Patents
Literature
269 results about "Collision resistance" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
Collision resistance is a property of cryptographic hash functions: a hash function H is collision resistant if it is hard to find two inputs that hash to the same output; that is, two inputs a and b such that H(a) = H(b), and a ≠ b. Every hash function with more inputs than outputs will necessarily have collisions. Consider a hash function such as SHA-256 that produces 256 bits of output from a large input (≤ 2⁶⁴-1 bits).
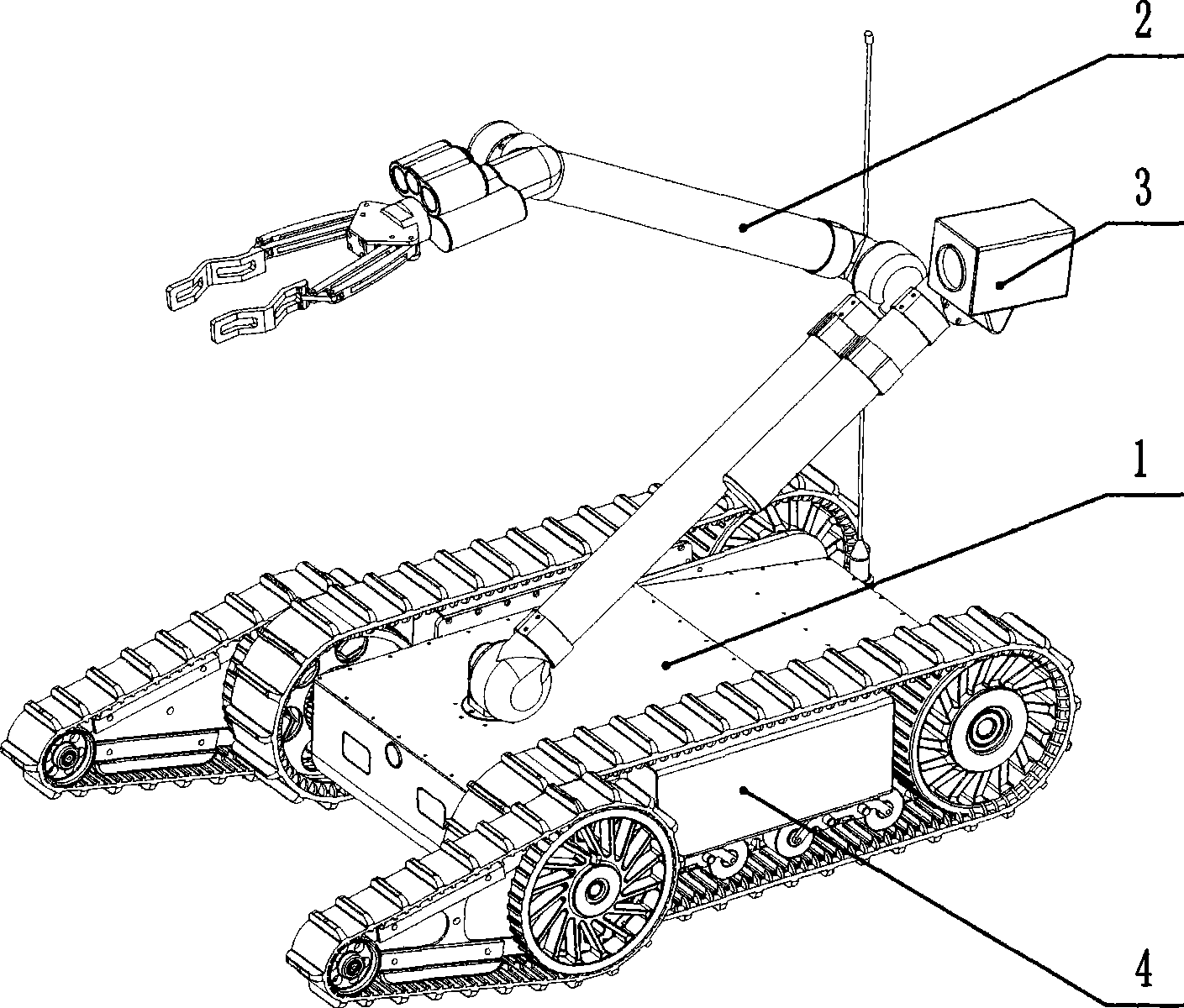
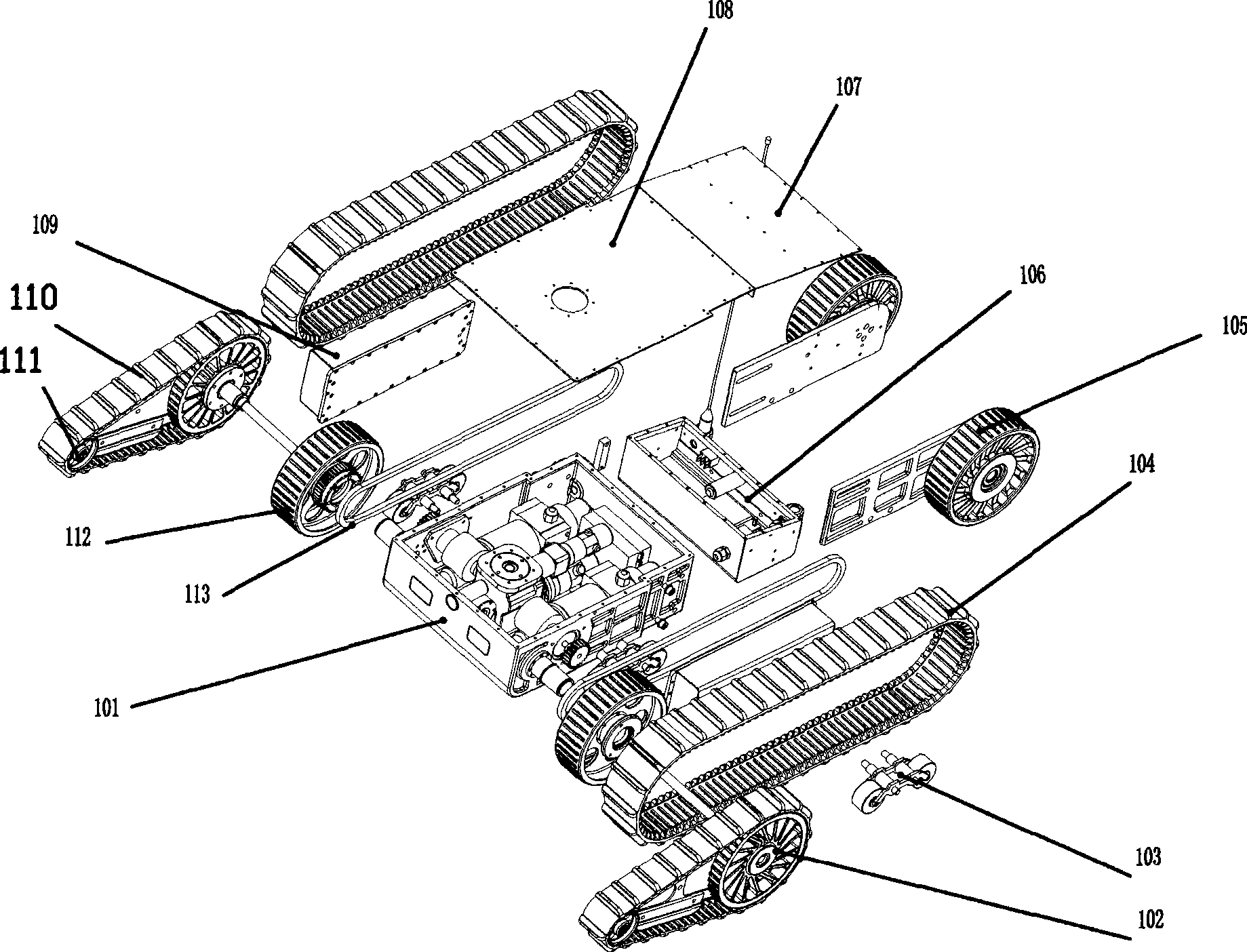
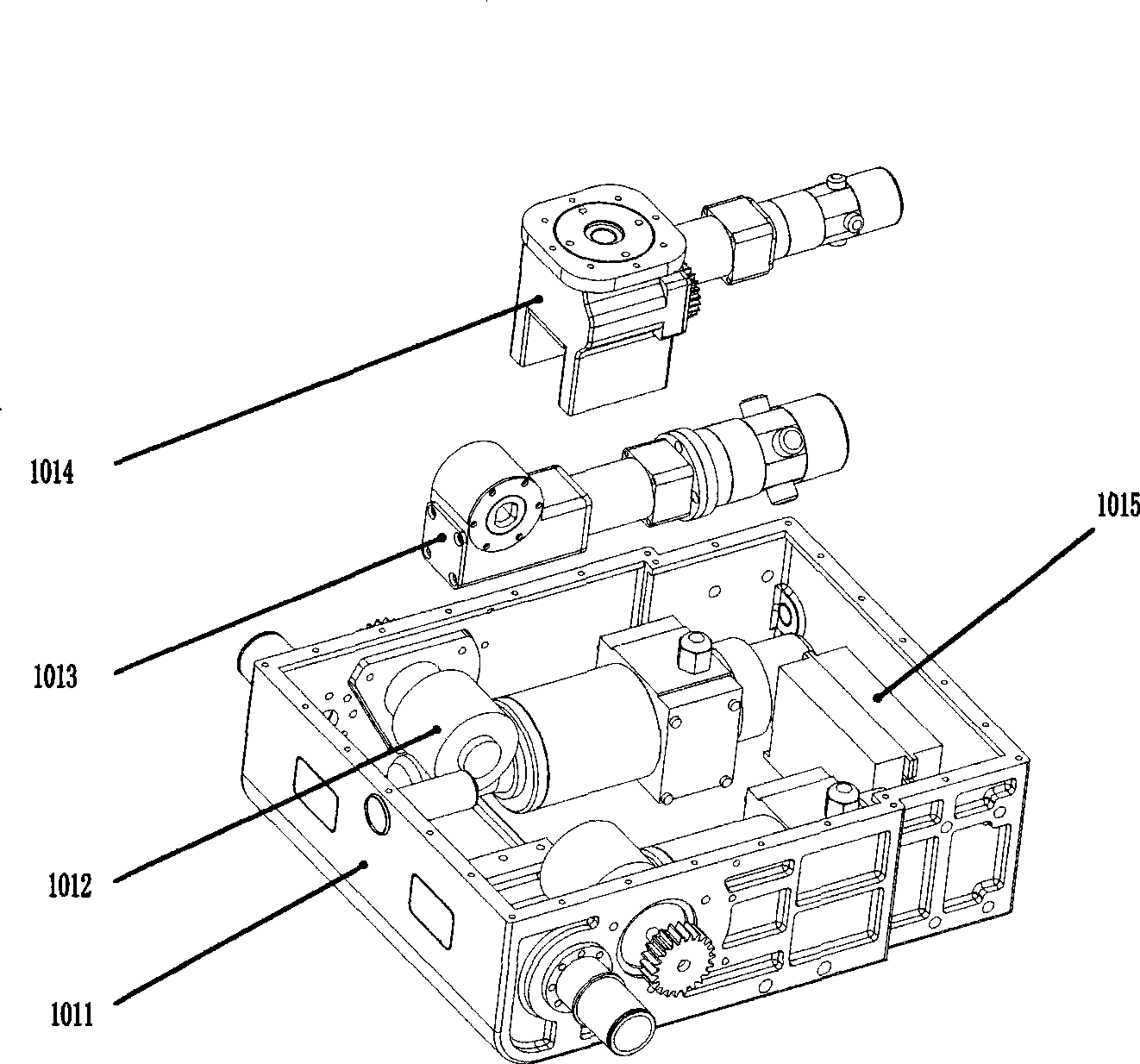
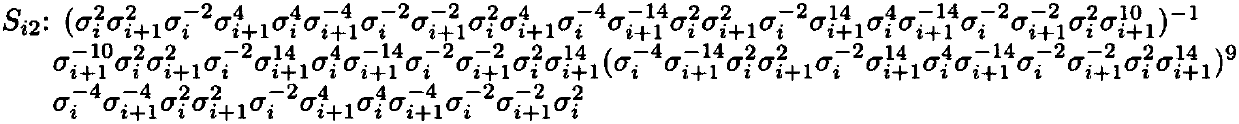
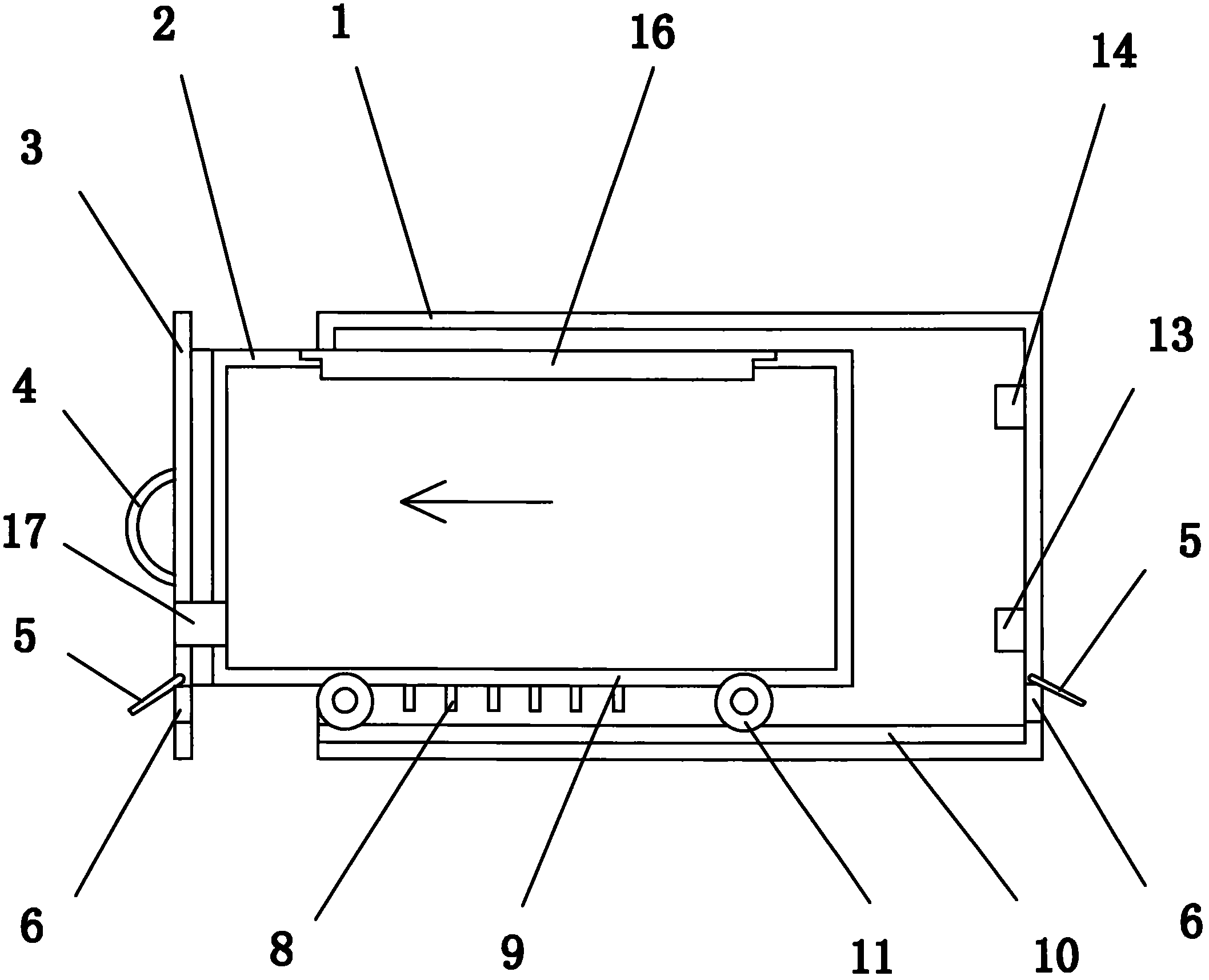
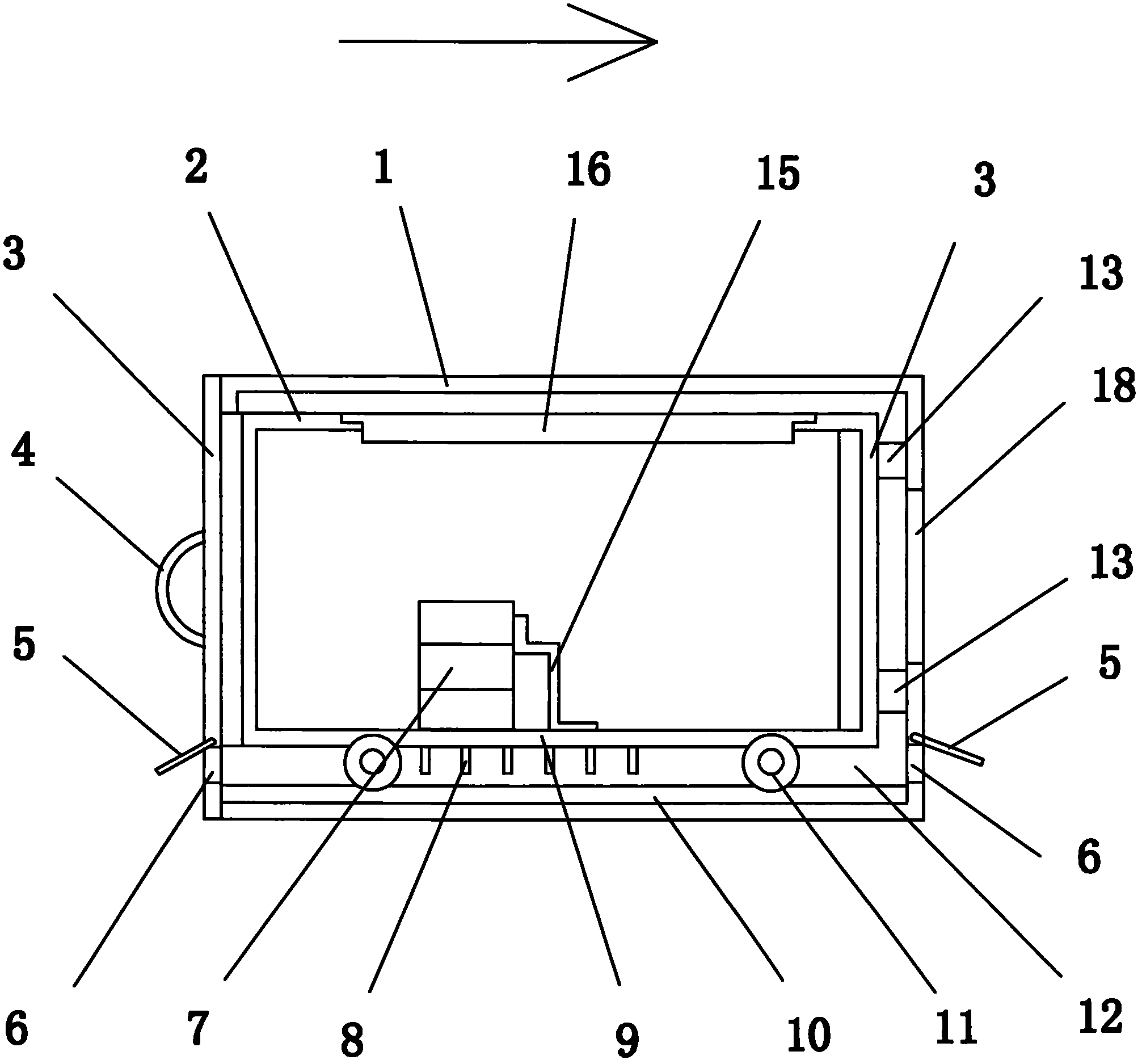
Miniature self-service ground robot
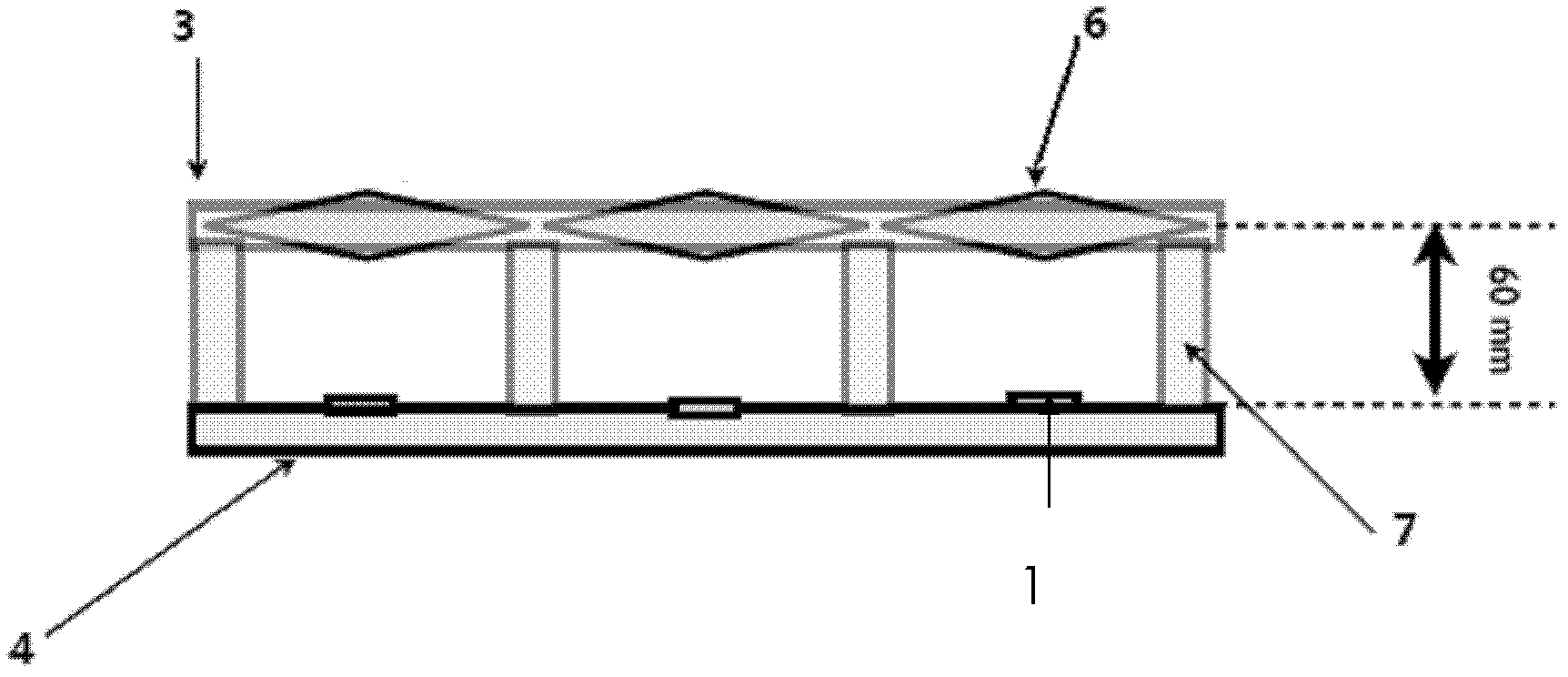
InactiveCN101367207AImprove passabilityImprove reliabilityGripping headsVehiclesRobotic armAbsorbed energy
The invention relates to a small unmanned ground robot which is characterized by comprising a traveling drive mechanism, an arm mechanism, a camera tripod head pat, a carrier frame of the robot, and a control module, wherein the traveling drive mechanism is fixed on the carrier frame of the robot; the arm mechanism is arranged on the traveling drive mechanism in a detachable mode; the camera tripod head part is arranged on the arm mechanism in a detachable mode; and the control module is separated from the robot to control various complicated actions of the robot. The small unmanned ground robot has the advantages that the traveling drive mechanism of the robot adopts a track mode to increase the adhesive force with the ground; track wheels adopt the design of absorbing energy and vibration to improve the capacity of collision resistance of the robot; detachable front auxiliary wheels adopt a track structure to improve trafficability performance of the robot, and have the functions of assisting spanning entrenchments and obstacles, assisting climbing stairs, and rotating and turning over; mechanical arms adopt six freedom of motion, have the characteristics of flexibility, convenience, reliability, strong working capability, and the like, and can grab and carry objects; the robot adopts the design of no exposed skinned wires and water resistance and can work all day long; and the traveling drive mechanism can walk in water.
Owner:郭长青
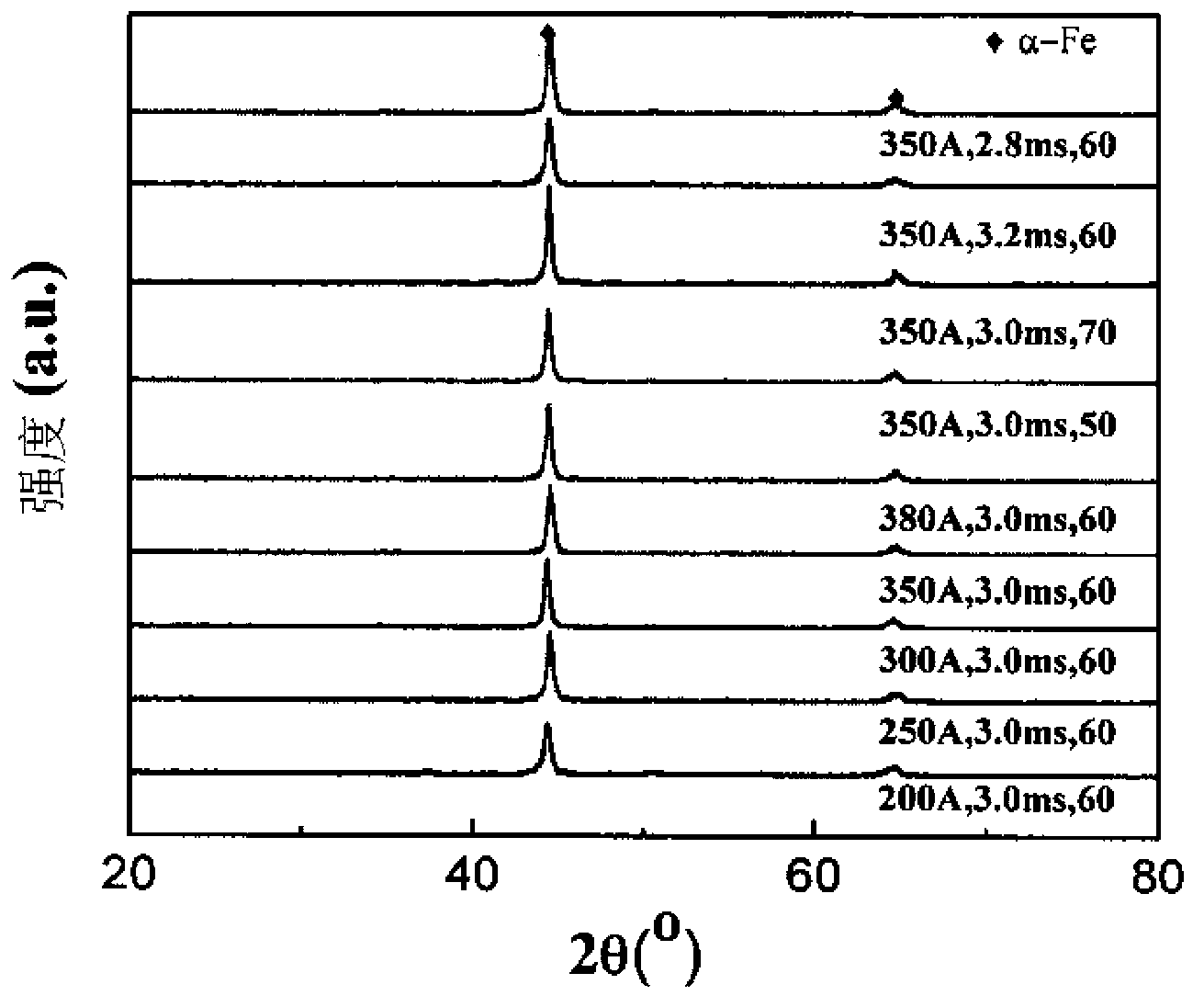
Iron-based amorphous powder for wear-resisting and corrosion-resisting coating and preparation method thereof
InactiveCN103302287AImprove wear and corrosion resistanceWear and corrosion resistance and long service lifeMetallic material coating processesSurface engineeringThermal spraying
The invention discloses iron-based amorphous powder for wear-resisting and corrosion-resisting coating and a preparation method thereof, and belongs to the technical field of surface engineering. Iron-based amorphous alloy coating adopts iron as a main component, and also comprises amorphous phase (in at least 30 percent by volume), and the representation formula of all elements in percentage by weight is FeaCrbNicSidBeMnfCgMohNbiCujCokRel. The powder is prepared through direct ball-milling mixing in proportion of all components according to the required weight ratio. The powder can be used for not only laser cladding but also thermal spraying technology, mixed powder is melt by high-energy density laser beams, an iron-based amorphous or amorphous composite cladding layer is formed on the outer surface of a matrix, the cladding layer has the characteristics of higher wear and collision resistance, the dilution rate is low, the wear-resisting and collision-resisting service lives of a petroleum drill rod, an air compressor screw rod, a roller, a water-cooled wall pipe and an economizer pipe are remarkably prolonged, the process is simpler, and the manufacturing cost is low.
Owner:NORTH CHINA ELECTRIC POWER UNIV (BAODING) +1
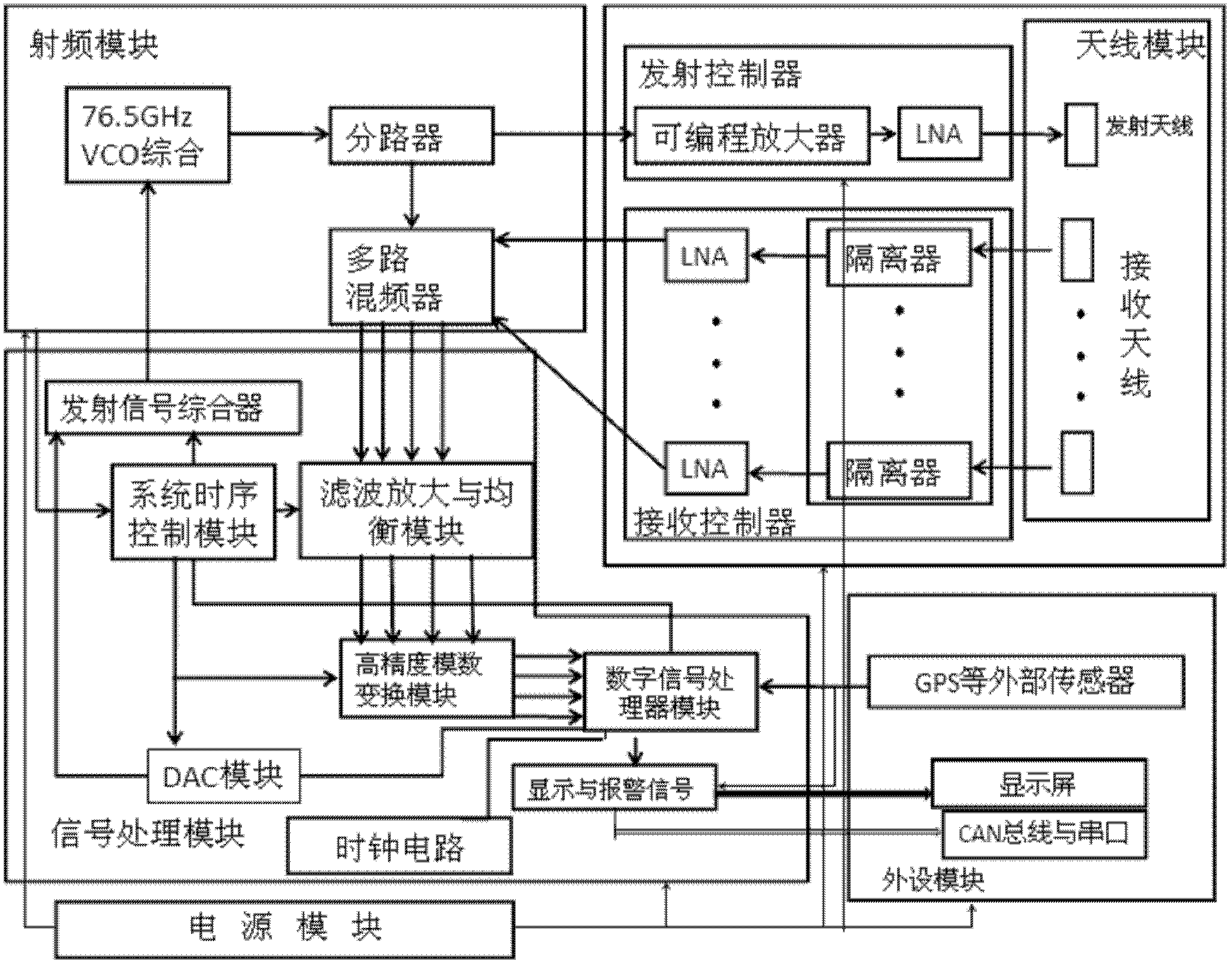
77GHz millimeter wave radar transmit-receive device for automobile collision resistance
InactiveCN102435981AOvercome interlock-prone situationsReliable Guaranteed StabilityWave based measurement systemsRadar systemsSystem stability
The invention, which belongs to the radar communication technology field, relates to an automobile anti-collision radar system, especially to a 77GHz millimeter wave radar transmit-receive device for automobile collision resistance. The device particularly comprises an antenna module, a radio frequency module, a signal processing module, a peripheral module and a power supply module. A signal emission synthesizer and a filter amplification and equalization module of the signal processing module are connected with the radio frequency module. A demultiplexer of the radio frequency module is connected with an emission controller of the antenna module; and a multipath mixer of the radio frequency module is connected with a reception controller of the antenna module. And a display and alarming signal module and a digital signal processor module are respectively connected with the peripheral module. The antenna module employs a mode combining a lens and an antenna as well as the system works at a frequency range of a 77GHz millimeter wave, so that the system stability and the sensitivity precision can be reliably ensured. The signal processing module enables accuracy of sampling data to be ensured and a dynamic rang of a signal to be effectively improved. And an integrated module assembly is employed to design the radio frequency module, so that high precision angle measurement and rapid switching of the reception antenna are realized.
Owner:BEIJING INSTITUTE OF TECHNOLOGYGY +2
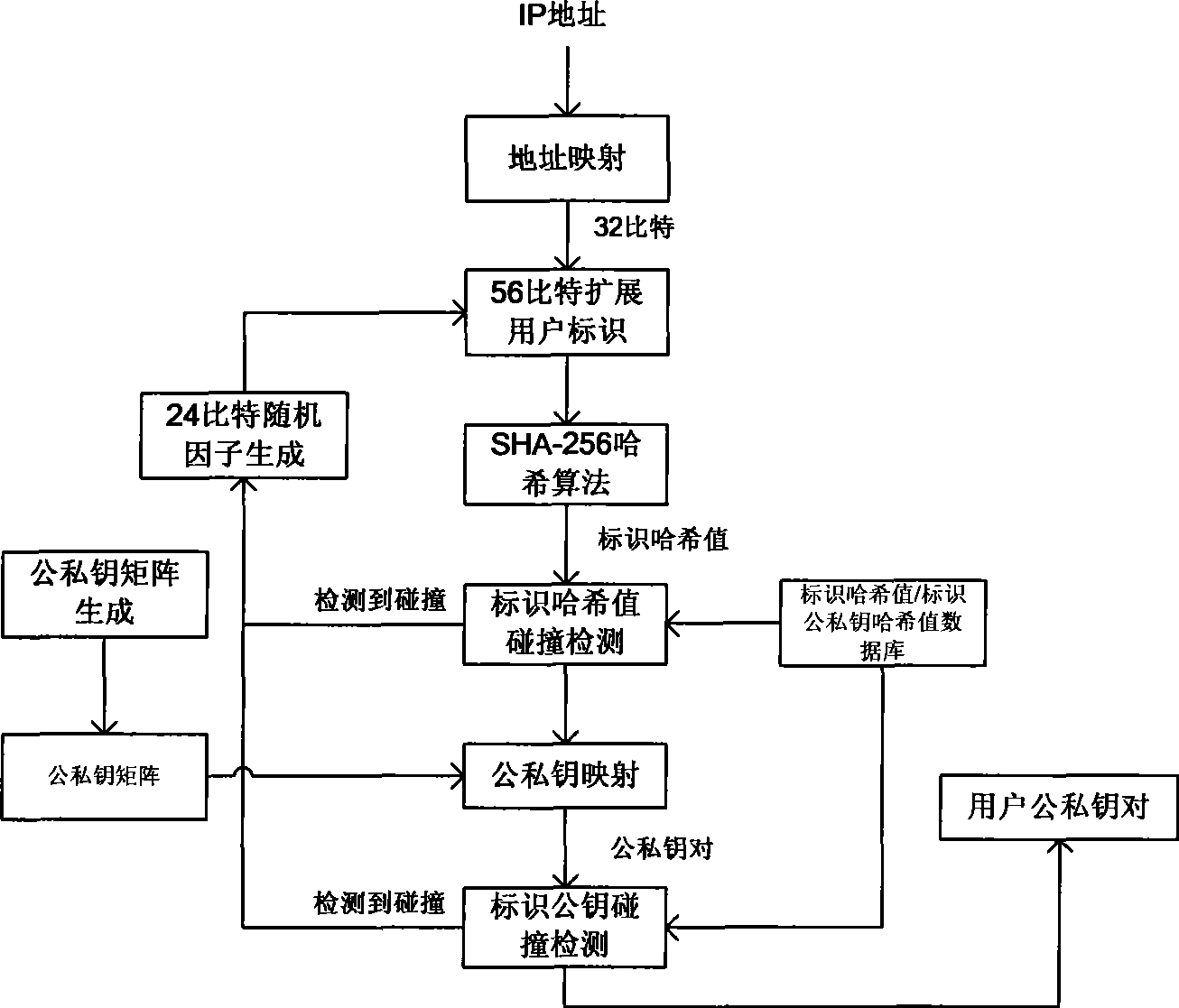
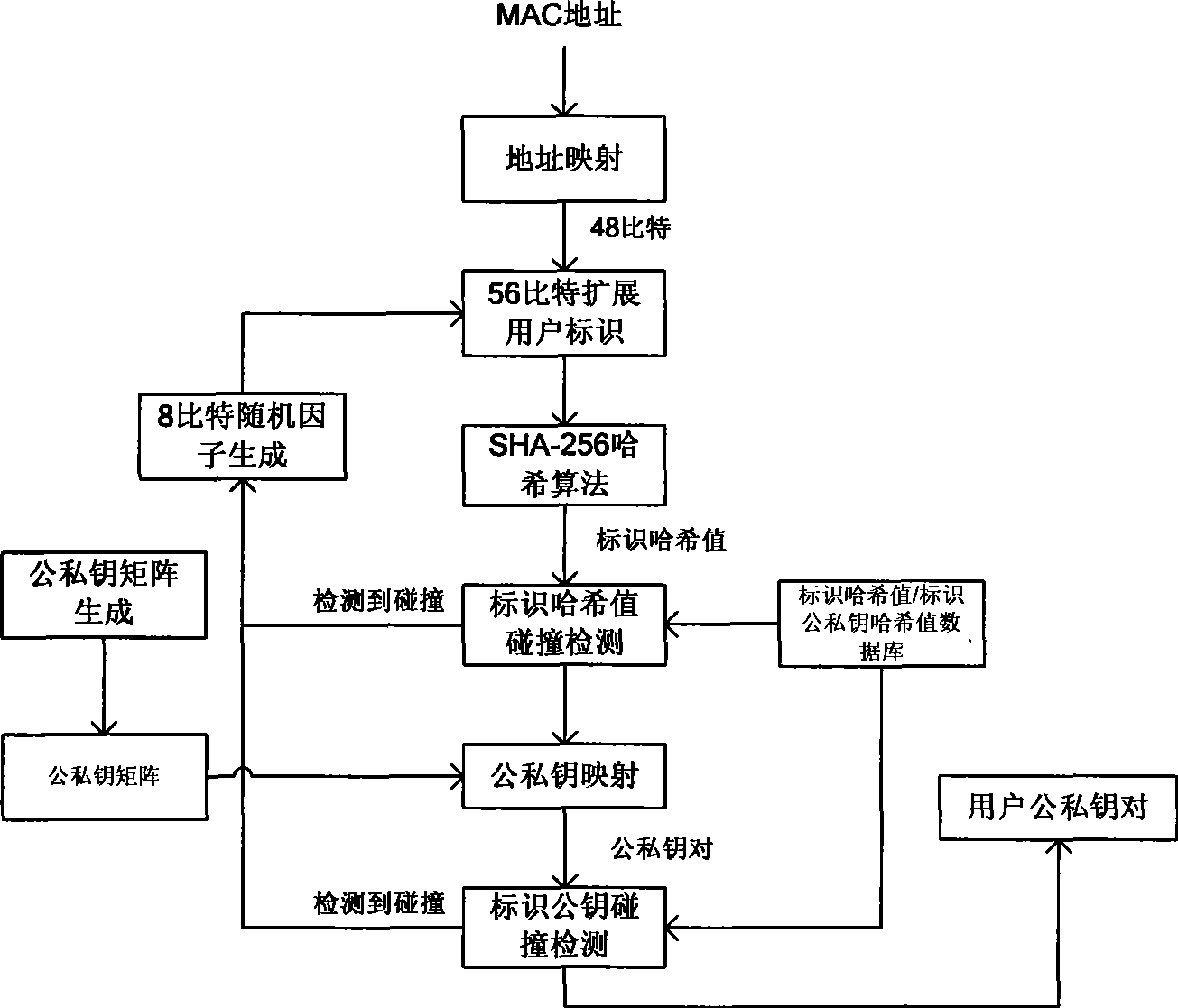
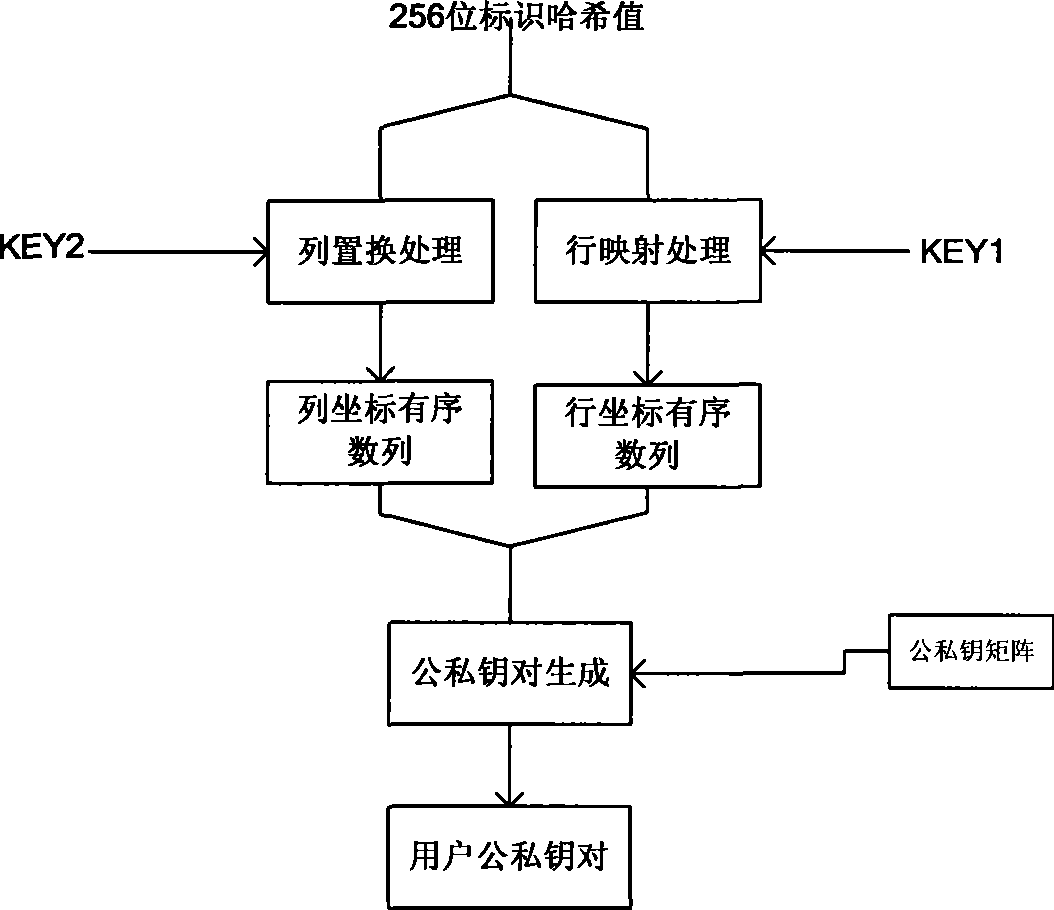
Collision-resistance method for mapping public-private key pairs by utilizing uniform user identification
ActiveCN101447980AResolve collisionImprove unityKey distribution for secure communicationPublic key for secure communicationCommunications securityUser identifier
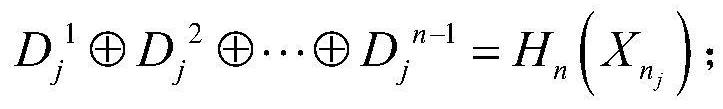
The invention discloses a collision-resistance method for mapping public-private key pairs by utilizing a uniform user identification, relating to the technology of mapping public-private key pair through a user identification in a non-collision manner in the filed of communication network cryptology. The method uses an extensible uniform user identifier with the length of 56 bits to prevent collision of the user public-private key pairs with the assistance of a circle Hash collision algorithm and carries out identification mapping by row mapping and column permutation algorithm of Hash identification value so as to generate a great number of user public-private key pairs by a plurality of private key seeds. On the basis of not losing computational efficiency, the method improves the security and has the advantages of convenient usage and the like, and is particularly applied to public-private key pair mapping through identification by a large number of users in communication network as well as security certification and communication security by the public-private key pairs.
Owner:NO 54 INST OF CHINA ELECTRONICS SCI & TECH GRP
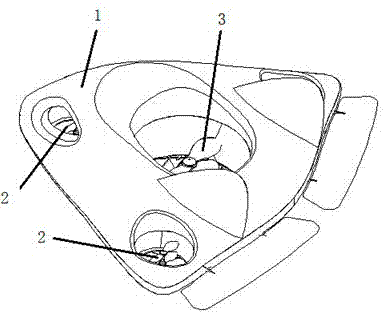
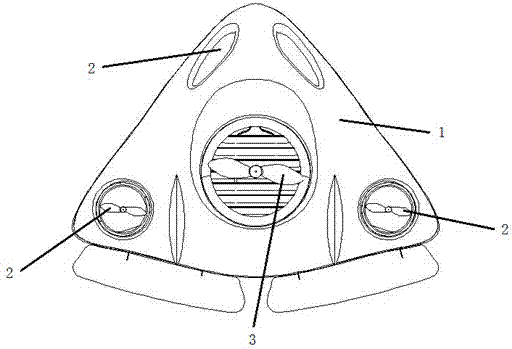
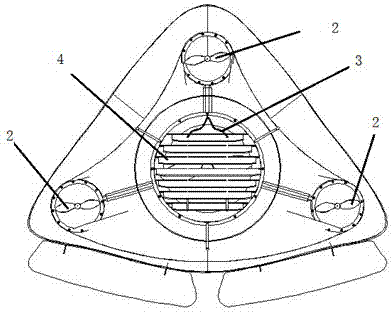
Multifunctional rotating life-saving device
InactiveCN102140858ASo as not to damageNot harmedLife-savingProtective buildings/sheltersFree rotationEngineering
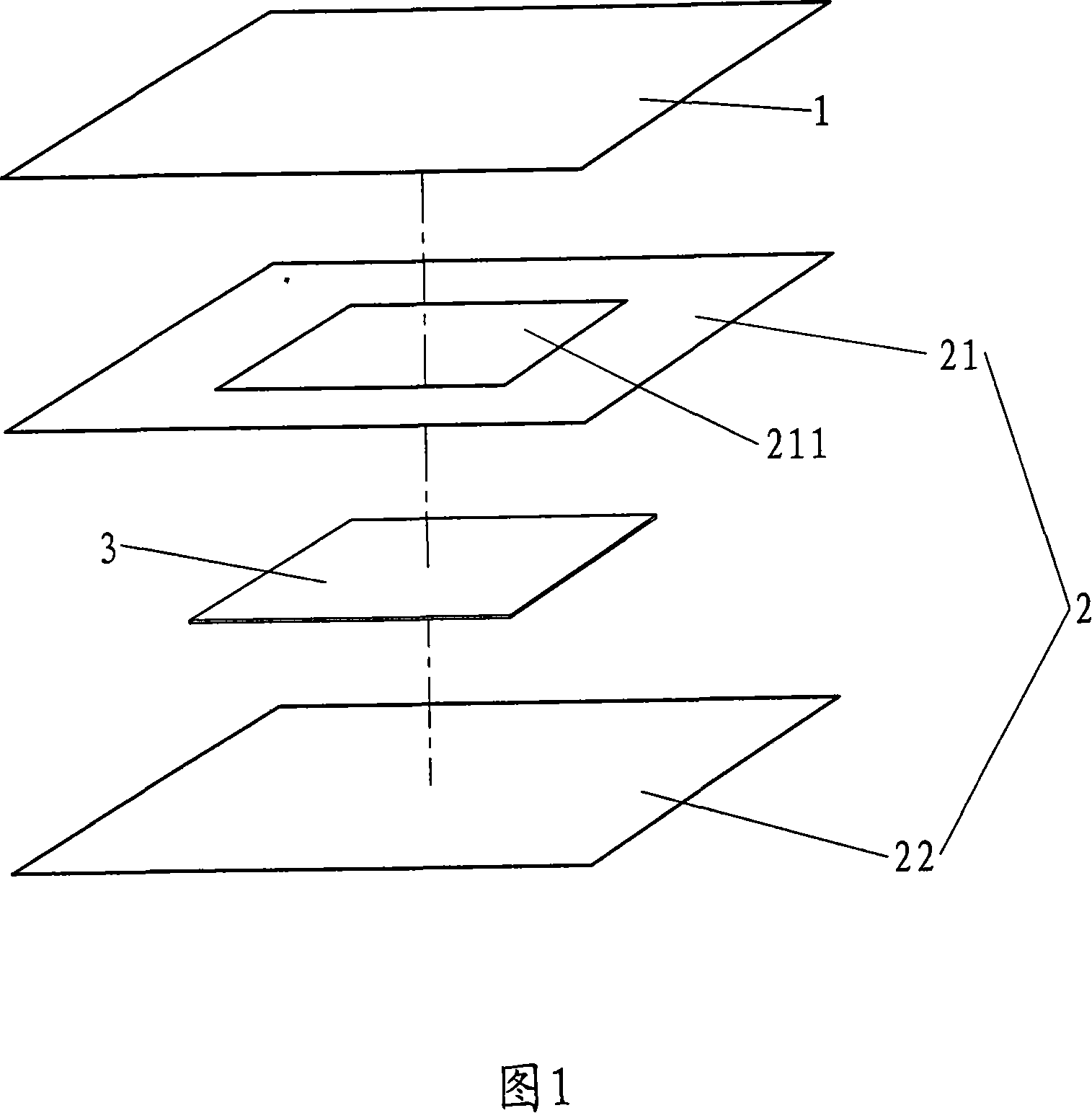
The invention relates to a multifunctional rotating life-saving device. The multifunctional rotating life-saving device enables people and articles which are positioned in the multifunctional rotating life-saving device to all keep in an upright state forever without being injured by seism and collision through the free rotation of a cube shell and a spherical rotating inner shell and is used in the fields of seismic resistance, collision resistance of transportation means, and the like and for manufacturing a large-size seismic-resistant life-saving rockerie, a seismic-resistant life-saving bed, a seismic-resistant life-saving table, seismic-resistant life-saving student desks and chairs, a seismic-resistant life-saving TV cabinet, a seismic-resistant life-saving safety box, a seismic-resistant life-saving anti-theft door, a vertically lifting seismic-resistant life-saving elevator, a seismic-resistant life-saving bathtub, a seismic-resistant life-saving closestool, a high-grade winerotating winebottle, an underground mine seismic-resistant life-saving system, a marine perils preventing life-saving ship, a collision-resistant life-saving automobile, a life-saving plane, an alienspacecraft, a movable combined seismic-resistant life-saving building, a multifunctional rotating seismic-resistant cabinet, a multifunctional rotating seismic-resistant filing cabinet, a multifunctional rotating seismic-resistant wardrobe, a high-seismic-resistant rotating tumbler building, and the like. The multifunctional rotating life-saving device and related products thereof are suitable for each family and unit.
Owner:邹海
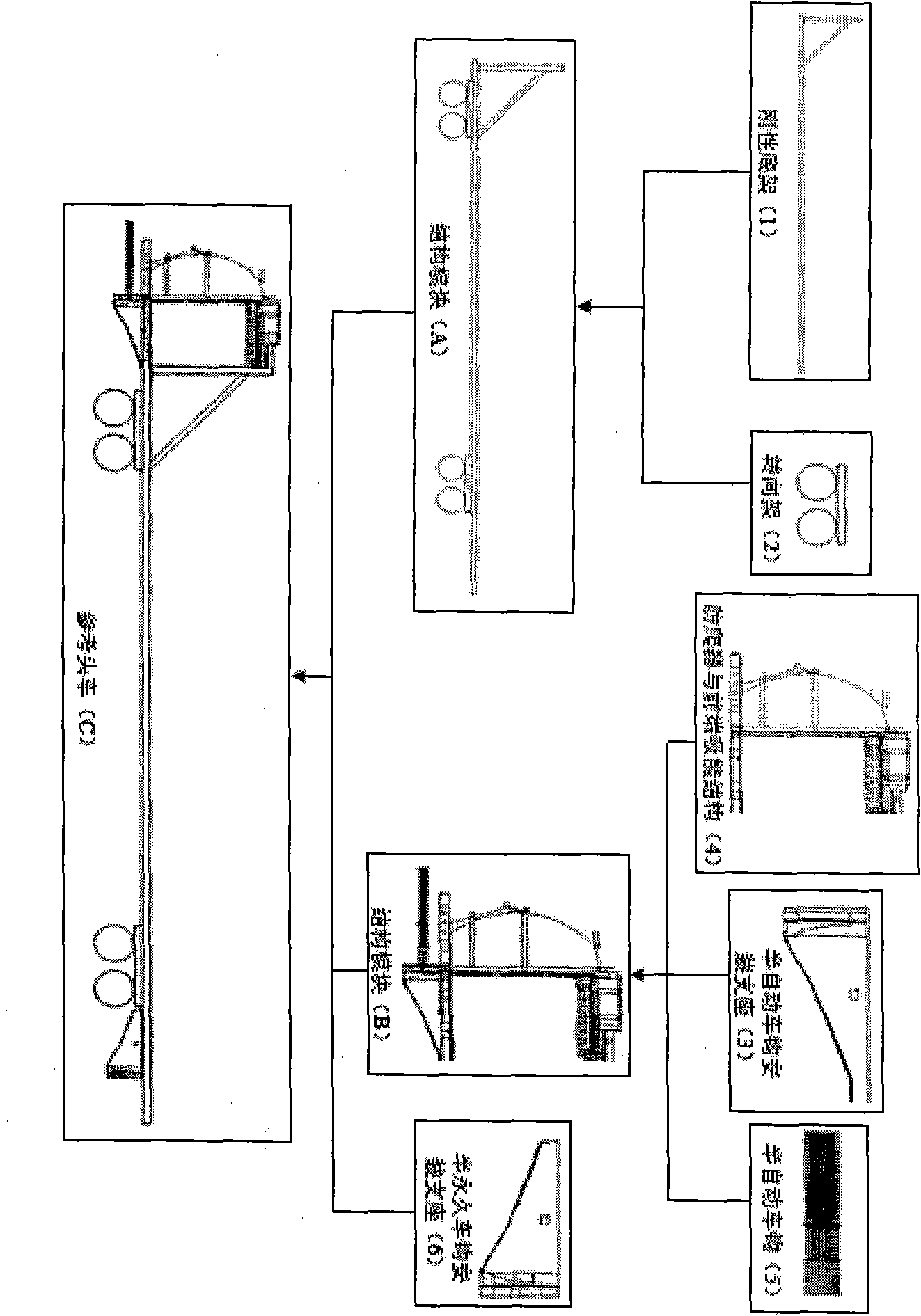
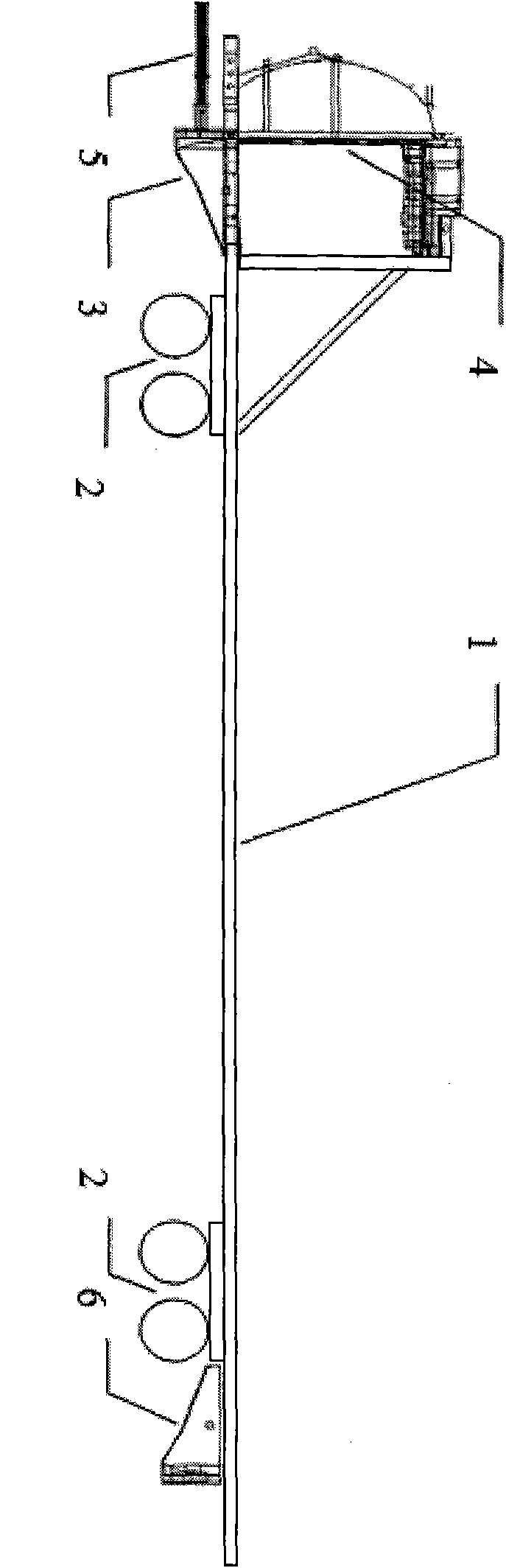
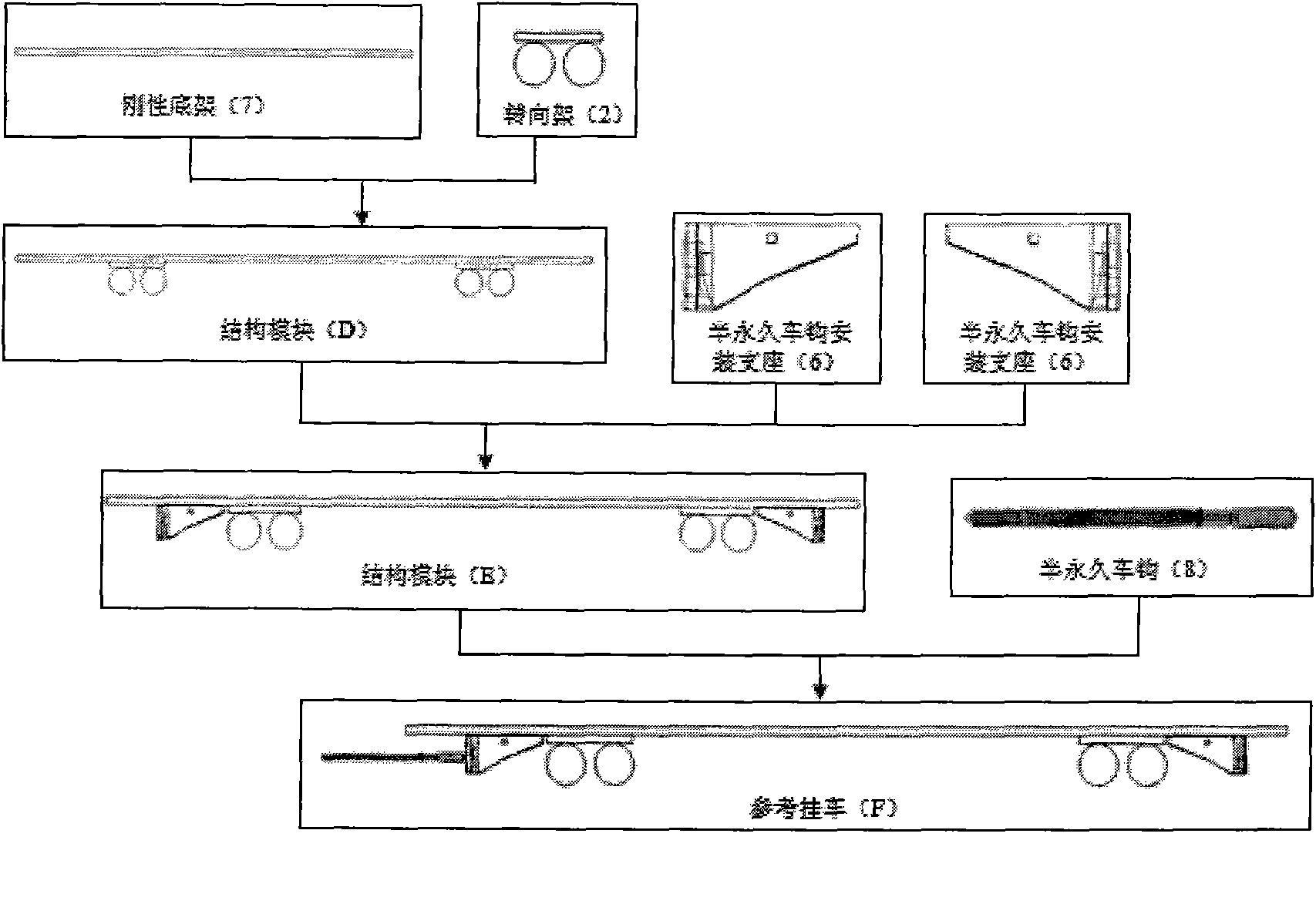
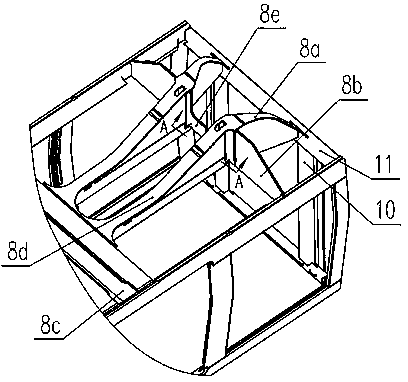
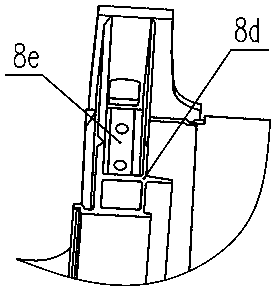
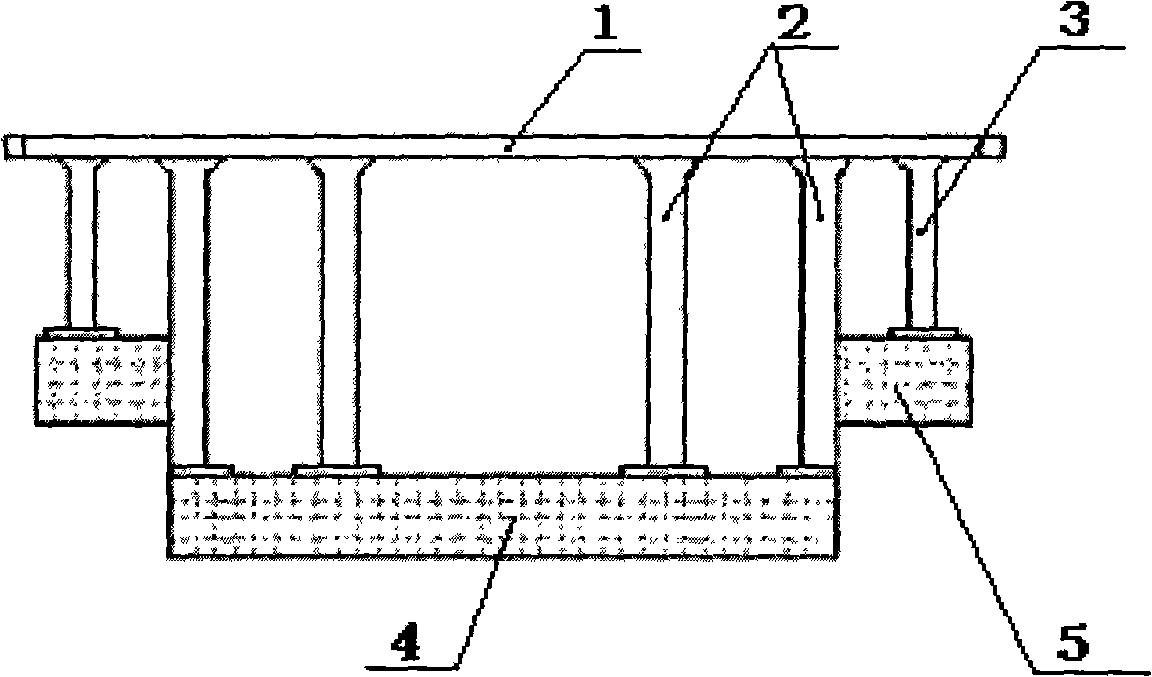
Method for assembling reference train unit collision model
InactiveCN102175414AComprehensive assessment of crashworthinessRailway vehicle testingShock testingCollision resistanceCollision test
The invention discloses a method for assembling a reference train unit collision model. The method comprises the following steps: assembling a reference train head, assembling a reference trailer, assembling a reference trailer unit, assembling a train unit and assembling a trail unit counterweight. According to the method provided by the invention, a 'reference train unit collision test model' and a 'reference train unit collision simulation model' can be acquired, thereby supplying test and analysis means to different stages of train unit collision resistance design and greatly increasing the reliability of train unit collision resistance design. In the early stage of train body collision resistance design, the reference train unit collision test and simulation are introduced, thereby greatly shortening the researching and developing period. The reference train unit collision test model has repeatability, thereby obviously lowering the cost of collision test and achieving the effect as same as the effect of a real train unit collision test. The method provided by the invention has important engineering practice significance for increasing the level of train unit collision resistance design.
Owner:肖锋
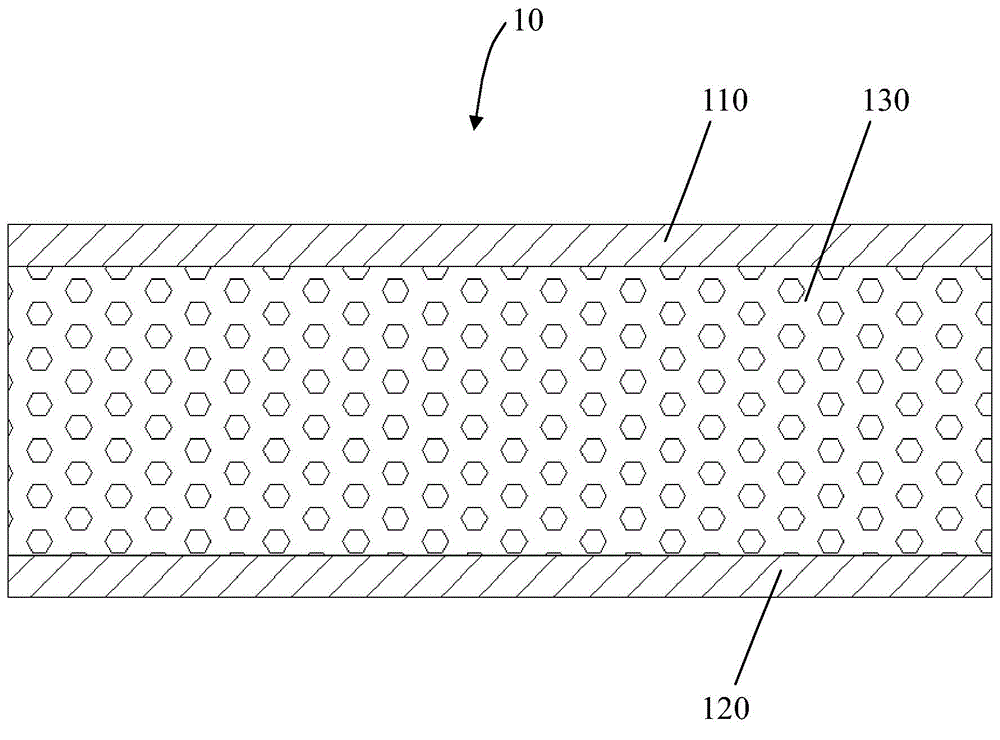
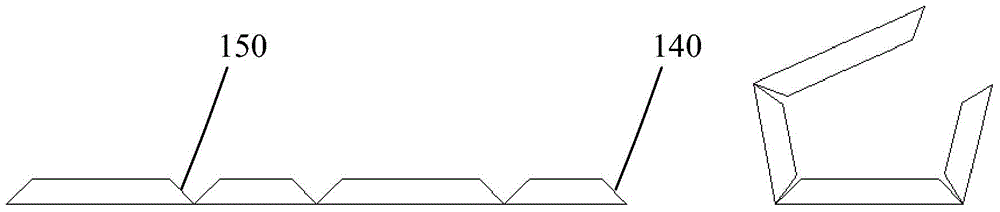
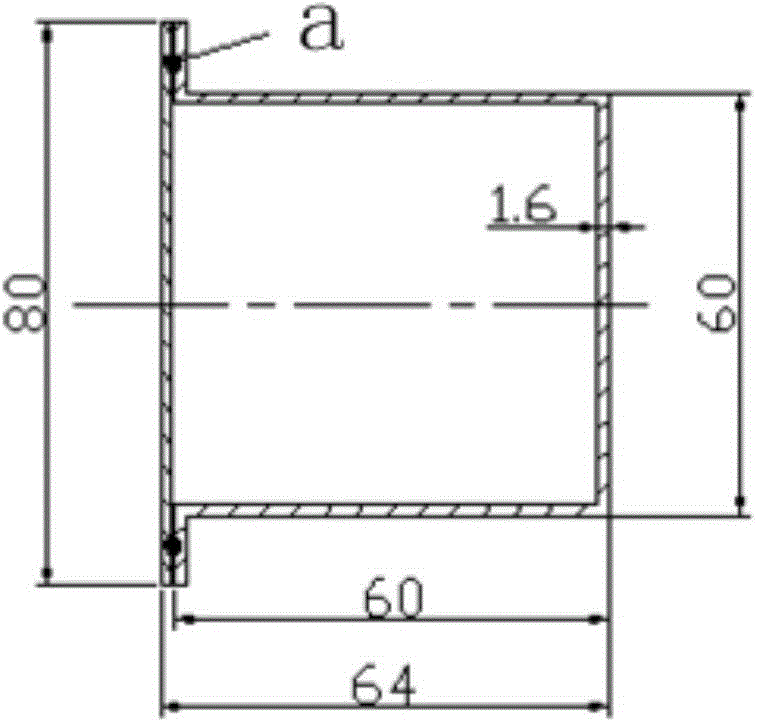
Composite blast pipe construction method
ActiveCN103604007ASimple structureBeautiful appearance and light weightLighting and heating apparatusSpace heating and ventilation detailsCollision resistanceSealant
The invention discloses a composite blast pipe construction method including the following steps of 1) producing plates for making composite blast pipes, 2) dividing and cutting the plates for making the composite blast pipes according to requirements of molding dimensions, 3) bonding the parts of the divided and cut plates for making the composite blast pipes to form the composite blast pipes, and 4) connecting and lifting the composite blast pipes formed by means of bonding and connecting. The plates for making the composite blast pipes include outer colored steel plates, inner colored steel plates and phenolic aldehyde plates sandwiched between the outer colored steel plates and the inner colored steel plates. In the step of connecting the plates for making the composite blast pipes, the joints of the outer colored steel plates are turned and wrapped and fixedly connected by rivets, the joints of the phenolic aldehyde plates are connected by means of adhesive liquid, and the joints of the inner colored steel plates are filled and sealed by solid sealant. The plates for making the composite blast pipes are produced by sandwiching the flame-retardant phenolic aldehyde plate between the double thick colored steel plates, and have the advantages of good heat insulation effect, high strength, collision resistance, simple structure, long service life and convenience in construction.
Owner:CHINA CONSTR EIGHT ENG DIV CORP LTD
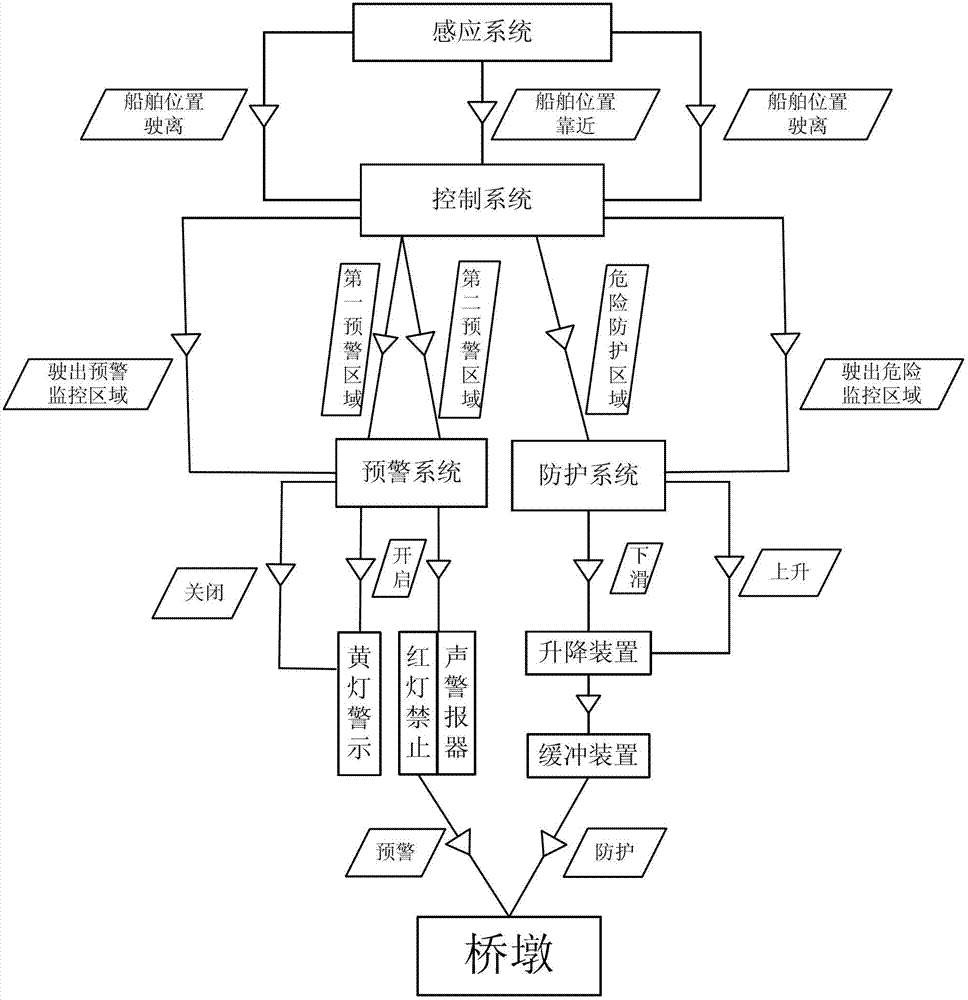
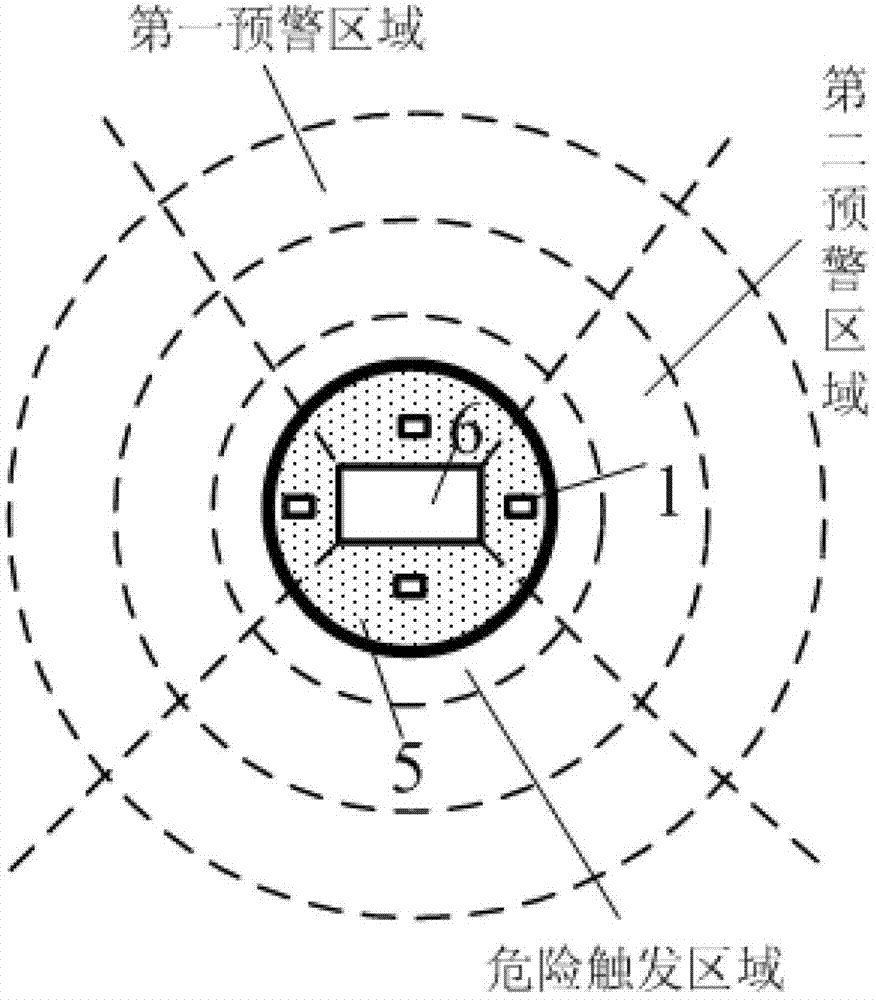
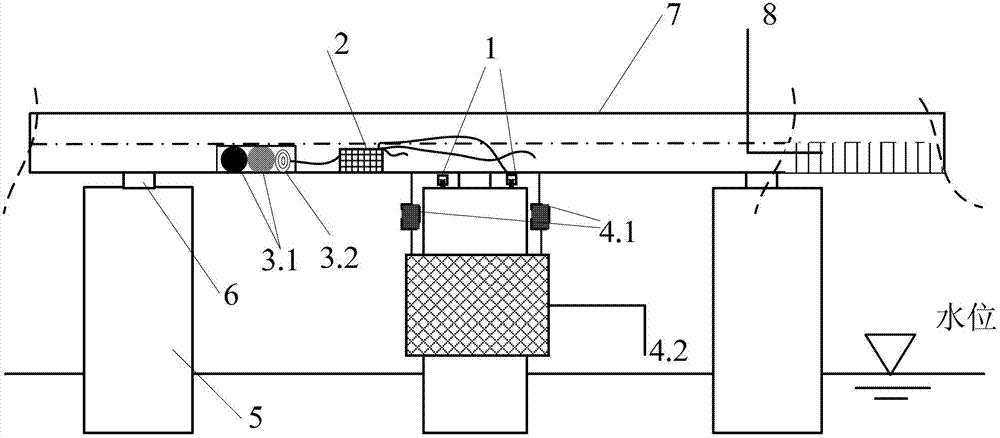
Early warning and protective method for collision resistance of bridge piers
ActiveCN103195023AAvoid Corrosion FailureExtend your lifeClimate change adaptationMarine craft traffic controlControl systemElectrical impulse
The invention provides an early warning and protective method for collision resistance of bridge piers. The method includes that step one, an electronic induction device detects ships within a certain sea area range and amplifies detected physical signals into electrical impulse signals, when the ships sail into a monitored and early warned area, a control system controls an alarm system to raise the alarm, and the ships can adjust sailing directions; step two, when the ships move on and sail into danger areas, the control system controls output of high-low levels to achieve early warning and / or protective functions according to the sizes of the electrical impulse signals; and step three, when the ships leave the monitored sea area after collision and the electronic induction device cannot detect signals, the control system controls reset of an early warning and protective system so as to achieve recycling. According to the early warning and protective method, early warning and protection are combined, ship-bridge collision accidents can be avoided effectively by the aid of intelligent early warning, and the protective system does not occupy navigation channels and not prone to corrosion by seawater and capable of being recycled under the normal state.
Owner:SHANGHAI JIAO TONG UNIV
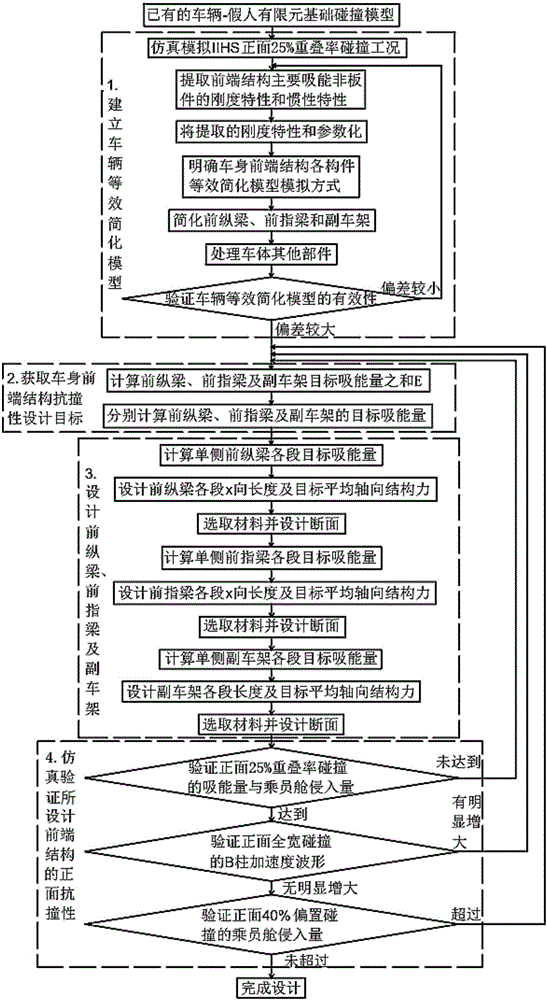
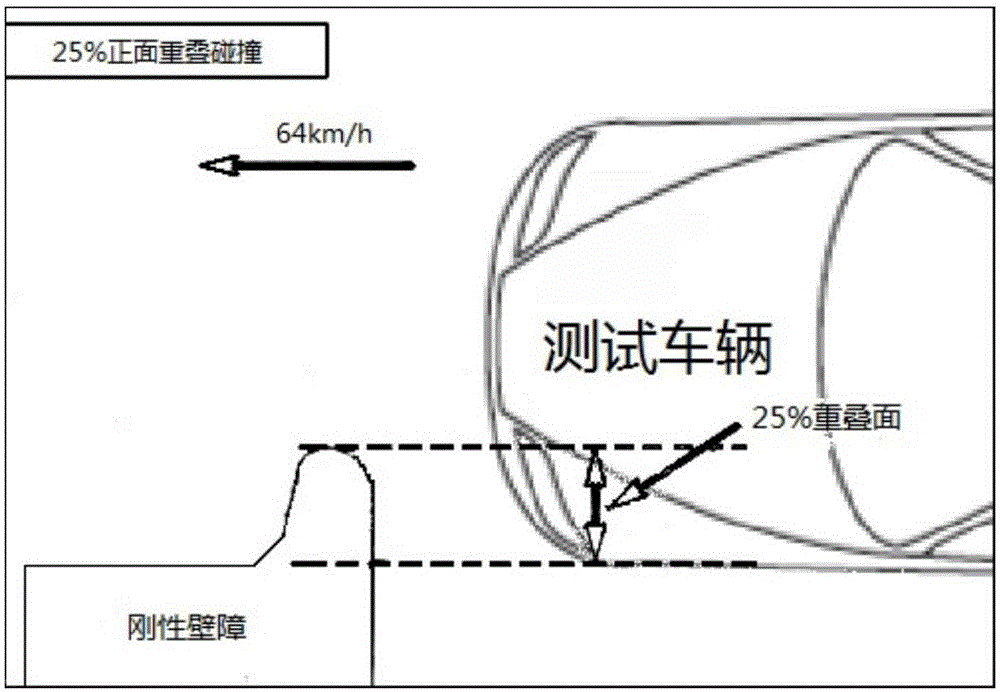
Design method for vehicle body front-end structure with vehicle front surface 25% overlapping ratio collision
InactiveCN106709151AOmit the modification processShorten the timeGeometric CADDesign optimisation/simulationVehicle frameEngineering
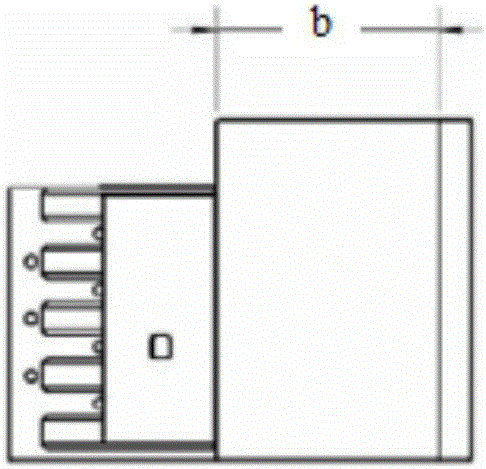
The invention discloses a design method for a vehicle body front-end structure with vehicle front surface 25% overlapping ratio collision, and aims to solve the problems of design blindness in an existing optimization design process for vehicle body front-end members with vehicle front surface 25% overlapping ratio collision, and repeated modeling and long calculation time during adoption of a CAE technical means in the optimization design process. The design method for the vehicle body front-end structure with the vehicle front surface 25% overlapping ratio collision comprises the steps of 1, building an equivalent simplified model of a vehicle: 1) extracting a stiffness characteristic and an inertia characteristic; 2) parameterizing the extracted stiffness characteristic and inertia characteristic; 3) clearly determining a simulation mode of an equivalent simplified model of each member of the vehicle body front-end structure; 4) simplifying a front longitudinal beam, a front fingerboard and an auxiliary frame; 5) processing other parts of a vehicle body; and 6) verifying the equivalent simplified model of the vehicle; 2, obtaining an anti-collision design objective of the vehicle body front-end structure; 3, designing the front longitudinal beam, the front fingerboard and the auxiliary frame; and 4, performing simulation verification on front surface collision resistance of the vehicle body front-end structure after optimization design.
Owner:JILIN UNIV
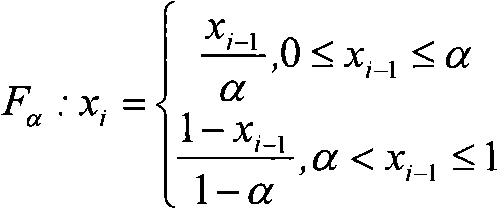
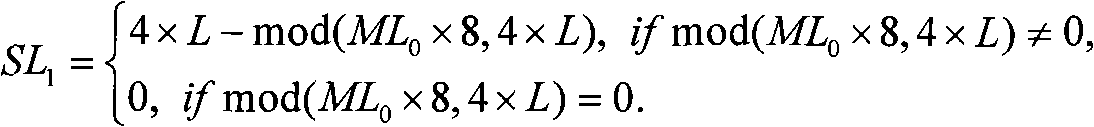
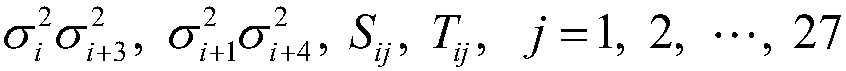
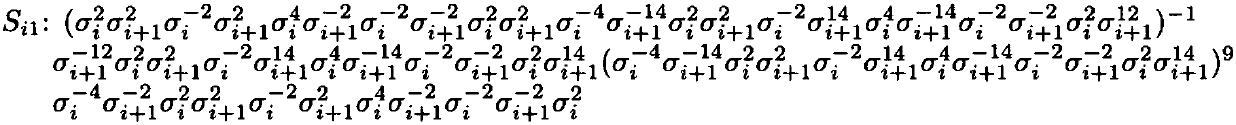
One-way hashing function construction method and system based on built-in chaos mapping
InactiveCN101296079APrevent tamperingKey distribution for secure communicationUser identity/authority verificationHash functionCollision resistance
The invention provides a method and a system for structuring expandable one-way hash function based on embedded chaotic mapping. The structuring method comprises the following steps of: receiving the scheduled chaotic mapping, an initial value, a cipherkey and a message to be treated so as to generate a group of initial buffer value chaotic sequence; using the chaotic sequence to bit-stuff the message so as to divide the stuffed message pad into subblocks with the same length; carrying out Boolean operation to the initial buffer value sequence group and one of the subblocks and taking the result as a new buffer value sequence group; carrying out the Boolean operation again to the new buffer value sequence group and another subblock from the subblocks with preset order until finishing the Boolean operation to all subblocks; cascading of final output, which is taken as the one-way hash function value sequence of the message. Therefore, the structuring method is simple and easy for operation, which effectively realizes the diffusing and mixing of the message and has obvious enhancement in the aspects of security, collision resistance and operation speed.
Owner:SONY CHINA
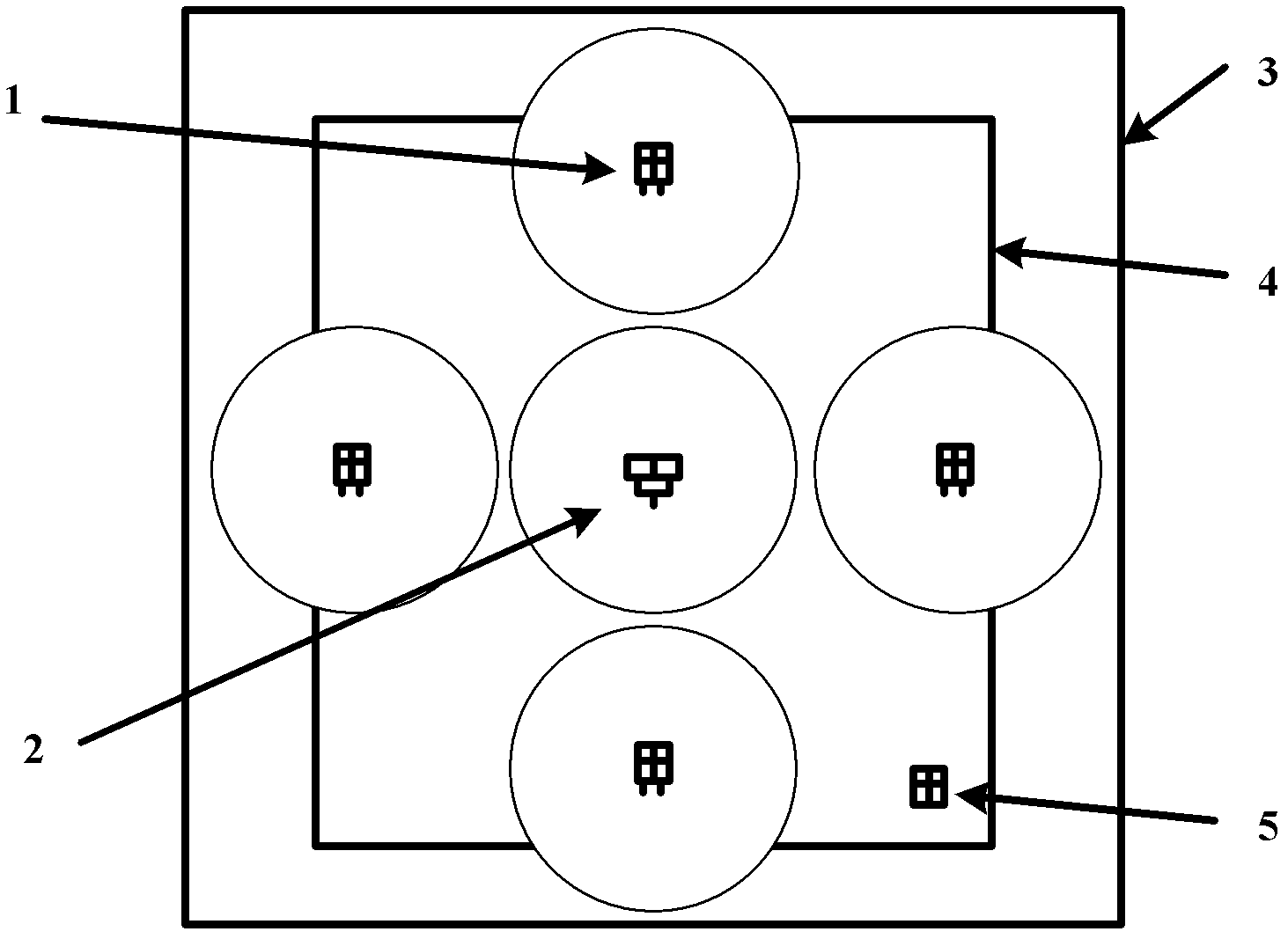
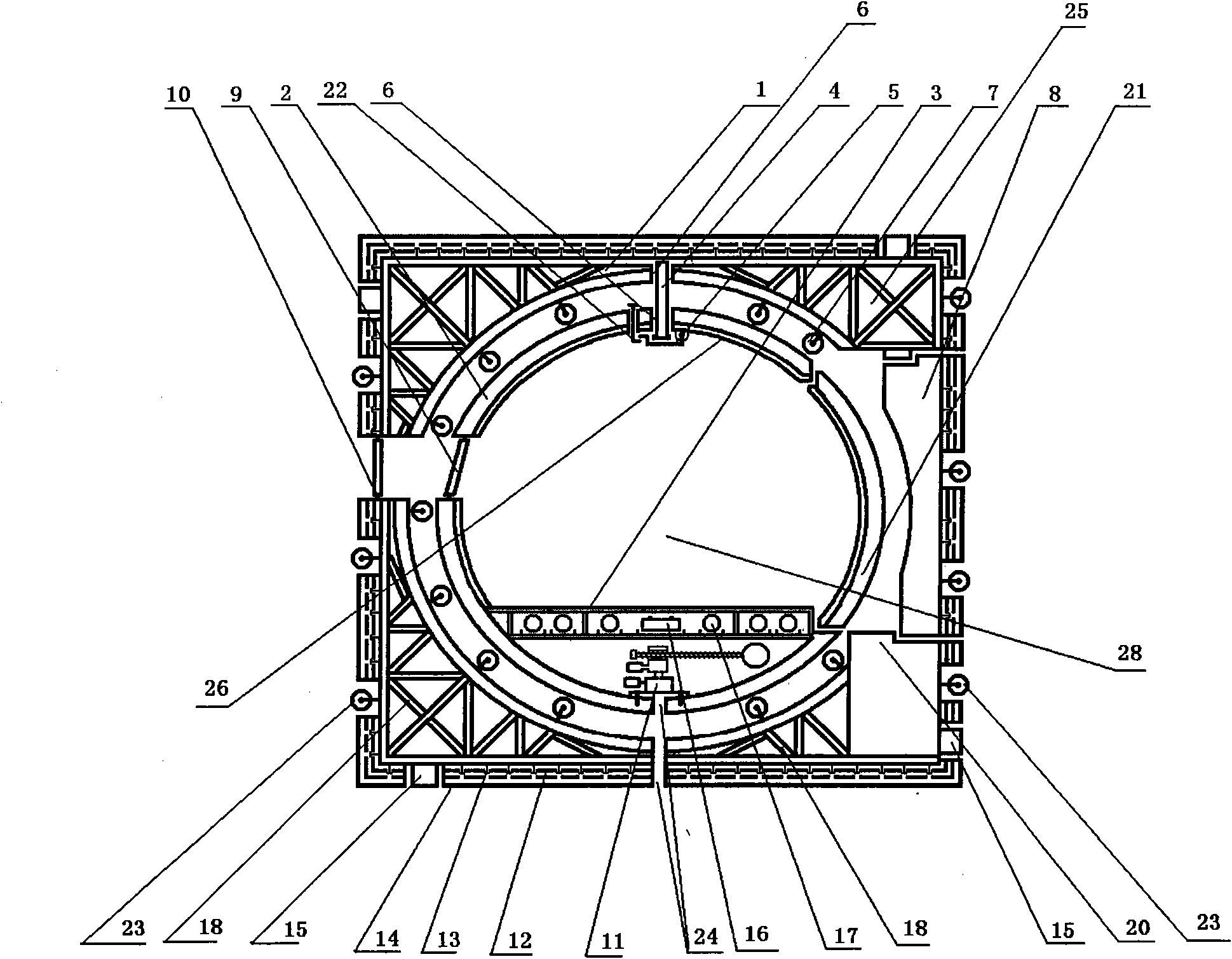
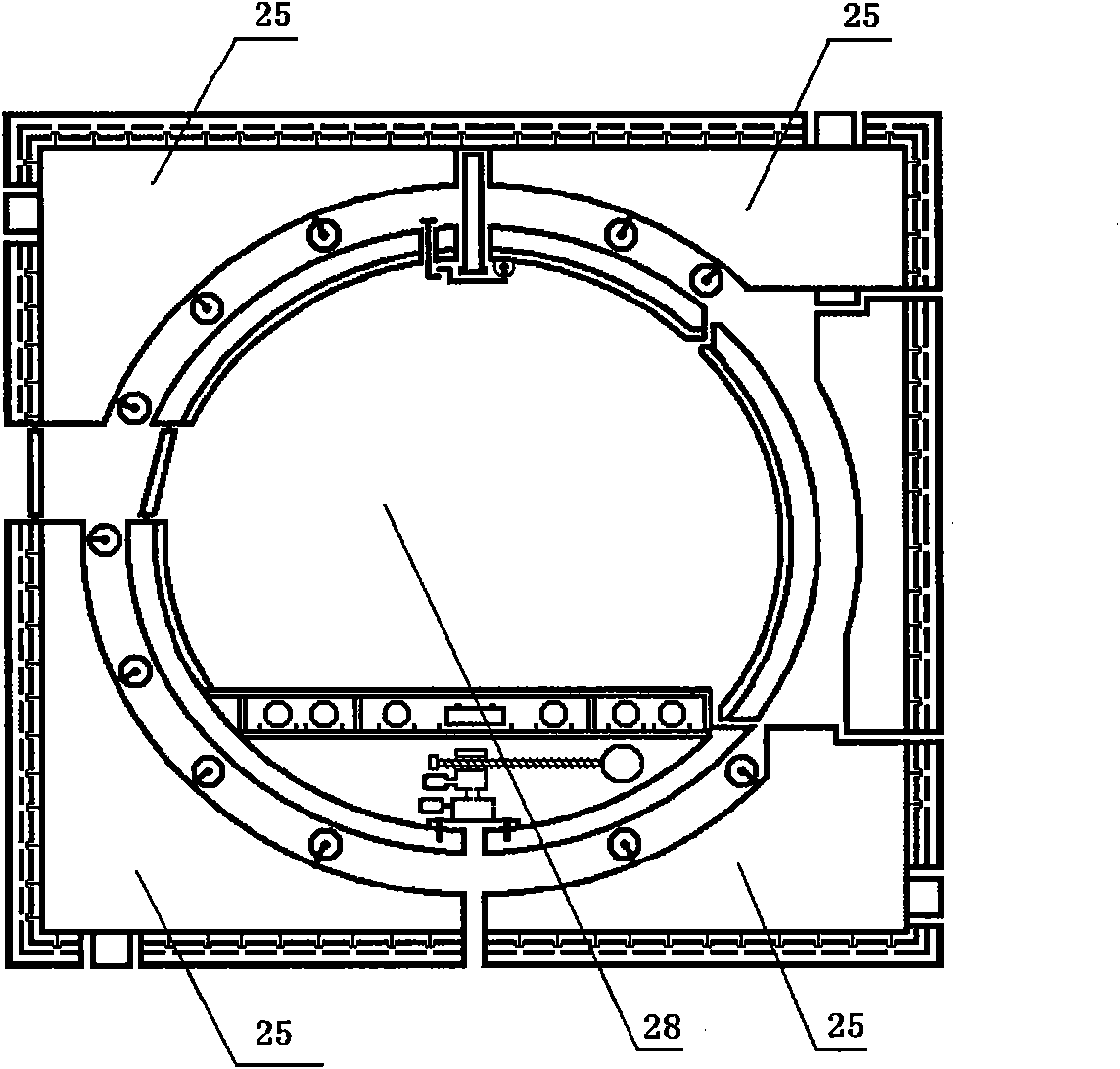
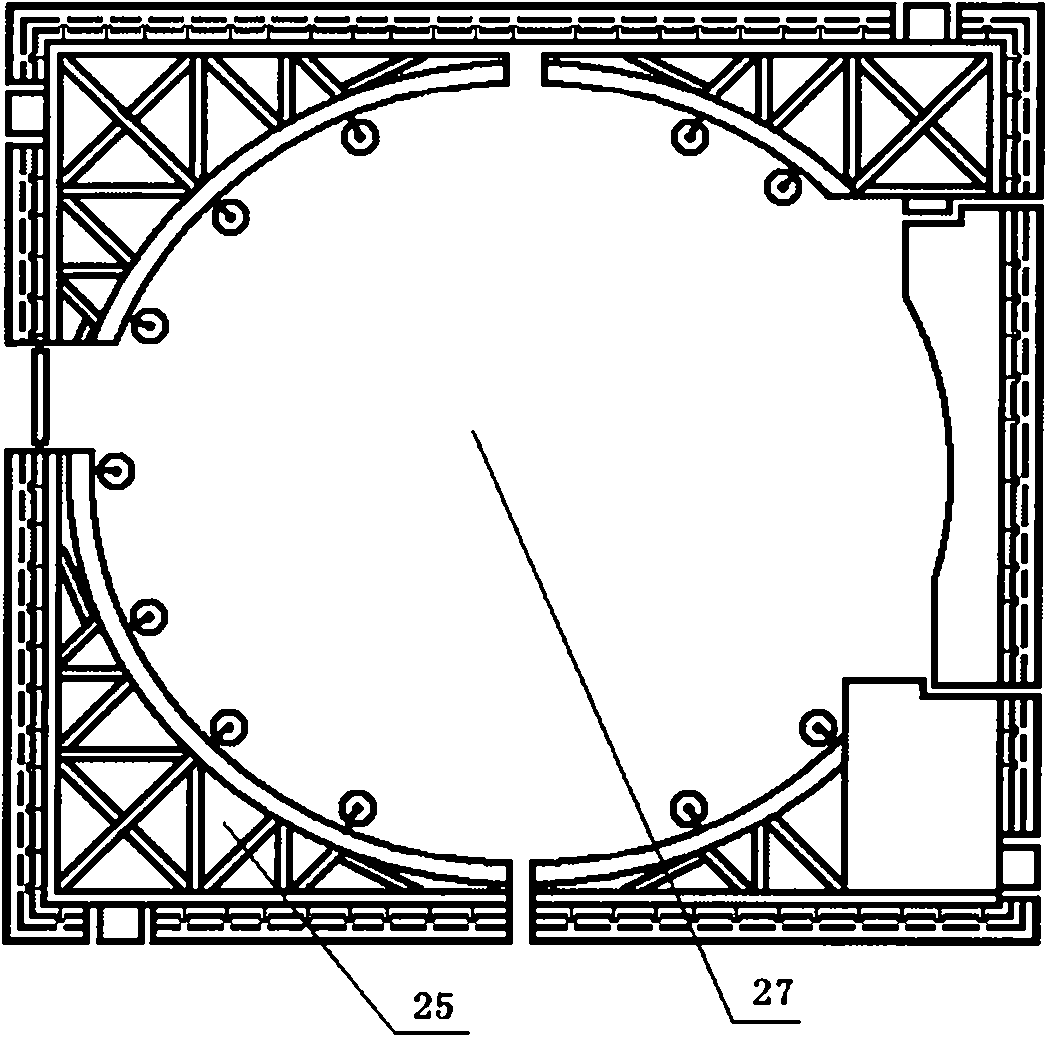
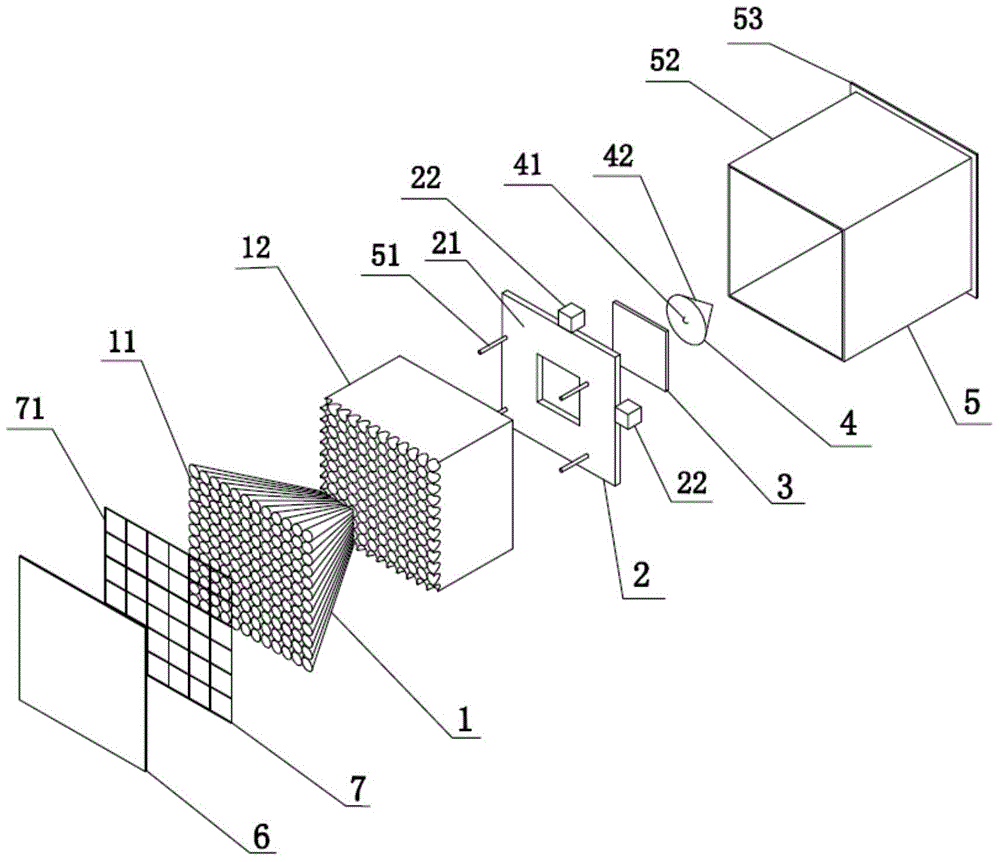
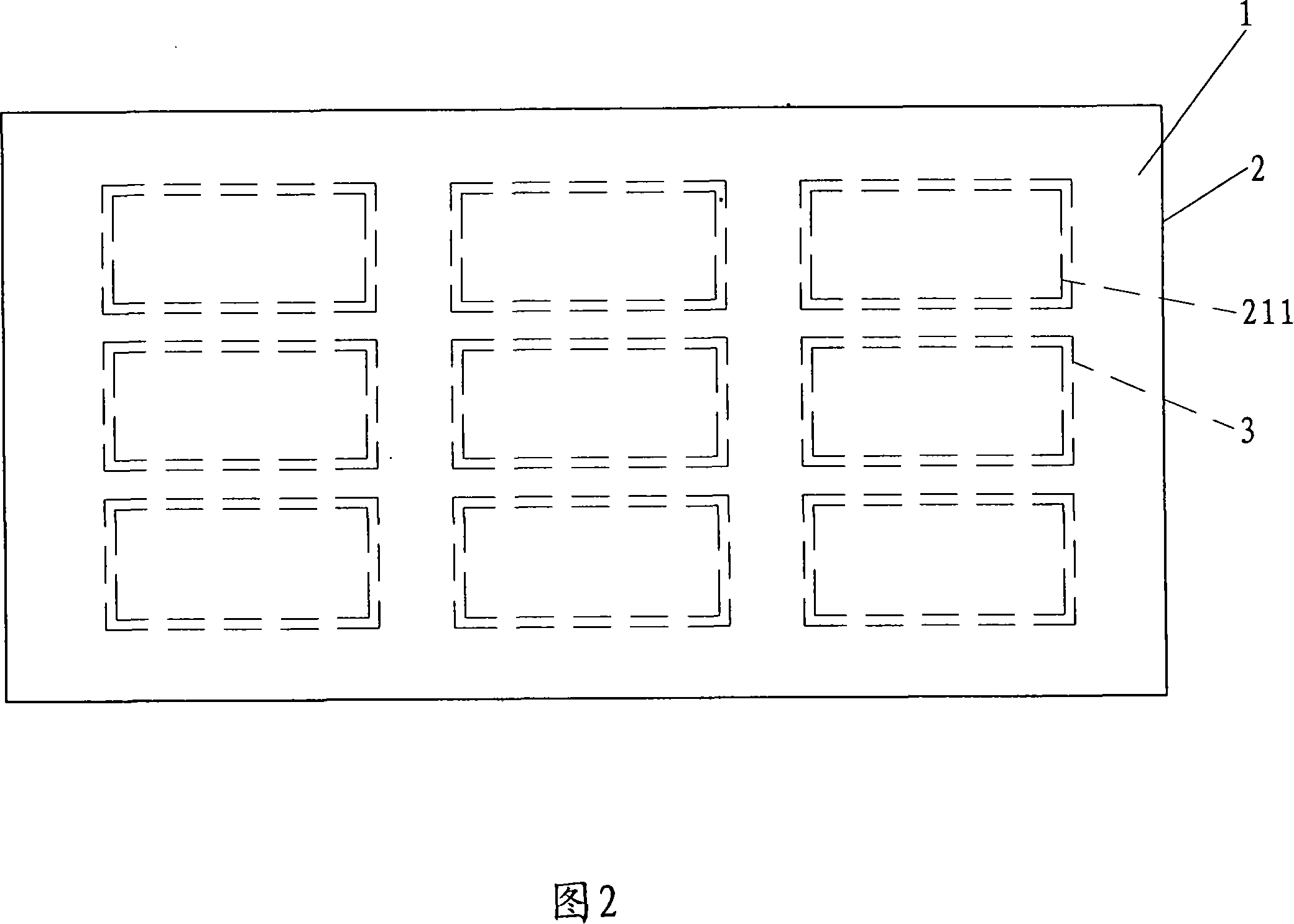
Arbitrary-curved-surface plane seamless spliced high-quality large-screen display device
The invention discloses an arbitrary-curved-surface plane seamless spliced high-quality large-screen display device. The arbitrary-curved-surface plane seamless spliced high-quality large-screen display device is formed by stacking brick-shaped optical-fiber rear-projection display modules, wherein elements of each brick-shaped optical-fiber rear-projection display module include a variable-cross-section optical fiber panel, a signal processing module, a liquid crystal display panel, an LED (light-emitting diode) light source module, a fixing device, a shell, an anti-dazzling frosting coating and a touch sensing plate. The arbitrary-curved-surface plane seamless spliced high-quality large-screen display device has beneficial effects that a seamless spliced high-quality screen with small dot pitch can be produced, a display video picture of an arbitrary curved surface, a special arbitrary shape, and an arbitrary area can be realized; the seamless splicing principle is the primary-pixel splicing principle, pixel points are uniformly and compactly arranged, and the display consistency of the brightness and color is optimal; by adopting the modularized production, the constitutional part is easy to repair and replace; the touch sensing plate can be embedded into the display device, so that precision in positioning can be realized, and the picture quality and the shape of the display device are not affected; the water resistance and collision resistance are relatively good.
Owner:梁岗
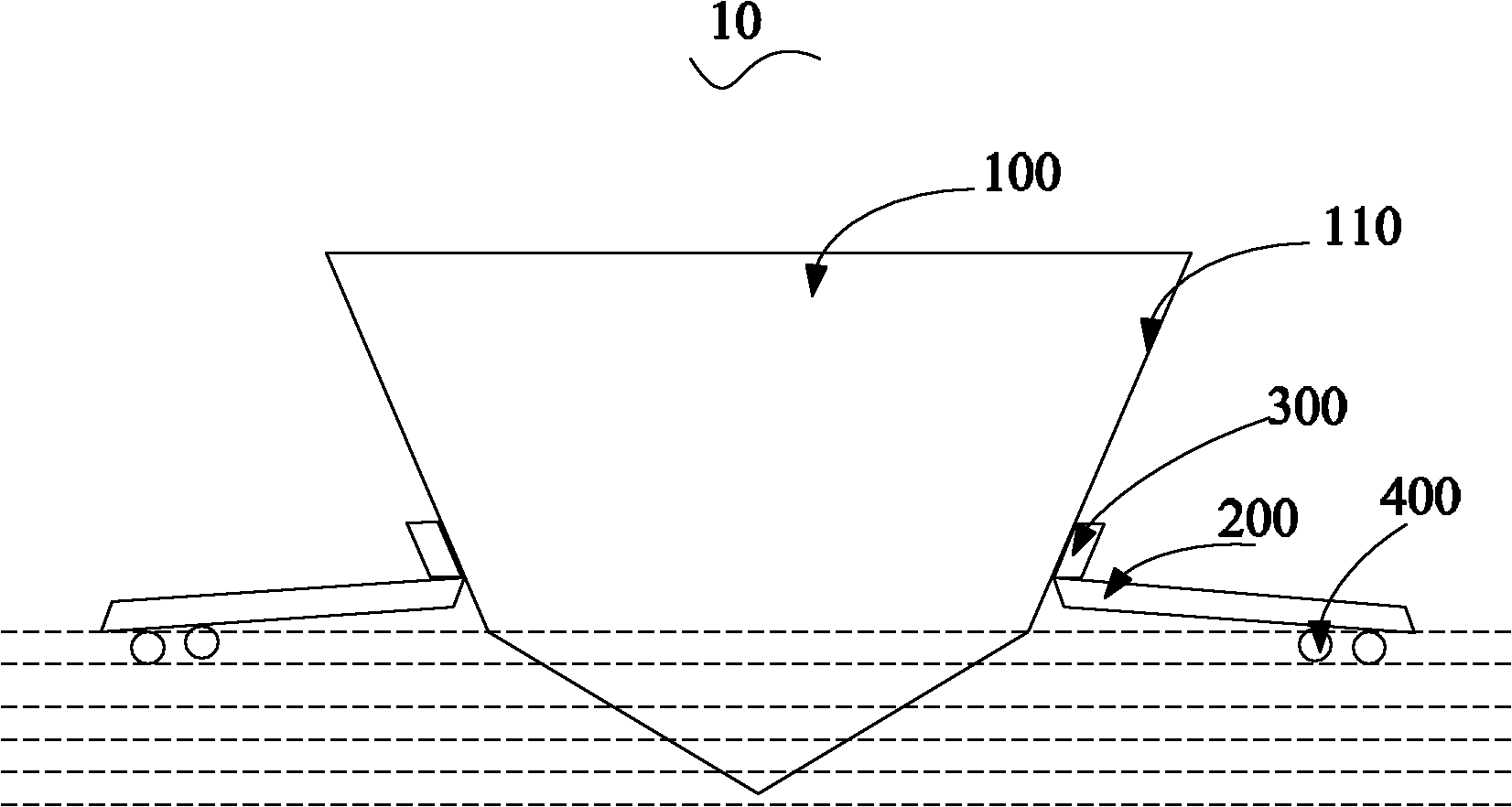
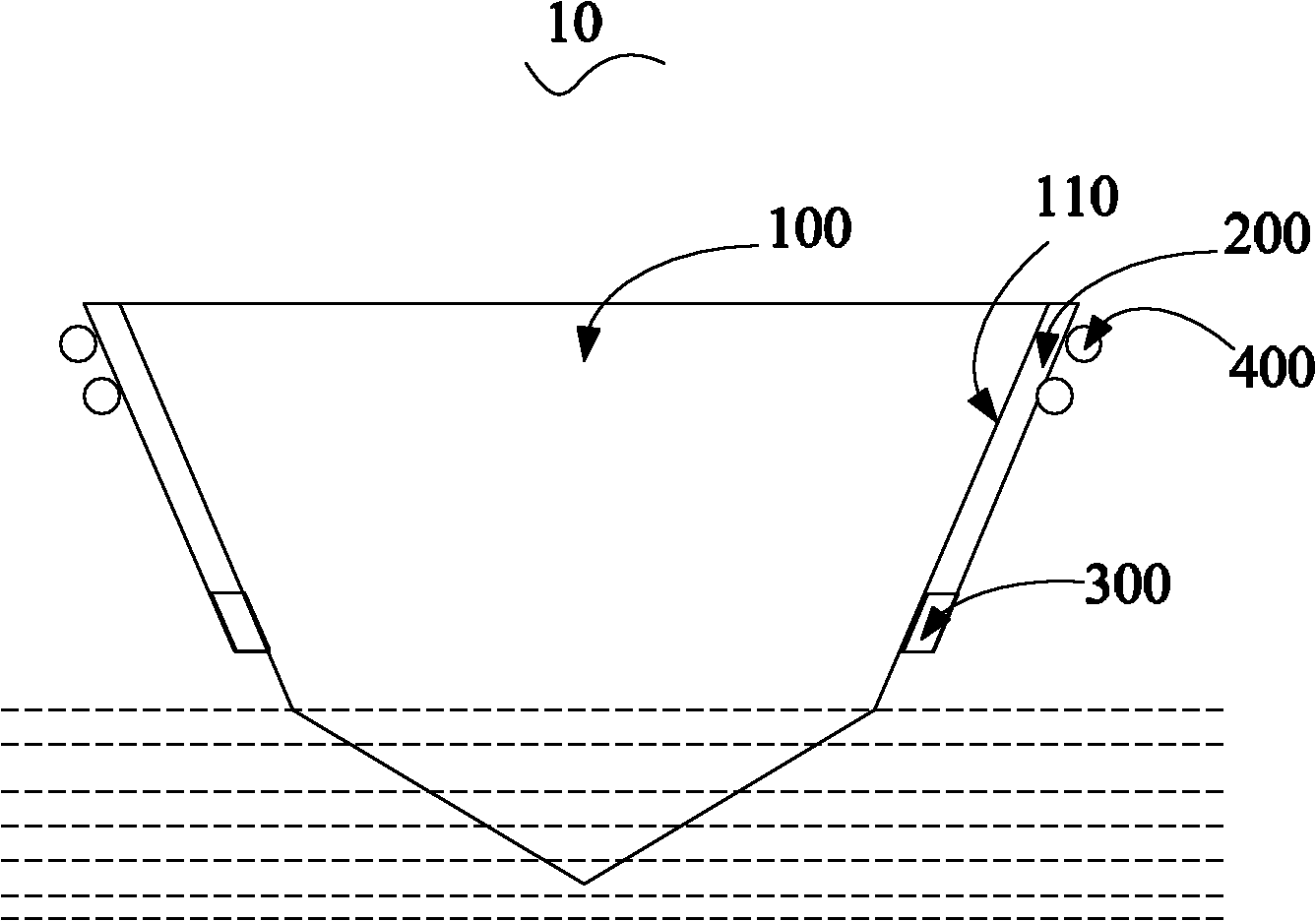
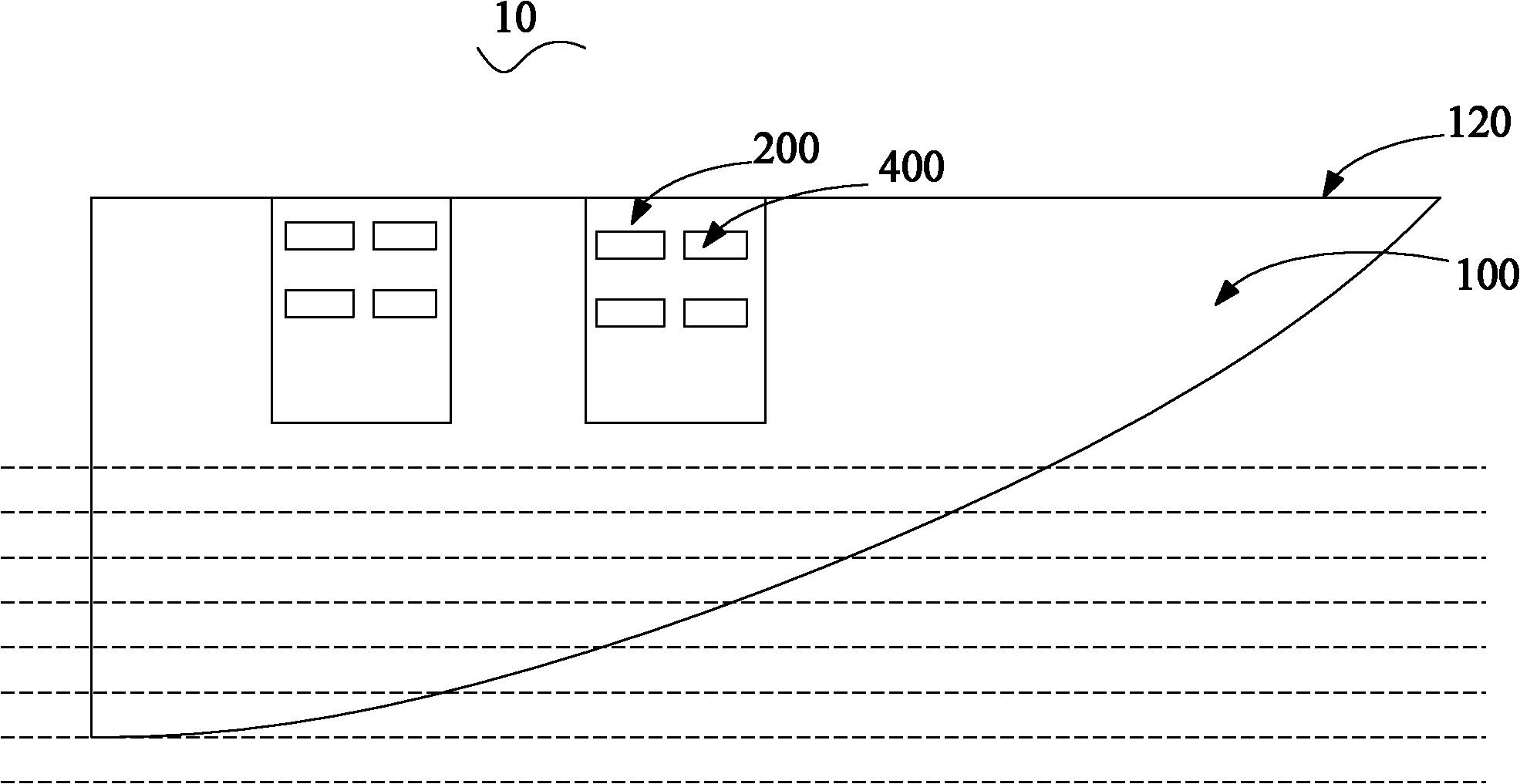
Collision and rolling resistant monohull ship
ActiveCN102602510AReduce torqueEnsure balanceVessel cleaningHullsMarine engineeringCollision resistance
A collision and rolling resistant monohull ship comprises a ship body, and rotatable stabilizing boards are arranged on the outer sides of the two side walls of the ship body. Accordingly, during voyage of the collision and rolling resistant monohull ship, the side walls of the stabilizing boards distant from the ship body are close to the water surface, moment generated by the gravity of the collision and rolling resistant monohull ship is reduced by resistance moment of water to the stabilizing boards, so that the collision and rolling resistant monohull ship can be kept balance, transverse rolling during voyage is reduced and transverse rolling amplitude is decreased, and collision resistance of the ship body is improved due to the fact that the stabilizing boards can prevent collision.
Owner:SHENZHEN HISPEED BOATS TECH
Method for establishing public key cryptogram against quantum computing attack
ActiveCN107911209AKey distribution for secure communicationCryptographic attack countermeasuresPlaintextHash function
The present invention relates to the field of information safety, and discloses a method for establishing public key cryptogram against quantum computing attack. The method comprises the following steps of: (11) a protocol first party selects a braid group Bn with an index n of being not small than 7, and selects a subgroup A generated by employing a1, a2, ..., ak in the Bn and a subgroup B generated by employing b1, b2, ..., bm in the Bn; (12) the protocol first party selects [Theta], wherein Bn maps to {0, 1}k is an Hash function from Bn to plaintext space {0, 1}k collision resistance; (13)the protocol first party selects an element x as a private key, wherein x=x(a1, a2, ..., ak) belonging to A, and selects (Bn, A, B, [Theta], X-1b1x, x-1b2x, ..., x-1bmx) as a public key; (14) a protocol second party selects an element y, wherein y=y(b1, b2, ..., bm) belonging to B, calculates KB=(y< 1>y(x< 1>b1x, x< 1>b2x, ..., x< 1>bmx))< 1>=(y< 1>x< 1>yx)< 1>=x< 1>y< 1>xy, performs encryption calculation of a plaintext p to obtain a ciphertext (img file='DDA0001531187730000011. TIF' wi='286' he='71' / ) and sends t to the protocol first party; and (15) the protocol first party calculates KA=x<1>x(y< 1>a1y,y< 1>a2y, ...,y< 1>aky)=x< 1>y< 1>xy, performs decryption calculation to obtain a plaintext (img file='DDA0001531187730000012. TIF' wi='283' he='70' / )(img file='DDA0001531187730000013. TIF' wi='510' he='63' / ). The method provided by the invention can resist all the known attacks comprising quantum computing attack.
Owner:SHENZHEN UNIV
High-corrosion-resistance trivalent chromium blue white passivation concentrated solution and preparation method thereof
ActiveCN106756955AEven and bright blueSolution to short lifeMetallic material coating processesCobalt saltSolvent
The invention discloses high-corrosion-resistance trivalent chromium blue white passivation concentrated solution. The passivation solution comprises the following raw materials and contents: 100-350 g / L of chromic salt, 50-250 g / L of cobalt salt, 50-200 g / L of complexing agent, 50-200 g / L of oxidizing agent, and 10-120 g / L of pH conditioning agent; and solvent is water. The passivation concentrated solution adopts the most advanced international trivalent chromium, contains no hexavalent chromium, belongs to the new generation of environment-friendly product, and is simple in process operation, easy to operate and control, excellent in stability, uniform and bright in blue of a passivation membrane, compact and firm in film formation, higher in corrosion and collision resistance and meanwhile, longer in service life.
Owner:济南德锡科技有限公司
Twin-box multifunctional vehicular battery box
ActiveCN103253118ARealize the heat dissipation functionImprove reliabilityElectric propulsion mountingPropulsion coolingThermal insulationAutomotive battery
The invention provides a twin-box multifunctional vehicular battery box which comprises an inner box, an outer box, pulley sliding rails and a battery system. The twin-box multifunctional vehicular battery box is characterized in that both the inner box and the outer box are of closed box structures and mutually form a drawer type movable assembly structure, ventilation holes are arranged in an interlayer space between the inner box and the outer box, ventilation doors are mounted on the ventilation holes, and the inner box is provided with a thermal conductive plate in an interlayer. The technical requirements for the battery box of an electric vehicle, such as thermal insulation, water tightness, shock resistance, collision resistance, thermal dissipation and the like can be met, so that reliability of the battery system can be improved, and the service life of the battery system can be prolonged.
Owner:BEIJING PRIDE NEW ENERGY BATTERY
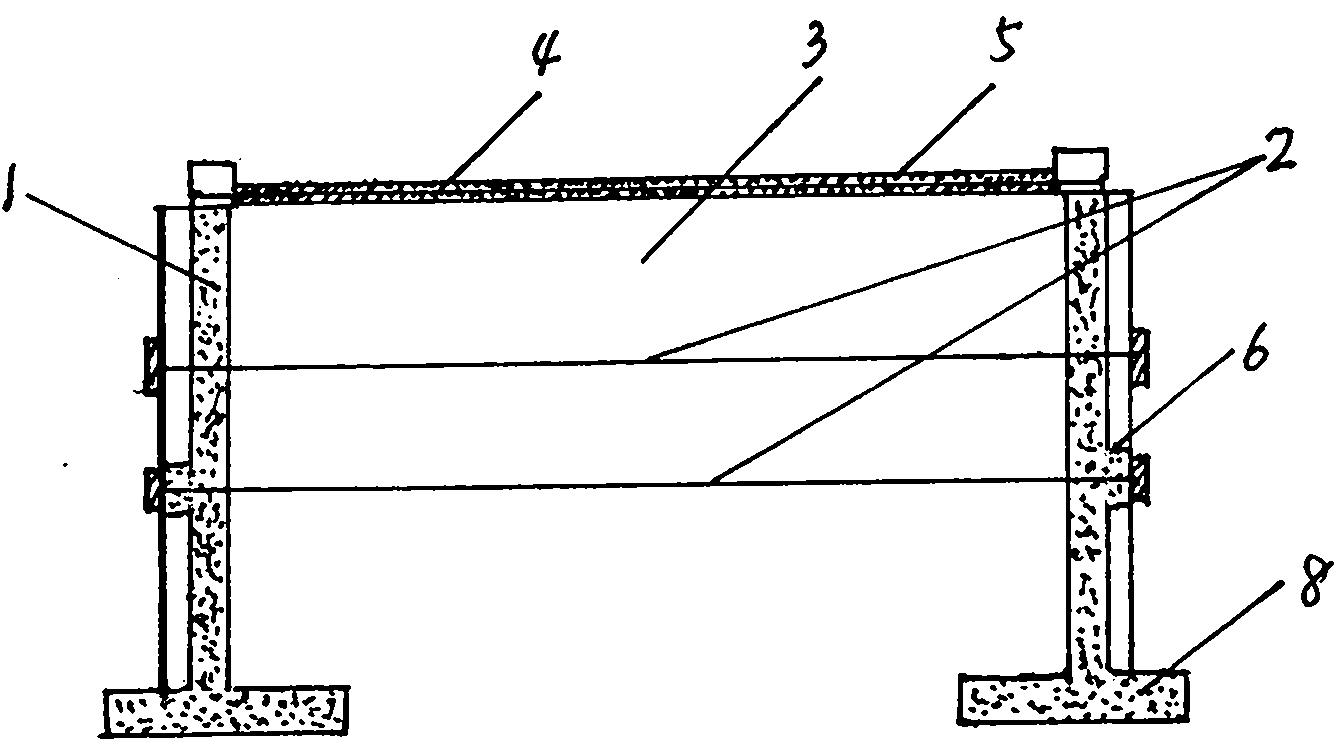
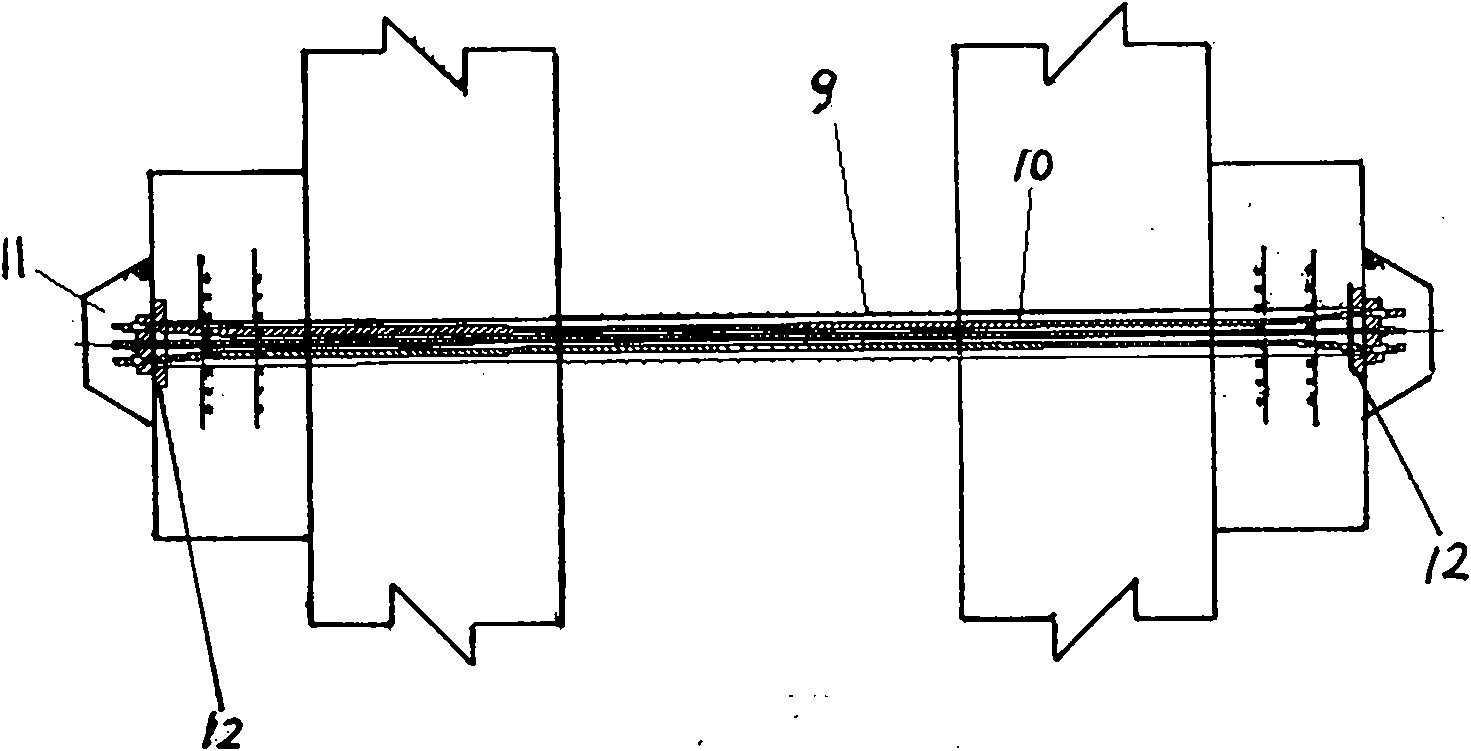
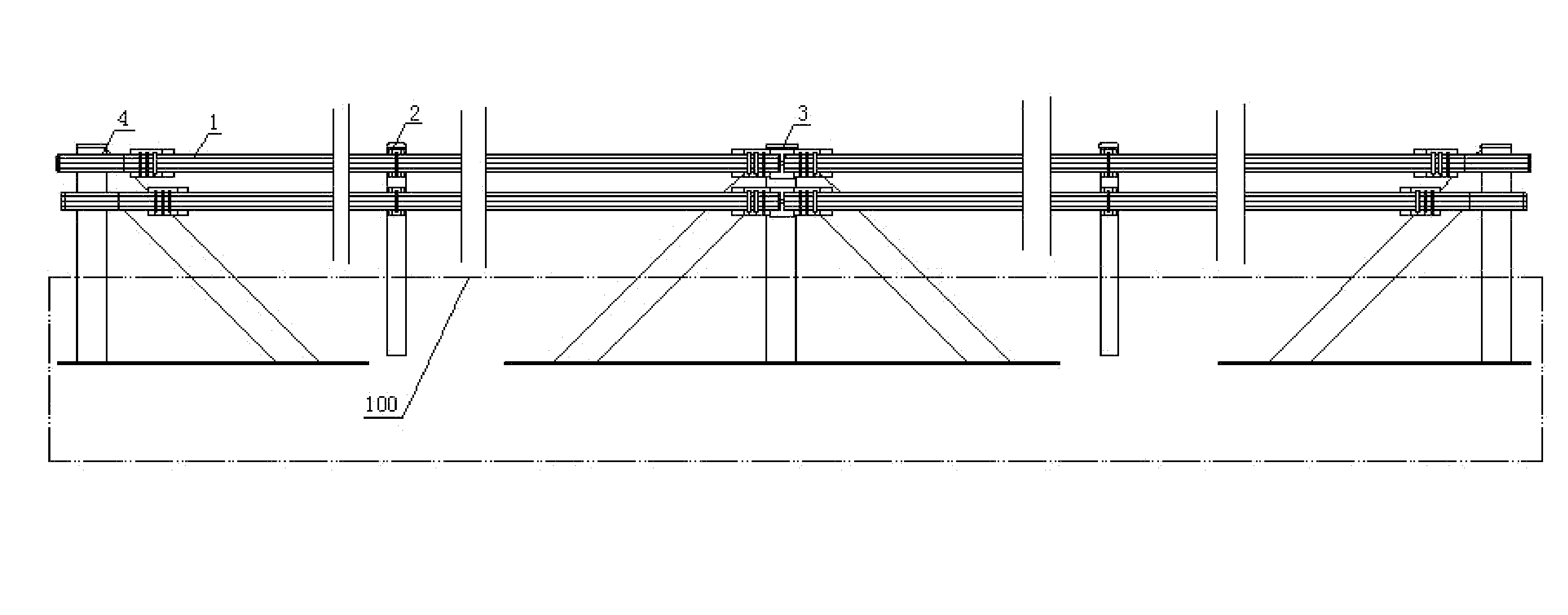
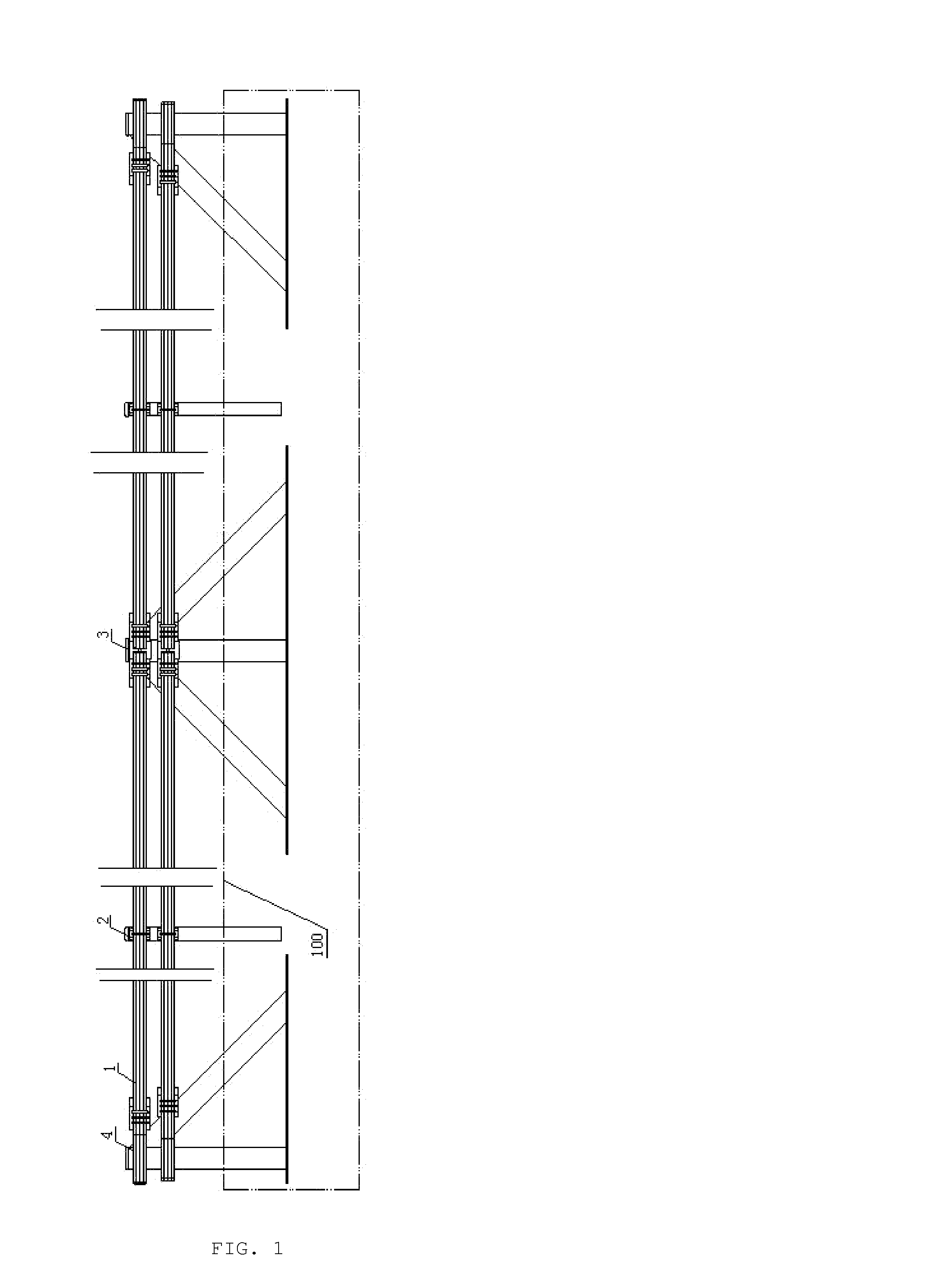
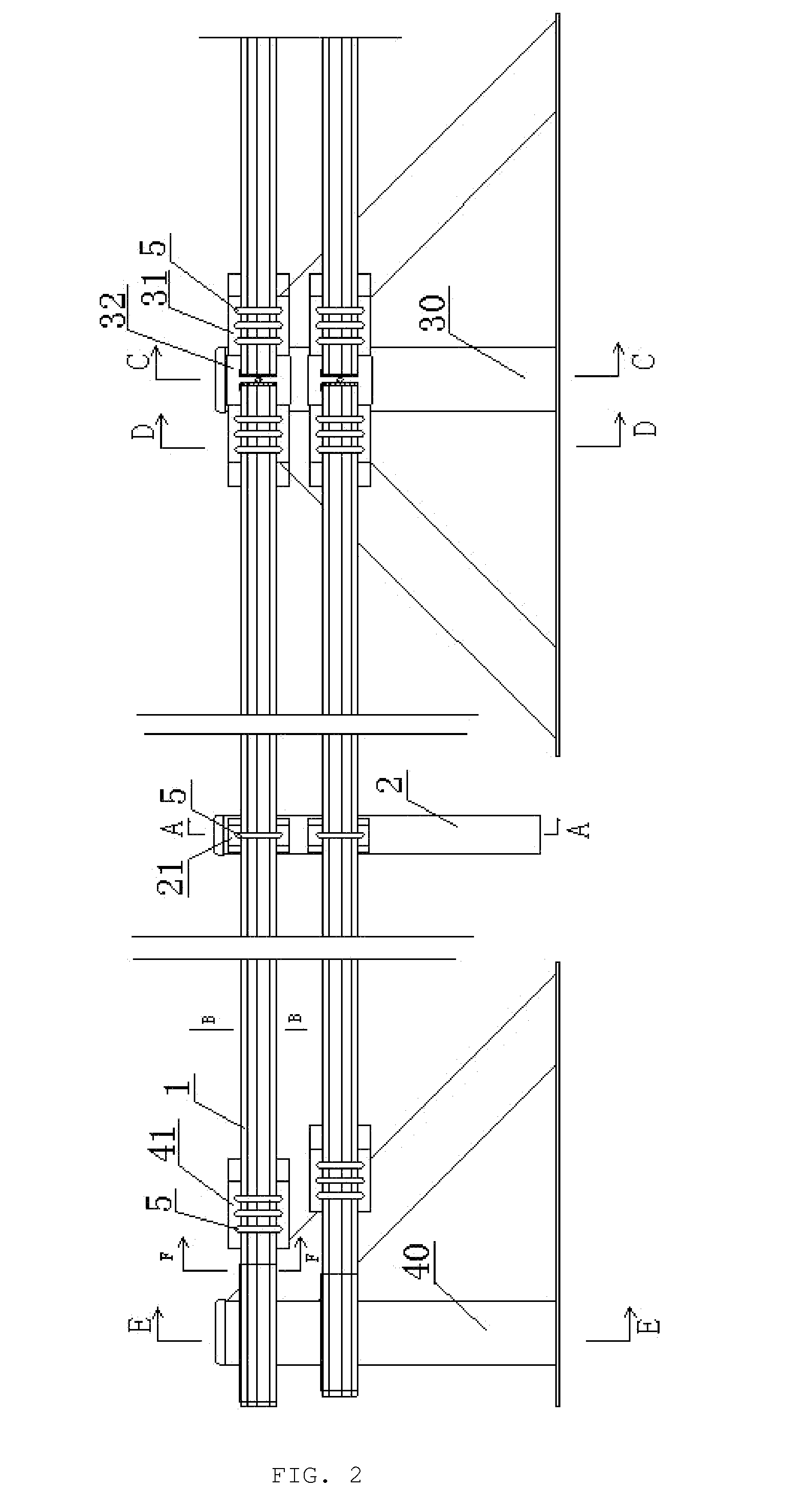
Counter-pulled type rib retaining wall of pre-stressing force cantilever
InactiveCN101899839AHigh altitudeReduced bearing capacity requirementsArtificial islandsUnderwater structuresEarthquake resistanceReinforced concrete
The invention provides a counter-pulled type rib retaining wall of a pre-stressing force cantilever. The retaining wall is formed by connecting cantilever type reinforced concrete earth-retaining wall bodies, which are symmetrically arranged on two sides of a roadbed, with a counter-pulled anchor rope which runs through the width of the roadbed, wherein the cross sections of the earth-retaining wall bodies have single-layered shapes or ladder-type multi-layer shapes. A base plate is arranged below the earth-retaining wall bodies, and ribs for mounting anchor piers are arranged in the middle parts of the earth-retaining wall bodies; a plastic pipe sleeve is arranged outside the counter-pulled anchor rope; the counter-pulled anchor rope comprises n bundles of steel stranded wires; and a grouting protective layer is arranged between the plastic pipe sleeve and the steel stranded wires. The integrity, the skid resistance, the overturn resistance, the collision resistance and the earthquake resistance of the earth-retaining wall can meet operating requirements, the limit height of the earth-retaining wall is higher than that of the conventional earth-retaining wall, and the earth-retaining wall has a wide application range and a low requirement on the foundation bearing capacity.
Owner:SHANDONG UNIV
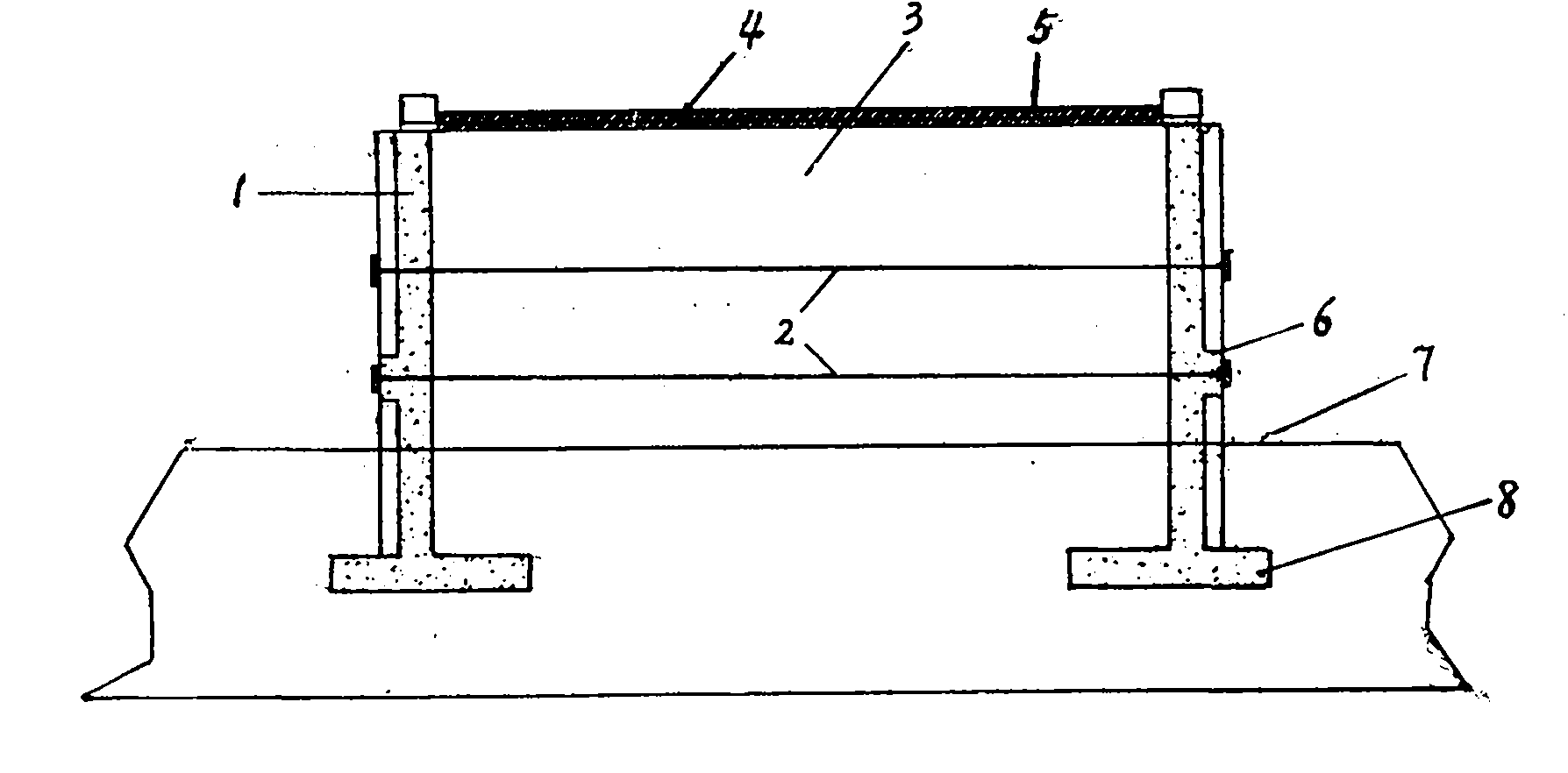
Guardrail device for highway
InactiveUS20140103278A1Reasonable design structureGood anti-collision performancePasturing equipmentRoadway safety arrangementsEngineeringCollision resistance
The present invention involves a kind of guardrail device used for a highway, wherein, said guardrail plate is formed by PVC resin and has reinforcing bands fixed therein; a bracket is set between a small vertical column and the guardrail plate, the bracket being fixed to the small vertical column, the guardrail plate being fixed to the bracket by frame bolts; a middle large vertical column mechanism is comprised of a middle connecting plate, a connecting ring and a guardrail plates having end portions; two guardrail plates wind reversely within the connecting ring; an end large vertical column mechanism comprises a sheath, an end connecting plate and guardrail plates having end portions, the sheath is fixed to the end large vertical column, the outer sheath is wound around by guardrail plates which are fixed to the end connecting plate by frame bolts. The whole design of the invention is reasonable in structure, have good performance of collision resistance, low cost and long life performance. It displays nice cushion property at the moment of vehicle collision and uneasily to impose scratch on the car, which greatly reduce the possibility to cause secondary damage to the passenger and vehicle. Moreover, the material used brings no pollution to the environment, therefore it's green.
Owner:CAI WENXUE
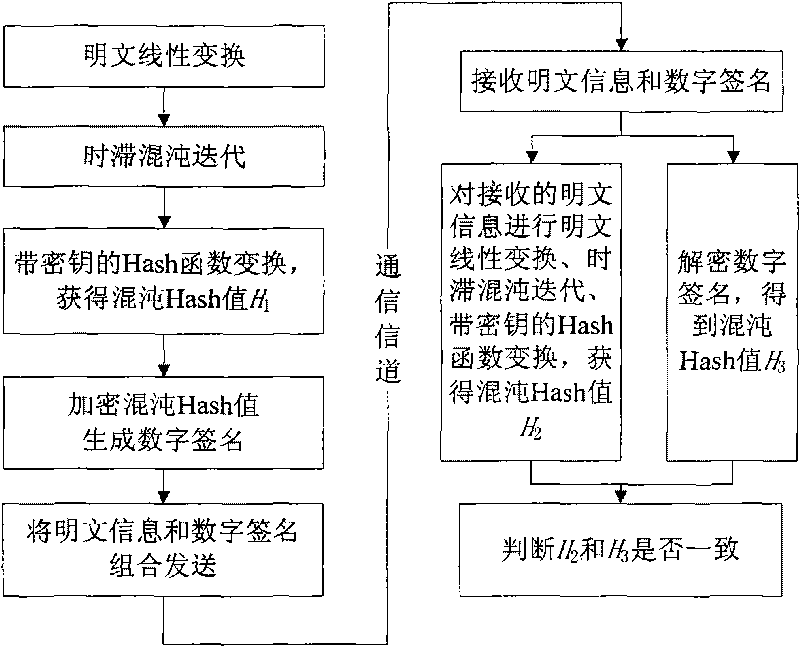
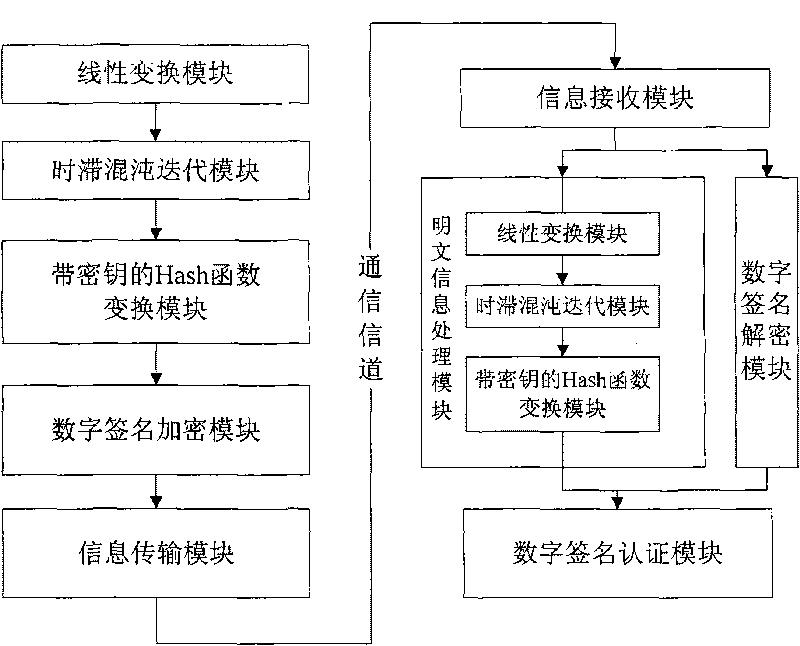
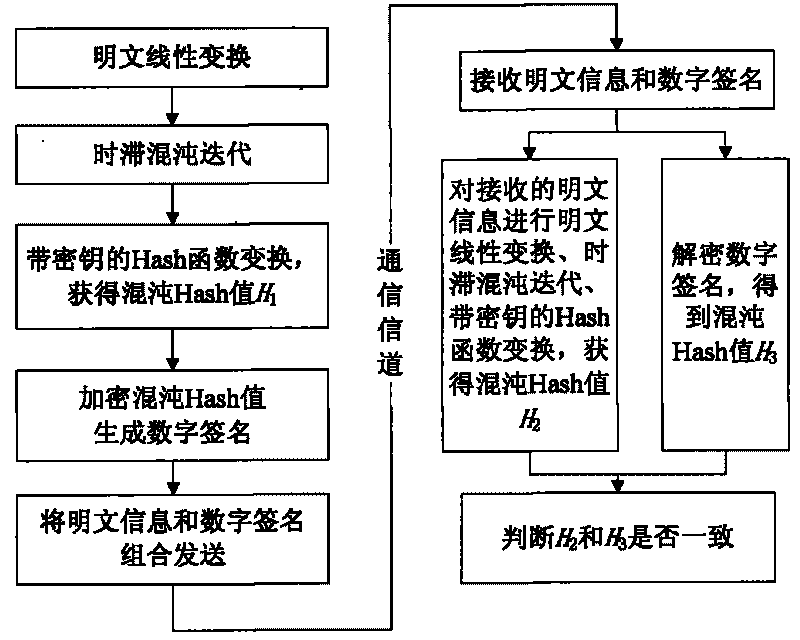
Time-lag chaos iteration-based digital signature method and device
The invention discloses a time-lag chaos iteration-based digital signature method and a time-lag chaos iteration-based digital signature device, and belongs to the technical field of communications. The process of generating a digital signature comprises the following steps: 1) performing ASCII encoding on a clear text and linearly quantizing a value domain; 2) performing one-dimensional time-lag chaos iteration; 3) performing a Hash functional transformation with a key; 4) encrypting, and the like. The process of authenticating the digital signature comprises the following steps: 5) performing the same step as the process of generating the digital signature on the received clear text and generating a Hash value; 6) decrypting the received digital signature (the Hash value); 7) authenticating, and the like. Due to the use of the sensitivity and the ergodicity of the time-lag chaos iteration, the clear-text information is modulated in the iteration track (process) of the time-lag chaos iteration, so that the generated Hash value has larger key space and higher safety. The time-lag chaos iteration-based digital signature method and the time-lag chaos iteration-based digital signature device are suitable for various secure transmission occasions of texts, video and audio files and the like which need the digital signature for verification, and have the characteristics of simple operation, high speed, irreversibility, anti-counterfeiting, strong attack and collision resistance, and the like.
Owner:UNIV OF ELECTRONICS SCI & TECH OF CHINA
Manufacturing method for flexible solar cell unit
ActiveCN101132031AEasy to operateSolve the shortcomings of not being portable and not being able to be used anytime, anywhereFinal product manufactureSemiconductor devicesEngineeringBandage
Owner:XIAMEN TOPUNIVE TECH
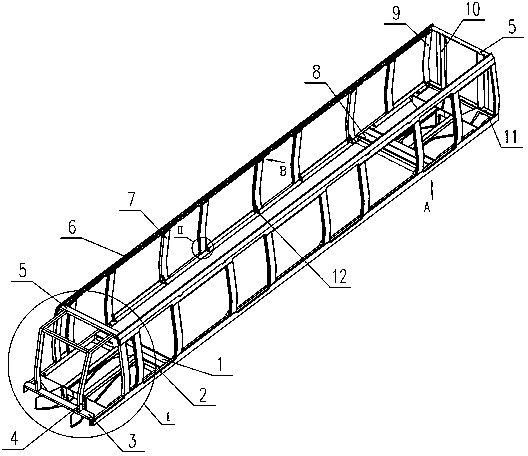
B-shaped subway vehicle body structure
ActiveCN103802849AImprove local stress conditionsIncrease stiffnessRailway transportAxle-box lubricationBogieSocial benefits
The invention discloses a B-shaped subway vehicle body structure. In order to improve the longitudinal loading capacity of a vehicle body, the vehicle body structure comprises an integral loading barrel skeleton structure including chassis edge beams, cab end beams, cab columns, top cover cross beams, top cover edge beams, door columns, angle columns, end wall columns and chassis end beams; the barrel skeleton structure is fixed above a bogie; I-end traction guide beams are fixedly connected onto the cab end beams; II-end traction guide beams are fixedly connected onto the chassis end beams. The B-shaped subway vehicle body structure has high strength while keeping the light weight of the vehicle body, can bear 1,000 kN longitudinal load, provides a structure foundation for vehicle collision resistance design, is beneficial to improve the safety performance of the vehicle, and has better economic and social benefits.
Owner:ZHUZHOU ELECTRIC LOCOMOTIVE CO
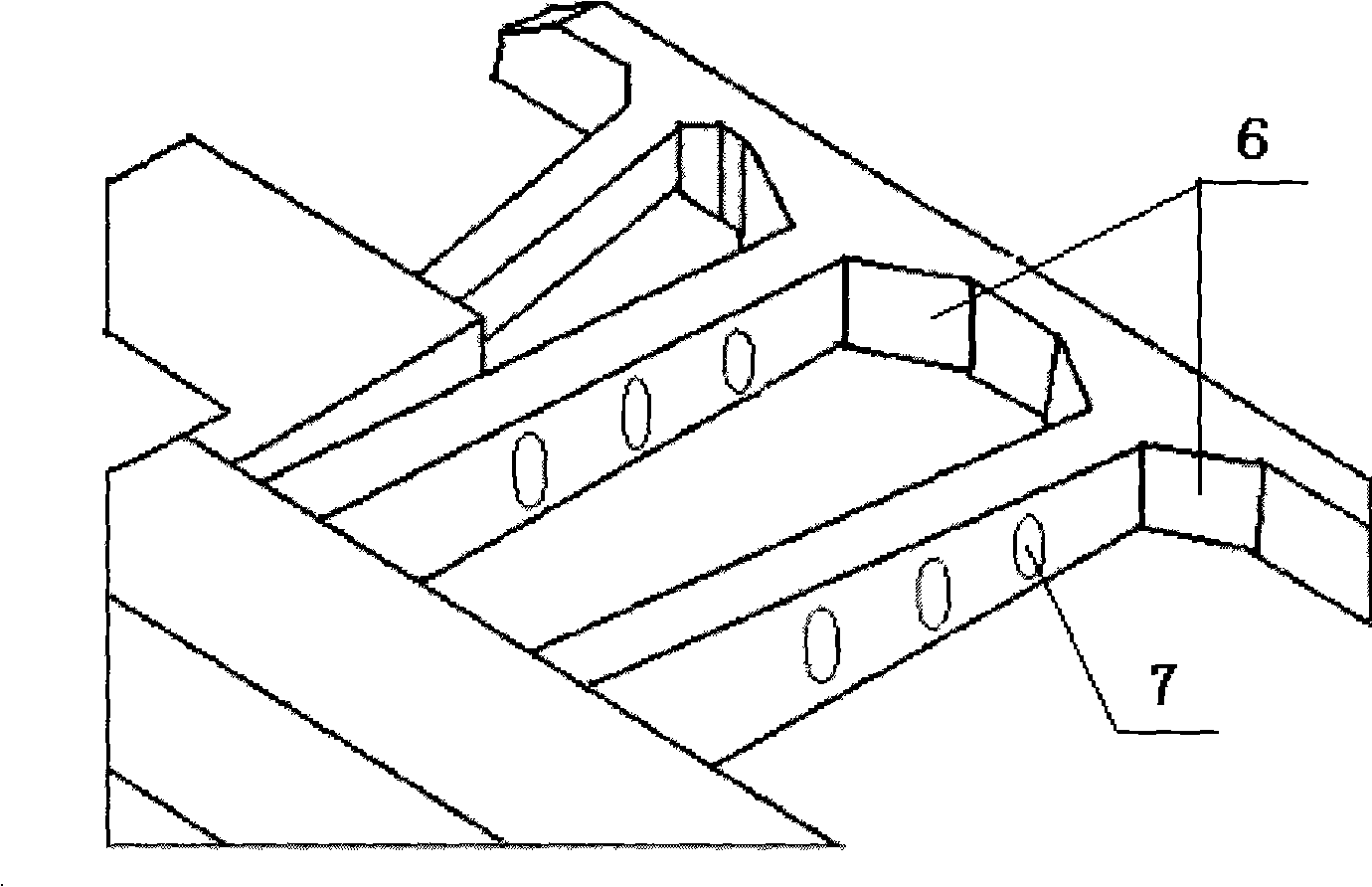
Rail vehicle anti-collision safety device
InactiveCN101289089AReduce manufacturing costPromote absorptionUnderframesEnergy absorptionEngineering
The invention relates to a safety device for railbound vehicle and discloses a collision resistance safety device for railbound vehicle, comprising a front cross beam, a longitudinal beam, a side longitudinal beam, a main energy absorption box and a side energy absorption box; one end of the longitudinal beam is connected with the front cross beam, and the other end is connected with the main energy absorption box; one end of the side longitudinal is connected with the front cross beam, and the other end is connected with the side energy absorption box; and the side longitudinal beam is positioned at the outside of the longitudinal beam; the front cross beam and the longitudinal beam are box-type closed beams; the connection point of the front cross beam and the longitudinal beam is provided with a welding strengthening plate; the side face of the longitudinal beam is provided with a plurality of holes. The safety device of railbound vehicle of the invention has good energy absorption performance and collision stability, reduces collision acceleration of vehicle, can protect passenger more effectively and is especially suitable for high-speed monorail.
Owner:SHANGHAI MAGNETIC SUSPENSION COMM ENG TECH RES CENTE
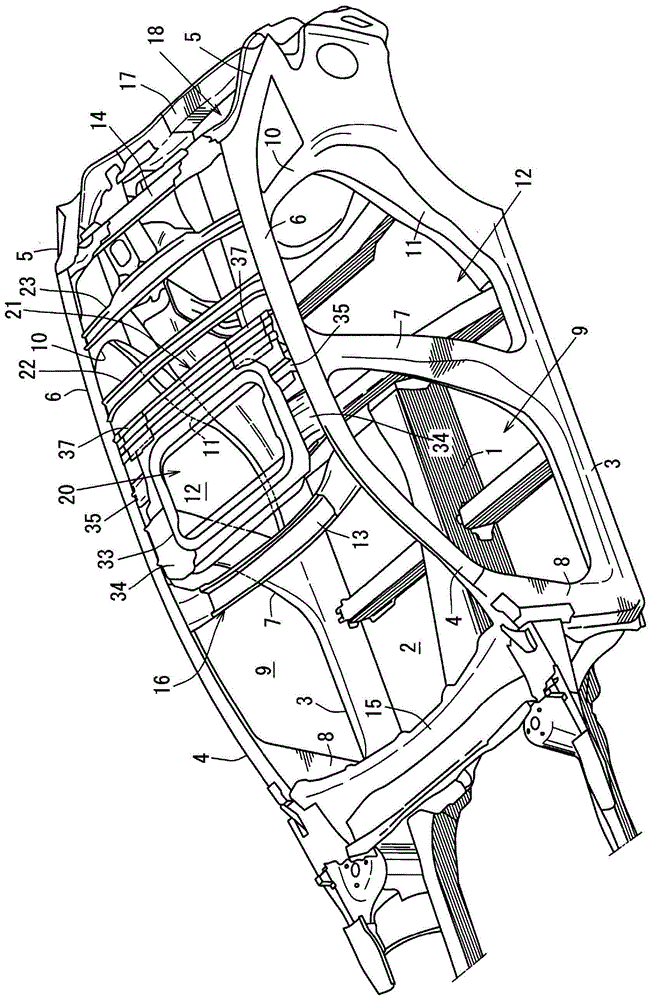
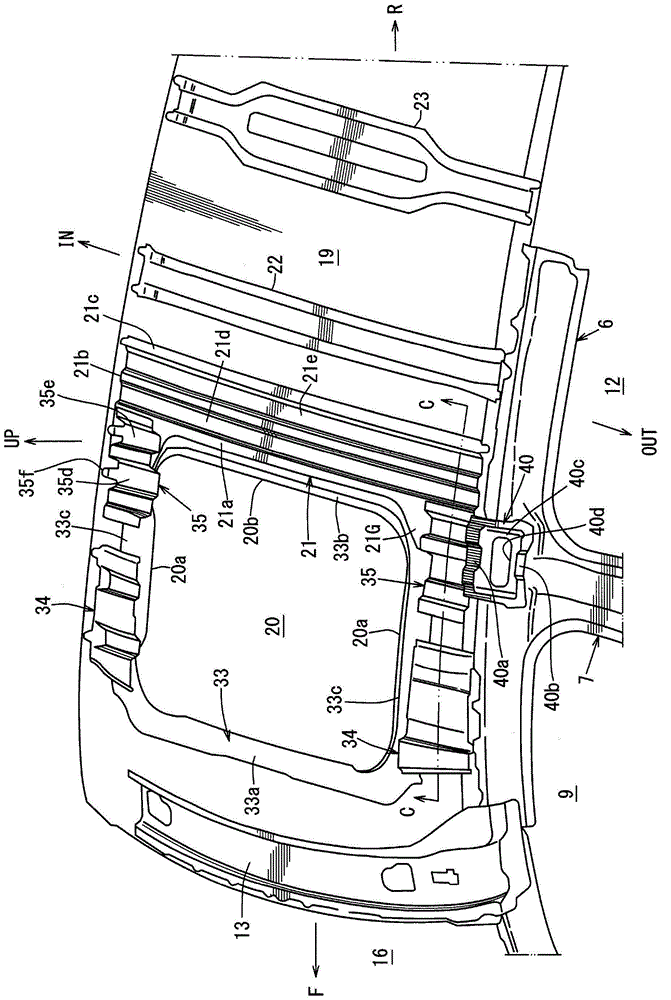
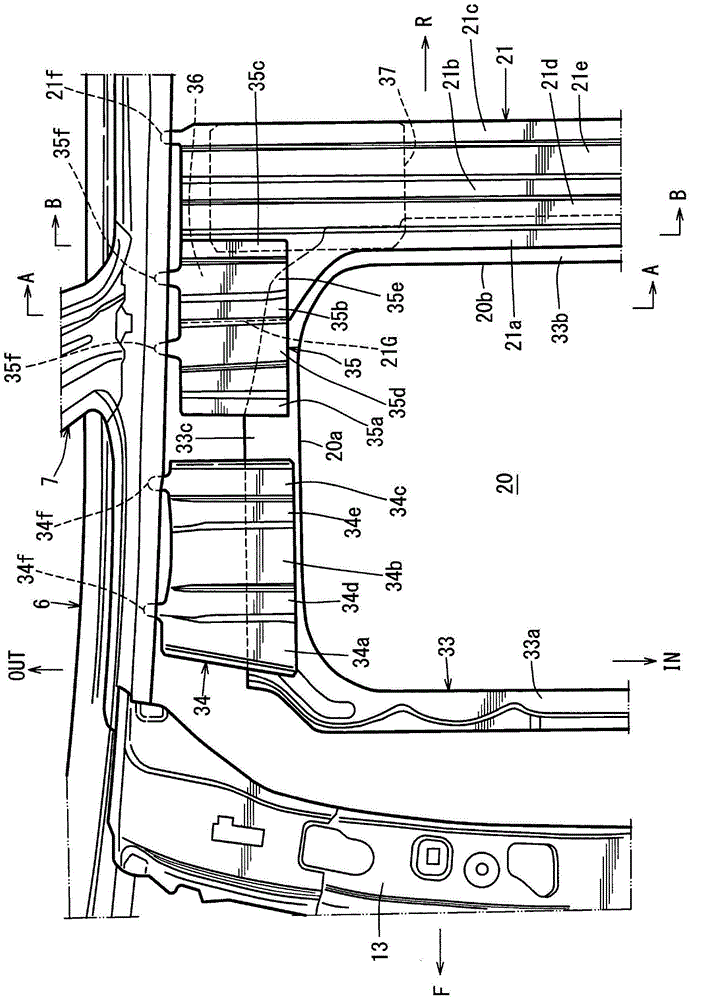
Upper vehicle-body structure of automotive vehicle provided with sun roof
ActiveCN105292268AValid linkAchieve lightweight and high rigiditySuperstructure subunitsCollision resistanceFront edge
Provided is an automotive upper portion vehicle structure with a sun roof opening, which can effectively connect the upper portion of a center pillar and an end portion position of a roof reinforcement in a vehicle width direction deviate along front and rear directions, thereby realizing light weight, and great rigidity, and in particular improving the vehicle width direction rigidity as side collision resistance. A connecting reinforcement (35) interconnecting a fixing plate (33) which is a window-frame member to reinforce a sun roof opening (20) and a roof side rail (6) at a position corresponding to a center pillar is provided. The connecting reinforcement (35) is positioned forward of the roof reinforcement (21), has a specified second sectional shape, and extends in a vehicle width direction roughly horizontally. A rear edge portion of the connecting reinforcement (35) and a front edge portion of the roof reinforcement (21) are connected to each other, and an inboard edge portion of the connecting reinforcement (35) and a front edge portion of the roof reinforcement (21) are connected via the fixing plate (33).
Owner:MAZDA MOTOR CORP
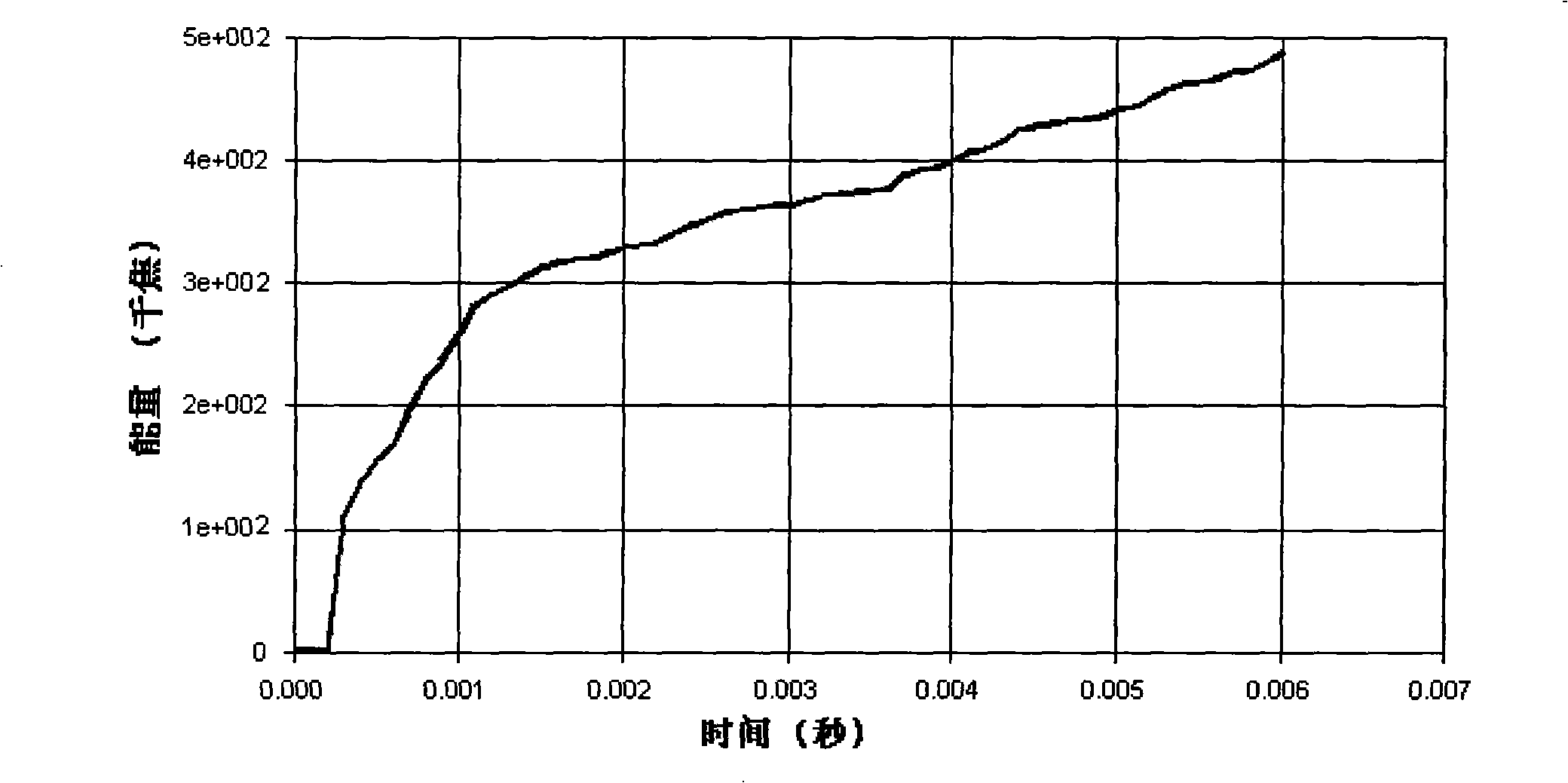
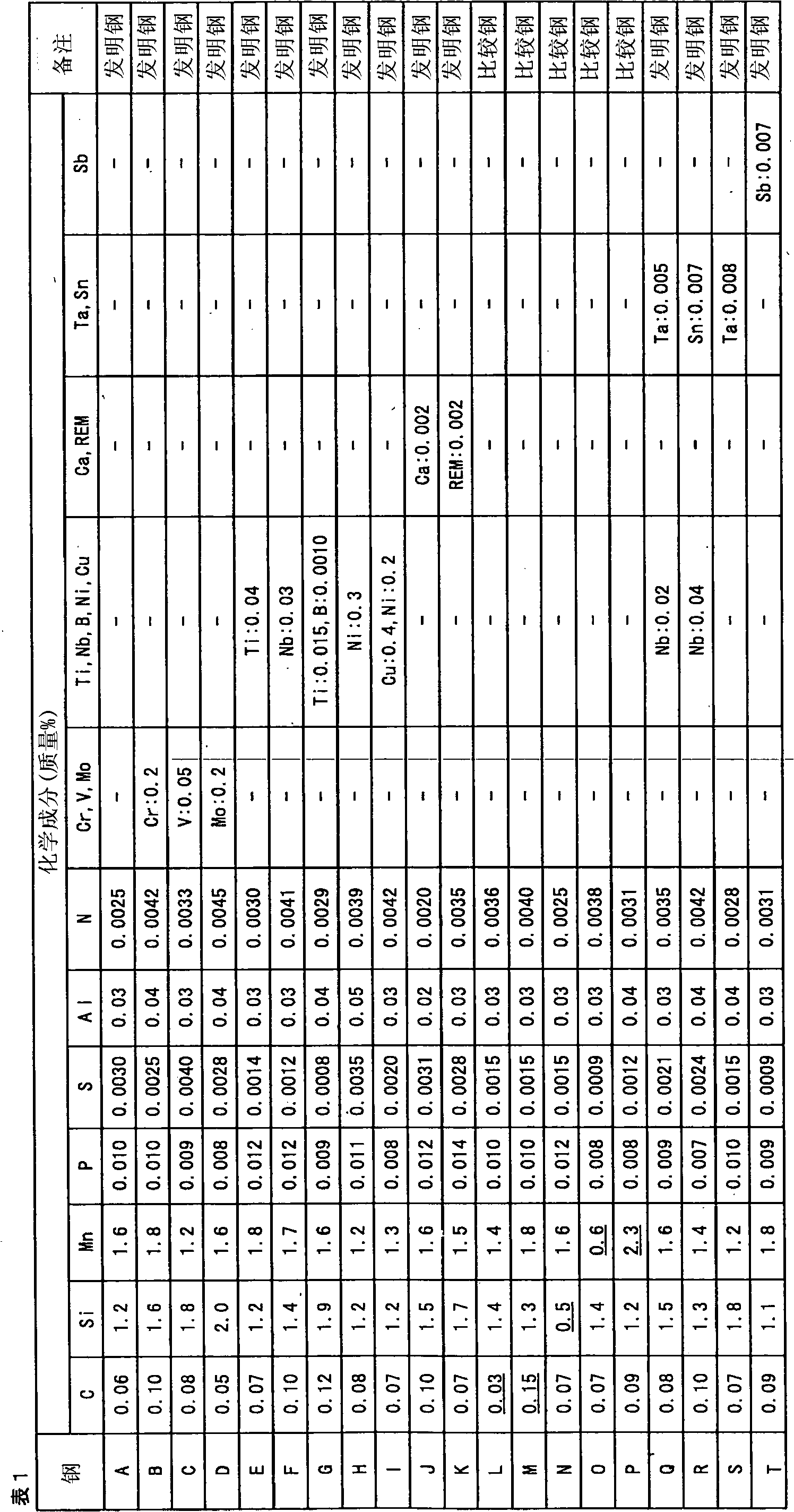
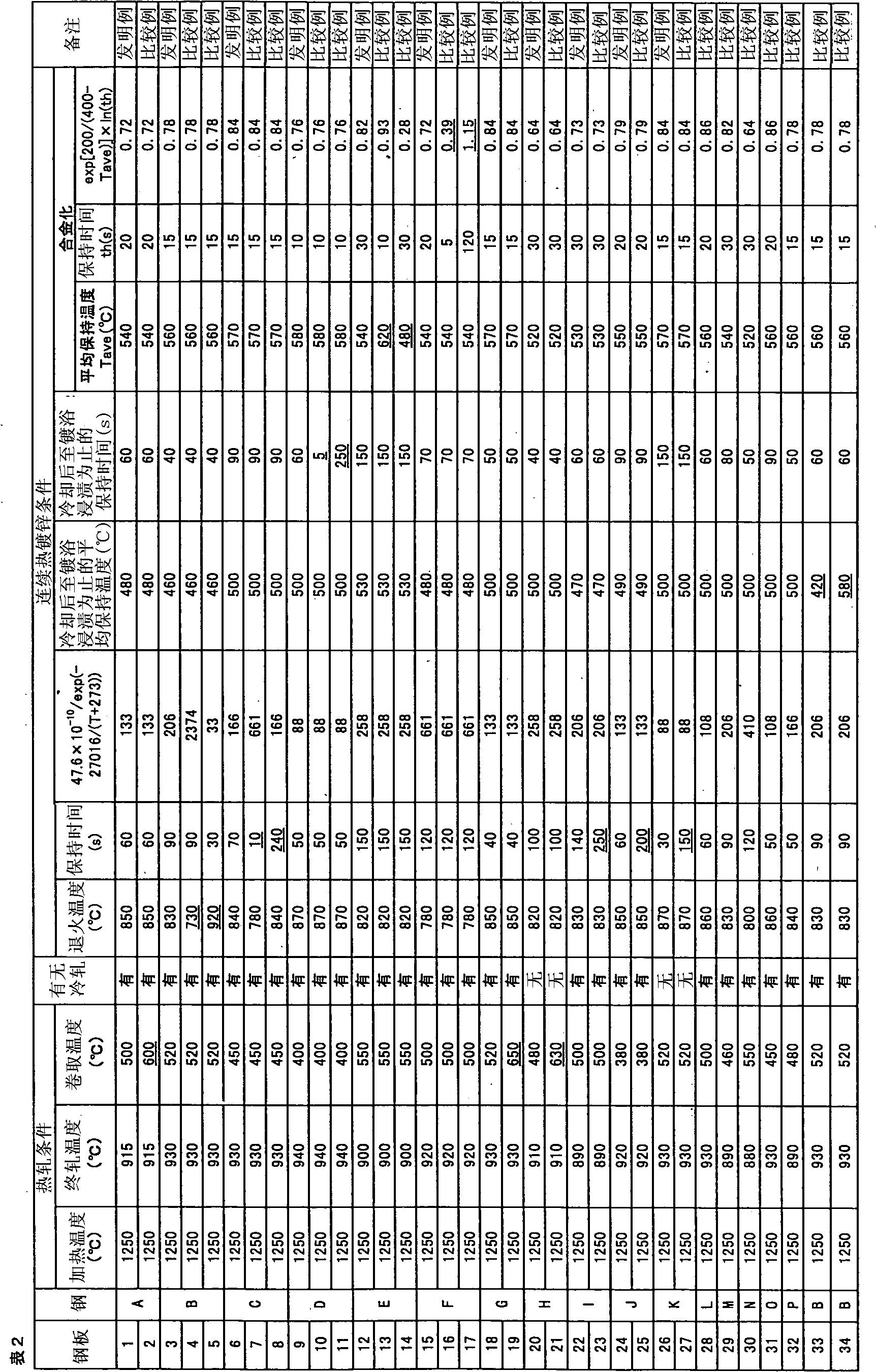
High-strength hot-dip galvanized steel sheet with excellent processability and impact resistance and process for producing same
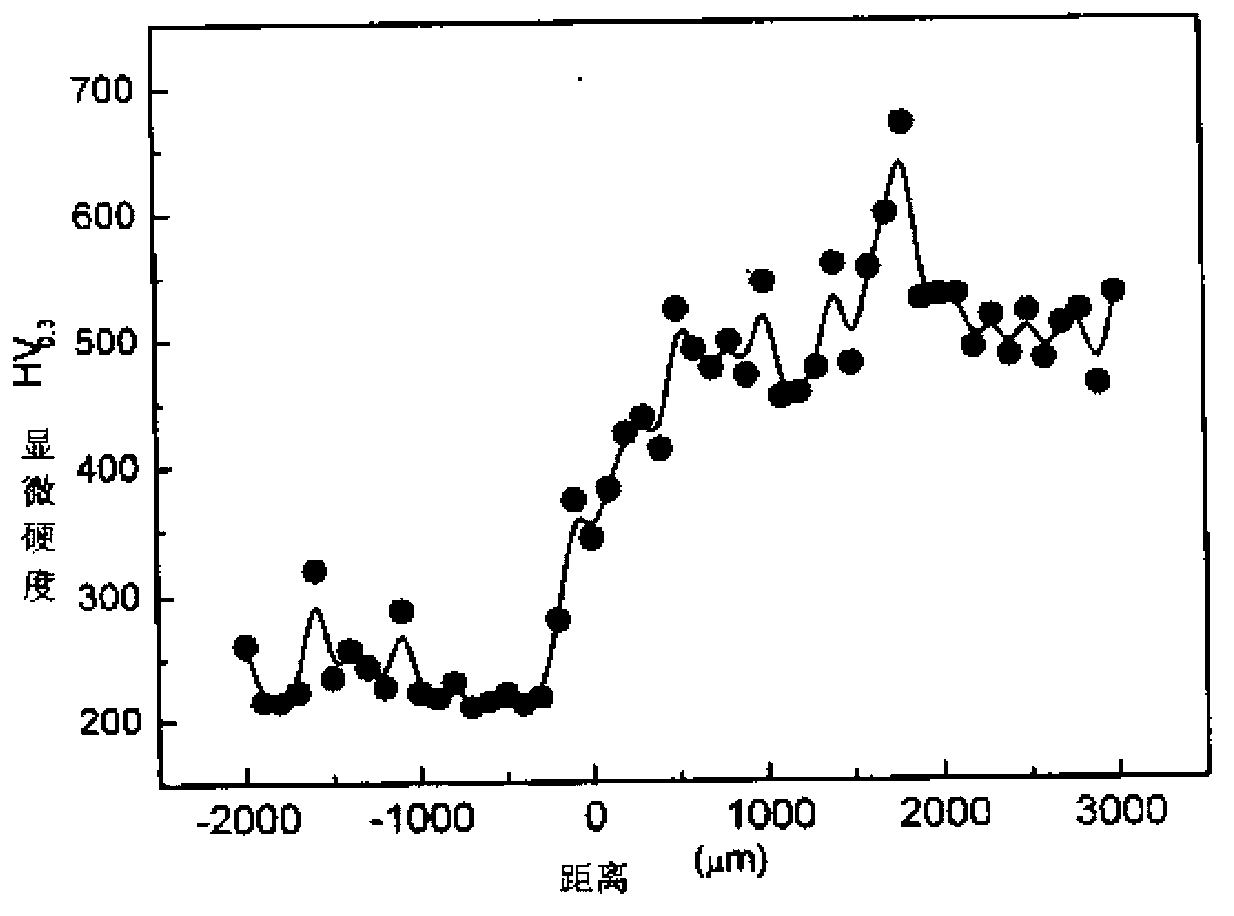
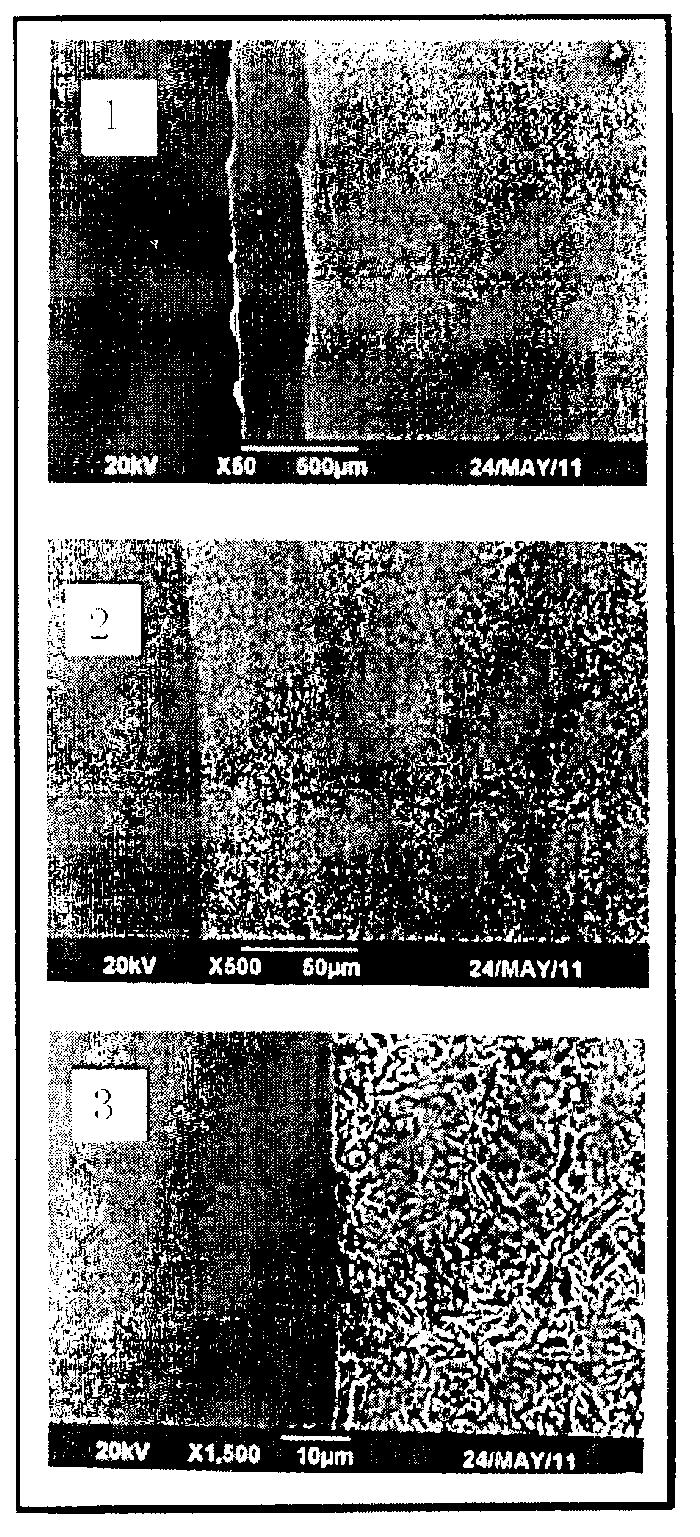
ActiveCN102712977AGood impact resistanceImprove impact resistanceHot-dipping/immersion processesFurnace typesAbsorbed energyHigh intensity
Provided is a hot-dip galvanized steel sheet which has a tensile strength TS of 590 MPa or higher and excellent processability and which, even when no strain is introduced thereinto by pressing, highly absorbs energy in a low-strain range up to about 5% and has excellent collision resistance. Also provided is a process for producing the steel sheet. The galvanized steel sheet has a composition which contains, in terms of mass%, 0.04-0.13% C, 0.7-2.3% Si, 0.8-2.0% Mn, up to 0.1% P, up to 0.01% S, and 0.01-0.1% Al, with the remainder comprising iron and incidental impurities, and has a structure which comprises, in terms of areal proportion, at least 75% ferrite phase, at least 1% bainitic ferrite phase, and 1-10% pearlite phase, has a martensite phase content of up to 10% in terms of areal proportion, and satisfies (areal proportion of martensite) / ((areal proportion of bainitic ferrite)+(areal proportion of pearlite))<=0.6, and in which the ratio of the Mn concentration in the ferrite phase to the Mn concentration in the second phase is 0.70 or above.
Owner:JFE STEEL CORP
Collision-resistant structure of agricultural plant protection unmanned aerial vehicle
InactiveCN104260875AImprove crash resistanceStrong wind resistanceWingsPower plant typeAgricultural engineeringCollision resistance
The invention discloses a collision-resistant structure of an agricultural plant protection unmanned aerial vehicle. The collision-resistant structure comprises a wing shell and a hybrid power system arranged in the wing shell, wherein the hybrid power system comprises a main rotor and multiple auxiliary rotors; the main rotor is arranged in the middle of the wing shell; the multiple auxiliary rotors are uniformly distributed at several corners of the wing shell; and finned plates with adjustable directions are arranged below the main rotor. According to the mode, the collision-resistant structure disclosed by the invention has the advantages that the collision resistance of the unmanned aerial vehicle can be improved, and the unmanned aerial vehicle has the excellent wind resistance and the good control ability.
Owner:优飞科技(苏州)有限公司
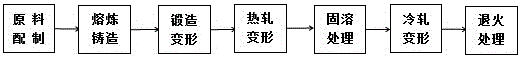
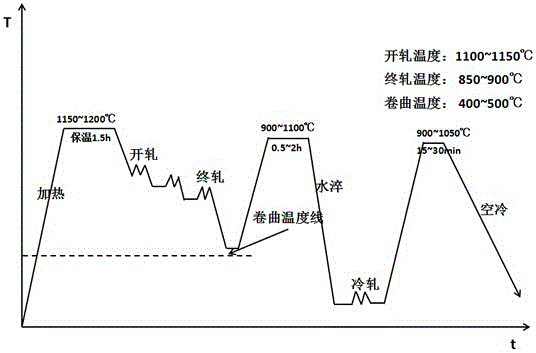
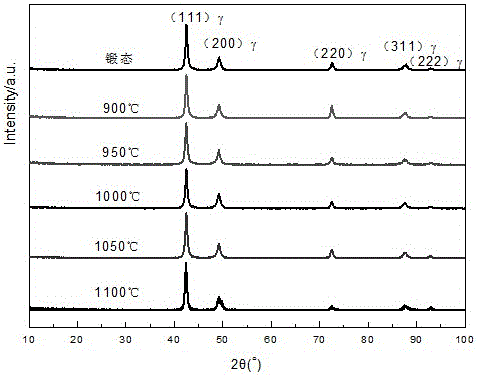
Microalloyed high-aluminum high-ductility steel plate and manufacturing method thereof
The invention relates to a microalloyed high-aluminum high-ductility steel plate and a manufacturing method thereof, and belongs to the field of alloy steel. The steel plate comprises the chemical components, by mass, including 0.8%-1.0% of C, 28%-30% of Mn, 8.0%-10% of Al, 0.02%-0.10% of Nb, 0.02%-0.10% of V, 0.02%-0.10% of Ti, 0.02%-0.08% of N, 0-0.003% of P, 0-0.003% of S and the balance Fe and inevitable impurities. The manufacturing method comprises the steps that firstly, raw materials are prepared according to the chemical components, then a plate billet is forged after smelting and casting, the plate billet is heated, homogenized and subjected to multi-pass hot rolling deformation with the accumulative deformation rate being 85%-90%, water cooling after rolling is conducted, and then the plate billet is air-cooled to the room temperature; secondly, the hot-rolled steel plate is subjected to solution treatment, fast heated to a solution treatment temperature for heat preservation for a period of time, and then water-quenched to the room temperature; thirdly, the steel plate subjected to the solution treatment is pickled, cold-rolled and subjected to multi-pass rolling deformation with the accumulative compression amount being 65%-80%; and fourthly, the cold-rolled steel plate is subjected to final annealing treatment, and then water-quenched to the room temperature, so that the microalloyed high-aluminum high-ductility steel plate is obtained. According to the steel plate manufactured through the manufacturing method, the strength and ductility product can reach 50 GPa*%, and the impact and collision resistance of the material is obviously improved.
Owner:KUNMING UNIV OF SCI & TECH
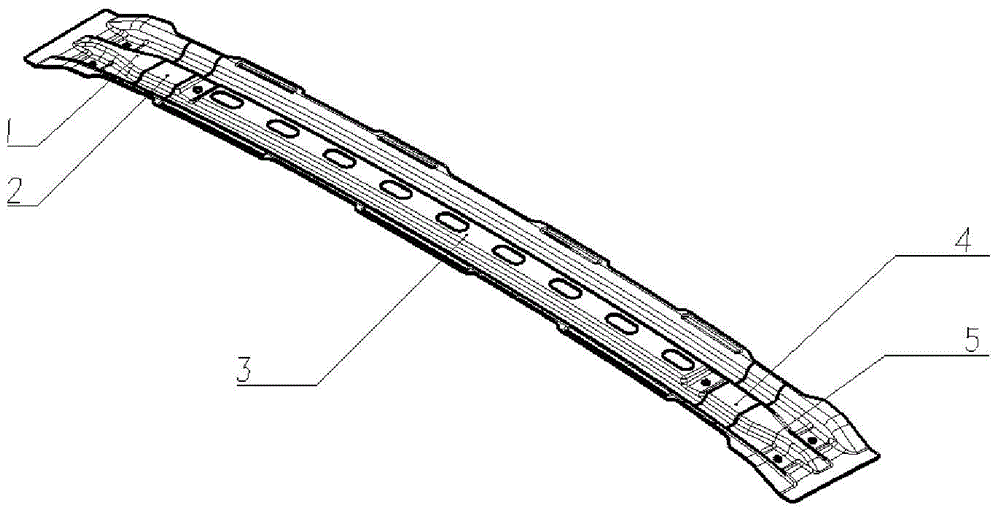
Variable-thickness automobile roof middle cross beam and manufacturing method thereof
InactiveCN104925141AEnsure safetyReduce weightSuperstructure subunitsVariable thicknessCollision resistance
The invention provides a variable-thickness automobile roof middle cross beam. A roof middle cross beam body is of a thin-wall structure and sequentially comprises a left body section, a left transition section, a middle body section, a right transition section and a right body section. The left body section and the right body section are connected with an automobile side body column B and have a uniform thickness. The left transition section and the right transition section are of a continuous variable-thickness structure and become smaller in thickness from the two ends to the middle body section. The middle body section is the thinnest portion of the roof middle cross beam. According to the variable-thickness automobile roof middle cross beam, by means of the design that parts of different thicknesses are arranged along an automobile body in the Y axis direction, the safety requirements for collision resistance and pressure resistance of the roof middle cross beam are met, and the design of light parts can be achieved at the same time.
Owner:BAOSHAN IRON & STEEL CO LTD
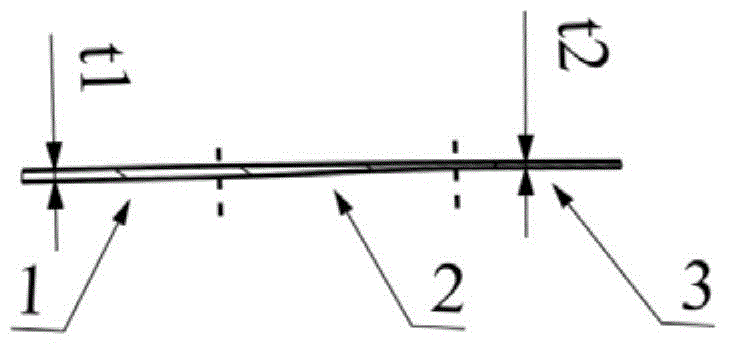
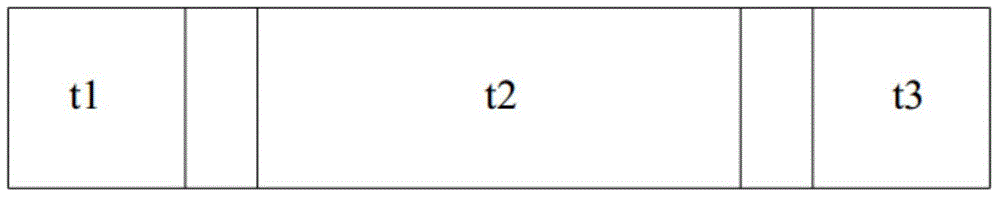
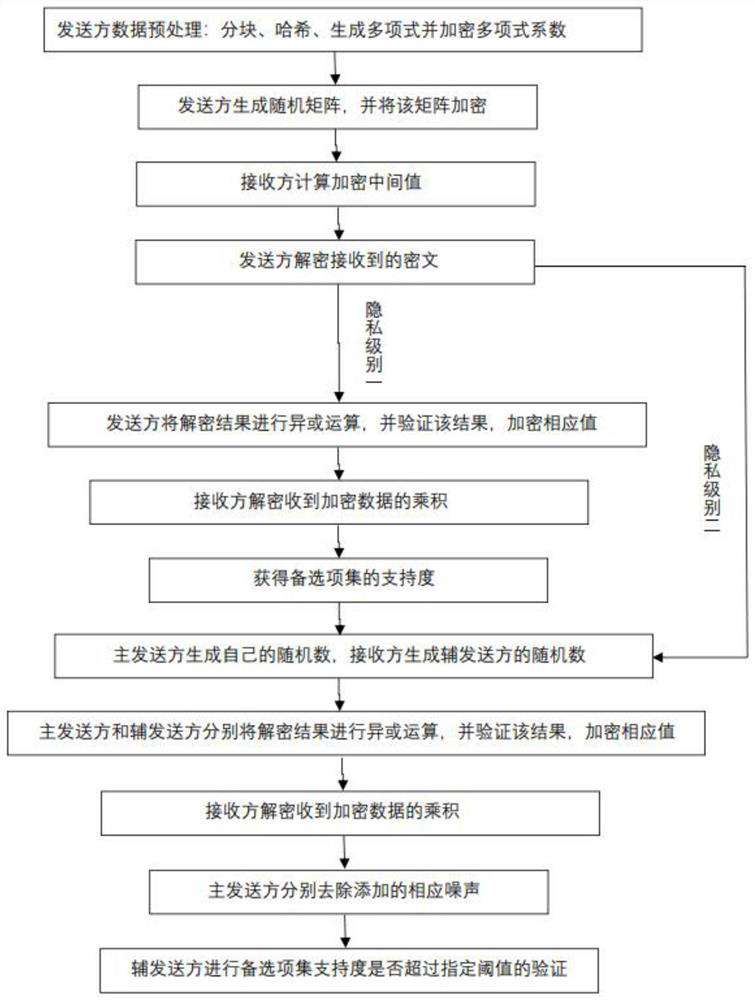
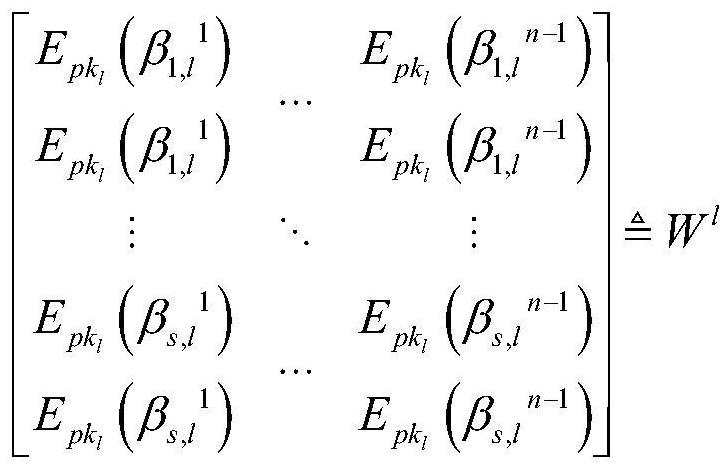
Vertical partition data PPARM method based on multi-party set intersection solving
ActiveCN112966283AIncrease in the number of participating sitesFewer communication roundsEncryption apparatus with shift registers/memoriesDigital data protectionHash functionAlgorithm
The invention discloses a vertical partition data PPARM method based on multi-party set intersection solving, and mainly solves the technical problems of high communication traffic cost and insufficient privacy protection in the prior art. The scheme comprises the following steps: 1) a sender preprocesses data; 2) a first protocol execution stage: firstly, a sender encrypts a random matrix, and a receiver calculates an encryption intermediate value by using a homomorphic encryption algorithm; then, the sender performs result verification by using the collision resistance of the hash function; finally, the receiver decrypts to obtain the support degree; and 3) an execution stage of the second protocol: the difference between the stage and the protocol I is that a verification result is firstly subjected to blind processing so as to cover the real support degree, and finally, security comparison is carried out. According to the invention, along with the increase of participating sites, when the privacy level I is reached, the number of communication rounds is small, and when the privacy level II is reached, a completely trusted third-party server does not need to be introduced; therefore, the communication cost is effectively reduced, and the information privacy is improved.
Owner:XIDIAN UNIV
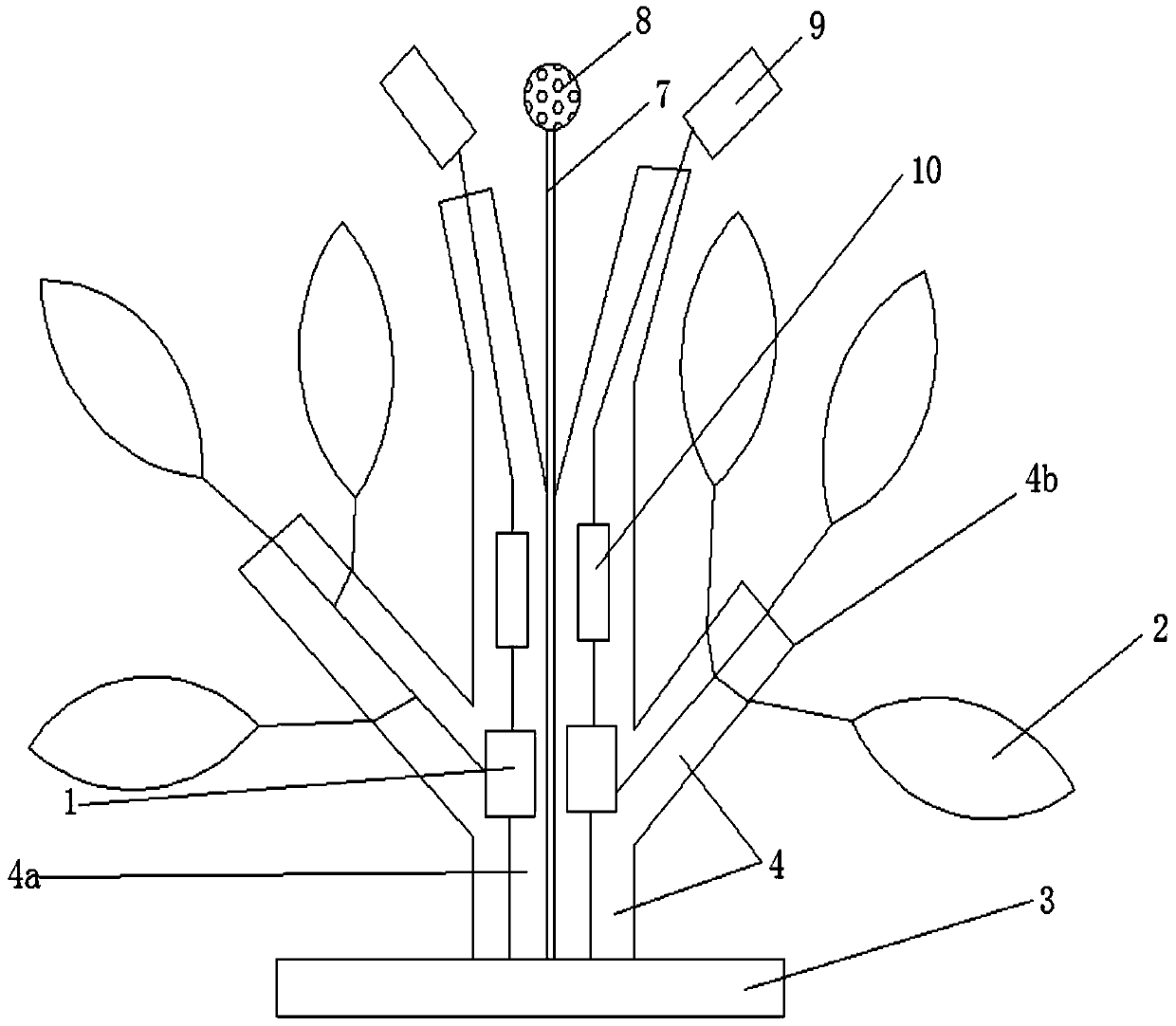
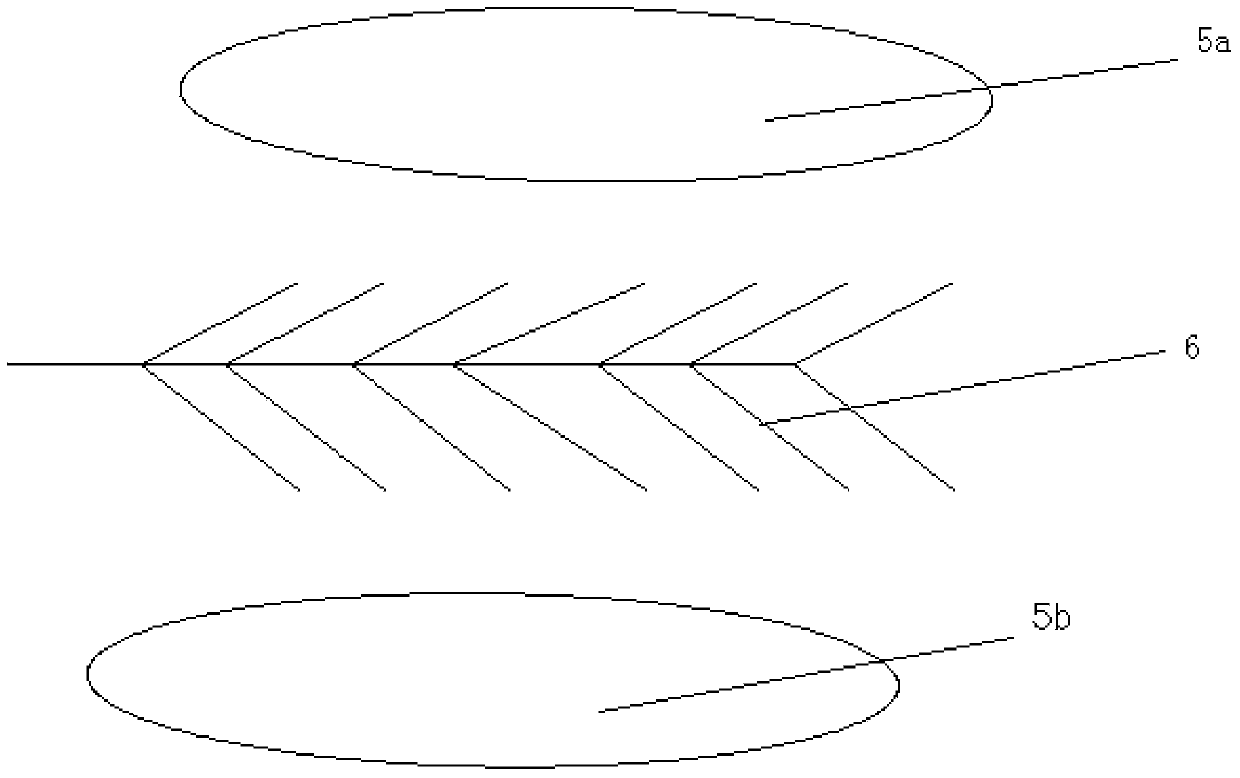
High-voltage electrostatic precipitator
InactiveCN103691556ASimple and safe structurePlay a decorative roleElectrode constructionsParticulatesHome environment
The invention discloses a high-voltage electrostatic precipitator. The high-voltage electrostatic precipitator comprises a high-voltage generation module and electrostatic precipitation boards, and is characterized by further comprising a base and at least one mounting rod mounted above the base, wherein the high-voltage generation module is mounted in the mounting rod, the electrostatic precipitation boards are distributed on the mounting rod and connected with the high-voltage generation module through wires. The high-voltage electrostatic precipitator can be made in a simulation tree shape, is simple in structure, safe, attractive and elegant, can be combined organically with urban or home environment and can also have a decorative function; the electrostatic precipitator is long in service life and low in energy consumption, can absorb and precipitate suspended particulates and PM 2.5 in urban public places and home in an omnibearing and three-dimensional manner, and has good performance of wind resistance, collision resistance and bending resistance; and further, a solar panel is adopted for power supply, so that the electrostatic precipitator is independent from external power supply while saving the energy, and the application field of the electrostatic precipitator is broadened effectively.
Owner:广东瑞通文化发展有限公司
Simplified analysis method for collision bending of thin-wall curved beam of automotive body
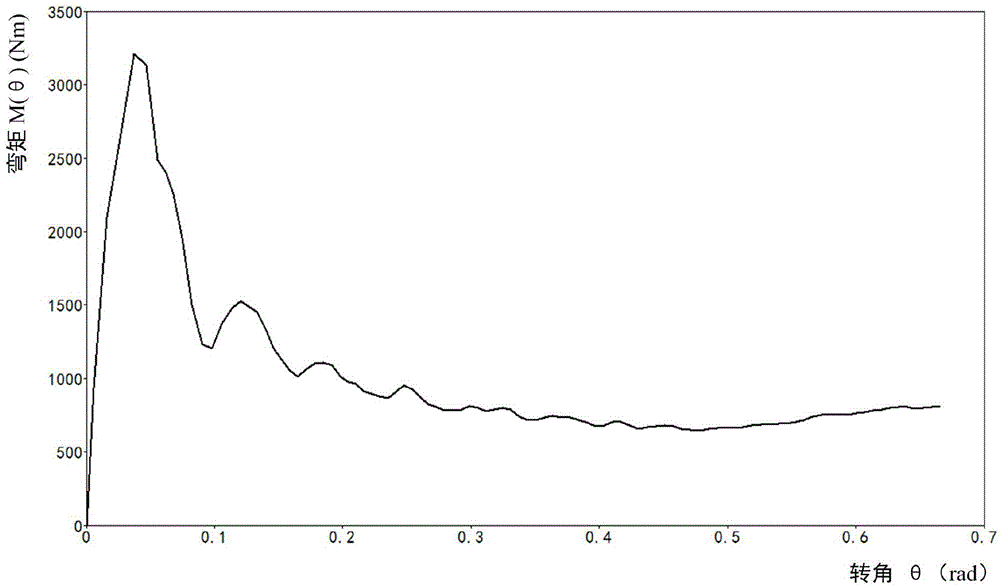
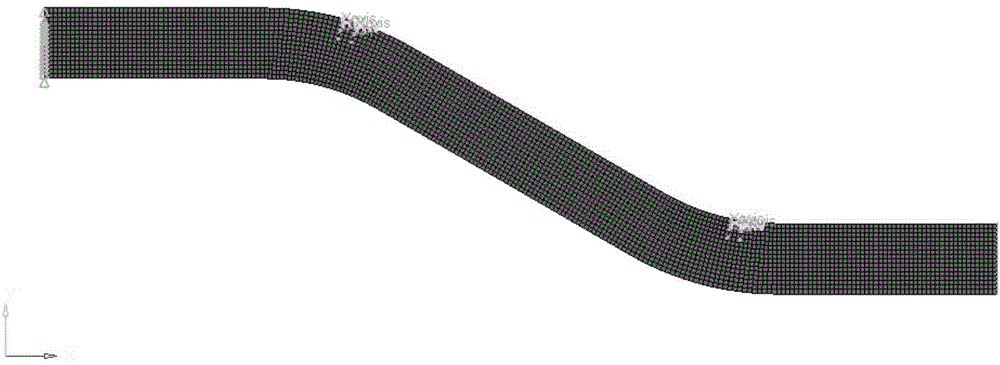
InactiveCN103559354APredicting Bending Deformation PropertiesImprove simulation accuracySpecial data processing applicationsElement modelCollision analysis
The invention discloses a method for establishing a simplified model for collision bending of a thin-wall curved beam of an automotive body by adopting a beam element, a nonlinear rotating spring element, a damping element and a column hinge element and belongs to the field of the design for the automotive body. The method is mainly adopted for researching the collision resistance at a conceptual phase for an automobile. According to the method, a bending moment and corner (M(Theta)-Theta) curve is evaluated for the nonlinear rotating spring element during a bending process of the thin-wall curved beam, so as to simulate the rotating features of a plastic hinge of the thin-wall curved beam during the bending process. The damping element and the column hinge element are established at a joint of the nonlinear rotating spring element, so that a correct moving relation of the model during an analysis process is ensured. The simplified analysis method for the collision bending of the thin-wall curved beam of the automotive body provided by the invention can fully meet the requirements for the research on the collision resistance at the conceptual phase for the automobile, the time for calculating a finite element model in the collision analysis of the automobile is greatly shortened and the working efficiency is increased.
Owner:JILIN UNIV
Metal surface imitation exterior paint
InactiveCN101875798ARealistic metal decoration effectGood weather resistanceRubber derivative coatingsEpoxy resin coatingsEpoxyRecoating
The invention discloses metal surface imitation exterior paint which comprises 10-15 parts of higher chlorinated polyethylene, 10-15 parts of thermoplastic acrylic resin, 7-10 parts of chlorinated rubber resin, 3-8 parts of epoxy resin, 30-50 parts of dimethylbenzene, 5-10 parts of butyl acetate, 20-40 parts of non-leafing silver powder, 5-10 parts of pearl powder, 6-16 parts of plasticizer, 2-5 parts of metal directing agent and 0.7-1.5 parts of ultraviolet absorber. The metal surface imitation exterior paint has excellent weather resistance, is resistant to various corrosive substances, protects outer walls of a building for a long time, prolongs the service life of the building, and is applicable to areas where air is seriously polluted. A paint film has high strength, water resistance, wear resistance, collision resistance and low maintenance cost and is not easy to damage. Simultaneously, the paint film is smooth, has a certain self-cleaning ability, and can remain brightness for a long time. When damaged, the paint film can be repaired by repainting, which is simple and practicle and has a good repair effect.
Owner:刘昆虎