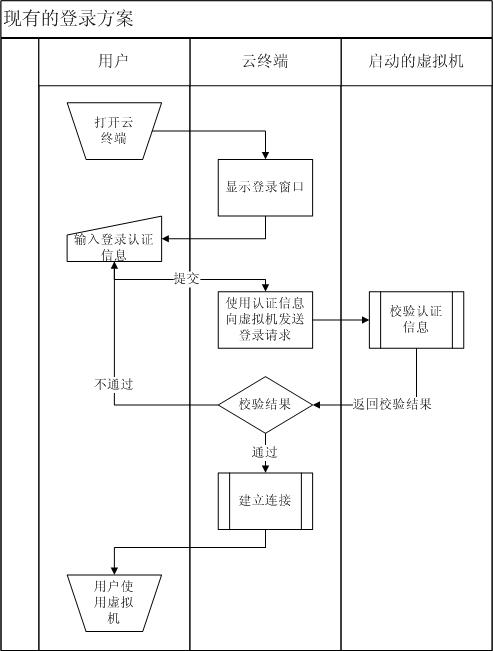
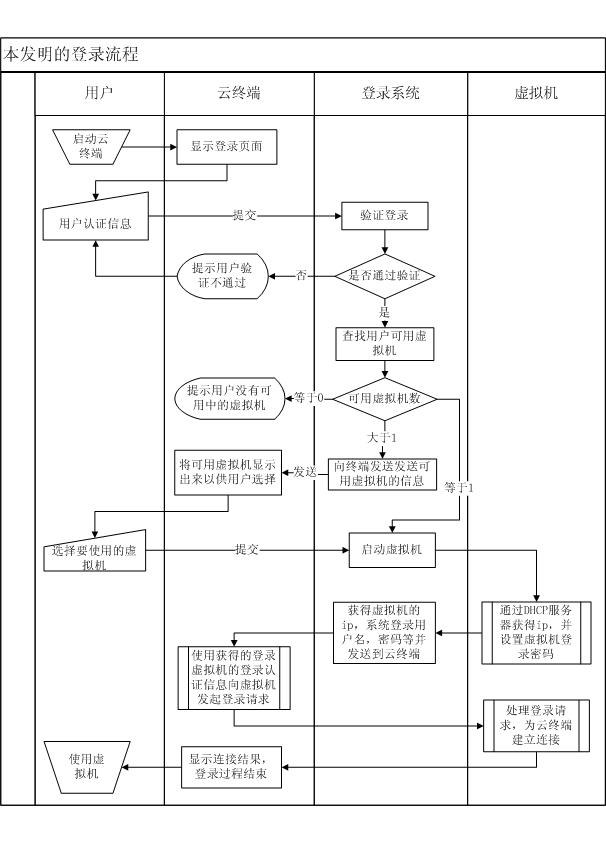
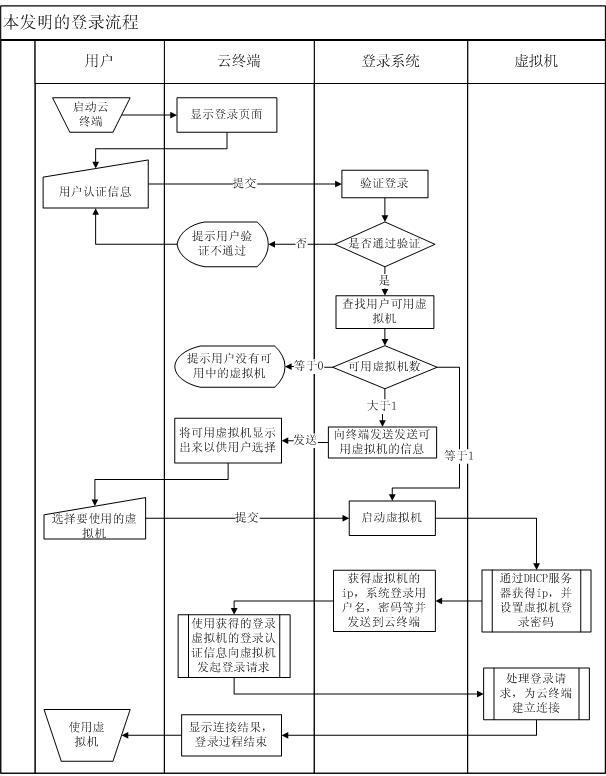
Method for mini-station to authenticate and log in virtual machine in cloud system and login system
The invention discloses a method for a mini-station to authenticate and log in a virtual machine in a cloud computing system and a login system. The method comprises the following steps that: (1) the mini-station logs in the cloud computing system by the login system; (2) the login system searches for the number of available virtual machines in the cloud computing system; (3) the login system starts the virtual machine in the cloud computing system according to virtual machine selection rules and executes steps (4) to (6) if the number of the available virtual machines is more than or equal to 1, otherwise returns information indicating that the cloud computing system does not have available resources to the mini-station, and the mini-station quits; (4) the virtual machine generates virtual machine login information, and transmits the virtual machine login information to the login system; (5) the login system transmits the virtual machine login information to the mini-station; and (6) the mini-station logs in the virtual machine. By the method and the login system, the mini-station can rapidly authenticate and log in the virtual machine, and the virtual machine is not required to be kept in a starting state so as to make safer the system and effectively save resources.
Owner:GCI SCI & TECH
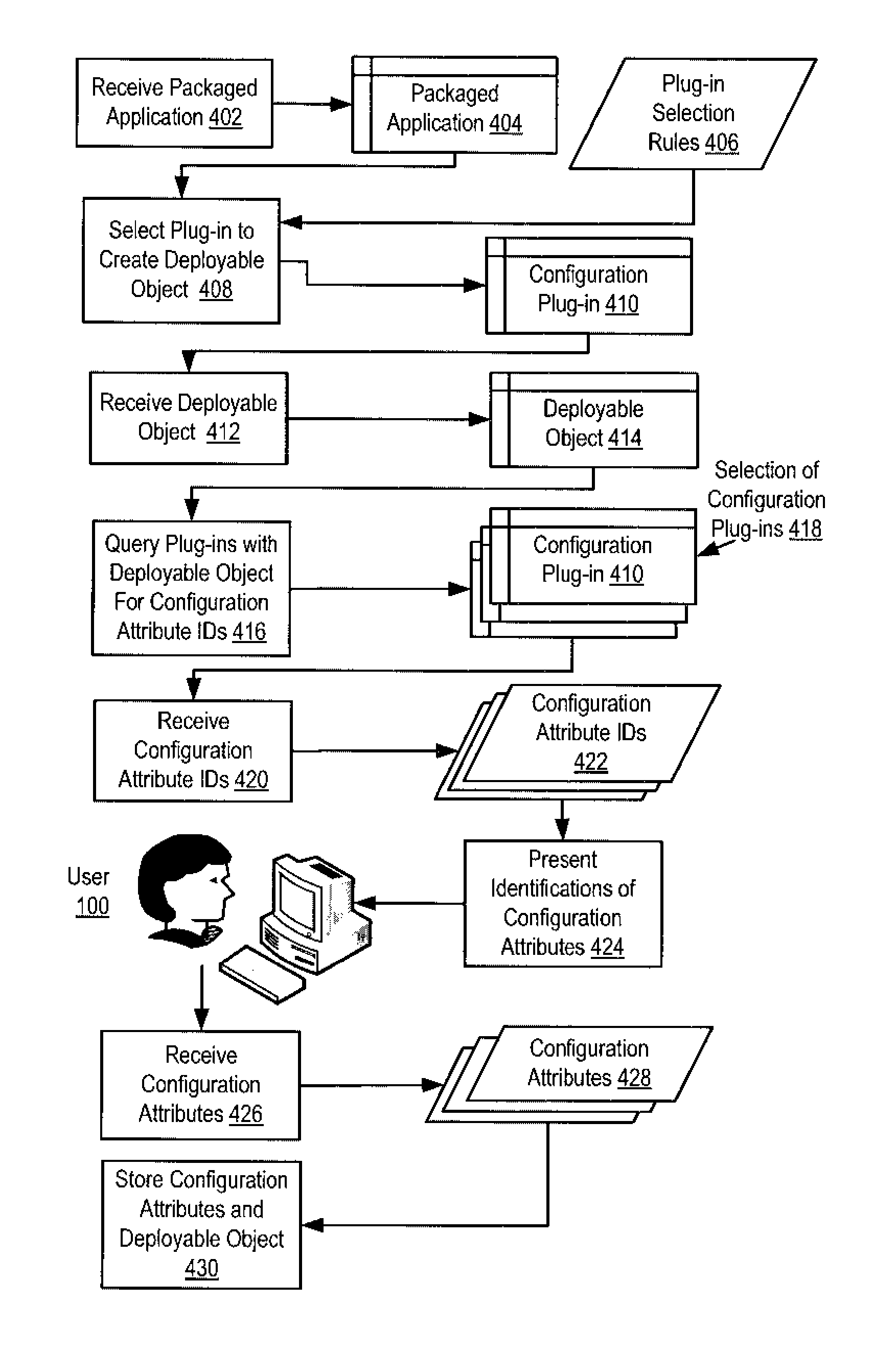
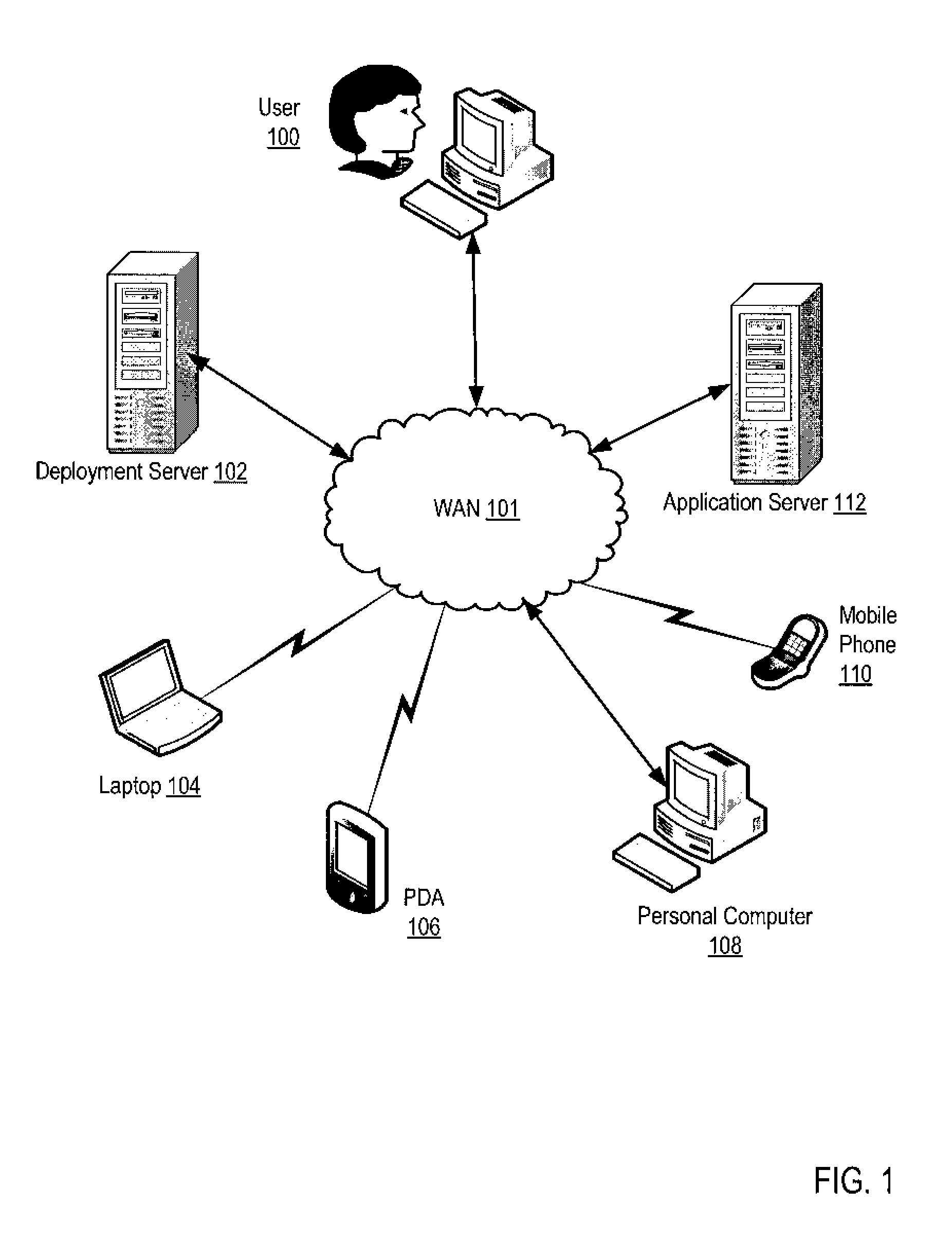
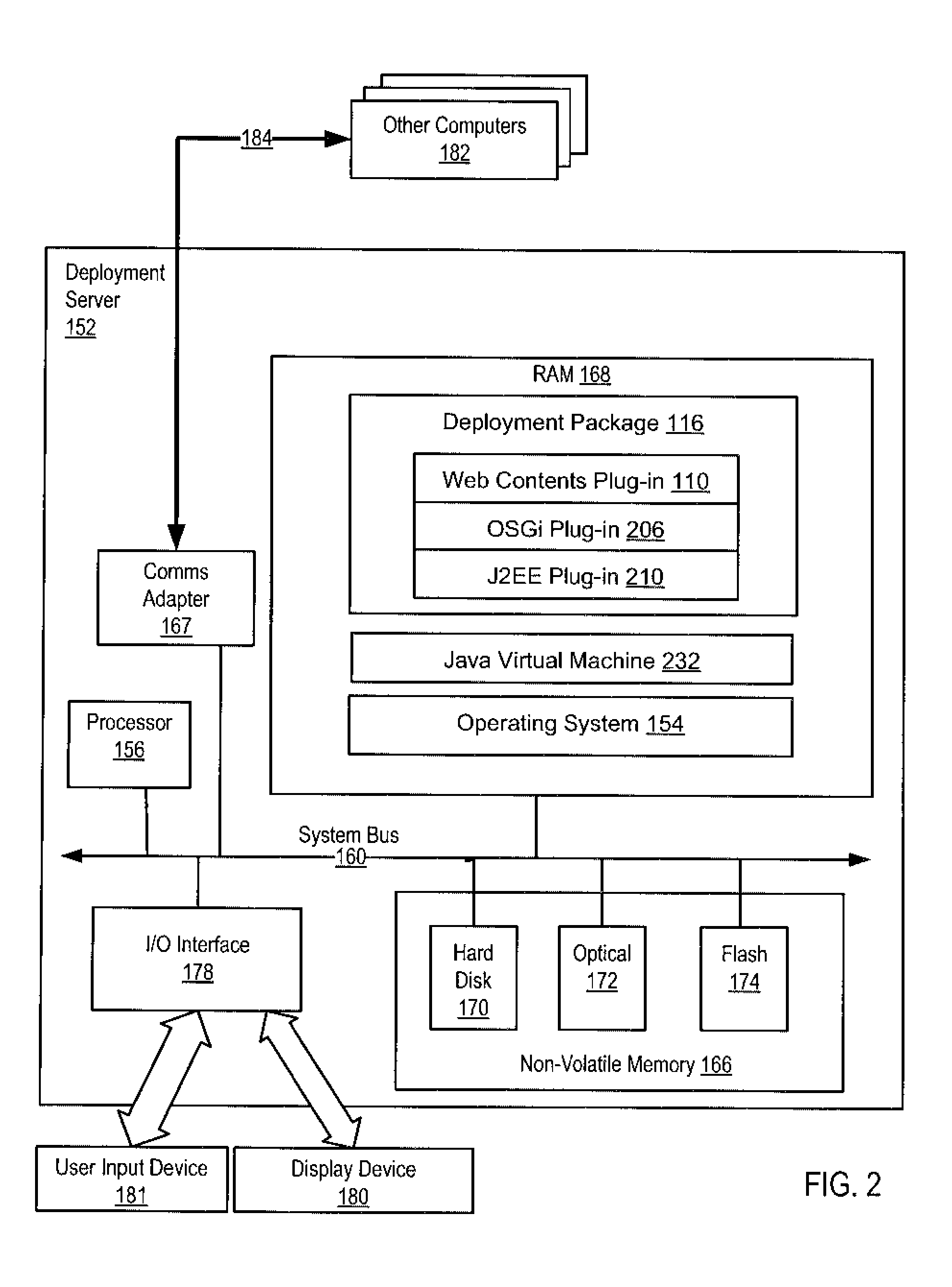
Programming model generic application deployment
Methods, systems, and computer program products are provided for deploying an application. Embodiments include receiving a packaged application for deployment and an instruction to perform a deployment management operation; selecting in dependence upon plug-in selection rules one of a plurality of configuration plug-ins for creating a deployable object from the packaged application; receiving from the selected configuration plug-in a deployable object; querying one or more of the plurality of configuration plug-ins with the deployable object for identifications of configuration attributes needed to perform the deployment management operation; receiving from each of the queried configuration plug-ins identifications of configuration attributes needed to deploy the deployable object; presenting the identifications of configuration attributes needed to deploy the deployable object to a user; receiving from the user the configuration attributes needed to deploy the deployable object; and storing the deployable object and the configuration attributes.
Owner:IBM CORP
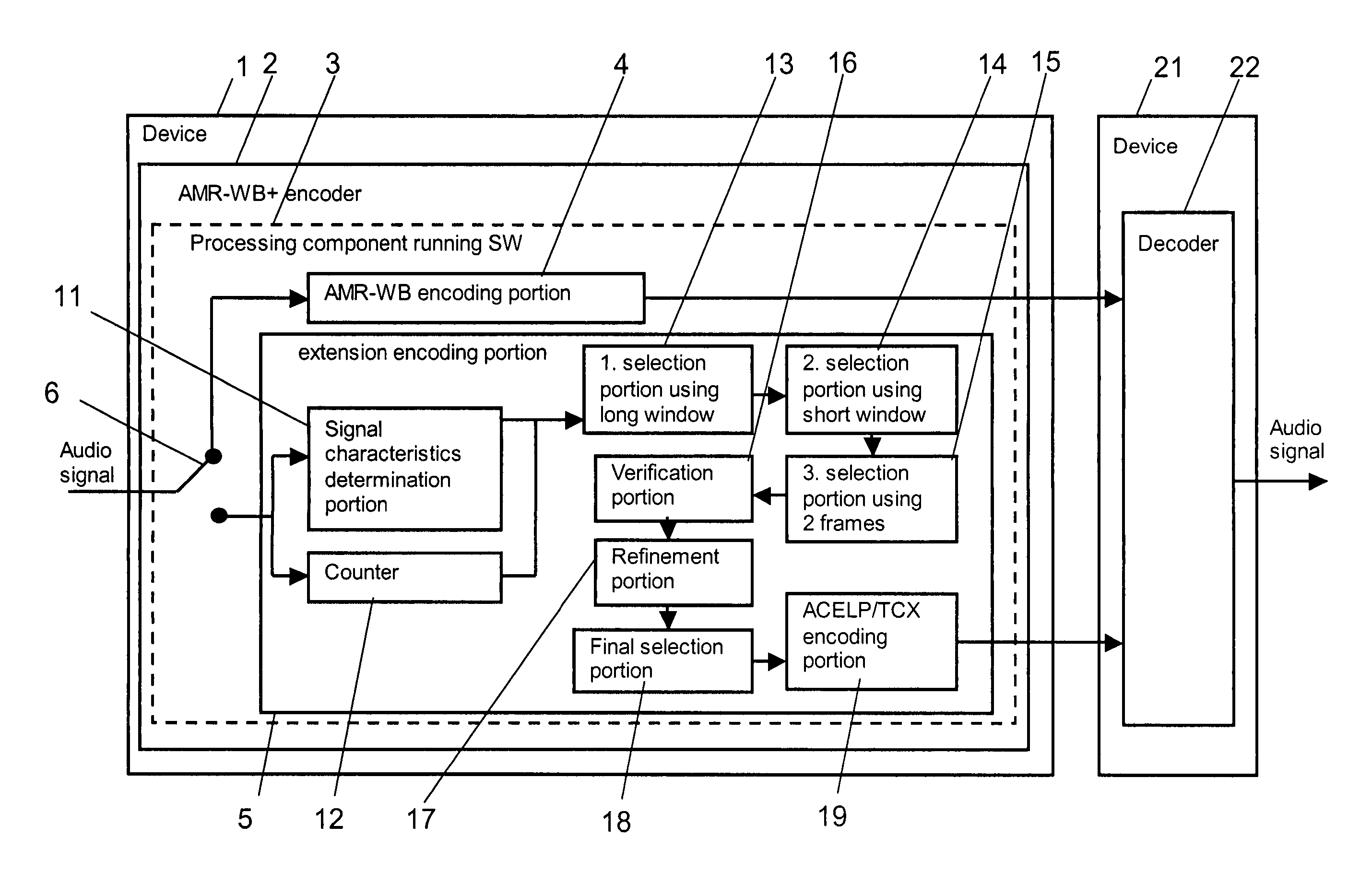
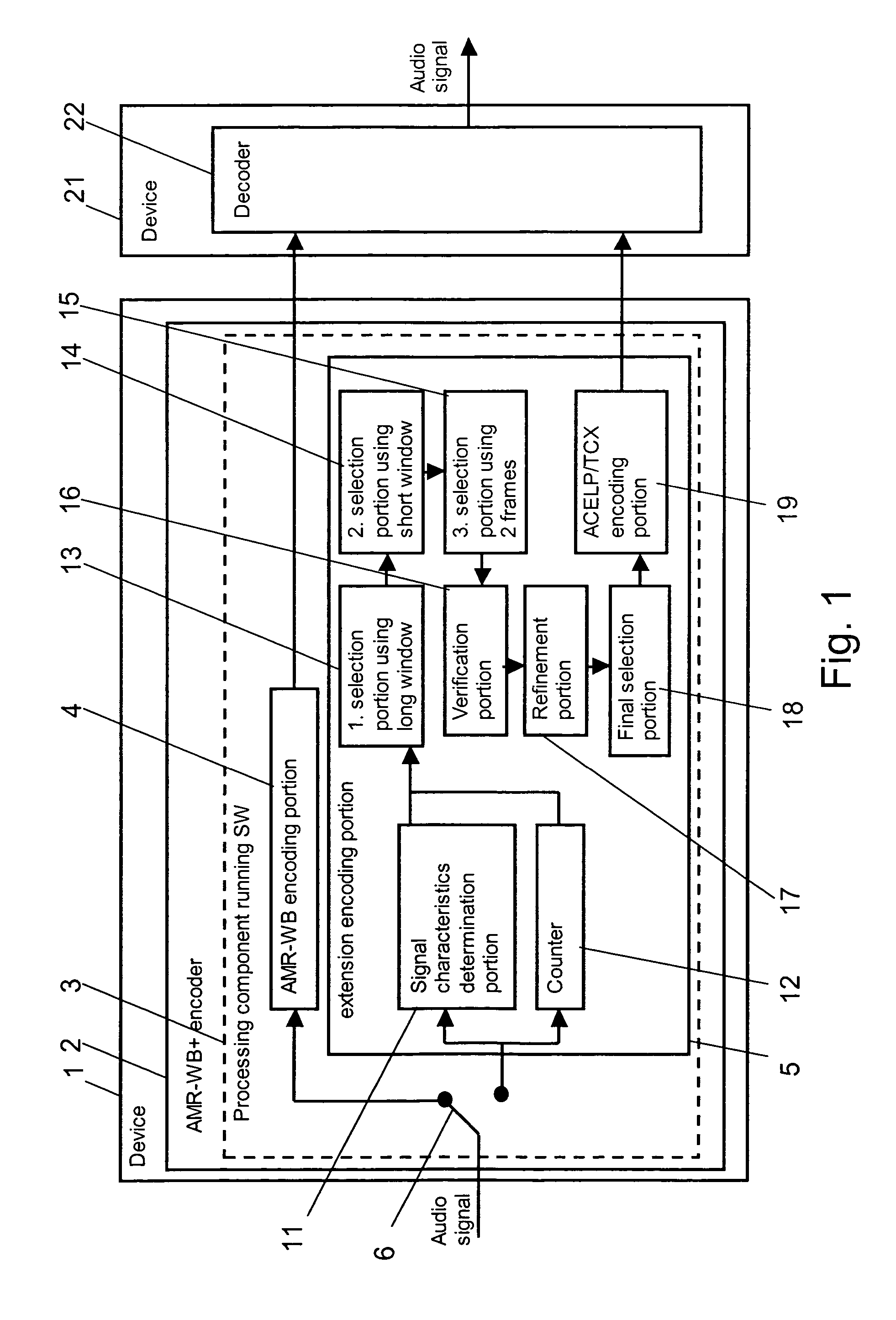
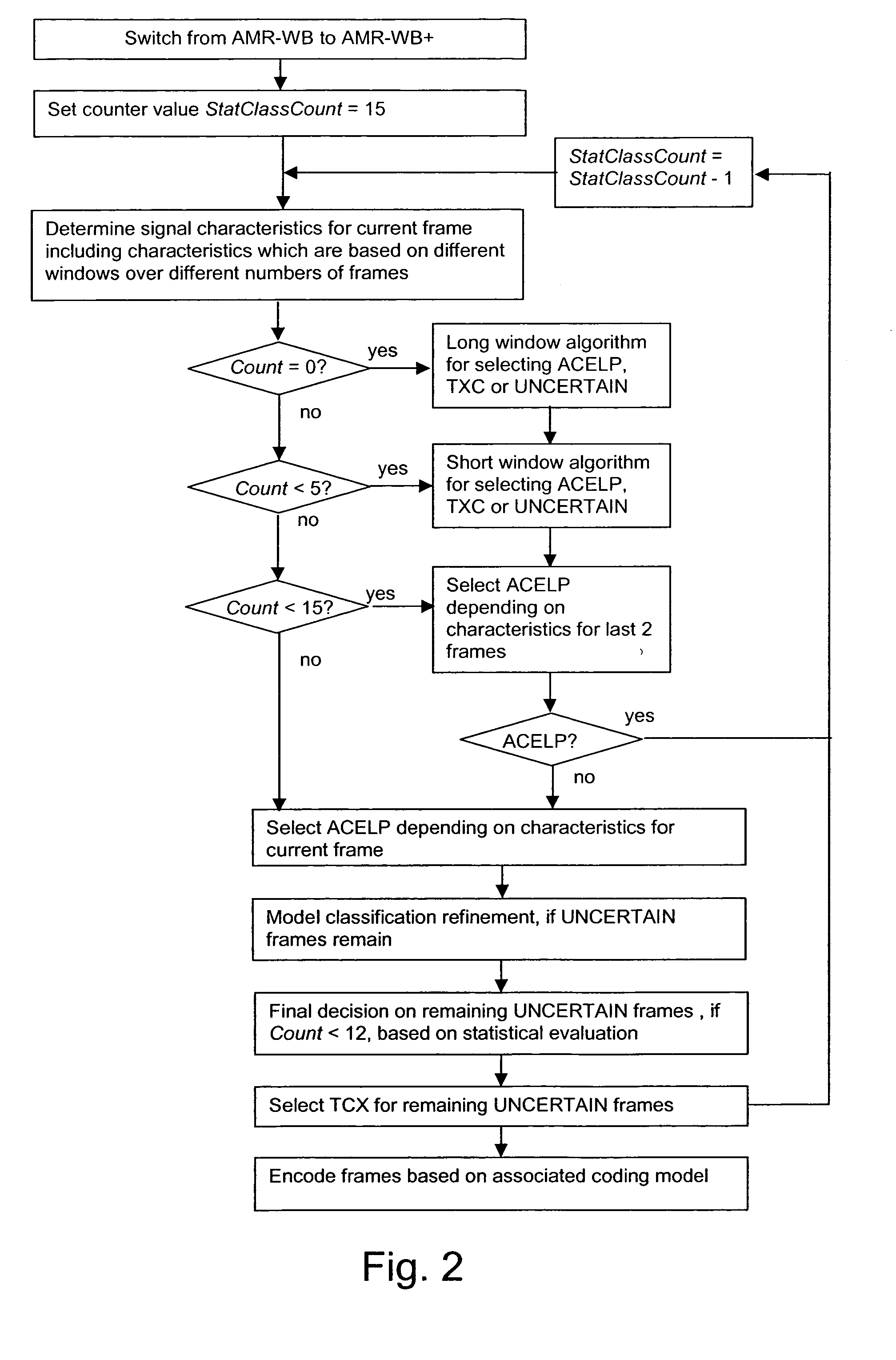
Audio encoding with different coding models
A method for supporting an encoding of an audio signal is shown, wherein at least a first and a second coder mode are available for encoding a section of the audio signal. The first coder mode enables a coding based on two different coding models. A selection of a coding model is enabled by a selection rule which is based on signal characteristics which have been determined for a certain analysis window. In order to avoid a misclassification of a section after a switch to the first coder mode, it is proposed that the selection rule is activated only when sufficient sections for the analysis window have been received. The invention relates equally to a module 2,3 in which this method is implemented, to a device 1 and a system comprising such a module 2,3, and to a software program product including a software code for realizing the proposed method.
Owner:NOKIA TECHNOLOGLES OY
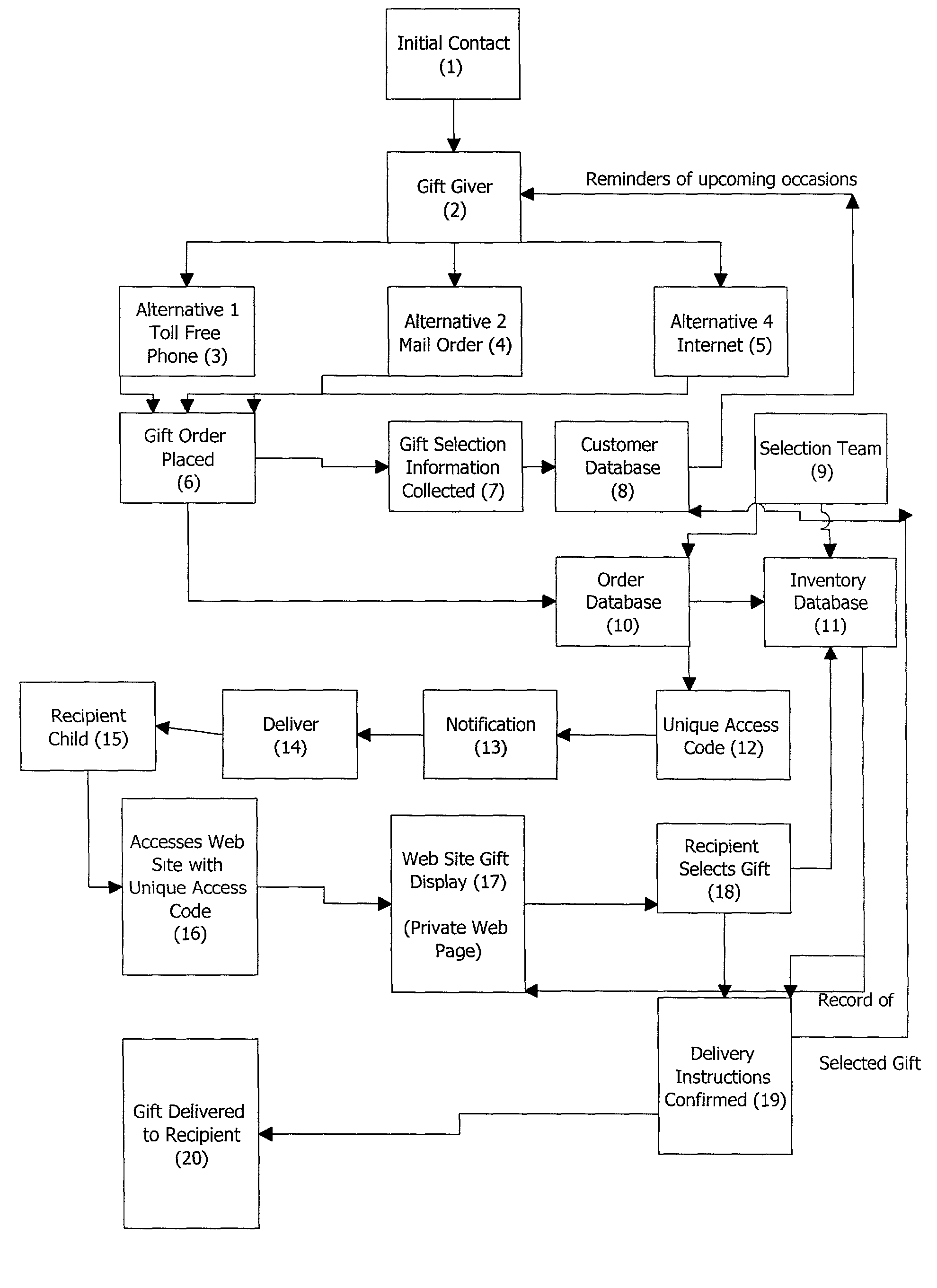
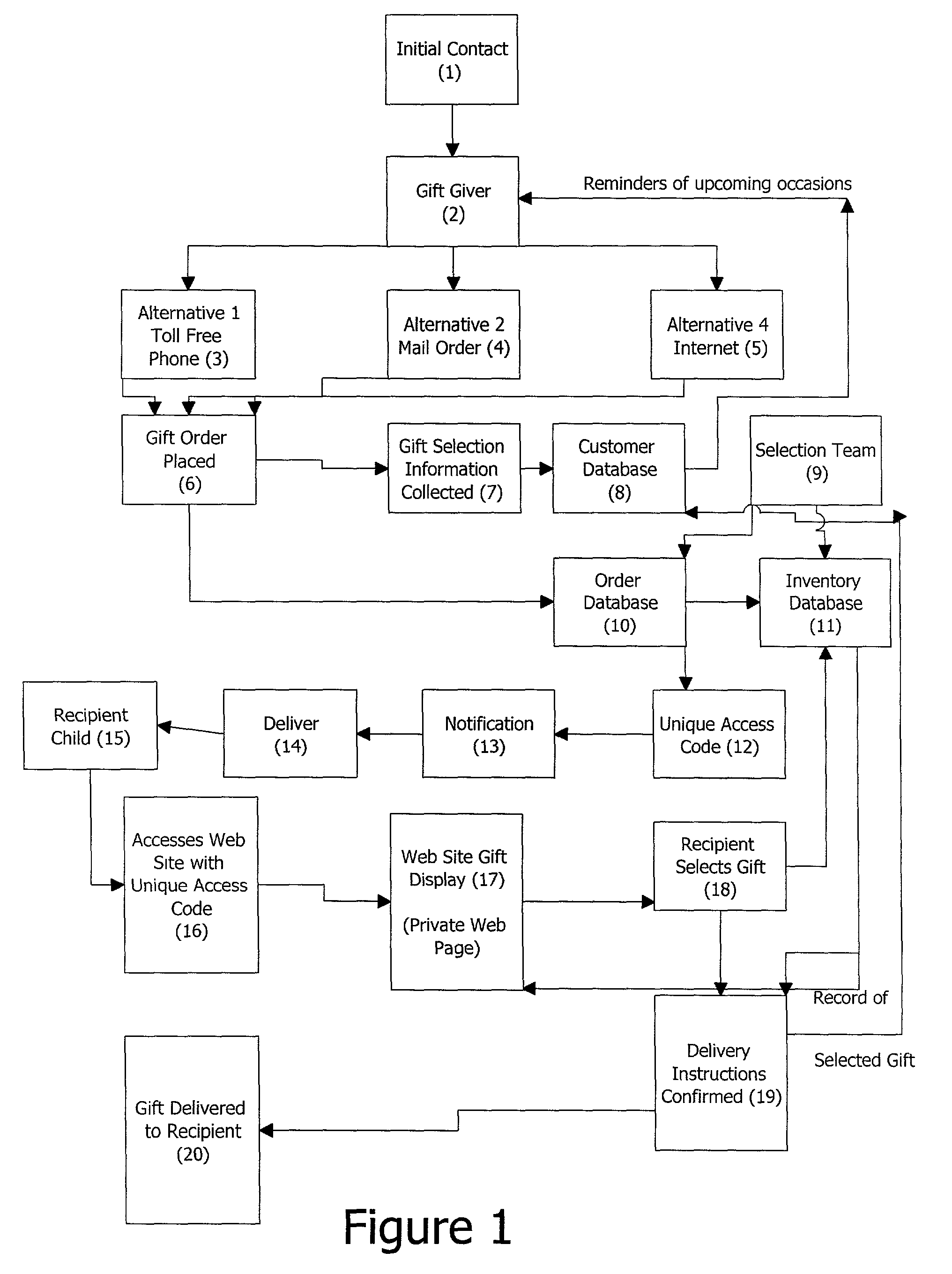
Gift selection and fulfillment system
InactiveUS7117168B2Good choiceDiscounts/incentivesBuying/selling/leasing transactionsNotification ReceiverSelection criterion
The invention provides a method for gift selection and fulfillment, especially suited to children, which comprises: contacting a potential gift giver by conventional advertising; providing information to the potential gift giver for contacting an order accepting system; obtaining an order from the gift giver that includes a set of gift selection criteria; supplying a computer program for comparing that is used for comparing the gift selection criteria with a set of gift selection rules; and generating a set of gift choices and storing the gift choices in a database record-keyed to a unique access code: notifying the recipient of the unique access code to make a gift choice by means of a connection to a computer network; generating a display of the available gift choices along with a personal message and photo of the gift giver, keyed to the unique access code; recording the recipient's gift selection and generating a delivery order for delivery of the gift selected to the recipient. The method may that further comprise obtaining from the gift giver information regarding other children to whom the gift giver wishes to give gifts on specified occasions; storing the information with gift giver contact information; and sending a reminder of the specified gift occasion to the gift giver to initiate a new gift selection and delivery. The method may include having the set of gift selection rules include special interest items. The method may also include gift selection rules that are provided by a team having one or more experts in child development, and with input from children.
Owner:RESOURCE CONSORTIUM LTD LLC
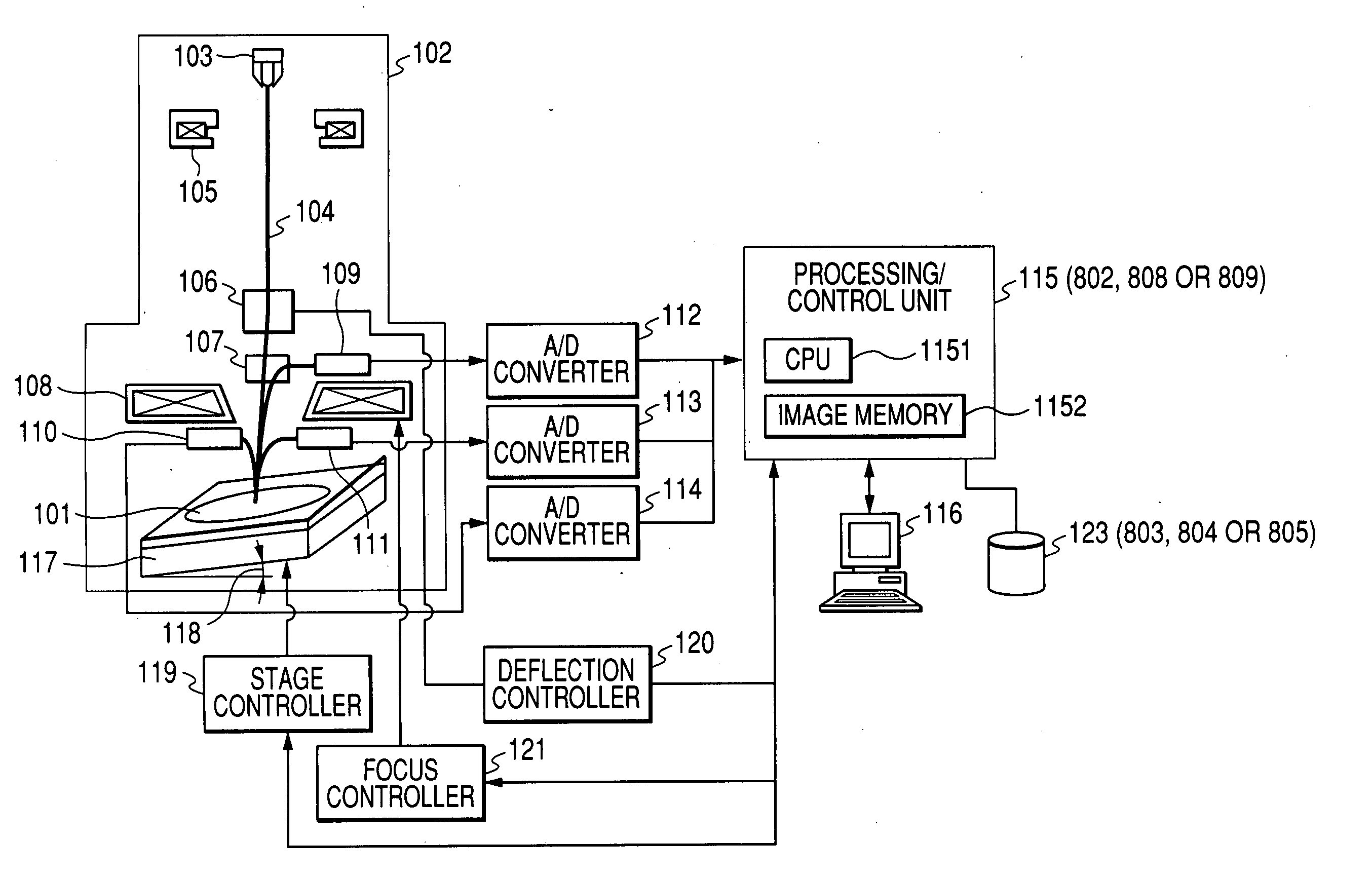
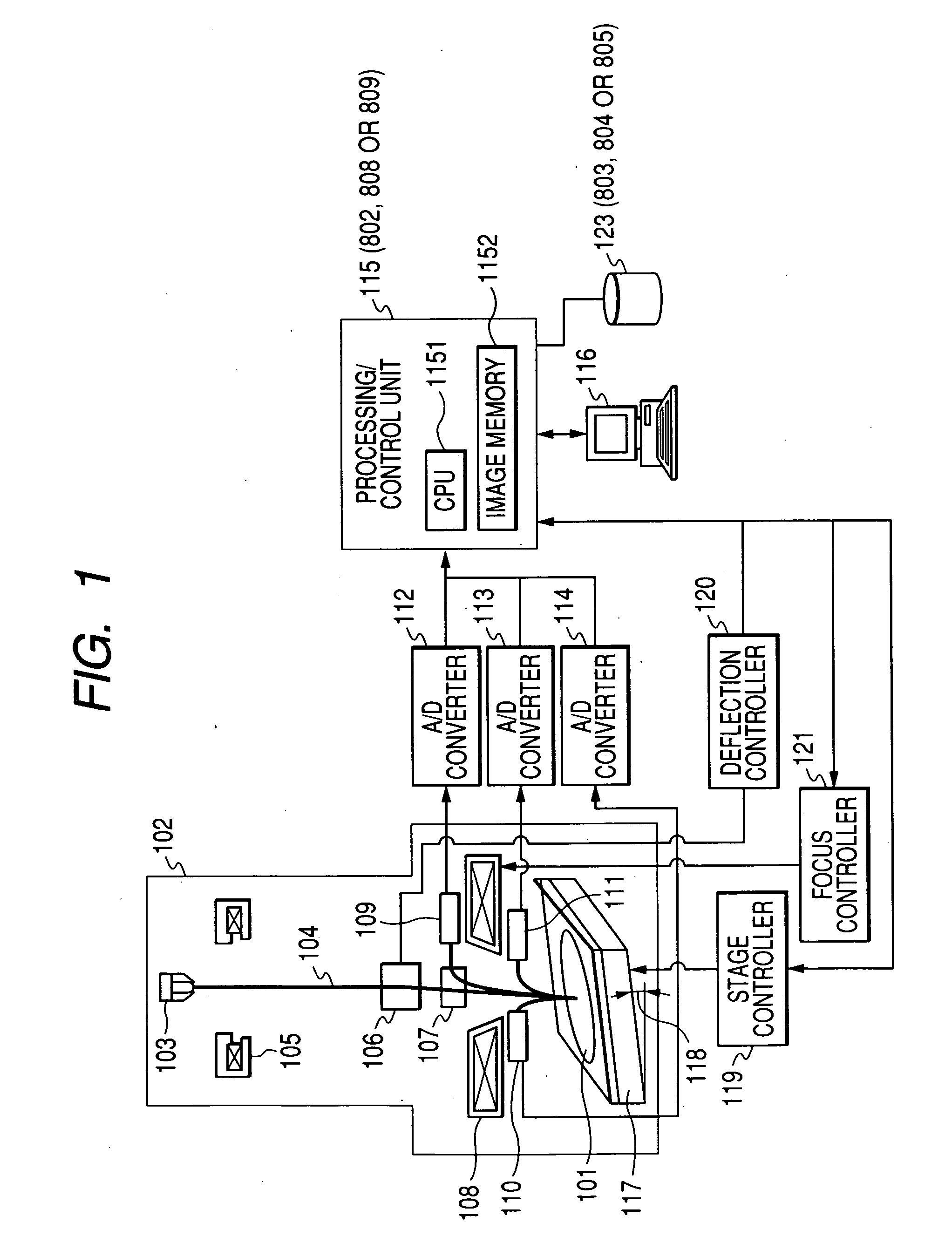
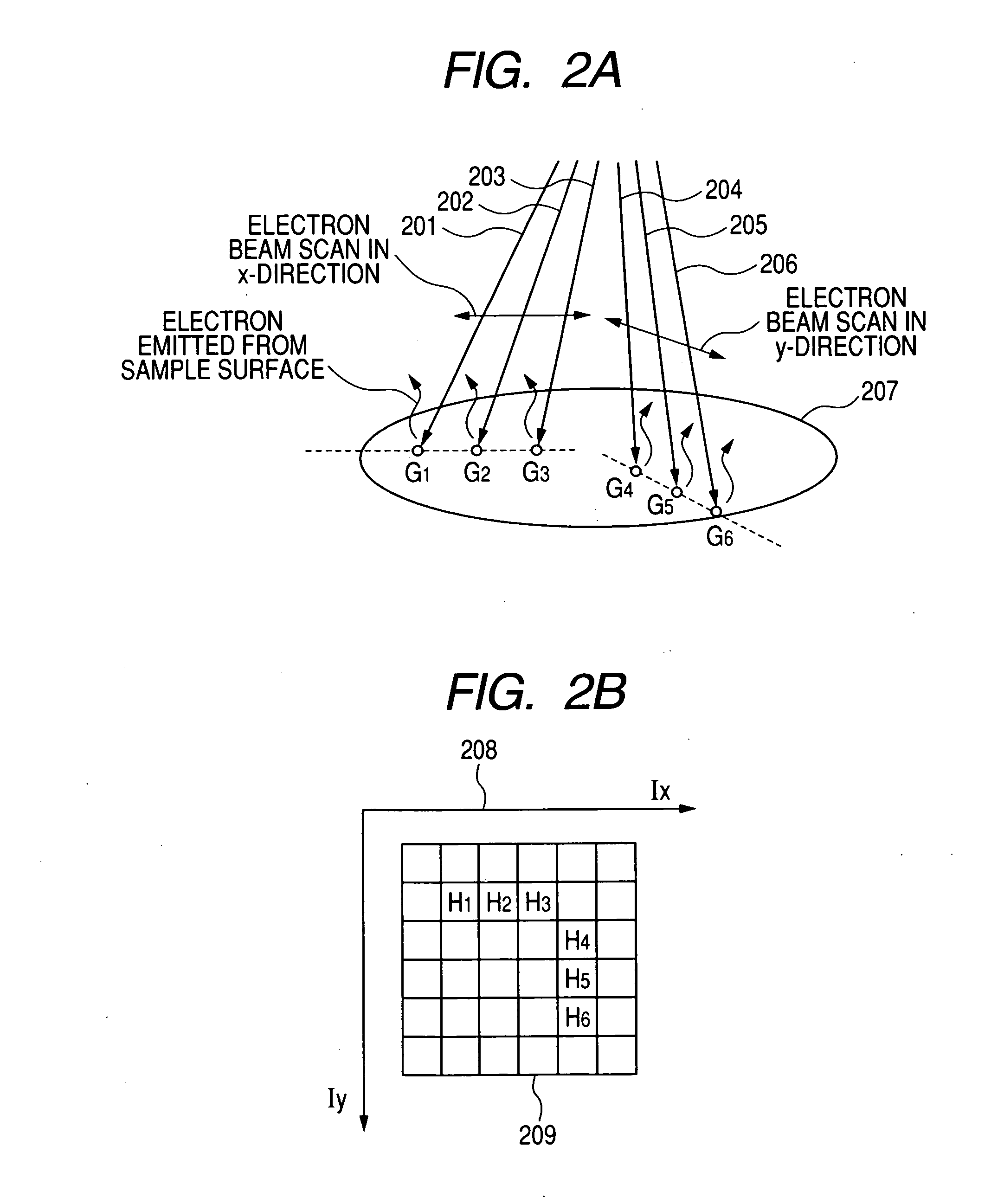
Method and apparatus for arranging recipe of scanning electron microscope and apparatus for evaluating shape of semiconductor device pattern
InactiveUS20060284081A1Increase speedQuickly accommodate changeMaterial analysis using wave/particle radiationElectric discharge tubesDevice materialMagnification
In order to provide an imaging-recipe arranging or creating apparatus and method adapted so that selection rules for automatic arrangement of an imaging recipe can be optimized by teaching in a SEM apparatus or the like, the imaging-recipe arranging or creating apparatus in this invention that arranges an imaging recipe for SEM-observing a semiconductor pattern using a scanning electron microscope includes a database that receives and stores layout information of the above semiconductor pattern in a low-magnification field, and an imaging-recipe arranging unit which, on the basis of the database-stored semiconductor pattern layout information, arranges the imaging recipe automatically in accordance with the automatic arrangement algorithm that includes teaching-optimized selection rules for selecting an imaging point(s).
Owner:HITACHI HIGH-TECH CORP
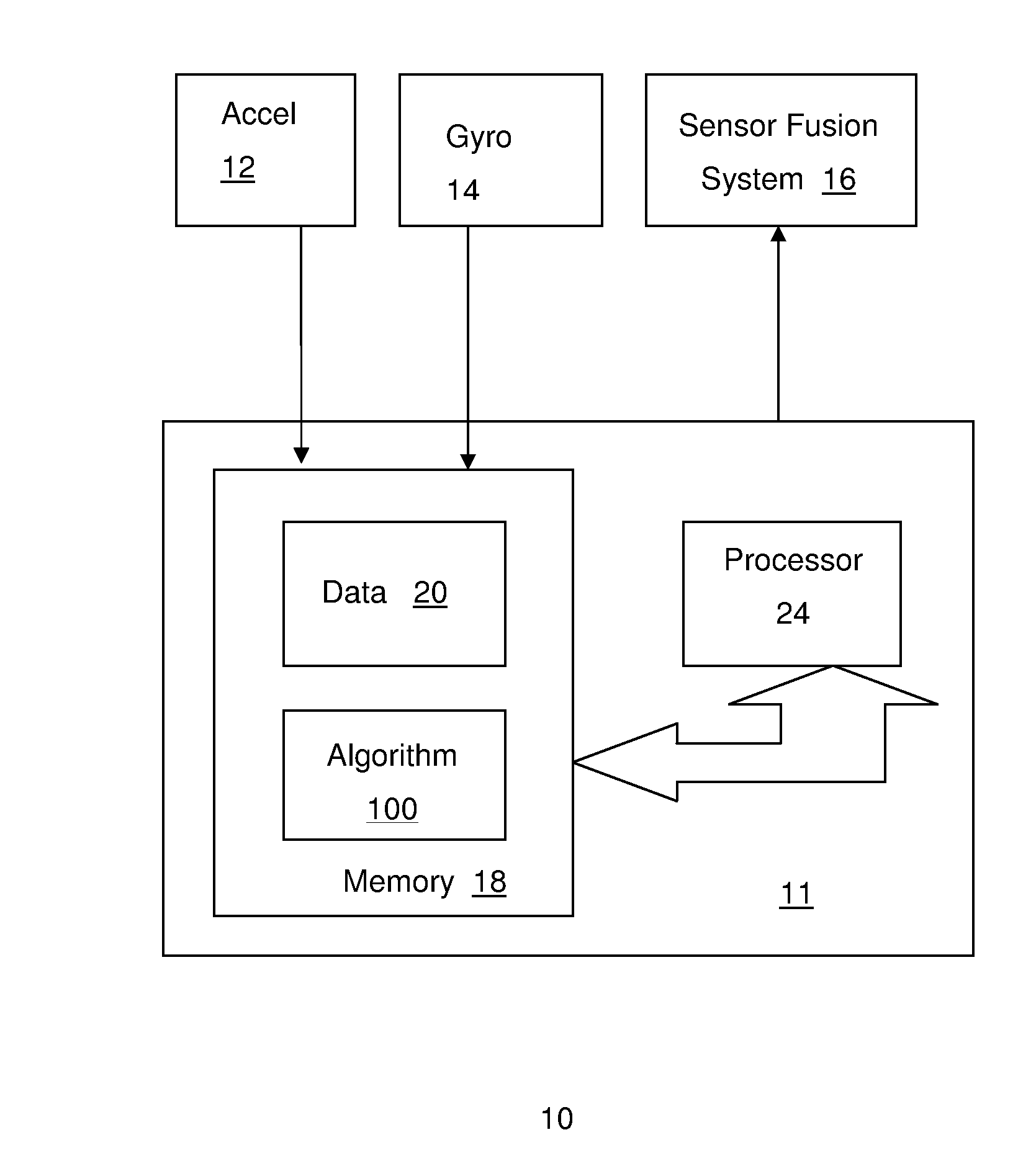
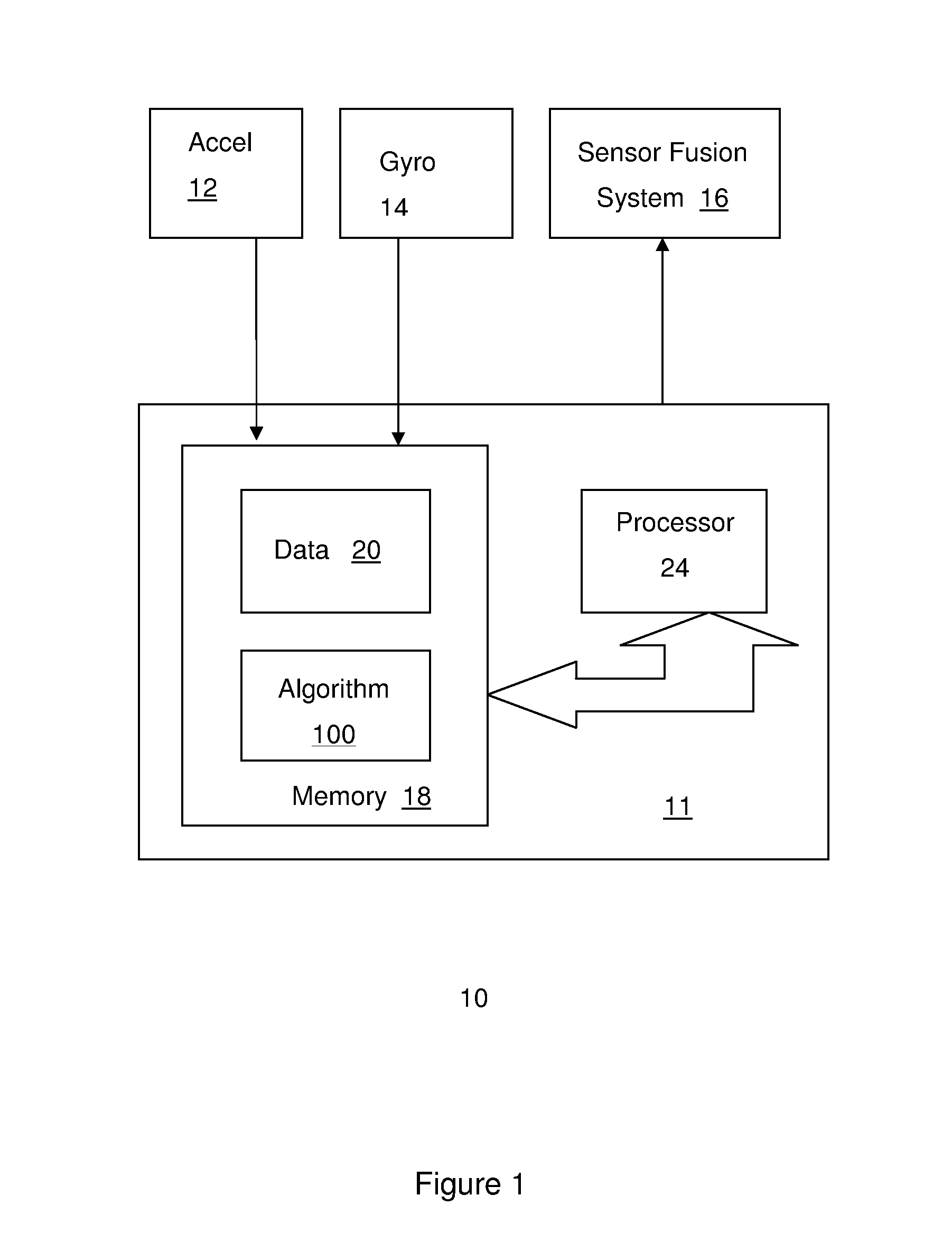
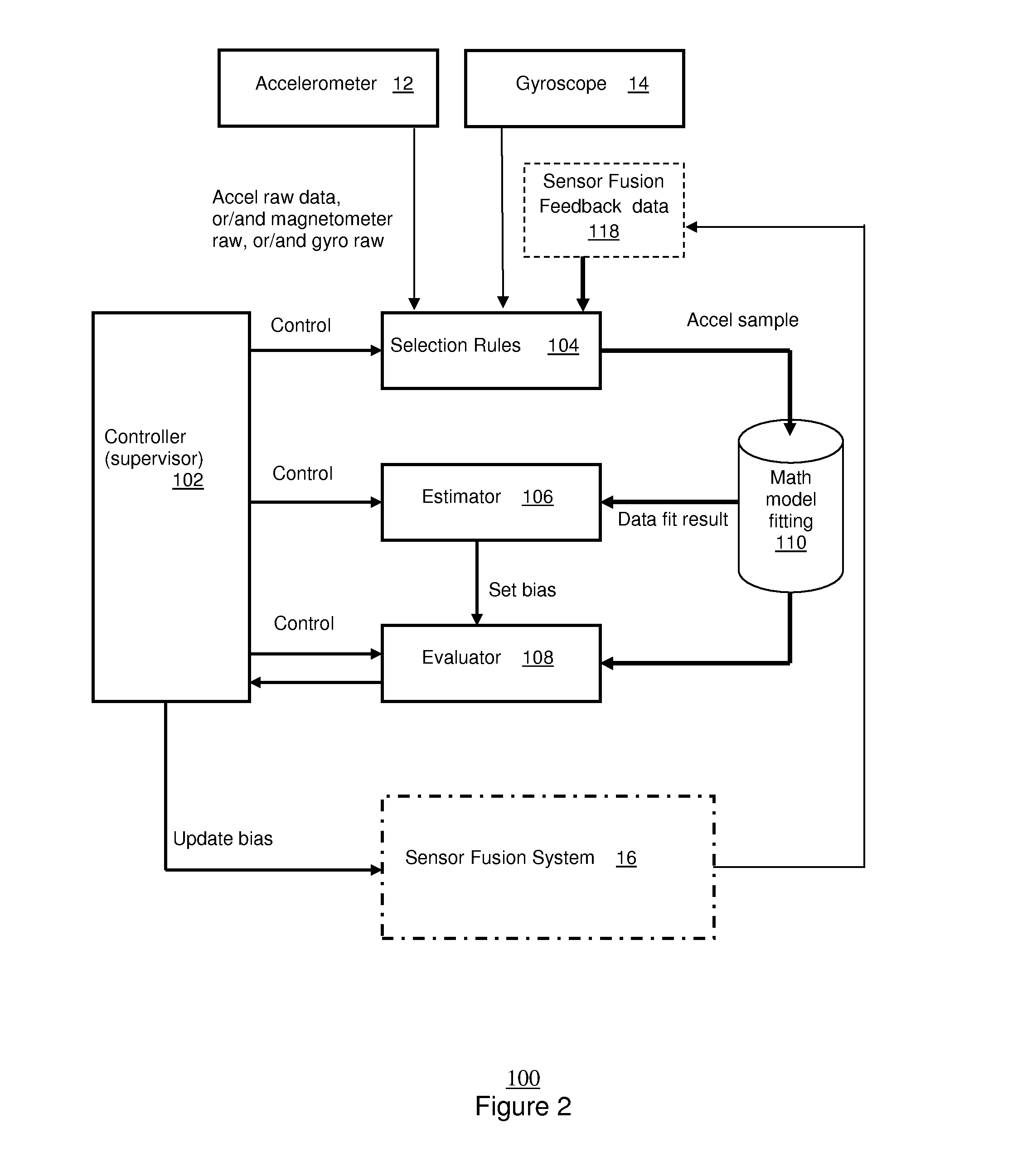
N-use automatic calibration methodology for sensors in mobile devices
ActiveUS20130197845A1Eliminate needTesting/calibration of speed/acceleration/shock measurement devicesComplex mathematical operationsAccelerometerAlgorithm
A method, system and computer readable medium for calibrating an accelerometer in a portable device is disclosed. The method, system and computer readable medium comprises receiving data from the accelerometer, and providing accelerometer samples from the data based upon one or more selection rules that adaptively selects data that satisfy certain criteria. The method system and computer readable medium also includes fitting the accelerometer samples to a mathematical mode. The method system and computer readable medium further includes providing a bias of the accelerometer based upon a center of the mathematical model.
Owner:INVENSENSE
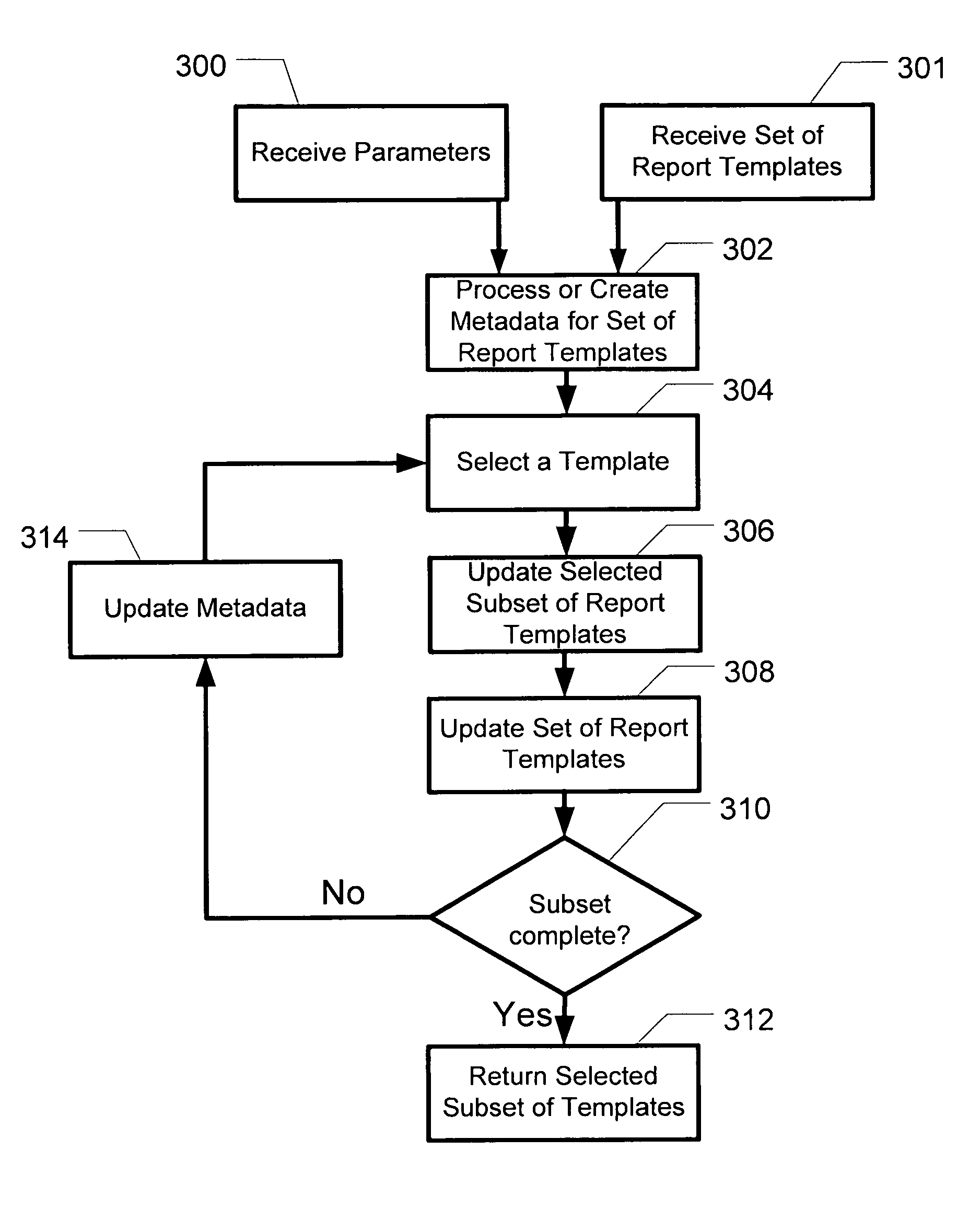
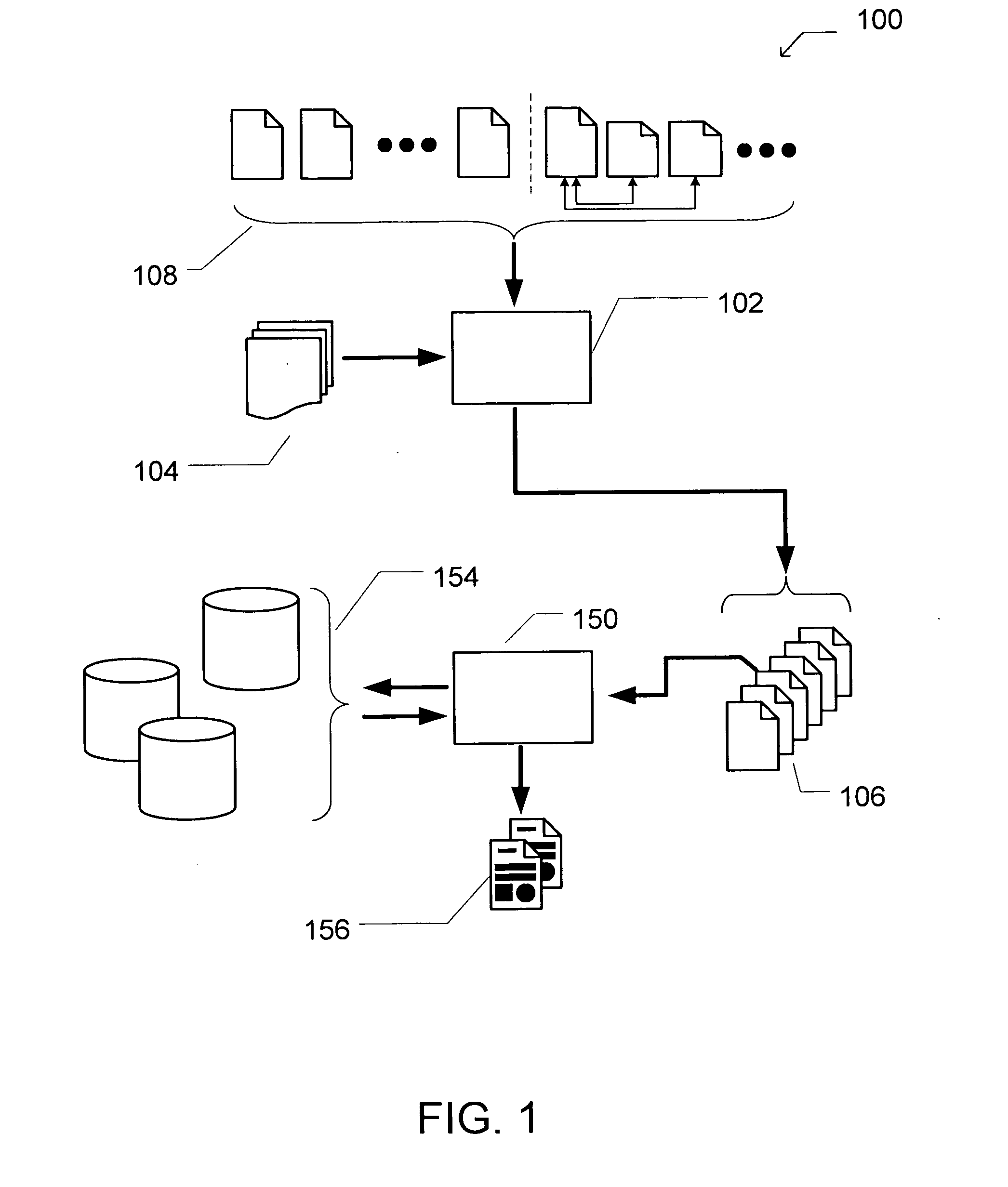
Apparatus and method for selecting a subset of report templates based on specified criteria
Owner:BUSINESS OBJECTS SOFTWARE
Scalable sensor localization for wireless sensor networks
InactiveUS7970574B2Error minimizationSolve small or large problems more accuratelyNetwork traffic/resource managementNetwork topologiesWireless sensor networkingSelf adaptive
Owner:THE BOARD OF TRUSTEES OF THE LELAND STANFORD JUNIOR UNIV
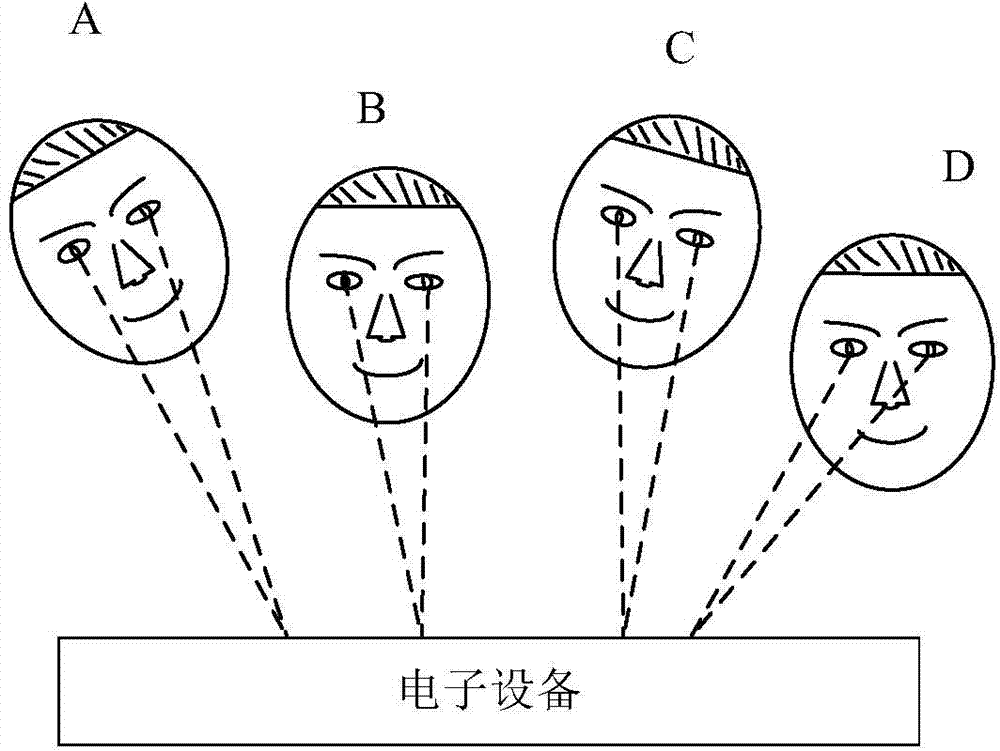
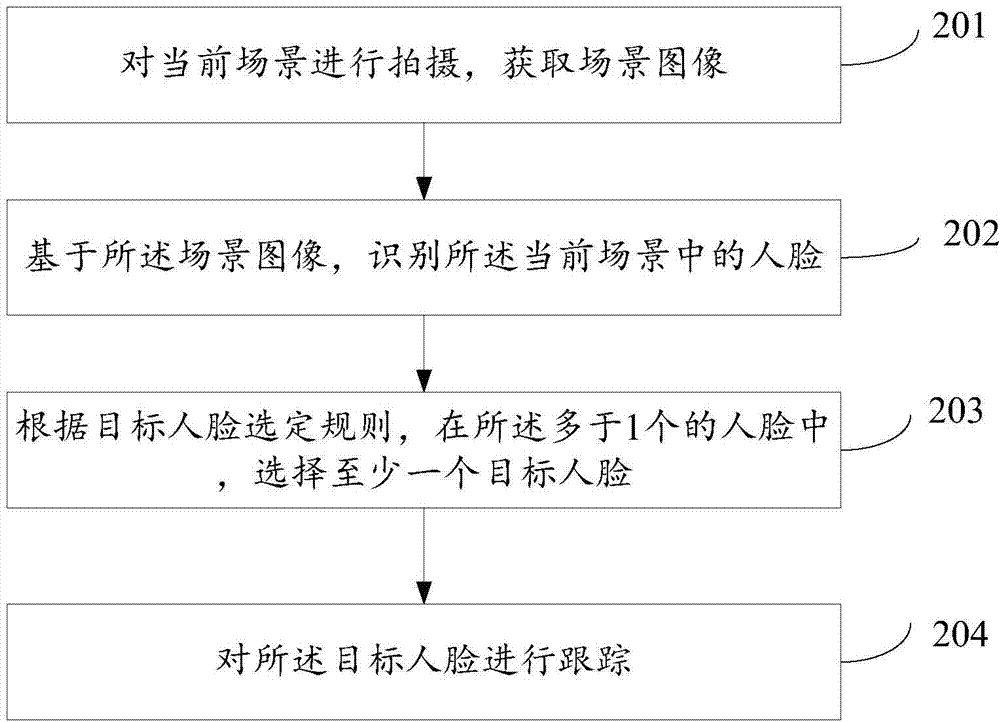
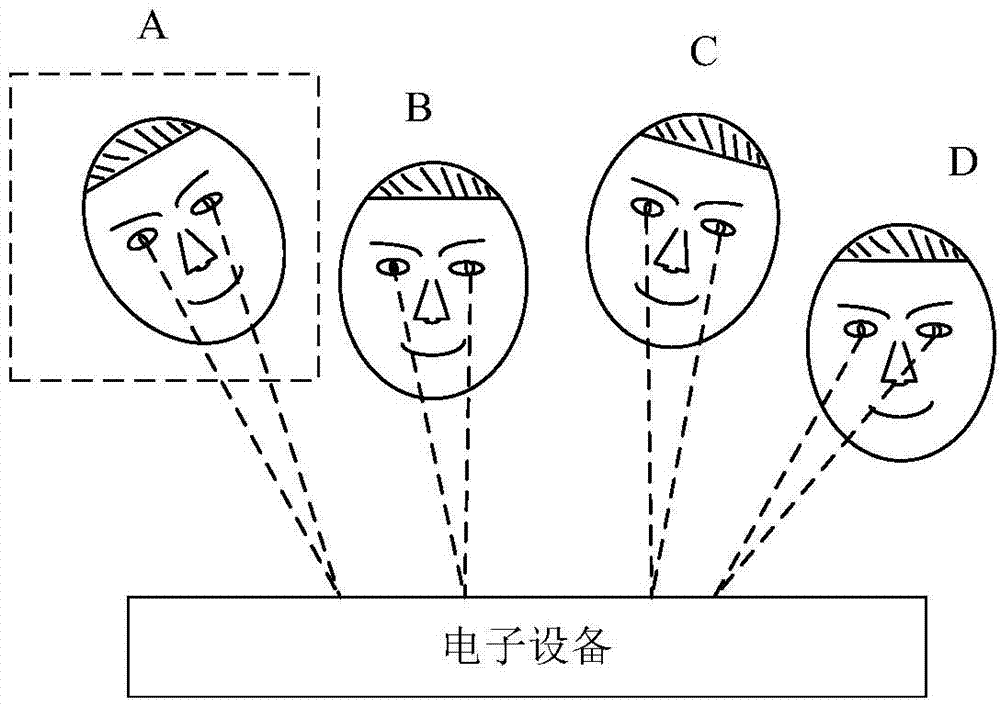
Target human face tracking method and electronic equipment
InactiveCN104732210ACorrect image processing effectCharacter and pattern recognitionImaging processingElectronic equipment
The invention relates to a target human face tracking method and electronic equipment. The target human face tracking method includes the steps that a current scene is shot, and then a scene image is obtained; based on the scene image, human faces in the current scene are recognized; when the number of the human faces is more than one, at least one target human face is selected from more than one human faces according to a target human face selection rule; the target human face is tracked. Through the electronic equipment and the target human face tracking method, the target human face can be selected from the scene having more than one human face according to requirements and can be tracked, so the pertinence and accuracy of image processing are improved.
Owner:SUPERD CO LTD
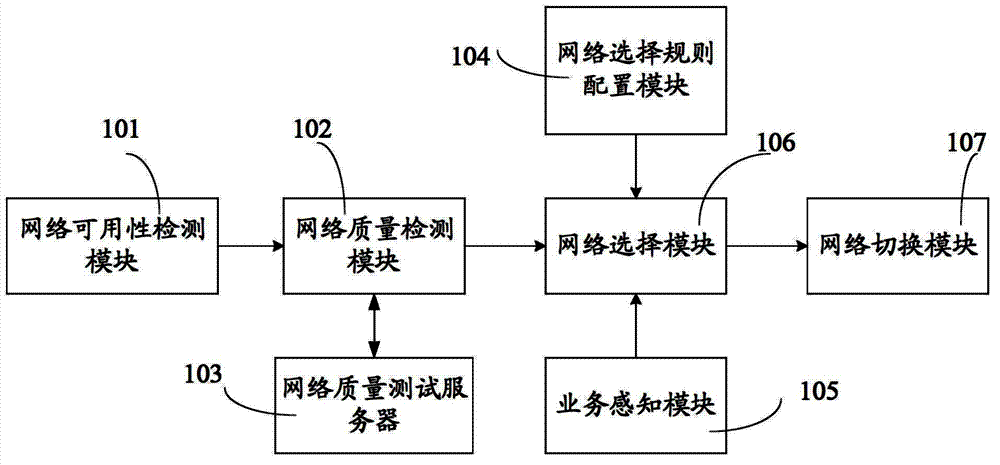
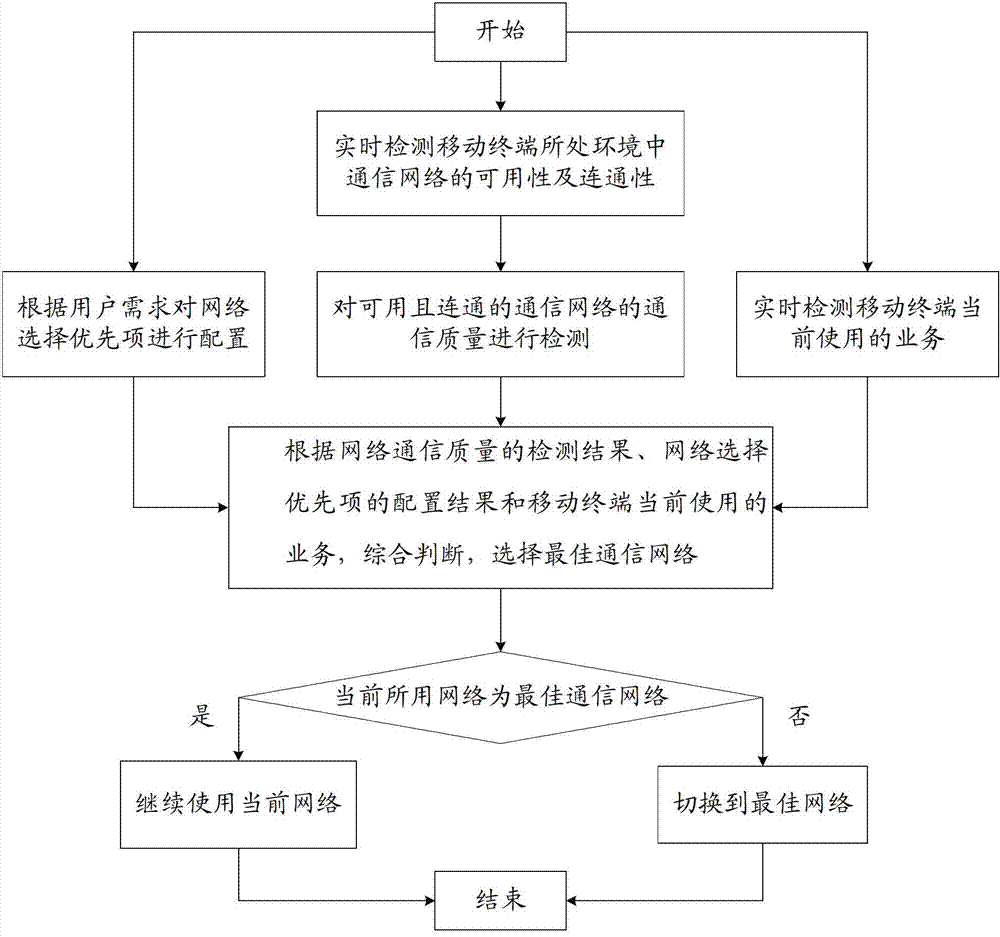
System and method of mobile terminal for selecting optimal communication network
InactiveCN103052144ATake advantage ofIncrease incomeAssess restrictionUser needsCommunication quality
The invention relates to a system and a method of a mobile terminal for selecting an optimal communication network. The system comprises a network availability detection module, a network quality detection module, a network quality test server, a network selection rule configuration module, a service perceiving module, a network selecting module and a network switching module, wherein the network availability detection module is used for detecting the network availability and connectivity of a communication network involving the mobile terminal in real time; the network quality detection module and the network quality test server are used for detecting the communication quality of an available and connected communication network; the network selection rule configuration module is used for configuring the network selection priority according to user demands; the service perceiving module is used for detecting the service currently used by the mobile terminal in real time; the network selecting module is used for selecting an optimal communication network according to the detection result of the network communication quality, the configuration result of the network selection priority and the service currently used by the mobile terminal; and the network switching module is used for switching the communication network currently used by the mobile terminal into the optimal communication network. According to the system and the method of the mobile terminal for selecting the optimal communication network, the demands on network quality, use expense and service requirements are comprehensively considered and users can make full use of the network and obtain the maximum profit on the premise of guaranteeing the communication quality.
Owner:北京思特奇信息技术股份有限公司
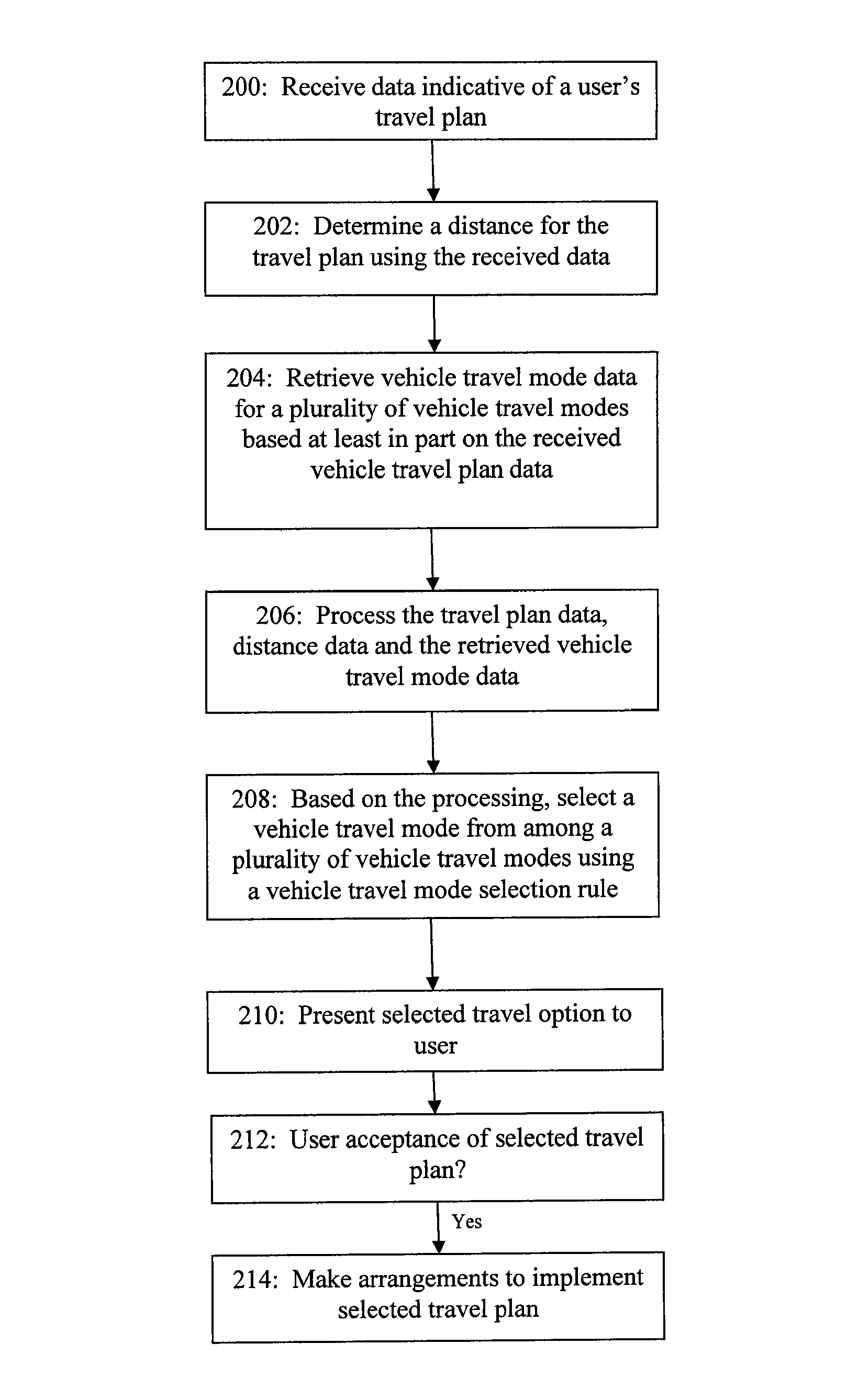
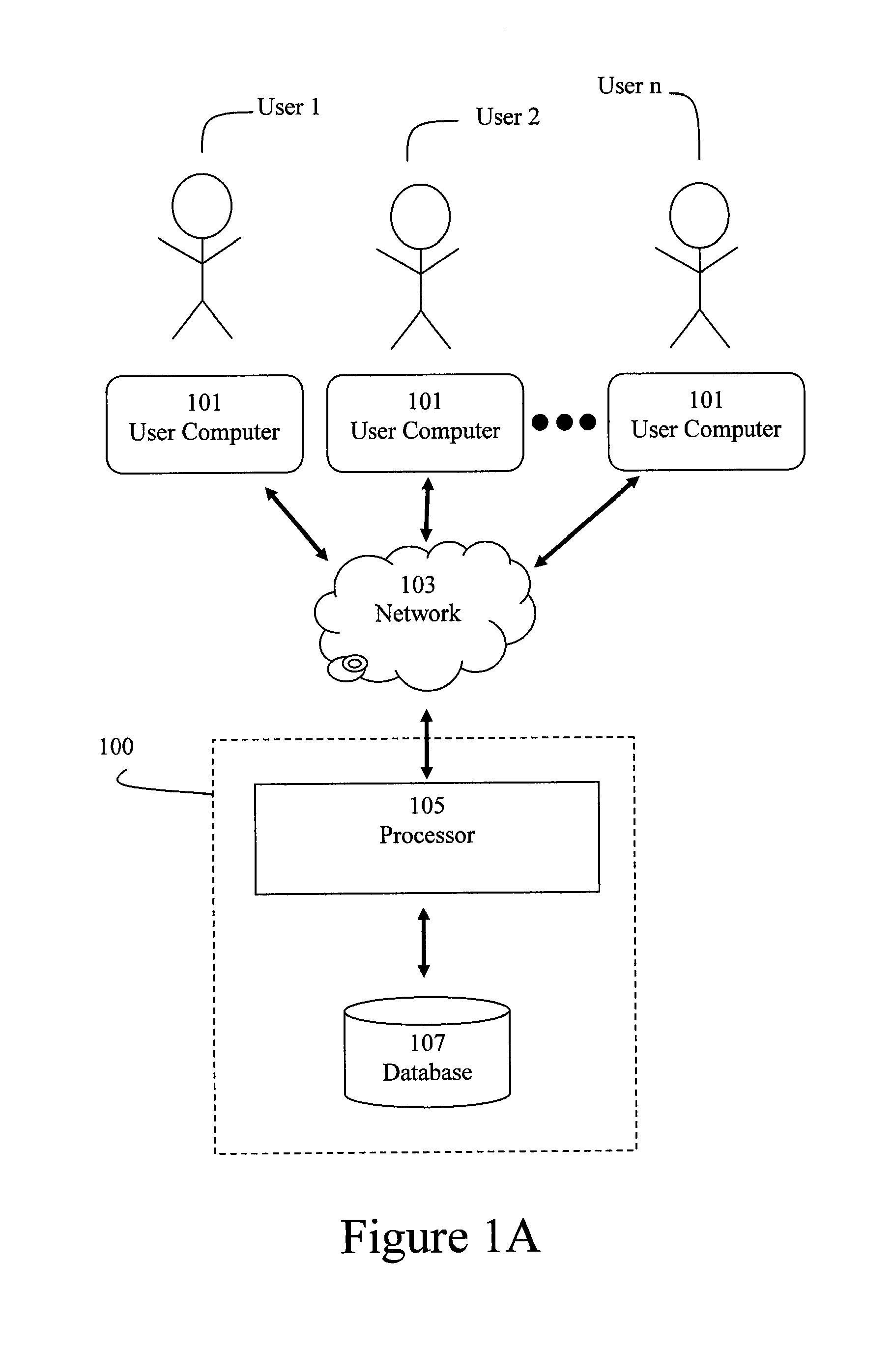
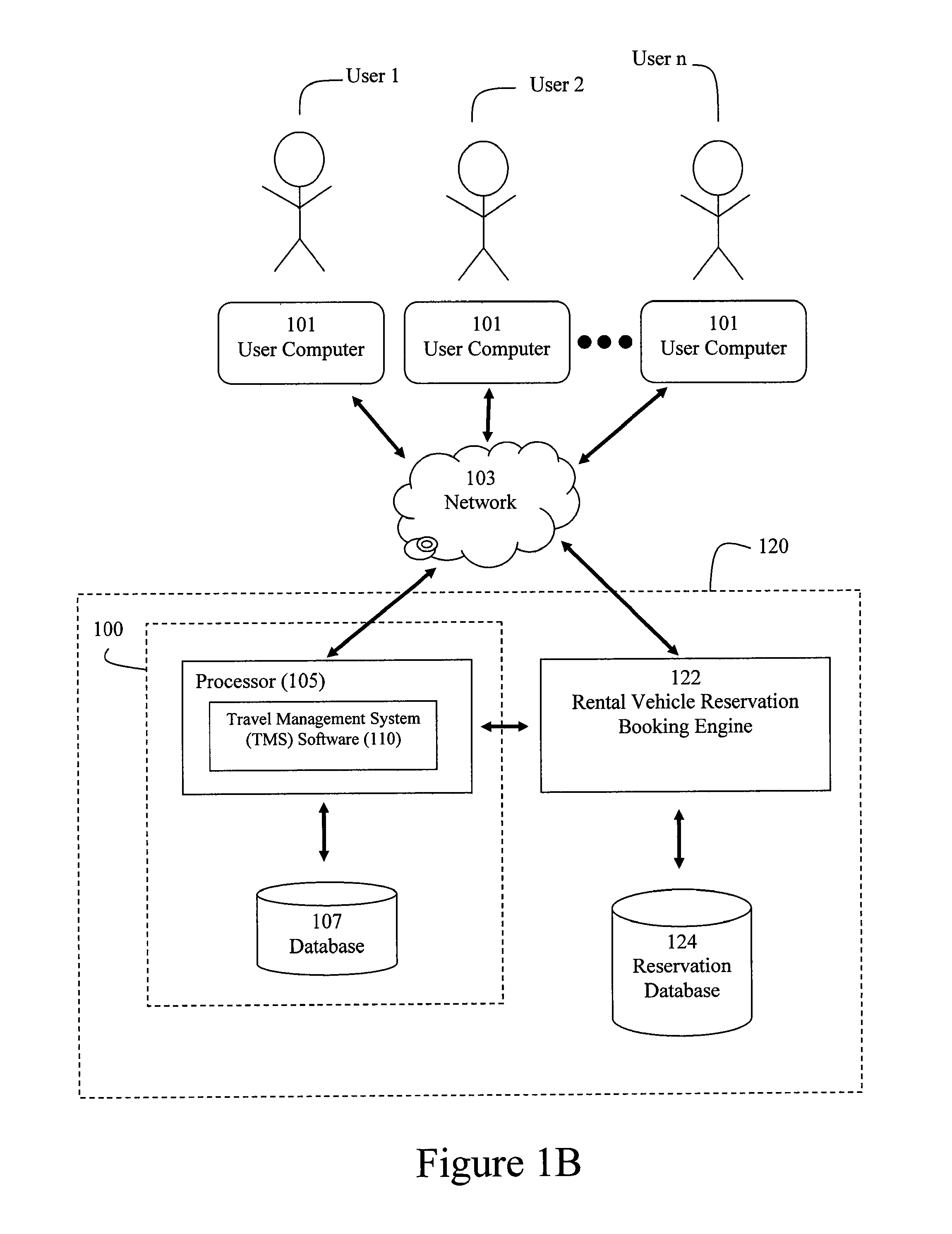
Method and system for managing vehicle travel
Methods and systems for facilitating efficient travel management are disclosed. Exemplary embodiments comprise a processor configured to make selections from among a plurality of vehicle travel modes based on a vehicle travel mode selection rule using, at least in part, received travel plan information. In a preferred embodiment, this selection can be based on any of a number of factors, including monetary costs and carbon emissions associated with different vehicle travel mode options.
Owner:THE CRAWFORD GROUP