Patents
Literature
97 results about "Weak correlation" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
A weak correlation means that as one variable increases or decreases, there is a lower likelihood of there being a relationship with the second variable. In a visualization with a weak correlation, the angle of the plotted point cloud is flatter. If the cloud is very flat or vertical, there is a weak correlation.
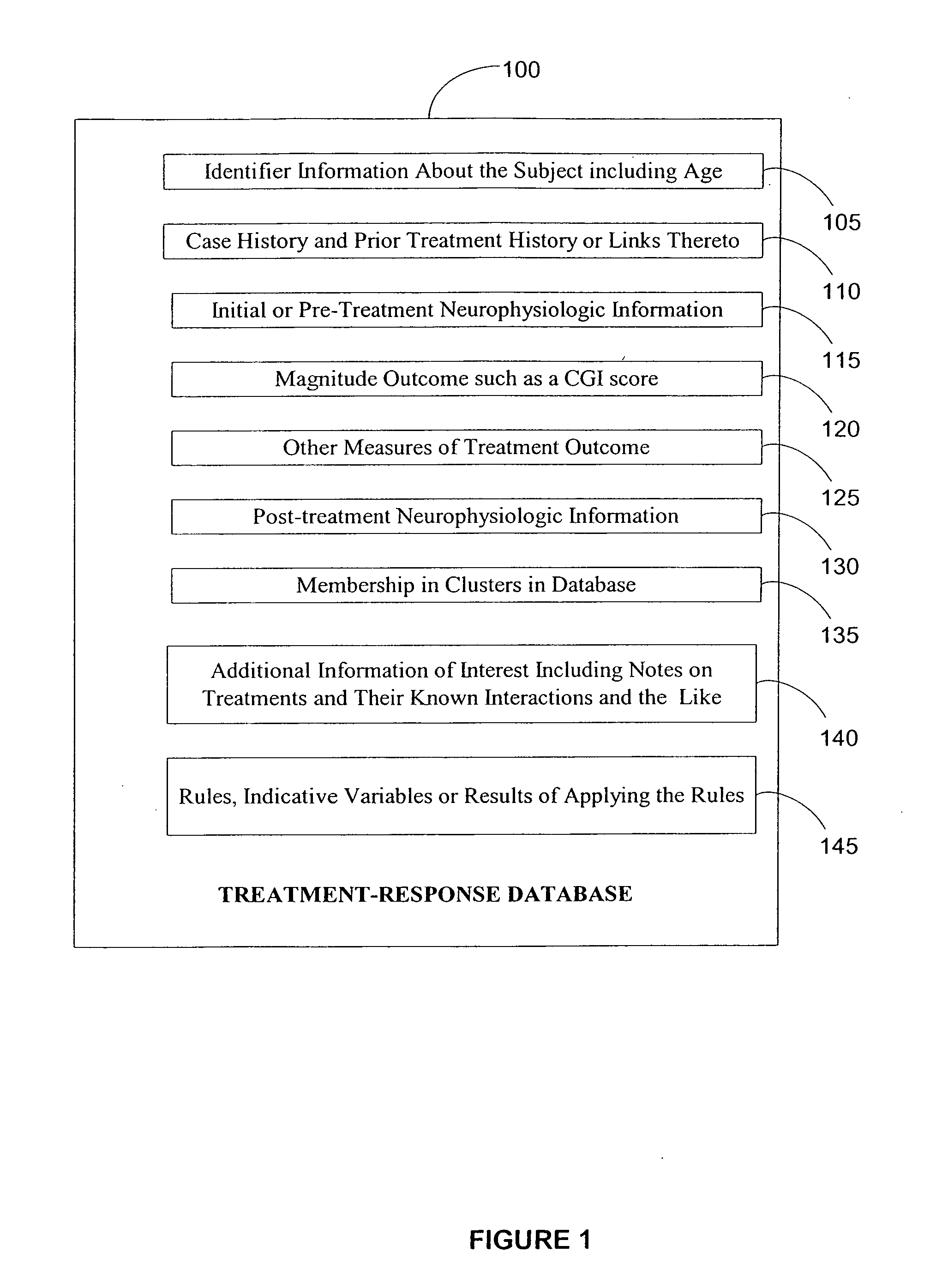
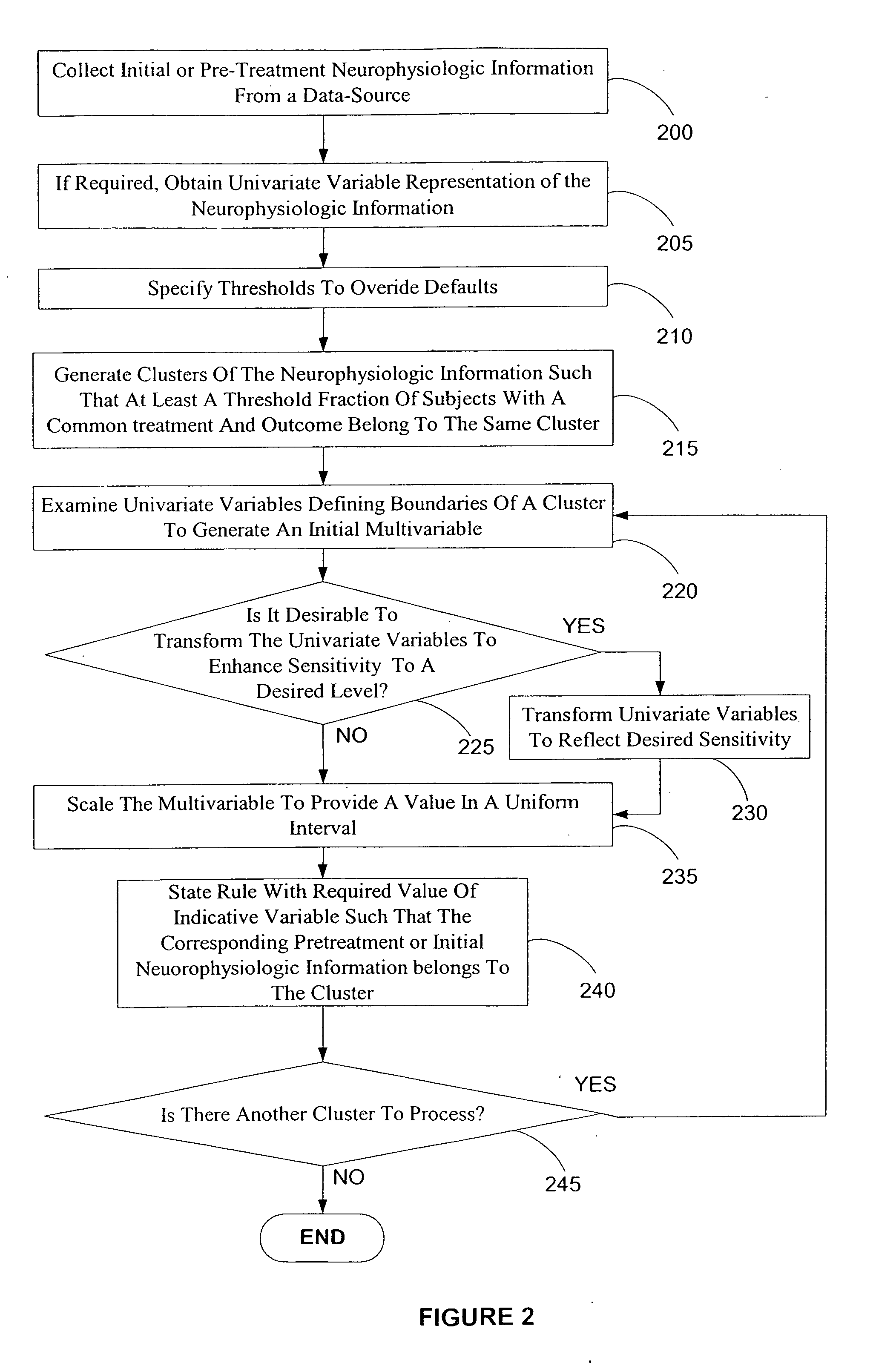
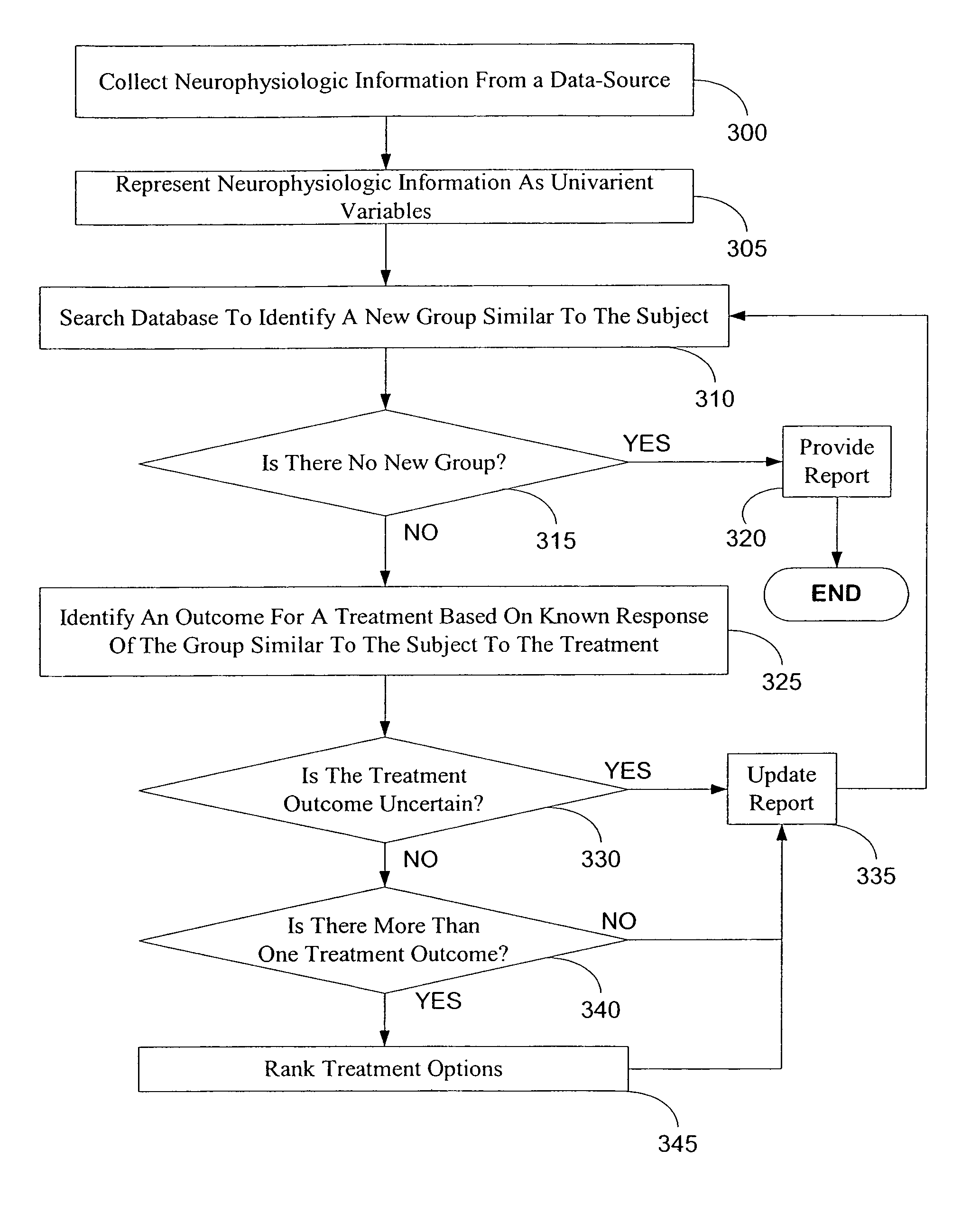
Electroencephalography based systems and methods for selecting therapies and predicting outcomes
InactiveUS7177675B2Quality improvementHigh-quality informationElectroencephalographyMedical data miningMode of actionClinical psychology
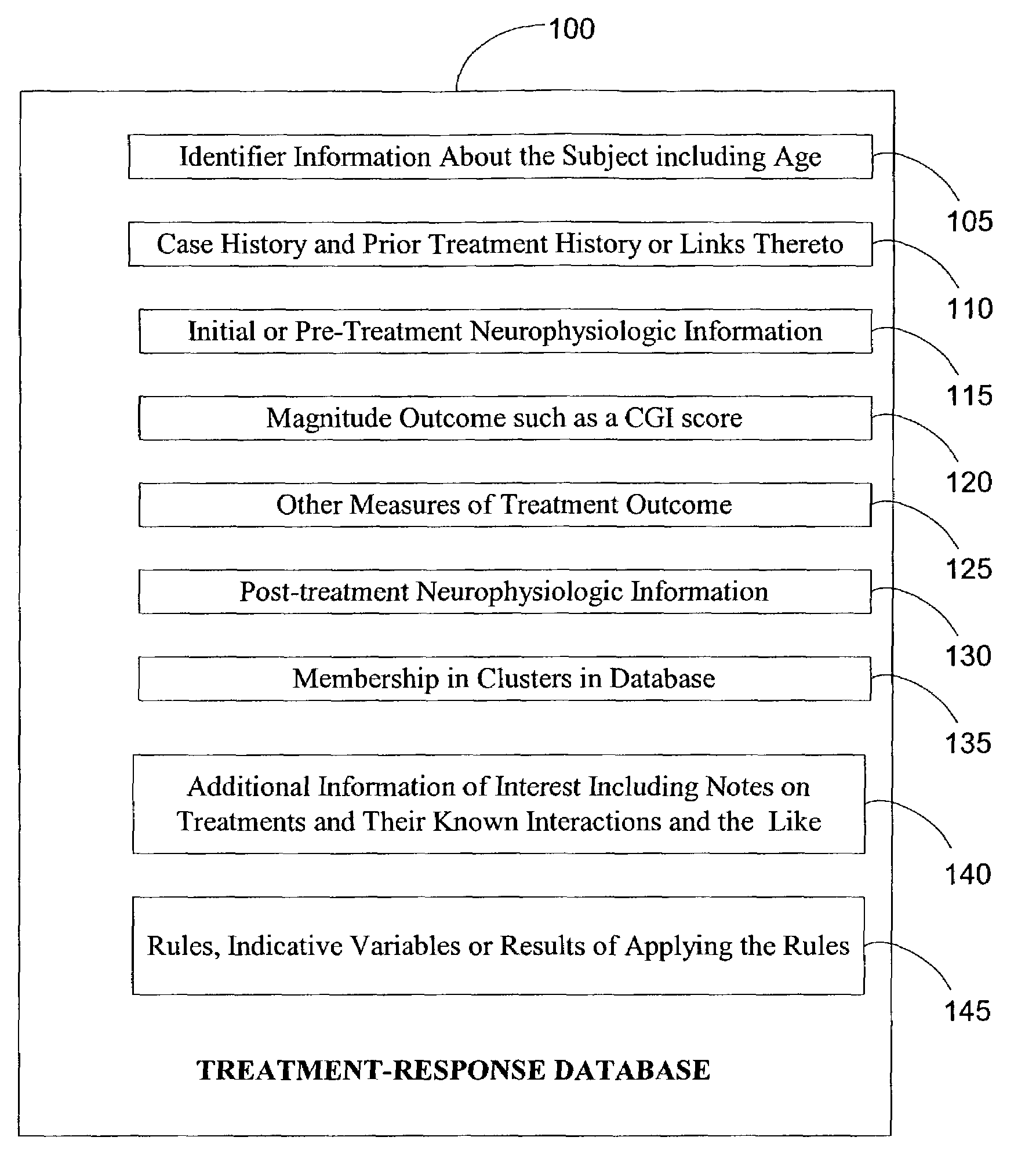
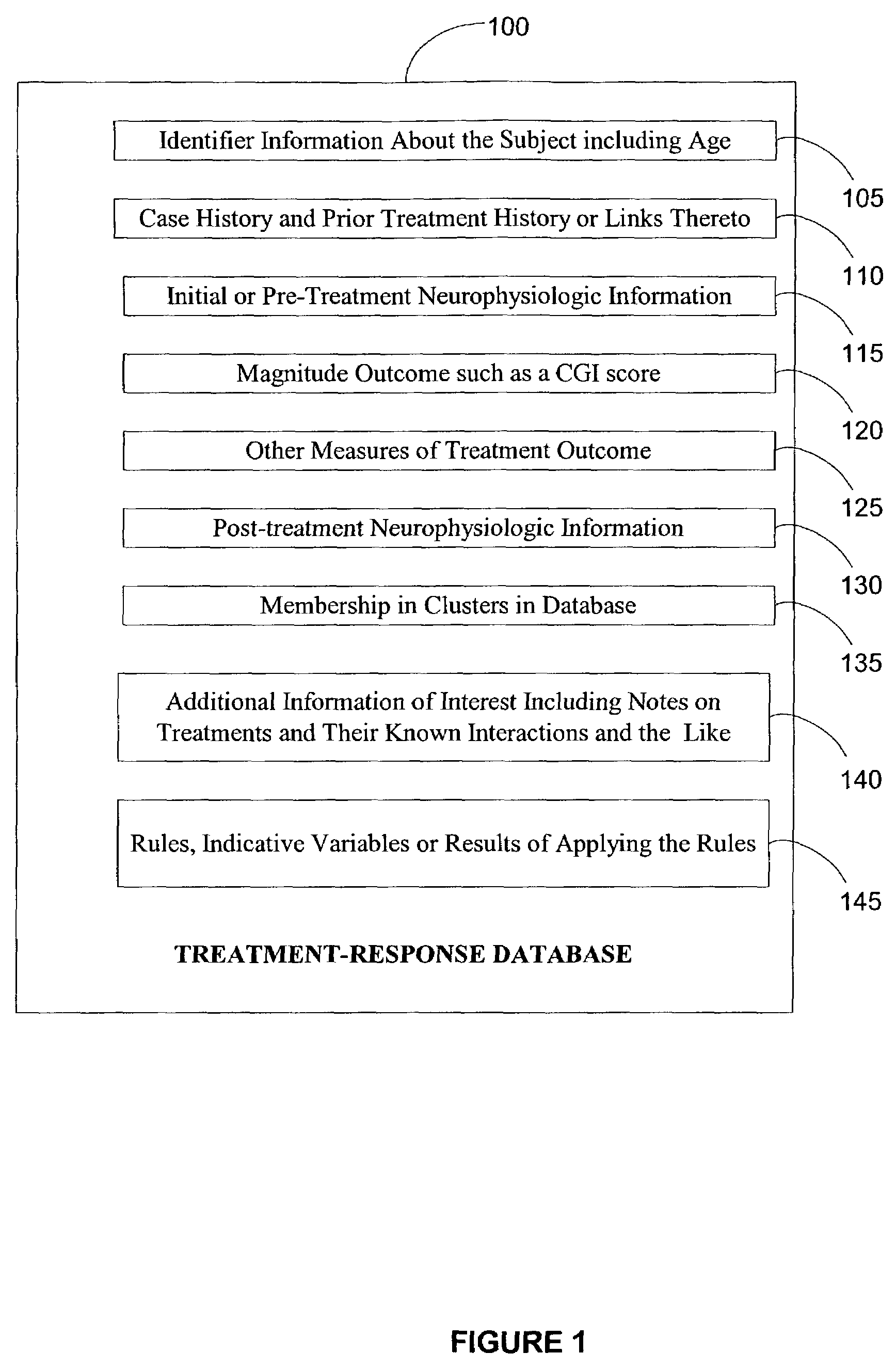
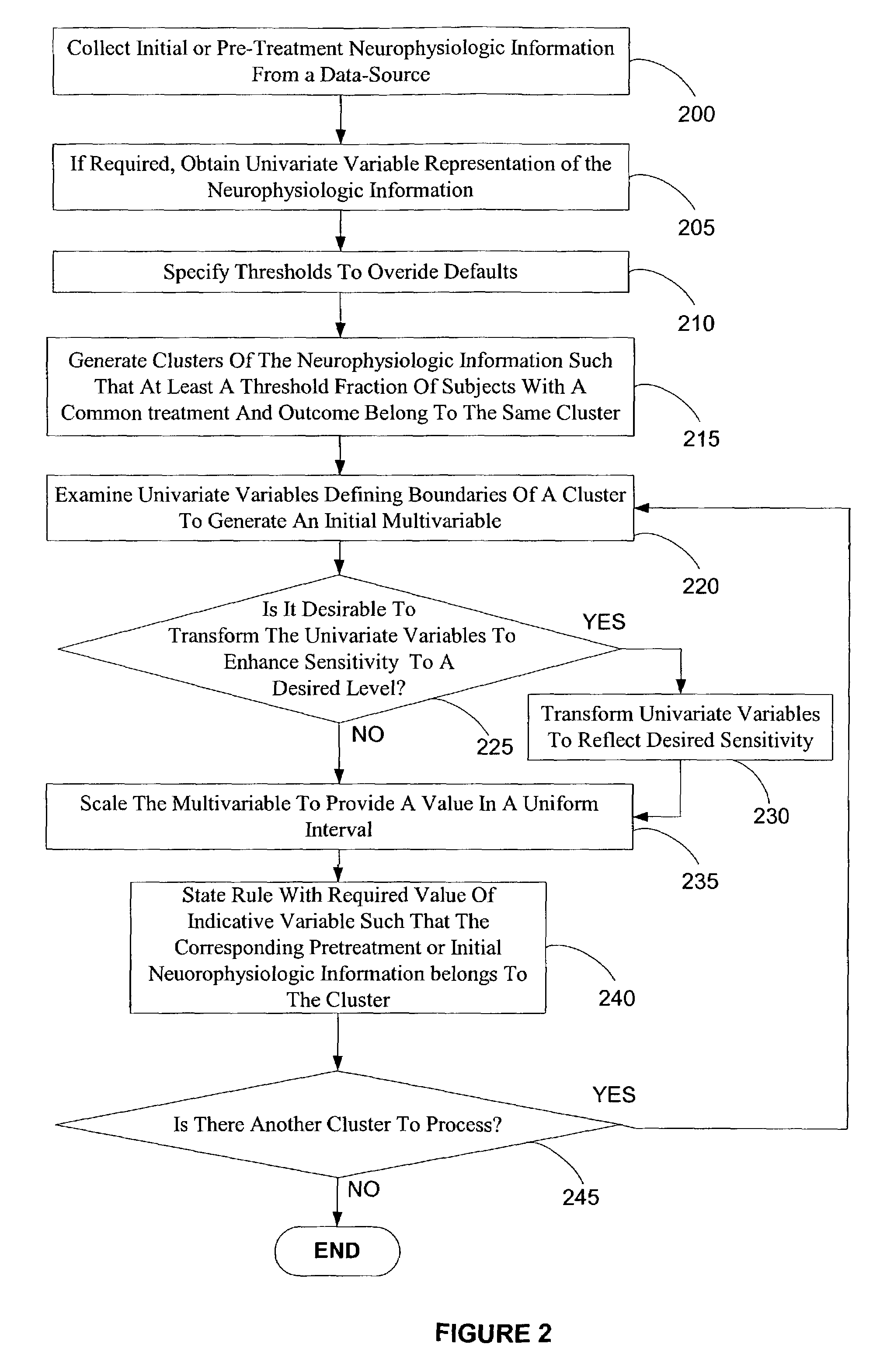
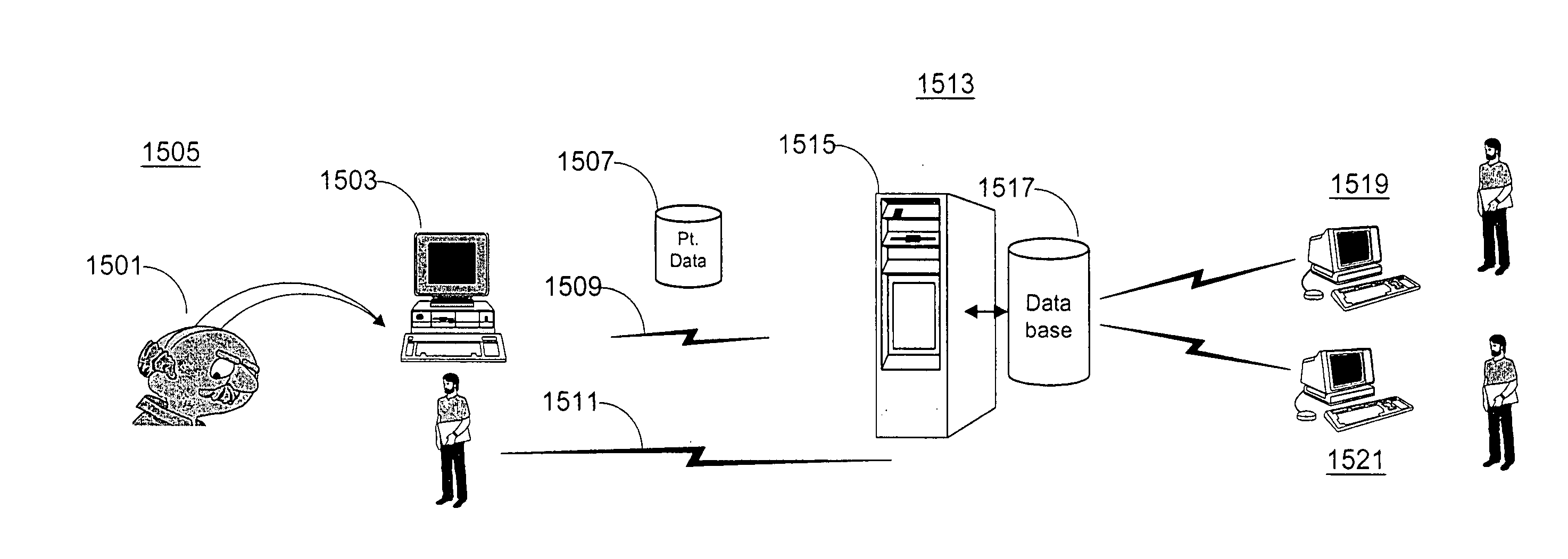
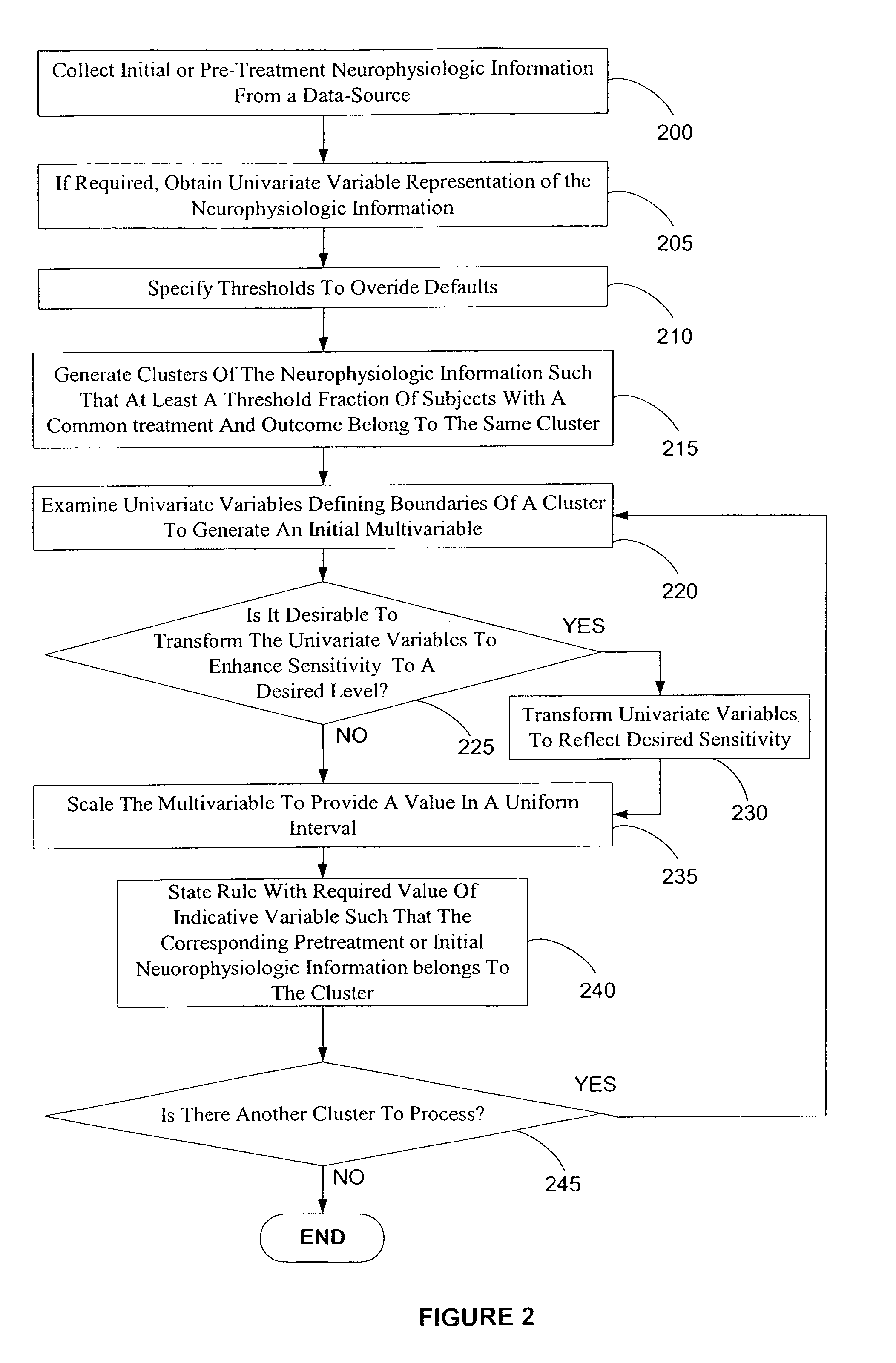
A method and system for utilizing neurophysiologic information obtained by techniques such as quantitative electroencephalography (QEEG), electrode recordings, MRI in appropriately matching patients with therapeutic entities is disclosed. The present invention enables utilization of neurophysiologic information, notwithstanding its weak correlation with extant diagnostic schemes for mental disorders, for safer and expeditious treatment for mental disorders, discovering new applications for therapeutic entities, improved testing of candidate therapeutic entities, inferring the presence or absence of a desirable response to a treatment, and deducing the mode of action of one or more therapeutic entities. In particular, methods for effectively comparing neurophysiologic information relative to a reference set are disclosed along with database-based tools for deducing therapeutic entity actions on particular patients such that these tools are readily accessible to remote users.
Owner:CNS RESPONSE
Electroencephalography based systems and methods for selecting therapies and predicting outcomes
InactiveUS20080125669A1Reduction in experimentationSimple designElectroencephalographyMedical data miningMode of actionClinical psychology
Owner:CNS RESPONSE
Electroencephalography based systems and methods for selecting therapies and predicting outcomes
InactiveUS7489964B2Reduction in experimentationSimple designElectroencephalographyMedical data miningMode of actionClinical psychology
A method and system for utilizing neurophysiologic information obtained by techniques such as quantitative electroencephalography (QEEG), electrode recordings, MRI in appropriately matching patients with therapeutic entities is disclosed. The present invention enables utilization of neurophysiologic information, notwithstanding its weak correlation with extant diagnostic schemes for mental disorders, for safer and expeditious treatment for mental disorders, discovering new applications for therapeutic entities, improved testing of candidate therapeutic entities, inferring the presence or absence of a desirable response to a treatment, and deducing the mode of action of one or more therapeutic entities. In particular, methods for effectively comparing neurophysiologic information relative to a reference set are disclosed along with database-based tools for deducing therapeutic entity actions on particular patients such that these tools are readily accessible to remote users.
Owner:CNS RESPONSE
True random number generator
InactiveCN101515228AImprove design efficiencySimple structureRandom number generatorsNumber seriesData signal
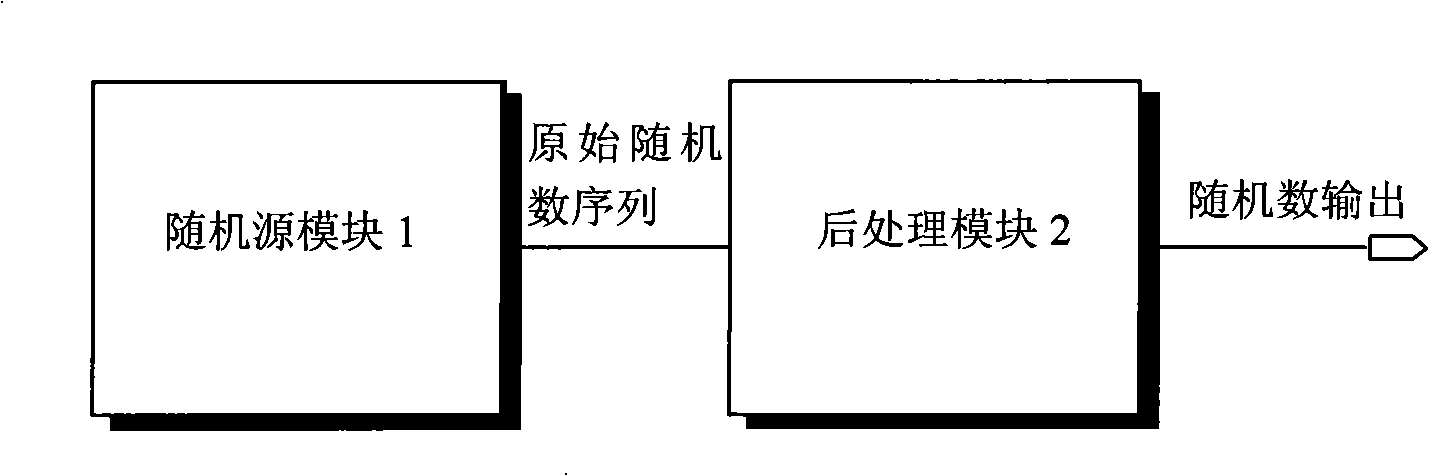
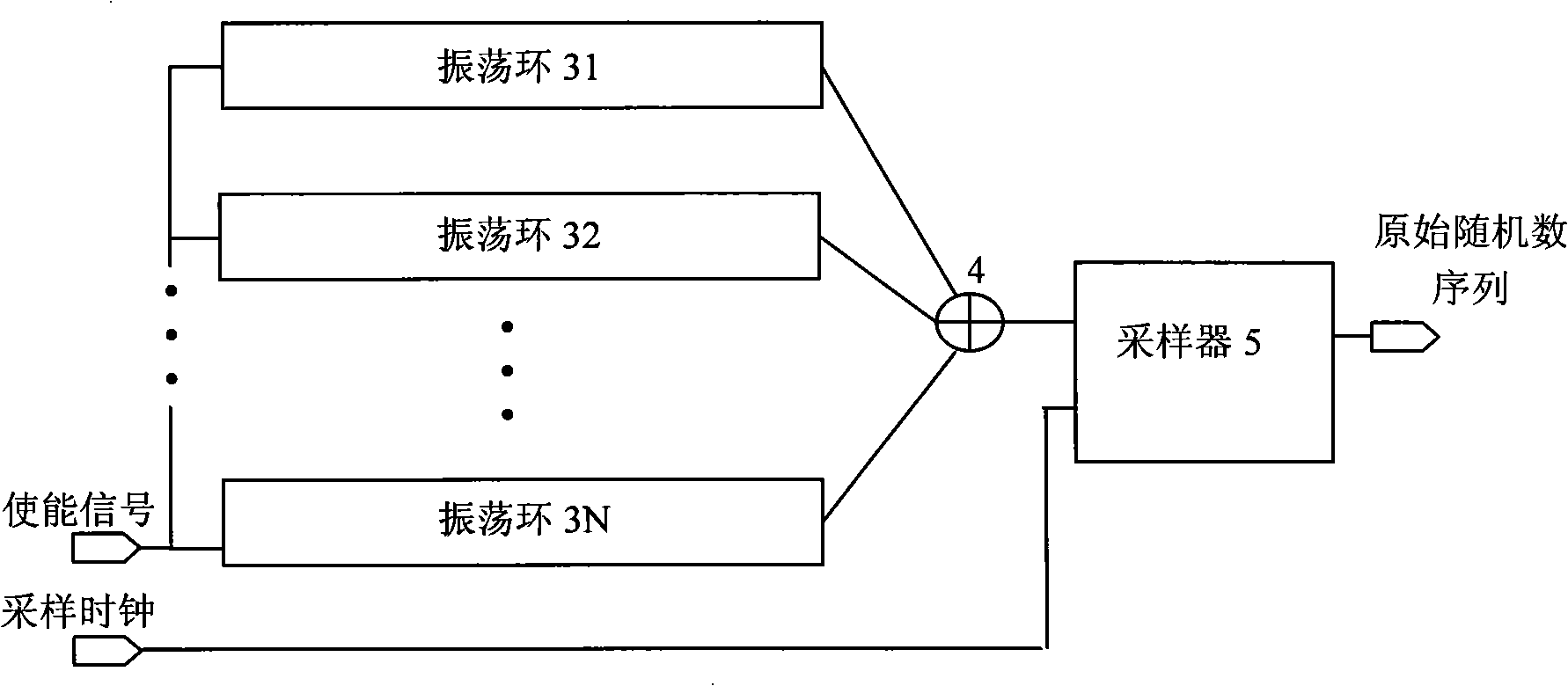
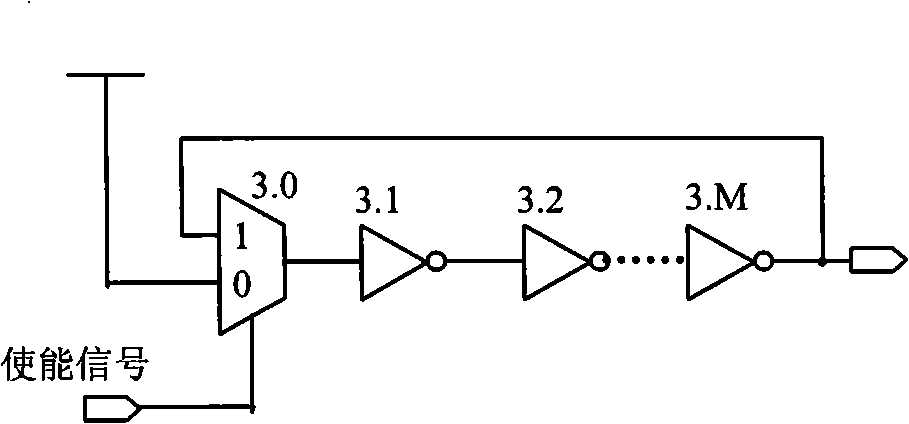
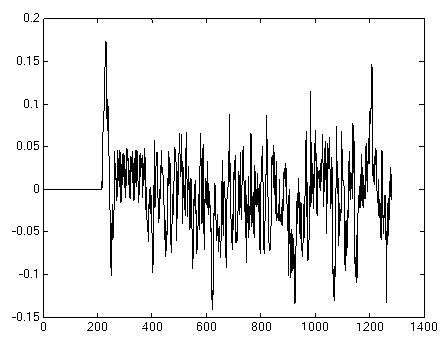
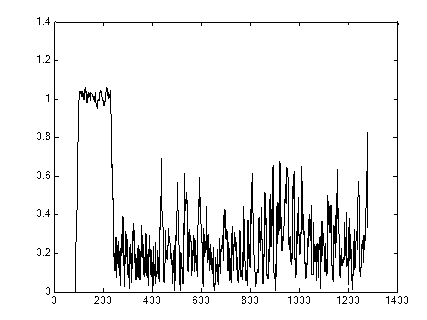
The invention discloses a true random number generator, comprising a stochastic source module and a post-processing module. The stochastic source module is used for generating digital signals having random characteristics and providing the digital signals for the post-processing module; the post-processing module carries out post-processing for the digital signals by using a loop code error-correcting method, thereby eliminating bias of data signals to obtain random number series. The stochastic source module can be composed of a plurality of sets of inverter oscillating rings, and the post-processing module is realized by a linear feedback shift register (LFSR). The TRNG (True Random Number Generator) has simple structure and only general digital logic devices are used, so the true random number generator has good technology weak correlation and can be rapidly transplanted in an integrated circuit design flow after prototype verification is carried out, thereby improving the efficiency of module design and reducing the development risk.
Owner:HUAZHONG UNIV OF SCI & TECH
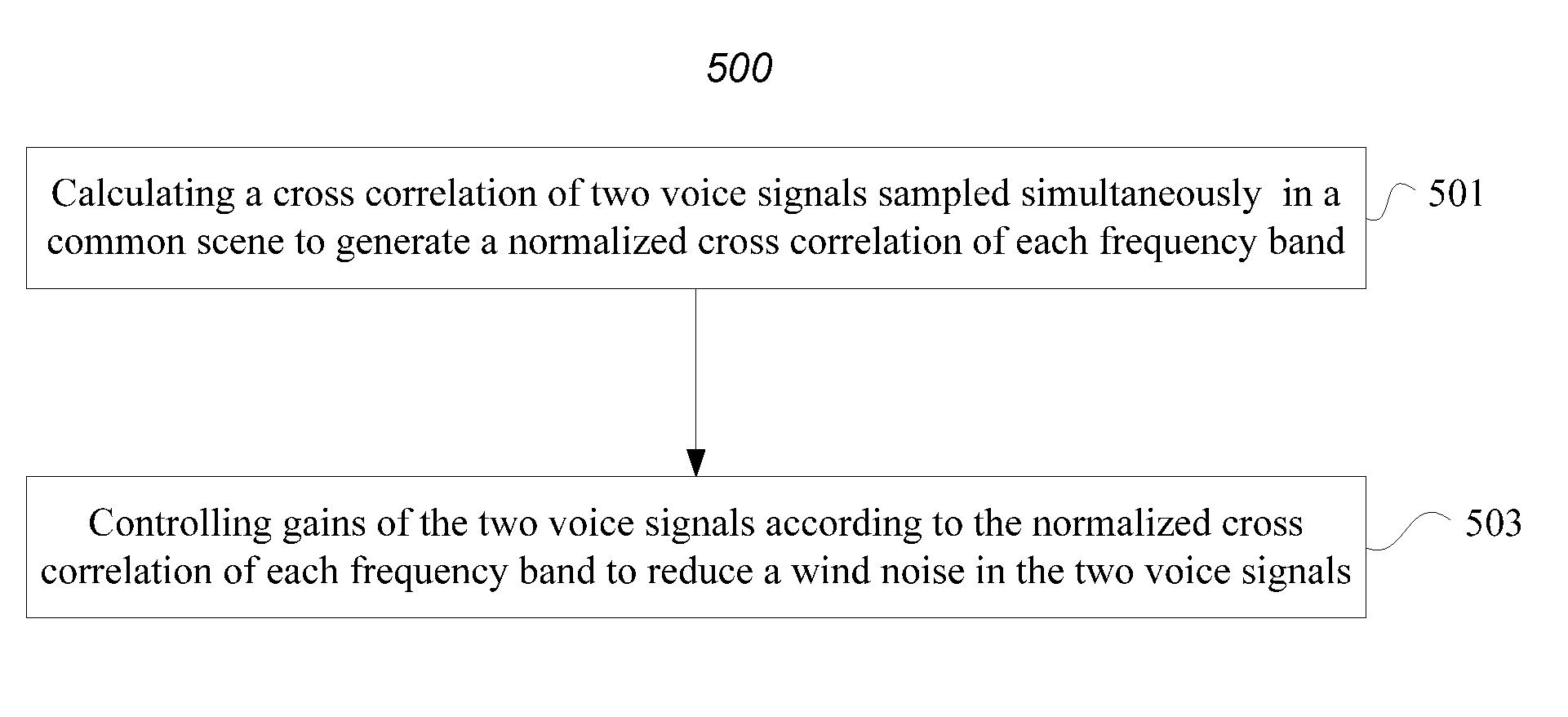
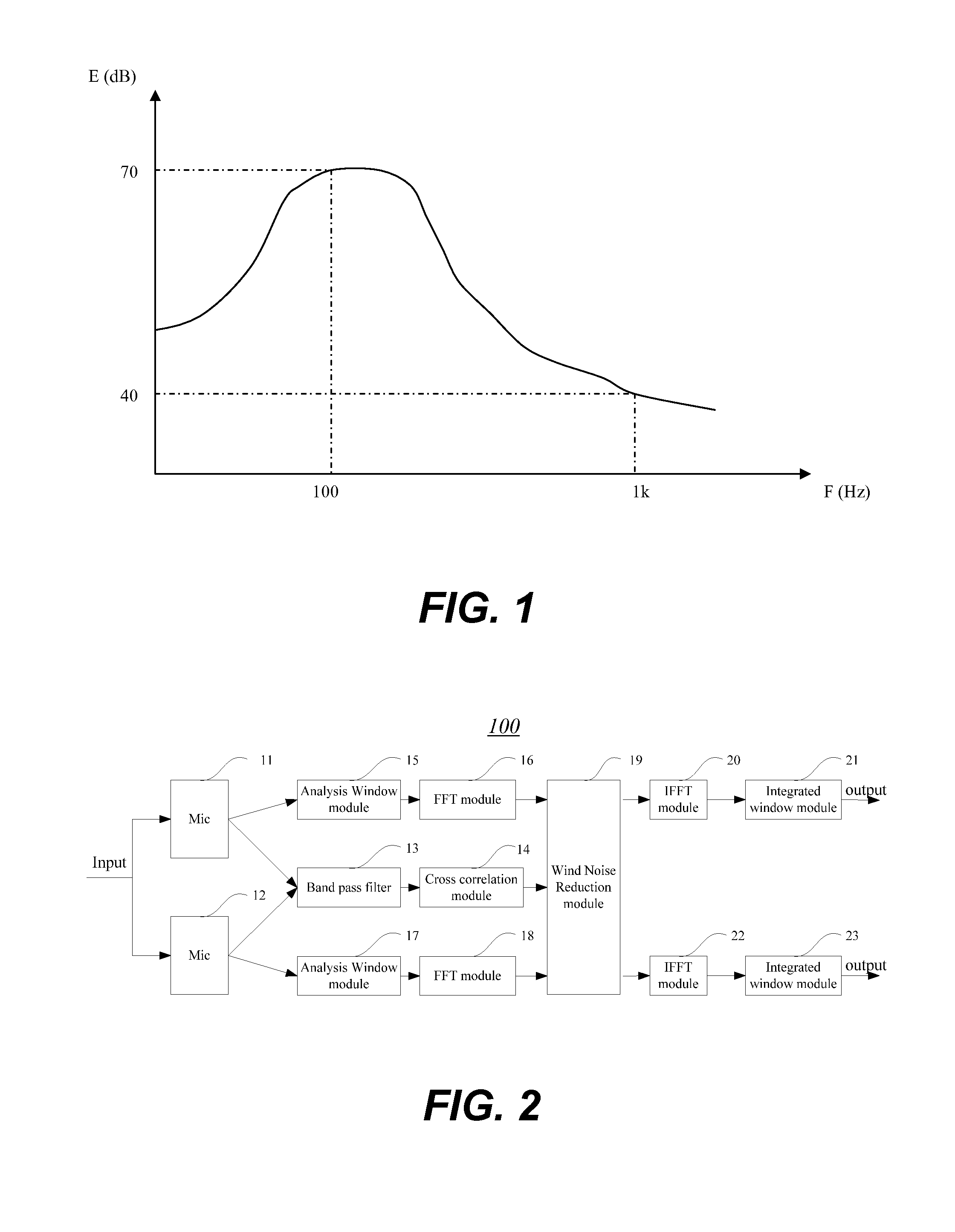
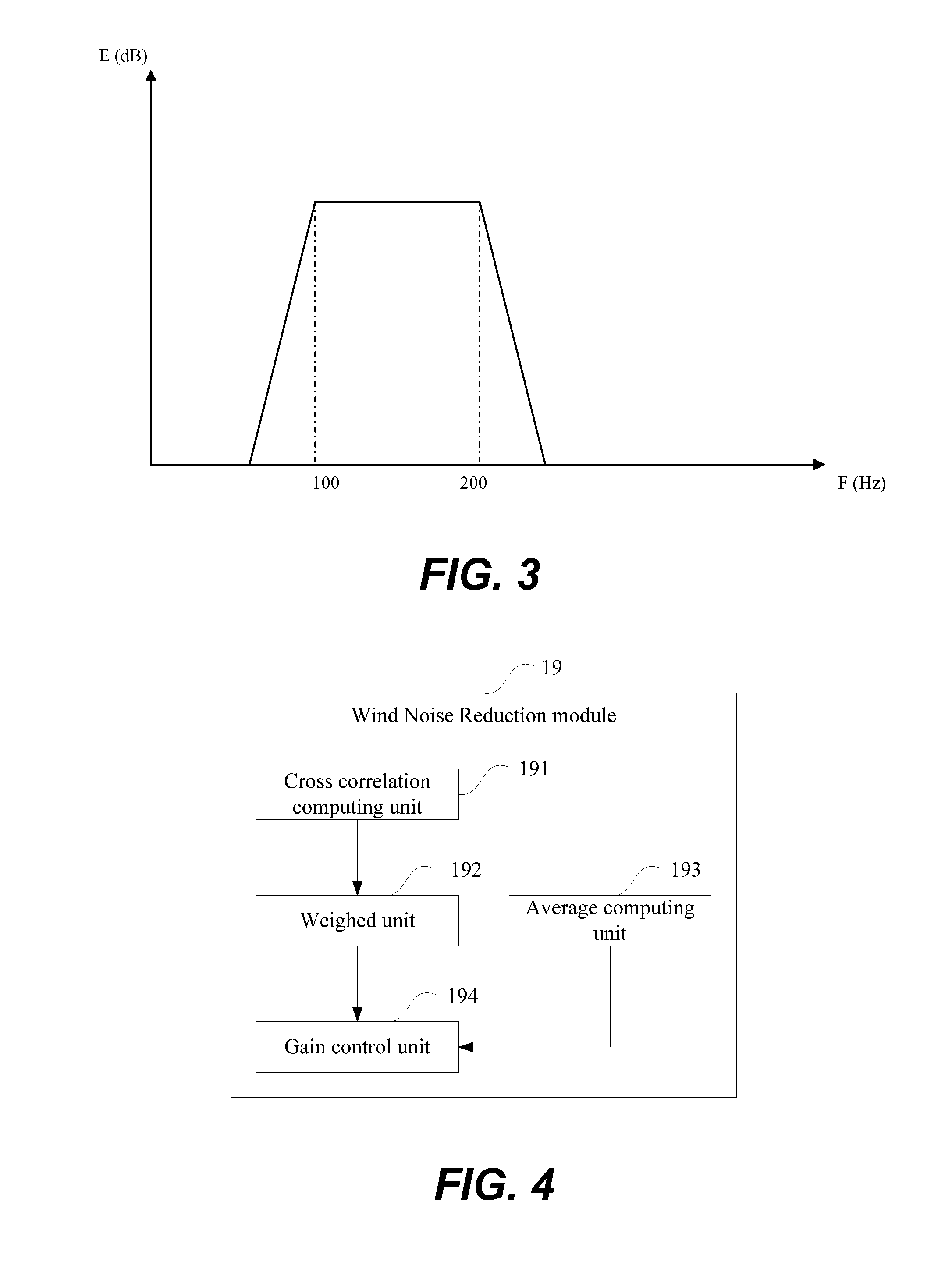
Method and apparatus for reducing wind noise
InactiveUS20100158269A1Reduce wind noiseMinimal impactSignal processing for reducing noiseSpeech analysisComputer scienceSpeech sound
Techniques pertaining to techniques to reduce wind noises effectively in recorded signals are disclosed. According to one aspect of the present invention, there is a strong correlation between two voice signals from target voices in the same frequency band sampled simultaneously by a pair of microphones in a common scene while there is a weak correlation between wind noises in the same frequency band of the two voice signals sampled simultaneously by the pair of microphones in the common scene. Taking advantage of this feature to provide a larger gain to the frequency band having a strong correlation and a smaller gain to the frequency band having a weak correlation, thereby the wind noise is reduced efficiently with minimum impact on the target voices.
Owner:VIMICRO CORP
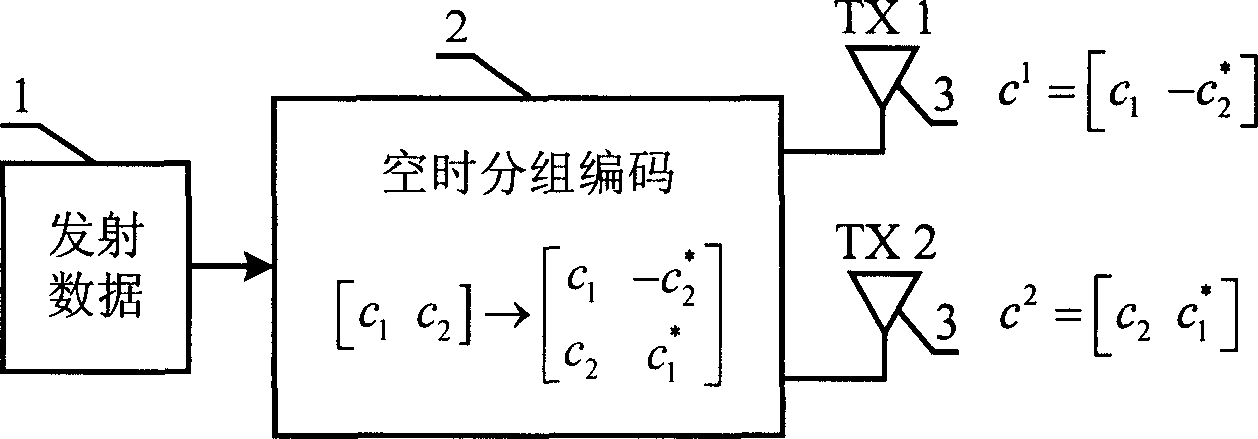
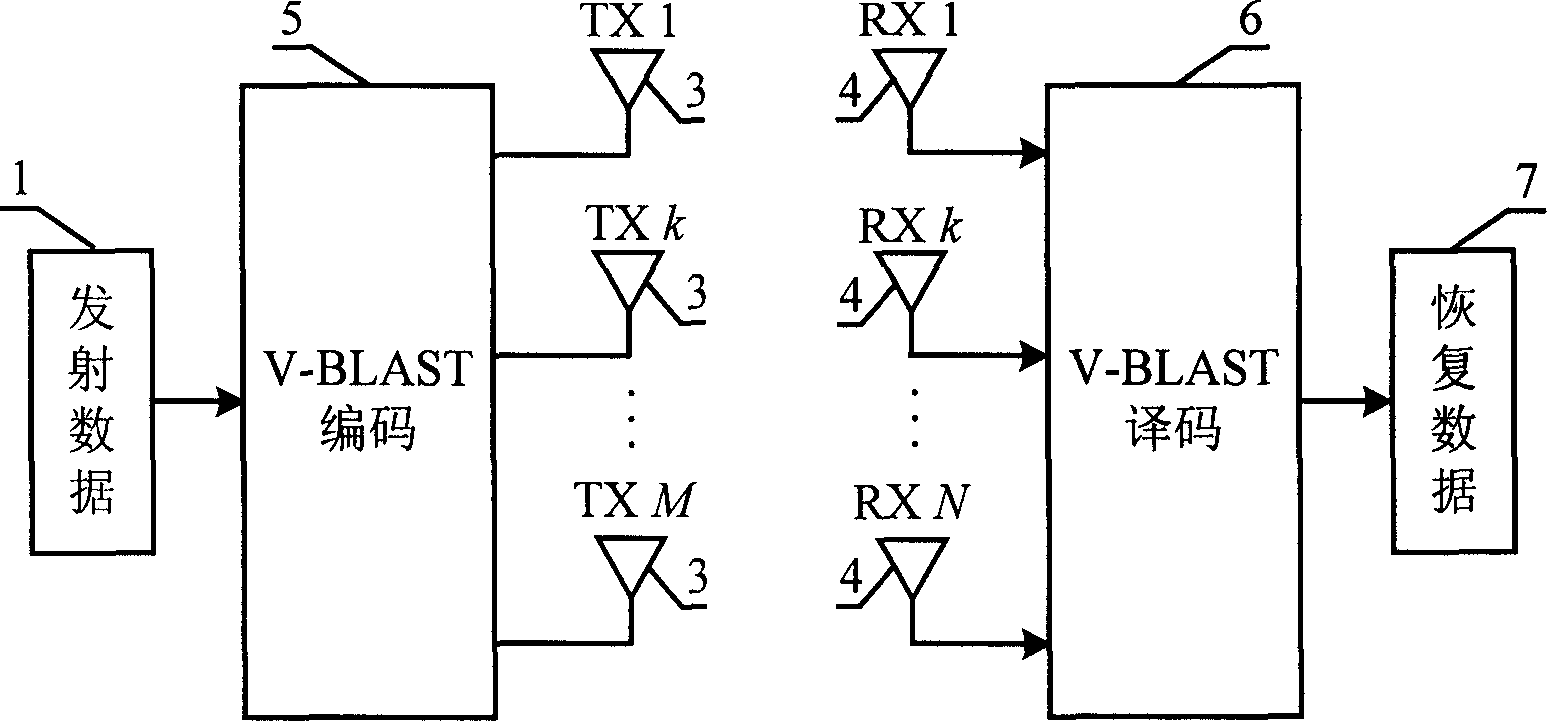
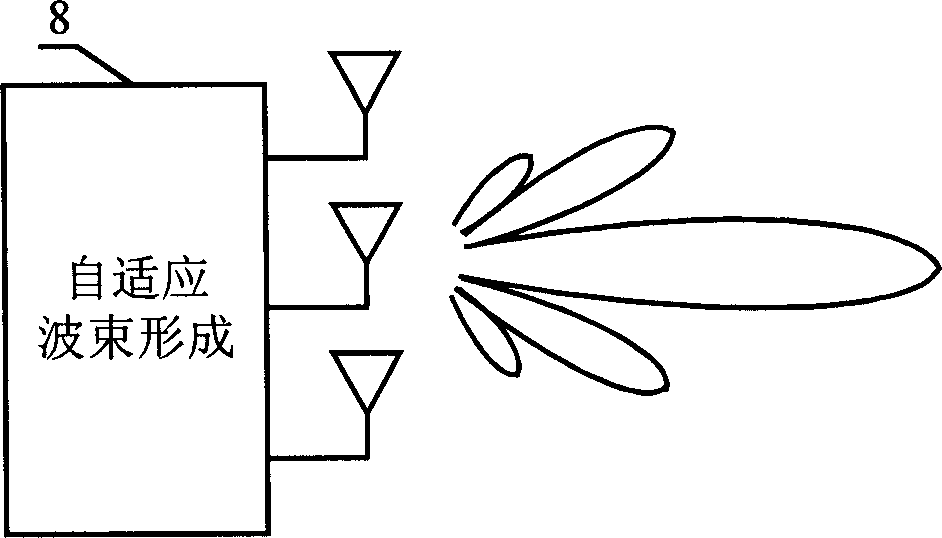
Self-adaptive adjustment multi-antenna communication method and communication system according to channel space correlation
InactiveCN1731701AIncrease transfer rateImprove communication qualitySpatial transmit diversityControl signalTransmitter
Disclosed is a communication system and multi antenna communication method of signal channel space correlation self-adapting adjustment. The communication method comprises: sending control signal, detecting channel status information; selecting communication initial transmission scheme; business information transmission; monitoring channel change and switching transmission schemes during communication and coordinating communication clients. The inventive communication system comprises: transmitter for controlling signal information and receiver, business information transmitter and receiver. The invention is characterized in that it exploits intelligent antenna scheme in strong correlation for channel space and exploits V-BLAST scheme in weak correlation for keeping higher transmission ratio and good communication quality.
Owner:UNIV OF ELECTRONICS SCI & TECH OF CHINA
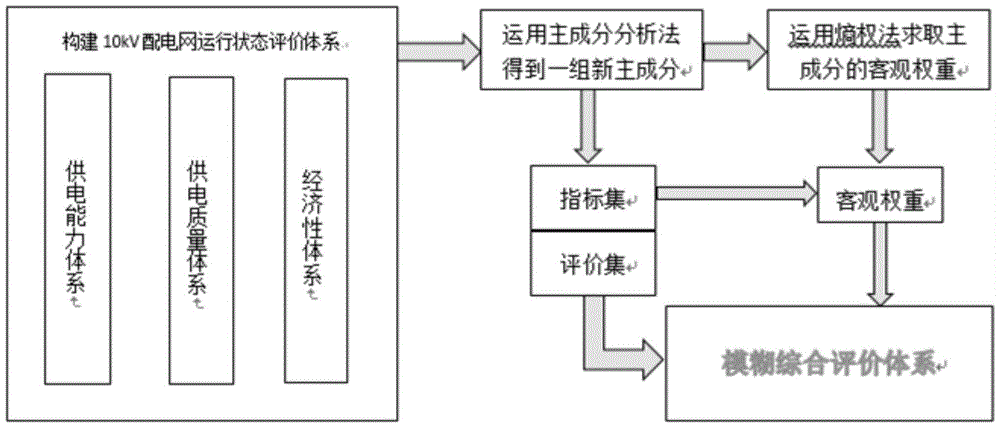
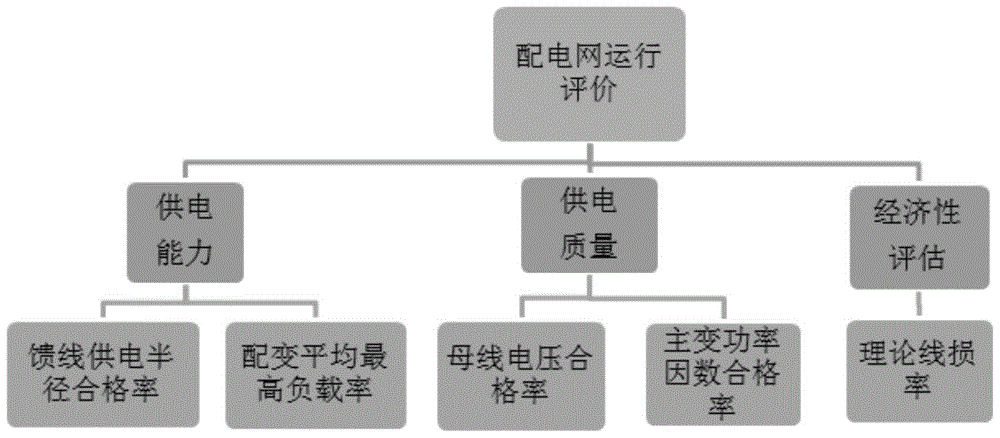
Intermediate-voltage distribution operation state fuzzy integrated evaluation method based on principle component analysis method and entropy weight method
InactiveCN105719048AConsider relevanceTake ambiguity into accountResourcesEntropy weight methodPrincipal component analysis
The invention discloses an intermediate-voltage distribution operation state fuzzy integrated evaluation method based on a principle component analysis method and an entropy weight method. Major information in source data can be reserved by use of the principle component analysis method, a power supply capability, power supply quality and economic indexes are taken as the source data representing an operation state of a distribution network, through solving a feature value and a feature vector of a correlation coefficient matrix, principle components of operation of the distribution network are determined, and an evaluation system with weak correlation yet large envelope information content is formed. Given fuzziness existing in index evaluation, new evaluation indexes are objectively endowed with weights by use of the entropy weight method in the system, and a fuzzy integrated evaluation system of a 10kV distribution network operation mode is finally formed. According to the invention, the fuzziness of the evaluation indexes is taken into consideration, qualitative analysis and quantitative determination are realized, and the method provided by the invention is reasonable and scientific to a certain degree.
Owner:SHANGHAI MUNICIPAL ELECTRIC POWER CO +1
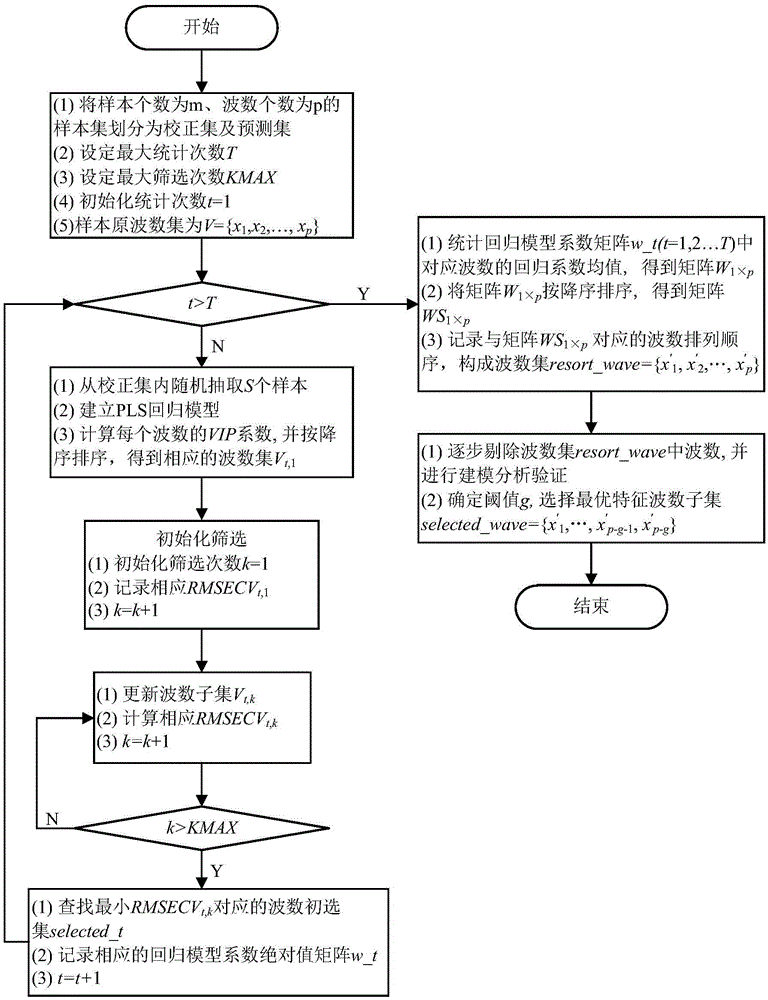
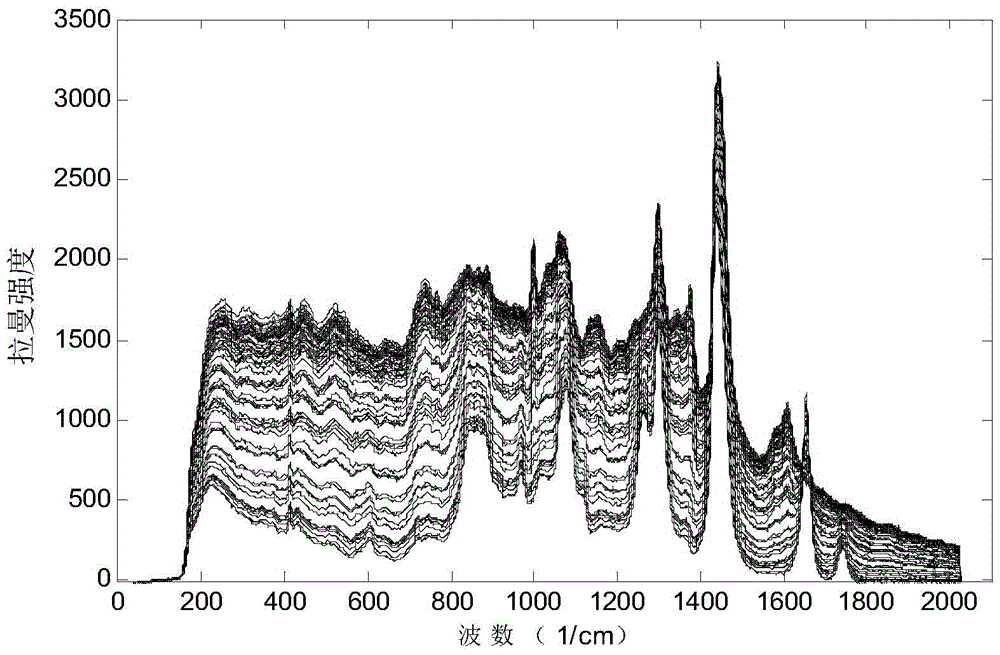
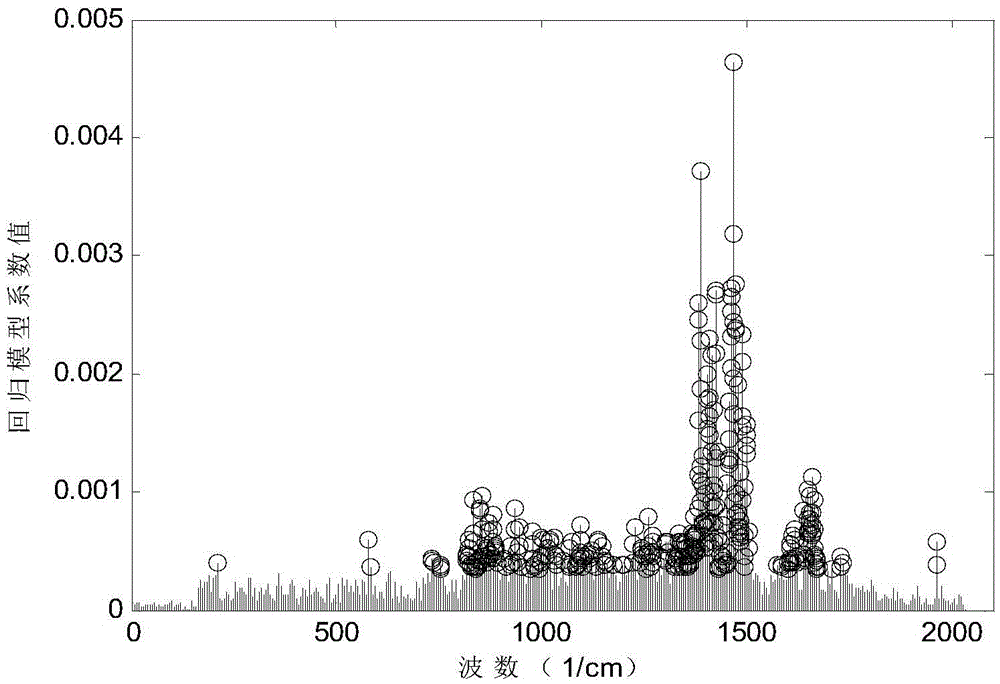
Spectrum wave number selection method
ActiveCN105630743AExclude subjective factorsImprove robustnessColor/spectral properties measurementsComplex mathematical operationsRe sequencingStatistical physics
The invention discloses a spectrum wave number selection method. Correction samples are randomly sampled many times according to wave numbers of spectra, a partial least square regression model is built, a variable projection importance coefficient of each wave number is calculated, the variable projection importance coefficients are sequenced in a descending mode, wave number sets corresponding to the distribution sequence are obtained, the re-sequenced wave number sets are subjected to wave number screening step by step, a result of each time of wave number selection is calculated, and a wave number primary selection set is obtained; then, absolute values of a partial least square regression coefficient of each wave number in the wave number primary selection sets is counted and correspondingly processed, the processed partial least square regression coefficients are sequenced in a descending mode, a corresponding wave number distribution sequence is recorded, then a strategy for reversely eliminating wake-correlation wave numbers is adopted, and the optimal feature wave number set is obtained. The method can fully mine effective information in wave numbers, effectively solves the subjectivity problem of wave number selection, extracts feature wave numbers to the largest extent, eliminates influences of weak correlation factors, and remarkably improves robustness and precision of the model.
Owner:ZHEJIANG UNIV
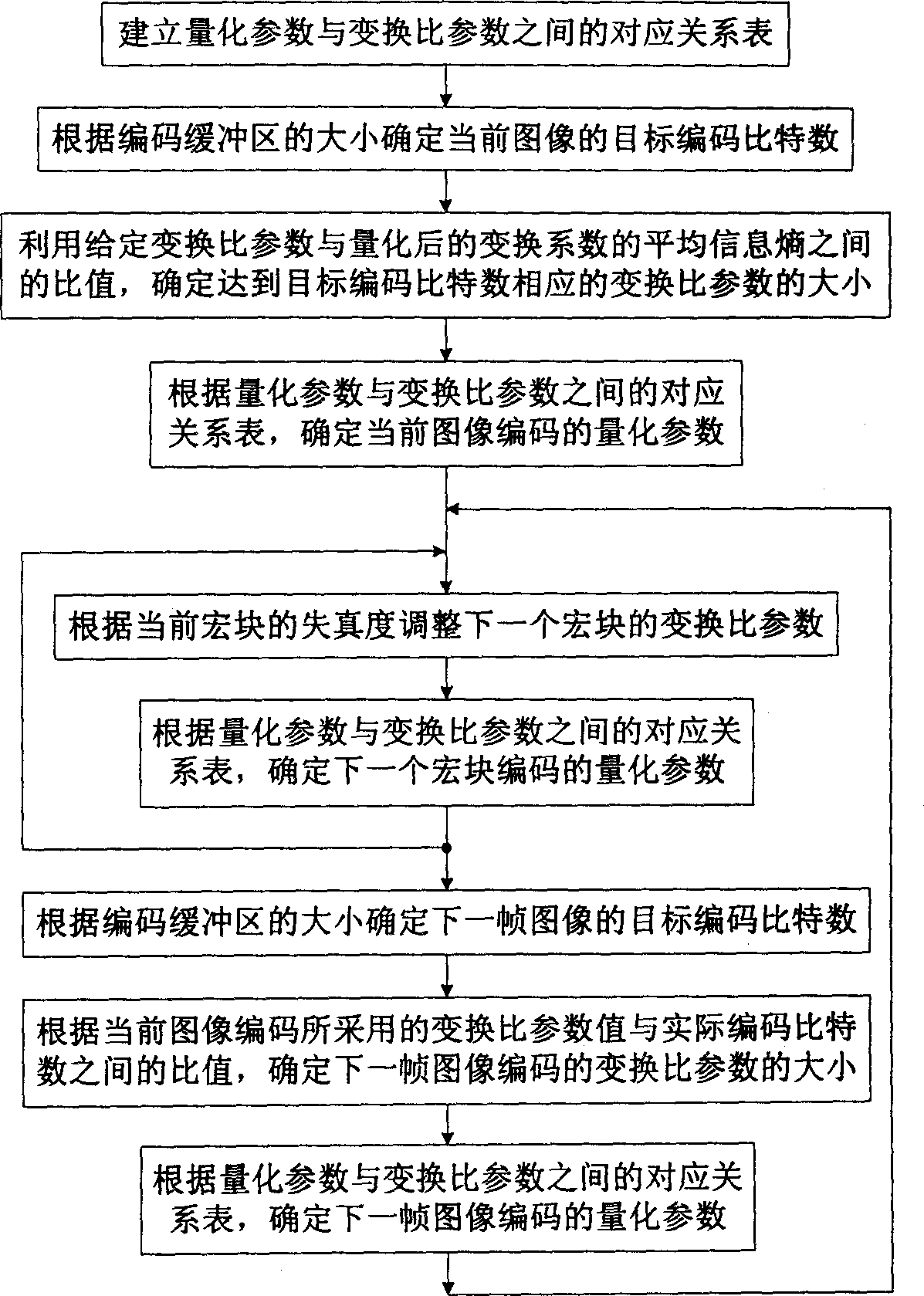
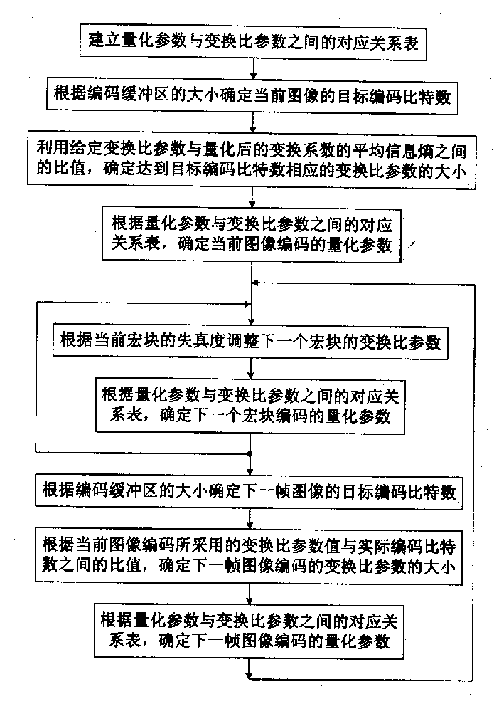
Method for controlling video coding bit rate
InactiveCN1434638AEncoding bitrate control is fastAccurate encoding bit rate controlPulse modulation television signal transmissionCode conversionVideo encodingLinear relationship
This invention discloses a video code bit rate control method in which quick and accurate predict of the code bit rate can be realized by the good linear relationship between code bit number and transformation ratio parameter, good information source weak correlation between code distortion and the transformation ratio paremter, the target code bit number can be determined, according to the predict and the code buffer, then code quqntification parameter is adjusted according to the relationship between the transformation rate and the quantification parameters to control the code bit rate. Thecode parameter is adjusted according to code macro-block distortion.
Owner:HUAZHONG UNIV OF SCI & TECH
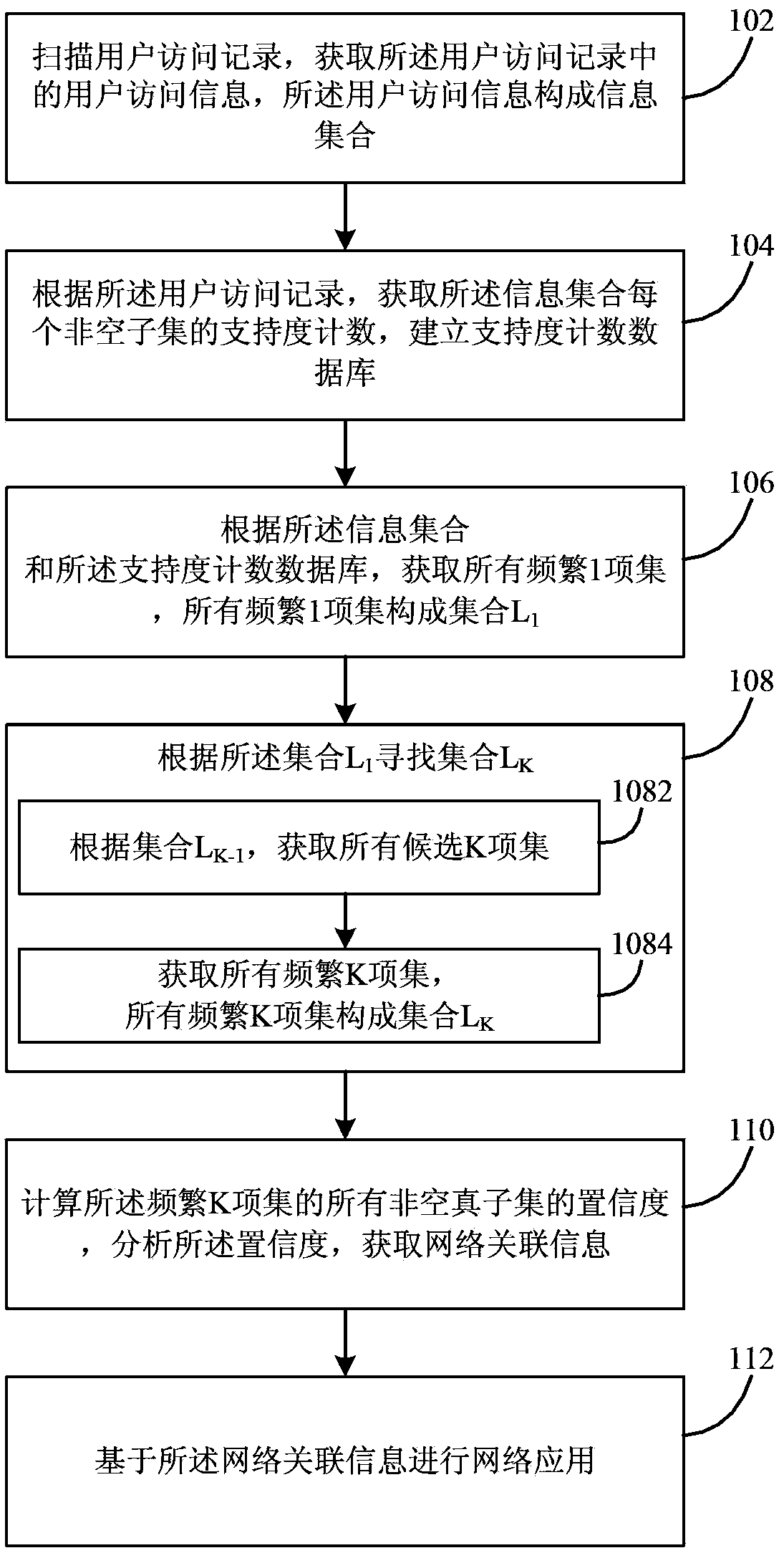
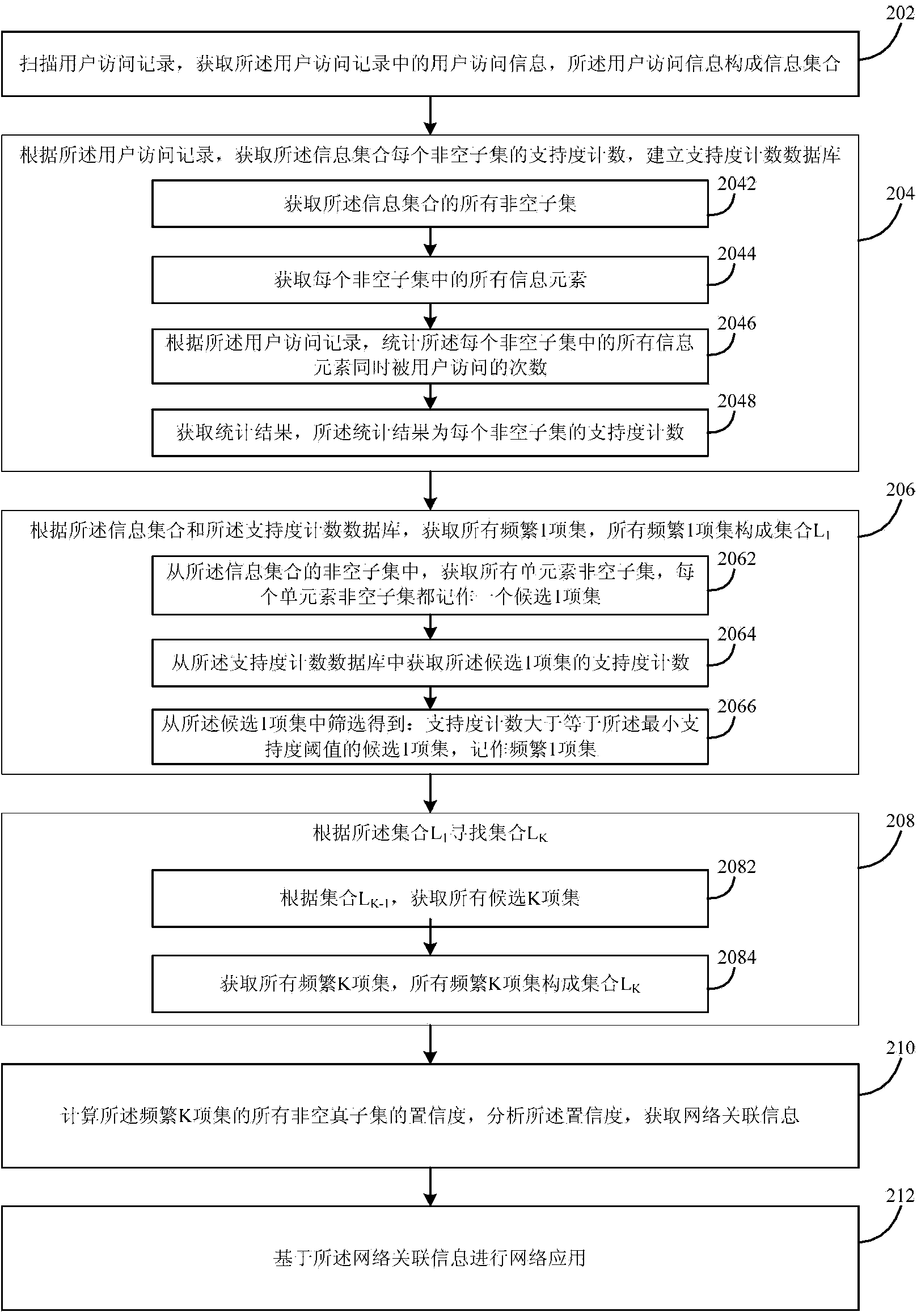
Gateway correlation information obtaining method and system
InactiveCN103514267AStrong correlationAccurately reflectWeb data indexingSpecial data processing applicationsData miningInformation acquisition
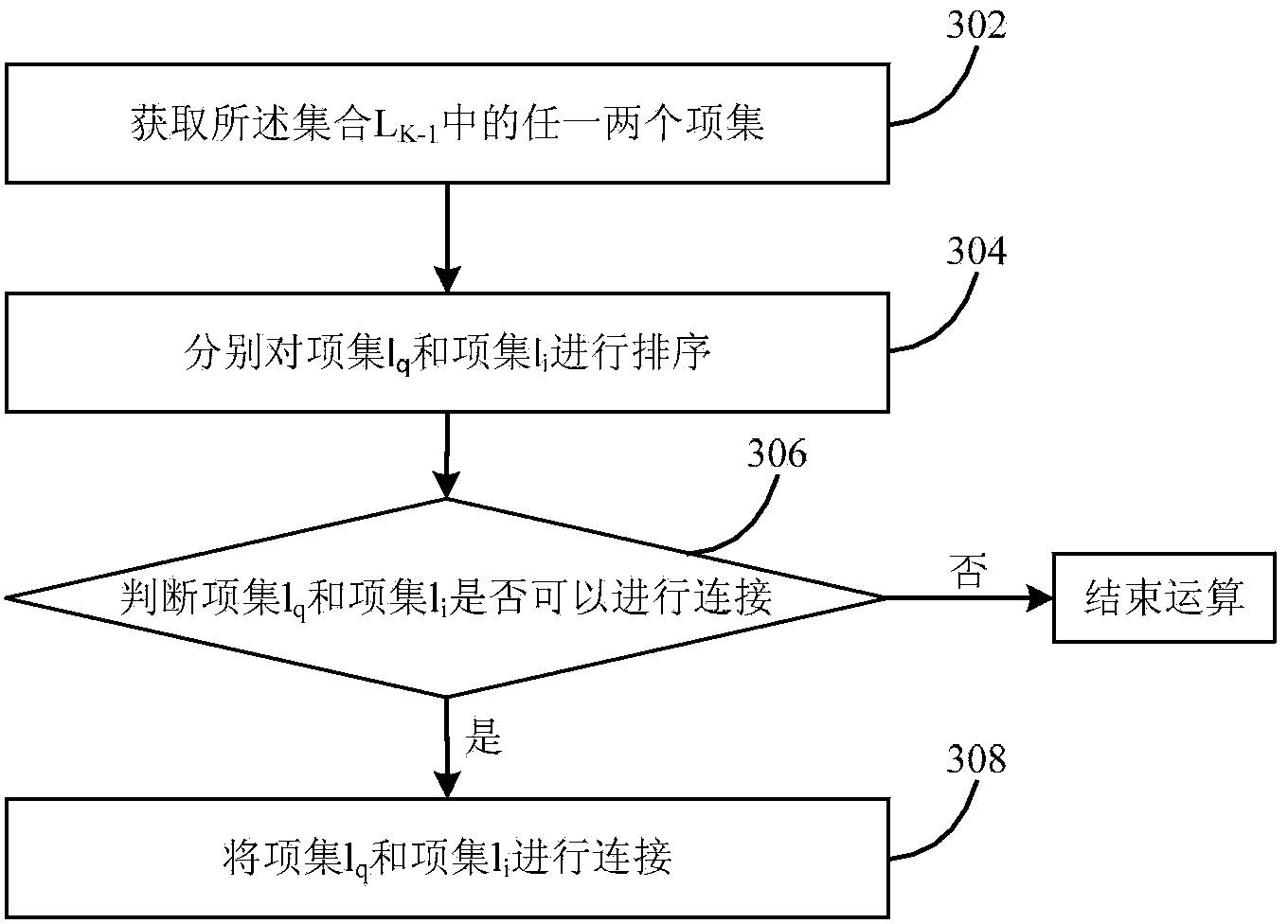
The invention provides a gateway correlation information obtaining method and system. The gateway correlation information obtaining method includes the following steps that a user access record is scanned; user access information in the user access record is obtained and forms an information set; according to the user access record, support degree counting of each nonvoid subset of the information set is obtained and a support degree counting database is established; according to the information set and the support degree counting database, all frequent one item sets are obtained and form a set L1; according to the set L1, a set LK is searched for, confidence coefficients of all the nonvoid vacuum subsets of the frequent one item sets and all frequent K item sets are analyzed, and network correlation information is obtained; based on the network correlation information, network application is performed. By means of the gateway correlation information obtaining method and system, the problem of weak correlation degree of the obtained network correlation information is solved.
Owner:KUAICHUAN SHANGHAI ADVERTISING
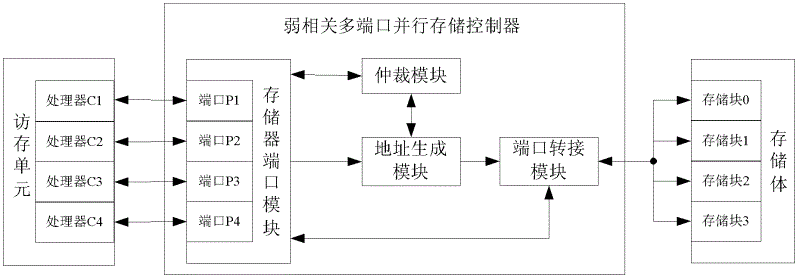
Weak correlation multiport parallel store controller
InactiveCN102622192AIncrease flexibilityReduce in quantityInput/output to record carriersComputer architectureControl store
The invention provides a weak correlation multiport parallel store controller, which is connected with a access memory unit in peripheral equipment and a storage stack including a plurality of storage body and can achieve multiport parallel storage between the visiting and storage unit in the peripheral equipment and the storage stack in the peripheral equipment. The weak correlation multiport parallel store controller comprises a storage port module, an arbitration module, an address generation module and a port switching module. The weak correlation multiport parallel store controller has the following advantages of (1) supporting block reading and writing in random lengths and being high in dexterity; (2) enabling transmission of address and data to multiplex in the same group of signal wires to complete, greatly reducing quantity of the transmission signal wires in a system, being favorable for application of distribution and wiring and reducing complexity and cost of the system; and (3) being simple in structure, less in used transmission signal wires and capable of supporting design and achievement of a large-scale multiport storage, and improving efficiency of parallel access memory of a plurality of processors.
Owner:BEIJING INSTITUTE OF TECHNOLOGYGY
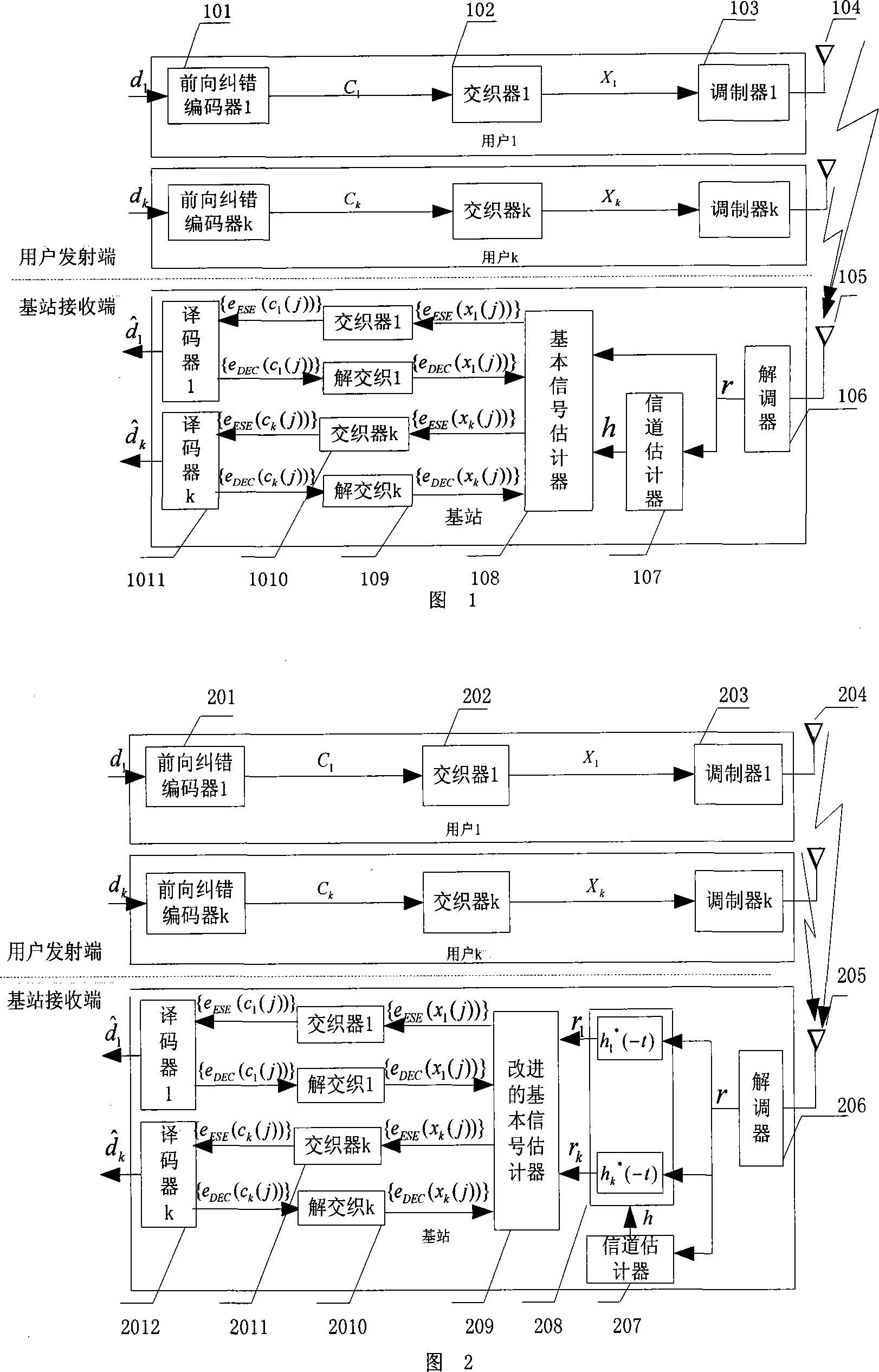
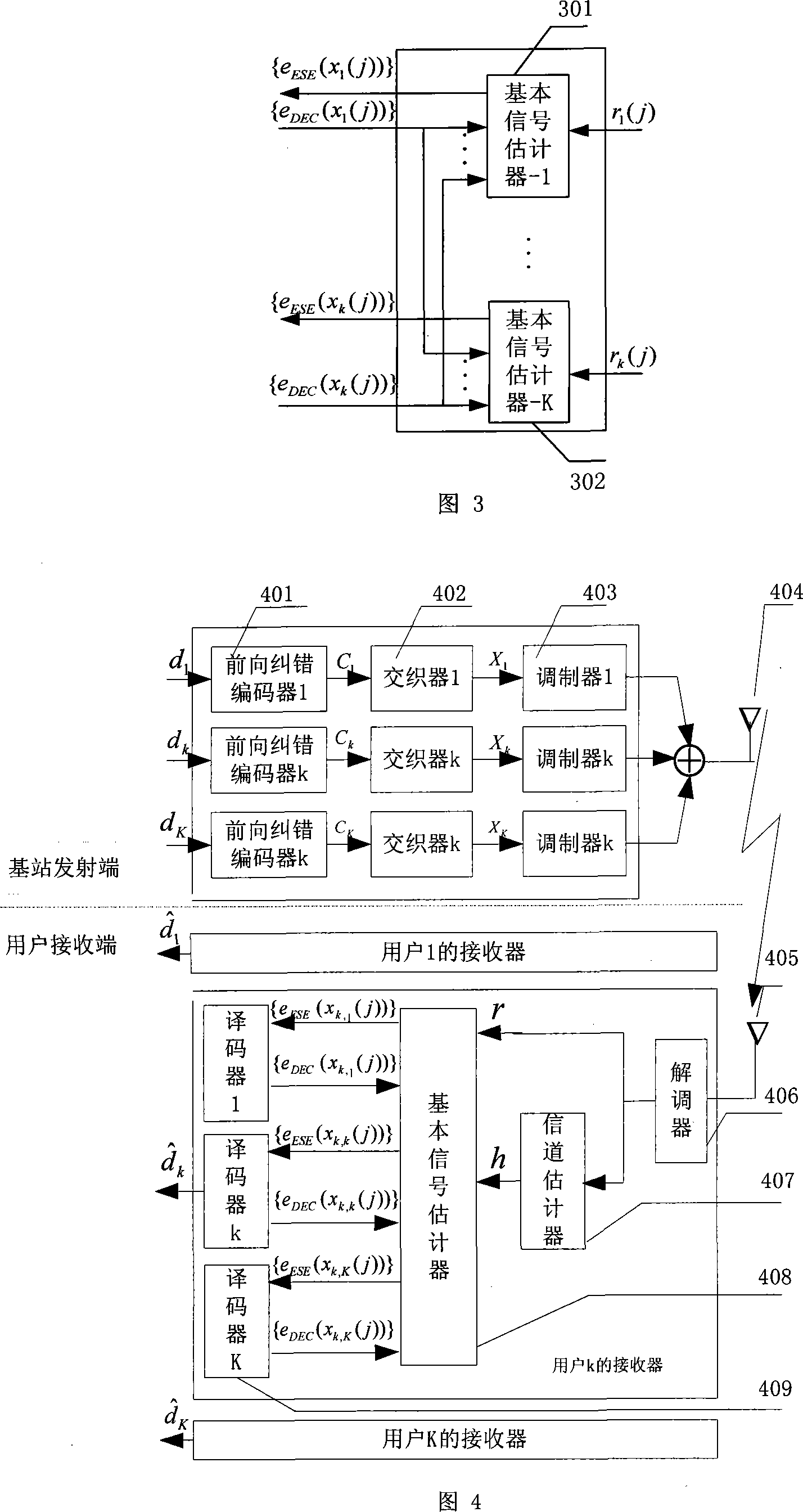
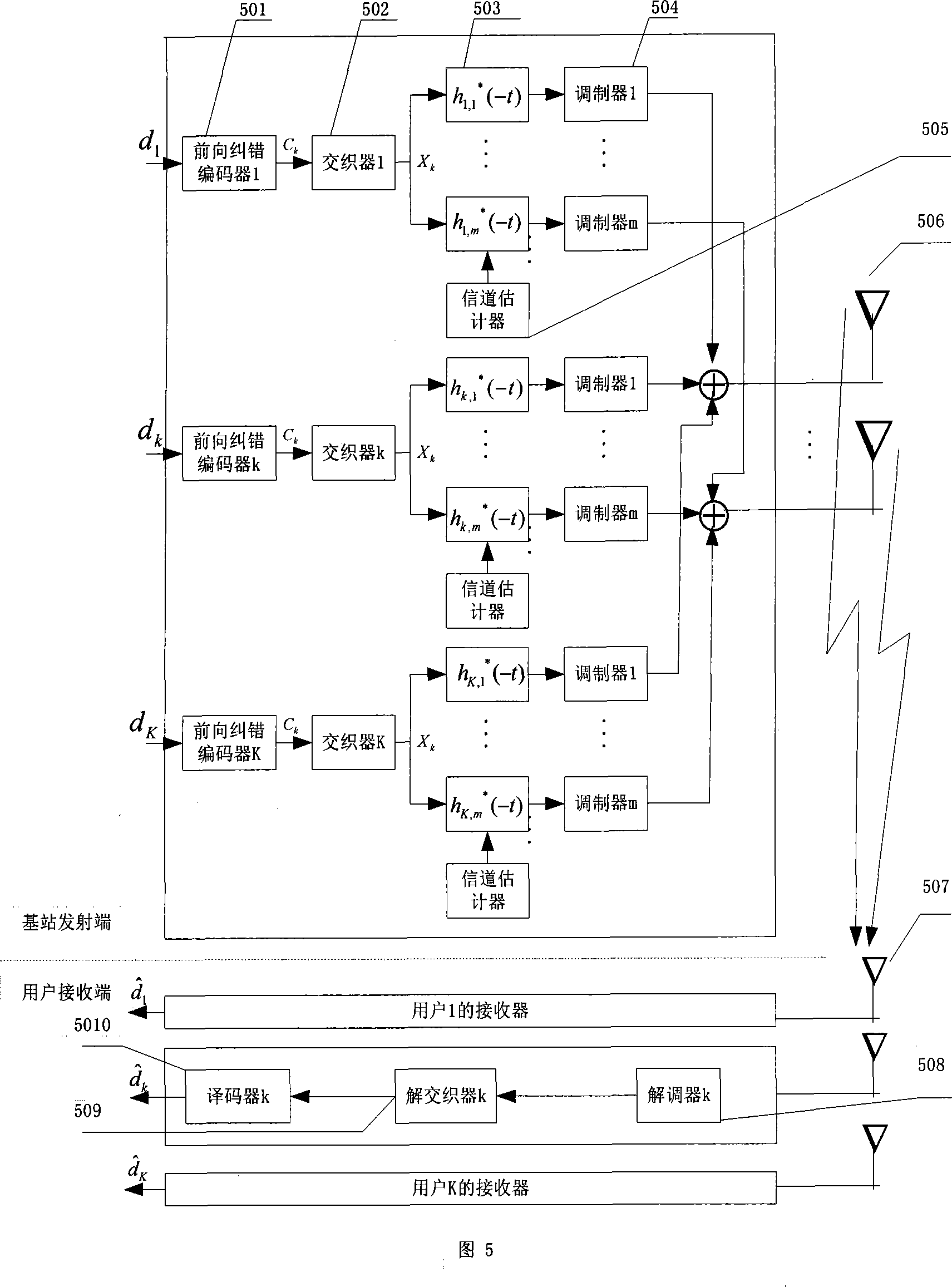
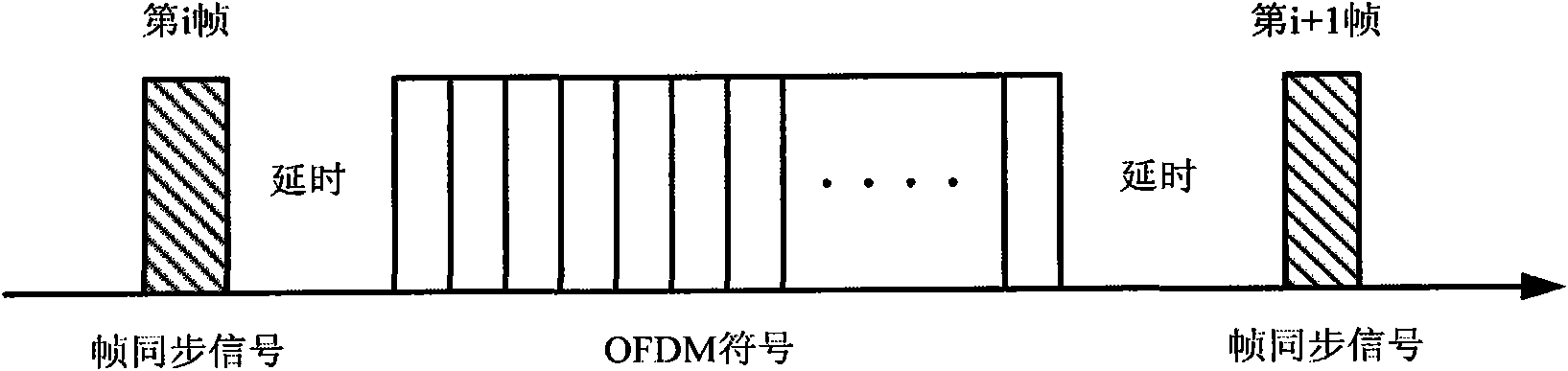
Time division multiplex and time reversal based IDMA wireless communication scheme
InactiveCN101098163AThe signal detection process is simpleReduce complexityDigital technique networkTime-division multiplexMulti user interferenceTime-division multiplexing
The invention discloses a IDMA ascending and descending communication system based on time-division multiplex (TDD)and time reverse (TR), named as time-division multiplex time reverse interlace multiple address (TDR-IDMA)system, wherein the invention uses time-division complex to reversely rotate the respond time of channel impact and taking reverse value as the front signal processor at the receiver of ascending channel and the signal pre-treating device at the sender of the descending channel. Via the weak correlation of channel impact responses of different users, the front signal processor can effectively restrain multiple user interferences, thereby the iterate multi-user check at the receiver of base station can be quickly contracted, and the signal preprocessor at the sender of the descending channel can support the signal check of mobile terminal, and the time-division multiplex can arrange channel evaluator of mobile receiver to base station, to simply the complexity of descending receiver most and improve descending data transmission rate. Compared with traditional IDMA system, the TDR-IDMA has quick multi-user and simplified mobile device.
Owner:UNIV OF ELECTRONICS SCI & TECH OF CHINA
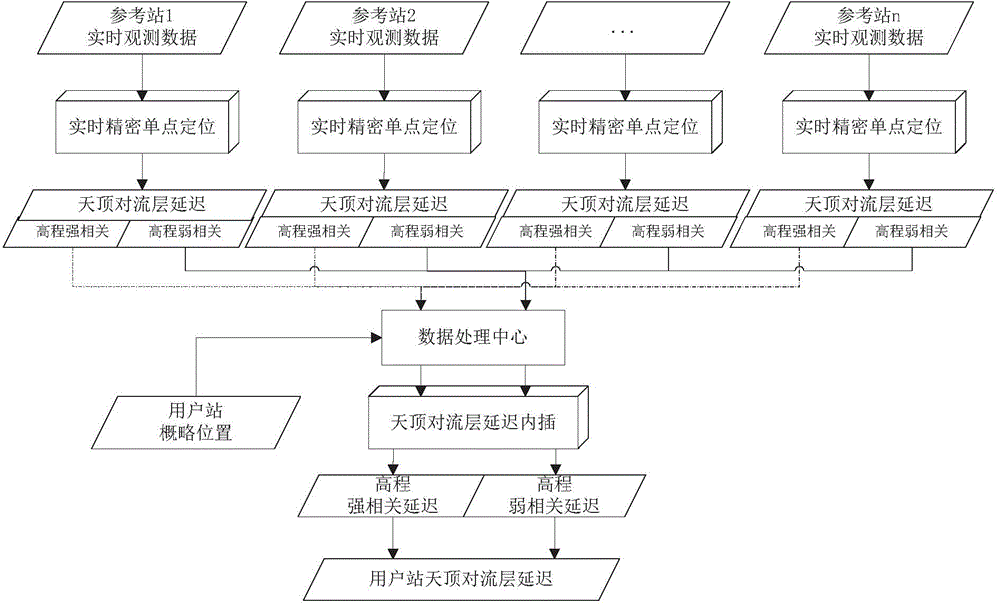
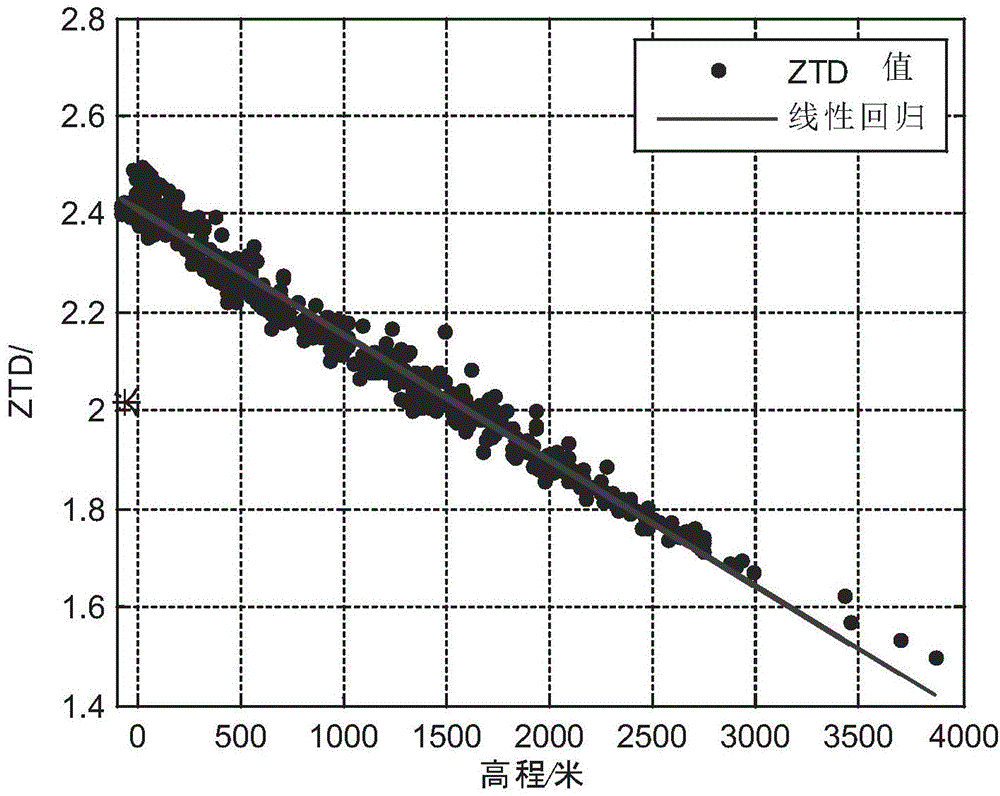
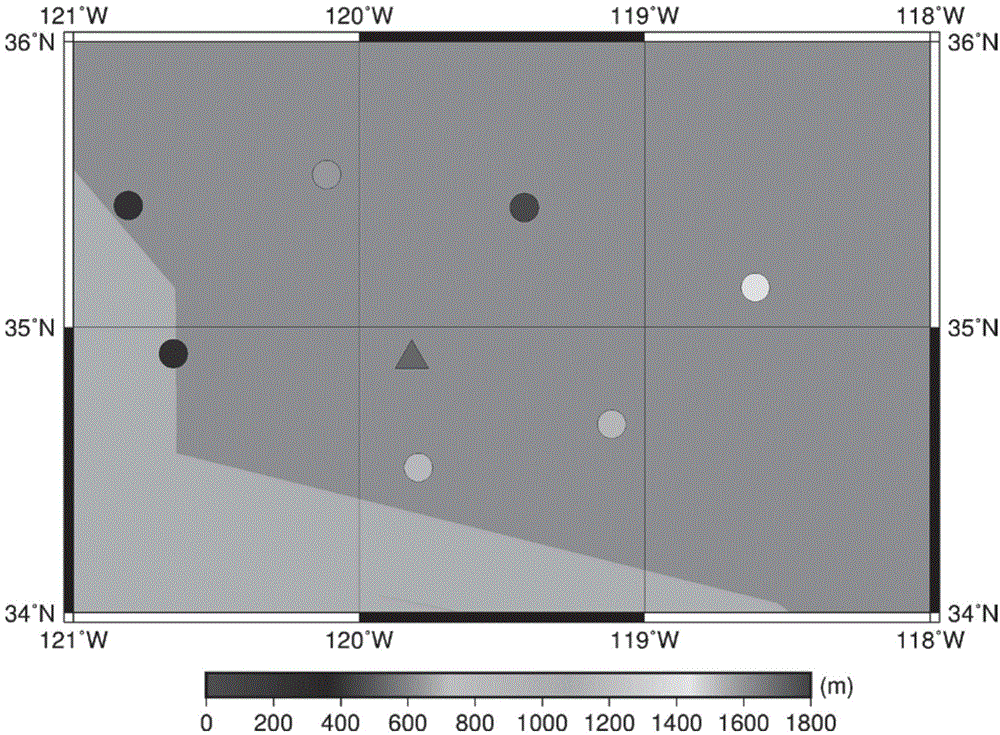
Sparse reference station network zenith troposphere delay modeling method considering elevation difference
ActiveCN104656108ASimple interpolation modeling methodSmall amount of calculationSatellite radio beaconingInformaticsTroposphereComputer science
The invention discloses a sparse reference station network zenith troposphere delay modeling method considering the elevation difference. Conventional local area network enhancement PPP (precise point position) modeling methods do not consider effects caused by the elevation difference on the interpolation accuracy and depend on a certain amount of reference stations. According to the method, the relation between the elevation difference and zenith troposphere delay is considered, reference station zenith troposphere wet delay values are calculated through non-ionosphere combined precise point filtering, zenith troposphere dry delay values are calculated through a model, the dry (wet) delay values are divided into an elevation strong correlation part and an elevation weak correlation part according to the relation between the troposphere delay values and elevation factors, and the sparse reference station network zenith troposphere delay modeling method considering the elevation difference is provided on the basis. The method considers the effects caused by the elevation difference on the troposphere delay values, is applicable to sparse reference station local area networks and is low in dependence on the number of the reference stations.
Owner:SOUTHEAST UNIV
Timed synchronization method for OFDM-WLAN (orthogonal frequency division multiplexing-wireless local area network) system
InactiveCN103298100AHigh precisionPrecise positioningSynchronisation arrangementNetwork topologiesHardware implementationsComputer science
The invention provides a timed synchronization method for an OFDM-WLAN system. The method comprises the following steps: 1) utilizing a delayed autocorrelation and length maintaining algorithm to achieve coarse synchronization and obtain the energy of an STF (short training field); 2) utilizing the energy to perform automatic gain control (AGC); 3) utilizing the weak correlation of noise and the strong correlation of the STF to achieve fine synchronization; and 4) combining the coarse synchronization with the fine synchronization to obtain the initial position of a data symbol. The timed synchronization method for the OFDM-WLAN system utilizes the STF and meanwhile skillfully utilizes the randomness of the noise to achieve timed synchronization, thereby greatly reducing the calculation and the hardware implementation complexity of a synchronization algorithm and meanwhile being capable of locating the position of the symbol rapidly and accurately.
Owner:SOUTHEAST UNIV
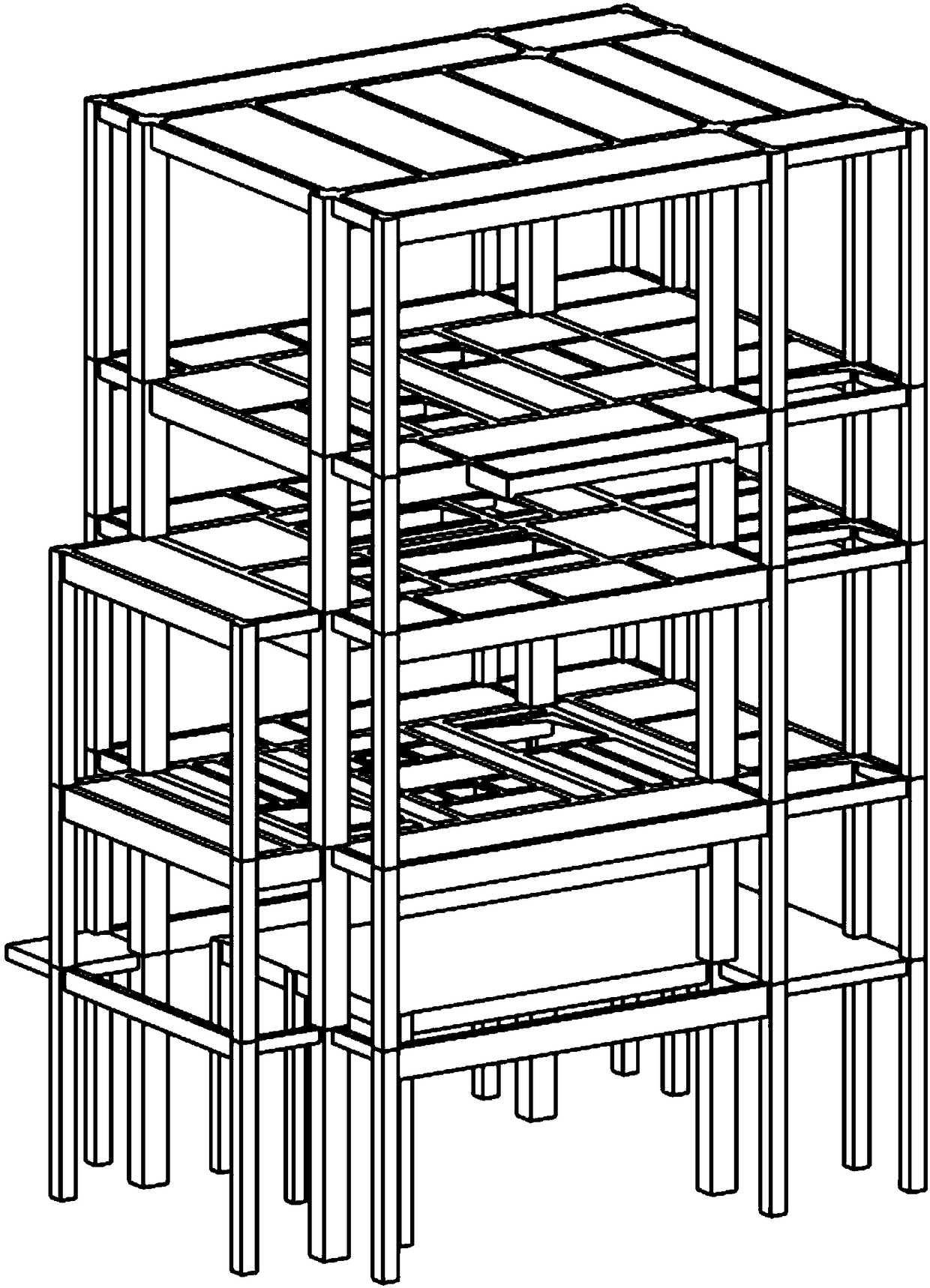
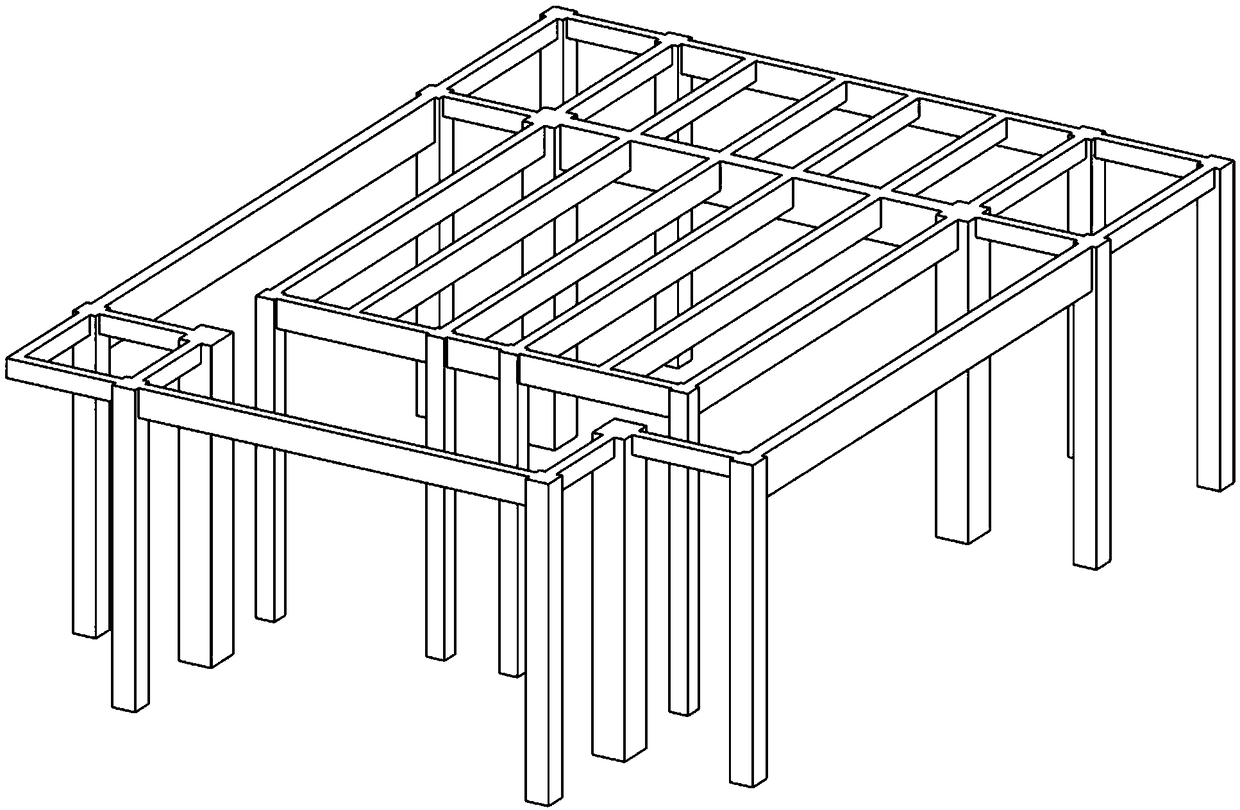
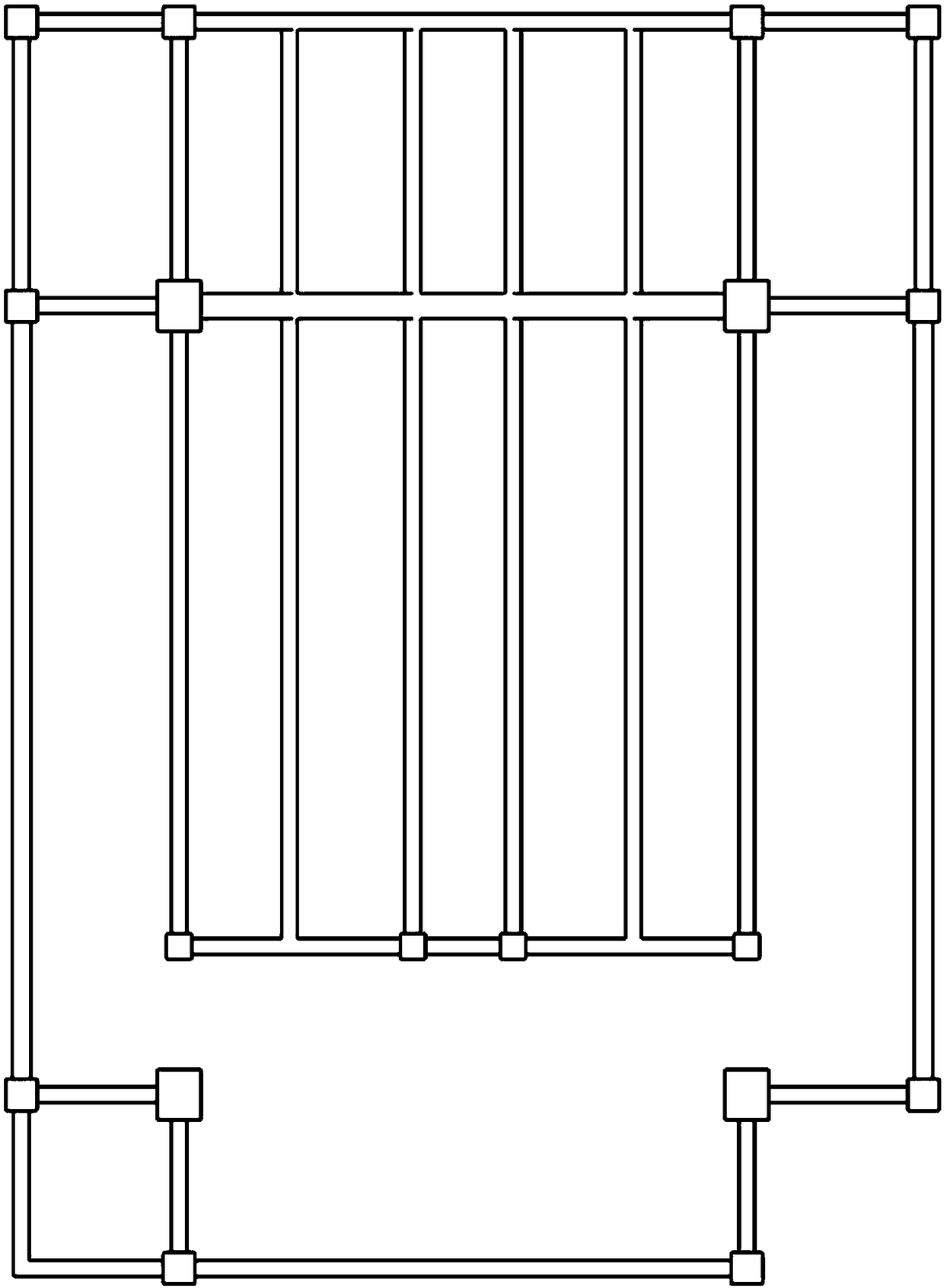
A weak association method and system based on a BIM model
ActiveCN109190209AAchieve synchronizationAvoid complexityGeometric CADDesign optimisation/simulationWeak correlationShop drawing
The invention discloses a weak correlation method and system based on a BIM model. The method comprises the following steps: constructing a structural calculation model corresponding to each componentthereof according to the BIM model; generating a calculation book unit for each component in the structural calculation model according to the input information; generating a projection direction construction drawing of the local BIM model according to the input instruction; establishing the matching relationship between the calculation book unit and the components in the local BIM model by weakassociation algorithm; extracting calculation information from the calculation book unit to form labeling information; forming construction drawings based on input instructions according to the drawing specification by the tagging information and the components in the local BIM model. The scheme solves the problem that the construction drawings generated by the strong association method in the prior art are not convenient to modify and adjust subsequently, realizes the synchronization of the labeling information of the construction drawings and the component information of the BIM model, and reduces the limitation of the strong association and the complexity of the secondary software at the same time.
Owner:长沙恩为软件有限公司
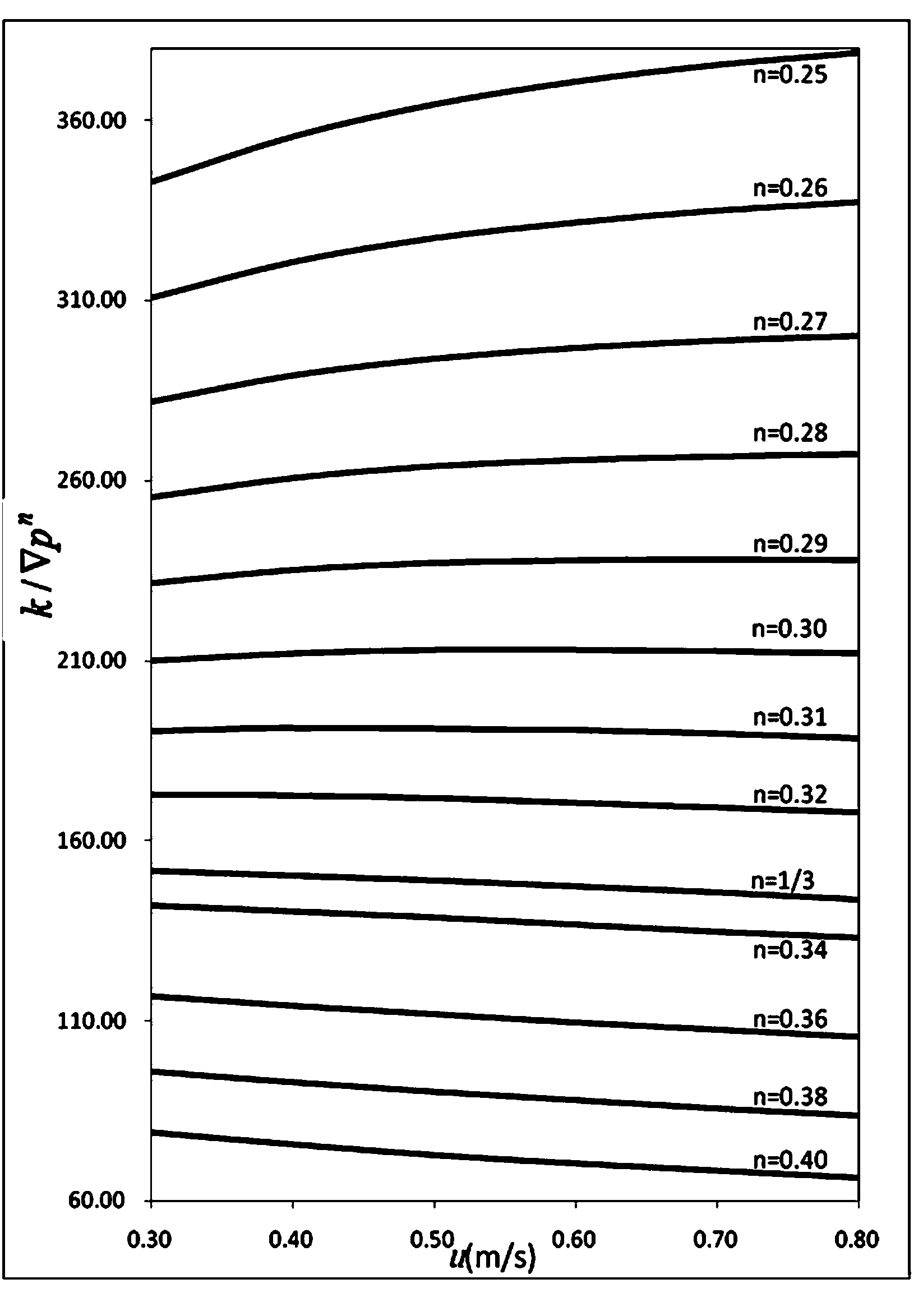
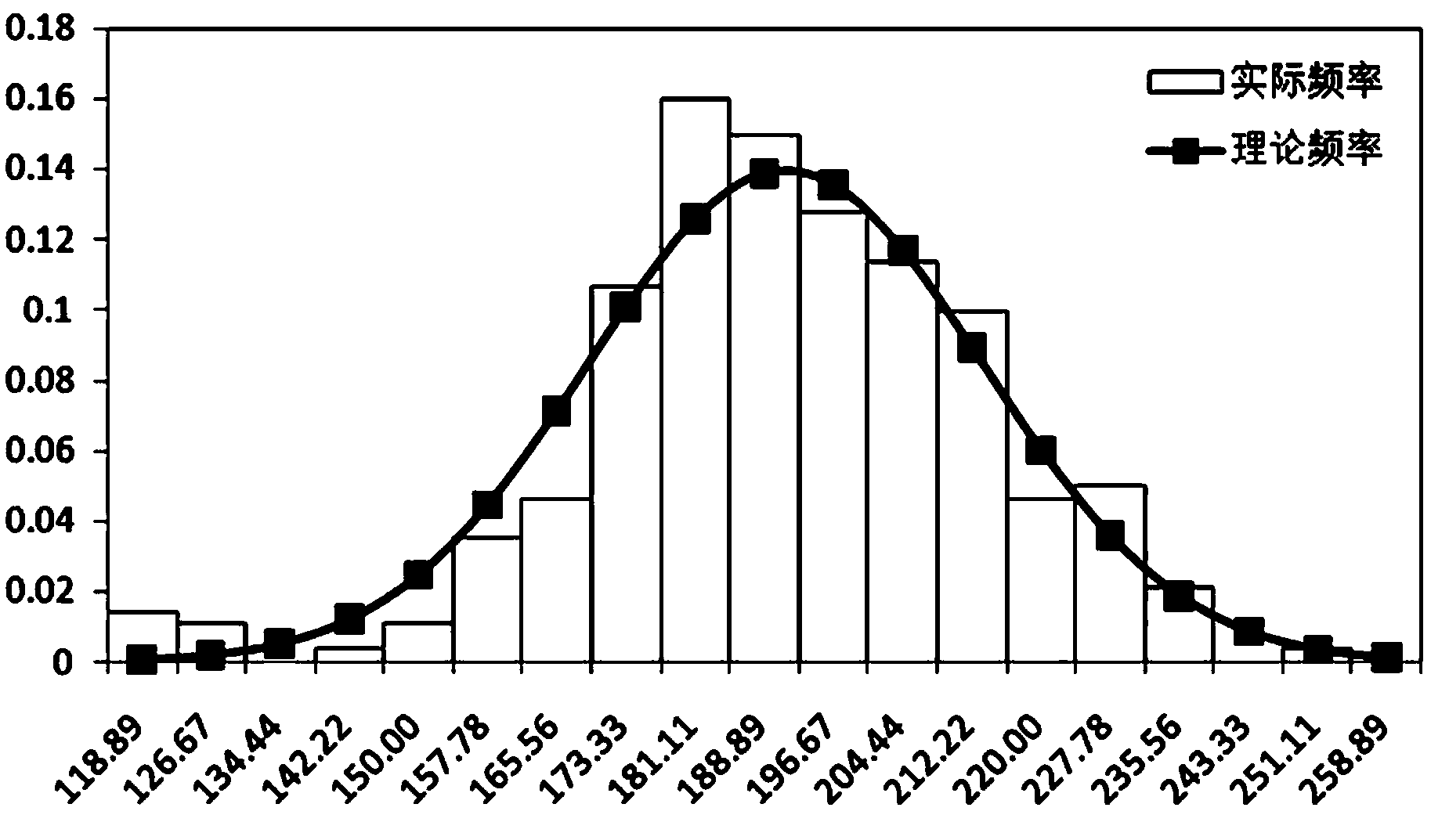
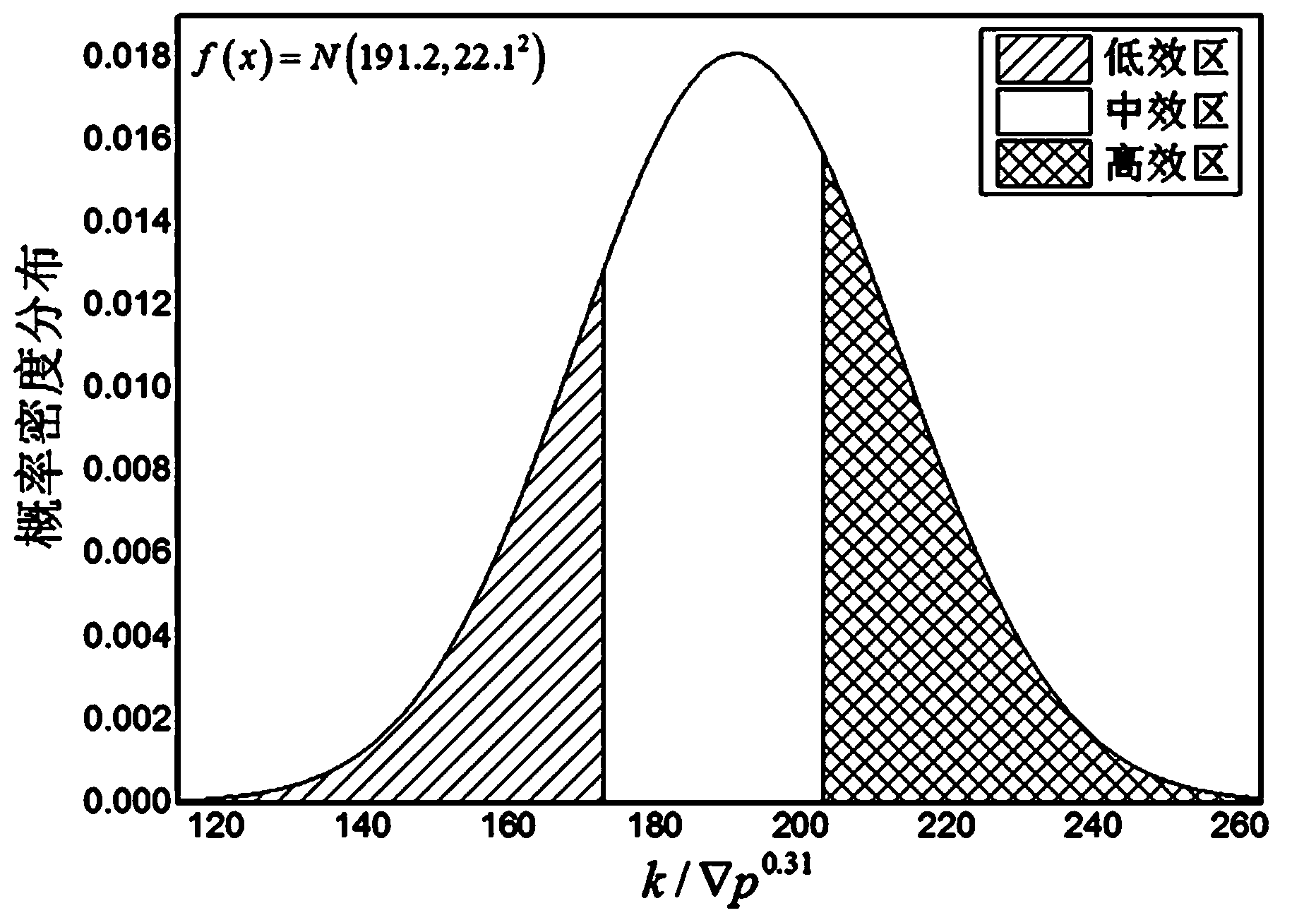
Energy efficiency quantitative evaluation method for heat exchanger
ActiveCN104036115AReflect intrinsic energy efficiency attributesImprove stabilitySpecial data processing applicationsFixed energyEngineering
The invention relates to an energy efficiency quantitative evaluation method for a heat exchanger. The energy efficiency evaluation index of the heat exchanger of the same kind is made to meet the stability requirement, the energy efficiency evaluation index of the heat exchanger is in a weak correlation relation with the flowing speed of fluid of the heat exchanger and the heat exchange area, and based on the requirement in the heat exchanger and heat transfer element performance test method GB / T27698-2011, the method comprises the steps that (1), the heat transfer performance of the evaluated heat exchanger is tested, and a total heat transfer coefficient k under the standard work condition is obtained; (2) the flowing performance of the evaluated heat exchanger is tested under the same condition, and the flowing pressure drops delta pc and delta ph generated when cold fluid and heat fluid flow through the heat exchanger under the standard work condition are obtained; (3) the energy efficiency evaluation index (please see the formula in the specification) of the evaluated heat exchanger is calculated. The method reflects the fixed energy efficiency property of the heat exchanger, the energy efficiency of the heat exchanger of the same kind meets the determined probability statistics distribution rule, and the scientific implementation method is provided for determining the energy efficiency and grade of the heat exchanger.
Owner:LANZHOU GUANYU HEAT TRANSFER & ENERGY SAVING ENG RES +2
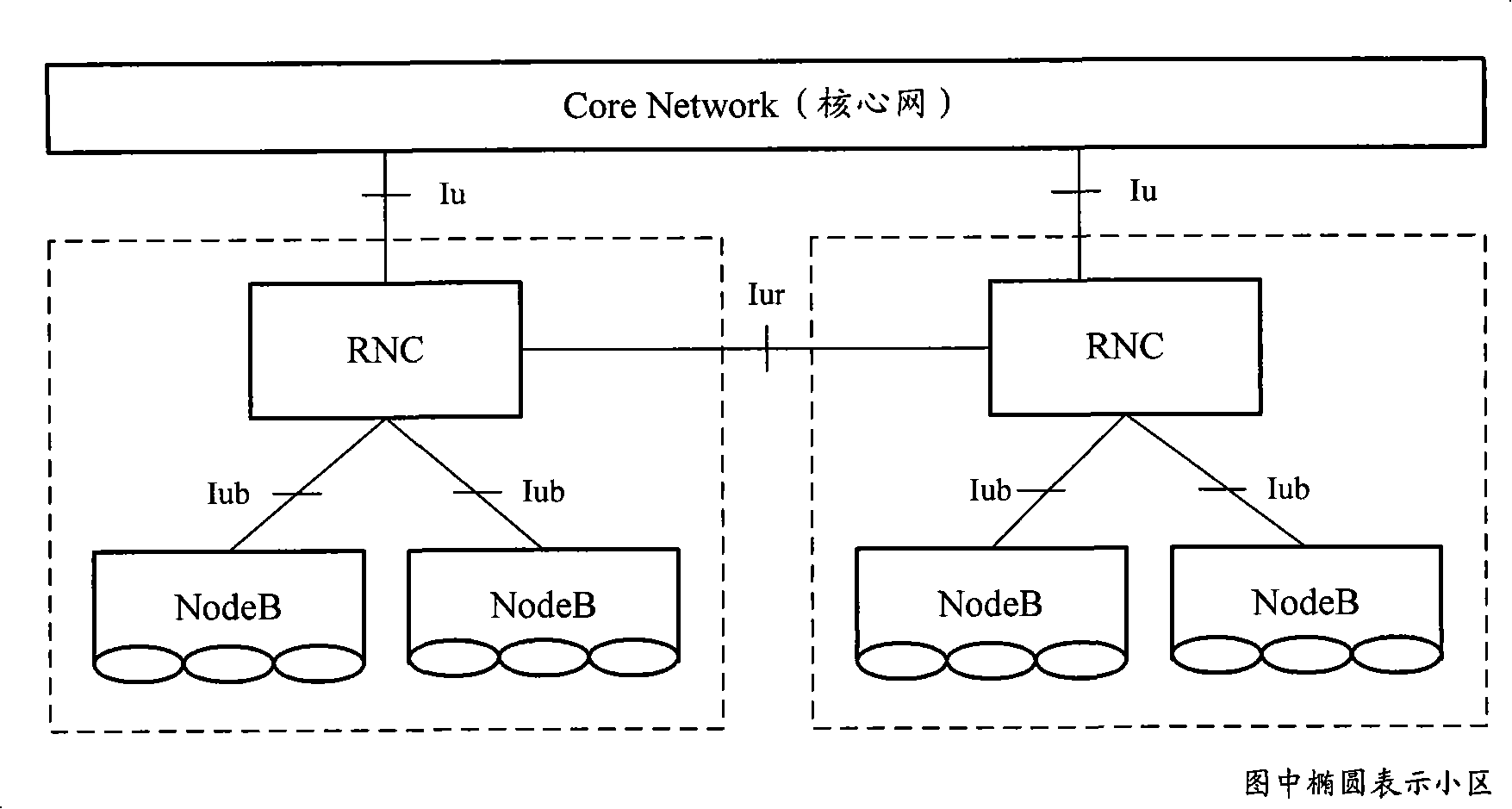
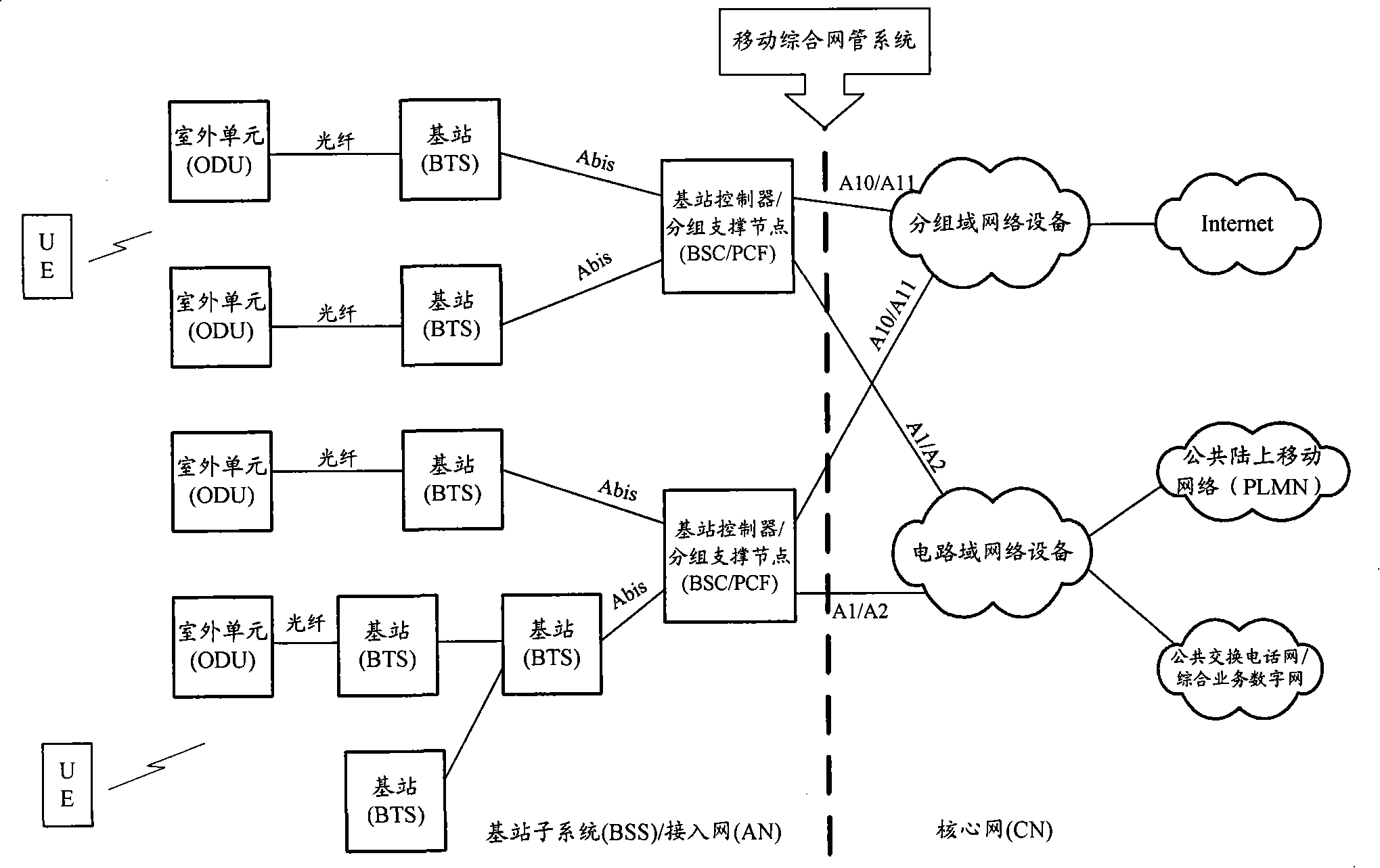
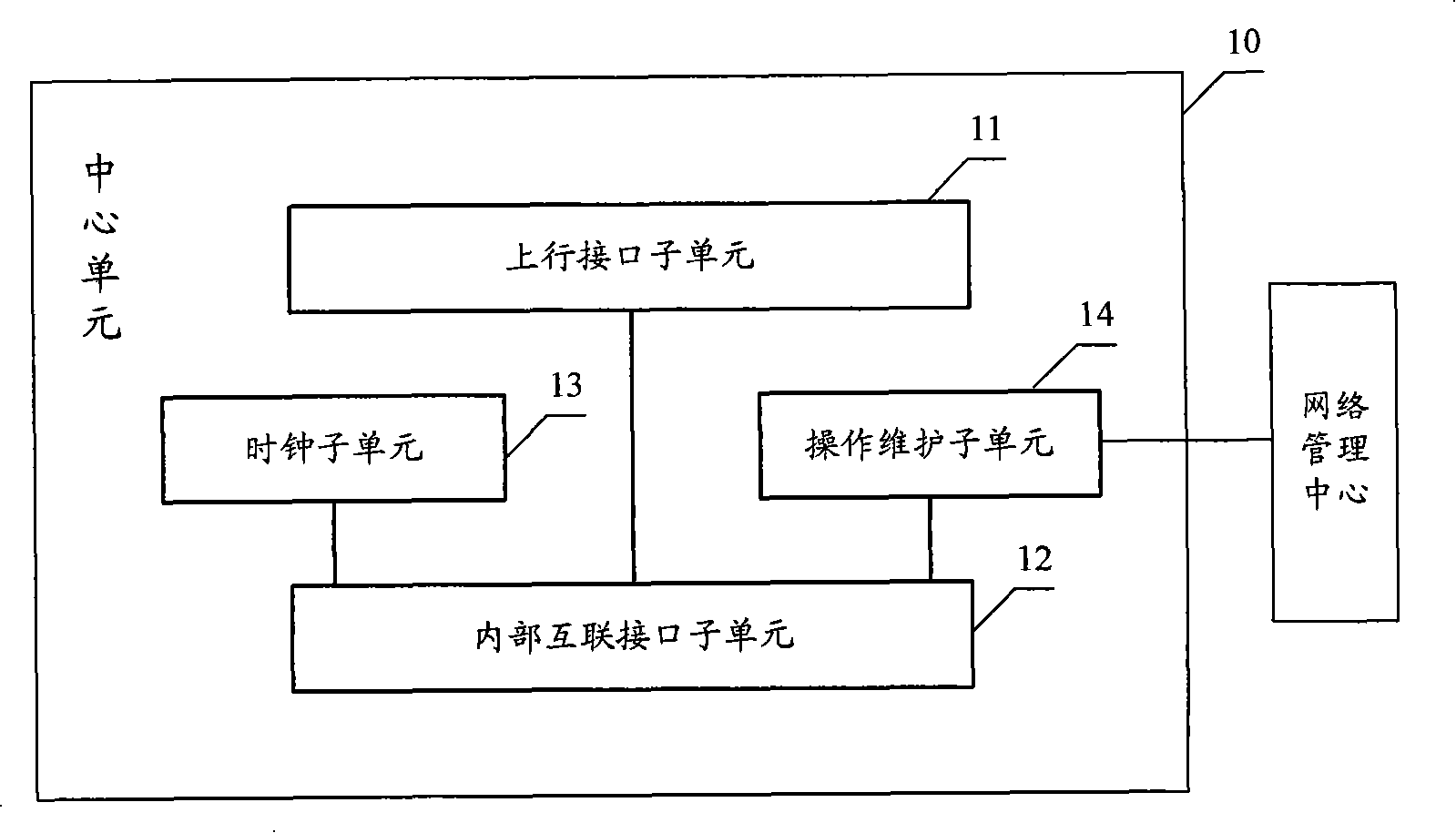
Distributed base station controller and its unit, data transmission method
ActiveCN101159893AFlexible networkingRadio/inductive link selection arrangementsWireless communicationAccess networkBusiness data
The invention discloses a distributed base station controller and a unit thereof and a data transmission method, wherein, the distributed base station controller includes a central unit and at least one pulling unit. The central unit is used to convert protocols of interactive signaling and business data between core network node and the pulling unit and perform operation processing in weak correlation with business for the pulling unit. The pulling unit is used to convert protocols of signaling and business data between the central unit and the base station, perform multi-drop merging and converging processing for received up data and sent to the central unit. When the pulling units are more than one, connect with the central unit respectively or in cascade connection with the central unit. The invention can realize flexible networking mode, deploy a SDU unit with multi-drop merging function in the distributed base station controller on a transmission converging node of wireless access network and improve the converging capability of the transmission converging node.
Owner:HUAWEI TECH CO LTD
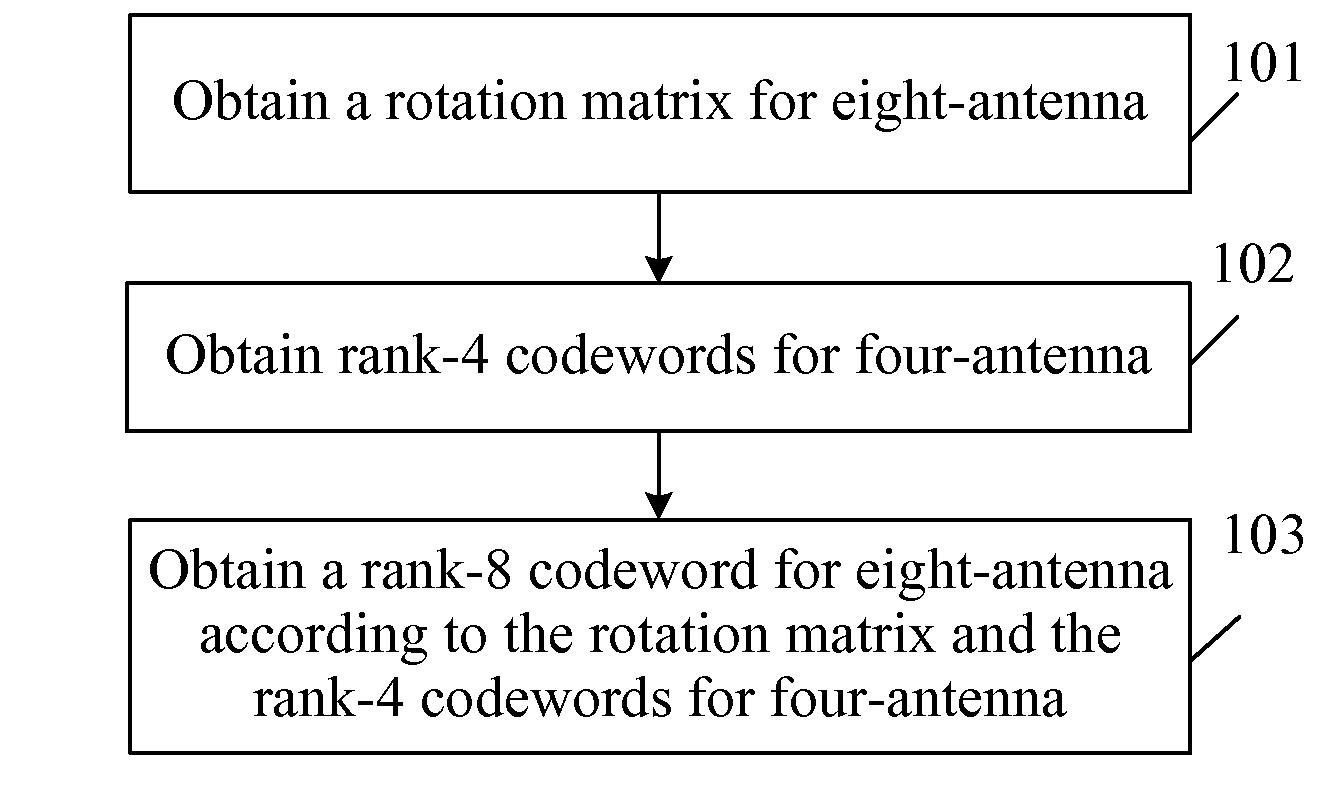
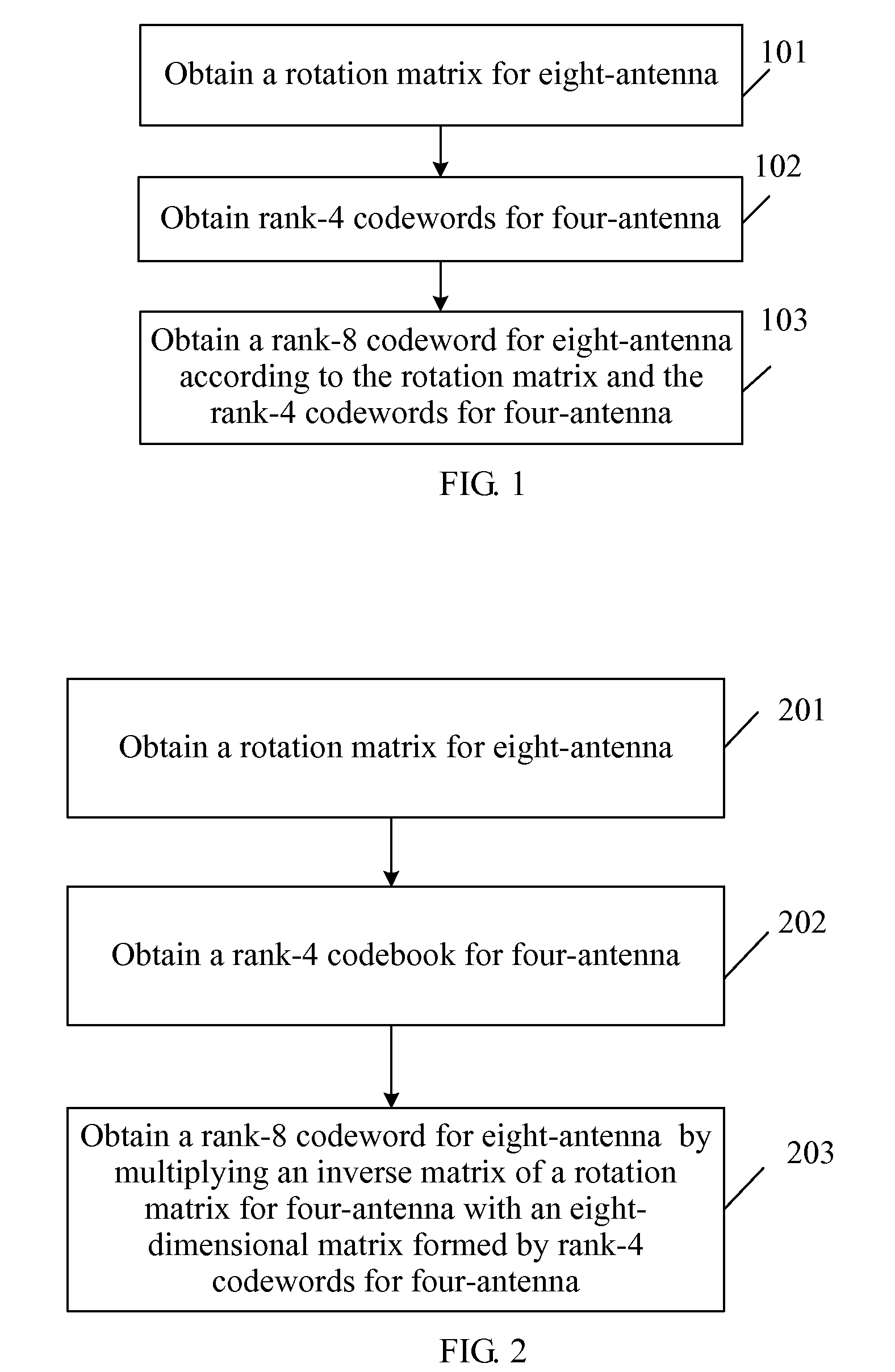
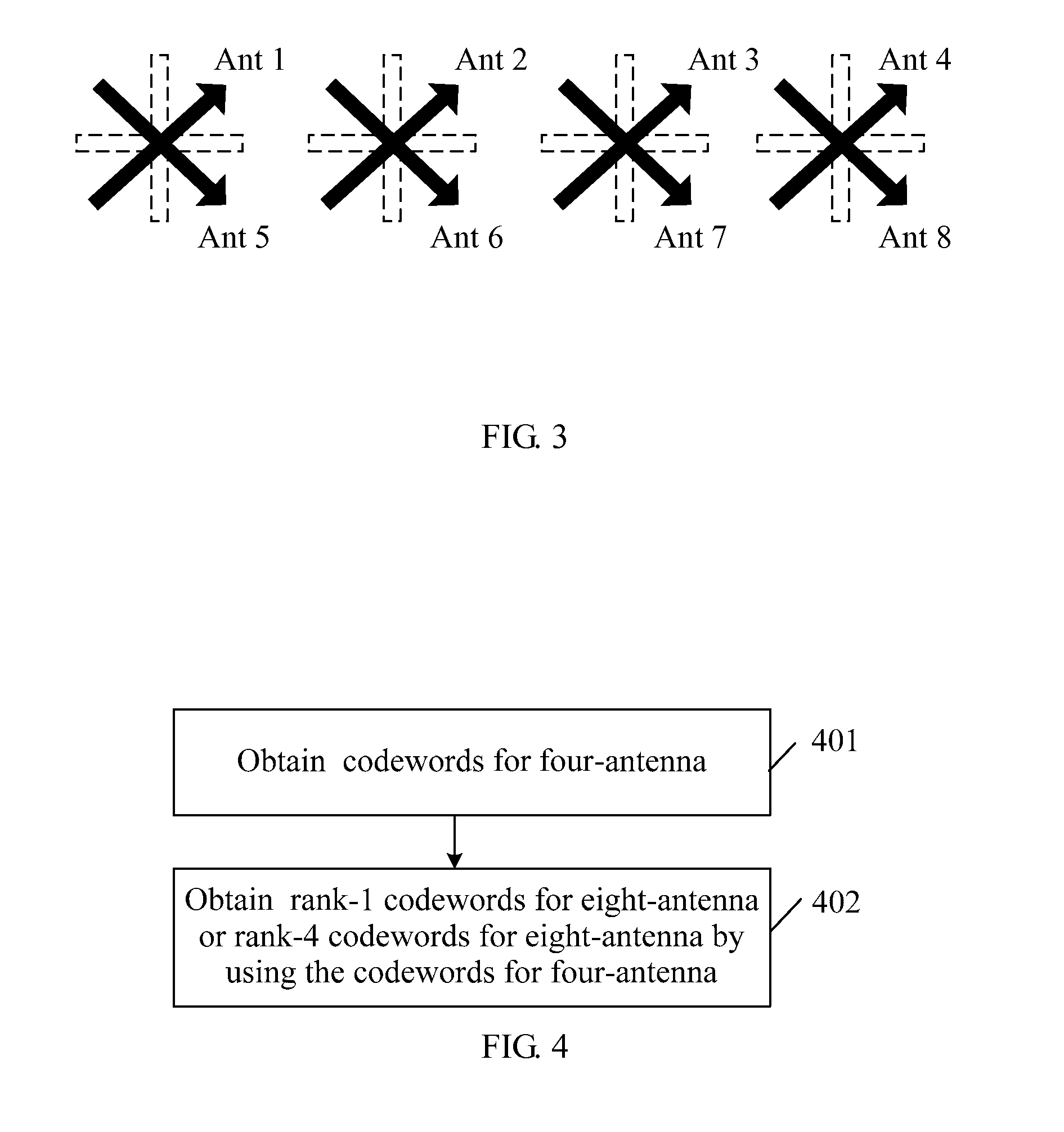
Method for generating codebook, method and apparatus for data transmission
ActiveUS20120087422A1Polarisation/directional diversitySecret communicationData transmissionUser equipment
A method for generating a codebook and a method and an apparatus for data transmission are provided. The method includes: receiving a label of a codeword sent by a User Equipment (UE); selecting the codeword identified by the label from the codebook for eight-antenna; and coding data to be sent by using the codeword. The codebook for eight-antenna includes at least one rank-8 codeword for eight-antenna. The rank-8 codeword for eight-antenna is generated by multiplying an inverse matrix of a rotation matrix for eight-antenna with an eight-dimensional matrix formed by rank-4 codewords for four-antenna; or generated by extending rank-4 codewords for eight-antenna, where the rank-4 codeword for eight-antenna is generated according to codewords for four-antenna. Therefore, the codeword in the codebook for eight-antenna is applicable to scenarios including dual-polarization strong correlation, dual-polarization weak correlation, single-polarization strong correlation, and single-polarization weak correlation, etc.
Owner:HUAWEI TECH CO LTD
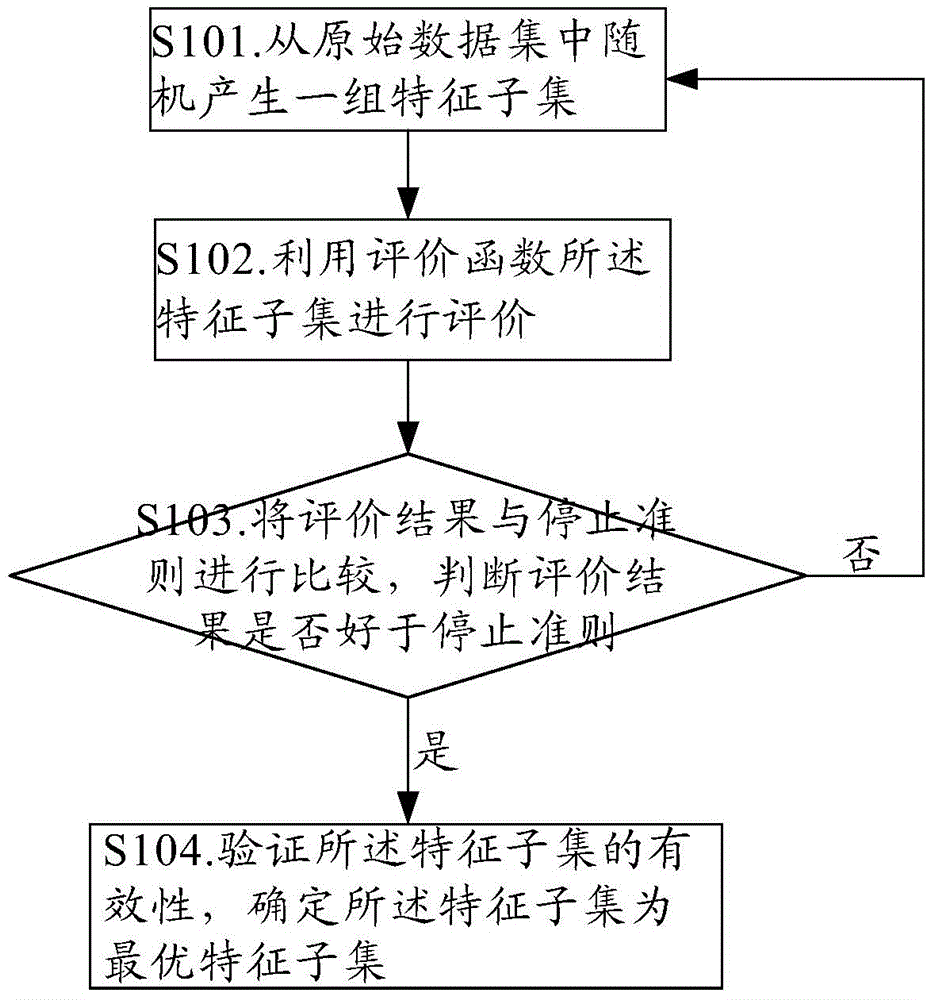
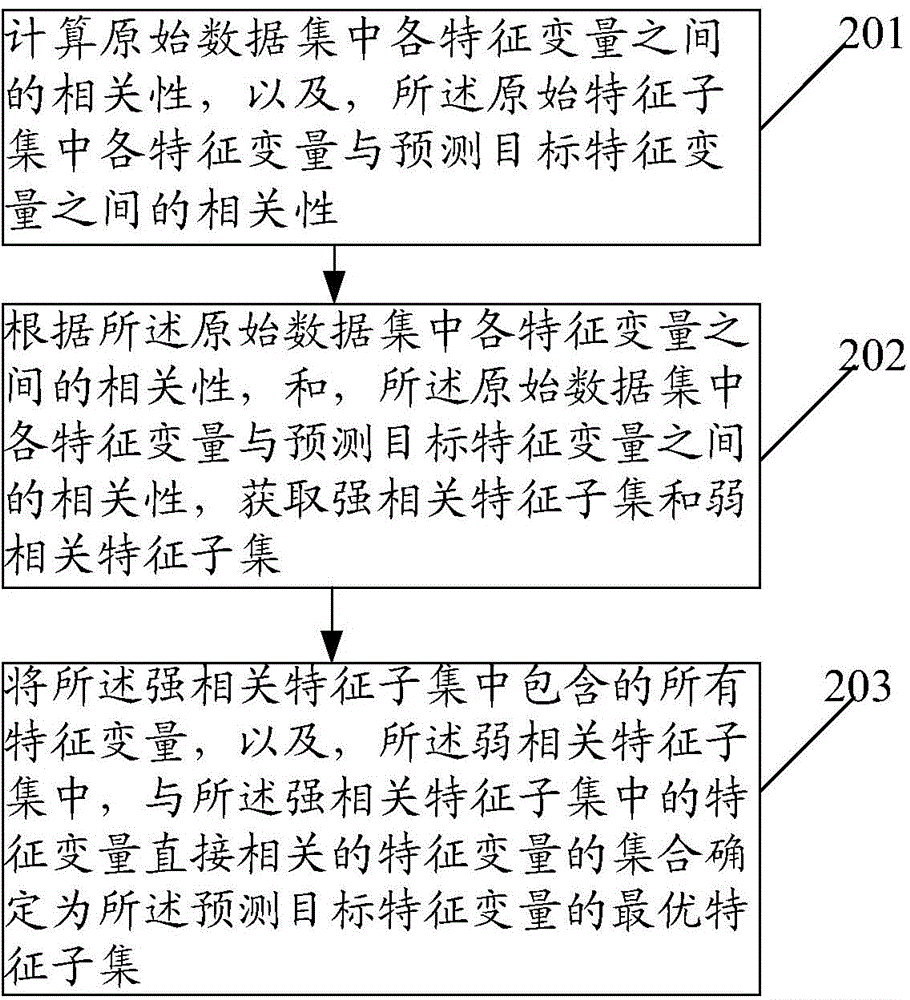
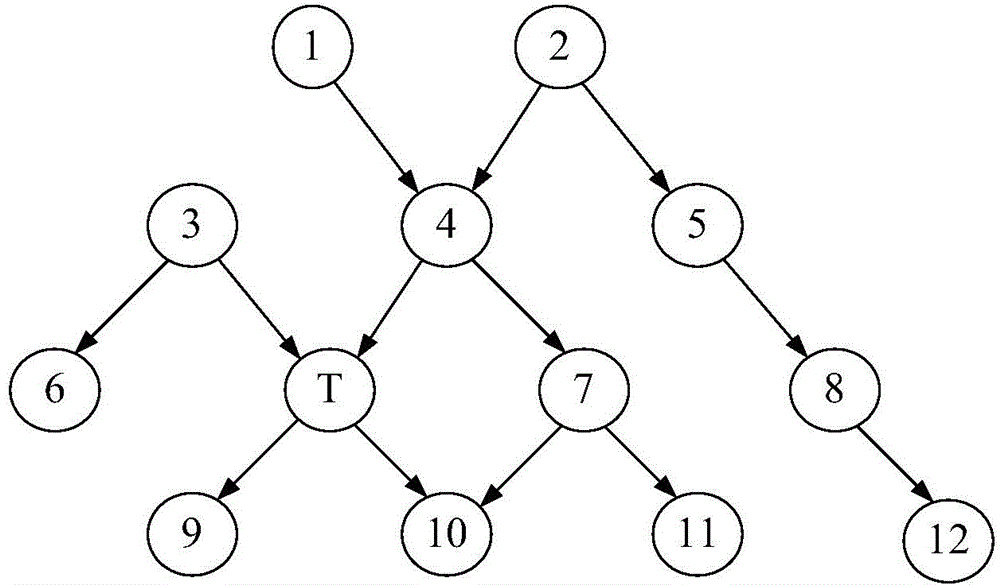
Characteristic selection method and device
ActiveCN105260371AImprove computing efficiencyImprove effectivenessSpecial data processing applicationsOriginal dataHigh dimensional
The invention provides a characteristic selection method and device, and relates to the technical field of data mining. According to the characteristic selection method and device, an optimum characteristic subset is determined on the basis of the correlation among characteristic variables, so that the effectiveness and operation efficiency of high-dimensional data characteristic selection are improved. The characteristic selection method provided by the invention comprises the following steps: calculating the correlation among characteristic variables in an original data set and the correlation between the characteristic variables in the original data set and predicted objective characteristic variables; obtaining a strong correlation characteristic subset and a weak correlation characteristic subset according to the correlation among the characteristic variables in the original data set and the correlation between the characteristic variables in the original data set and the predicted objective characteristic variables; and determining the set of all the characteristic variables contained in the strong correlation characteristic subset and the characteristic variables directly correlated to the characteristic variables in the strong correlation characteristic subset in the weak correlation characteristic subset as the optimum characteristic subset of the predicted objective characteristic variables.
Owner:HUAWEI TECH CO LTD
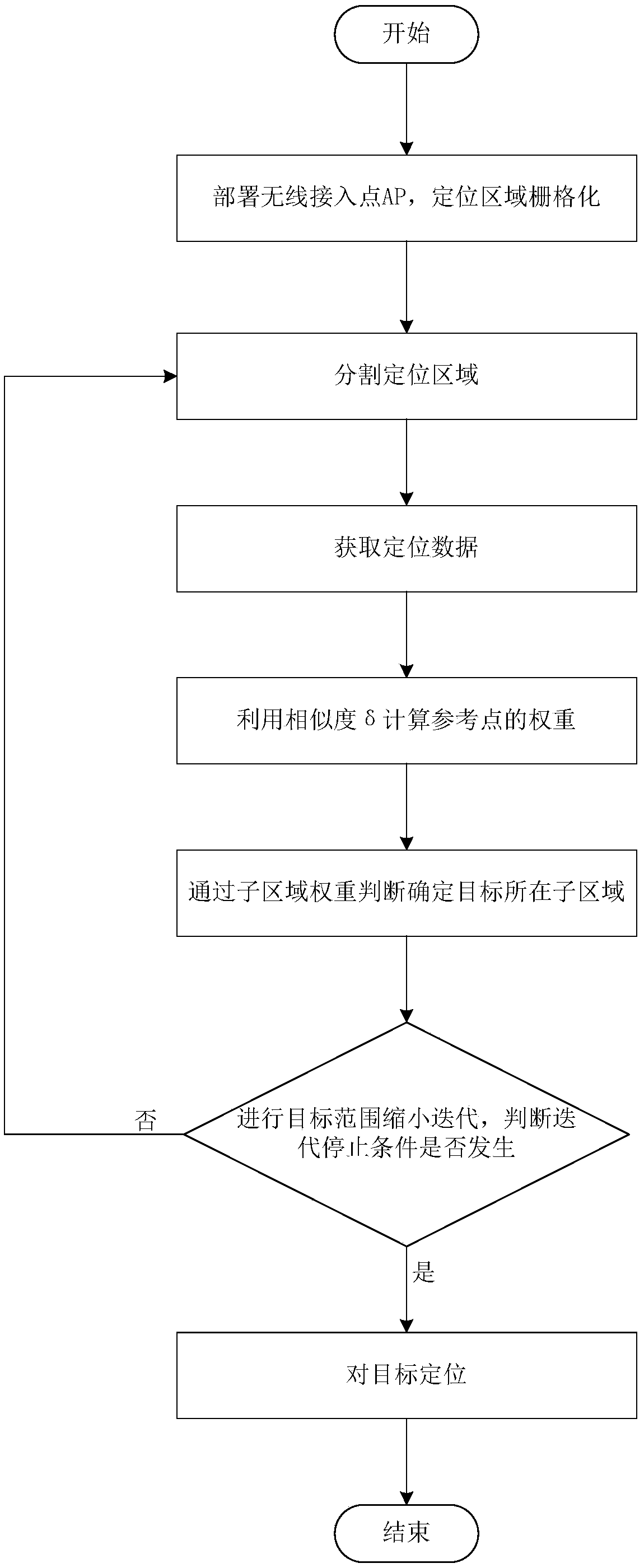
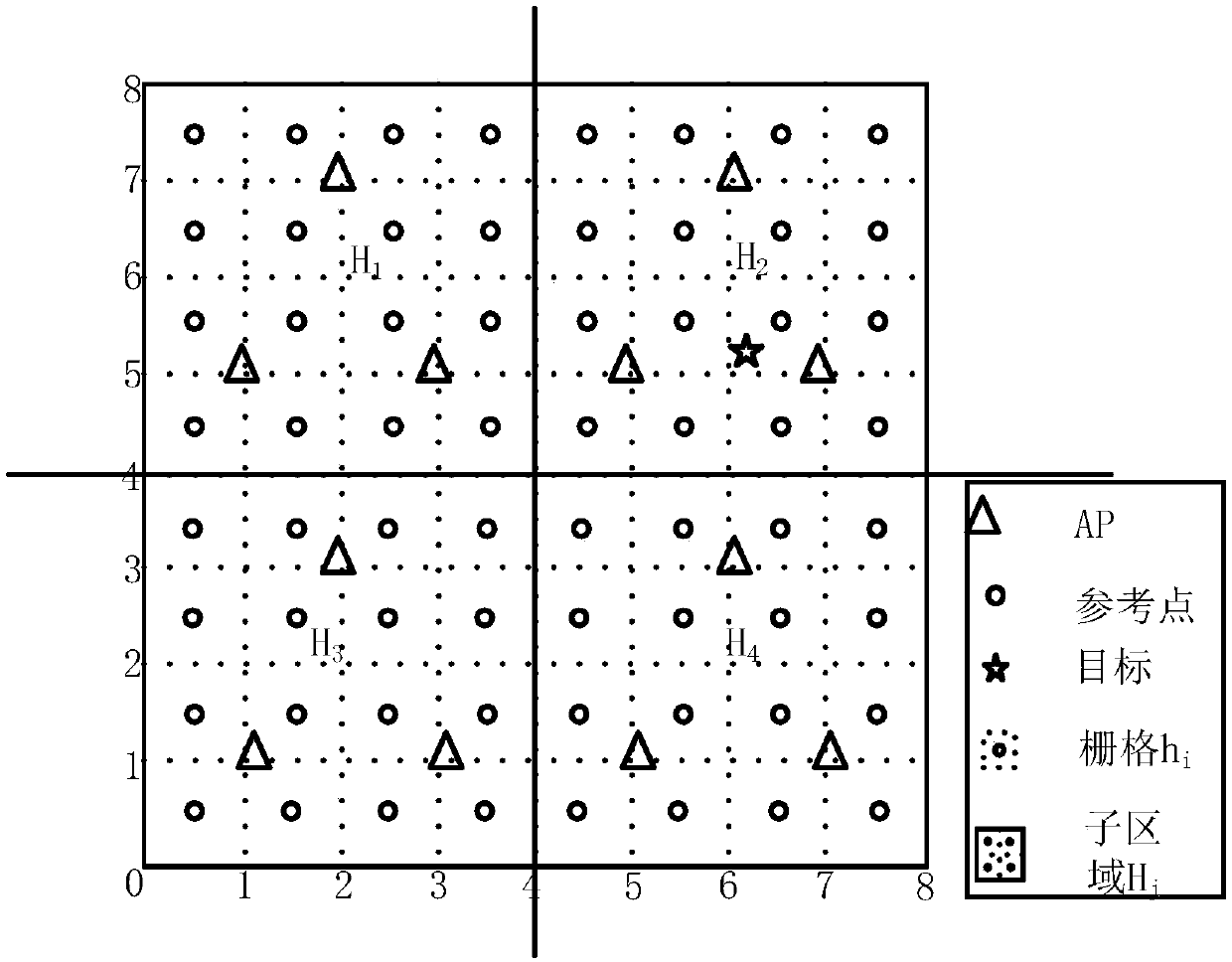
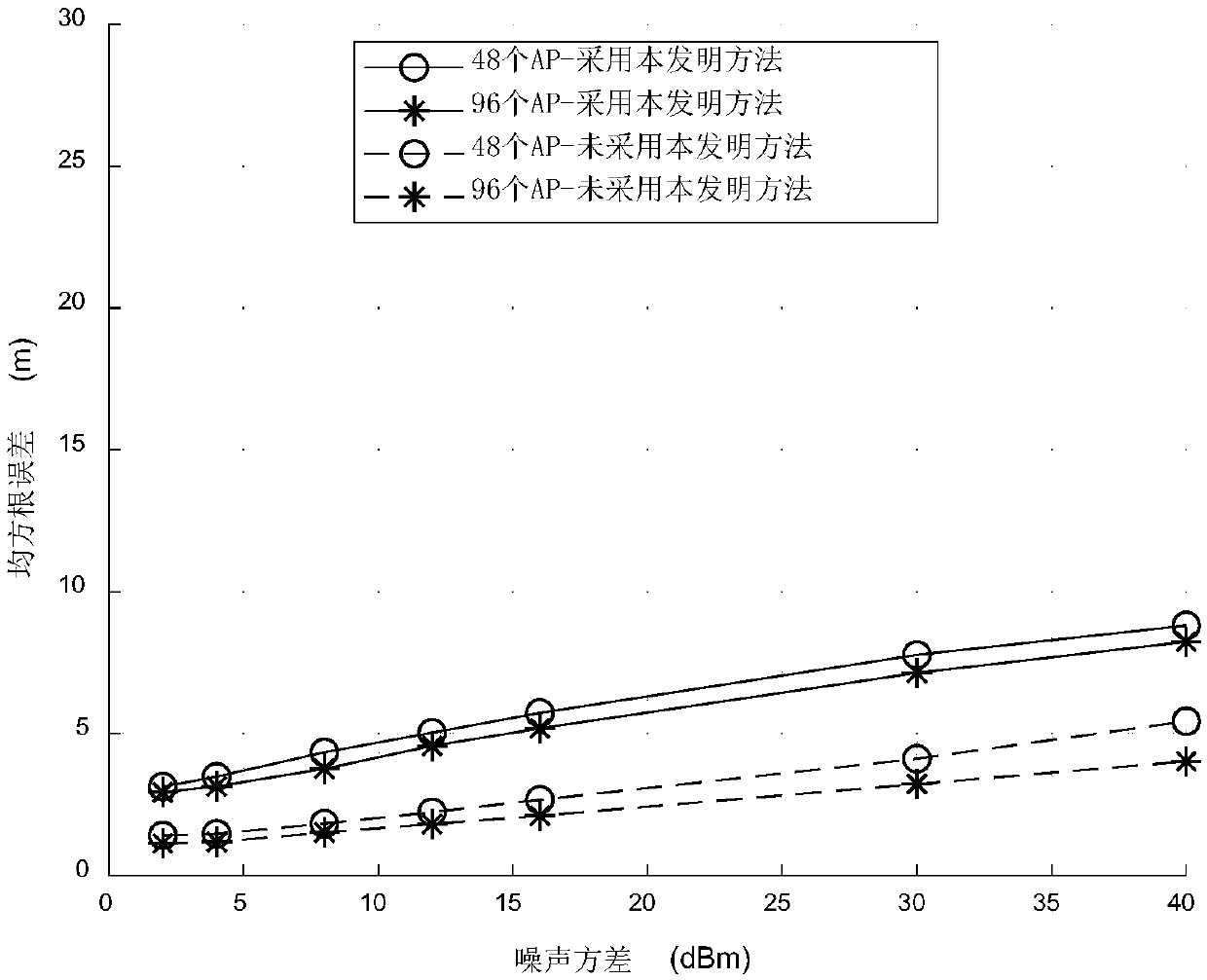
WiFi indoor location method based on iterative partition space method
ActiveCN108989986AImprove robustnessImprove noise immunityParticular environment based servicesUsing reradiationWi-FiSystem maintenance
The invention discloses a WiFi indoor ocation method based on iterative partition space method, which mainly solves that problem of exist Wi Fi positioning technology is inaccurate, the system complexity is high, the dependence on the signal propagation model is high, the method includes: deployment of wireless access point AP, location area rasterization; segmentation of location area; acquiringof positioning data; calculating of the weight of reference point by using similarity beta; determining of a sub-region where the target is located by judging the sub-region weight; target range narrowing Iteration; and target Location. The invention gradually reduces the area where the positioning target is located by the iterative division space method, remove the interference of AP, which is far away from the target and has weak correlation with the positioning target, improves the anti-noise performance, reduces the complexity of the positioning system, reduces the dependence on the signalpropagation model, improves the robustness of the system, ensures the positioning accuracy, and reduces the system maintenance cost. The invention can be used for indoor positioning in a more complexindoor environment.
Owner:XIDIAN UNIV
A method for network intrusion detection and alarm
InactiveCN102281163AClear evaluation criteriaData switching networksRisk evaluationCorrelation attack
Based on the network intrusion detection and alarm method, the IDS alarm information attributes include time stamp, source IP, destination IP, port number, attack type and detector ID, and determine the following basic elements; 1) node and service; 2) node value and service value ;3) node security degree; 4) alarm reliability; 5) alarm risk; The evaluation of the alarm information also needs to evaluate the environmental matching degree of the alarm information, so its algorithm is still multi-layered; 6-1), calculate the environmental matching degree according to the matching degree of known environmental factors; 6-2), use and The method of calculating the matching degree of the environment is the same method to calculate the credibility and danger level and the final alarm threat level; the state of the attack type credibility is divided into three types: high, medium and low, and the values are 1, 0.6, and 0.2 respectively. , the state of the correlation attack is respectively set to three states of strong correlation, weak correlation and no correlation.
Owner:NANJING UNIV +1
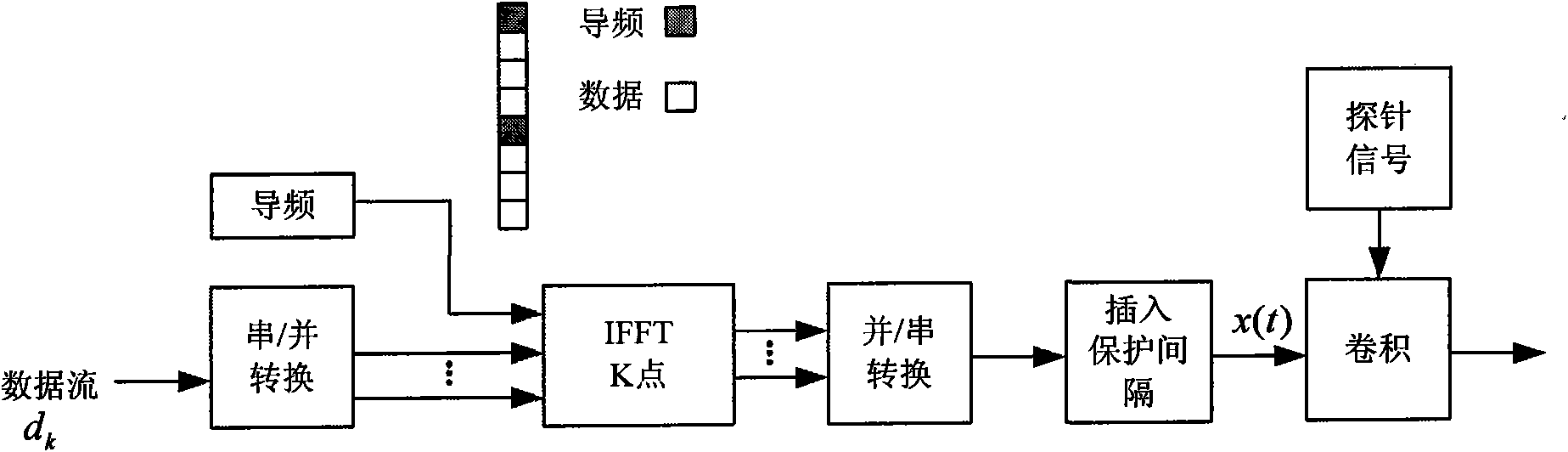
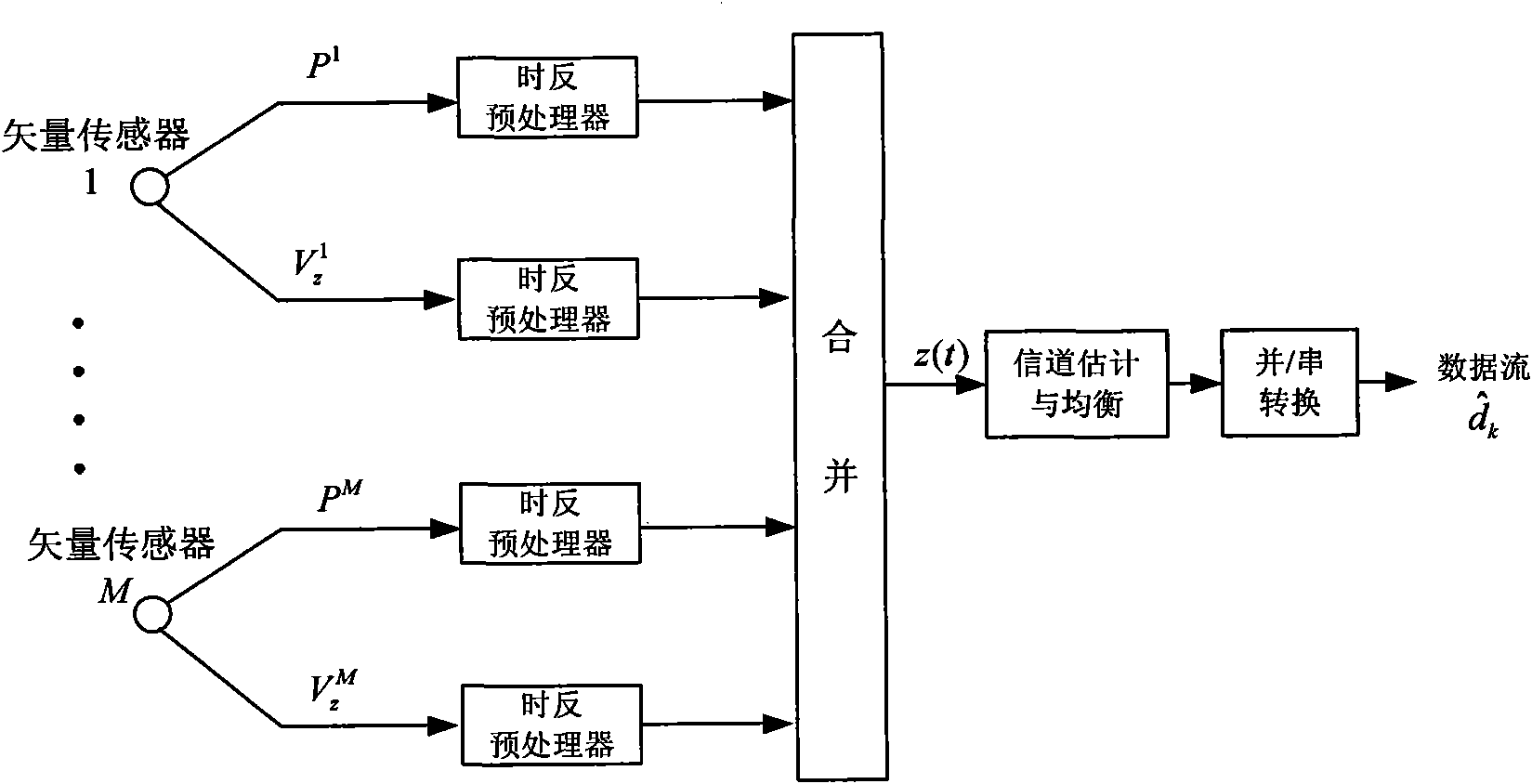
Vector sensor-based orthogonal frequency division multiplexing (OFDM) underwater sound communication method
ActiveCN102025424AImprove communication performanceImprove performanceBaseband system detailsMulti-frequency code systemsVertical vibrationEngineering
The invention discloses a vector sensor-based orthogonal frequency division multiplexing (OFDM) underwater sound communication method, which comprises that: a receiver uses a vertical receiving array consisting of M vector sensors of which each comprises an acoustic pressure channel and at least a vertical vibration velocity channel; after frame synchronizing signals are captured, frequency-domain passive time reversal processing is performed on the acoustic pressure channel and the vertical vibration velocity channel to combine the data of each channel into a path; and OFDM channel estimation and equalization processing are performed to finally recover original information. The vector sensor-based OFDM underwater sound communication method has the advantages that: the vector sensors form the receiver of an OFDM communication system to provide conditions for space diversity required by the time reversal processing by utilizing weak correlation between an acoustic pressure and a vertical vibration velocity component, and the vector sensor array replaces a conventional acoustic pressure array under the condition of the same receiving array size so as to remarkably improve communication performance.
Owner:THE 715TH RES INST OF CHINA SHIPBUILDING IND CORP
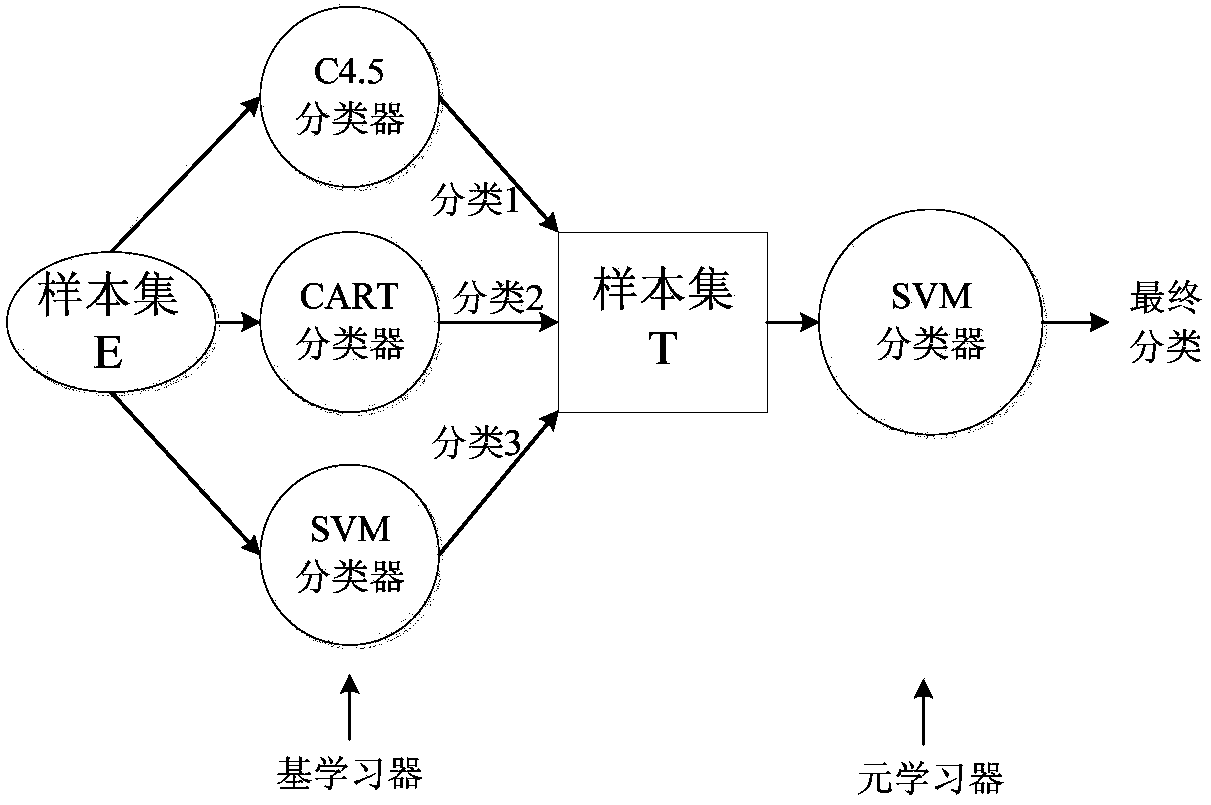
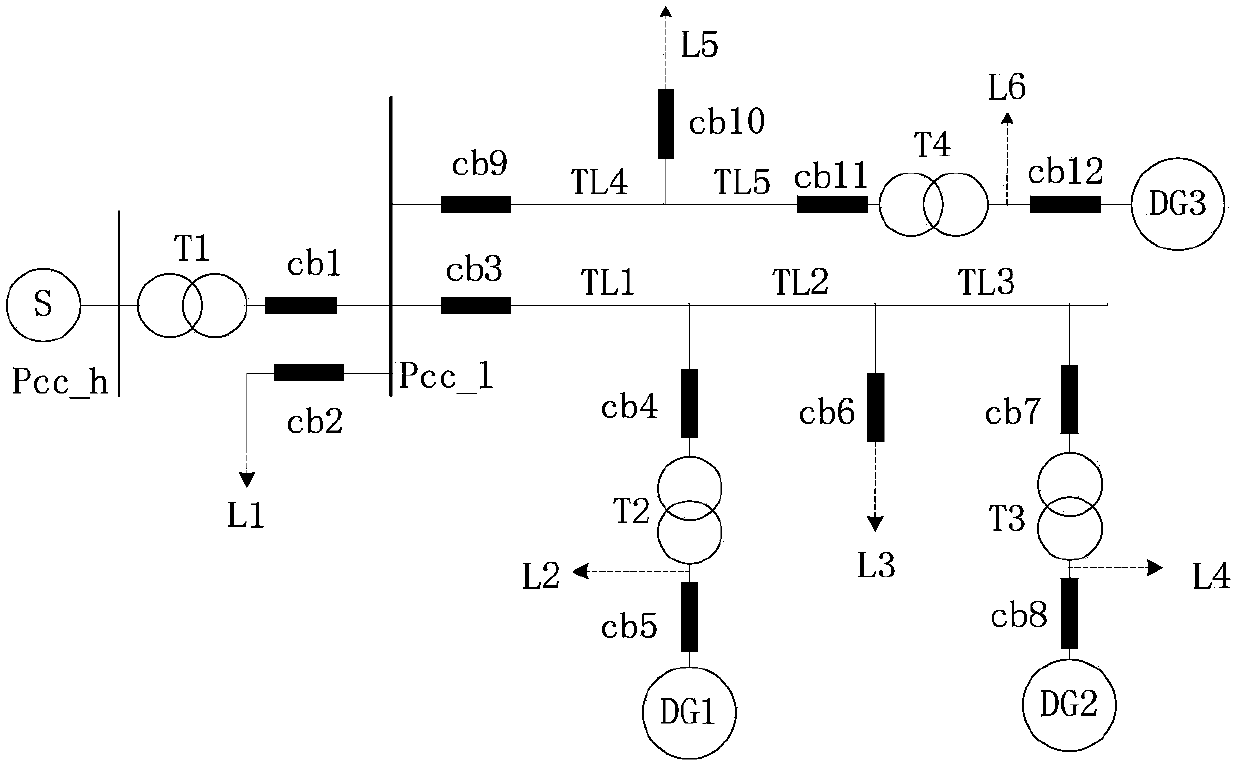
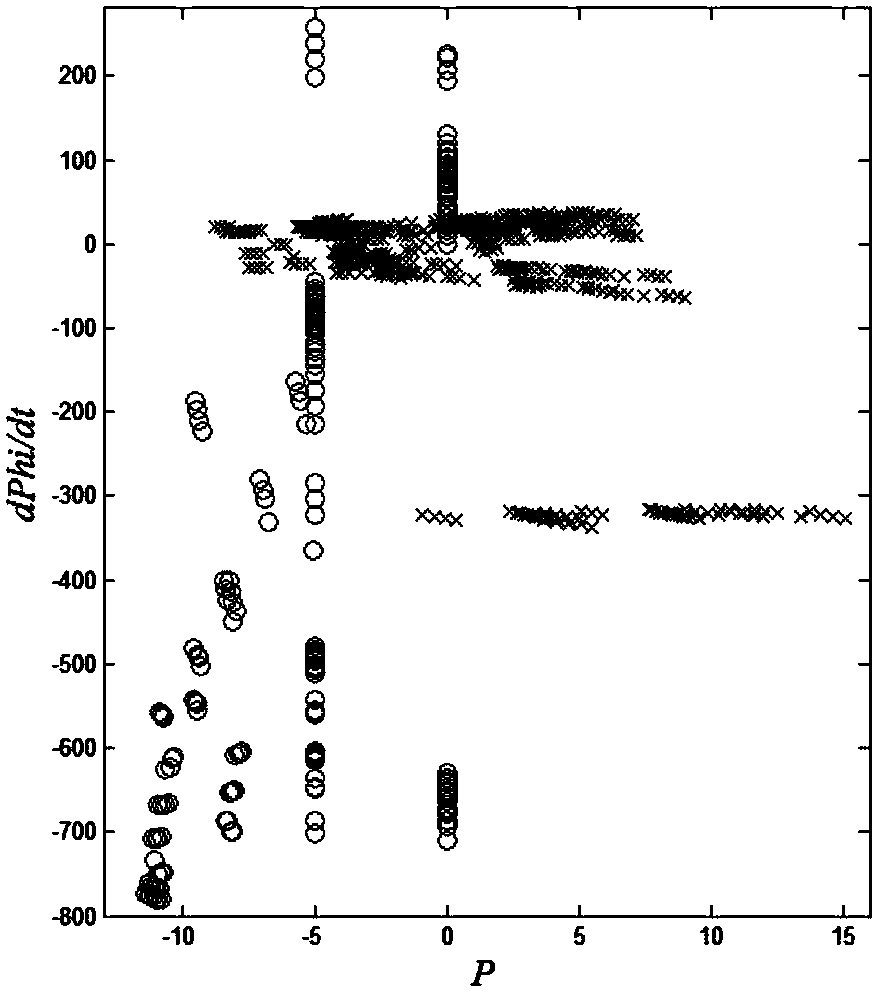
Distributed generation island detection method based on meta learning
InactiveCN103778569ASolve the accuracy problemSolve the problem of overfittingData processing applicationsKnowledge representationIslandingOverfitting
The invention relates to a distributed generation island detection method based on meta learning. The distributed generation island detection method based on meta learning comprises the following steps that (1) key features for island detection are recognized by using an RELIEF algorithm, so that a key feature set is obtained; (2) classification prediction is carried out on the original key feature set through a plurality of basic learning devices; (3) the classification results of the basic learning devices serve as feature items to be added to a training set, and a new sample set T is generated; (4) a meta learning device uses the sample set T as a training set, and carries out relearning on the classification results of the basic learning devices to obtain a final detection result. Compared with the prior art, the distributed generation island detection method based on meta learning solves the problems that due to weak correlation features in samples, accuracy of a classification algorithm can be reduced, and overfitting is caused, and has the advantages of being good in applicability, high in detection accuracy and the like.
Owner:SHANGHAI JIAO TONG UNIV
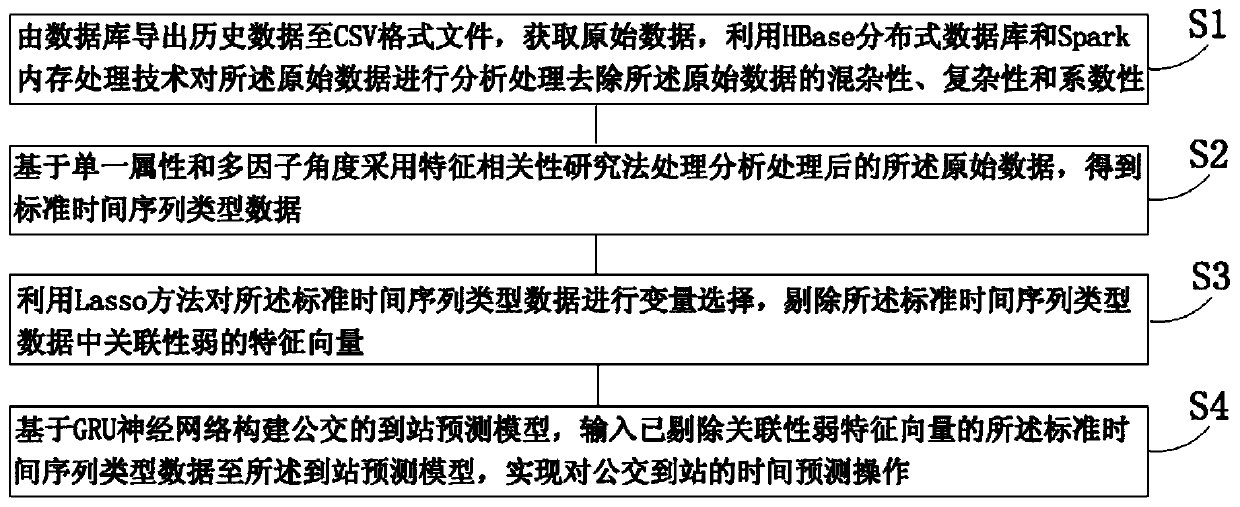
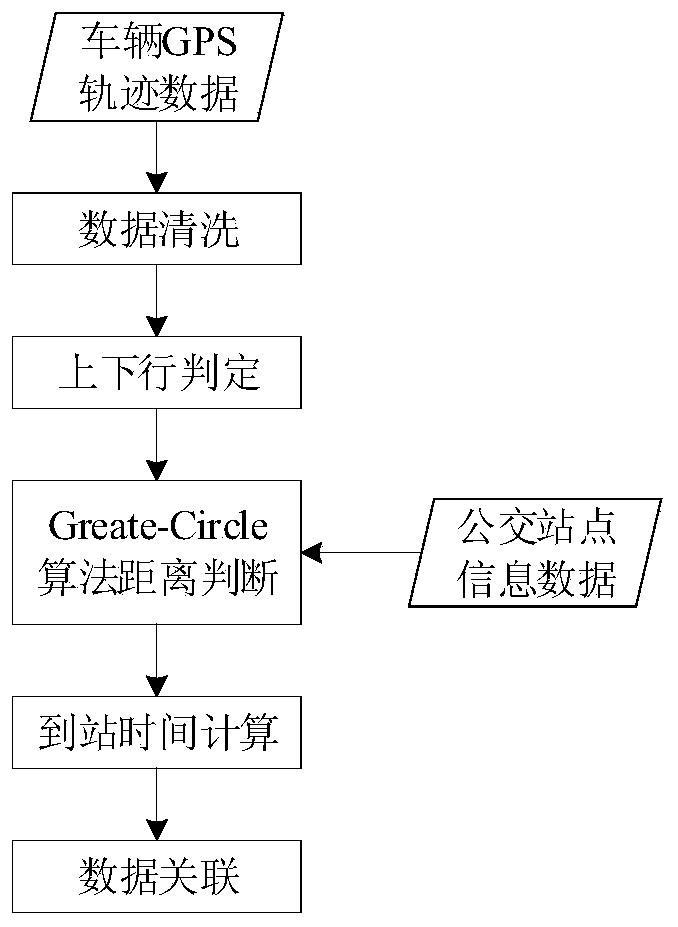
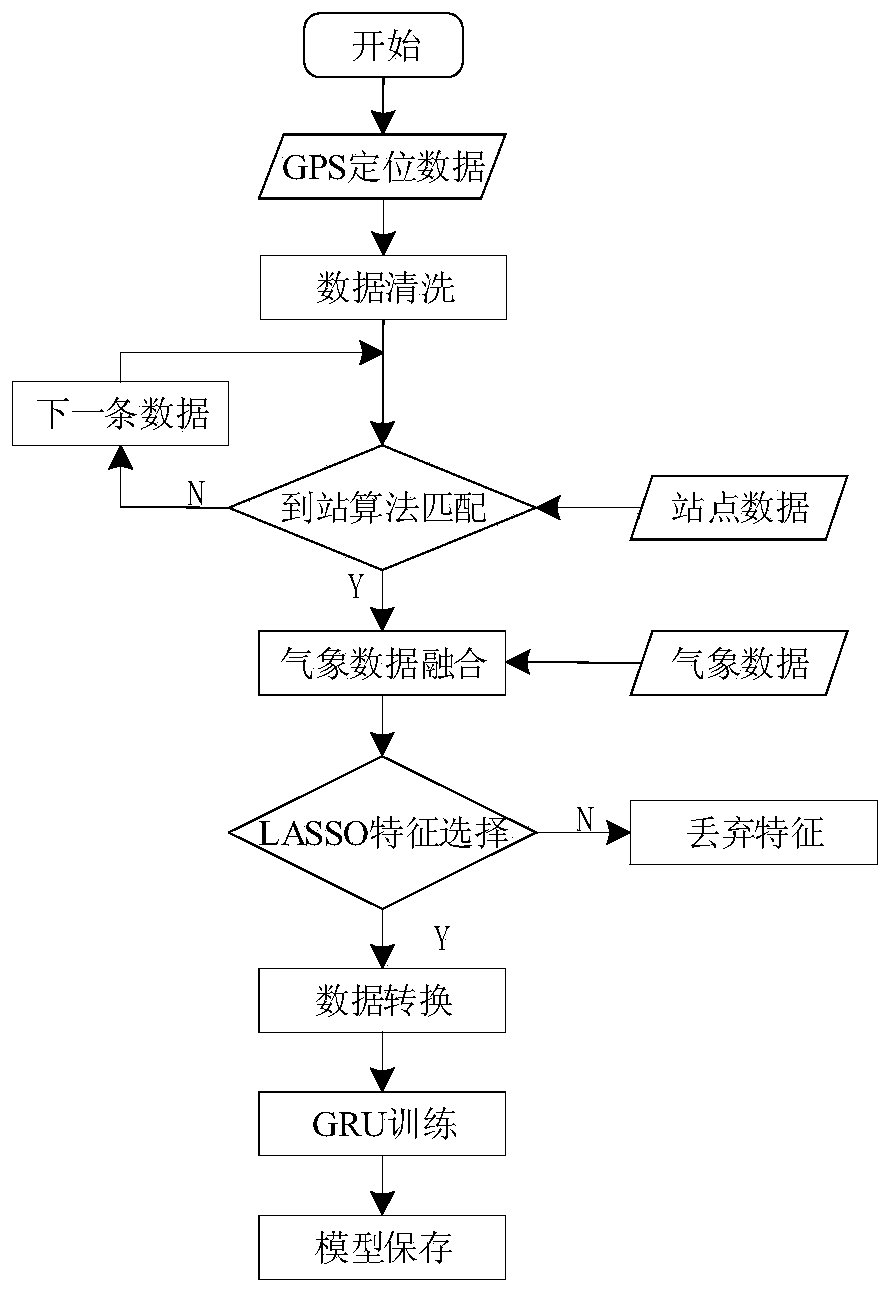
Bus arrival time prediction method based on GRU neural network
ActiveCN109920248AImplement extractionImprove accuracyDetection of traffic movementNeural architecturesOriginal dataAlgorithm
The invention discloses a bus arrival time prediction method based on a GRU neural network. The method comprises: outputting historical data from a database to a CSV format file, acquiring original data, and analyzing the original data by using an HBase distributed database and a Spark memory processing technology to remove hybridity, complexity and coefficient of the original data; on the basis of single attributes and a multi-factor perspective, analyzing and processing the processed original data by using a feature correlation research method to obtain standard time sequence type data; withthe Lasso method, carrying out variable selection on the standard time sequence type data, and rejecting a feature vector with weak correlation in the standard time sequence type data; and constructing a bus arrival prediction model based on a GRU neural network and inputting the standard time sequence type data with the feature vector with weak correlation rejected to the arrival prediction model, thereby realizing bus arrival time prediction operation. Therefore, the accuracy of the bus arrival time prediction is improved effectively.
Owner:NANTONG UNIVERSITY
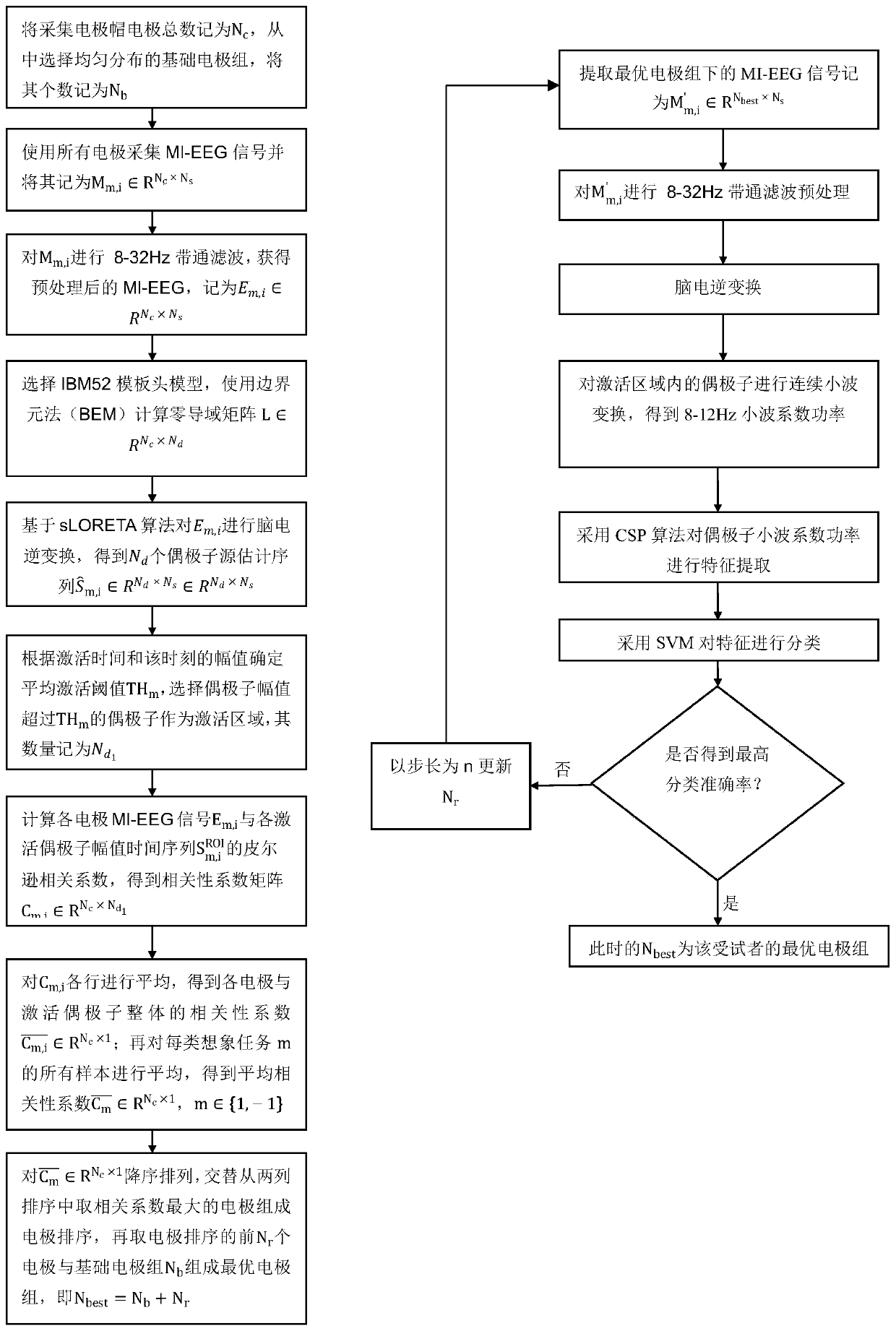
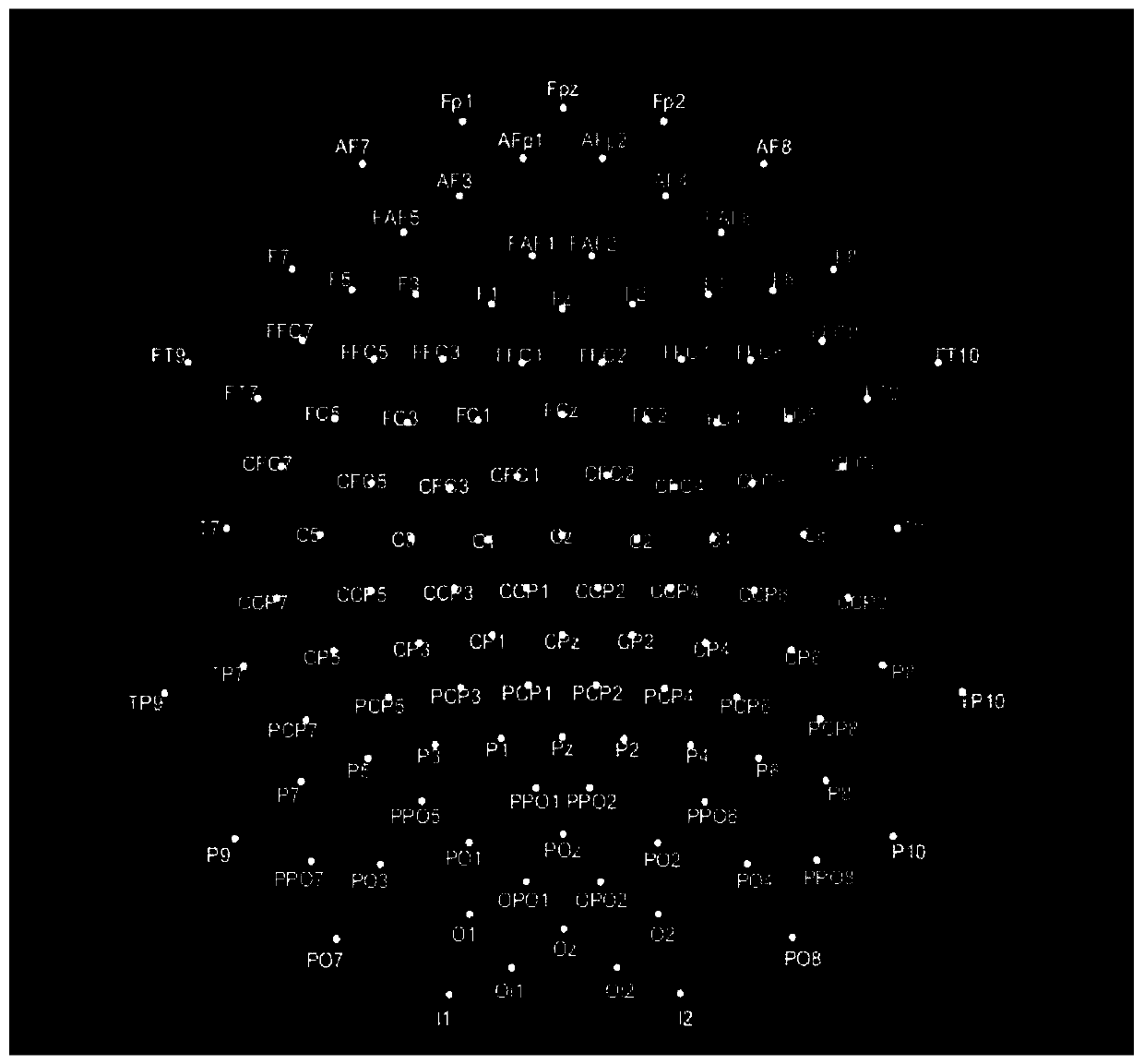
Electrode selection method based on brain-derived imaging and correlation analysis
ActiveCN110584660AFully excavatedImprove missing deficienciesDiagnostic recording/measuringSensorsBand-pass filterPeak value
The invention discloses an electrode selection method based on brain-derived imaging and correlation analysis. The electrode selection method includes the steps that a base electrode set is determinedaccording to initial electrode configuration of an electrode cap; then collected motor imagery electroencephalogram signals are preprocessed by band-pass filtering; then a standardized low-resolutionbrain electromagnetic tomography imaging algorithm is used for brain-derived imaging of MI-EEG, and a time series of a brain-derived domain dipole amplitude is obtained; then according to a dipole amplitude peak of each experiment, a cortical activated area is determined, and the time series of the dipole amplitude in the activated area and Pearson correlation coefficients of the MI-EEG signals of each electrode are calculated and arranged in descending order; and finally, an optimal electrode set is formed by selecting an electrode with a high correlation coefficient to be combined with thebase electrode set. According to the electrode selection method, electrodes with weak correlation with an imaginary task and disadvantageous to classification are excluded, and great significance forimproving the computational efficiency and the experimental convenience is achieved.
Owner:BEIJING UNIV OF TECH
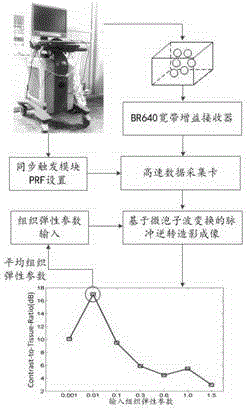
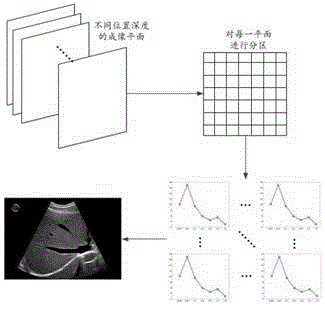
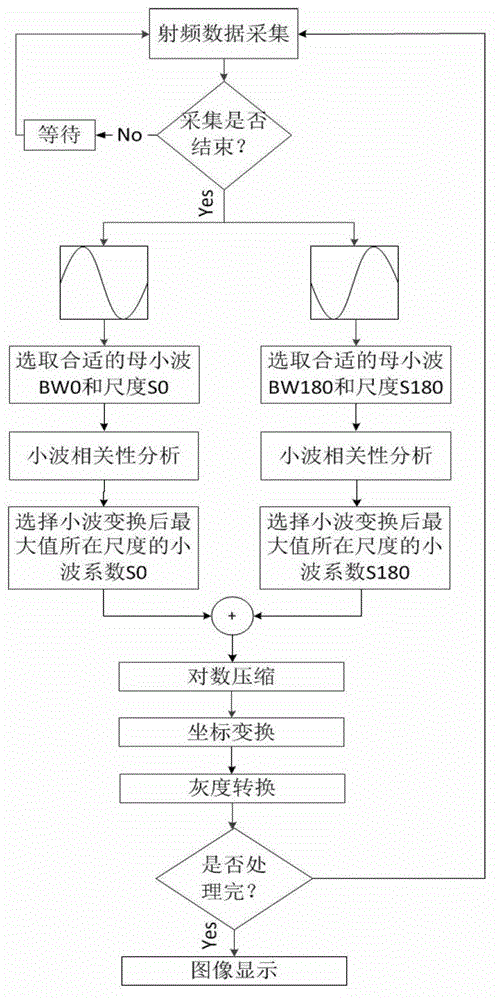
Micro-elasticity imaging method based on tissue microbubble dynamics model
ActiveCN103330576AControl importHigh detection sensitivityOrgan movement/changes detectionUltrasonic/sonic/infrasonic dianostic techniquesSonificationDynamic models
The invention provides a micro-elasticity imaging method based on a tissue microbubble dynamics model. According to the invention, a mother wavelet which has strong correlation with a microbubble signal and weak correlation with a tissue signal is established according to that microbubble vibration is influenced by characteristics of a surrounding tissue, and a tissue microbubble dynamics model can be used for establishing the relation of a microbubble vibration signal and tissue elasticity, the microbubble signal is detected for imaging through a pulse inversion and wavelet transform combined imaging algorithm, and when the detection signal is the closest to a model signal, the maximum tissue contrast ratio can be obtained, so that the elasticity parameters of the tissue within the range of a dozen to tens of microns around the tissue are obtained in a reverse derivation manner. The method can be applied to real-time monitoring on a high-intensity focused ultrasound therapeutic process and elasticity detection of a biological thin-layer tissue, can overcome the limitations that the general elasticity imaging requires external pressure, and is influenced by boundary conditions easily, and effectively improves the imaging resolution to the micron level from the millimeter level.
Owner:XI AN JIAOTONG UNIV
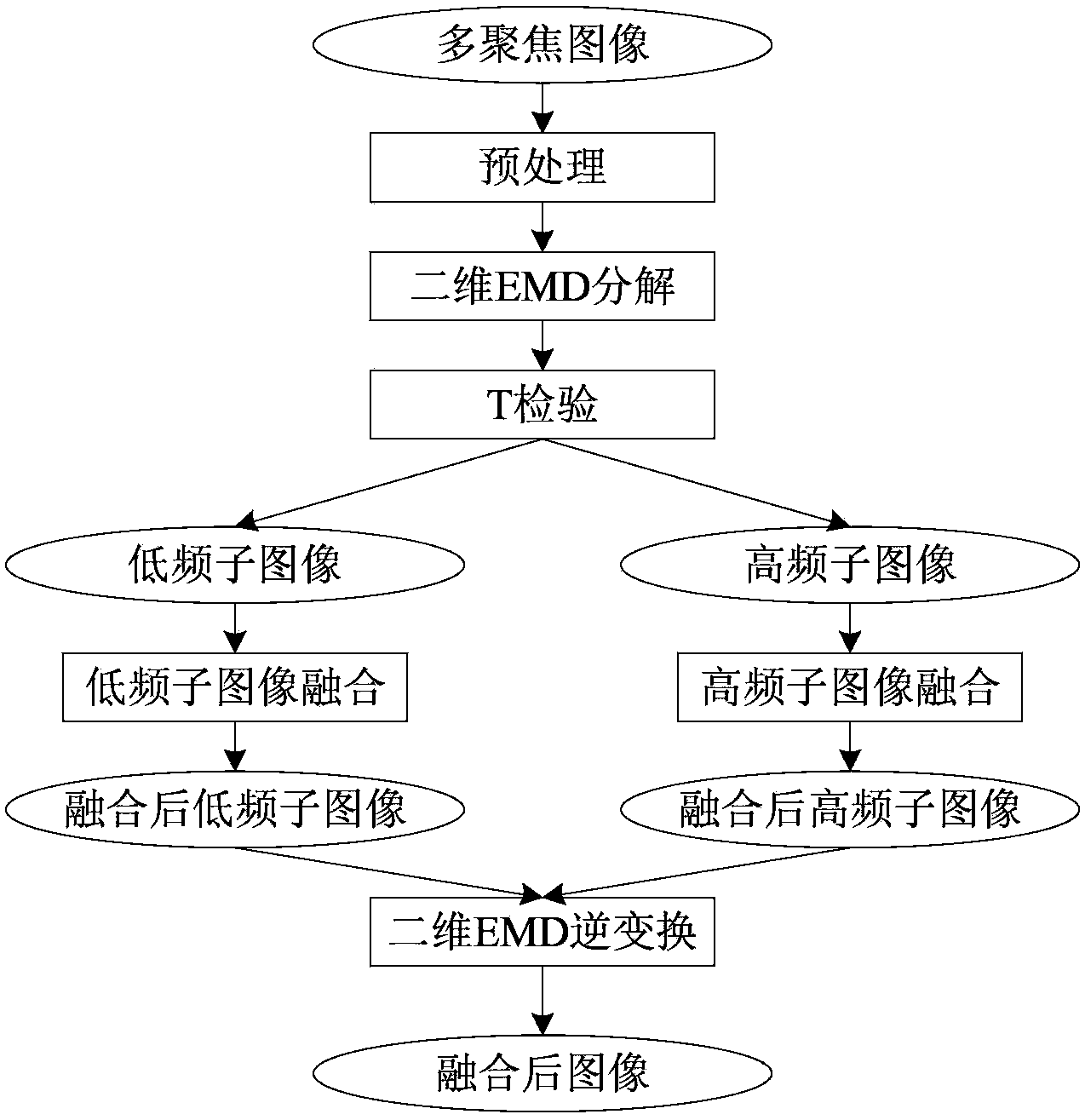
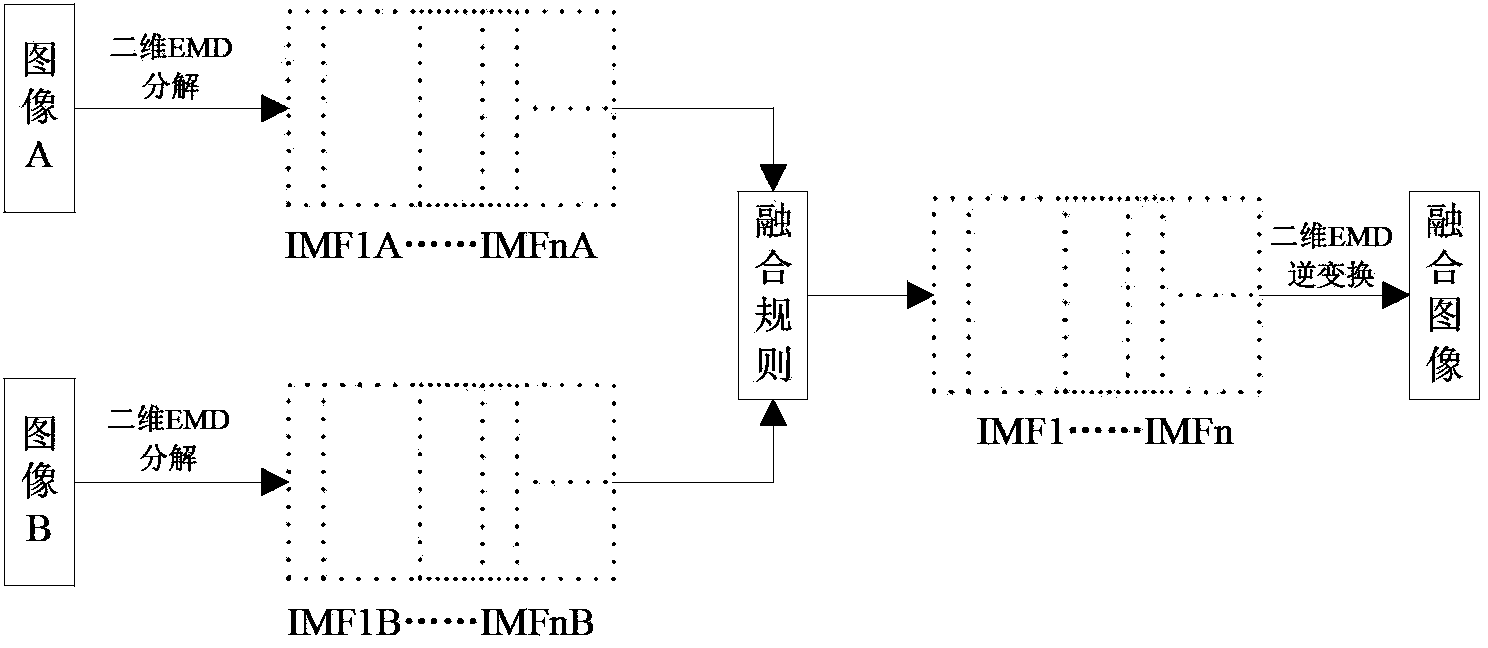
Multi-focus image fusion method based on two-dimensional empirical mode decomposition (EMD) and genetic algorithm
InactiveCN103413284AQuality improvementAvoid choosing difficult questionsImage enhancementDecompositionGenetic algorithm
The invention relates to a multi-focus image fusion method based on two-dimensional empirical mode decomposition (EMD) and a genetic algorithm. At first, two-dimensional empirical mode decomposition (EMD) is performed on a source image, and therefore, the problem of weak correlation of local features of image fusion based on wavelet transform can be solved, and the problem of difficulty in wavelet basis function selection in a traditional wavelet method can be solved; high / low frequency selection is performed on obtained intrinsic mode function (IMF) components according to T-test, and then, fusion is performed on low-frequency components through adopting a regional information entropy maximum criterion, and regional correlation calculation is performed on high-frequency components, and components of which the correlations are in different threshold ranges are fused, and the selection of thresholds is searched through adopting the genetic algorithm, and therefore, the defects of experience determination of regional matching thresholds can be avoided; and finally, two-dimensional empirical mode decomposition (EMD) inverse transformation is performed on fused components so as to obtain fusion results. Thus, based on the combination of the two-dimensional empirical mode decomposition (EMD) and the genetic algorithm, and the multi-focus image fusion method can greatly improve the quality of fused images and has important significance and great use value in subsequent processing and image display of an application system.
Owner:NORTHWESTERN POLYTECHNICAL UNIV
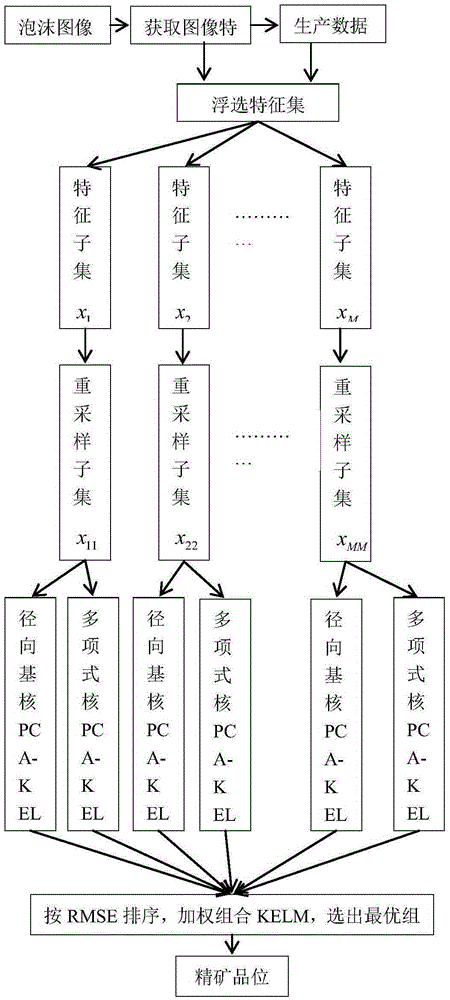
Antimony ore grade soft-measurement method based on selective fusion of heterogeneous classifier
ActiveCN105260805ASolve the problem of difficult online detectionSolve redundancyForecastingModel compositionOptimal weight
The invention provides an antimony ore grade soft-measurement method based on the selective fusion of a heterogeneous classifier. The method comprises the step of together forming a feature space based on the pretreatment of antimony flotation froth image feature data and production data related to the grade of the antimony ore. According to the method, firstly, some feathers are randomly selected to form a plurality of sub-sample spaces. Secondly, a plurality of different sub-samples in each sub-sample space are sampled through the bootstrap sampling process. At the same time, the PCA analysis is conducted on each sub-sample to obtain key features that are high in sensitivity to grade change and free of / weak in dependency. Thirdly, two KELMs are conducted respectively for each sub-sample set to construct a candidate sub-model, based on an RBF kernal of better learning ability and a polynomial kernel type KELM of better generalization ability. Fourthly, each candidate sub-model is endowed with a weight based on the method of information entropy. Finally, all candidate sub-models are sorted from small to large based on the RMSE, and then an optimal weighted sub-model combination is selected as a final model for the prediction on the grade of the antimony ore.
Owner:CENT SOUTH UNIV
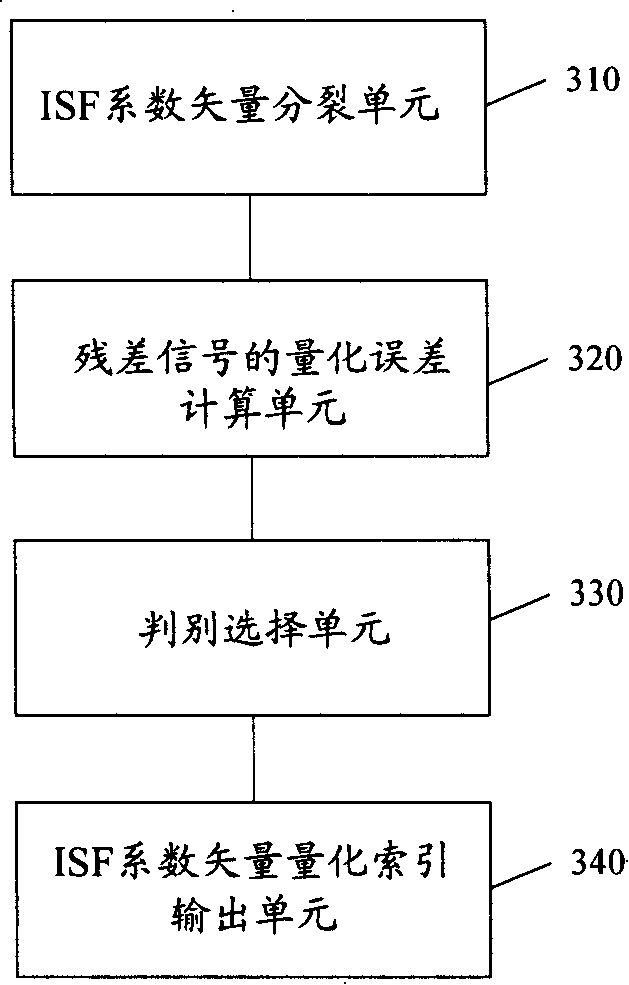
Method and device for selecting conductivity coefficient vector quantization
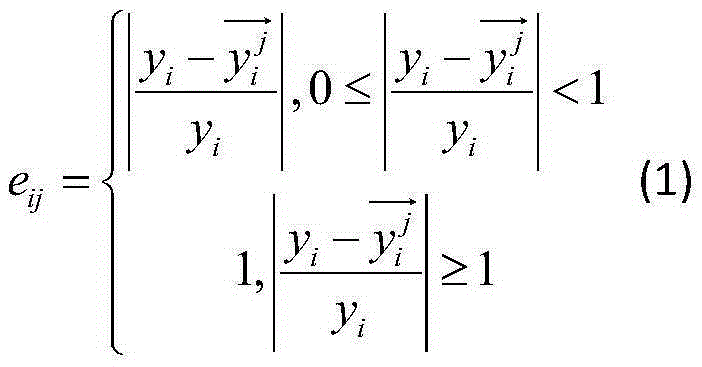
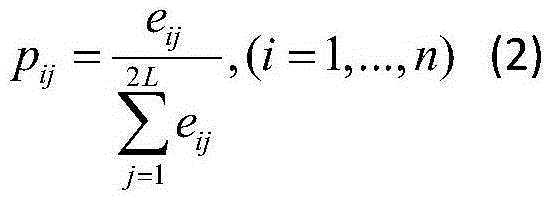
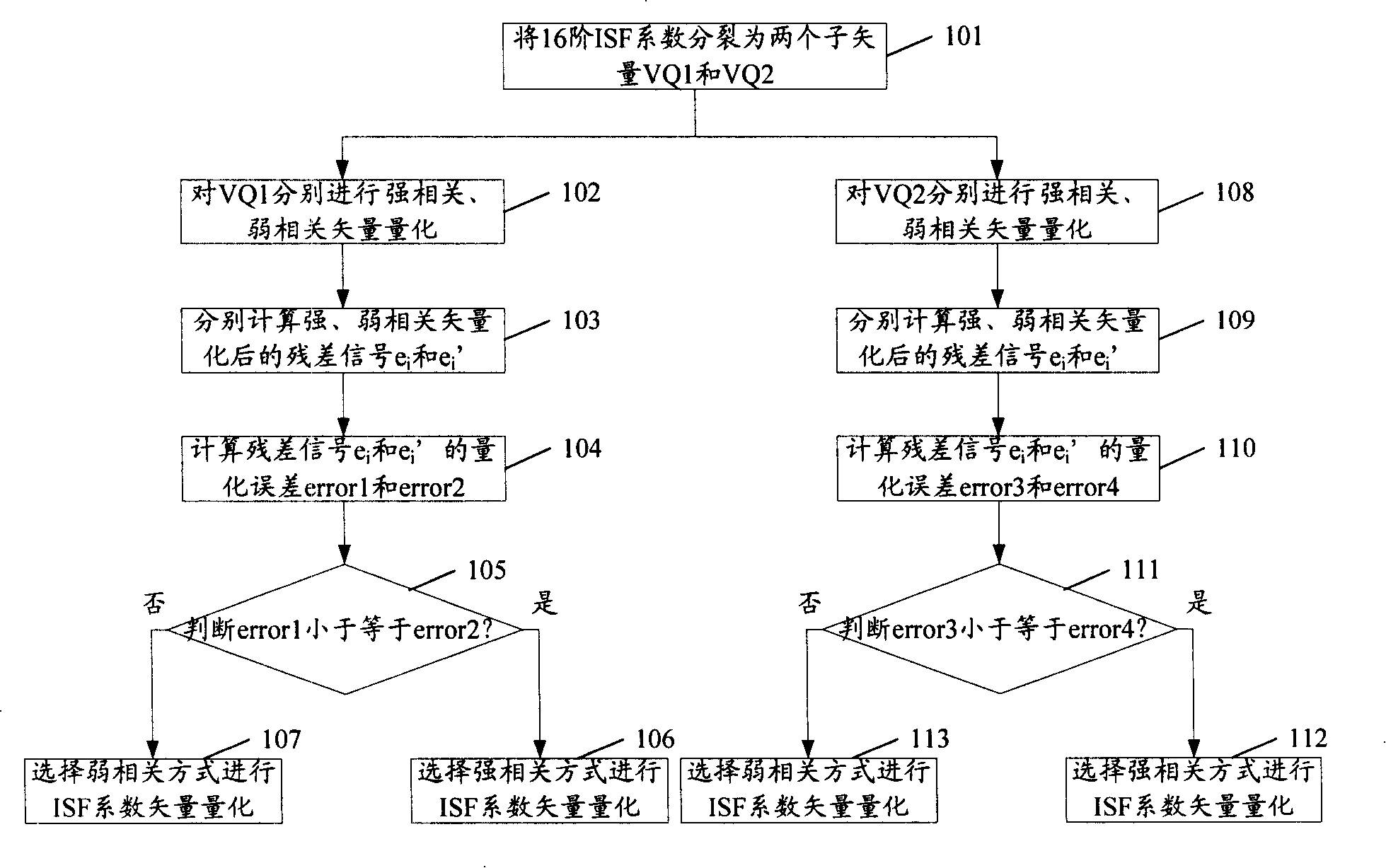
InactiveCN101192408AHigh quantitative accuracyReduced dynamic rangeSpeech analysisTime correlationBroadband
The invention discloses a method and a device for quantifying the vectors of the induced spectrum frequency (ISF) coefficients, which includes the steps as follows: the ISF coefficients are divided into at least two groups of sub-vectors; the inter-frame strong- and weak-correlation vectors of the induced spectrum are quantified for each group of sub-vectors; the residual signals are calculated after the strong- and weak-correlation vectors are quantified; the quantification errors of the above residual signals are also calculated; the quantification errors of the strong- and weak-correlation residual signals are judged for each group of sub-vectors; and the ISF coefficient vectors of the correlation manner with less quantification error in each group are quantified. The invention is based on the short-time correlation and the long-time correlation of the induced spectrum frequency coefficients, and different forecast coefficients are hereby applied to different dimension of the induced spectrum frequency coefficients, thus increasing forecast gains, narrowing the variation range of the residual signals, enhancing the accuracy for the ISF coefficients quantification, achieving clear quantification, and improving the quality for broadband phonetic coding.
Owner:HUAWEI TECH CO LTD +1
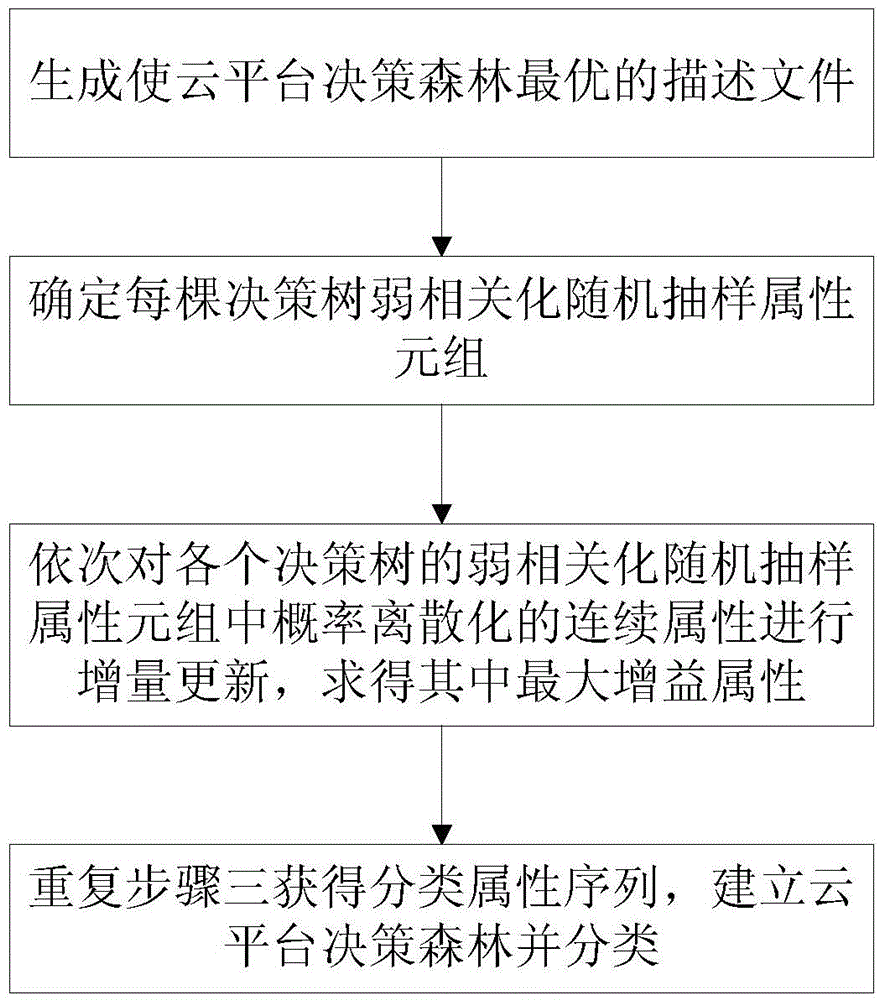
Cloud platform decision forest classification method based on discrete weak correlation
ActiveCN104679911AShorten the timeReduce excess spaceSpecial data processing applicationsClassification methodsDecision taking
The invention discloses a cloud platform decision forest classification method based on discrete weak correlation, which is used for weak correlation of a decision forest classification method of a cloud platform. The method comprises the steps of selecting a random sampling attribute element group according to correlation degree of data attributes, updating the continuous attribute of the probability discretion of the attribute group in a gain manner, and solving a maximum gain attribute; and finally establishing a cloud platform decision forest by virtue of an acquired classification attribute sequence. When a great amount data is processed, the time and space expenditure for establishing the cloud platform decision forest can be reduced, the capability and stability for resisting the data noise can be improved, and the classification prediction speed and the classification quality can be improved.
Owner:武汉理工数字传播工程有限公司